| File name: | File-Explorer.ps1 |
| Full analysis: | https://app.any.run/tasks/3c0f5cd4-2ad3-4eb5-aa4c-0b9ffc1a9fba |
| Verdict: | Malicious activity |
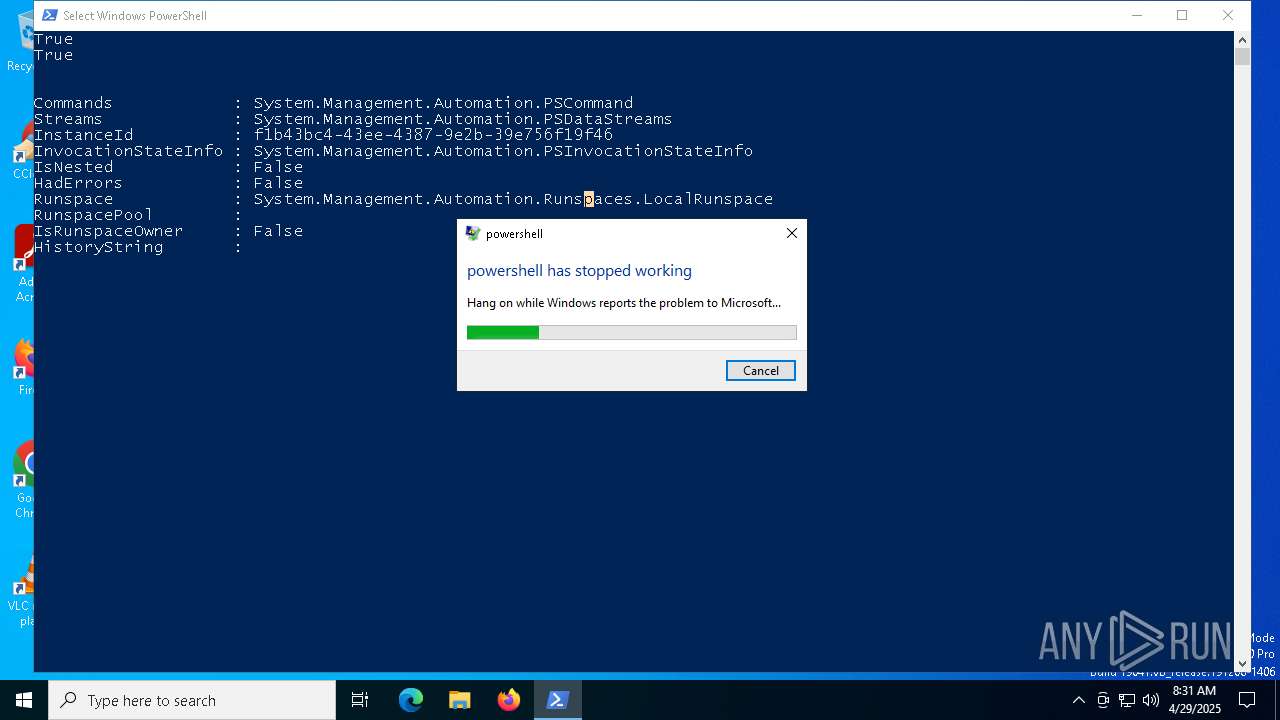
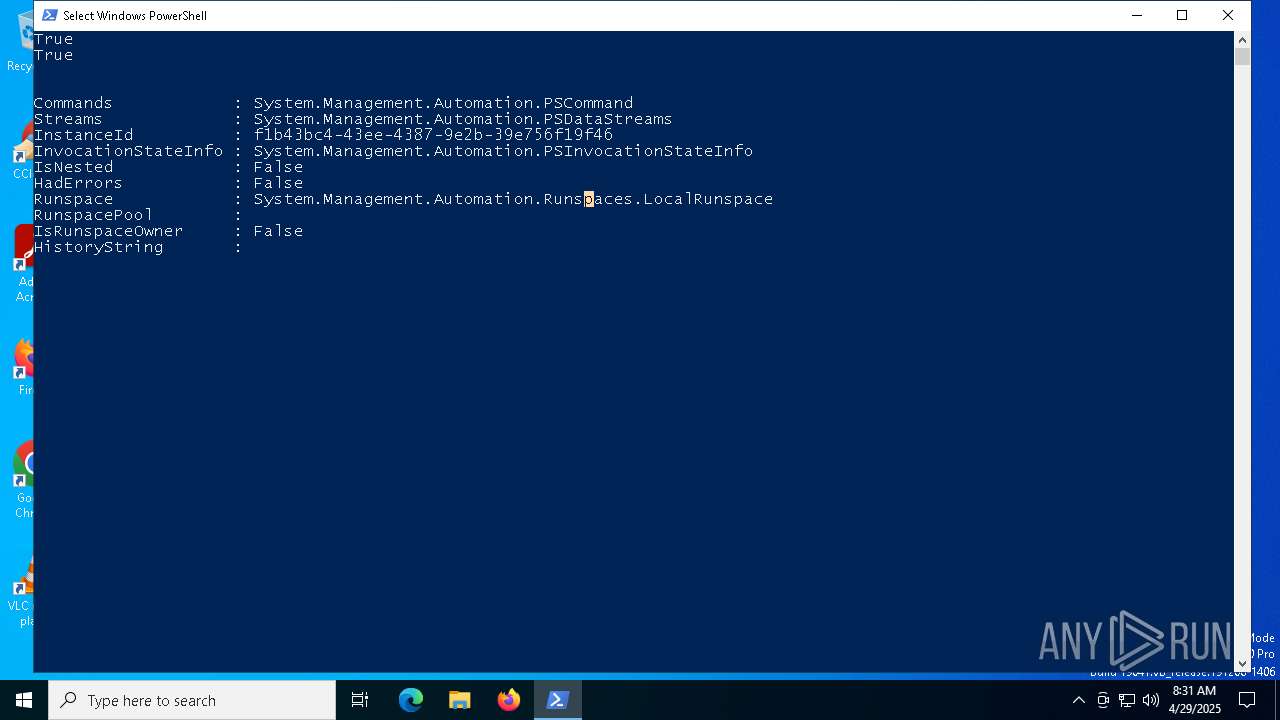
| Analysis date: | April 29, 2025, 08:31:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Non-ISO extended-ASCII text, with very long lines (14774), with CRLF line terminators |
| MD5: | 071224D43822D66F437E9F4283B98E2B |
| SHA1: | 1EC891153CCF49846EE67D210B29BC8FCCD70AB7 |
| SHA256: | 242B3487C5FB3A2FE27A1133D79F9E0BB32AC4BDC15FE00B29FFE175920C11C2 |
| SSDEEP: | 192:bGz6I62RXvOczTtwFzgn/ULMQdGWLGvCbJJWlCsHghHKzL/3P41+4lTM:a+n2NvZqFcn/ULMQd1GuJeFAhwD3PcM |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7012)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7012)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7012)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7012)
Connects to the server without a host name
- powershell.exe (PID: 7012)
CSC.EXE is used to compile C# code
- csc.exe (PID: 2108)
Executable content was dropped or overwritten
- csc.exe (PID: 2108)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 7012)
The process creates files with name similar to system file names
- wermgr.exe (PID: 1180)
INFO
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7012)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7012)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7012)
Disables trace logs
- powershell.exe (PID: 7012)
Checks proxy server information
- powershell.exe (PID: 7012)
- wermgr.exe (PID: 1180)
Reads the machine GUID from the registry
- csc.exe (PID: 2108)
Checks supported languages
- csc.exe (PID: 2108)
- cvtres.exe (PID: 6640)
Create files in a temporary directory
- cvtres.exe (PID: 6640)
- csc.exe (PID: 2108)
Creates files or folders in the user directory
- wermgr.exe (PID: 1180)
Reads the software policy settings
- wermgr.exe (PID: 1180)
- slui.exe (PID: 3100)
Creates files in the program directory
- powershell.exe (PID: 7012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
138
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "7012" "3220" "3180" "3296" "0" "0" "3300" "0" "0" "0" "0" "0" | C:\Windows\System32\wermgr.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ab1xisev.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5304 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES76F.tmp" "c:\Users\admin\AppData\Local\Temp\CSCD870432FA624F9988966DED8DDF415.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 7012 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\File-Explorer.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 949
Read events
11 949
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
11
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1180 | wermgr.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\Critical_powershell.exe_d52d907383af593b633a47addd4b79917e9947_00000000_93dc101b-b75b-4eca-9407-b7b3af3d885c\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10bb43.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:4123F9153C363995F046A942C9C249B9 | SHA256:0FAF31B94D14620203FA94A0ACDEA2C5A0197A5387513F06517FF71D78F96EDA | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OJR7HNWMCBO6ZR5WTLQ9.temp | binary | |
MD5:4123F9153C363995F046A942C9C249B9 | SHA256:0FAF31B94D14620203FA94A0ACDEA2C5A0197A5387513F06517FF71D78F96EDA | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zfqgmhuy.qix.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_awjy2t2u.fyn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ab1xisev.cmdline | text | |
MD5:FFEE56227929AE7E0FB44DEAC936BD35 | SHA256:C9C77DD5B58E7870509799AFA63EAE73D7C5438B71ED1E4EE3998E48315AB9B4 | |||
| 2108 | csc.exe | C:\Users\admin\AppData\Local\Temp\ab1xisev.out | text | |
MD5:2F1233895C5F705F57A1116A453C2288 | SHA256:A2B842B2A0E57EF9CDD87452B2FEF31DD7C3F2D2AB955AE2864D417669FFB682 | |||
| 6640 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES76F.tmp | binary | |
MD5:57E2FC3BA02F1372242F3AF8E0FACC79 | SHA256:BA8348734DEFA6D6AD102B26295806A308FB9F153170AAB6080F4F298FE7767A | |||
| 2108 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCD870432FA624F9988966DED8DDF415.TMP | binary | |
MD5:A881EC48A4C26B77358445922F0E47D0 | SHA256:2B63DB27F91E2F984A59DBE1A2F52C84E0857320FBB46E90308B5656F36B8CBD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
27
DNS requests
17
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7012 | powershell.exe | GET | 200 | 45.15.162.16:80 | http://45.15.162.16/Windows.txt | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1672 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7012 | powershell.exe | GET | 200 | 45.15.162.16:80 | http://45.15.162.16/System.txt | unknown | — | — | malicious |
1672 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1180 | wermgr.exe | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1180 | wermgr.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.29:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7012 | powershell.exe | 45.15.162.16:80 | — | DEDIPATH-LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7012 | powershell.exe | Misc activity | ET INFO Powershell Base64 Decode Command Inbound |
7012 | powershell.exe | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell Base64 Encoded Content Command Common In Powershell Stagers M2 |
7012 | powershell.exe | Misc activity | ET HUNTING EXE Base64 Encoded potential malware |
7012 | powershell.exe | A Network Trojan was detected | ET MALWARE Windows executable base64 encoded |