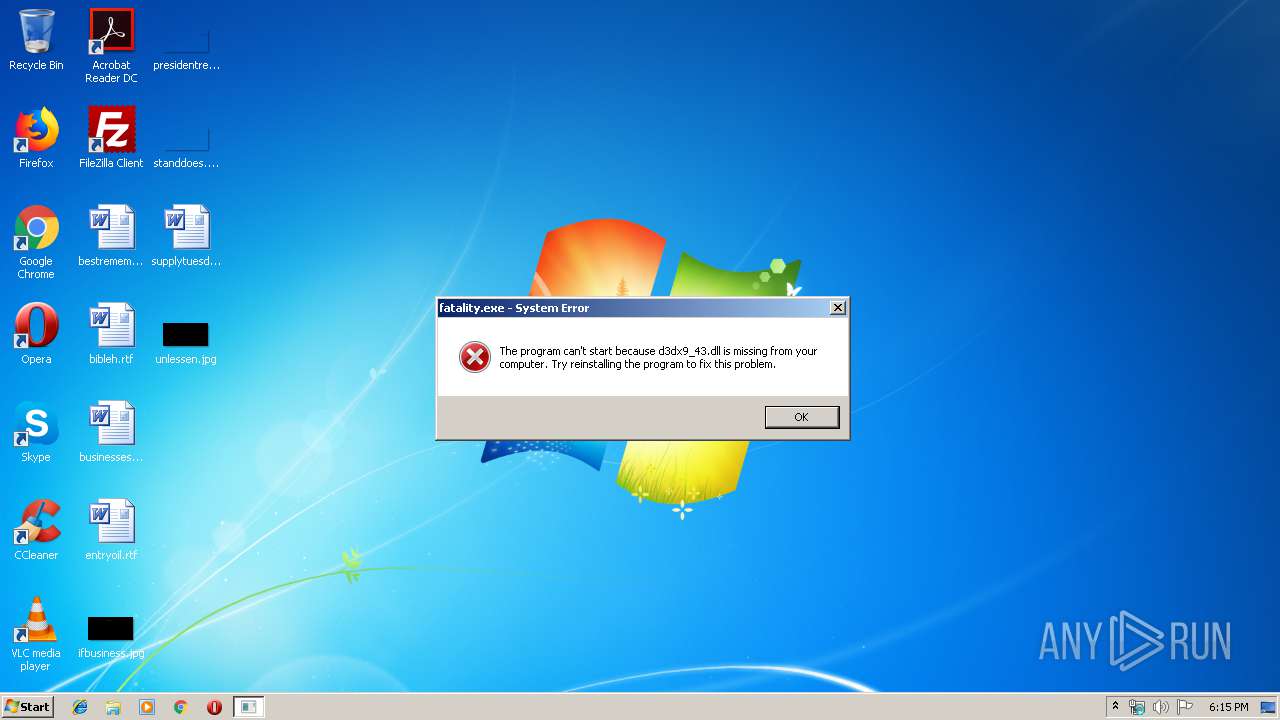
| File name: | fatality.exe |
| Full analysis: | https://app.any.run/tasks/9da0a26d-be5a-49ec-b009-cc0da151fbbe |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 18:15:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 11F6EFB617B6E565BBA9E647FA37E95B |
| SHA1: | 753049F9781F4D83607FDFF084D5C8F2CA683F39 |
| SHA256: | 242D7CD868BD4E7F34E73F1272CE9F4E3E99FD2D6DA4922394978F2B8D2ED824 |
| SSDEEP: | 49152:ztOdw9D/PQ0vkpKUjLKZyICW7D0C2LZrufVX:xOdmDg0eNj/IXw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2168)
INFO
Application launched itself
- chrome.exe (PID: 2168)
Manual execution by user
- chrome.exe (PID: 2168)
Reads the hosts file
- chrome.exe (PID: 2168)
- chrome.exe (PID: 1800)
Reads settings of System Certificates
- chrome.exe (PID: 1800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:23 17:26:18+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1079296 |
| InitializedDataSize: | 976896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3e221 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Feb-2019 16:26:18 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 23-Feb-2019 16:26:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00107722 | 0x00107800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51652 |
