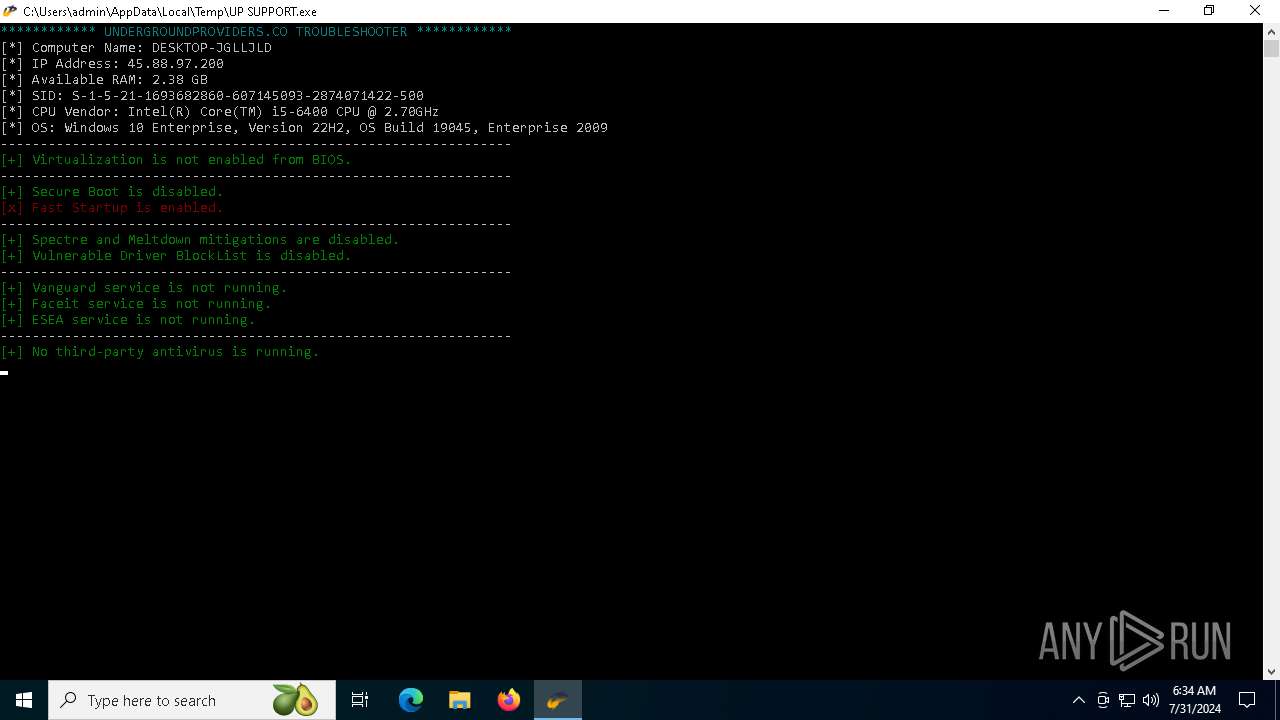
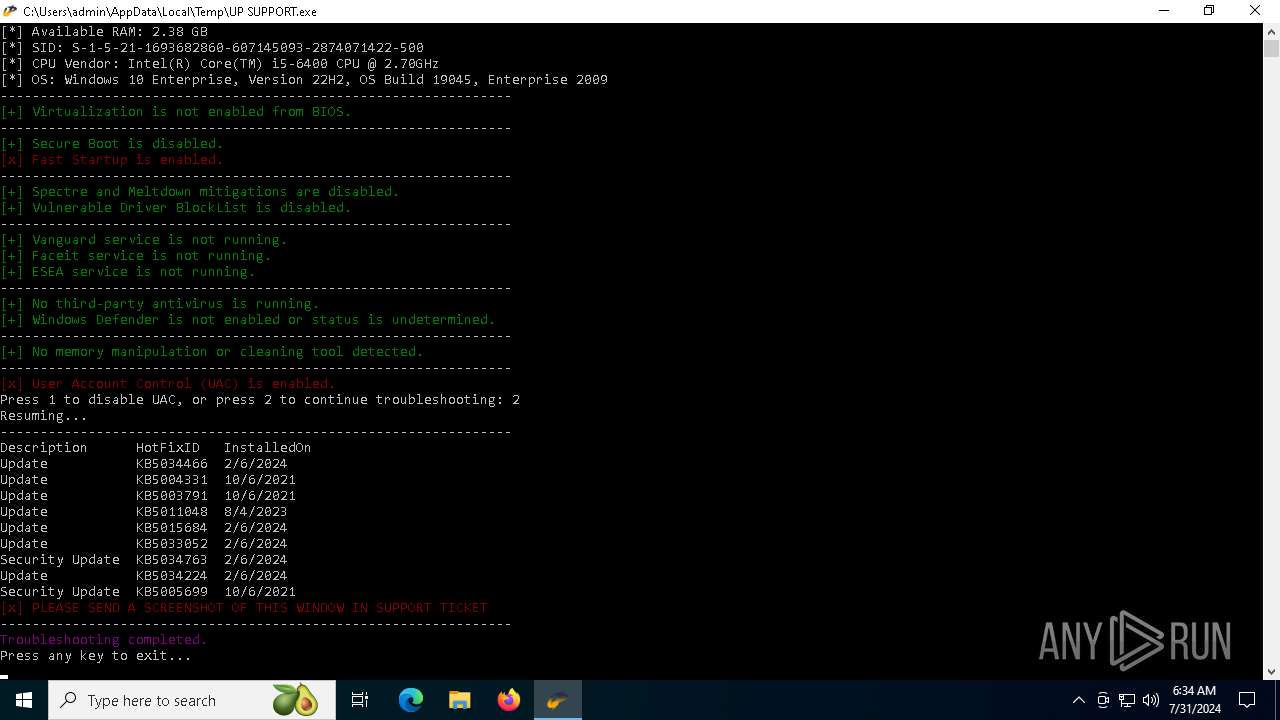
| File name: | UP SUPPORT.exe |
| Full analysis: | https://app.any.run/tasks/95d5c332-c2d3-4df4-a529-367d223635cc |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2024, 06:33:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | A8D48B63386D3597B1337DE0A077AE3A |
| SHA1: | AFCC006CBC523E893142202F7B351199C0B8CEFE |
| SHA256: | 2442260A9B051B994C3EE75FAC2F2DDDE78AD38B6A1E0ABE00A1E02D70E9822E |
| SSDEEP: | 98304:bXDrQ2ErFo+CrrUyMzSvRRyOC2HpaxF3fycPfDmlH4ubCOMGRHgtEdmpVpFJlbkt:Fzh4QHV7iNqN9KJtxLS |
MALICIOUS
Drops the executable file immediately after the start
- UP SUPPORT.exe (PID: 6588)
Antivirus name has been found in the command line (generic signature)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 6388)
SUSPICIOUS
Process drops legitimate windows executable
- UP SUPPORT.exe (PID: 6588)
Process drops python dynamic module
- UP SUPPORT.exe (PID: 6588)
Application launched itself
- UP SUPPORT.exe (PID: 6588)
The process drops C-runtime libraries
- UP SUPPORT.exe (PID: 6588)
Executable content was dropped or overwritten
- UP SUPPORT.exe (PID: 6588)
Loads Python modules
- UP SUPPORT.exe (PID: 1428)
Uses WMIC.EXE to obtain CPU information
- UP SUPPORT.exe (PID: 1428)
Get information on the list of running processes
- UP SUPPORT.exe (PID: 1428)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- UP SUPPORT.exe (PID: 1428)
Starts POWERSHELL.EXE for commands execution
- UP SUPPORT.exe (PID: 1428)
INFO
Checks supported languages
- UP SUPPORT.exe (PID: 6588)
- UP SUPPORT.exe (PID: 1428)
Reads the computer name
- UP SUPPORT.exe (PID: 6588)
- UP SUPPORT.exe (PID: 1428)
Reads the machine GUID from the registry
- UP SUPPORT.exe (PID: 1428)
Create files in a temporary directory
- UP SUPPORT.exe (PID: 6588)
- UP SUPPORT.exe (PID: 1428)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6396)
- powershell.exe (PID: 7064)
- powershell.exe (PID: 1560)
- powershell.exe (PID: 5696)
- powershell.exe (PID: 6320)
- powershell.exe (PID: 3848)
- powershell.exe (PID: 4496)
- powershell.exe (PID: 3472)
- powershell.exe (PID: 6220)
- powershell.exe (PID: 2188)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 6684)
PyInstaller has been detected (YARA)
- UP SUPPORT.exe (PID: 1428)
- UP SUPPORT.exe (PID: 6588)
Process checks whether UAC notifications are on
- UP SUPPORT.exe (PID: 1428)
Reads the software policy settings
- slui.exe (PID: 4580)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2748)
- WMIC.exe (PID: 3516)
Checks proxy server information
- slui.exe (PID: 4580)
- UP SUPPORT.exe (PID: 1428)
Reads Environment values
- UP SUPPORT.exe (PID: 1428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:10 09:46:14+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 156672 |
| InitializedDataSize: | 183808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa80 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Total processes
164
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | "C:\Users\admin\AppData\Local\Temp\UP SUPPORT.exe" | C:\Users\admin\AppData\Local\Temp\UP SUPPORT.exe | UP SUPPORT.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1560 | powershell.exe "Get-Service -Name vgc" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | powershell.exe Get-Process -name avgsvc.exe | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2708 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2748 | wmic qfe get Description,HotFixID,InstalledOn | C:\Windows\SysWOW64\wbem\WMIC.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3472 | powershell.exe Get-Process -name avp.exe | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3516 | wmic cpu get name,MaxClockSpeed /format:list | C:\Windows\SysWOW64\wbem\WMIC.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | powershell.exe "Get-Service -Name faceit" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3948 | powershell.exe "Test-Path -Path 'HKLM:\SOFTWARE\Microsoft\Windows NT\CurrentVersion\VulnerableDriverBlocklist'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4288 | powershell.exe "Get-ItemPropertyValue -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\Session Manager\Power' -Name 'HiberbootEnabled'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | UP SUPPORT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
69 663
Read events
69 660
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6872) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SideBySide |
| Operation: | write | Name: | LastScavengingStarvationReport |
Value: 4AF3F5B513E3DA01 | |||
| (PID) Process: | (6872) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31122195 | |||
| (PID) Process: | (6872) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
Executable files
28
Suspicious files
2
Text files
32
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\_queue.pyd | executable | |
MD5:BCF5440A884EF33DF02CE124557D0C2C | SHA256:2F2F30A6B697B7BA7C09DB16EC04517C85CDFAB13F142B9C810FDF9983522129 | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\Pythonwin\win32ui.pyd | executable | |
MD5:9A206178DC7E2A6CE185553245A3325D | SHA256:00EA5C2866A682627651B7883F80854748D7B7EE4F6C6B6D7B4ADF4D01DC4652 | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\_elementtree.pyd | executable | |
MD5:2E0C1916BBCB6362B92C5A1DDB7269DB | SHA256:86A5BF9C4A462FDD4F211E9CFE56285B28A72F673FFCCE40D5FEC19436DF265E | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\base_library.zip | compressed | |
MD5:04477665AB94518973A3996E48DDB91D | SHA256:0156B61FDBD087D7DB99D250280DDDE7F714065BF487BBB4C6F748521A52248C | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\_bz2.pyd | executable | |
MD5:852CAC1AC7232C5788CBA284C3122347 | SHA256:94D02CBCFAC3141CA0107253050D7B9D809FEA04B42964142BED3F090783A26A | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\_ctypes.pyd | executable | |
MD5:36BF6FFD59C04075D50F245EF5DE2AB9 | SHA256:7C11A5B8CBAEB0CD34544A7E4949C1B2A61CC78392C0155C0156306E6FF602E0 | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\_socket.pyd | executable | |
MD5:F7D2FE8CDDEDED1210B06AF09B0FAD3C | SHA256:C56088832A09820ABFD45135AC3874117D0CFE669E982314FDC3FE73CA195DEE | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\Pythonwin\mfc140u.dll | executable | |
MD5:E76B52D11DB435D36453D26C8B446A8F | SHA256:E422C9366A53536A35E307EF301F08661C28C29B7FCDA1B454333C6A41C6BB21 | |||
| 6588 | UP SUPPORT.exe | C:\Users\admin\AppData\Local\Temp\_MEI65882\_hashlib.pyd | executable | |
MD5:9AA769EFAC1446DB1D2E4E1C39500A20 | SHA256:DE7C71C90C7F58DCDC3DA159D08DDA7DC297E39C5F309849290238BAED7E230F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
44
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
3076 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5464 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.23.209.136:443 | www.bing.com | Akamai International B.V. | GB | unknown |
4032 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4340 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 131.253.33.254:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6672 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
httpbin.org |
| shared |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |