| File name: | e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.zip |
| Full analysis: | https://app.any.run/tasks/5433fba7-4dba-44e8-b3cd-0a78d7c6c7ff |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | September 16, 2024, 12:59:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
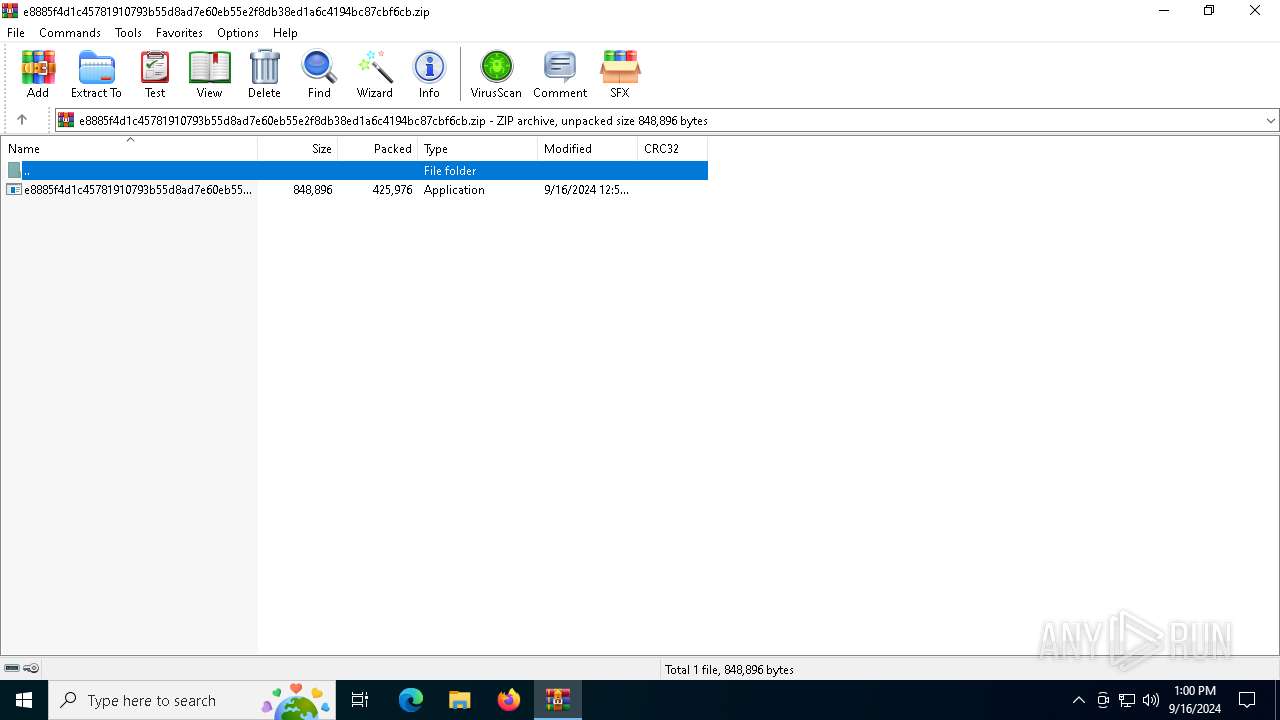
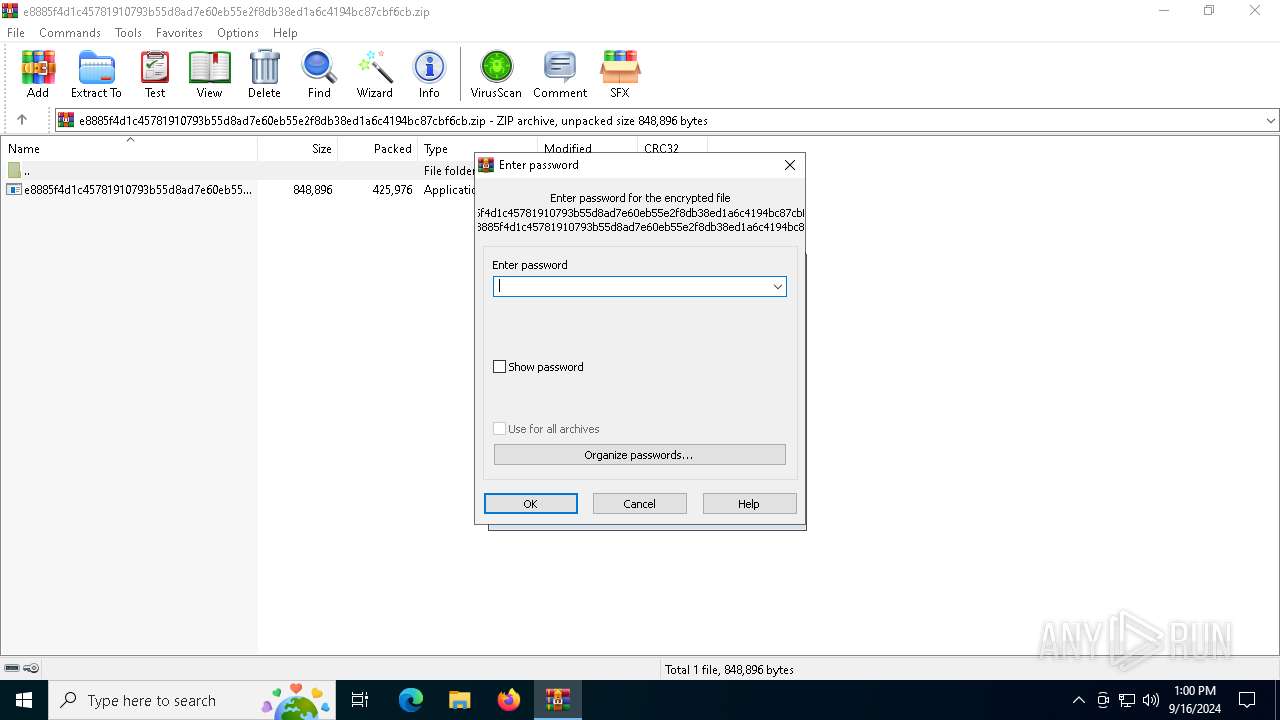
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | DD902C695AF38742BEA64A384C1DD5AE |
| SHA1: | A803ECFF2D9D8CD70A195A7A3581C6A79026BD11 |
| SHA256: | 241FCA6830D9995E8C58E95773DEF1760472C7618CD5F64A7FE10FEA49284B80 |
| SSDEEP: | 12288:h3Wdrr9zMOGcRbcPDw1xgWuRHnIy8vVA/8WQ6+YgWLrhvoDfJnJp7YLpX539:urr9zMOGcRgPDw1xg1RHnD8vVA/8WQ69 |
MALICIOUS
DARKCRYSTAL has been detected (SURICATA)
- ApplicationFrameHost.exe (PID: 7068)
SUSPICIOUS
Executable content was dropped or overwritten
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
Executed via WMI
- schtasks.exe (PID: 892)
- schtasks.exe (PID: 2040)
- schtasks.exe (PID: 1992)
- schtasks.exe (PID: 6848)
- schtasks.exe (PID: 2096)
- schtasks.exe (PID: 888)
- schtasks.exe (PID: 6372)