.rdata | 0x00109000 | 0x00070344 | 0x00070400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.32645 |
.data | 0x0017A000 | 0x00057910 | 0x00052C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.80584 |
.00cfg | 0x001D2000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0611629 |
.gfids | 0x001D3000 | 0x00000058 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.435639 |
.tls | 0x001D4000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x001D5000 | 0x0001C160 | 0x0001C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54944 |
.reloc | 0x001F2000 | 0x0000EF5C | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68302 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.69958 | 334 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.76538 | 67624 | UNKNOWN | German - Germany | RT_ICON |
3 | 3.8266 | 16936 | UNKNOWN | German - Germany | RT_ICON |
4 | 3.94476 | 9640 | UNKNOWN | German - Germany | RT_ICON |
5 | 4.10881 | 4264 | UNKNOWN | German - Germany | RT_ICON |
6 | 4.30067 | 1128 | UNKNOWN | German - Germany | RT_ICON |
102 | 2.79908 | 90 | UNKNOWN | German - Germany | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSVCP140.dll |
USER32.dll |
VCRUNTIME140.dll |
WINTRUST.dll |
WS2_32.dll |
Total processes
72
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6434481099006836693 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14964010623690755800 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9997202706193504756 --mojo-platform-channel-handle=4372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2410946731587995872 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5308759539298970684 --mojo-platform-channel-handle=4732 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5603551946680445479 --mojo-platform-channel-handle=4360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14962338739634104364 --mojo-platform-channel-handle=4664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17174654548997669831 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17629576601380878567 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,10977099621789015778,16935790807774845797,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15750567197549297208 --mojo-platform-channel-handle=3624 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
