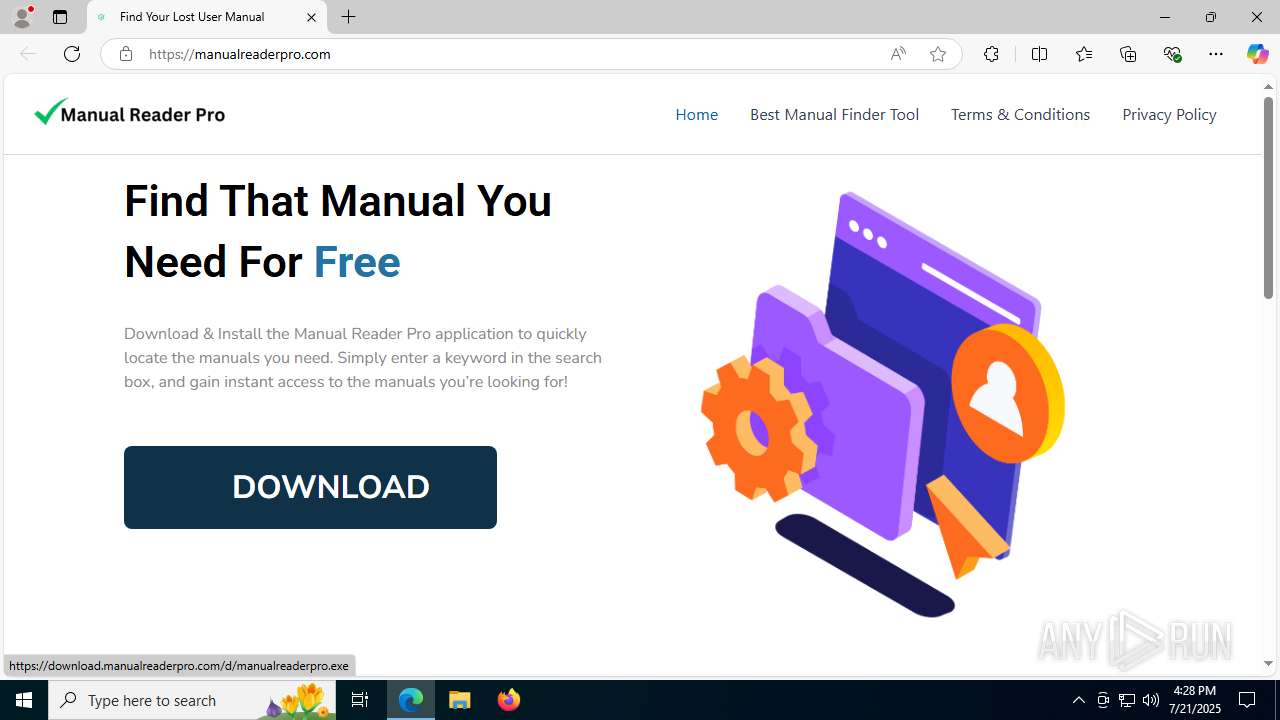
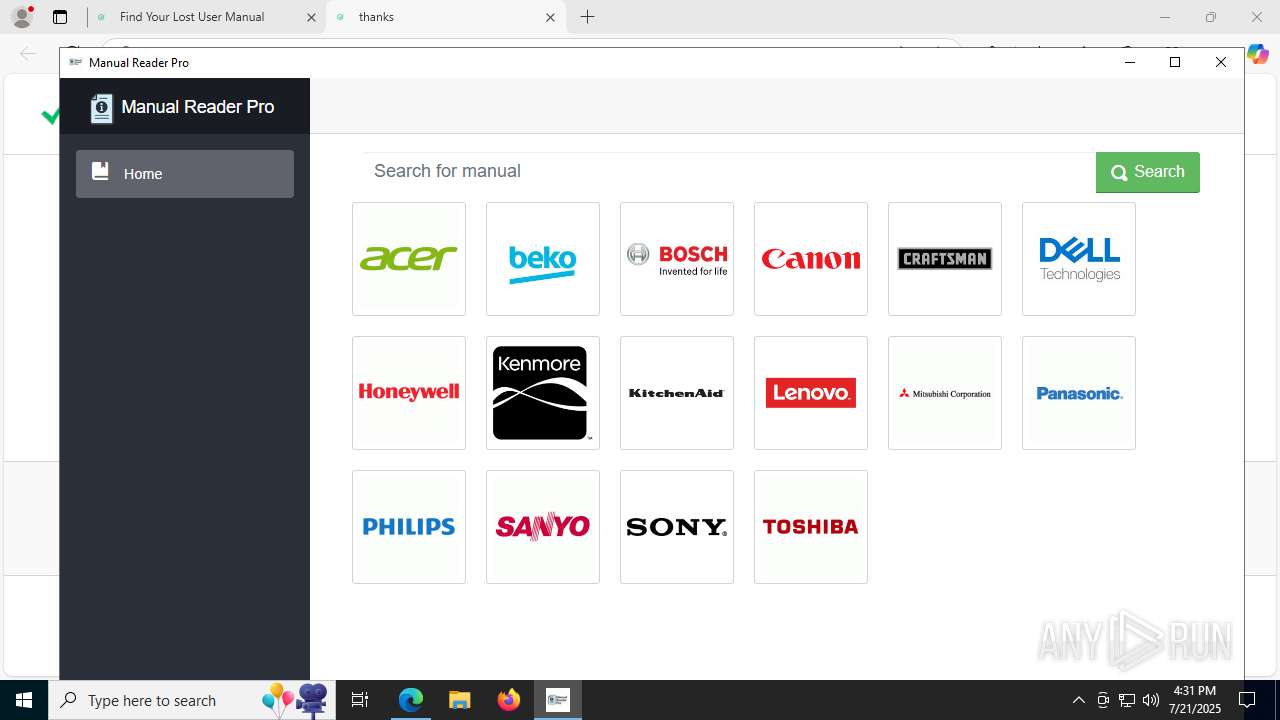
| URL: | manualreaderpro.com |
| Full analysis: | https://app.any.run/tasks/e7e02880-c2ff-4d20-9444-7d4f7ebd3ccd |
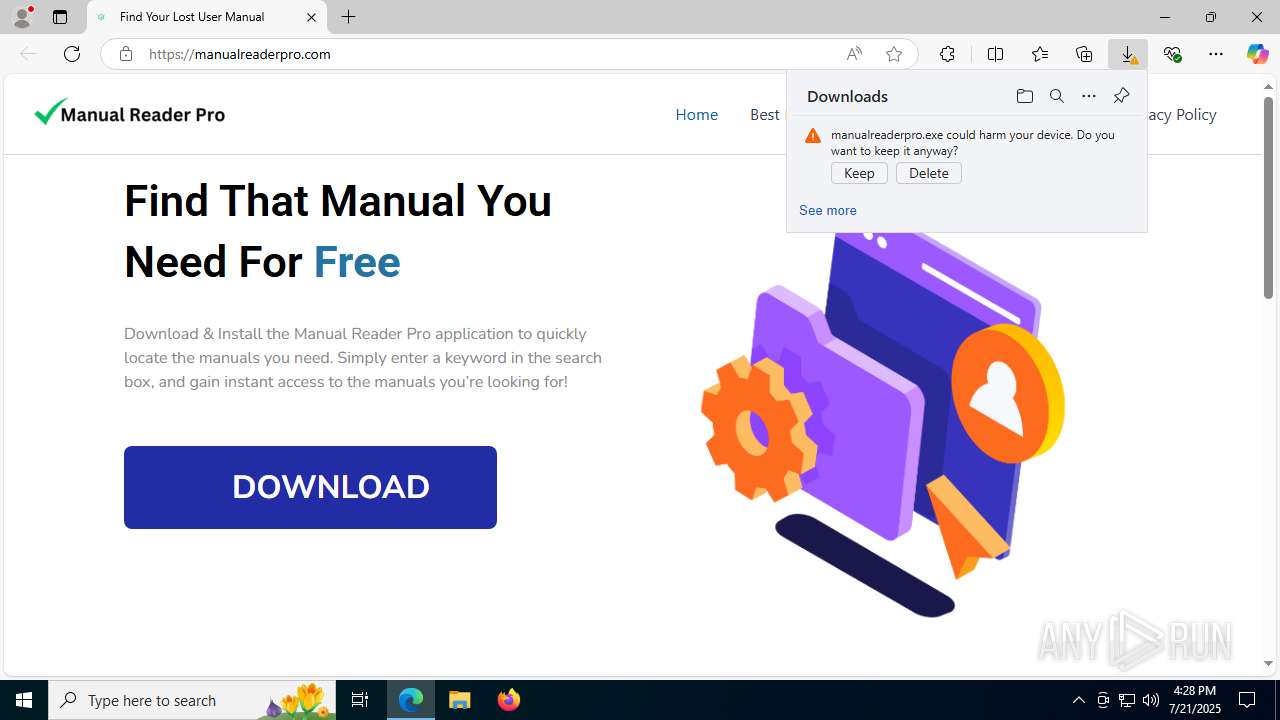
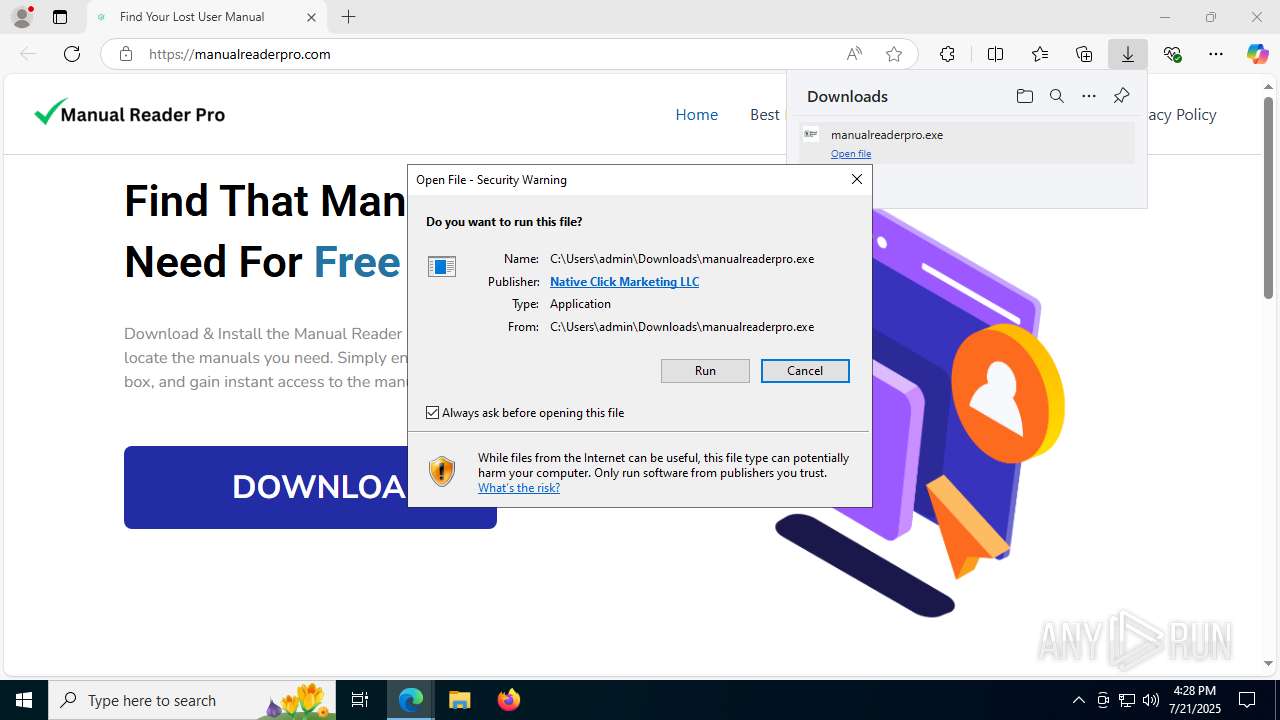
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2025, 16:28:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D3EA1712C0E04CAEC97E627688119D47 |
| SHA1: | 88A3434FAD7985D4B691224433E87F9BA93F5068 |
| SHA256: | 244B661E6DEB0DA56C999F97F47AE692BD3E06EBD47CBA3ED514BE34DCA3D49A |
| SSDEEP: | 3:5sE52:T52 |
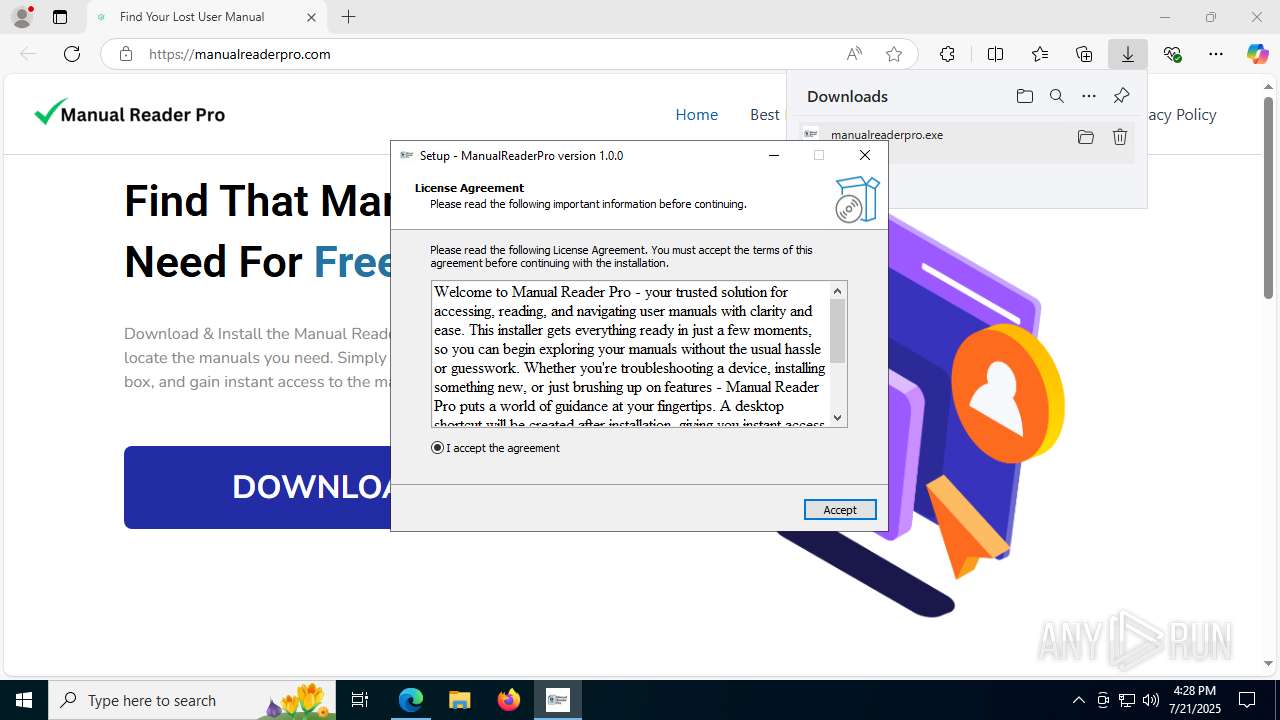
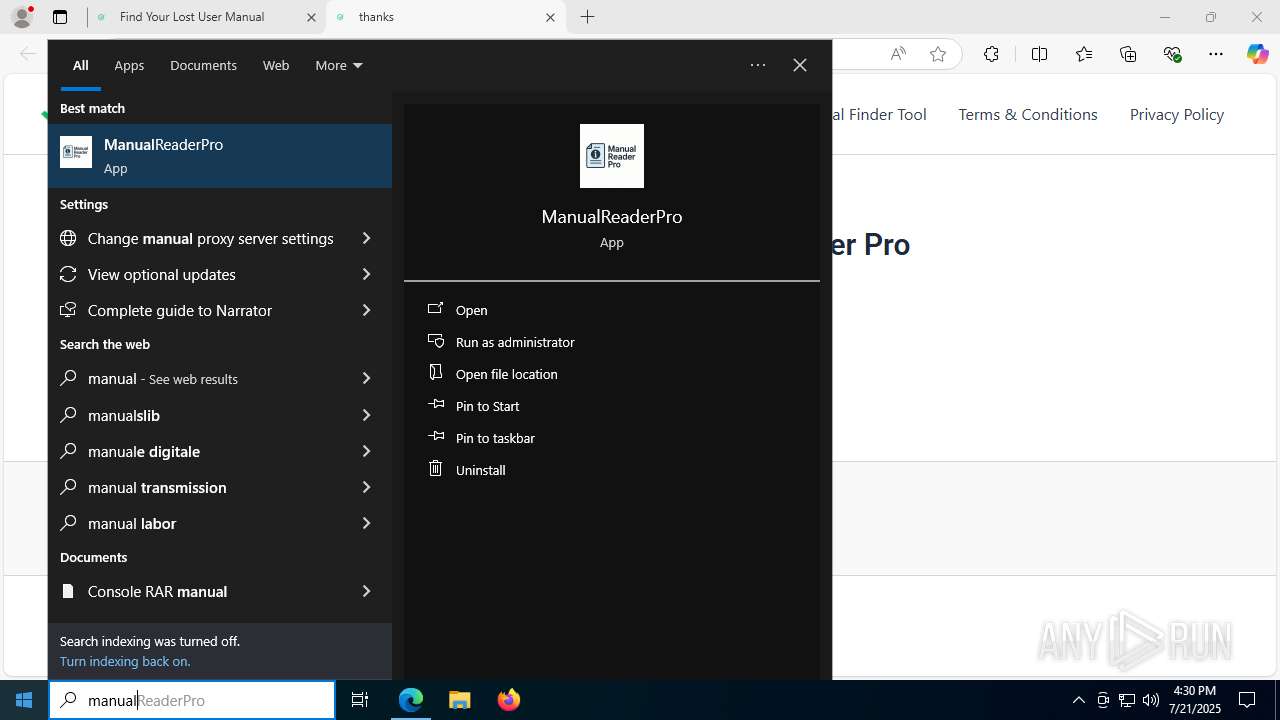
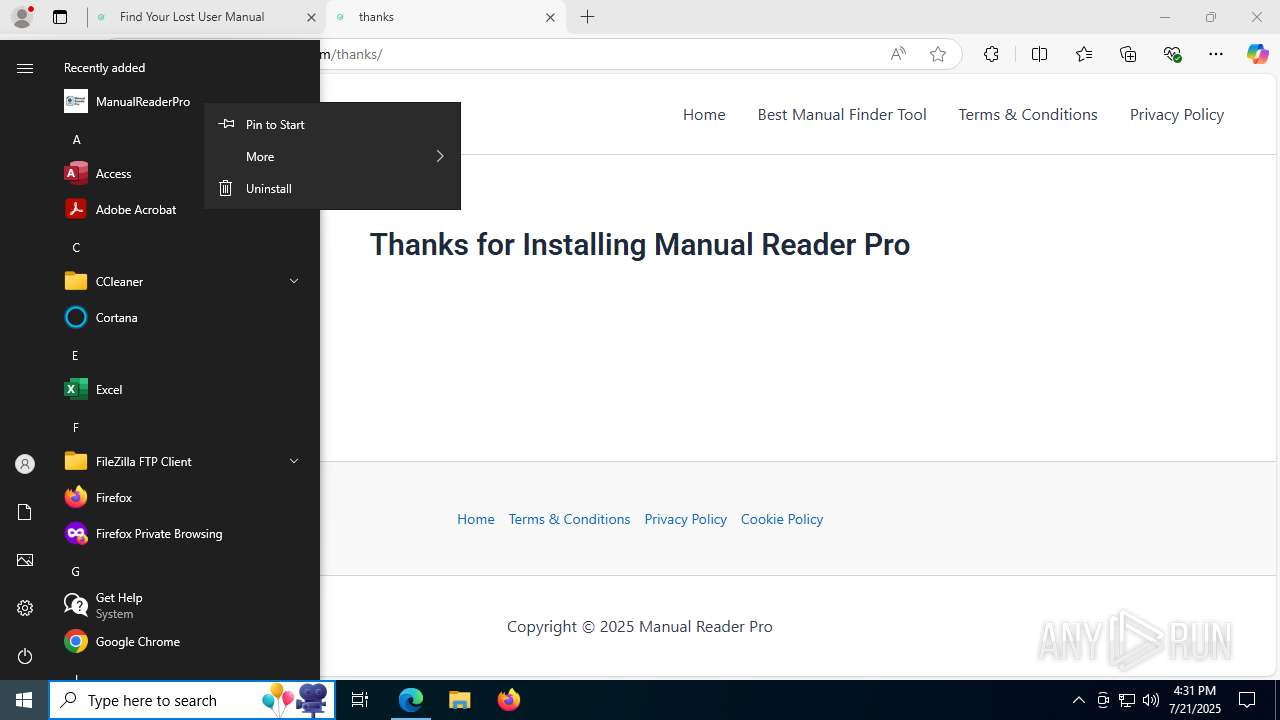
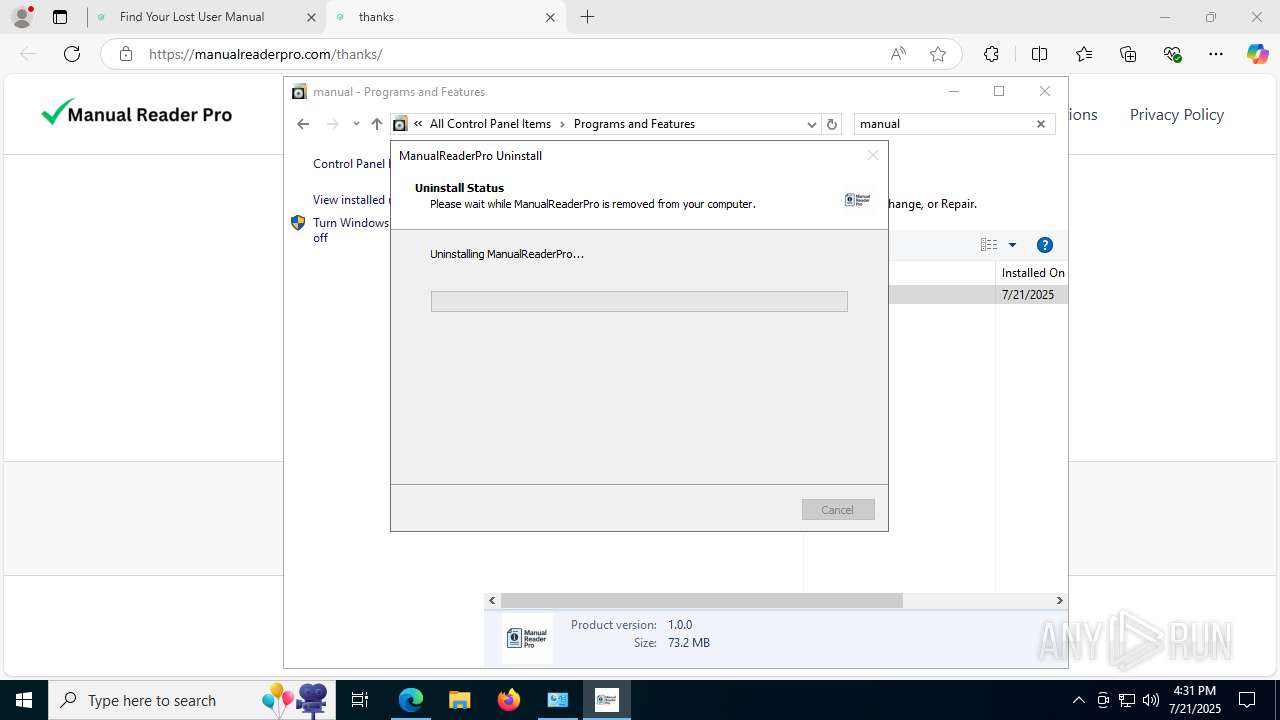
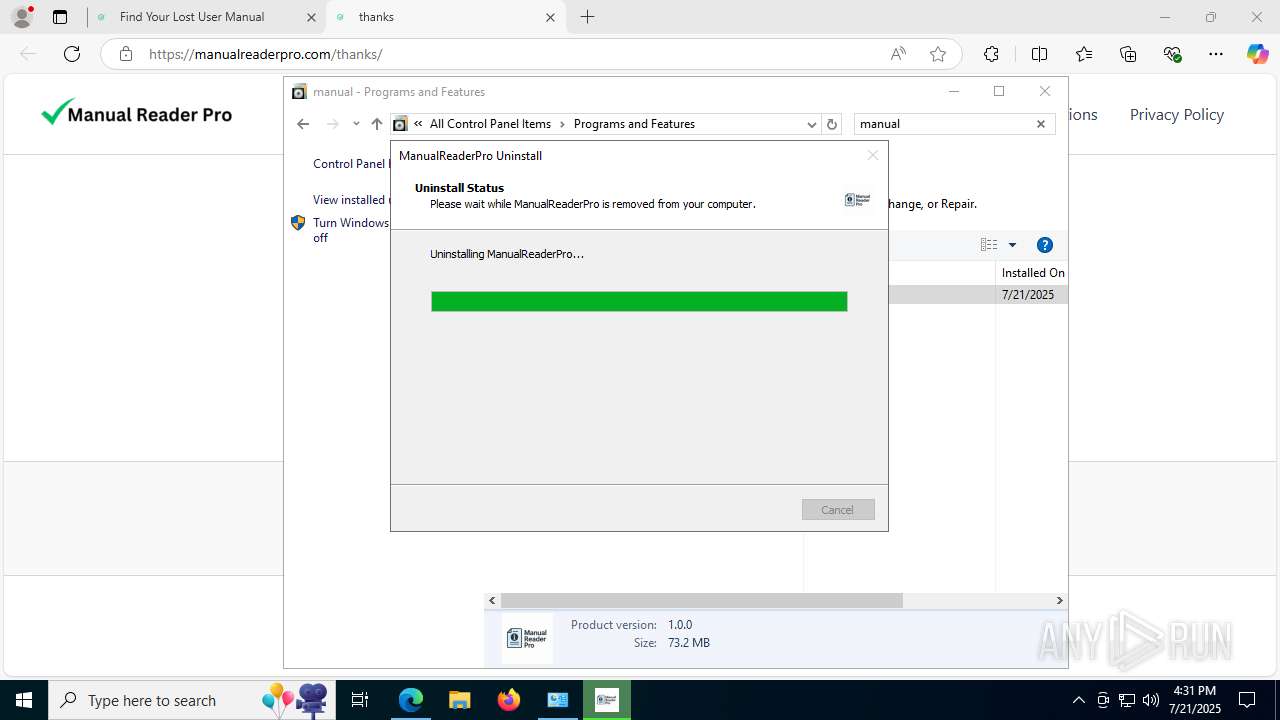
MALICIOUS
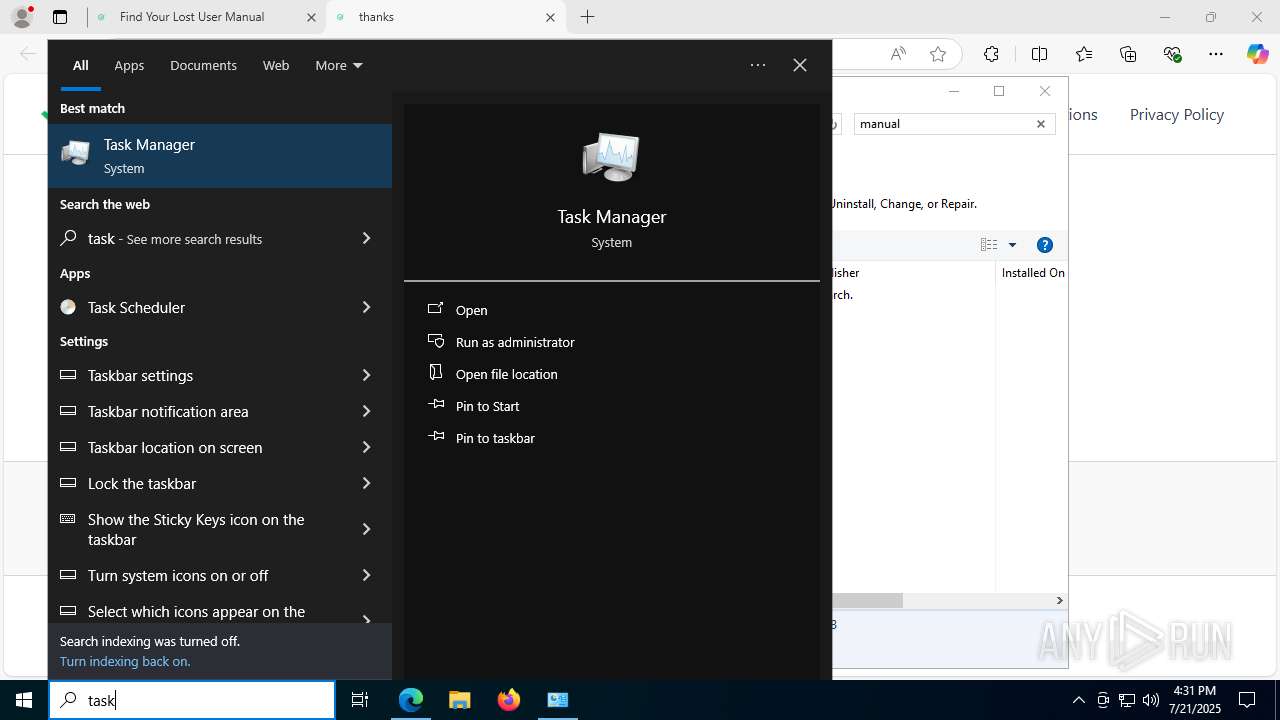
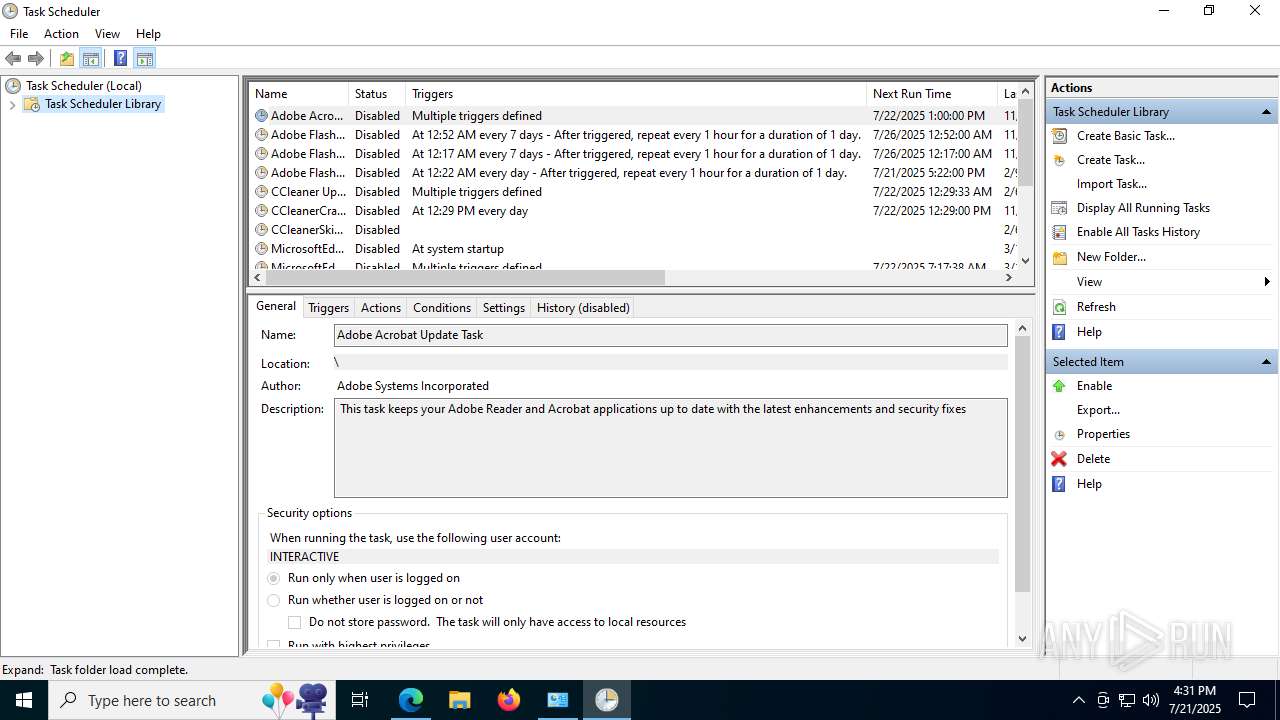
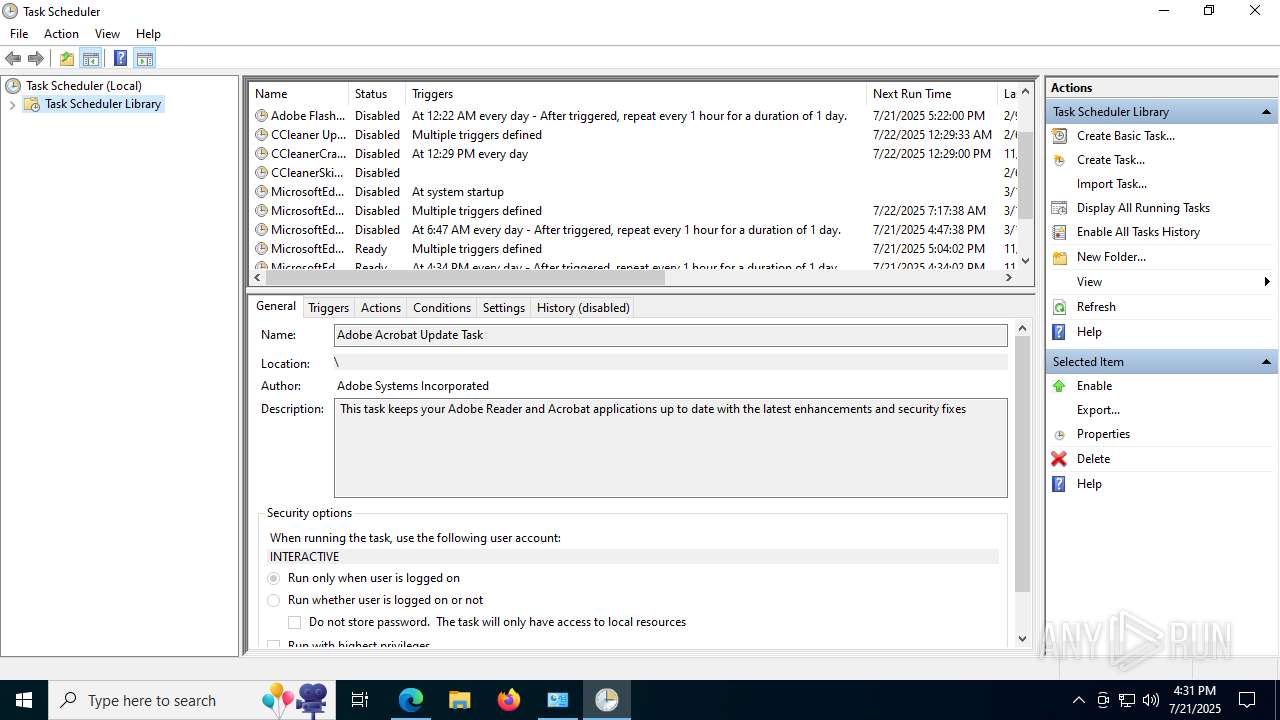
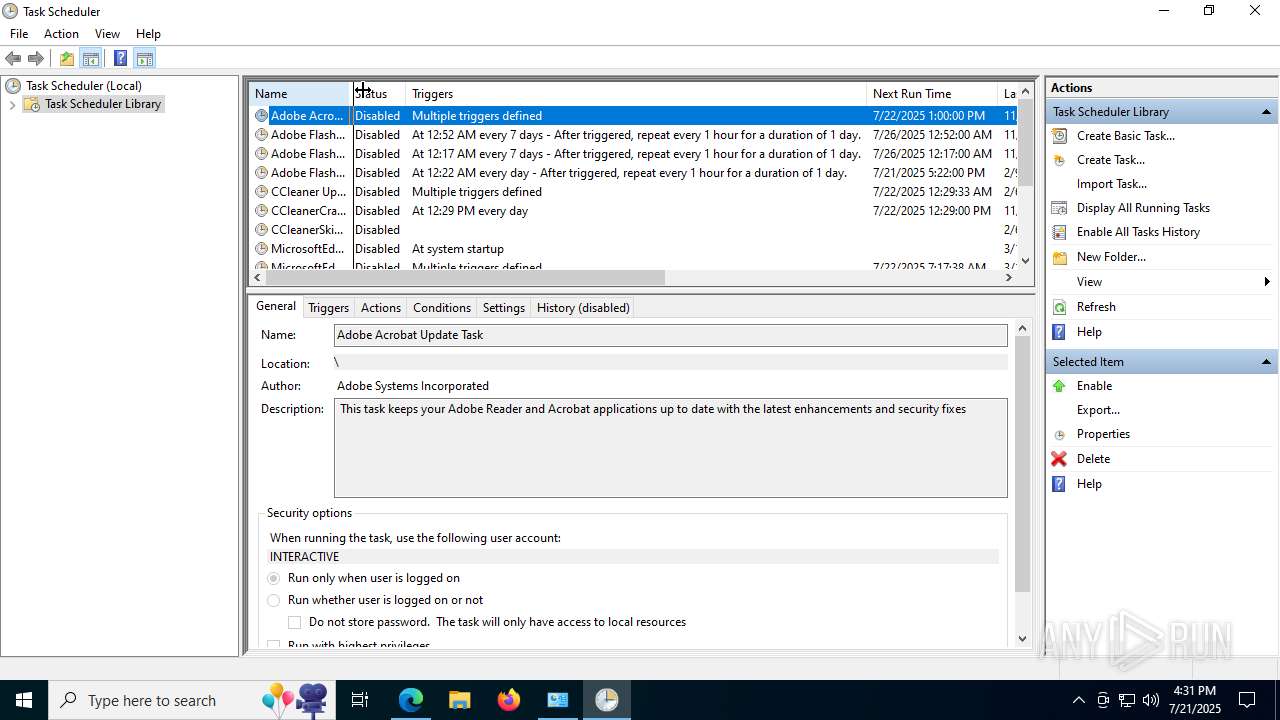
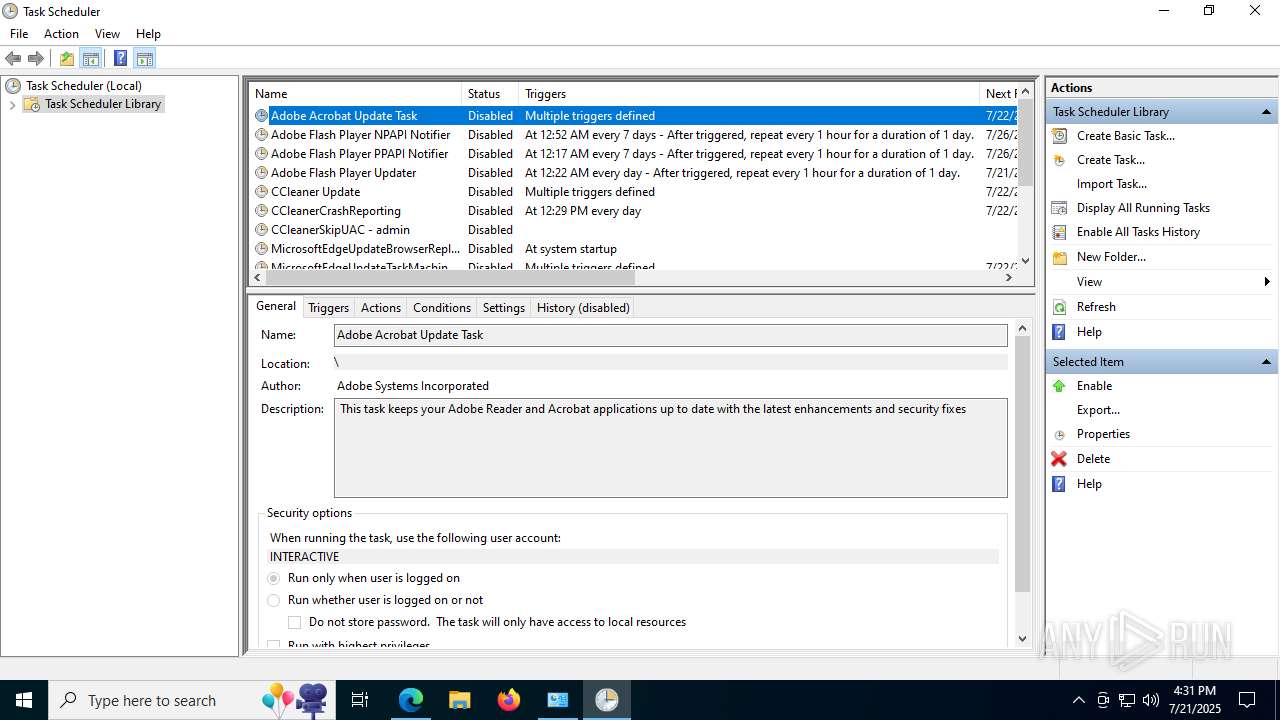
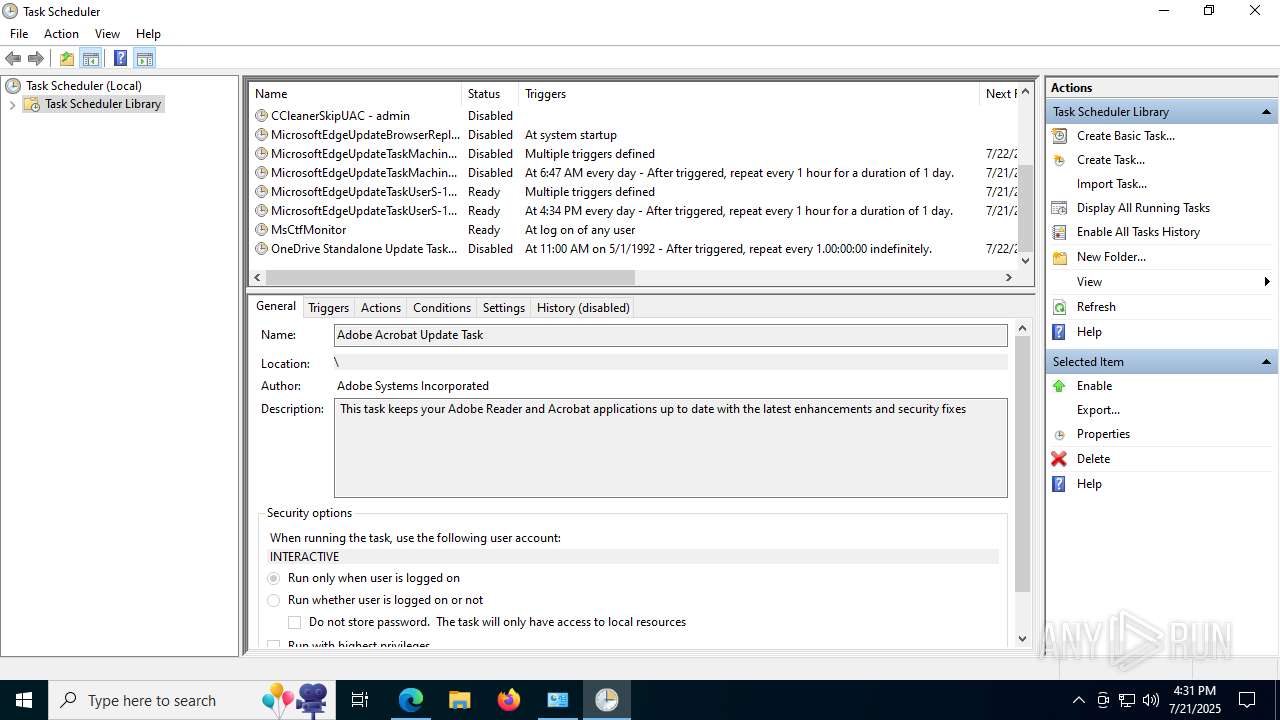
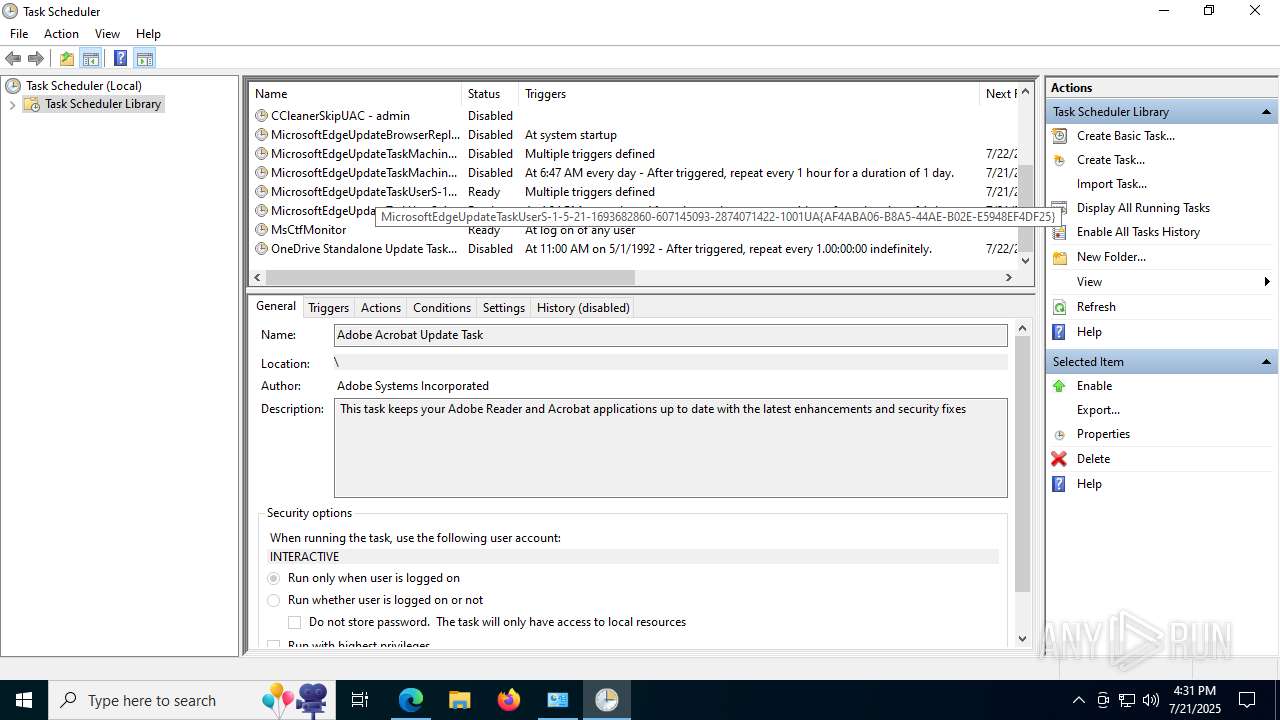
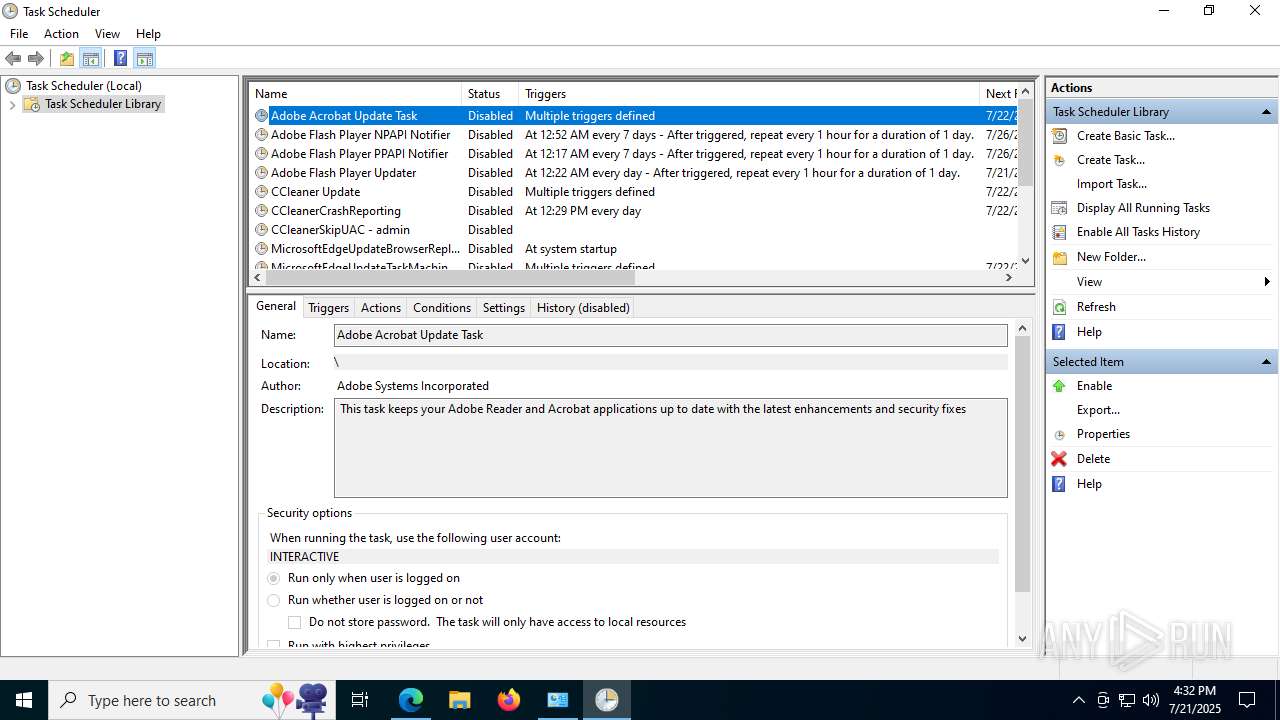
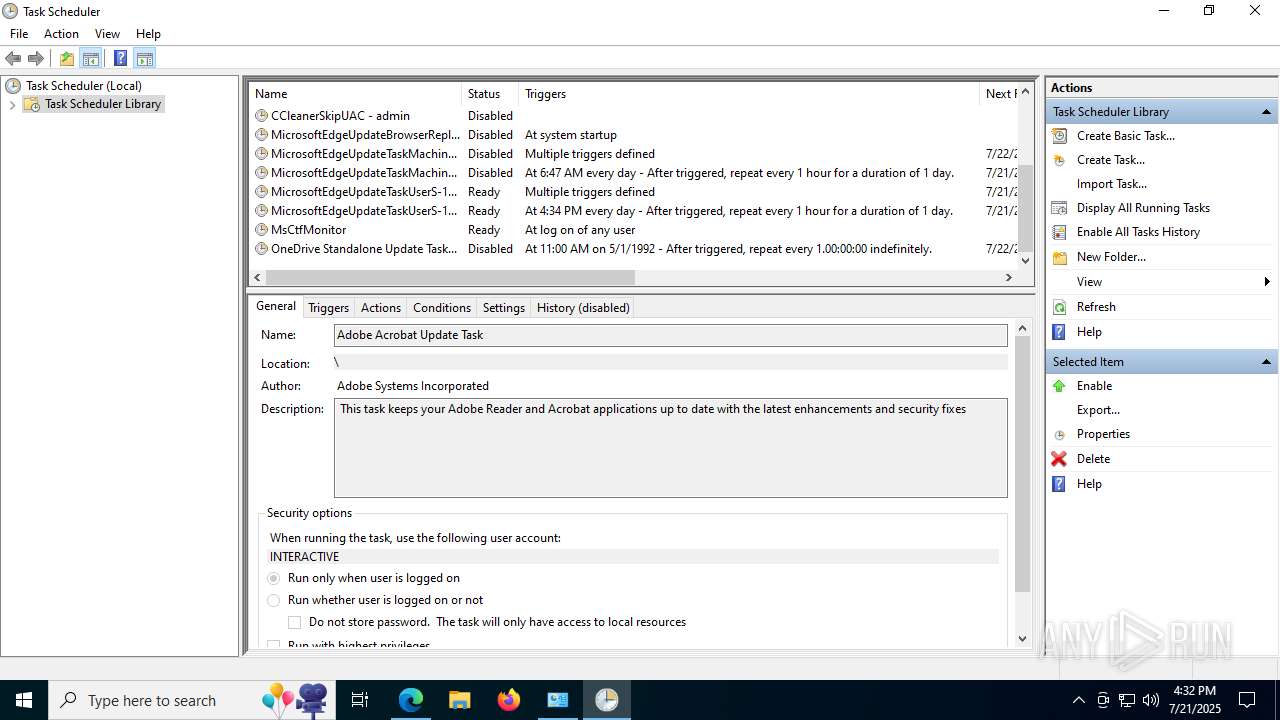
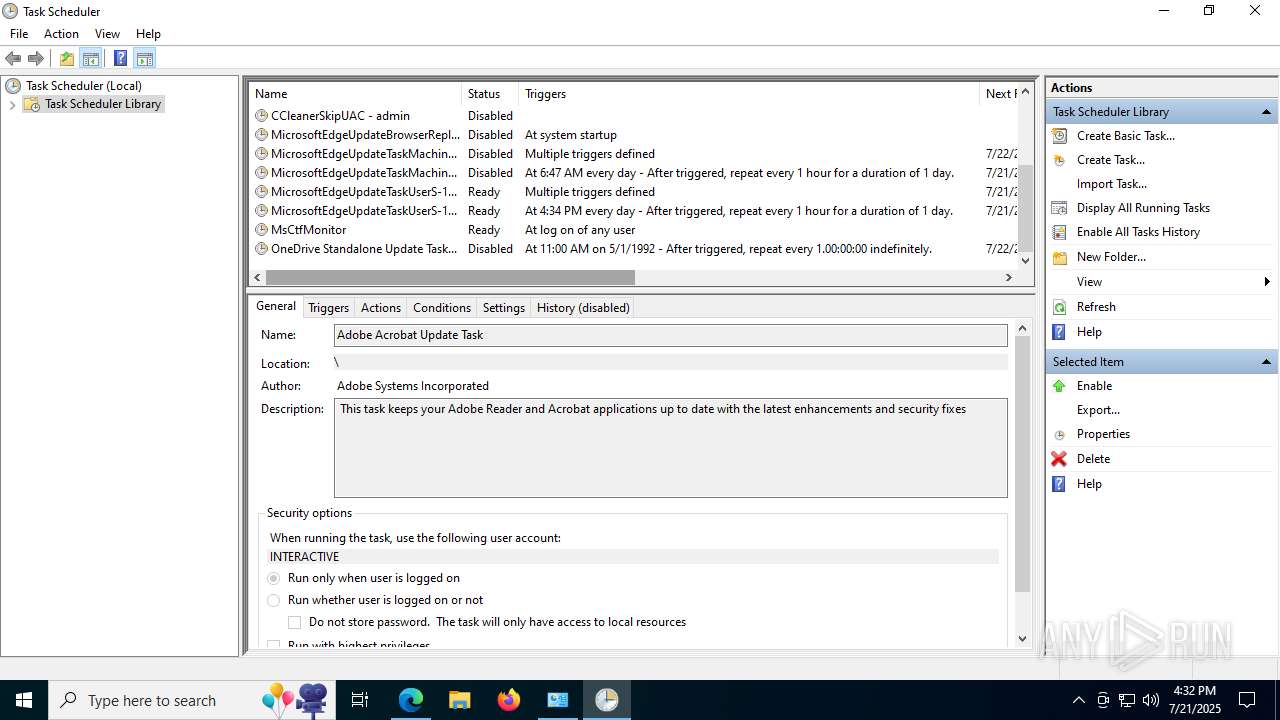
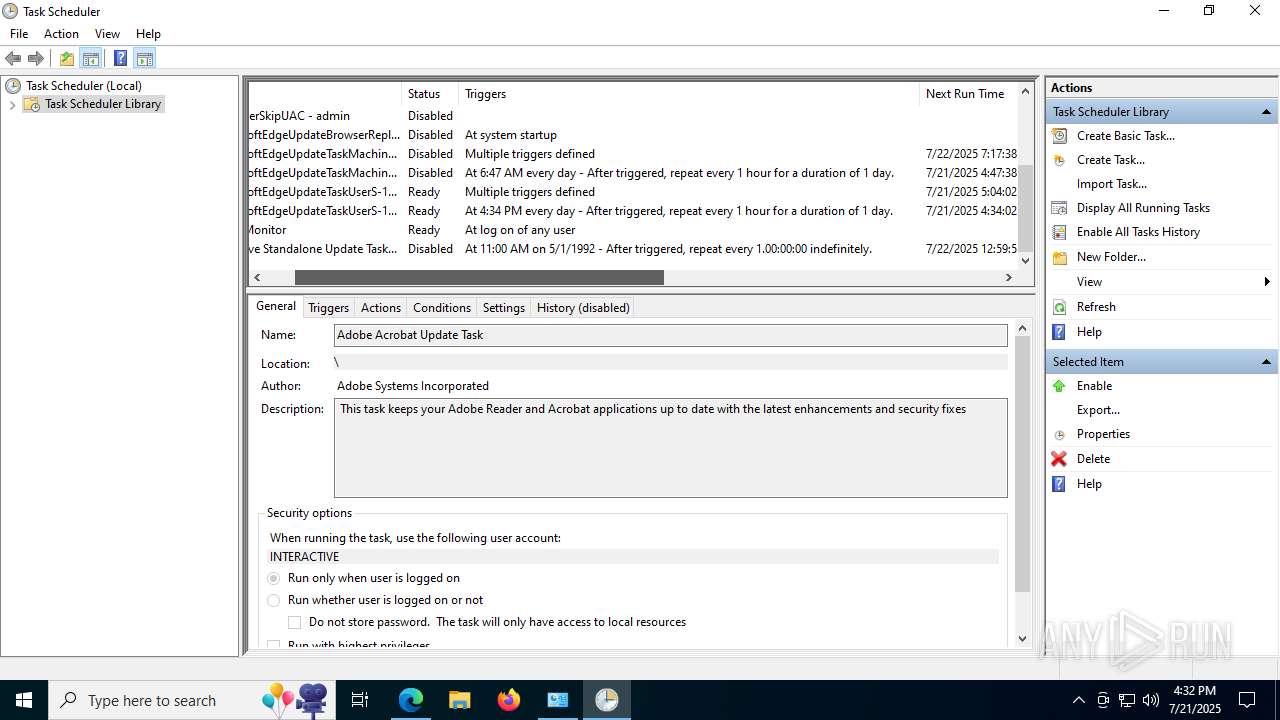
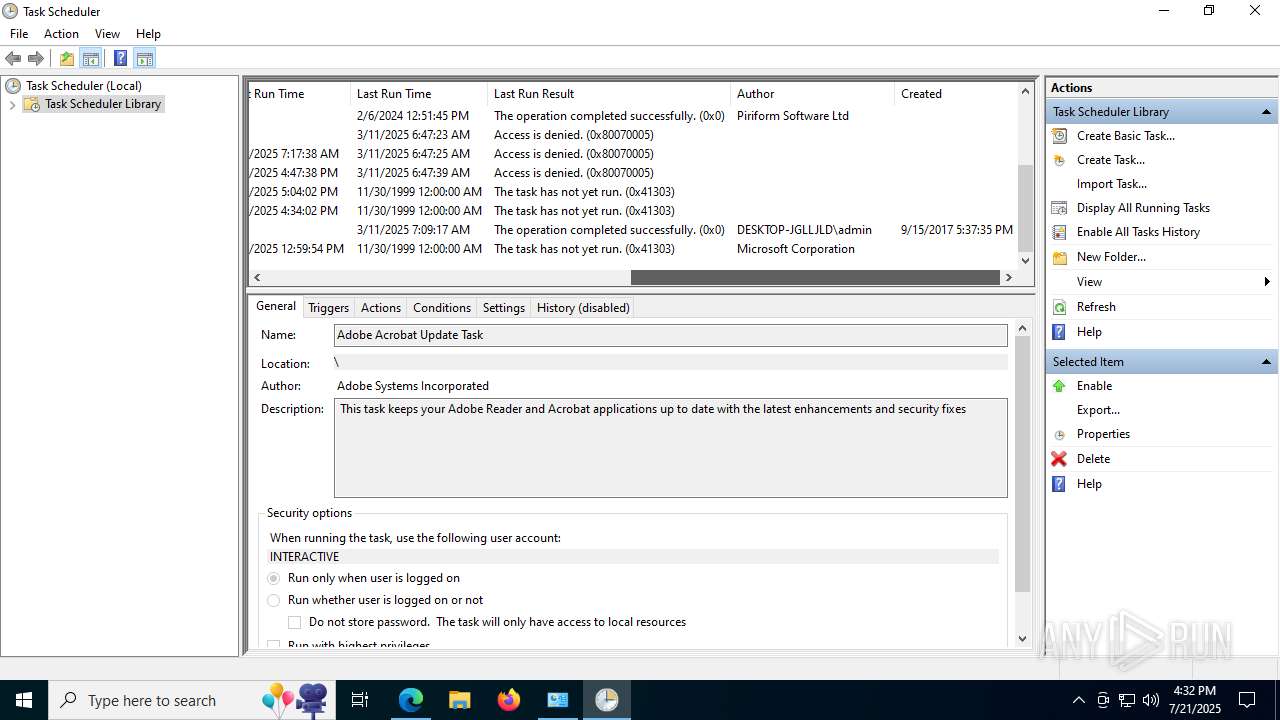
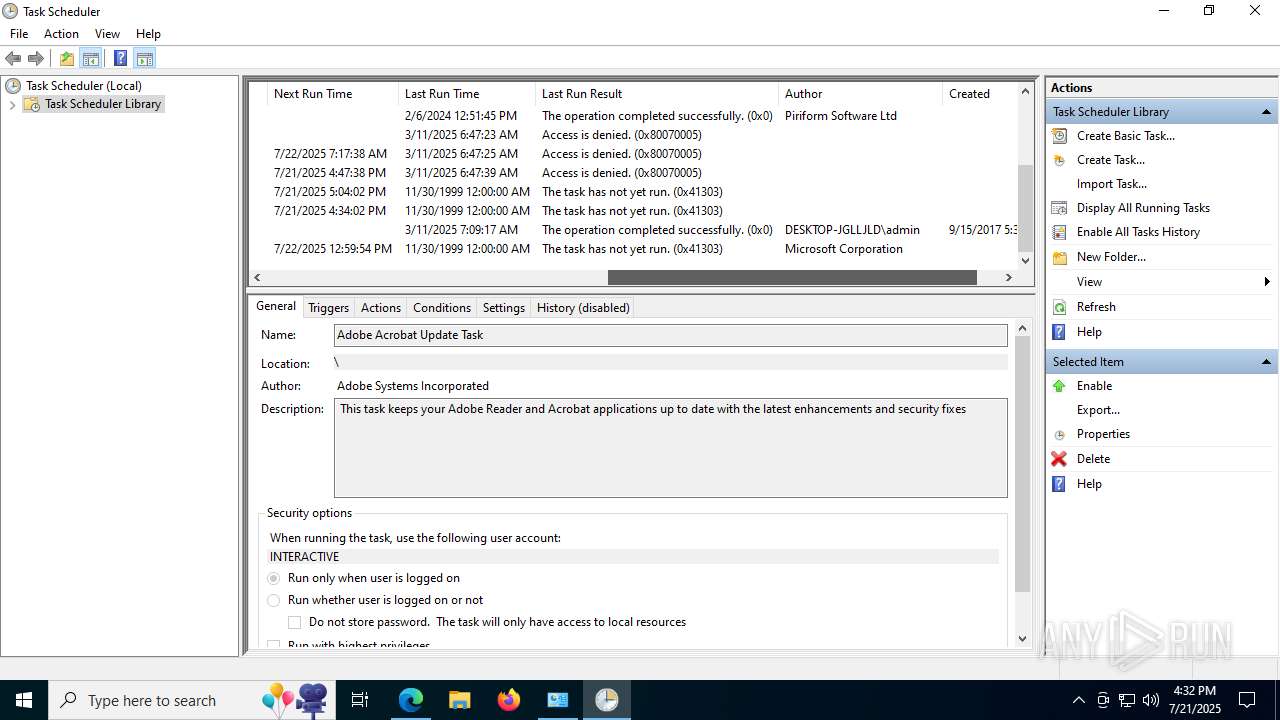
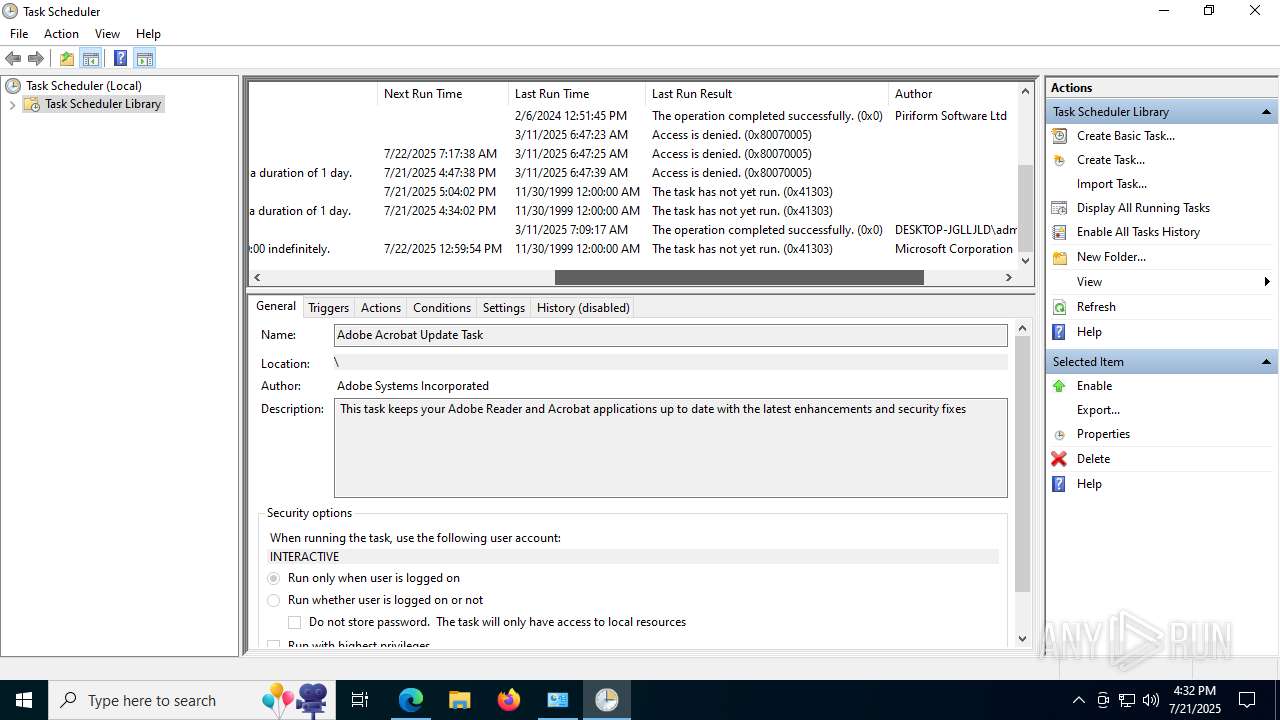
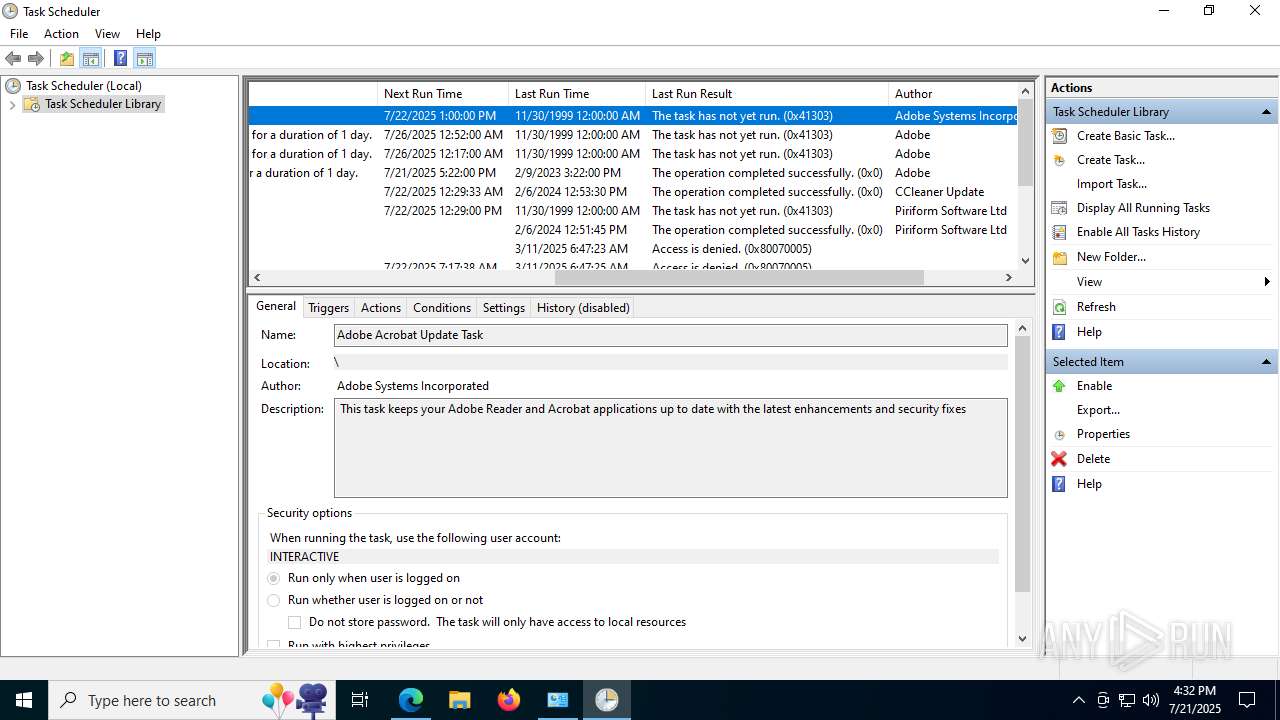
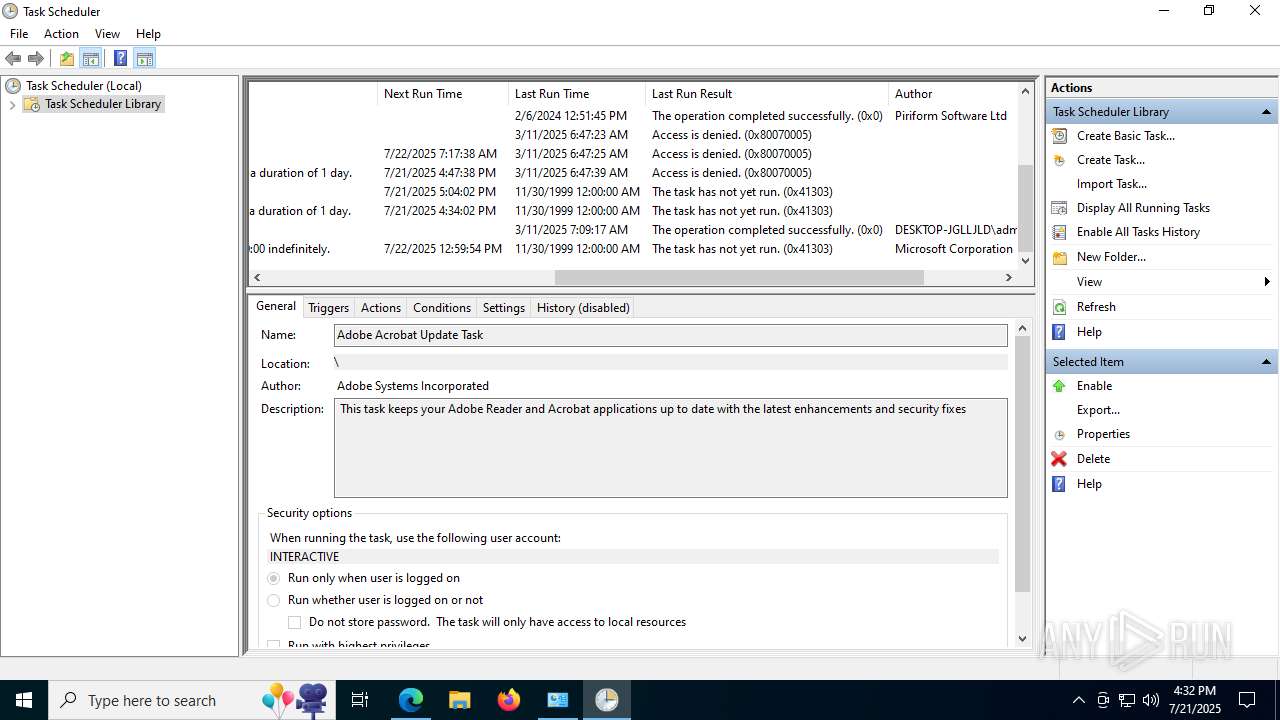
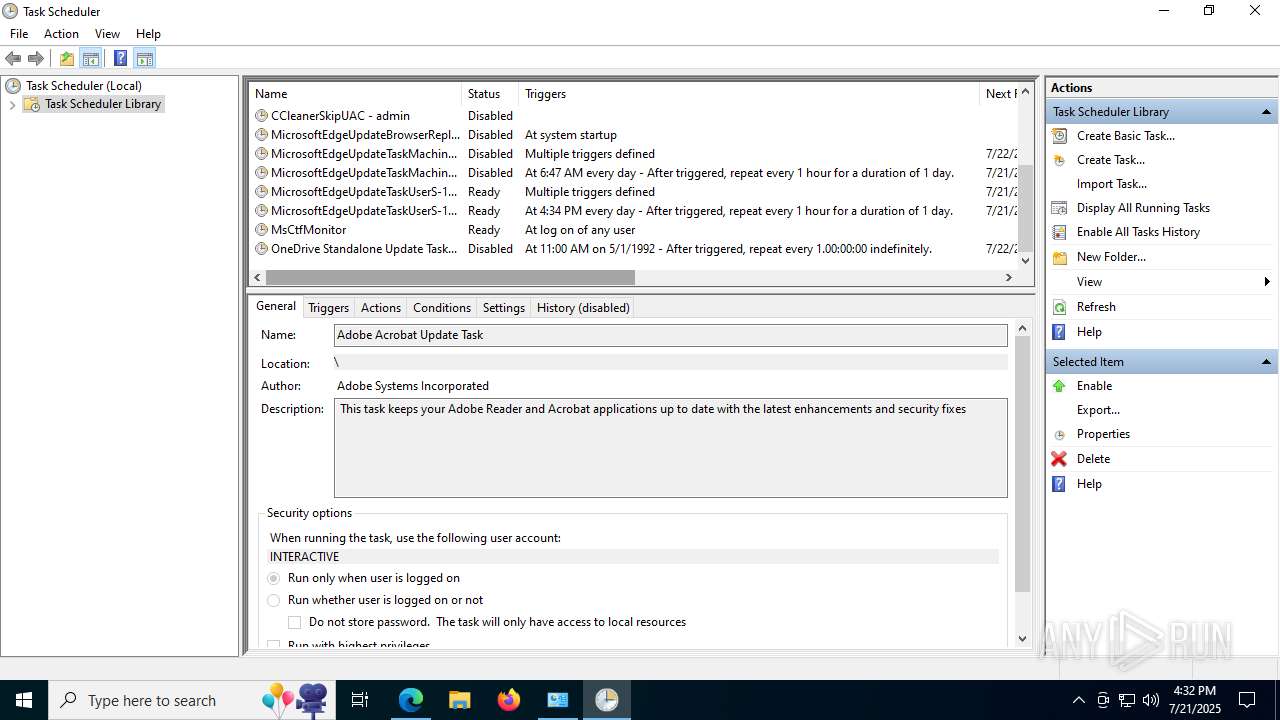
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7104)
YERO has been detected
- ManualReaderPro.exe (PID: 4788)
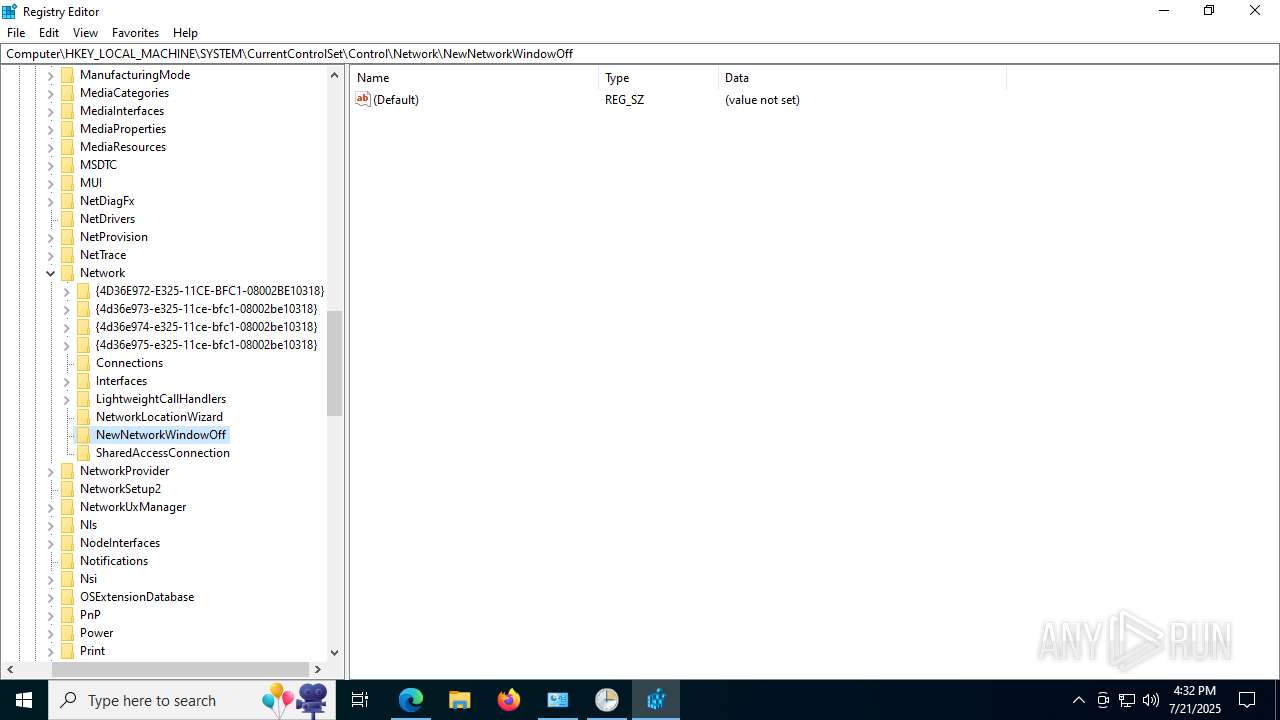
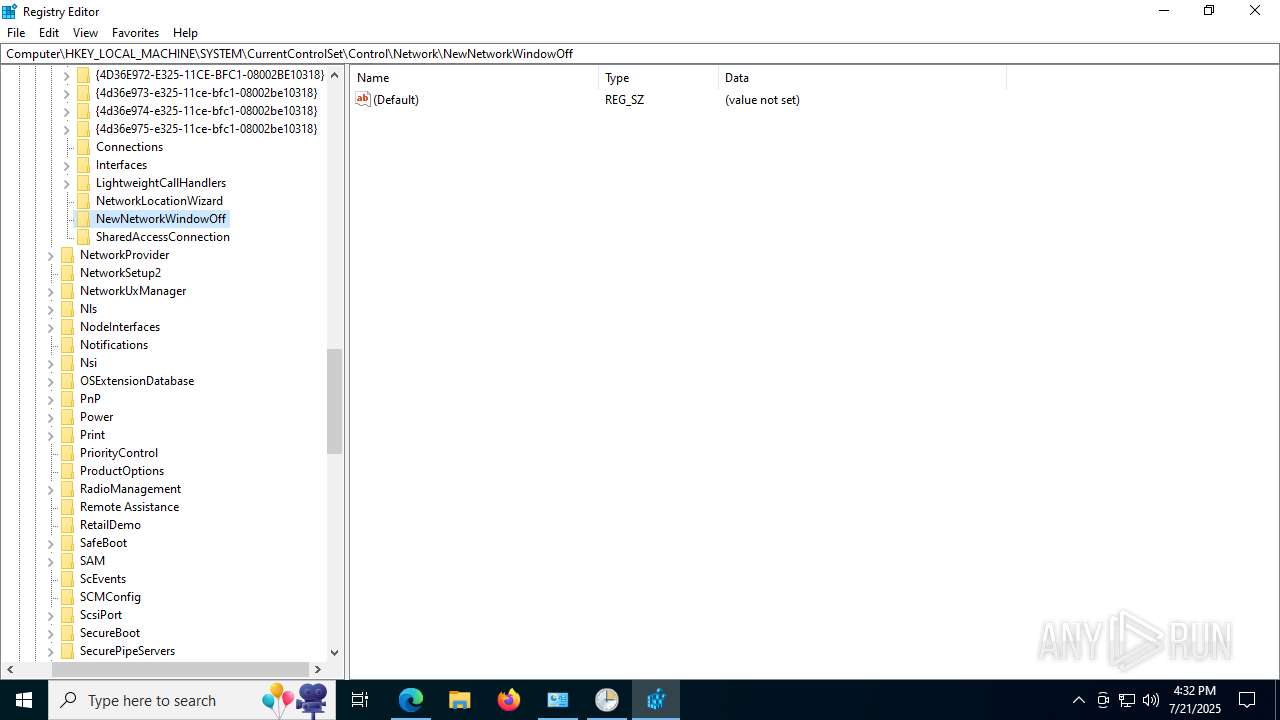
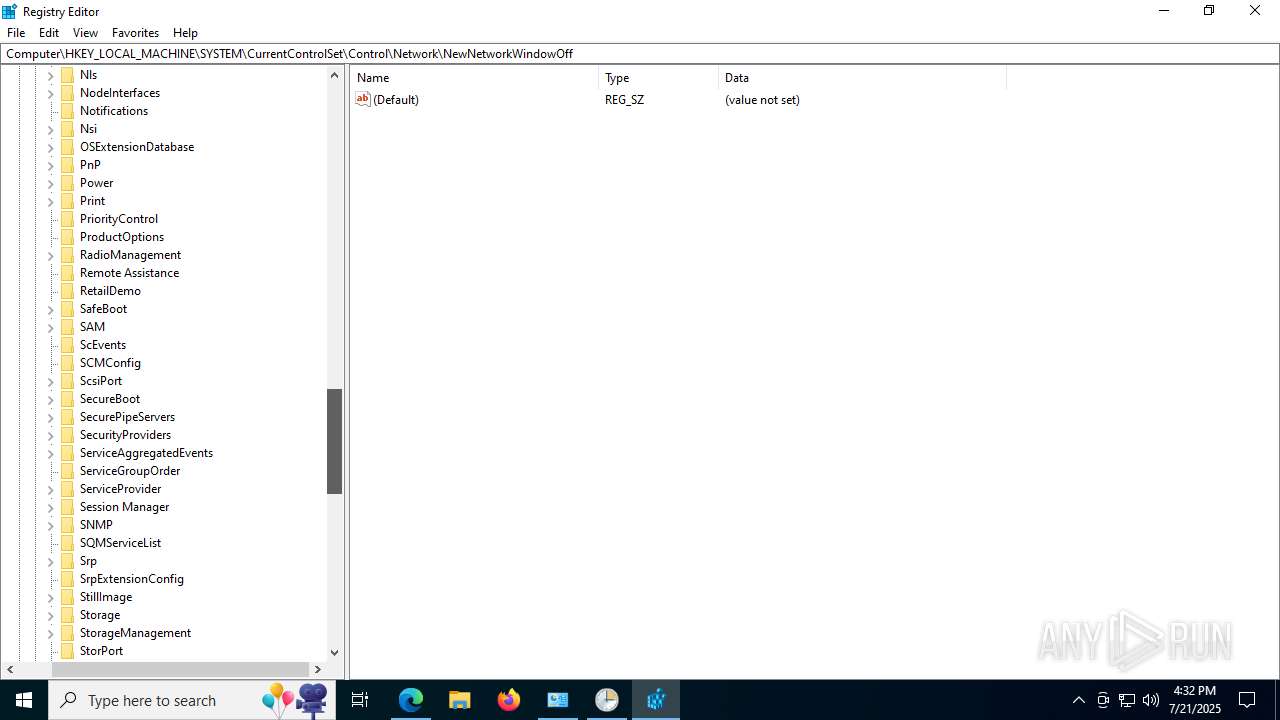
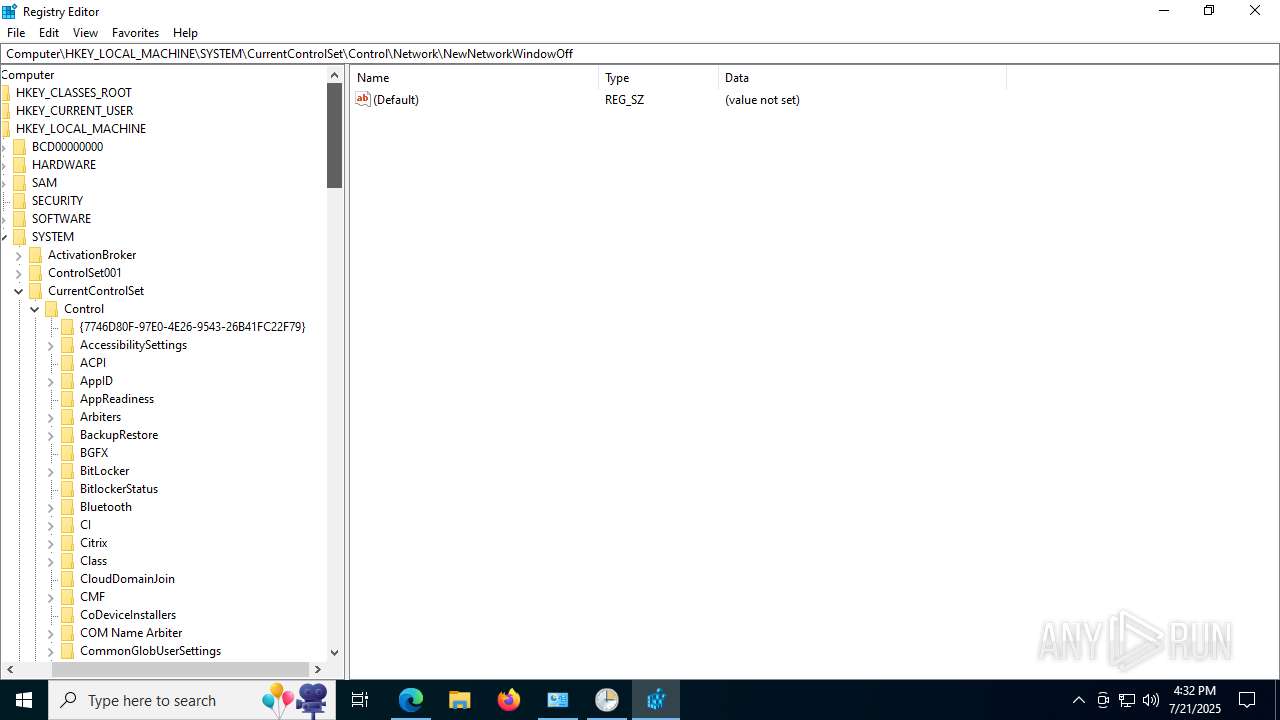
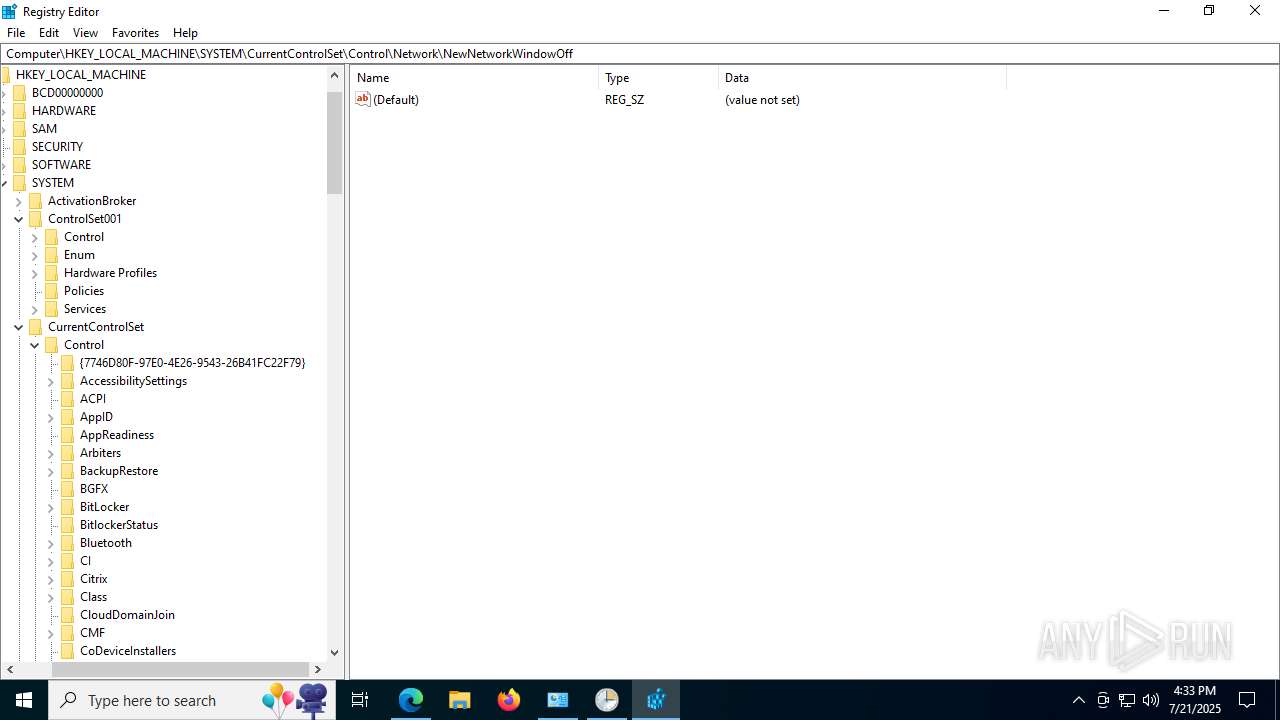
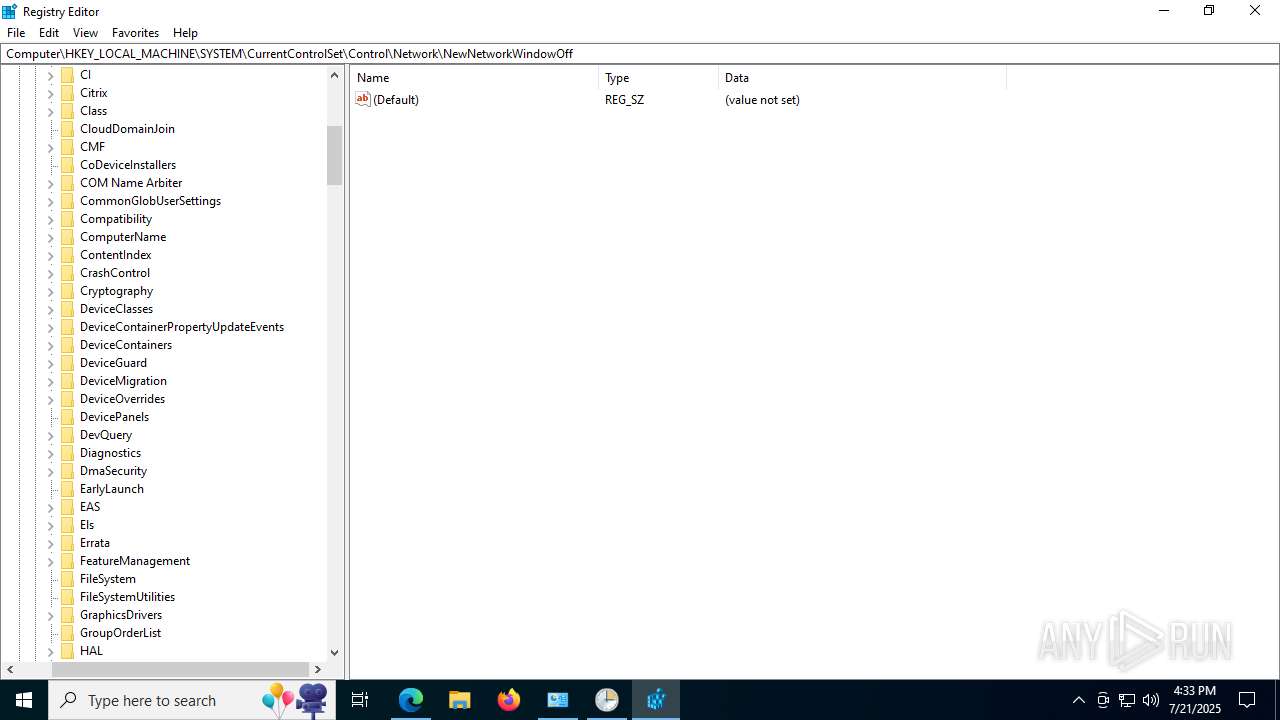
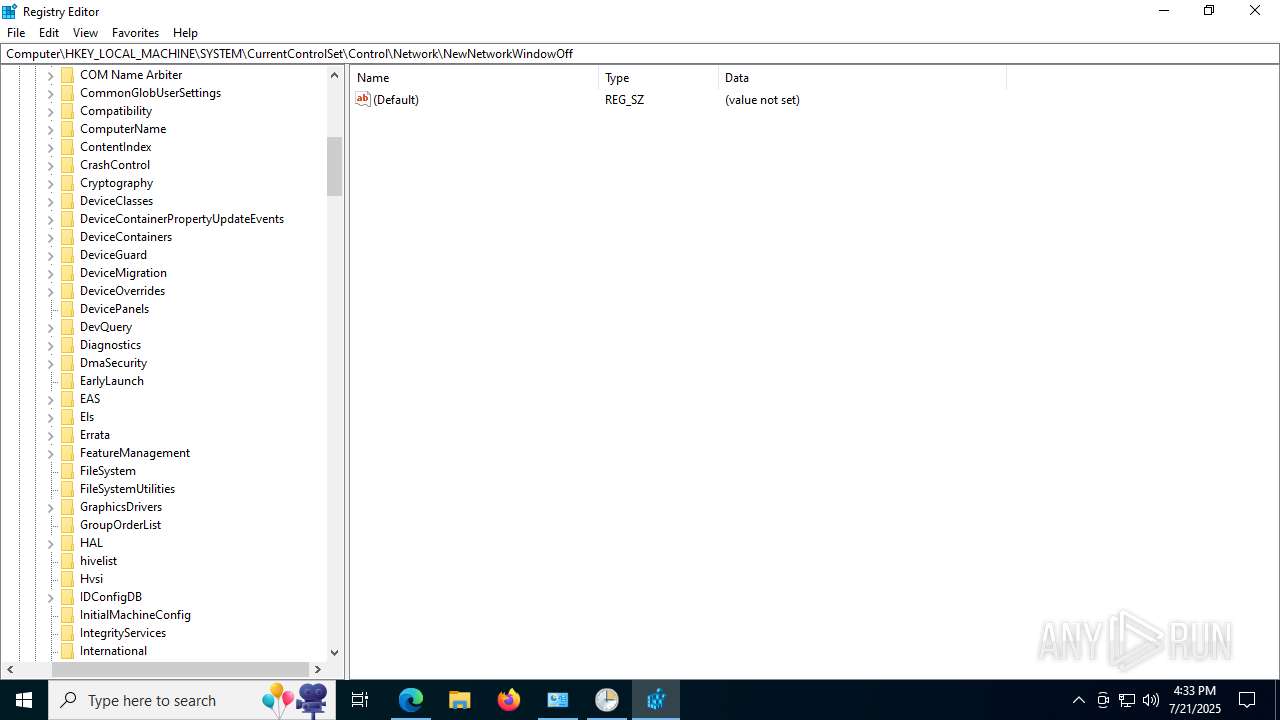
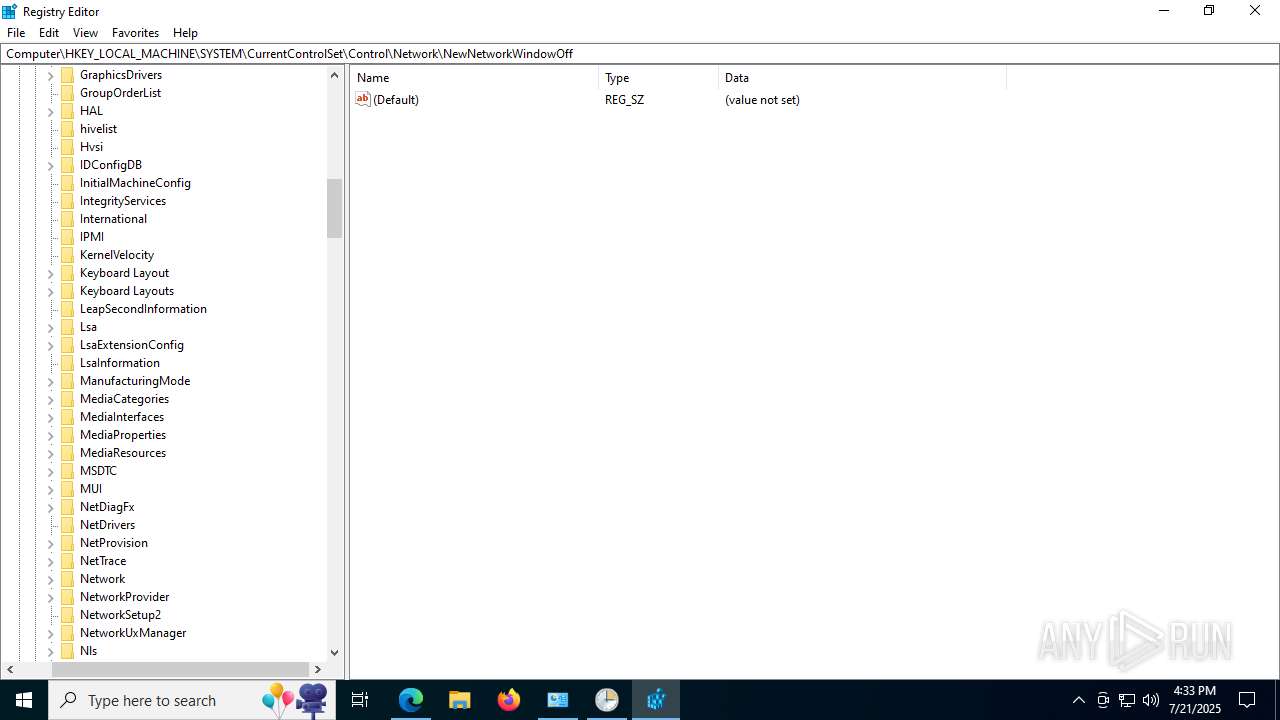
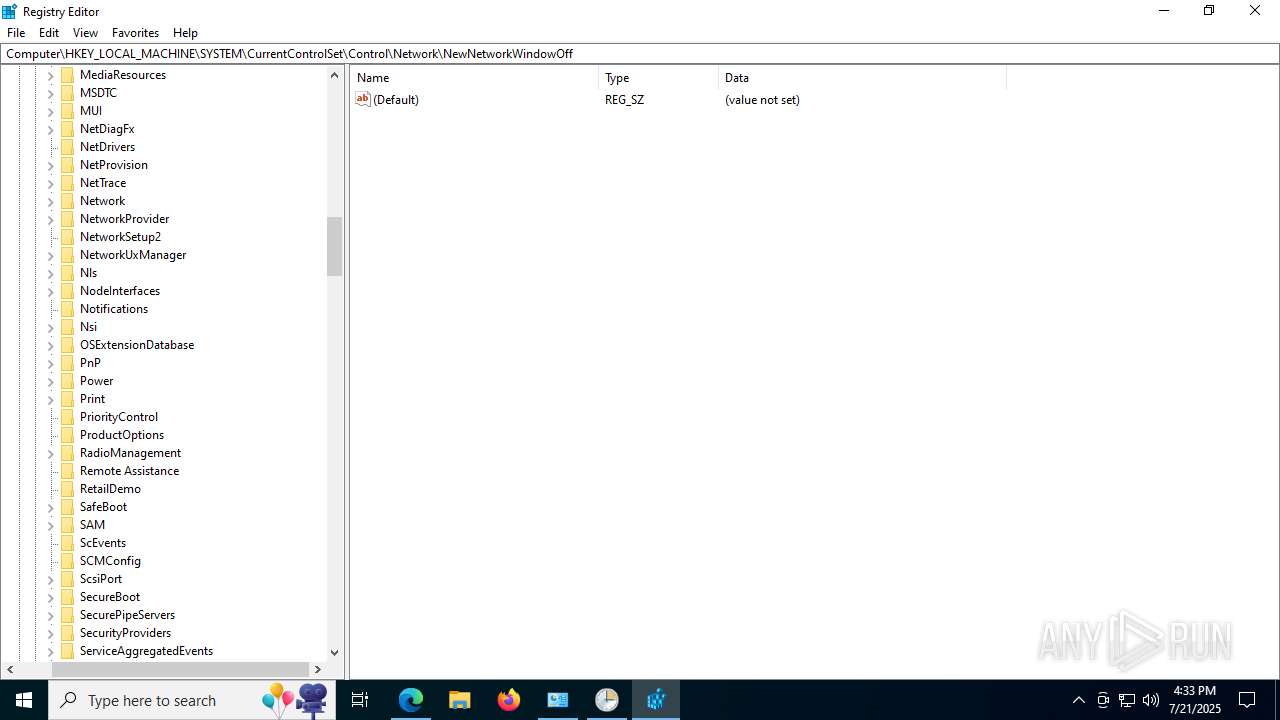
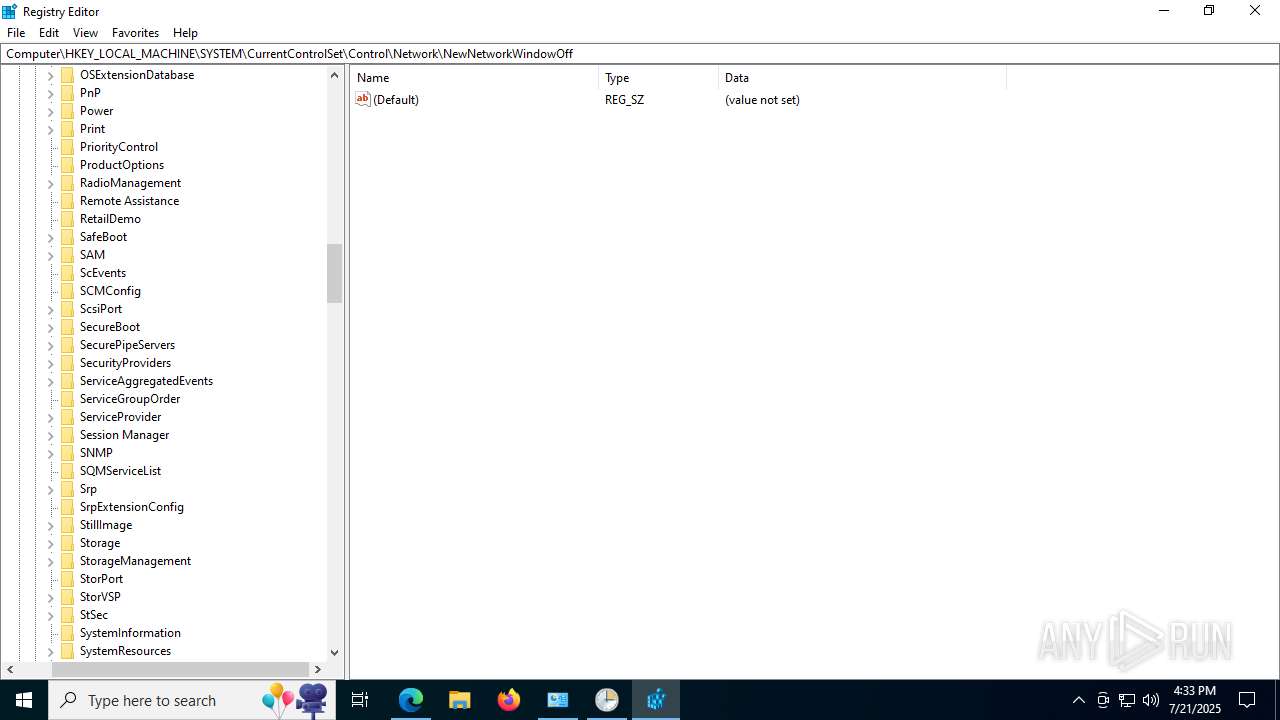
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 4540)
The DLL Hijacking
- msedgewebview2.exe (PID: 7332)
- msedgewebview2.exe (PID: 8212)
SUSPICIOUS
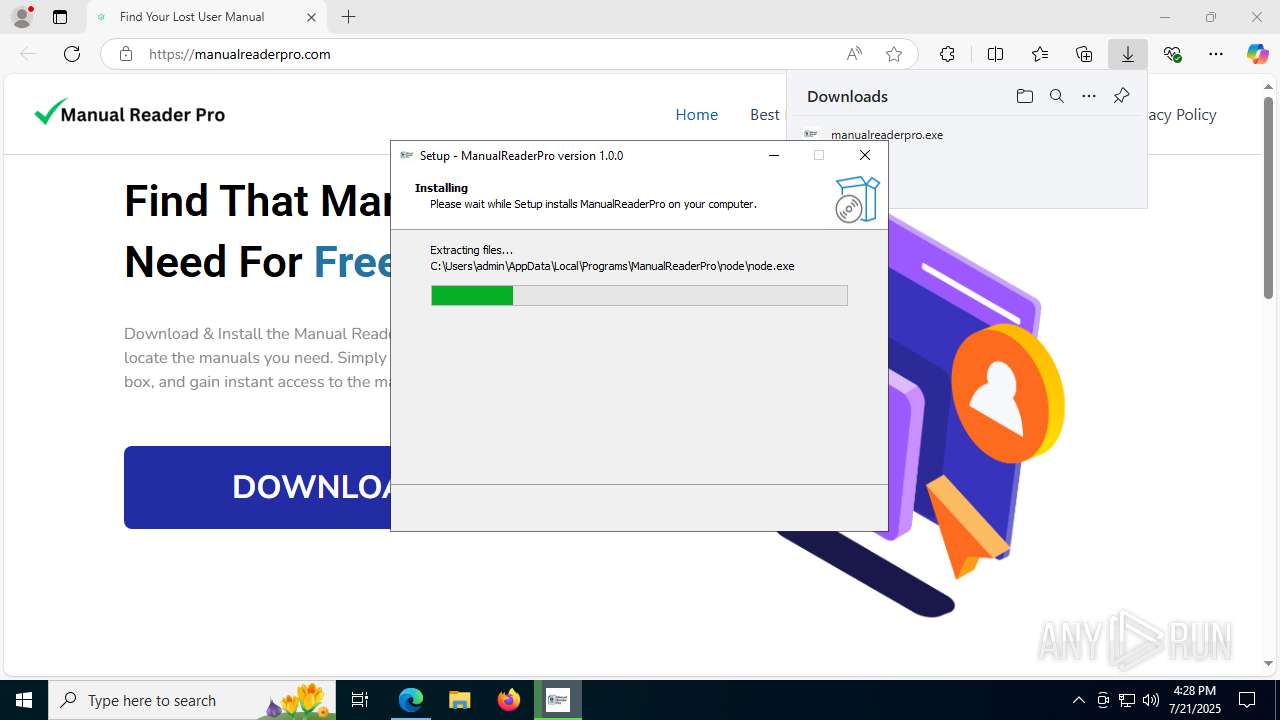
Executable content was dropped or overwritten
- manualreaderpro.exe (PID: 8068)
- manualreaderpro.tmp (PID: 7056)
- ManualReaderPro.exe (PID: 4788)
- tmp3138.exe (PID: 4168)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 516)
- setup.exe (PID: 4916)
- msedgewebview2.exe (PID: 6544)
- unins000.exe (PID: 8580)
- _unins.tmp (PID: 8504)
Reads the Windows owner or organization settings
- manualreaderpro.tmp (PID: 7056)
- _unins.tmp (PID: 8504)