- schtasks.exe (PID: 3140)
- schtasks.exe (PID: 5888)
- schtasks.exe (PID: 4080)
- schtasks.exe (PID: 7088)
- schtasks.exe (PID: 7024)
- schtasks.exe (PID: 4088)
- schtasks.exe (PID: 4976)
- schtasks.exe (PID: 2112)
- schtasks.exe (PID: 2264)
- schtasks.exe (PID: 1288)
- schtasks.exe (PID: 6204)
- schtasks.exe (PID: 6432)
- schtasks.exe (PID: 6852)
- schtasks.exe (PID: 5044)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 6372)
- schtasks.exe (PID: 3140)
- schtasks.exe (PID: 5044)
The process creates files with name similar to system file names
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
Starts itself from another location
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
Reads security settings of Internet Explorer
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
Reads the date of Windows installation
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
INFO
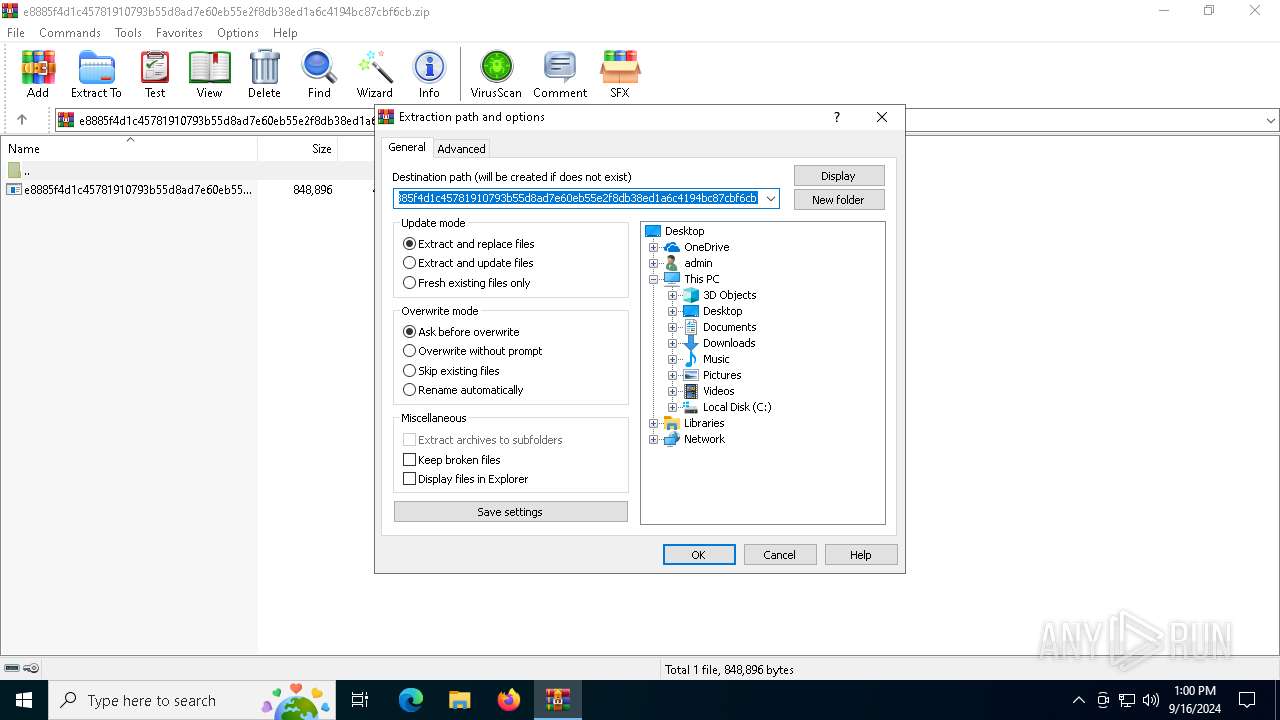
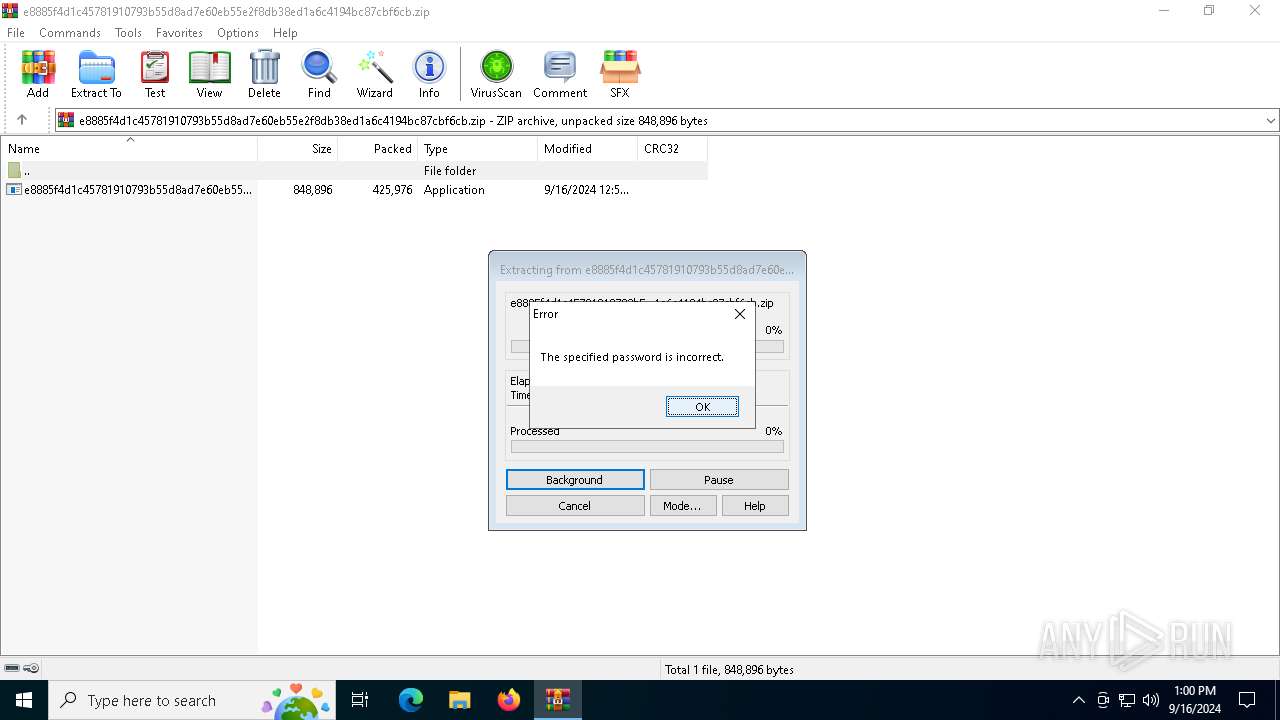
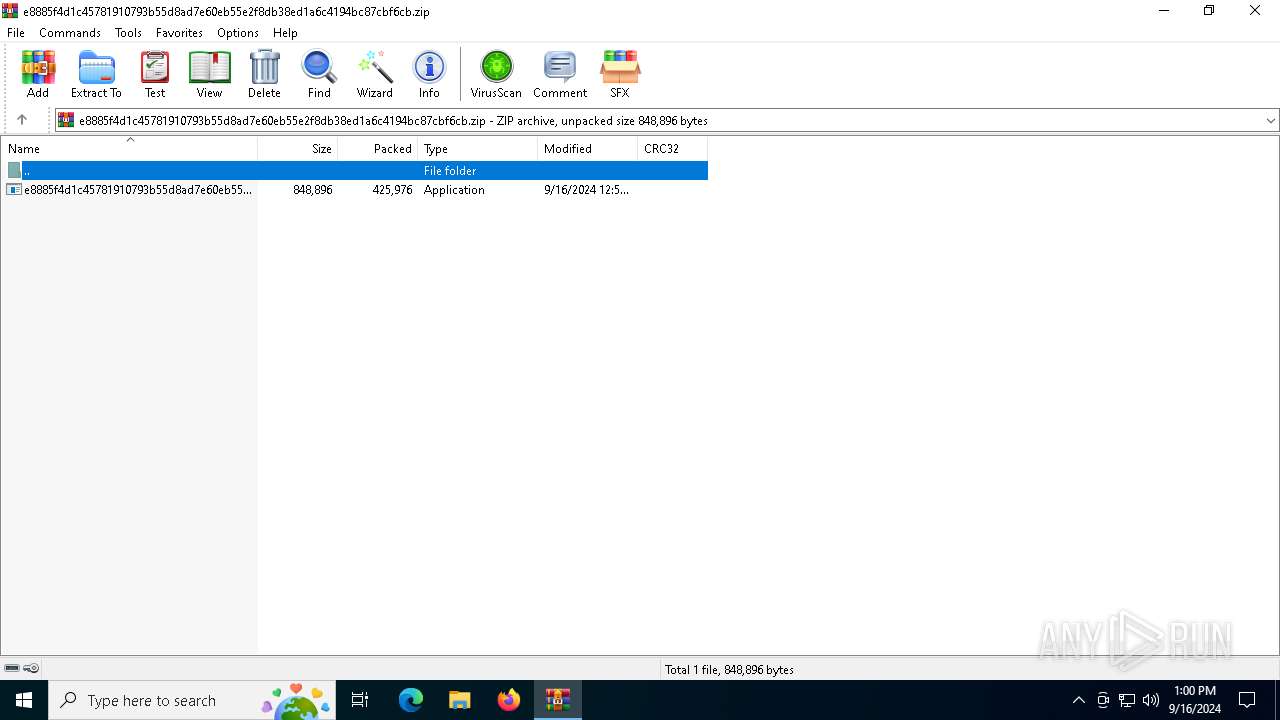
The process uses the downloaded file
- WinRAR.exe (PID: 5000)
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5000)