202
Read events
137
Write events
61
Delete events
4
Modification events
| (PID) Process: | (2152) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2168-13219784157793500 |
Value: 259 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
35
Text files
173
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\401d3a6e-7bcb-4e7d-8fae-1f4f1980dff9.tmp | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3a0bfc.TMP | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF3a0c4a.TMP | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3a0bec.TMP | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
37
DNS requests
25
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
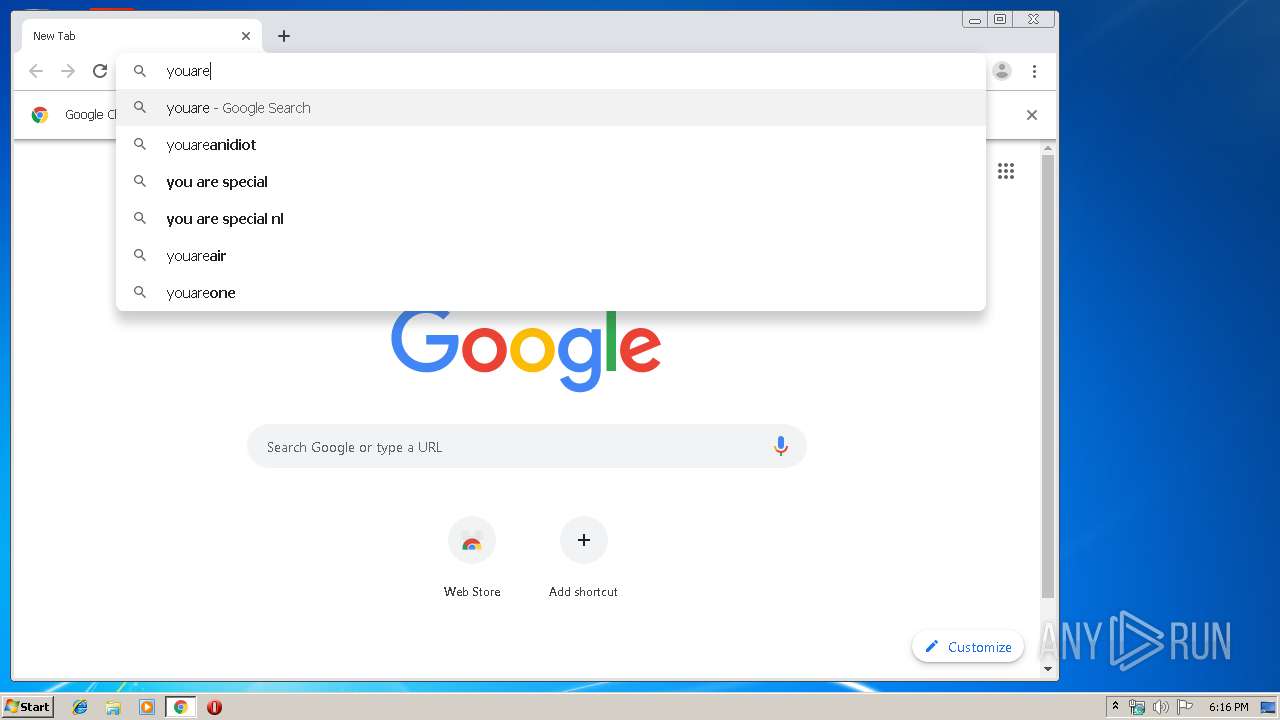
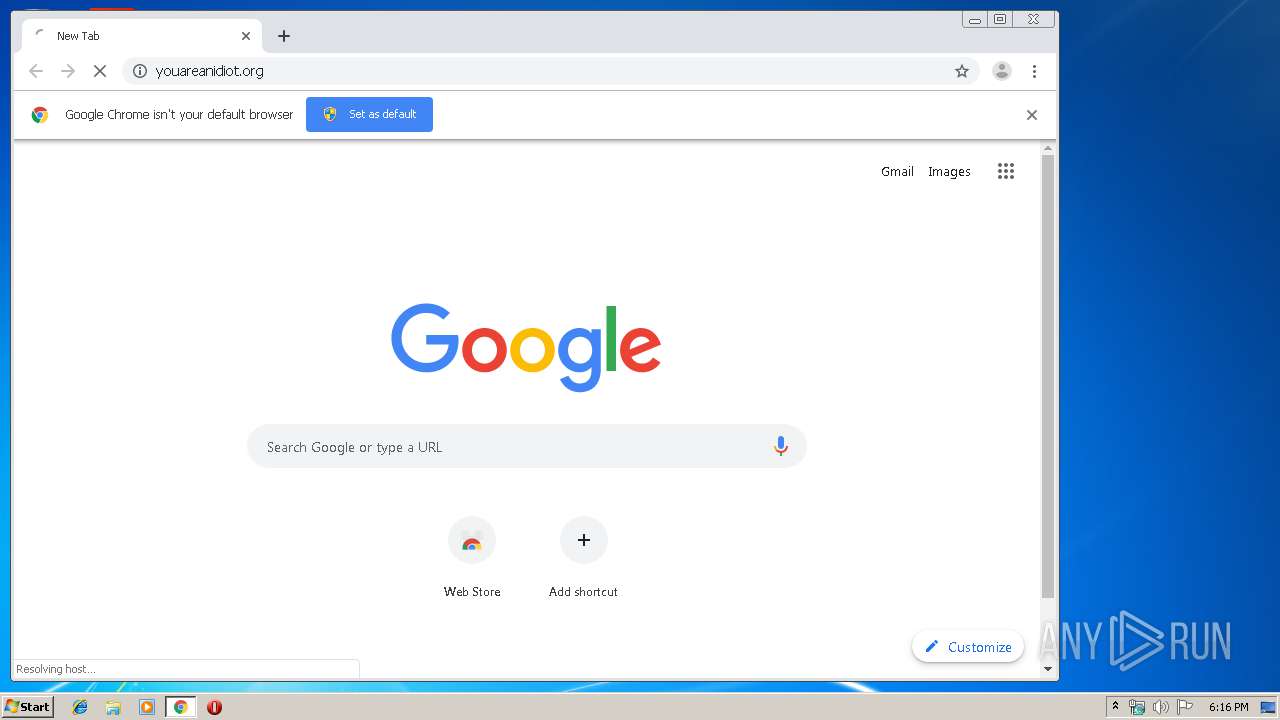
1800 | chrome.exe | GET | 302 | 67.227.226.240:80 | http://youareanidiot.org/ | US | — | — | malicious |
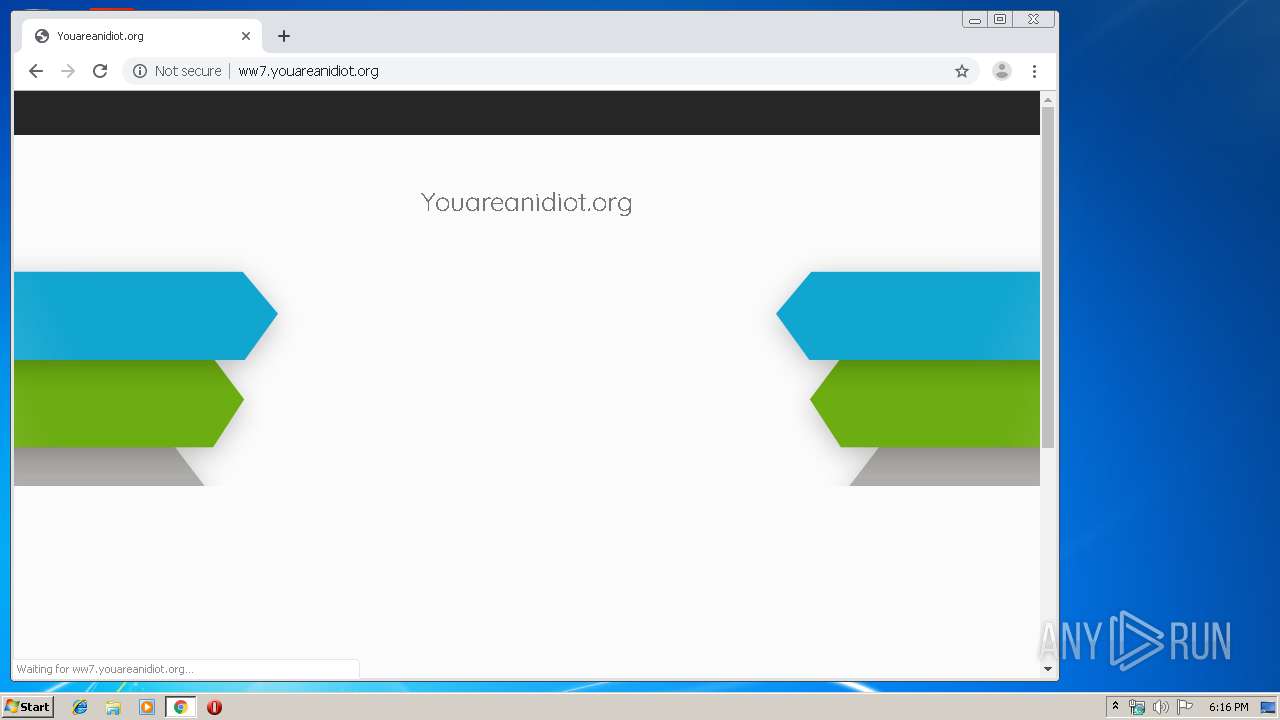
1800 | chrome.exe | GET | 404 | 199.59.242.153:80 | http://ww7.youareanidiot.org/favicon.ico | US | html | 3.93 Kb | whitelisted |
