| File name: | 7.hta |
| Full analysis: | https://app.any.run/tasks/7d10f089-bafa-4dff-8359-e6509ce6a726 |
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2019, 06:28:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 78B20AB8BF674F2583C4652EF14941F1 |
| SHA1: | 946CBAF2B40C96A76B0E9ACDEE0FE947760C9E85 |
| SHA256: | 2441E921CB5C605963C469050B904571165E0CBAC70D81FD1054990AB2D53ECA |
| SSDEEP: | 24:p37rysGWgjN9TLk/4TolcTCTVcxBOU9m9TnG10ti8uZLR/1S:pf1GVN9Hkq4mCTVPtGitNuFR/E |
MALICIOUS
Changes settings of System certificates
- mshta.exe (PID: 1360)
SUSPICIOUS
Adds / modifies Windows certificates
- mshta.exe (PID: 1360)
Creates files in the user directory
- mshta.exe (PID: 1360)
INFO
Reads internet explorer settings
- mshta.exe (PID: 1360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
32
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1360 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\7.hta" | C:\Windows\System32\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
126
Read events
104
Write events
20
Delete events
2
Modification events
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 0F000000010000001400000085FEF11B4F47FE3952F98301C9F98976FEFEE0CE09000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030353000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C01400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB5748501D00000001000000100000005B3B67000EEB80022E42605B6B3B72400B000000010000000E000000740068006100770074006500000003000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B812000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1360) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 190000000100000010000000DC73F9B71E16D51D26527D32B11A6A3D09000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030353000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C01400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB5748501D00000001000000100000005B3B67000EEB80022E42605B6B3B72400B000000010000000E000000740068006100770074006500000003000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B812000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
Executable files
0
Suspicious files
0
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1360 | mshta.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@wm.makeding[2].txt | — | |
MD5:— | SHA256:— | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\gtm[1].js | text | |
MD5:E894F9C95CEA482A673C65432239A4B0 | SHA256:1F0DC8F692D4A141746E81EFE978F78DBE1E407715FEEC5BAE3A27B106A16BC1 | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@wm.makeding[1].txt | text | |
MD5:51E3D247C781295302363015358C7DE3 | SHA256:227E1A5140C8116D22DD5365A50986A34AD12C197AEDEFF2BADBD09989623851 | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\shutdown[1].php | html | |
MD5:1A72C265E768FDC4D18E34F30C8D7447 | SHA256:54872F71945394A90A7C3A22C9A453EE4F4250437375276C3EAC22A813B00AEB | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\iclk[1].txt | html | |
MD5:752BD445940C9D8F45C0E410ABFA3317 | SHA256:0F5184AB97380D4A9FE177865ADCE1E293C95AB018A87A7BB72E509950FDD35C | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | image | |
MD5:54914D778FE90D75DEA6F56520A9118B | SHA256:66A01E7F4EBDAD4485E539A243EE685EF1F02D3869E1676881923F76108CB44B | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\insight.min[1].js | text | |
MD5:AA45F2757AA370D353DC4E4A859B2891 | SHA256:BC9CEF10D07E8DA3CE80181DE07A056414731F86E0DC12E2C81D652B28AC770B | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\error[1].aspx | html | |
MD5:7618AF02D84CAFC284C32E1F05092A7B | SHA256:C381D82C58FA45999F5B69ED04A08A0EA9E12712A03FCF8D9412D48DBD76476C | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\error[1] | text | |
MD5:35FE91C2AC1BA0913CC617622B9EB43F | SHA256:966240C0527B20E8E2553B7E5A68594AE69230AA00186F2C6C2C342405494837 | |||
| 1360 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\TvGoogleAnalytics[1].js | text | |
MD5:D7499F67114361AFCDE92BC347B2A729 | SHA256:37A185906236377FAA672B912CF29E759EC186D9D7273F97A49909F621F58F3C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
9
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
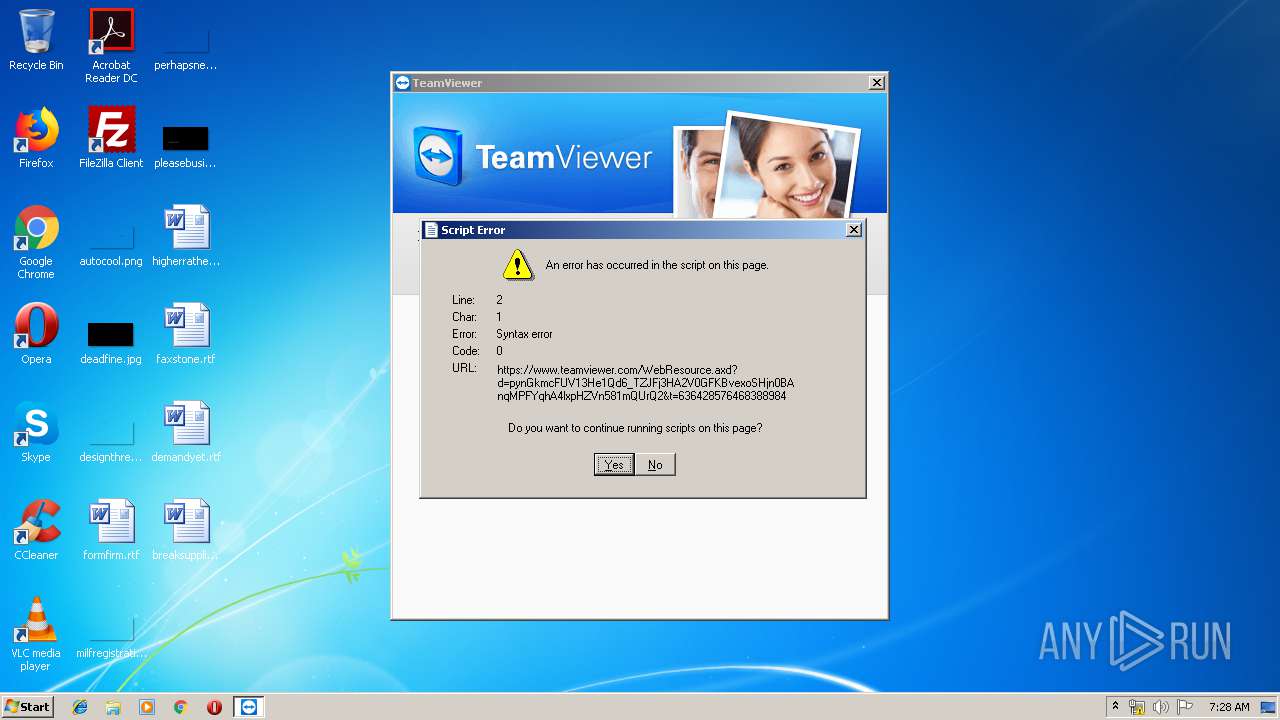
1360 | mshta.exe | GET | 301 | 143.204.207.172:80 | http://www.teamviewer.com/favicon.ico | US | html | 183 b | shared |
1360 | mshta.exe | GET | 200 | 106.75.80.169:80 | http://wm.makeding.com/iclk/?zoneid=22680&ref=wm&pid=1357&version=13.1.3629&os=win | CN | html | 522 b | malicious |
1360 | mshta.exe | GET | 302 | 106.75.80.169:80 | http://wm.makeding.com/redirect/url?segment=VzT4eX1GL7VX0-Ll0AxcR3ECLSiPlmt_4GTG0eIYRPV4dgS01pjr4PqE4P-Yefxmm-WYR2Zw2V59sHI4RU_kWlNr-tsyVUXfzKGAUav5fBv5meaEVRjqyr1OgeuTrAp09qfgVFaqq8TVknTW1cUarRehhIsAAM93cFqXUWUWHPfsIdBMRIw1LBv6o8f0kbMpIzSmTolc1LiwitZoOSwM1XpUZCgDfurX4XCR6j0xsWNWyrAomb0I7-6zbr2KYqsKBra5BjHBdJIEsPME-Cccej6ZEhO4zBHiEL_8EPzFWa8&utm_medium=wm&utm_source=wm.makeding.com&utm_content=Teamviewer%E8%BF%9C%E7%A8%8B%E6%8E%A7%E5%88%B6-win-&utm_campaign=LM&utm_term=Janetwo | CN | compressed | 522 b | malicious |
1360 | mshta.exe | GET | 200 | 106.75.60.242:80 | http://www.yuanchengxiezuo.com/shutdown.php?&utm_medium=wm&utm_source=wm.makeding.com&utm_content=Teamviewer%E8%BF%9C%E7%A8%8B%E6%8E%A7%E5%88%B6-win-&utm_campaign=LM&utm_term=Janetwo | CN | html | 11.7 Kb | unknown |
1360 | mshta.exe | GET | 200 | 106.75.60.242:80 | http://www.yuanchengxiezuo.com/res/img/shutdown-bg.png | CN | image | 21.3 Kb | unknown |
1360 | mshta.exe | GET | 200 | 23.43.114.192:80 | http://js.bizographics.com/insight.min.js | NL | text | 4.46 Kb | whitelisted |
1360 | mshta.exe | GET | 301 | 107.150.125.127:80 | http://pro.softgostop.com/api.php?page=shutdown&ref=wm&pid=1357&version=13.1.3629&os=win | US | — | — | unknown |
1360 | mshta.exe | GET | 200 | 172.217.16.200:80 | http://www.googletagmanager.com/gtm.js?id=GTM-5R286M | US | text | 69.7 Kb | whitelisted |
1360 | mshta.exe | GET | 200 | 216.58.206.14:80 | http://www.google-analytics.com/analytics.js | US | text | 17.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1360 | mshta.exe | 143.204.207.172:80 | www.teamviewer.com | — | US | unknown |
1360 | mshta.exe | 143.204.207.172:443 | www.teamviewer.com | — | US | unknown |
1360 | mshta.exe | 107.150.125.127:80 | pro.softgostop.com | Shanghai UCloud Information Technology Company Limited | US | unknown |
1360 | mshta.exe | 106.75.80.169:80 | wm.makeding.com | China Unicom Beijing Province Network | CN | malicious |
1360 | mshta.exe | 106.75.60.242:80 | www.yuanchengxiezuo.com | China Unicom Beijing Province Network | CN | unknown |
1360 | mshta.exe | 172.217.16.200:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1360 | mshta.exe | 216.58.206.14:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
1360 | mshta.exe | 23.43.114.192:80 | js.bizographics.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.teamviewer.com |
| shared |
pro.softgostop.com |
| unknown |
wm.makeding.com |
| malicious |
www.yuanchengxiezuo.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
js.bizographics.com |
| whitelisted |