Manual execution by a user
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
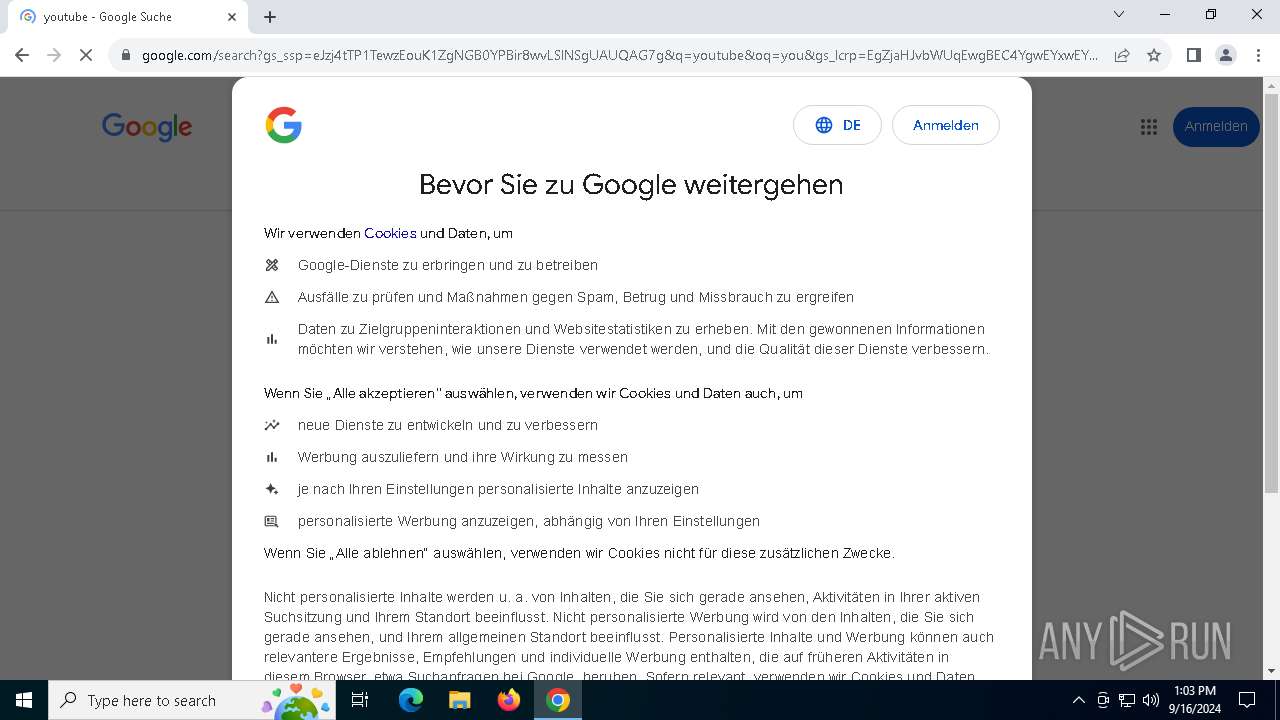
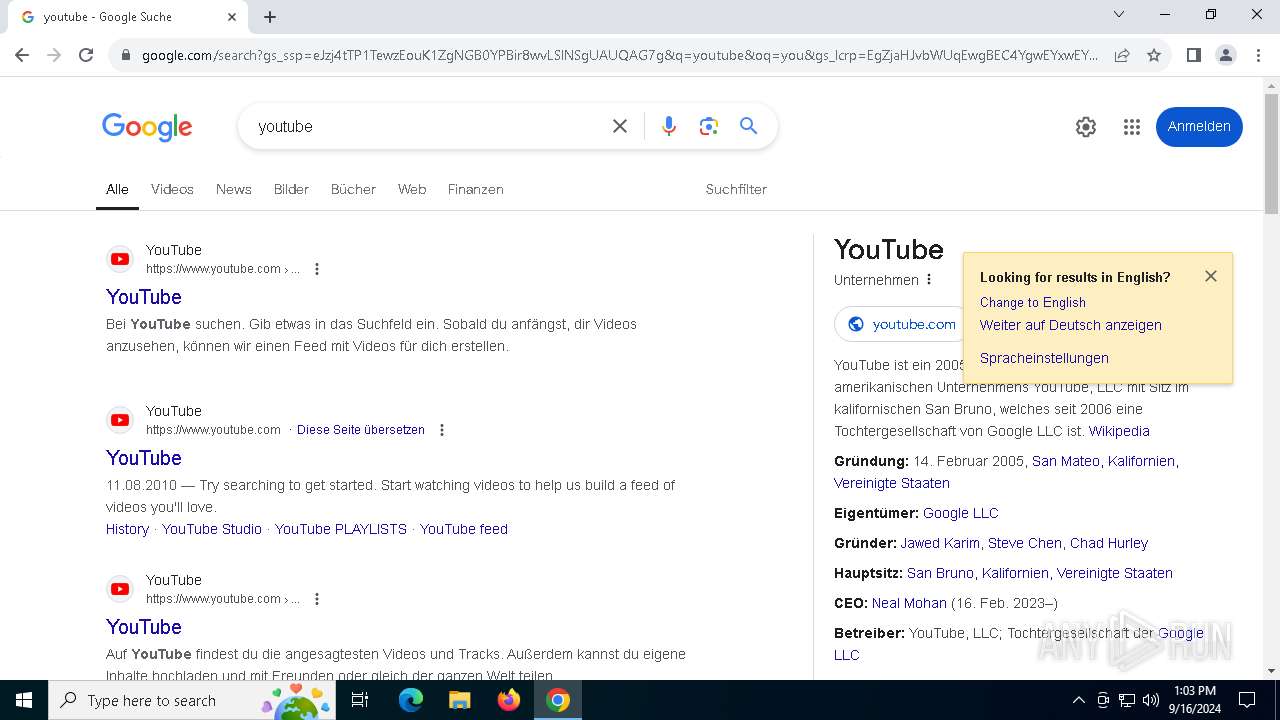
- chrome.exe (PID: 608)
Reads Environment values
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
- ApplicationFrameHost.exe (PID: 7068)
Reads the computer name
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
- ApplicationFrameHost.exe (PID: 7068)
Reads the machine GUID from the registry
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
- ApplicationFrameHost.exe (PID: 7068)
Checks supported languages
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
- ApplicationFrameHost.exe (PID: 7068)
Creates files in the program directory
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
Disables trace logs
- ApplicationFrameHost.exe (PID: 7068)
Checks proxy server information
- ApplicationFrameHost.exe (PID: 7068)
Application launched itself
- chrome.exe (PID: 608)
Process checks computer location settings
- e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:09:16 12:59:40 |
| ZipCRC: | 0x384934df |
| ZipCompressedSize: | 425976 |
| ZipUncompressedSize: | 848896 |
| ZipFileName: | e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe |
Total processes
175
Monitored processes
45
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3348 --field-trial-handle=1956,i,5910514700671123563,18227737646854869431,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 888 | schtasks.exe /create /tn "dwmd" /sc MINUTE /mo 14 /tr "'C:\Users\admin\Videos\dwm.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | schtasks.exe /create /tn "RegistryR" /sc MINUTE /mo 7 /tr "'C:\Users\Default\Links\Registry.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | schtasks.exe /create /tn "ctfmon" /sc ONLOGON /tr "'C:\Users\admin\My Documents\ctfmon.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1948 --field-trial-handle=1956,i,5910514700671123563,18227737646854869431,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1992 | schtasks.exe /create /tn "RegistryR" /sc MINUTE /mo 9 /tr "'C:\Users\Default\Links\Registry.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | schtasks.exe /create /tn "Registry" /sc ONLOGON /tr "'C:\Users\Default\Links\Registry.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | schtasks.exe /create /tn "dwm" /sc ONLOGON /tr "'C:\Users\admin\Videos\dwm.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2112 | schtasks.exe /create /tn "ctfmon" /sc ONLOGON /tr "'C:\Users\All Users\ctfmon.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 508
Read events
7 444
Write events
57
Delete events
7
Modification events
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.zip | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
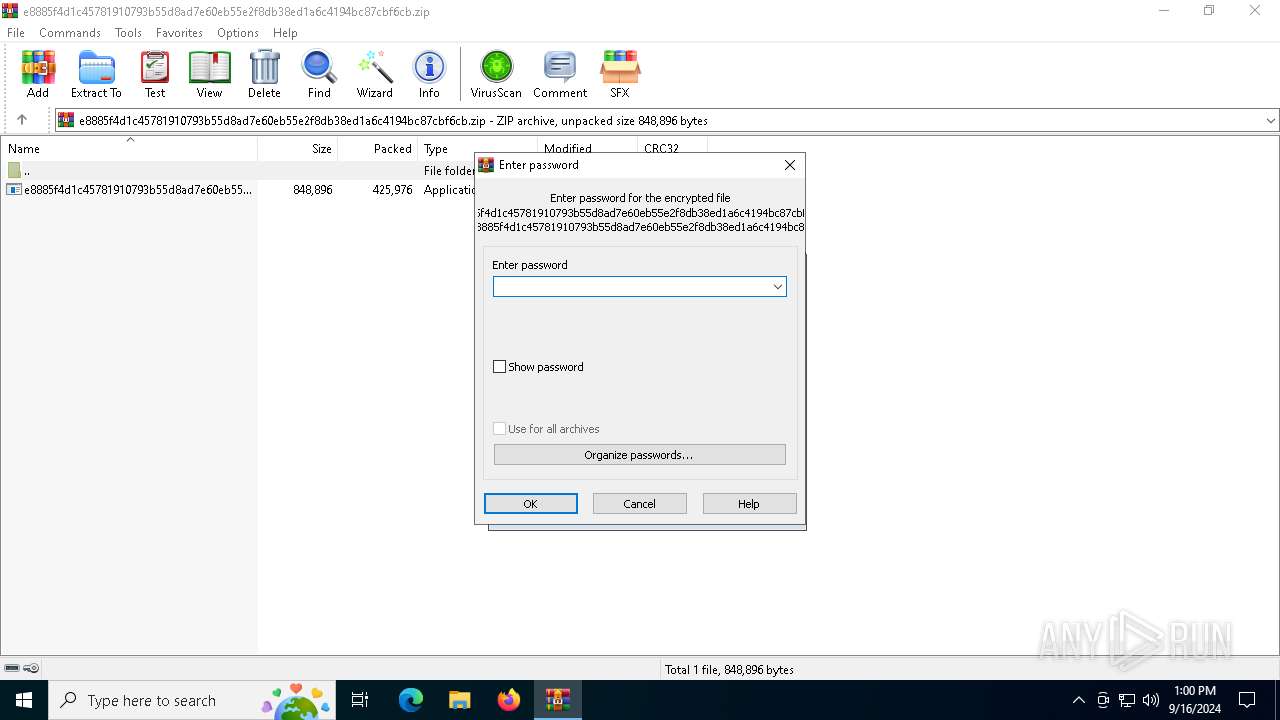
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (5000) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
8
Suspicious files
464
Text files
80
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe | C:\Users\admin\6dd19aba3e2428 | text | |
MD5:922312E2932EC34E574FAB529E6619ED | SHA256:4893D0C26C50F332FE4548D278C034AA29A14D184D42289E6233A130FF44C503 | |||
| 608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe | C:\ProgramData\f6fd79f27027e4 | text | |
MD5:038898CC19696E9DA7A79D01B47C255D | SHA256:A166665B14FCBA9F46D450EDBAF6B614B497DD5139DE034388DACACB41C37CFB | |||
| 2820 | e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe | C:\Users\admin\Documents\26c12092da979c | text | |
MD5:A0B165E1AF87C8B32469B03A64FBBD96 | SHA256:6BE3F061FC375A59027F97309F452D6905942BE36655ABE9806B2FBE97F24142 | |||
| 2820 | e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe | C:\ProgramData\e8885f4d1c45781910793b55d8ad7e60eb55e2f8db38ed1a6c4194bc87cbf6cb.exe | executable | |
MD5:268D50436BE43E7F6B465189E3934F7D | SHA256:E8885F4D1C45781910793B55D8AD7E60EB55E2F8DB38ED1A6C4194BC87CBF6CB | |||
| 608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF14b823.TMP | — | |
MD5:— | SHA256:— | |||
| 608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
90
DNS requests
82
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5816 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4528 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad36445m2ehnvje342fvryxajoma_3041/jflookgnkcckhobaglndicnbbgbonegd_3041_all_disrgfhbspkatdkpfhliap5vqe.crx3 | unknown | — | — | whitelisted |
7068 | ApplicationFrameHost.exe | GET | 400 | 141.8.197.42:80 | http://a1030351.xsph.ru/L1nc0In.php?oRE6WqBo52PHkmtbc7bga7aUDmxxMA=oV89N0poo2Tg9TXhLCDf88Wf&0t3u2Nb4HlwlnflwSwnGba=pE&vJevq9dTXGw4wo1l1sl5=gbsqLsYOZtNpQcSaW5&6f64094d00518d88b99b18e771cbd82e=8d26a4daf45cb7bd7a5120d716cfeab8&3938200463758de3f8d1a8e4c24f44b9=QOycTMiFDNlFDNzUzYxgTNjhzMmJjYzUGMmVTYwQWZxUWZ5MWZ3IDM&oRE6WqBo52PHkmtbc7bga7aUDmxxMA=oV89N0poo2Tg9TXhLCDf88Wf&0t3u2Nb4HlwlnflwSwnGba=pE&vJevq9dTXGw4wo1l1sl5=gbsqLsYOZtNpQcSaW5 | unknown | — | — | whitelisted |
368 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
368 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7068 | ApplicationFrameHost.exe | GET | 400 | 141.8.197.42:80 | http://a1030351.xsph.ru/L1nc0In.php?oRE6WqBo52PHkmtbc7bga7aUDmxxMA=oV89N0poo2Tg9TXhLCDf88Wf&0t3u2Nb4HlwlnflwSwnGba=pE&vJevq9dTXGw4wo1l1sl5=gbsqLsYOZtNpQcSaW5&6f64094d00518d88b99b18e771cbd82e=8d26a4daf45cb7bd7a5120d716cfeab8&3938200463758de3f8d1a8e4c24f44b9=QOycTMiFDNlFDNzUzYxgTNjhzMmJjYzUGMmVTYwQWZxUWZ5MWZ3IDM&oRE6WqBo52PHkmtbc7bga7aUDmxxMA=oV89N0poo2Tg9TXhLCDf88Wf&0t3u2Nb4HlwlnflwSwnGba=pE&vJevq9dTXGw4wo1l1sl5=gbsqLsYOZtNpQcSaW5 | unknown | — | — | whitelisted |