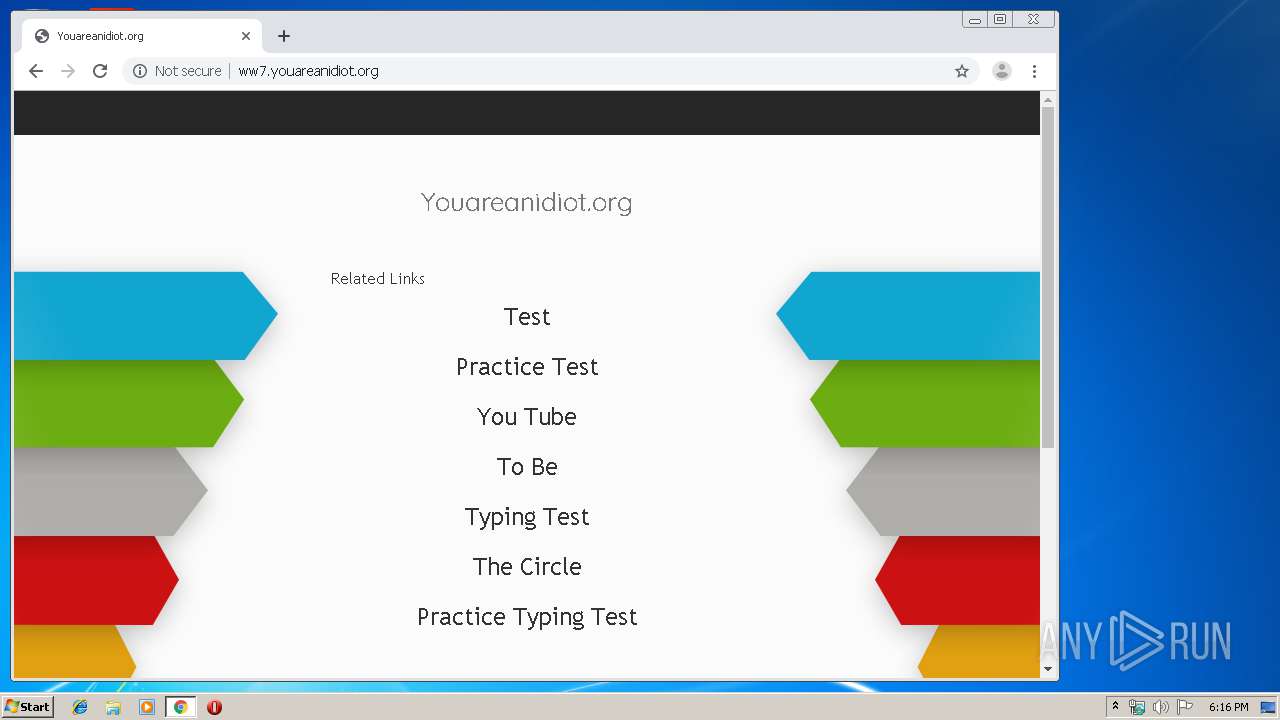
1800 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.youareanidiot.org/ | US | html | 3.93 Kb | whitelisted |
1800 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.youareanidiot.org/glp?r=&u=http%3A%2F%2Fww7.youareanidiot.org%2F&rw=1280&rh=720&ww=1042&wh=539 | US | text | 9.64 Kb | whitelisted |
1800 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.youareanidiot.org/public/legacy/10350/resources/arrows-bg-ext.png | US | image | 1.12 Kb | whitelisted |
1800 | chrome.exe | GET | 200 | 199.59.242.155:80 | http://tracking.bodis.com/tlpv?d=eyJkb21haW5fbmFtZSI6InlvdWFyZWFuaWRpb3Qub3JnIiwic2VydmVyIjo5MSwidGVybXMiOltdLCJVUkwiOiJodHRwOlwvXC93dzcueW91YXJlYW5pZGlvdC5vcmdcLyIsInJlZmVycmVyIjoiIiwiZHciOjEwNDIsImRoIjo1MzksInJ3IjoxMjgwLCJyaCI6NzIwfQ&t=1575310568&abp=0 | US | — | — | whitelisted |
1800 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
1800 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.youareanidiot.org/px.gif?ch=2&rn=1.3818520355252892 | US | image | 42 b | whitelisted |