Process drops legitimate windows executable
- manualreaderpro.tmp (PID: 7056)
- ManualReaderPro.exe (PID: 4788)
- tmp3138.exe (PID: 4168)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 516)
- setup.exe (PID: 4916)
- msedgewebview2.exe (PID: 6544)
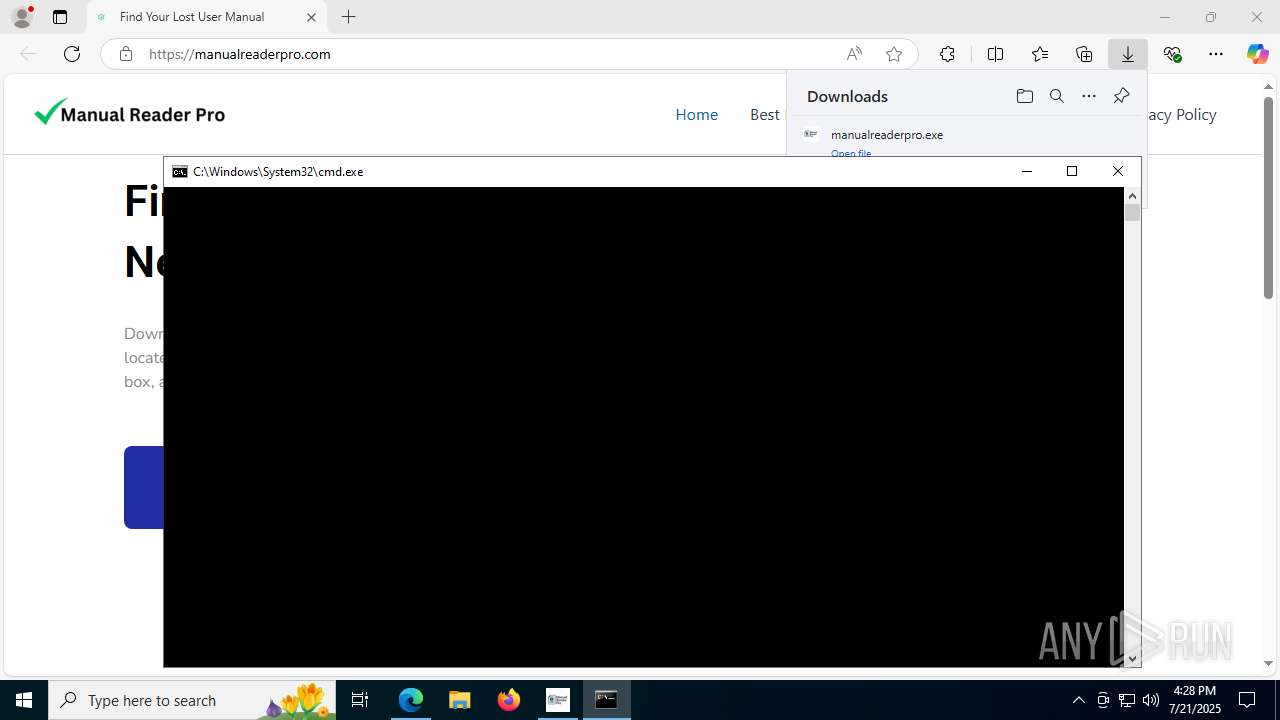
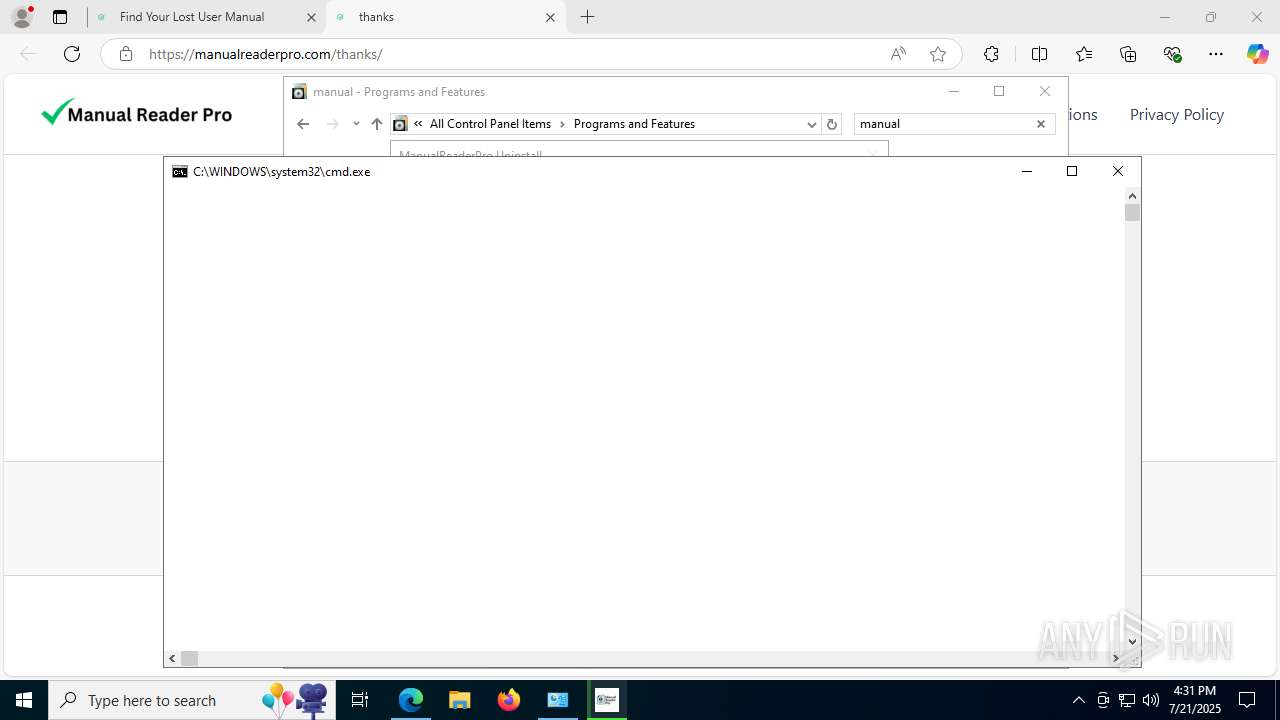
Starts CMD.EXE for commands execution
- manualreaderpro.tmp (PID: 7056)
- node.exe (PID: 7676)
- _unins.tmp (PID: 8504)
Reads security settings of Internet Explorer
- manualreaderpro.tmp (PID: 7056)
- ManualReaderPro.exe (PID: 4788)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 9068)
Executes script using NodeJS
- node.exe (PID: 7676)
Starts a Microsoft application from unusual location
- tmp3138.exe (PID: 4168)
- MicrosoftEdgeUpdate.exe (PID: 4540)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 4540)
- unins000.exe (PID: 8580)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdate.exe (PID: 5628)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7968)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1828)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7980)
The process executes via Task Scheduler
- cmd.exe (PID: 1160)
Application launched itself
- setup.exe (PID: 4916)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 9068)
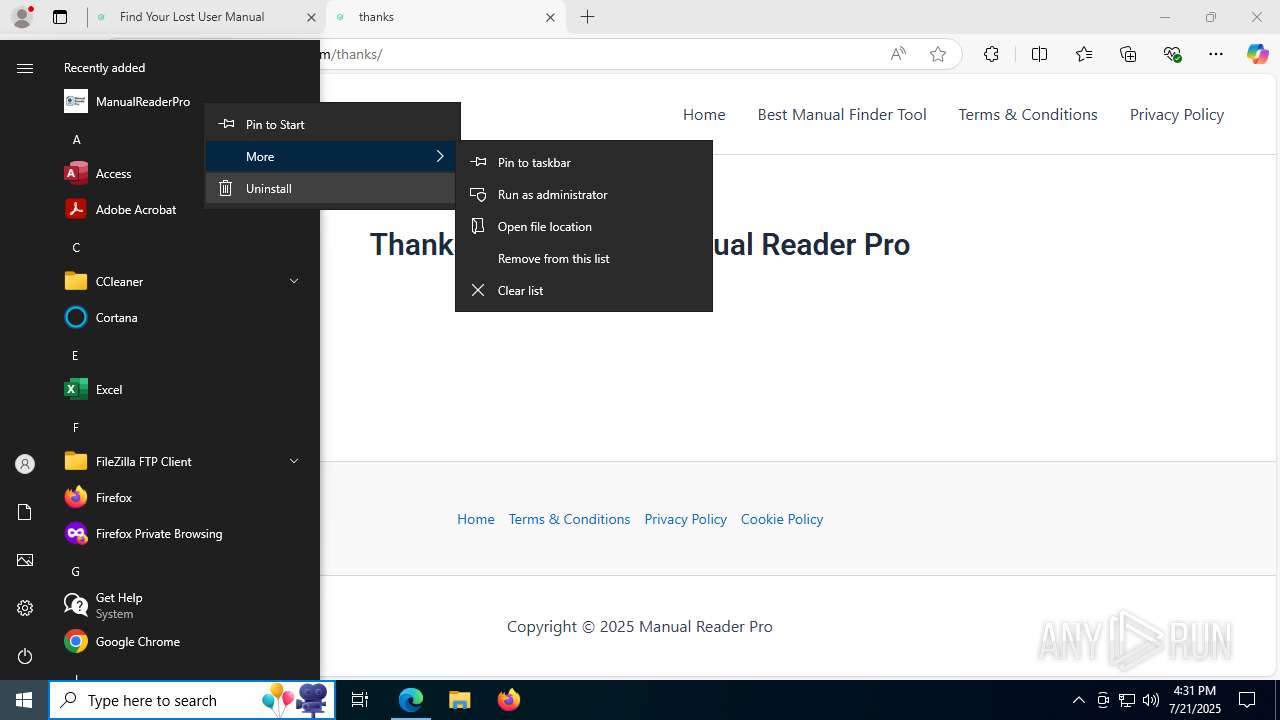
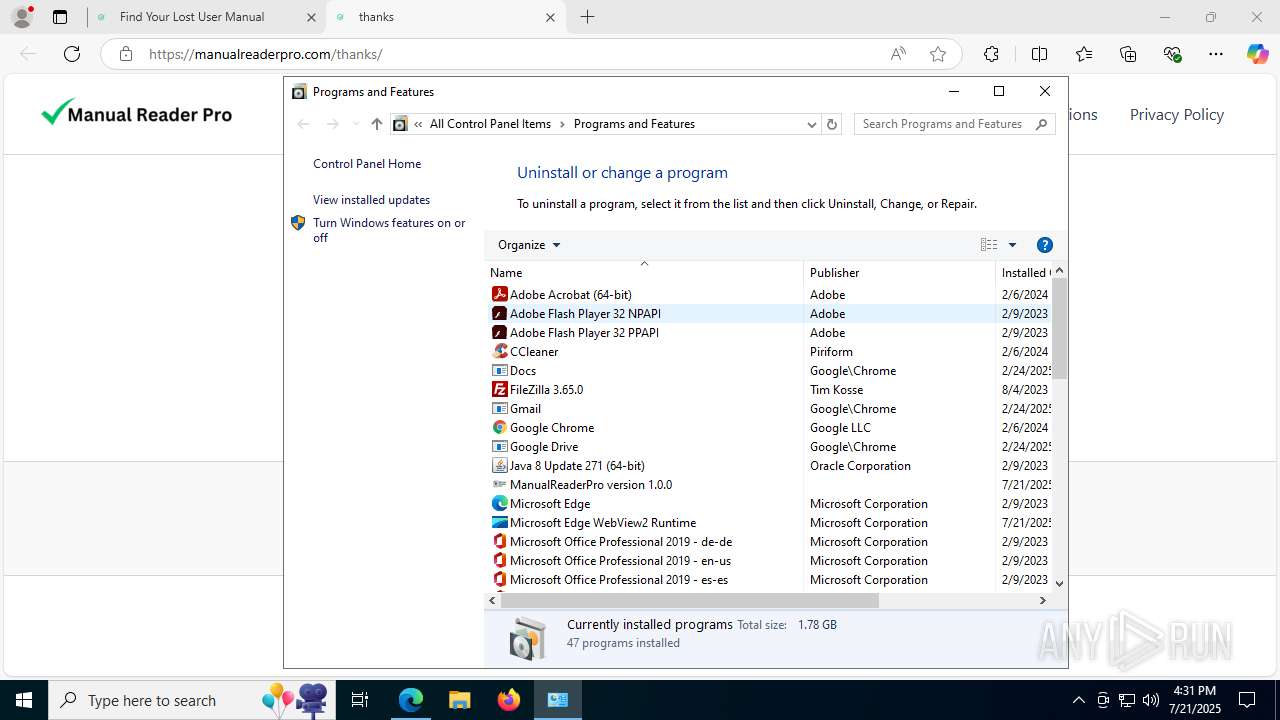
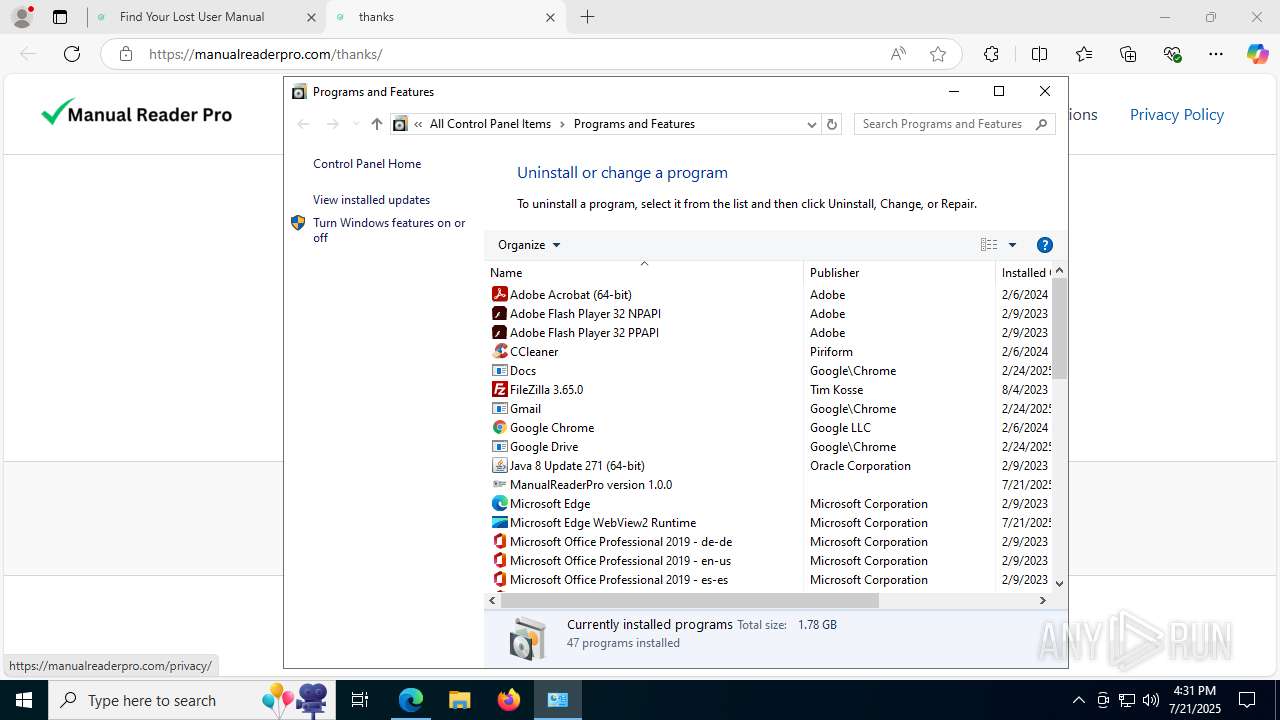
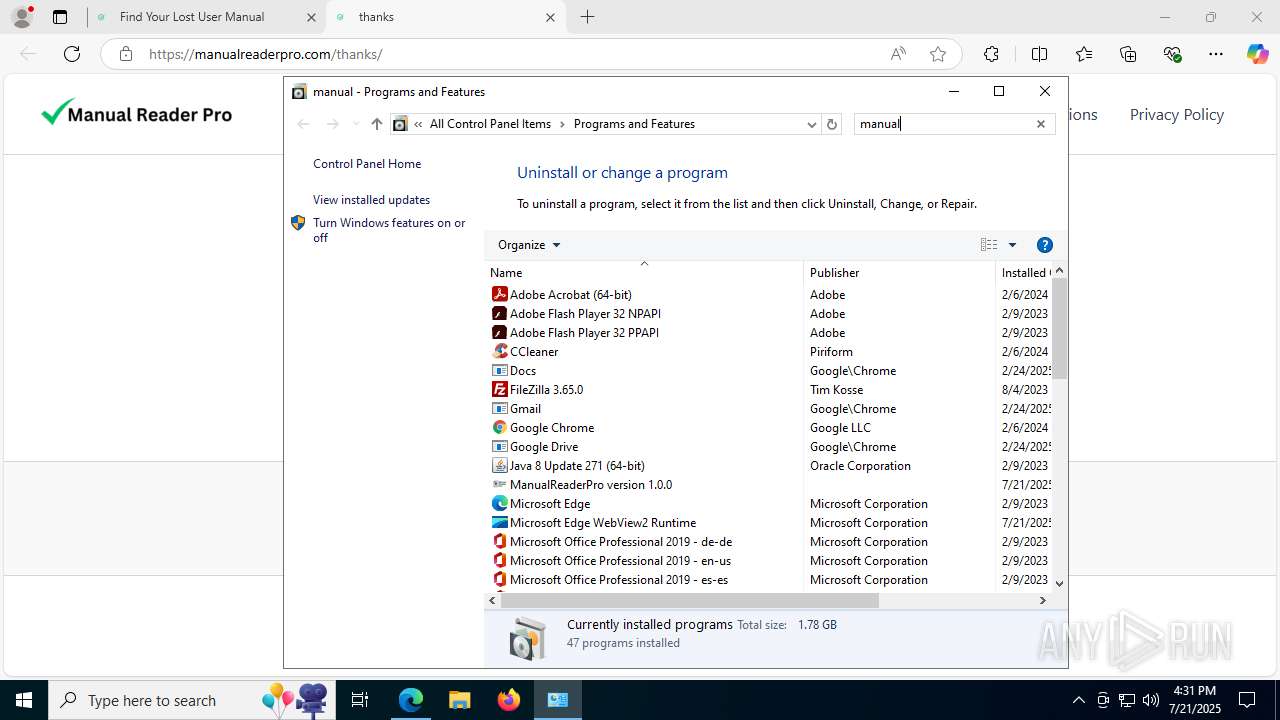
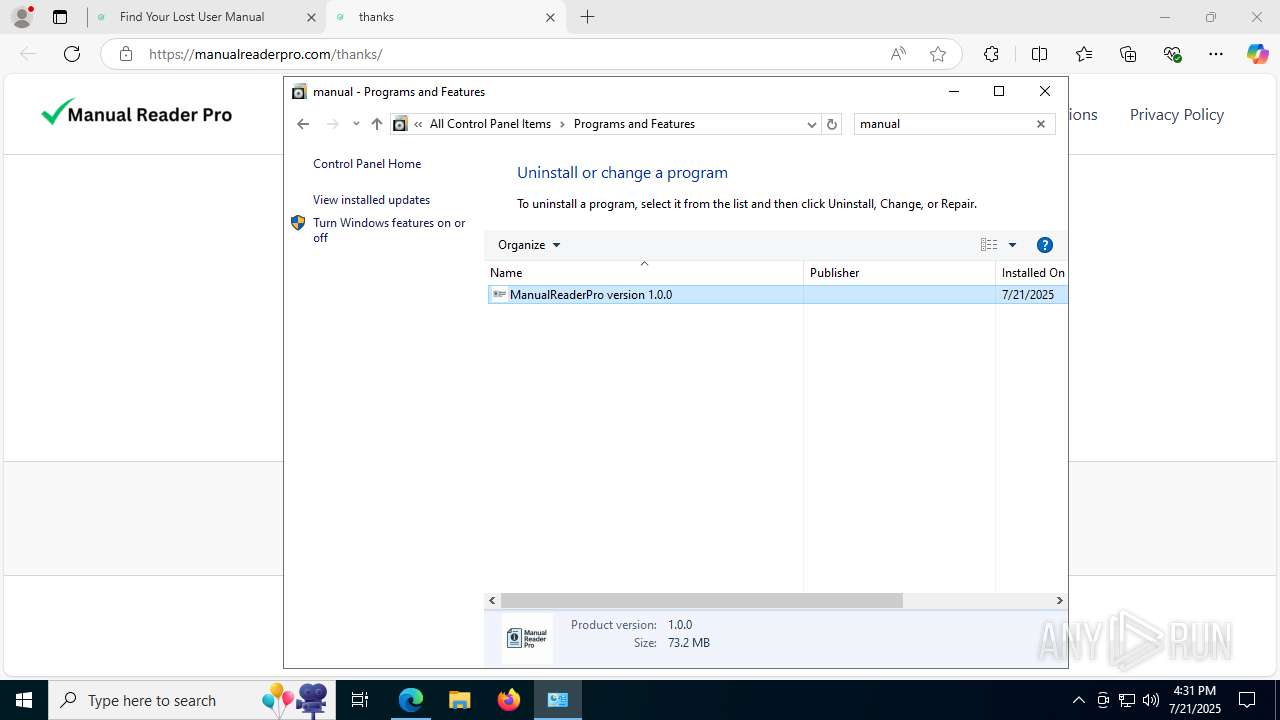
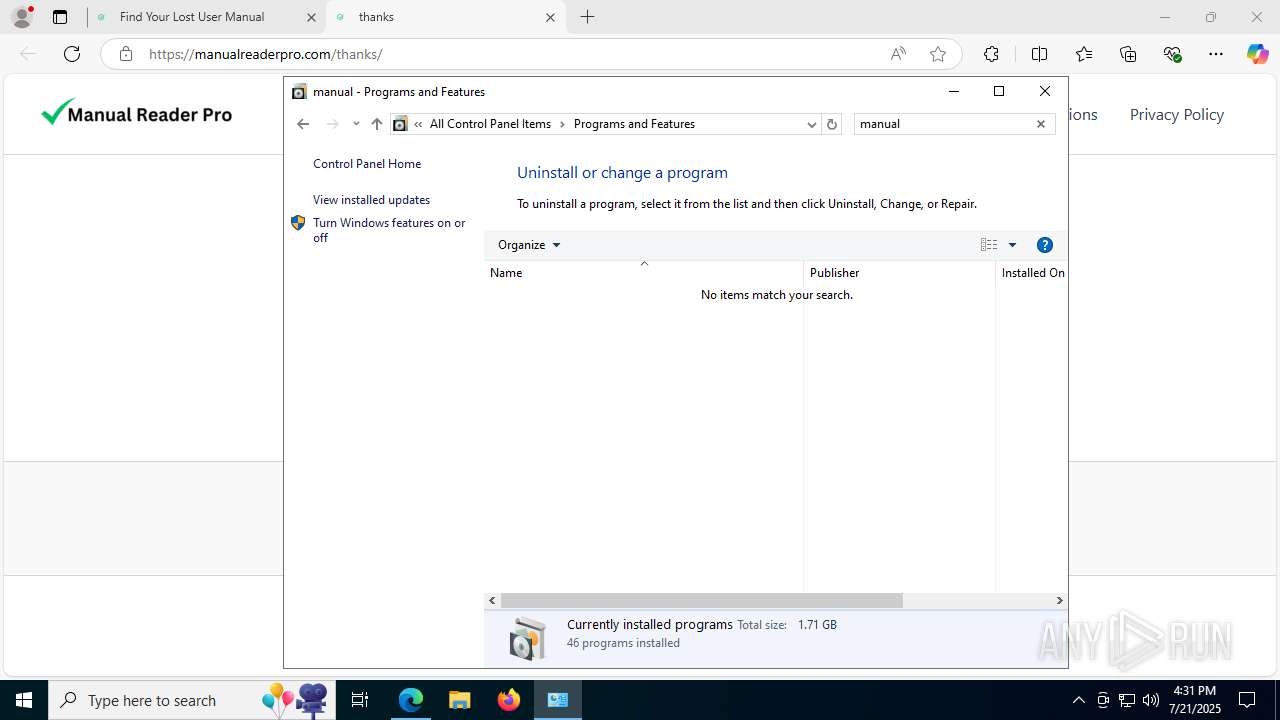
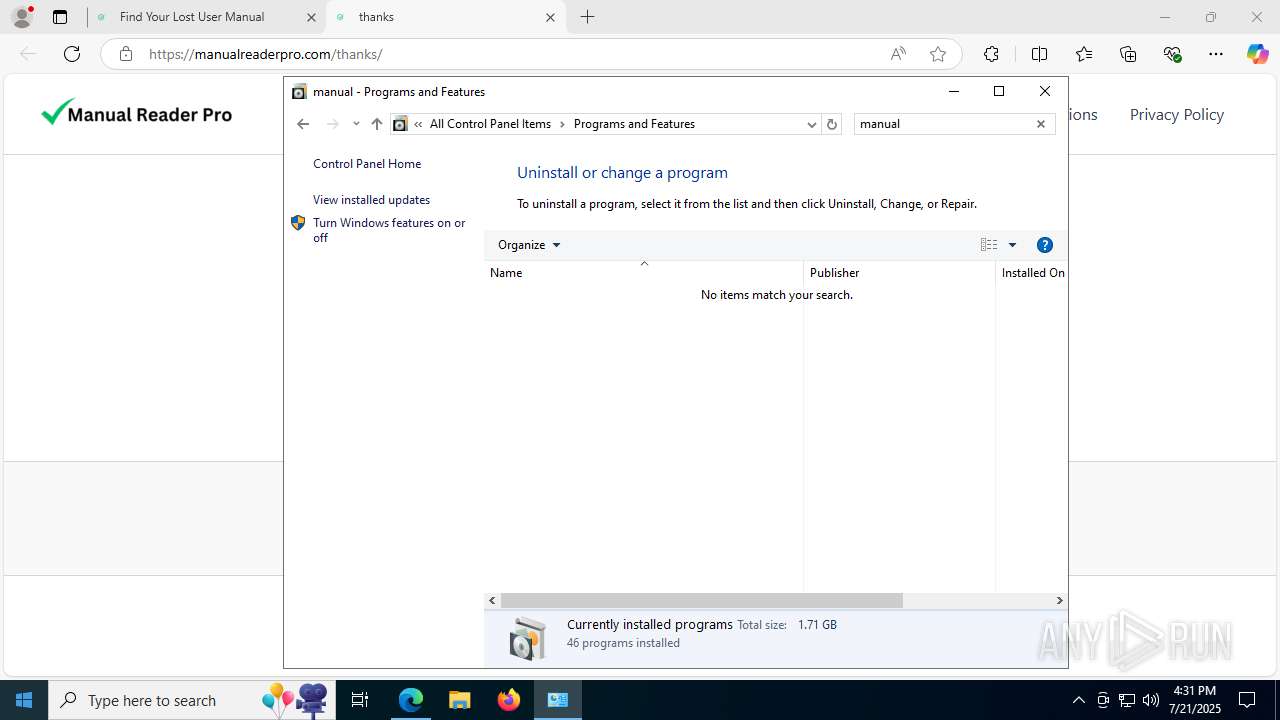
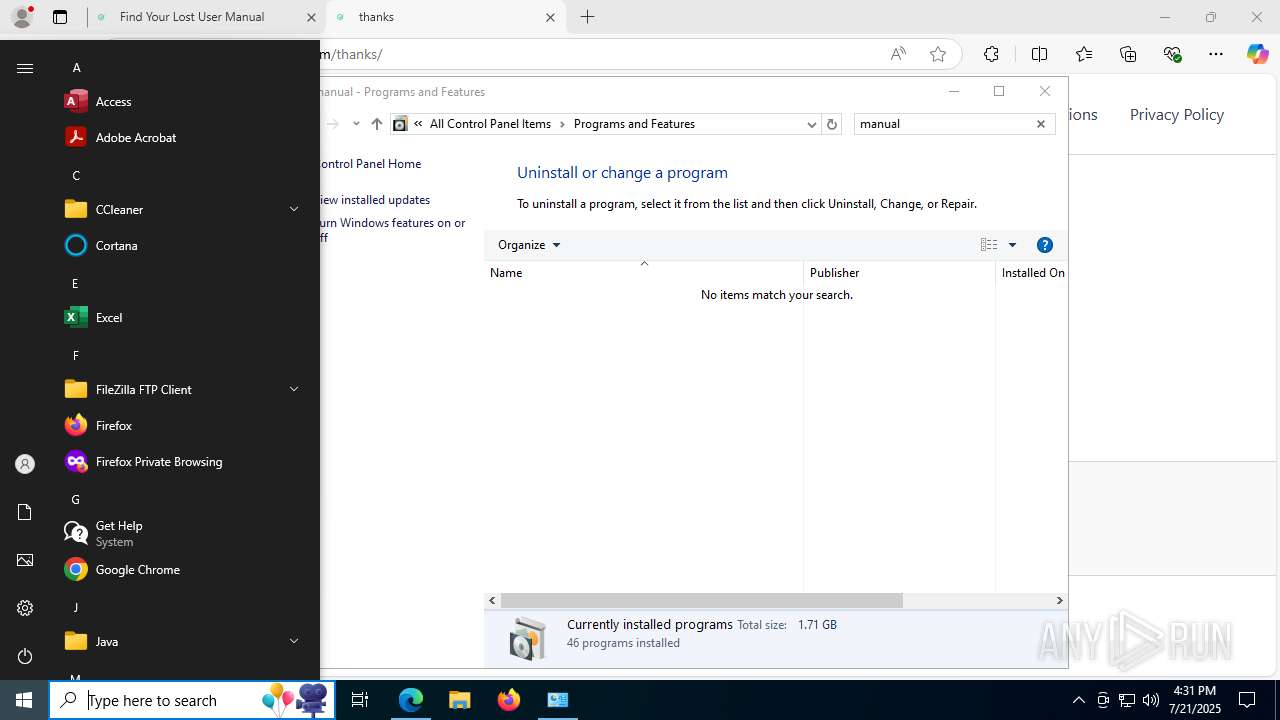
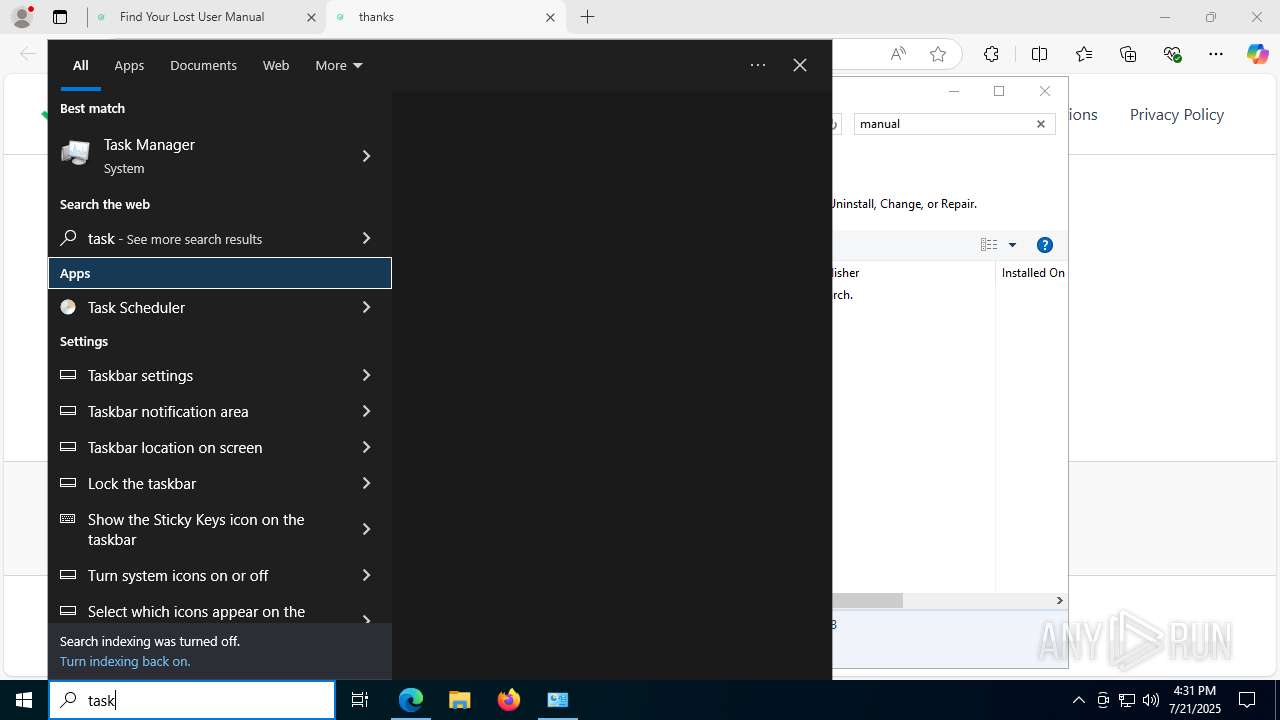
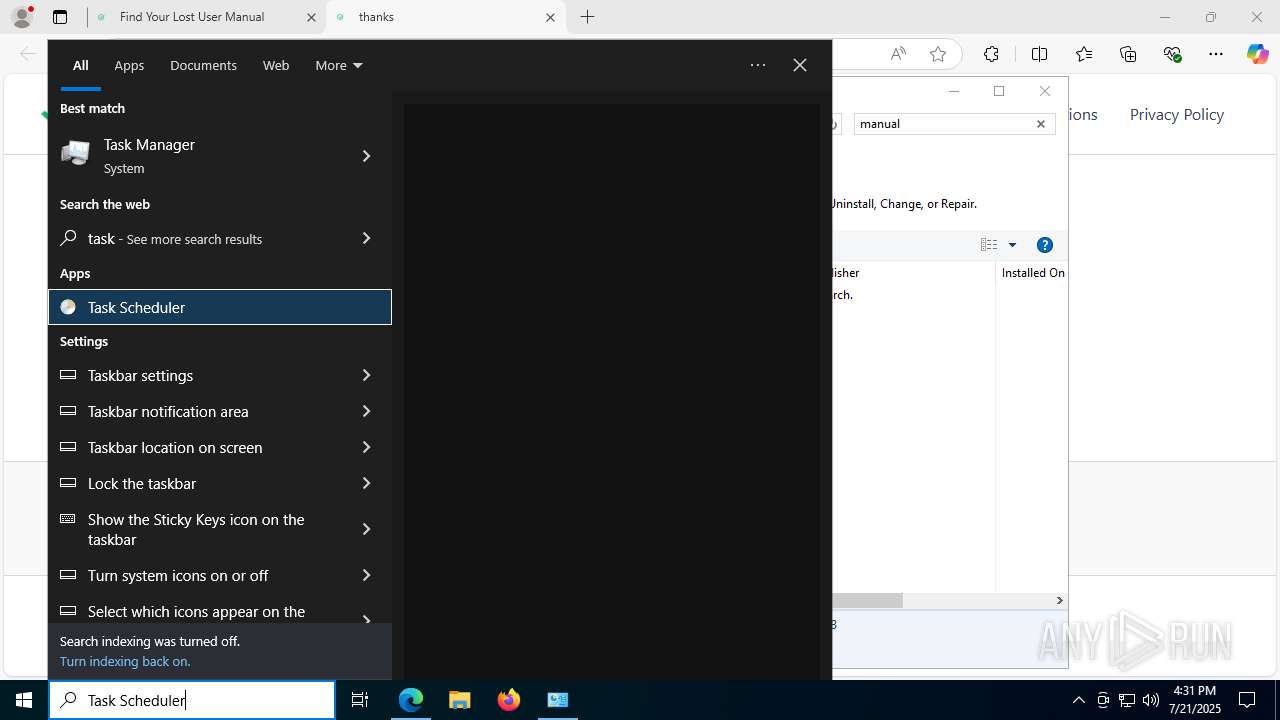
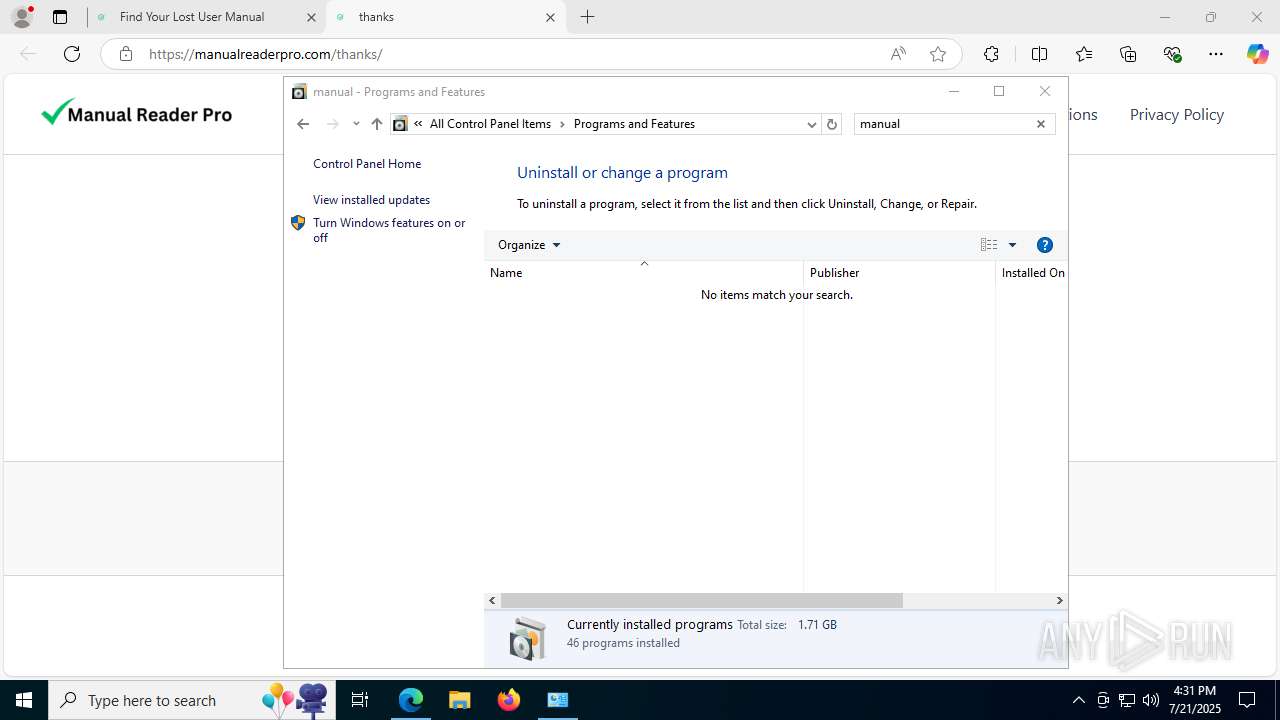
Searches for installed software
- setup.exe (PID: 4916)
- explorer.exe (PID: 8608)
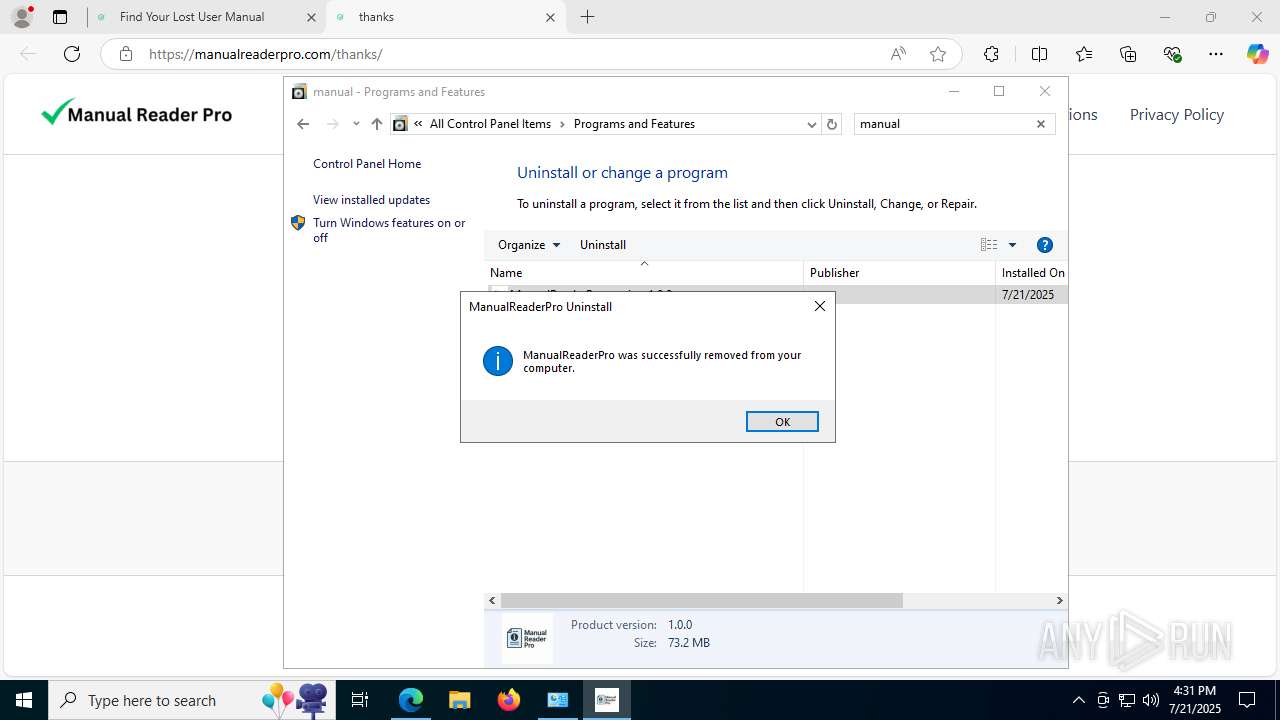
Creates a software uninstall entry
- setup.exe (PID: 4916)
Checks for external IP
- msedgewebview2.exe (PID: 6544)
Starts application with an unusual extension
- unins000.exe (PID: 8580)
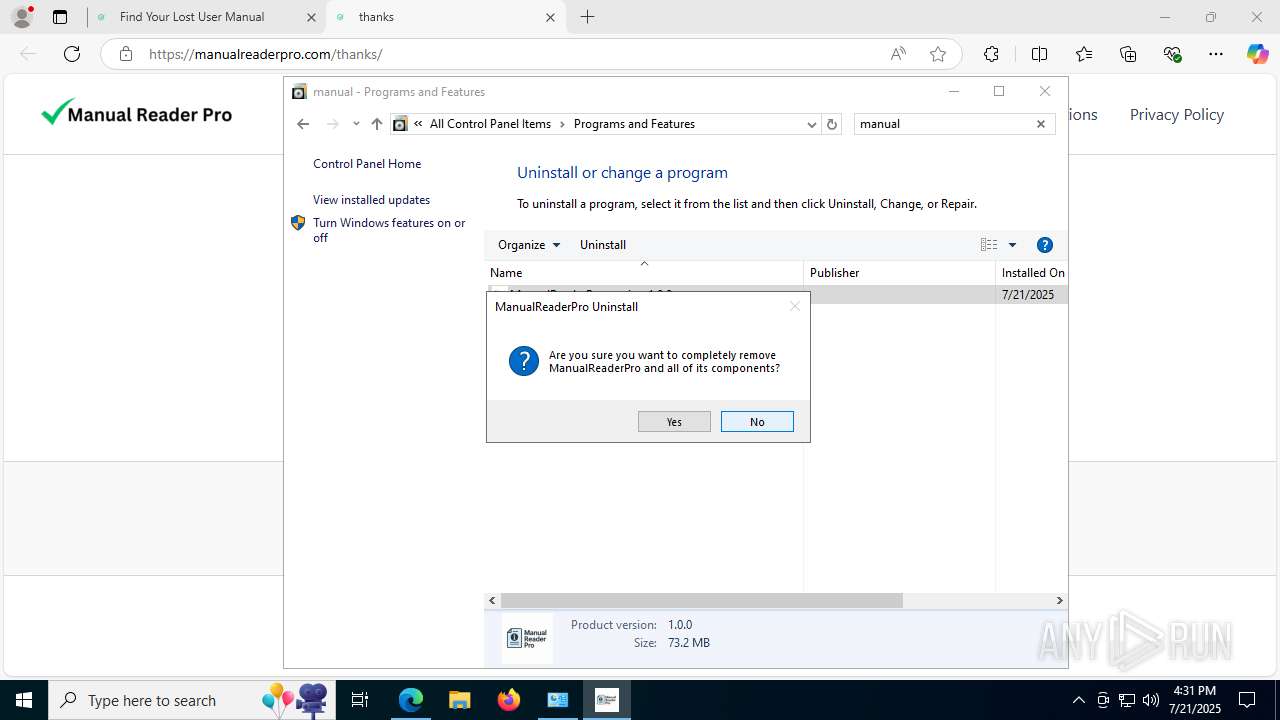
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8532)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5620)
INFO
Checks supported languages
- identity_helper.exe (PID: 7828)
- SearchApp.exe (PID: 5328)
- manualreaderpro.tmp (PID: 7056)
- manualreaderpro.exe (PID: 8068)
- ManualReaderPro.exe (PID: 4788)
- node.exe (PID: 7676)
- tmp3138.exe (PID: 4168)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- MicrosoftEdgeUpdate.exe (PID: 5628)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7968)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1828)
- MicrosoftEdgeUpdate.exe (PID: 7504)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7980)
- MicrosoftEdgeUpdate.exe (PID: 7440)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 516)
- setup.exe (PID: 4916)
- MicrosoftEdgeUpdate.exe (PID: 7924)
- msedgewebview2.exe (PID: 5468)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 7332)
- msedgewebview2.exe (PID: 6544)
- msedgewebview2.exe (PID: 7568)
- msedgewebview2.exe (PID: 8076)
- msedgewebview2.exe (PID: 1232)
- msedgewebview2.exe (PID: 7924)
- msedgewebview2.exe (PID: 5500)
- msedgewebview2.exe (PID: 6772)
- msedgewebview2.exe (PID: 5028)
- msedgewebview2.exe (PID: 2696)
- msedgewebview2.exe (PID: 432)
- msedgewebview2.exe (PID: 7924)
- msedgewebview2.exe (PID: 3460)
- msedgewebview2.exe (PID: 8440)
- msedgewebview2.exe (PID: 8524)
- ManualReaderPro.exe (PID: 8984)
- msedgewebview2.exe (PID: 9068)
- msedgewebview2.exe (PID: 9104)
- msedgewebview2.exe (PID: 7988)
- msedgewebview2.exe (PID: 8116)
- msedgewebview2.exe (PID: 4084)
- msedgewebview2.exe (PID: 8212)
- unins000.exe (PID: 8580)
- _unins.tmp (PID: 8504)
- setup.exe (PID: 7572)
Application launched itself
- msedge.exe (PID: 3656)
Reads Environment values
- identity_helper.exe (PID: 7828)
- node.exe (PID: 7676)
- MicrosoftEdgeUpdate.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 7924)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 9068)
Reads the computer name
- identity_helper.exe (PID: 7828)
- manualreaderpro.tmp (PID: 7056)
- node.exe (PID: 7676)
- ManualReaderPro.exe (PID: 4788)
- MicrosoftEdgeUpdate.exe (PID: 5628)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7968)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1828)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7980)
- MicrosoftEdgeUpdate.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- MicrosoftEdgeUpdate.exe (PID: 7440)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 516)
- MicrosoftEdgeUpdate.exe (PID: 7924)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 7332)
- msedgewebview2.exe (PID: 6544)
- ManualReaderPro.exe (PID: 8984)
- msedgewebview2.exe (PID: 9068)
- msedgewebview2.exe (PID: 8212)
- msedgewebview2.exe (PID: 7988)
- unins000.exe (PID: 8580)
- _unins.tmp (PID: 8504)
- setup.exe (PID: 4916)
Executable content was dropped or overwritten
- msedge.exe (PID: 1468)
- msedge.exe (PID: 3656)
Create files in a temporary directory
- manualreaderpro.exe (PID: 8068)
- manualreaderpro.tmp (PID: 7056)
- ManualReaderPro.exe (PID: 4788)
- tmp3138.exe (PID: 4168)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 9068)
- unins000.exe (PID: 8580)
- _unins.tmp (PID: 8504)
Reads the machine GUID from the registry
- manualreaderpro.tmp (PID: 7056)
- ManualReaderPro.exe (PID: 4788)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- SearchApp.exe (PID: 5328)
- msedgewebview2.exe (PID: 3872)
- ManualReaderPro.exe (PID: 8984)
- msedgewebview2.exe (PID: 9068)
- _unins.tmp (PID: 8504)
Creates files or folders in the user directory
- manualreaderpro.tmp (PID: 7056)
- node.exe (PID: 7676)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 516)
- setup.exe (PID: 7572)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 5468)
- msedgewebview2.exe (PID: 6544)
- msedgewebview2.exe (PID: 9068)
- msedgewebview2.exe (PID: 7988)
- setup.exe (PID: 4916)
Reads the software policy settings
- manualreaderpro.tmp (PID: 7056)
- ManualReaderPro.exe (PID: 4788)
- MicrosoftEdgeUpdate.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- SearchApp.exe (PID: 5328)
- MicrosoftEdgeUpdate.exe (PID: 7924)
- slui.exe (PID: 7812)
- _unins.tmp (PID: 8504)
Creates a software uninstall entry
- manualreaderpro.tmp (PID: 7056)
Reads product name
- node.exe (PID: 7676)
Checks proxy server information
- ManualReaderPro.exe (PID: 4788)
- MicrosoftEdgeUpdate.exe (PID: 6808)
- MicrosoftEdgeUpdate.exe (PID: 7504)
- MicrosoftEdgeUpdate.exe (PID: 7924)
- msedgewebview2.exe (PID: 3872)
- slui.exe (PID: 7812)
- msedgewebview2.exe (PID: 9068)
Disables trace logs
- ManualReaderPro.exe (PID: 4788)
Process checks computer location settings
- ManualReaderPro.exe (PID: 4788)
- SearchApp.exe (PID: 5328)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- setup.exe (PID: 4916)
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 8076)
- msedgewebview2.exe (PID: 1232)
- msedgewebview2.exe (PID: 5500)
- msedgewebview2.exe (PID: 7924)
- msedgewebview2.exe (PID: 5028)
- msedgewebview2.exe (PID: 2696)
- msedgewebview2.exe (PID: 6772)
- msedgewebview2.exe (PID: 3460)
- msedgewebview2.exe (PID: 432)
- msedgewebview2.exe (PID: 7924)
- msedgewebview2.exe (PID: 8440)
- msedgewebview2.exe (PID: 8524)
- msedgewebview2.exe (PID: 9068)
- msedgewebview2.exe (PID: 4084)
- _unins.tmp (PID: 8504)
The sample compiled with english language support
- tmp3138.exe (PID: 4168)
- ManualReaderPro.exe (PID: 4788)
- MicrosoftEdgeUpdate.exe (PID: 4540)
- manualreaderpro.tmp (PID: 7056)
- setup.exe (PID: 4916)
- MicrosoftEdge_X64_138.0.3351.95.exe (PID: 516)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 4540)
Compiled with Borland Delphi (YARA)
- manualreaderpro.exe (PID: 8068)
- manualreaderpro.tmp (PID: 7056)
Detects InnoSetup installer (YARA)
- manualreaderpro.exe (PID: 8068)
- manualreaderpro.tmp (PID: 7056)
Reads CPU info
- msedgewebview2.exe (PID: 3872)
- msedgewebview2.exe (PID: 9068)
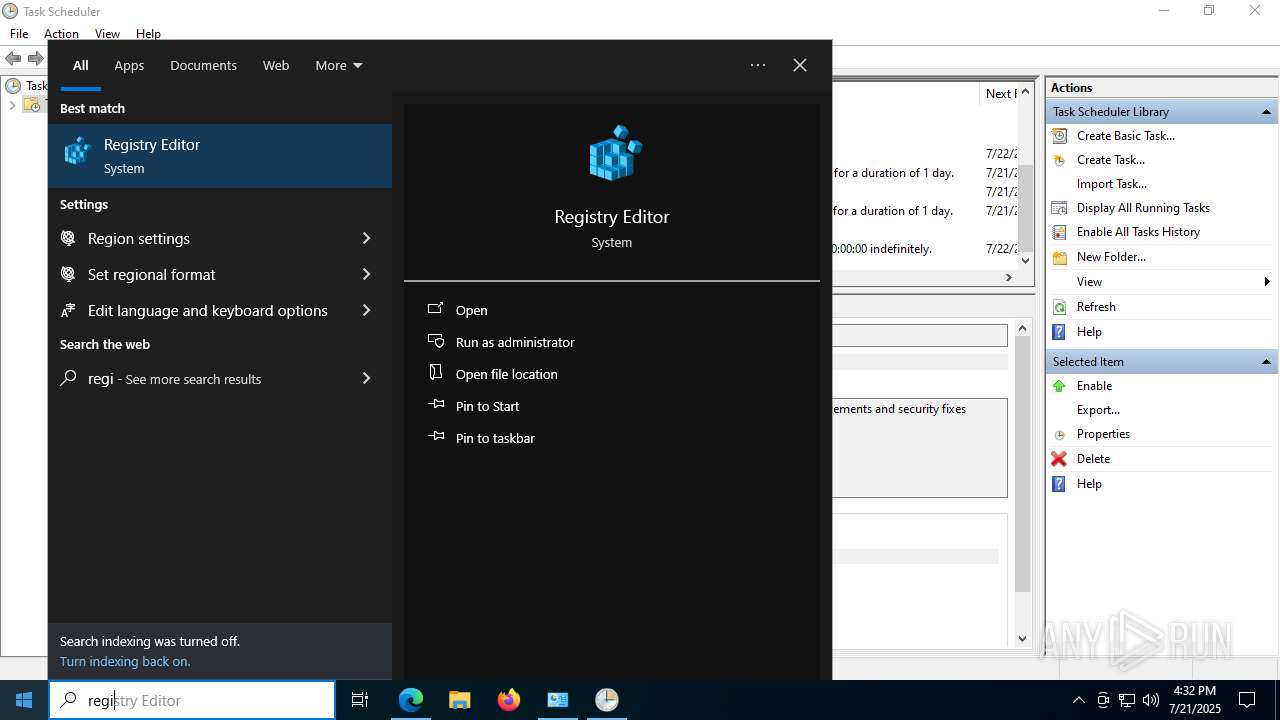
Manual execution by a user
- ManualReaderPro.exe (PID: 8984)
- mmc.exe (PID: 8836)
- regedit.exe (PID: 6180)
- regedit.exe (PID: 9064)
- mmc.exe (PID: 8960)
Reads security settings of Internet Explorer
- mmc.exe (PID: 8960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
267
Monitored processes
109
Malicious processes
13
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.95\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Programs\ManualReaderPro\ManualReaderPro.exe.WebView2\EBWebView" --webview-exe-name=ManualReaderPro.exe --webview-exe-version=1.0.0+a47db30e718df2a296dbf3979ebc300b721cf928 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=1 --force-high-res-timeticks=disabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --js-flags="--expose-gc --ms-user-locale=" --always-read-main-dll --field-trial-handle=1860,i,2235486578399526604,3956673594006981296,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,SafetyHub,SegmentationPlatform,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeCoupons,msAutofillEdgeCouponsAutoApply,msAutofillEdgeServiceRequest,msAutofillEnableEdgeSuggestions,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msETFOffstoreExtensionFileDataCollection,msETFPasswordTheftDNRActionSignals,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillShowDeployedPassword,msEdgeCaptureSelectionInPDF,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeScreenshotUI,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTipping,msEdgeTranslate,msEdgeUseCaptivePortalService,msEdgeWebCapture,msEdgeWebCaptureUniformExperience,msEdgeWebContentFilteringFeedback,msEdgeWorkSearchBanner,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLlmConsumerDlpPurview,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msNumberOfSitesToPin,msNurturingSitePinningWithWindowsConsent,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSitePinningWithoutUi,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --mojo-platform-channel-handle=5576 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.95\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 138.0.3351.95 Modules
| |||||||||||||||
| 436 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6704,i,17672314508304880086,8777747280449281902,262144 --variations-seed-version --mojo-platform-channel-handle=8172 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 516 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{B06AEFFC-5A8F-45A0-A1BF-829178B3BB8D}\MicrosoftEdge_X64_138.0.3351.95.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{B06AEFFC-5A8F-45A0-A1BF-829178B3BB8D}\MicrosoftEdge_X64_138.0.3351.95.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 138.0.3351.95 Modules
| |||||||||||||||
| 700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5704,i,17672314508304880086,8777747280449281902,262144 --variations-seed-version --mojo-platform-channel-handle=6388 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1160 | "C:\Windows\System32\cmd.exe" /C start "" /min "C:\Users\admin\AppData\Local\Programs\ManualReaderPro\node\node.exe" "C:\Users\admin\AppData\Local\Programs\ManualReaderPro\24c92c24-5c4e-451a-8885-9509dc69ab38.js" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.95\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Programs\ManualReaderPro\ManualReaderPro.exe.WebView2\EBWebView" --webview-exe-name=ManualReaderPro.exe --webview-exe-version=1.0.0+a47db30e718df2a296dbf3979ebc300b721cf928 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=1 --force-high-res-timeticks=disabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --js-flags="--expose-gc --ms-user-locale=" --always-read-main-dll --field-trial-handle=1860,i,2235486578399526604,3956673594006981296,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,SafetyHub,SegmentationPlatform,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeCoupons,msAutofillEdgeCouponsAutoApply,msAutofillEdgeServiceRequest,msAutofillEnableEdgeSuggestions,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msETFOffstoreExtensionFileDataCollection,msETFPasswordTheftDNRActionSignals,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillShowDeployedPassword,msEdgeCaptureSelectionInPDF,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeScreenshotUI,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTipping,msEdgeTranslate,msEdgeUseCaptivePortalService,msEdgeWebCapture,msEdgeWebCaptureUniformExperience,msEdgeWebContentFilteringFeedback,msEdgeWorkSearchBanner,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLlmConsumerDlpPurview,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msNumberOfSitesToPin,msNurturingSitePinningWithWindowsConsent,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSitePinningWithoutUi,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --mojo-platform-channel-handle=4552 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.95\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 138.0.3351.95 Modules
| |||||||||||||||
| 1468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2124,i,17672314508304880086,8777747280449281902,262144 --variations-seed-version --mojo-platform-channel-handle=2660 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1712 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://manualreaderpro.com/thank | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | manualreaderpro.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1828 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
63 067
Read events
61 220
Write events
1 766
Delete events
81
Modification events
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\ConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0049006E007000750074005F007B00380033003200620036003800640032002D0037006600650032002D0034006500370031002D0061003300610064002D003200360031003600360062003600350036006500630036007D0000007F3C15805CFADB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0041007000700073005F007B00360061006600300039003700320061002D0035003700620066002D0034006300310031002D0062006400340062002D006200650032006400340064003100340034003400350064007D0000007F3C15805CFADB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LastConstraintIndexBuildCompleted |
Value: 518517805CFADB017F3C15805CFADB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Input_{832b68d2-7fe2-4e71-a3ad-26166b656ec6} | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6af0972a-57bf-4c11-bd4b-be2d4d14445d} | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | IndexedLanguage |
Value: en-US | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppIndexer |
| Operation: | write | Name: | LatestCacheFileName |
Value: 410070007000430061006300680065003100330033003900370035003800380039003100310038003100330034003900340039002E007400780074000000D7A317805CFADB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppIndexer |
| Operation: | write | Name: | InstalledWin32AppsRevision |
Value: 7B00410042004100420044004200390032002D0039003700310043002D0034003500420035002D0041004500370046002D003400420041004600390046004200320033003900430037007D000000D7A317805CFADB01 | |||
| (PID) Process: | (3656) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
235
Suspicious files
744
Text files
411
Unknown types
125
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d368.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d368.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d368.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d368.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d378.TMP | — | |
MD5:— | SHA256:— | |||
| 3656 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
211
DNS requests
223
Threats
154
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1468 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:QpQKuDhEiaQm_gQ4DkpDv4qzmV_T8tDNN77QeCvr7Uk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3656 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6212 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3656 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEDE8qcg4zdsh5ONU5tvwIWo%3D | unknown | — | — | whitelisted |
5240 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3656 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
7000 | svchost.exe | GET | — | 199.232.214.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7aa19579-c418-44fd-8406-8933fb3edba4?P1=1753720144&P2=404&P3=2&P4=DamYnNj1%2bTSpl%2fKvGigl67FDCPztQBWEVhgYs97akRDbWacQXcHuP47VAIVz2JhqOo%2bM48v6fwXMxYYC77QkCQ%3d%3d | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3160 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1468 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1468 | msedge.exe | 142.250.186.72:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
1468 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1468 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1468 | msedge.exe | 188.114.96.3:443 | manualreaderpro.com | CLOUDFLARENET | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
manualreaderpro.com |
| malicious |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn.mxpnl.com |
| whitelisted |
cdn-defaultasset.s3.us-east-1.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1468 | msedge.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (manualreaderpro .com) |
1468 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1468 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1468 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1468 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1468 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1468 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2200 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (manualreaderproweb .com) |
7000 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
6544 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
Process | Message |
|---|---|
ManualReaderPro.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ManualReaderPro.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ManualReaderPro.exe | WebView2 Warning: Using default User Data Folder is not recommended, please see documentation. https://go.microsoft.com/fwlink/?linkid=2187341
|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Programs\ManualReaderPro\ManualReaderPro.exe.WebView2 directory exists )
|
ManualReaderPro.exe | WebView2 Warning: Using default User Data Folder is not recommended, please see documentation. https://go.microsoft.com/fwlink/?linkid=2187341
|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Programs\ManualReaderPro\ManualReaderPro.exe.WebView2\EBWebView directory exists )
|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|