4528 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad36445m2ehnvje342fvryxajoma_3041/jflookgnkcckhobaglndicnbbgbonegd_3041_all_disrgfhbspkatdkpfhliap5vqe.crx3 | unknown | — | — | whitelisted |
4528 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad36445m2ehnvje342fvryxajoma_3041/jflookgnkcckhobaglndicnbbgbonegd_3041_all_disrgfhbspkatdkpfhliap5vqe.crx3 | unknown | — | — | whitelisted |
4528 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad36445m2ehnvje342fvryxajoma_3041/jflookgnkcckhobaglndicnbbgbonegd_3041_all_disrgfhbspkatdkpfhliap5vqe.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7056 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6880 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5816 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5816 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
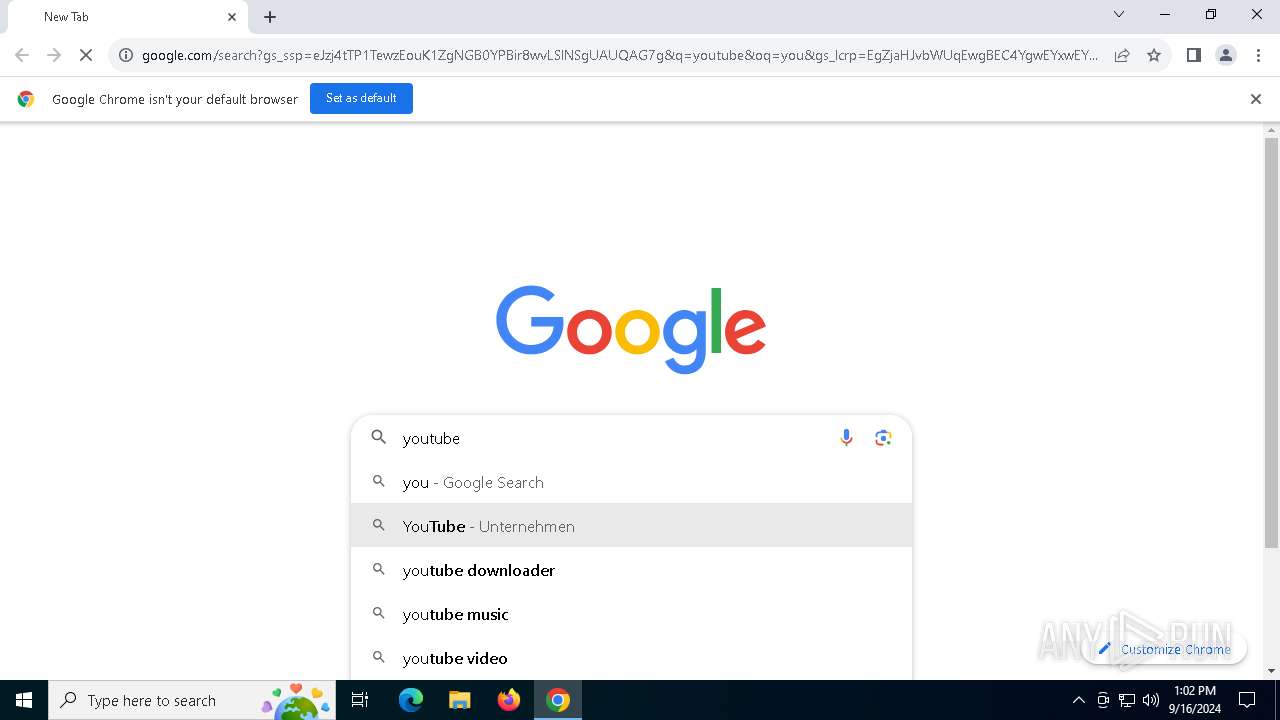
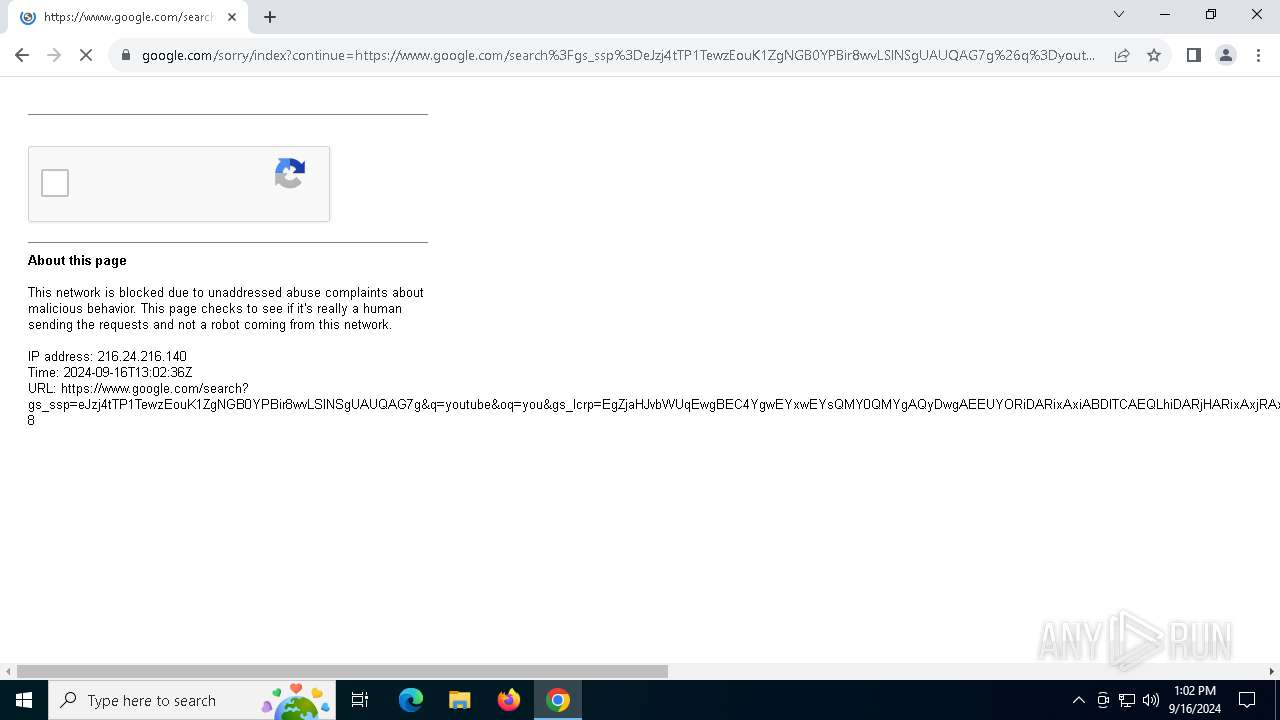
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
a1030351.xsph.ru |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to xsph .ru Domain |
7068 | ApplicationFrameHost.exe | A Network Trojan was detected | ET MALWARE DCRAT Activity (GET) |