1800 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww7.youareanidiot.org/public/legacy/10350/resources/arrows-bg.jpg | US | image | 93.6 Kb | whitelisted |
1800 | chrome.exe | GET | 200 | 172.217.16.195:80 | http://www.gstatic.com/domainads/tracking/caf.gif?ts=1575310568185&rid=1082062 | US | image | 43 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1800 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1800 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1800 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1800 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
1800 | chrome.exe | 172.217.22.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1800 | chrome.exe | 172.217.21.206:443 | apis.google.com | Google Inc. | US | whitelisted |
1800 | chrome.exe | 216.58.205.238:443 | ogs.google.com | Google Inc. | US | whitelisted |
1800 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 195.95.178.175:80 | r4---sn-pouxga5o-vu2s.gvt1.com | Asociatia Interlan | RO | whitelisted |
1800 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
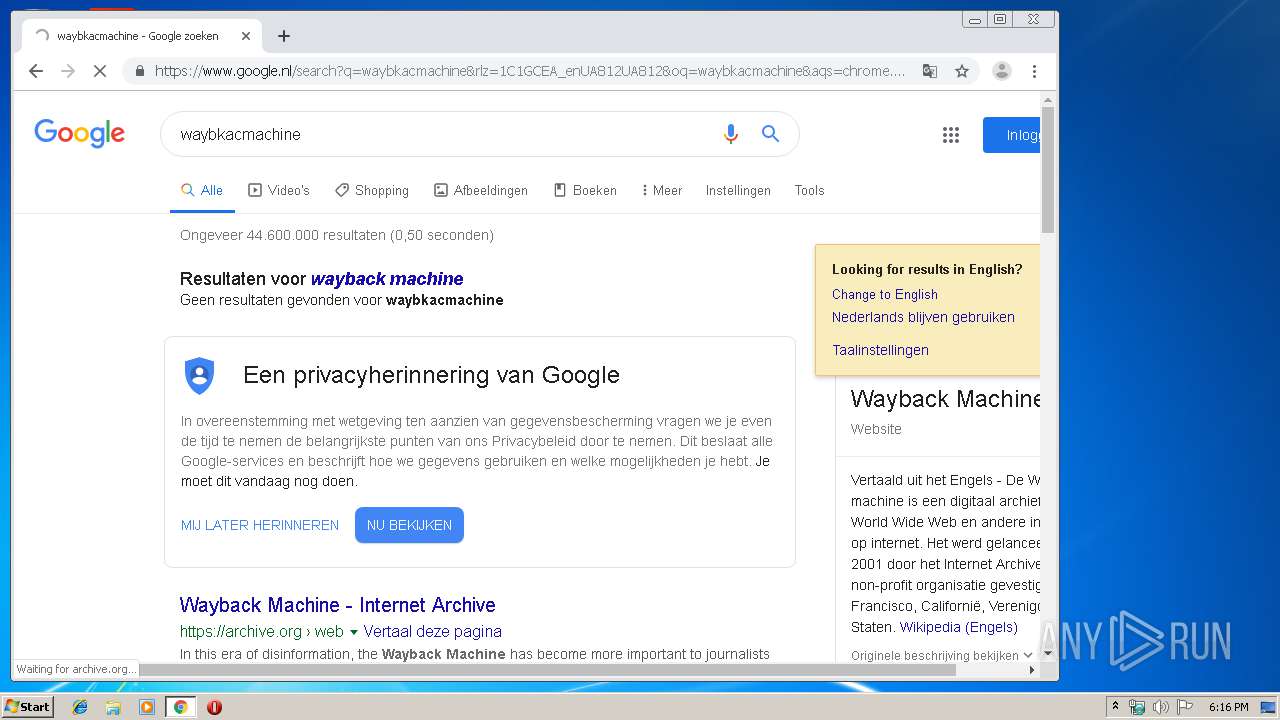
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1800 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |