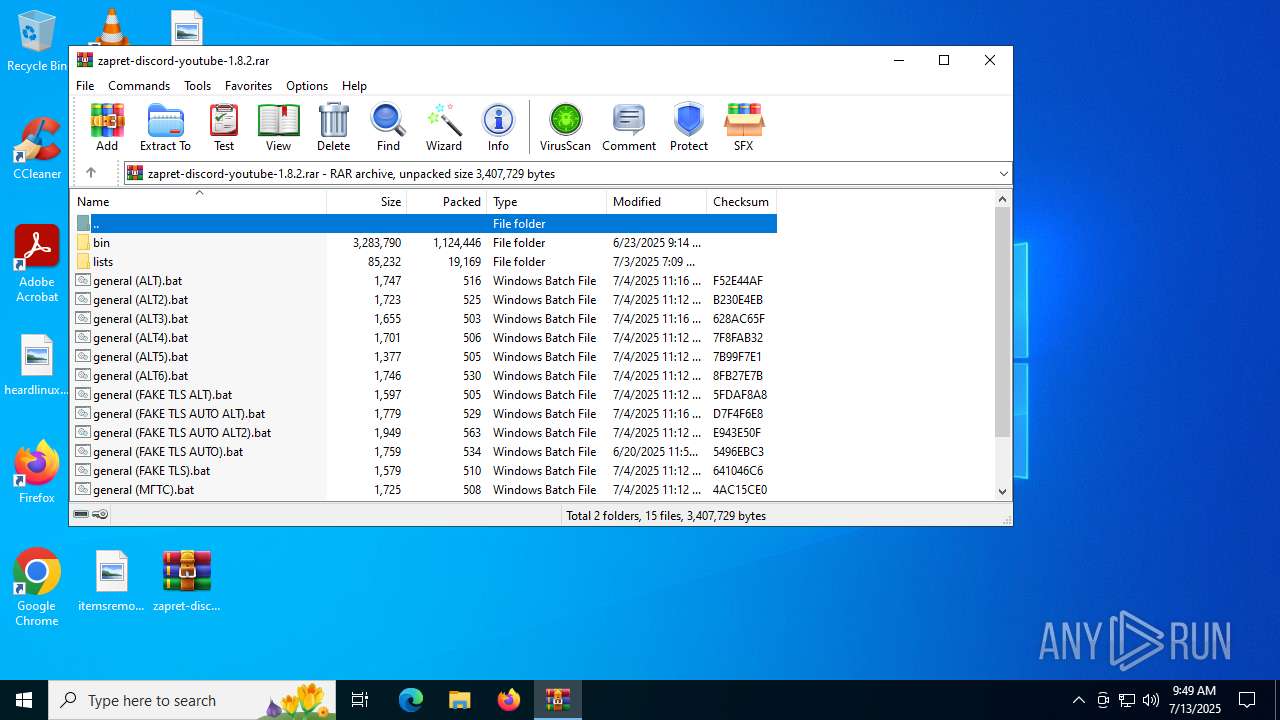
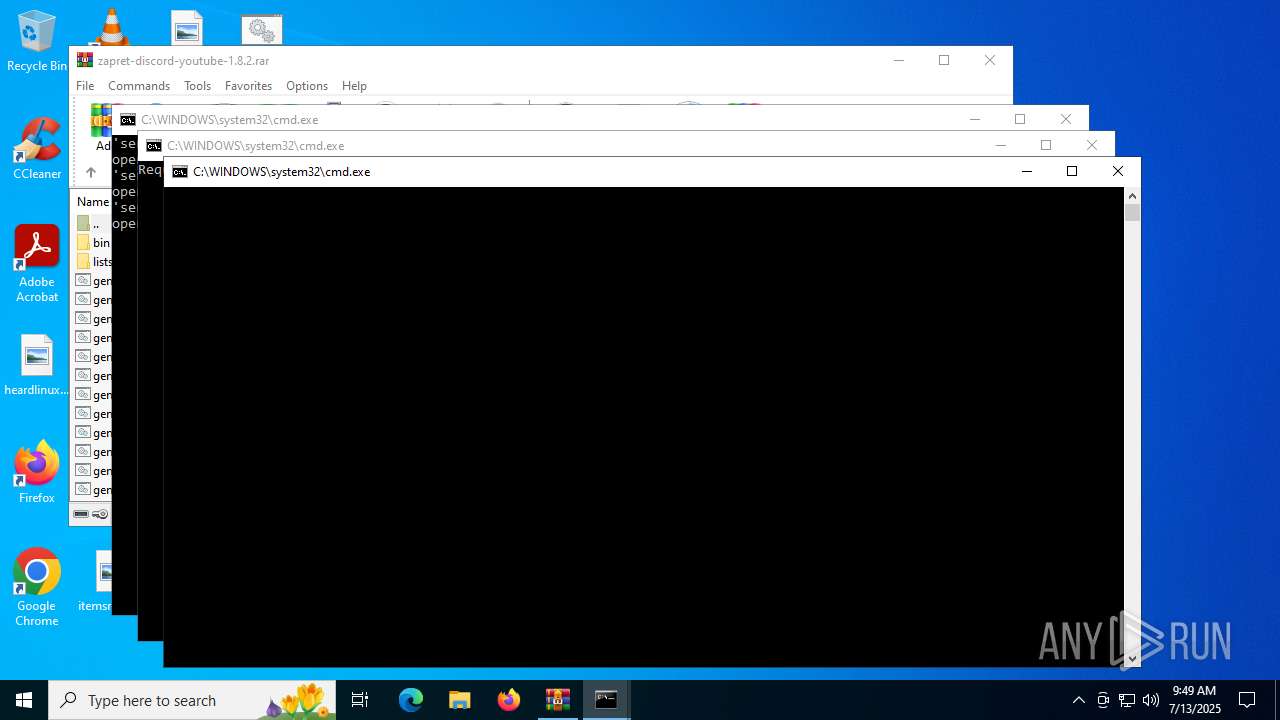
| File name: | zapret-discord-youtube-1.8.2.rar |
| Full analysis: | https://app.any.run/tasks/cf39b3d0-34a0-443a-a3af-09ca00ef9729 |
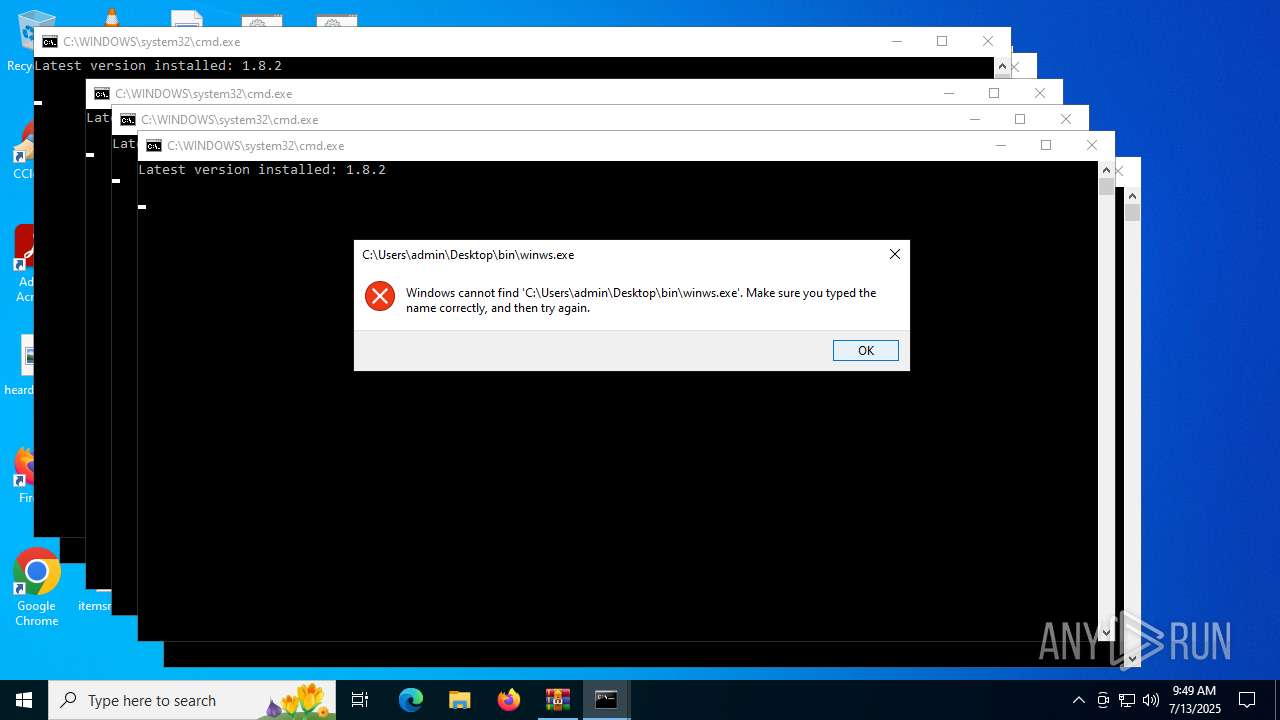
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2025, 09:49:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 699594F08756F1CCDB37D3C888866C24 |
| SHA1: | 29D3AB661D808806F282273E1C1E71BF753E8168 |
| SHA256: | 245BC512EC75518DBECE7542E4CA9F3651B0E34006031CDA16E7A70743C23D5A |
| SSDEEP: | 49152:1wAXb4FMyNCQMf5udb/DNj7Ze9rm45sDC69wDe1fwTCFvppsBS9VWIwQtkcTa8Z9:+AXb4utV58b/Jj789rv5D6uDefjFvppz |
MALICIOUS
No malicious indicators.SUSPICIOUS
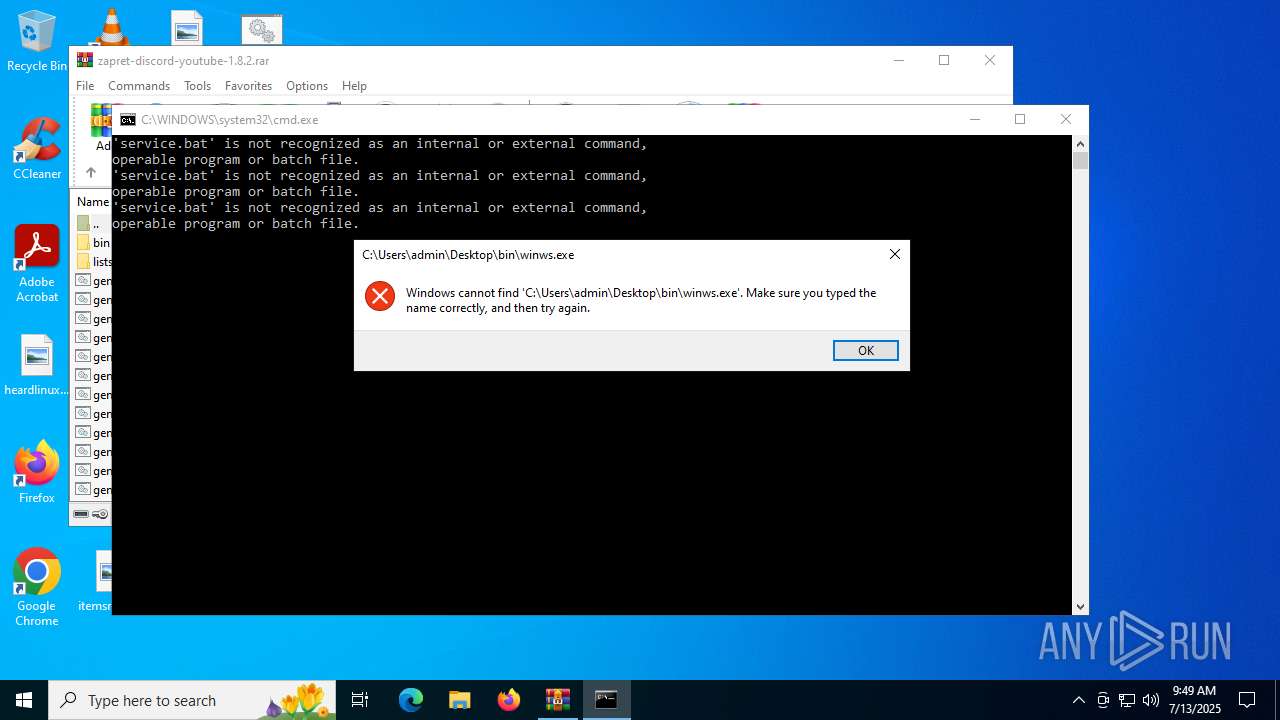
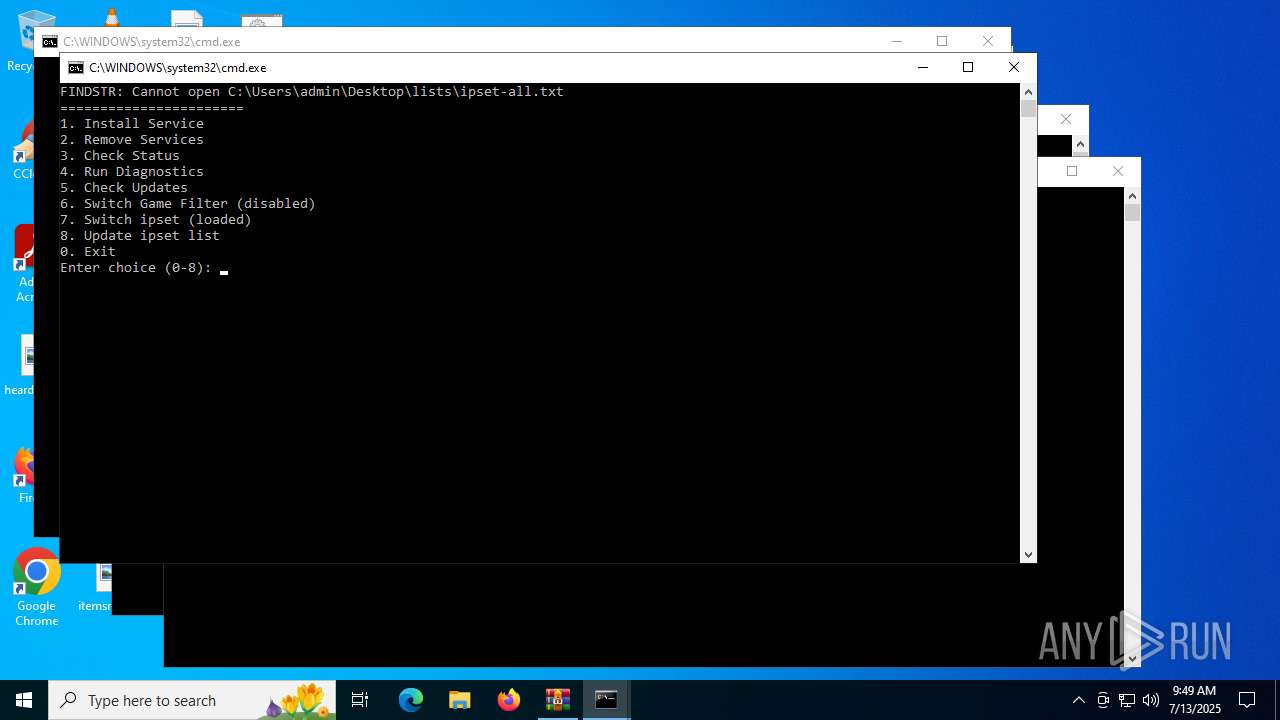
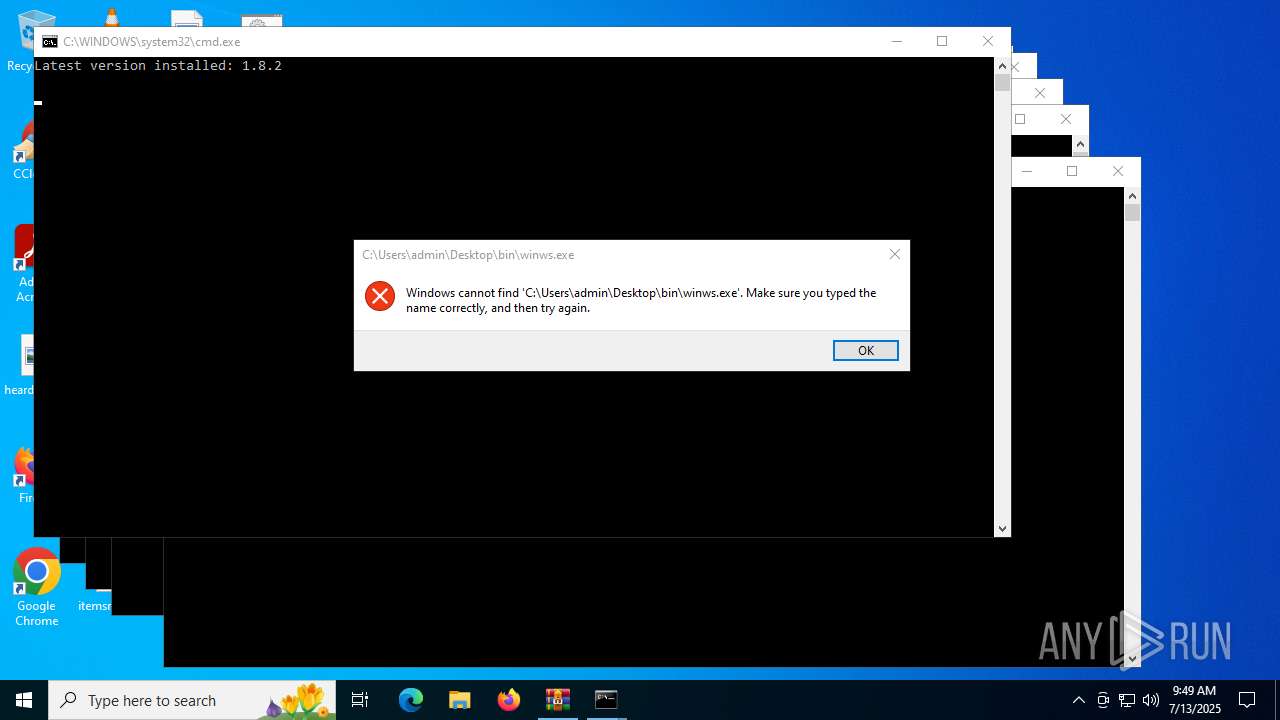
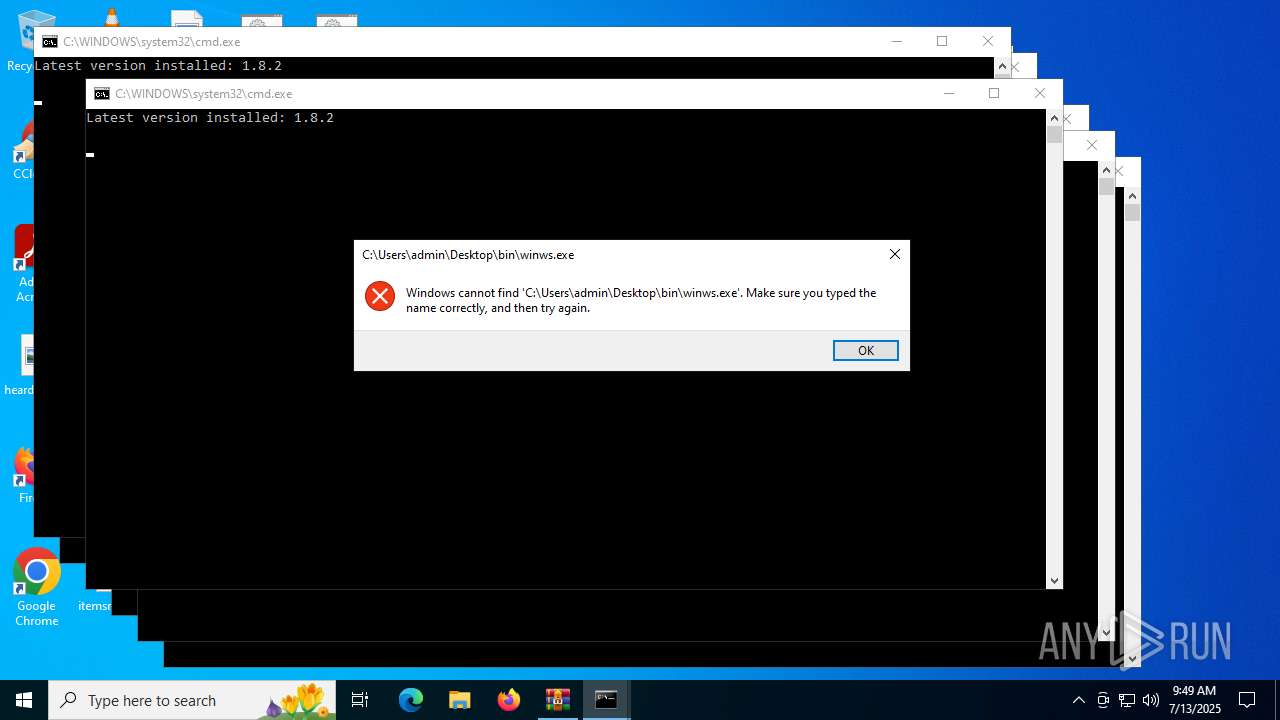
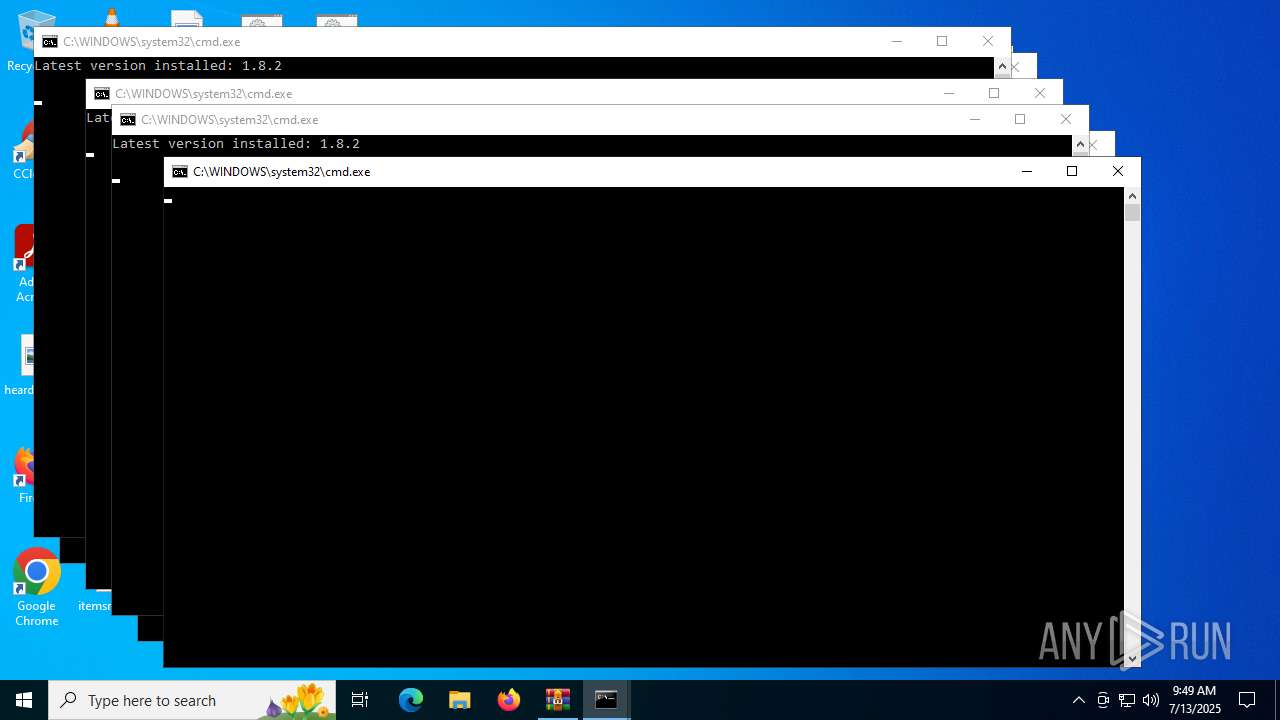
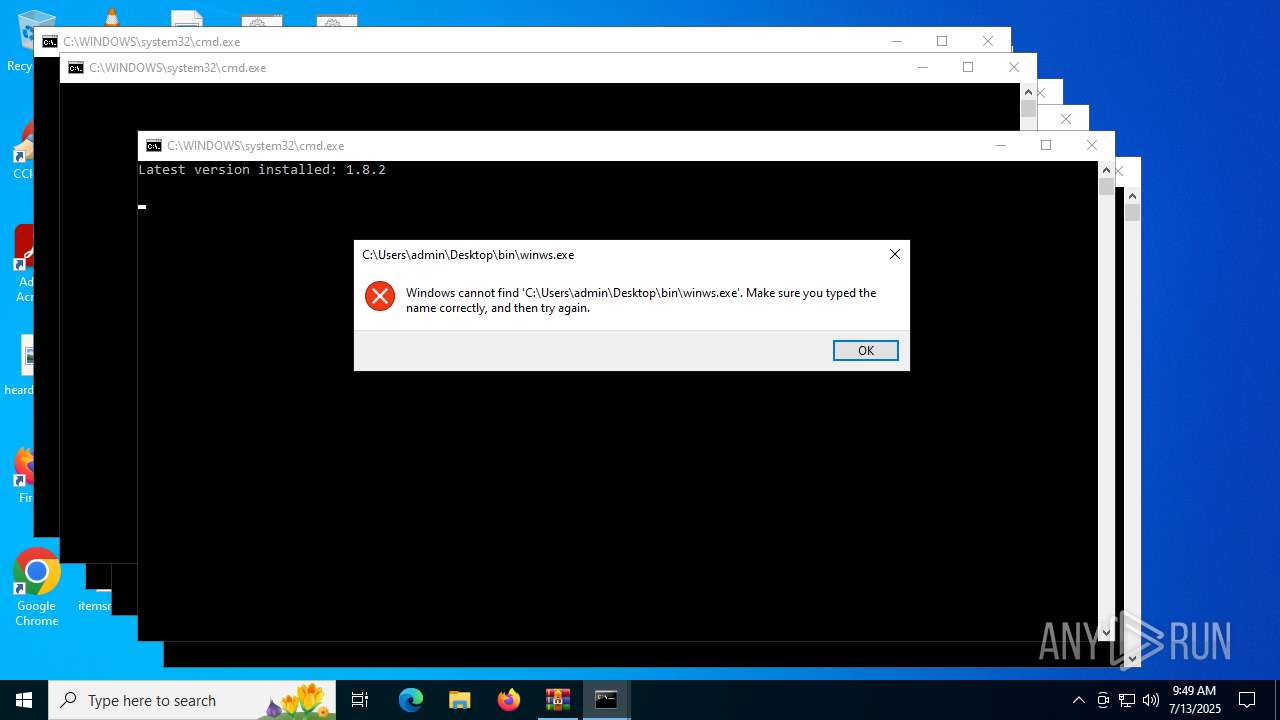
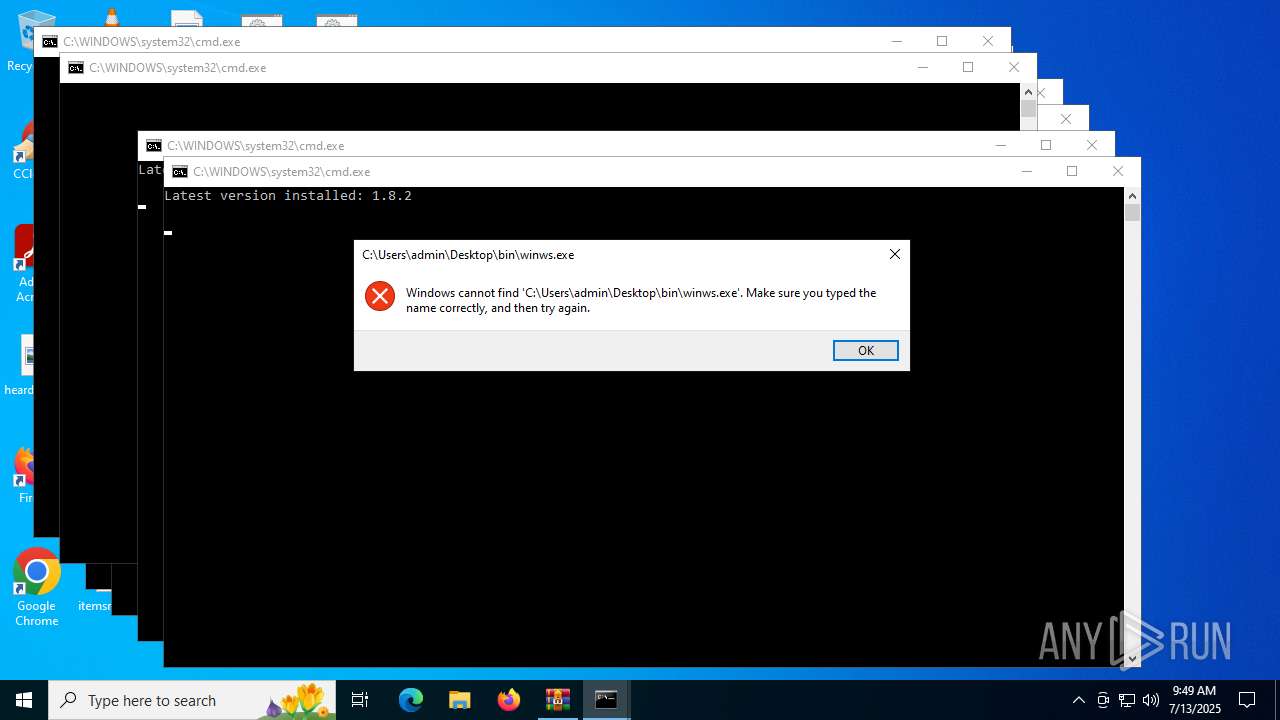
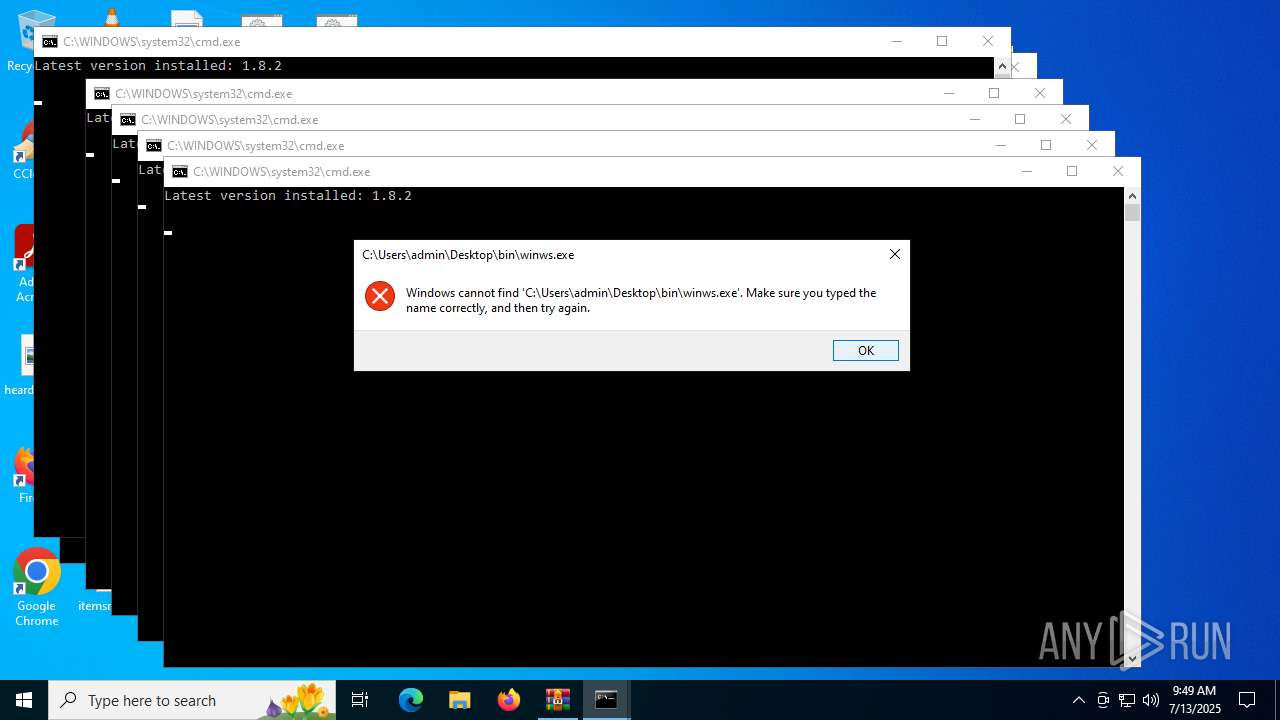
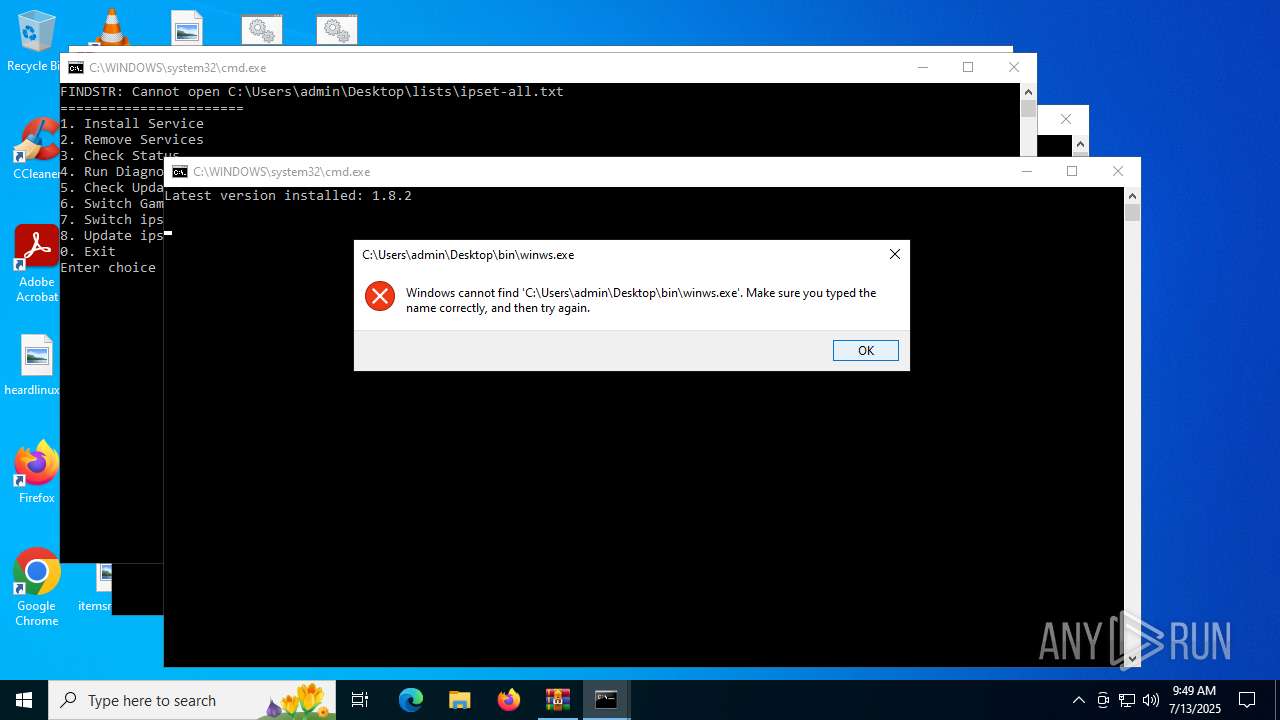
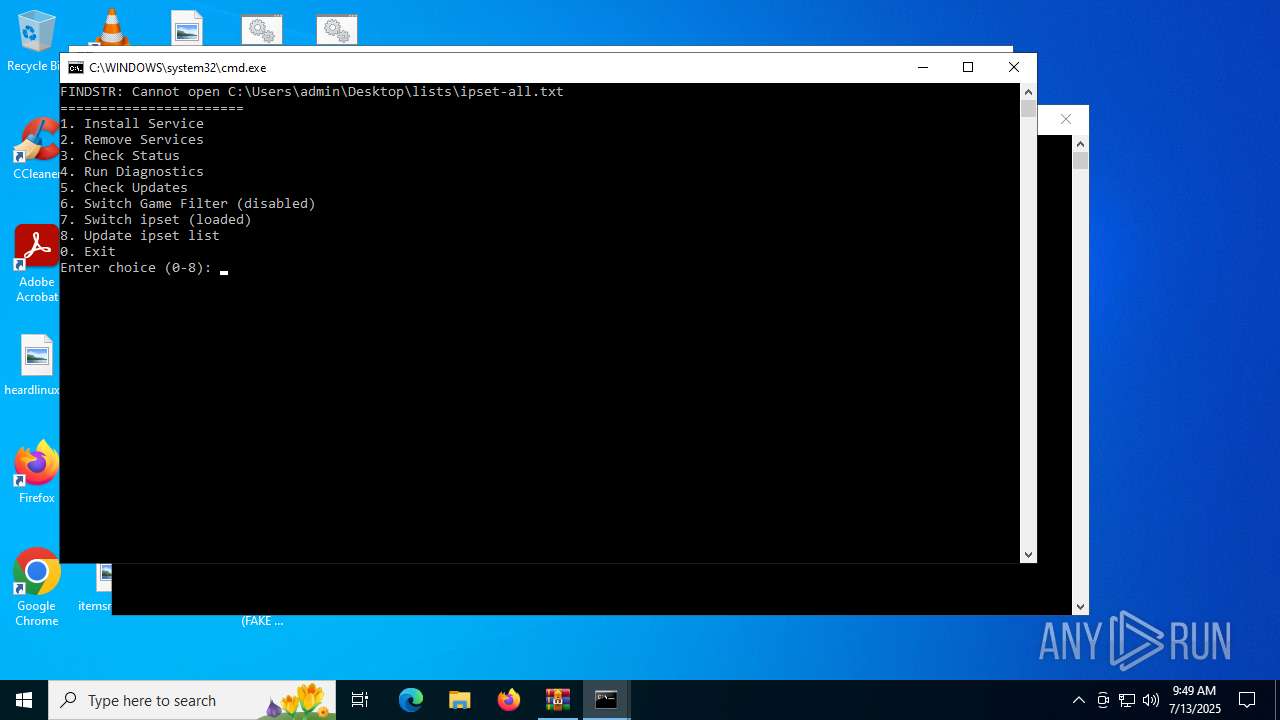
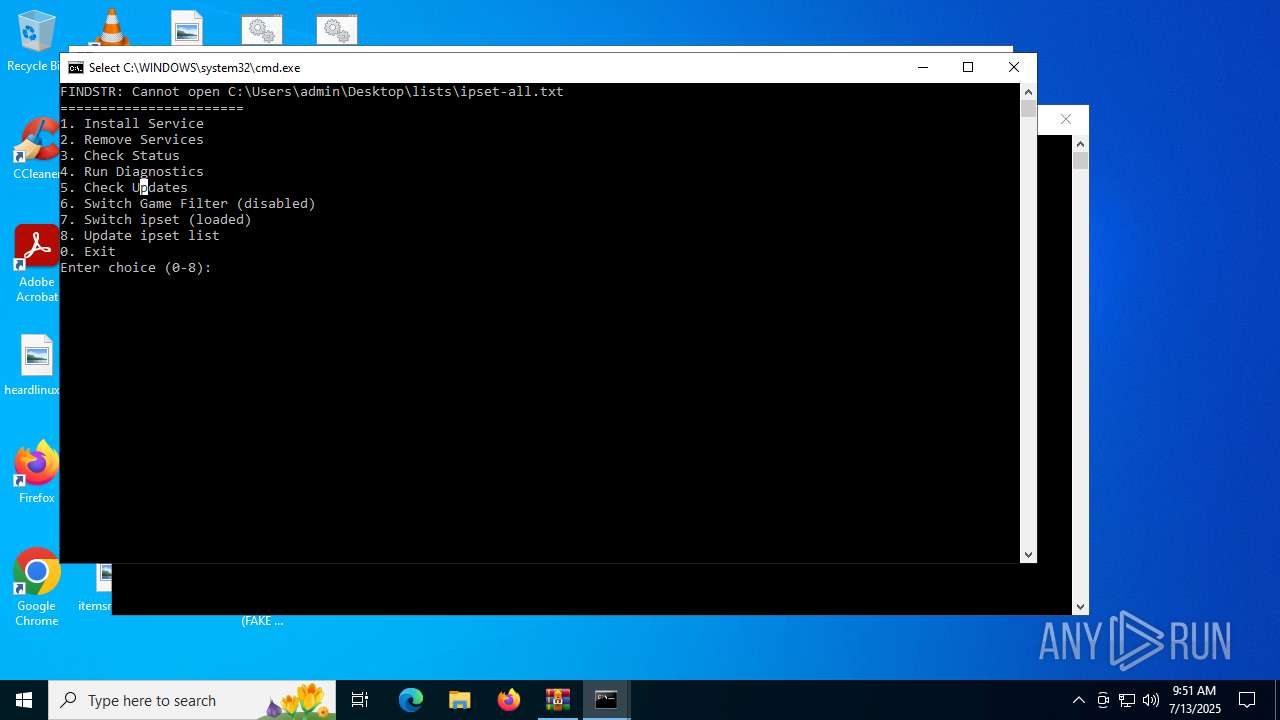
Starts application with an unusual extension
- cmd.exe (PID: 4112)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 2216)
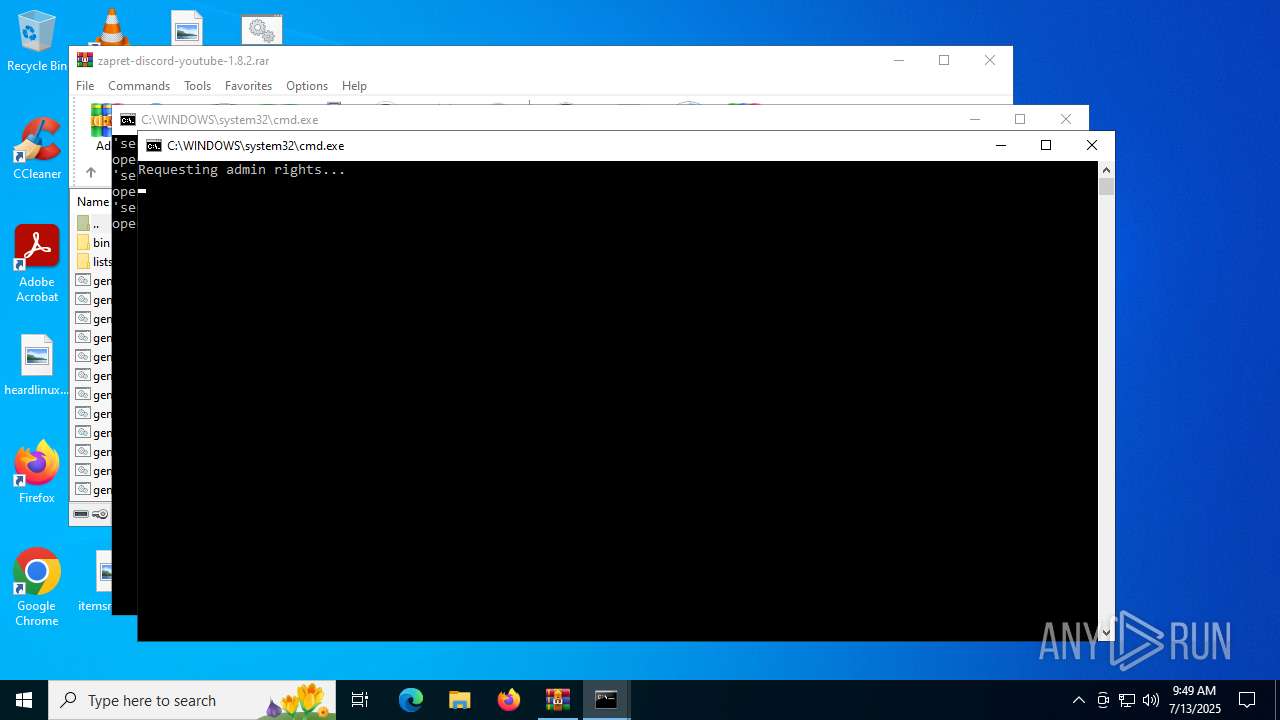
Starts process via Powershell
- powershell.exe (PID: 5352)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3000)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 5060)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 1324)
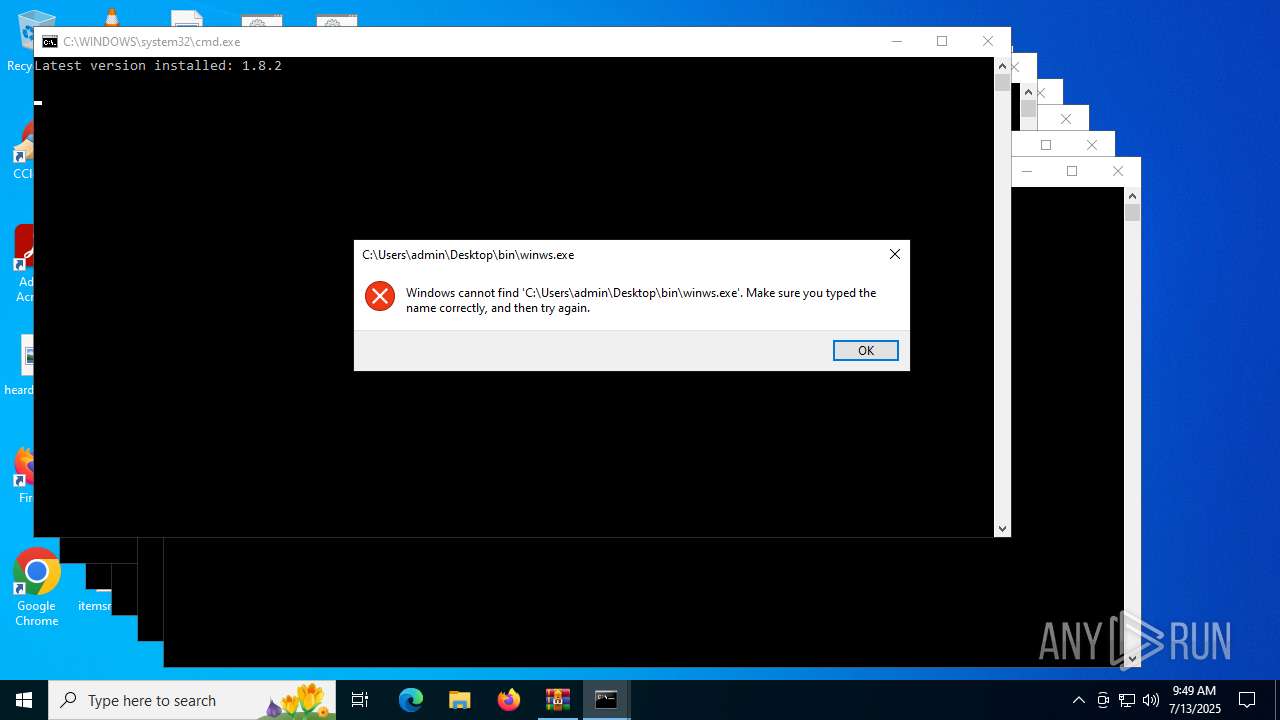
Application launched itself
- cmd.exe (PID: 1068)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 1352)
Starts SC.EXE for service management
- cmd.exe (PID: 424)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 4816)
- cmd.exe (PID: 4680)
- cmd.exe (PID: 1652)
- cmd.exe (PID: 5620)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 6384)
Hides command output
- cmd.exe (PID: 1028)
- cmd.exe (PID: 1324)
- cmd.exe (PID: 5060)
- cmd.exe (PID: 2404)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 1324)
Windows service management via SC.EXE
- sc.exe (PID: 6344)
- sc.exe (PID: 952)
- sc.exe (PID: 4748)
- sc.exe (PID: 4552)
- sc.exe (PID: 2280)
- sc.exe (PID: 4888)
- sc.exe (PID: 4132)
- sc.exe (PID: 4748)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5352)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 2216)
Executing commands from a ".bat" file
- powershell.exe (PID: 5352)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6840)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 4816)
- cmd.exe (PID: 4680)
- cmd.exe (PID: 1652)
- cmd.exe (PID: 5620)
- cmd.exe (PID: 424)
- cmd.exe (PID: 3980)
- cmd.exe (PID: 6384)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 4692)
Changes the display of characters in the console
- cmd.exe (PID: 4112)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 2216)
Manual execution by a user
- cmd.exe (PID: 4112)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 3148)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 6400)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 3000)
Checks supported languages
- chcp.com (PID: 5628)
- chcp.com (PID: 1232)
- chcp.com (PID: 5556)
- chcp.com (PID: 1632)
- chcp.com (PID: 4680)
- chcp.com (PID: 3196)
- chcp.com (PID: 4960)
- chcp.com (PID: 6412)
- chcp.com (PID: 1632)
- chcp.com (PID: 6796)
- chcp.com (PID: 5552)
- chcp.com (PID: 4816)
- chcp.com (PID: 3876)
- chcp.com (PID: 1632)
- chcp.com (PID: 5352)
- chcp.com (PID: 1232)
- chcp.com (PID: 5372)
- chcp.com (PID: 2764)
- chcp.com (PID: 2216)
- chcp.com (PID: 424)
- chcp.com (PID: 1232)
- chcp.com (PID: 6268)
- chcp.com (PID: 1740)
- chcp.com (PID: 1508)
- chcp.com (PID: 1192)
- chcp.com (PID: 6828)
- chcp.com (PID: 5556)
Disables trace logs
- powershell.exe (PID: 7092)
- powershell.exe (PID: 4520)
- powershell.exe (PID: 5116)
- powershell.exe (PID: 2348)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 3876)
- powershell.exe (PID: 6380)
- powershell.exe (PID: 3888)
Checks proxy server information
- powershell.exe (PID: 7092)
- powershell.exe (PID: 4520)
- powershell.exe (PID: 5116)
- powershell.exe (PID: 2348)
- powershell.exe (PID: 6512)
- powershell.exe (PID: 3876)
- powershell.exe (PID: 6380)
- slui.exe (PID: 4132)
- powershell.exe (PID: 3888)
Reads the software policy settings
- slui.exe (PID: 4132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 503 |
| UncompressedSize: | 1655 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | general (ALT3).bat |
Total processes
227
Monitored processes
93
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | findstr /R "^0\.0\.0\.0/32f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "C:\Users\admin\Desktop\lists\ipset-all.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | findstr /i "STATE" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | C:\WINDOWS\system32\cmd.exe /c sc query "zapret" | findstr /i "STATE" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 952 | sc query "zapret" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
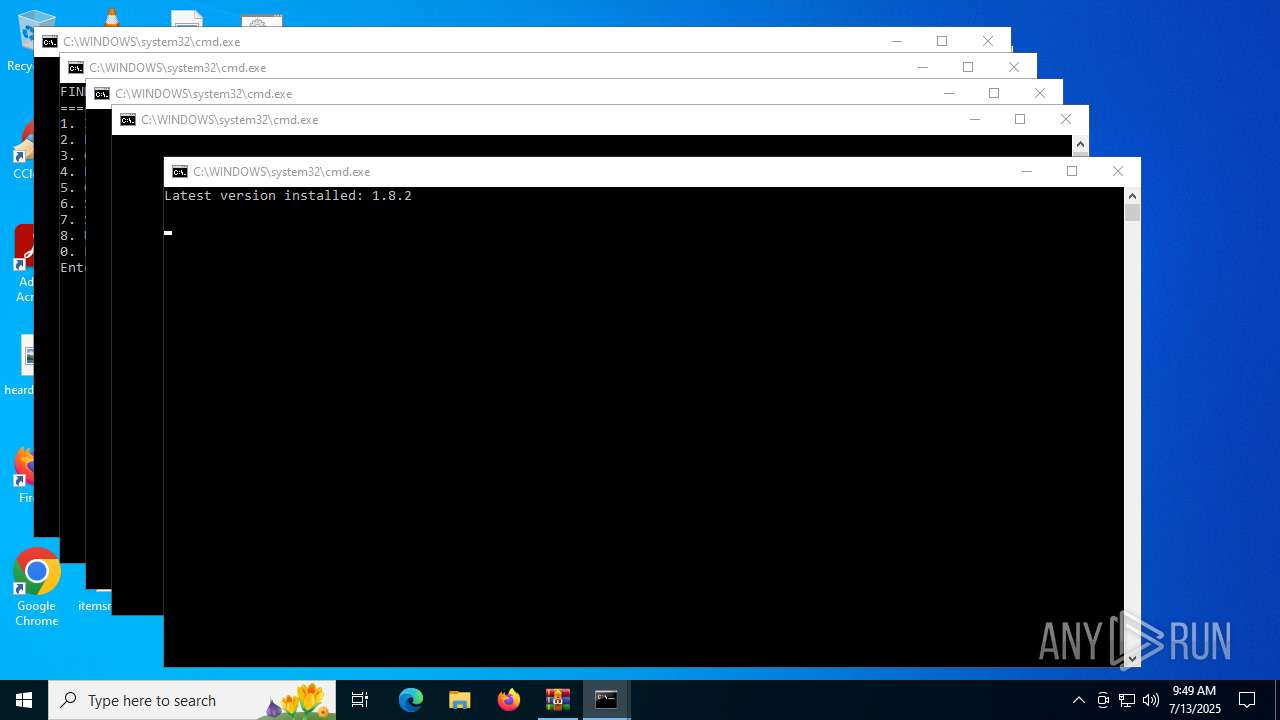
| 1028 | C:\WINDOWS\system32\cmd.exe /c powershell -command "(Invoke-WebRequest -Uri \"https://raw.githubusercontent.com/Flowseal/zapret-discord-youtube/main/.service/version.txt\" -Headers @{\"Cache-Control\"=\"no-cache\"} -TimeoutSec 5).Content.Trim()" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\general (ALT3).bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
51 512
Read events
51 501
Write events
11
Delete events
0
Modification events
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\zapret-discord-youtube-1.8.2.rar | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
1
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6512 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ktelmqxr.oqf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5116 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rju1lfas.sgp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5352 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mpoehfc5.heq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5352 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_utdg2qng.qua.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3888 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ik1hddxd.qsm.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6380 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cldogm4a.auo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_n4f1wn5l.o3m.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4520 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_riu0rknj.e43.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7092 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mx2gfmue.iym.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4520 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ctvugpov.gyb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
49
DNS requests
20
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7004 | RUXIMICS.exe | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.202.163.200:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
3788 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/Flowseal/zapret-discord-youtube/main/.service/version.txt | unknown | text | 5 b | whitelisted |
3788 | SIHClient.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/Flowseal/zapret-discord-youtube/main/.service/version.txt | unknown | text | 5 b | whitelisted |
— | — | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
— | — | POST | 200 | 40.126.31.3:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7004 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7004 | RUXIMICS.exe | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |