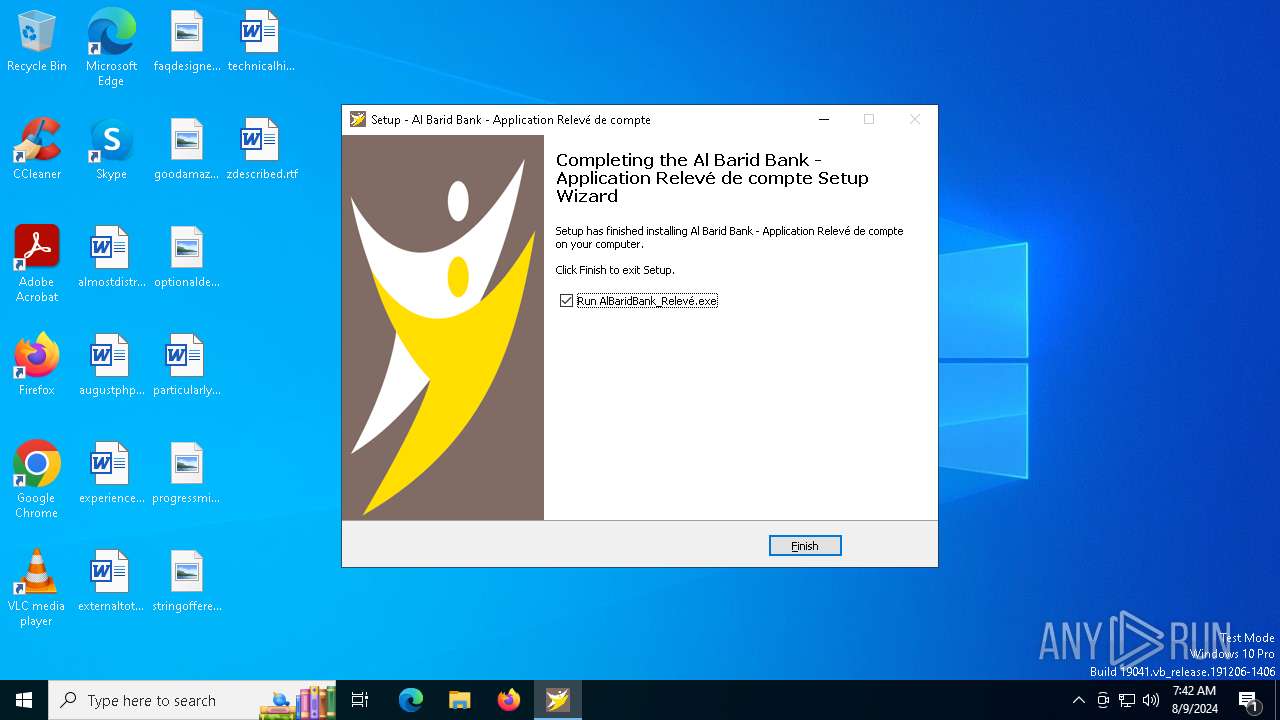
| File name: | Al Barid Bank Relevé de compte_Setup.exe |
| Full analysis: | https://app.any.run/tasks/33f3eb75-9ce8-4fe8-b5f9-7388a07cb703 |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2024, 07:41:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 95A5A5117656C75F3F9B679936255EE1 |
| SHA1: | D52E1FE99B9E9F03D85996476FEE404E013044D5 |
| SHA256: | 241BDE54C54268F4D3398F2B8D8C501EB50D11BDF3F72F39F137B4379EEED92D |
| SSDEEP: | 98304:m+cD4dnm0QhcpjdPokcVAcegYnzJaSLWu22l2+UDNm5E2ERHeTsxRbMuxhGstKVV:ZK4KoCit |
MALICIOUS
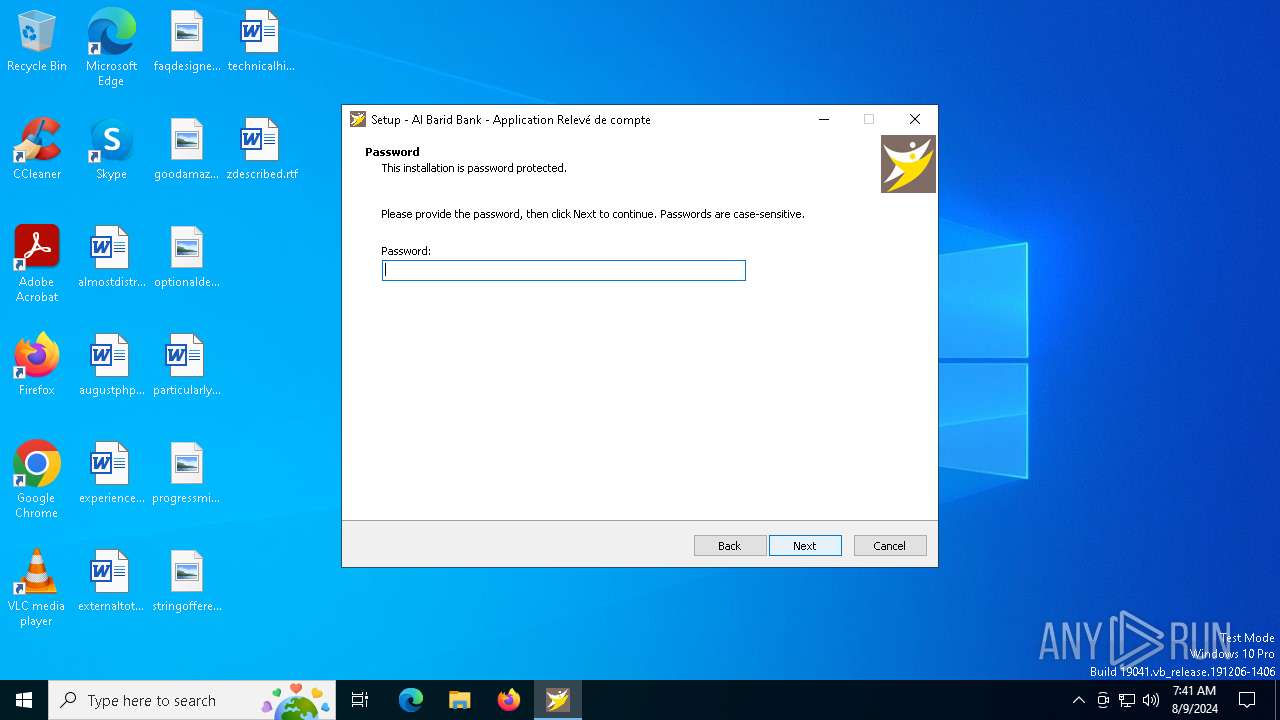
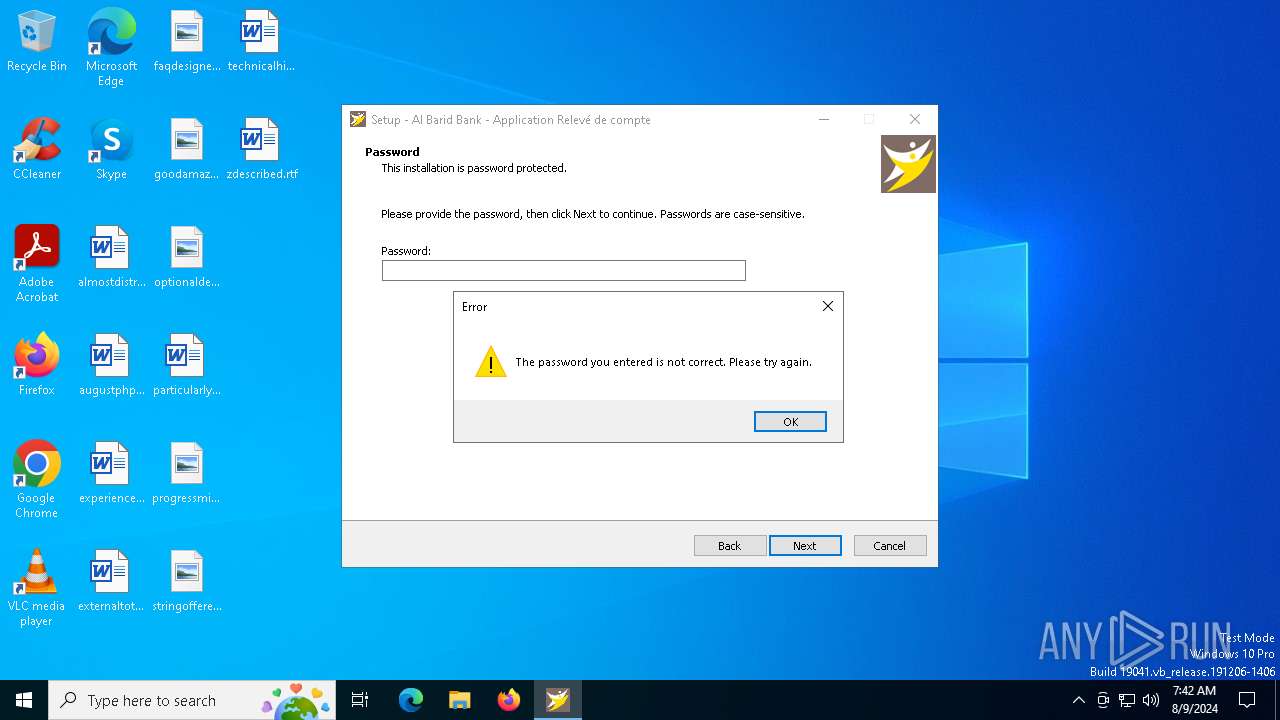
Bypass execution policy to execute commands
- powershell.exe (PID: 6552)
- powershell.exe (PID: 1688)
Adds path to the Windows Defender exclusion list
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- admin_microsoft_account.exe (PID: 460)
Changes powershell execution policy (Bypass)
- admin_microsoft_account.exe (PID: 460)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
Changes the autorun value in the registry
- admin_microsoft_account.exe (PID: 460)
Uses Task Scheduler to run other applications
- admin_microsoft_account.exe (PID: 460)
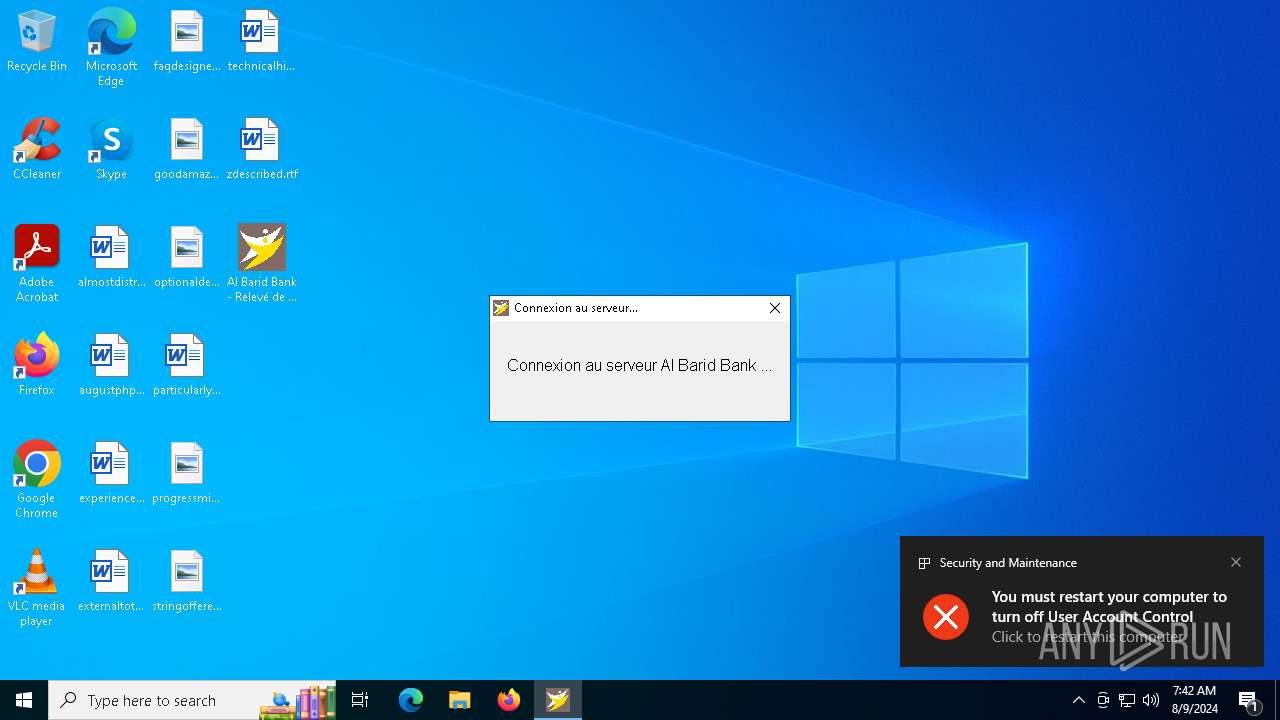
UAC/LUA settings modification
- reg.exe (PID: 6156)
SUSPICIOUS
Drops the executable file immediately after the start
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6504)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6400)
- admin_microsoft_account.exe (PID: 460)
Executable content was dropped or overwritten
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6504)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6400)
- admin_microsoft_account.exe (PID: 460)
Reads the Windows owner or organization settings
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
Reads the date of Windows installation
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6420)
Reads security settings of Internet Explorer
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6420)
- ShellExperienceHost.exe (PID: 6364)
Script adds exclusion path to Windows Defender
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- admin_microsoft_account.exe (PID: 460)
Starts POWERSHELL.EXE for commands execution
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- admin_microsoft_account.exe (PID: 460)
Starts CMD.EXE for commands execution
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
Uses REG/REGEDIT.EXE to modify registry
- admin_microsoft_account.exe (PID: 460)
Process drops legitimate windows executable
- admin_microsoft_account.exe (PID: 460)
The process drops C-runtime libraries
- admin_microsoft_account.exe (PID: 460)
Uses TASKKILL.EXE to kill process
- admin_microsoft_account.exe (PID: 460)
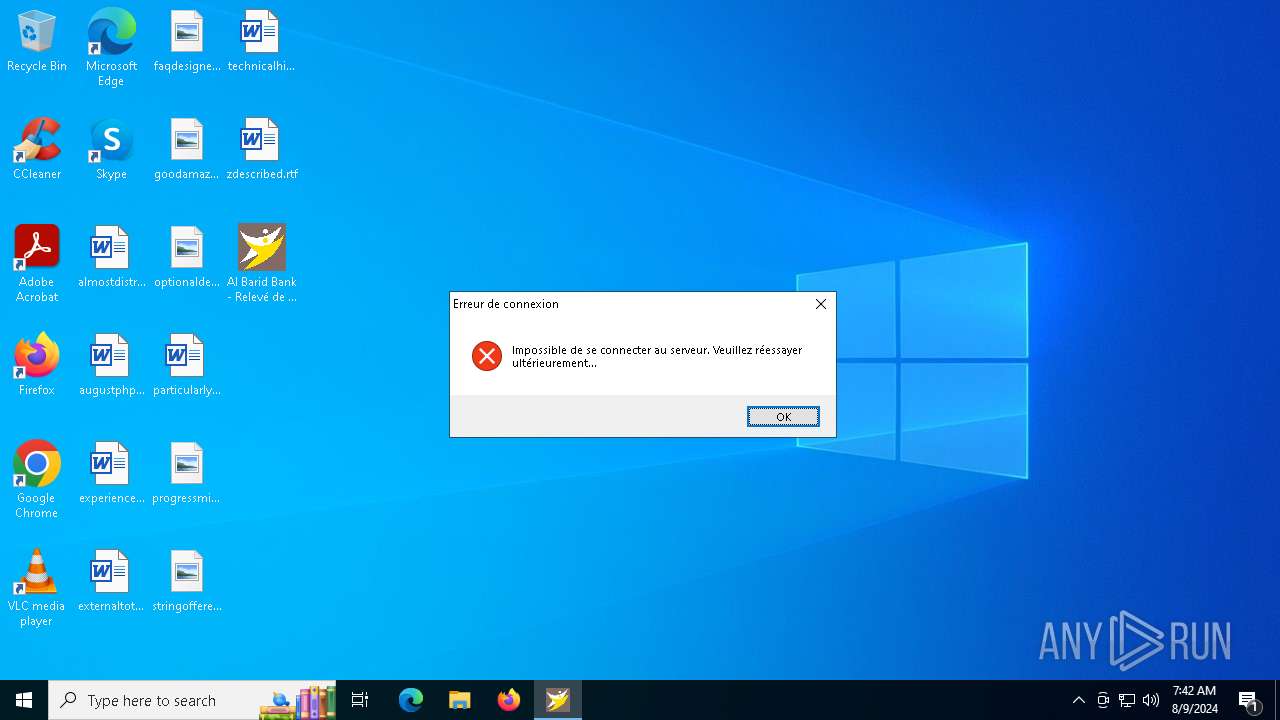
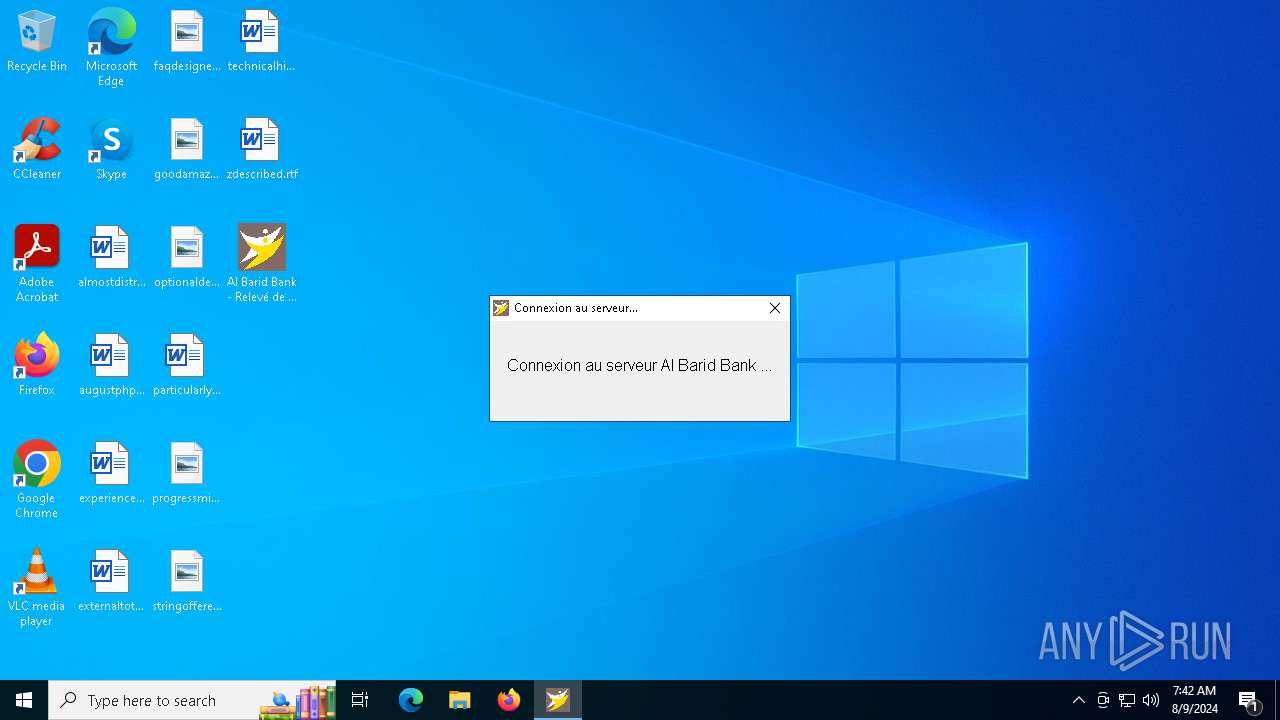
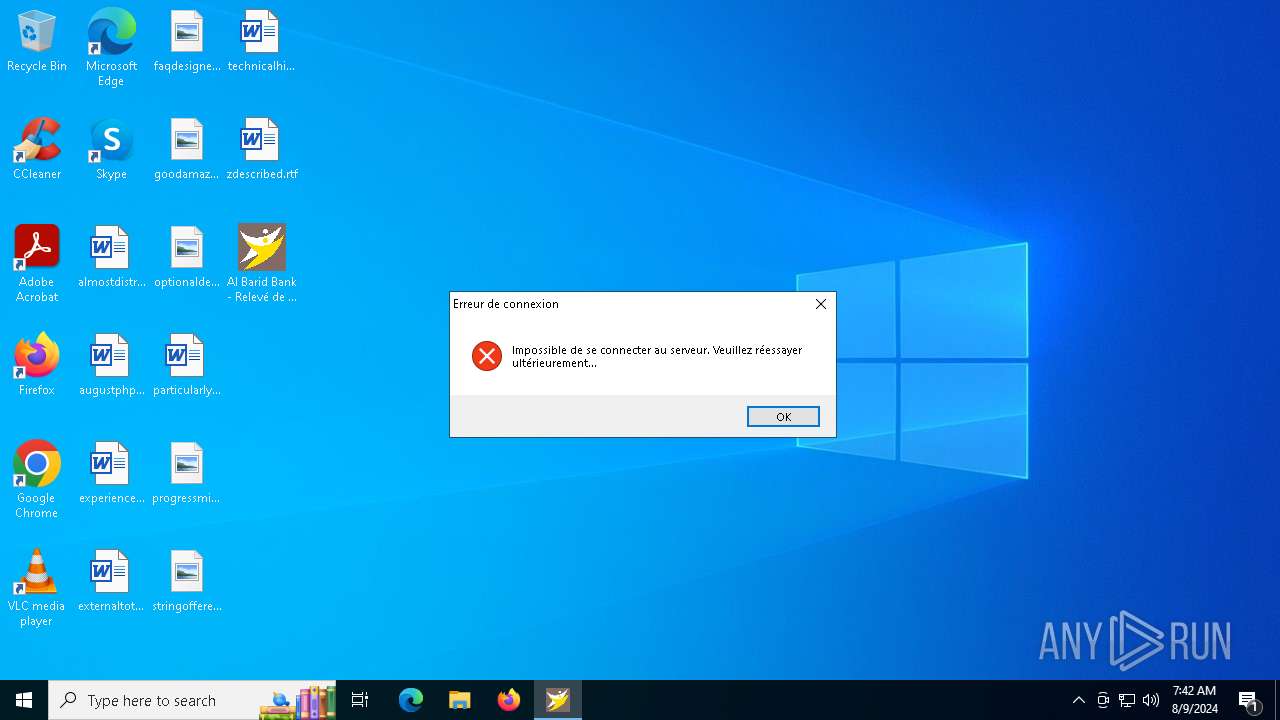
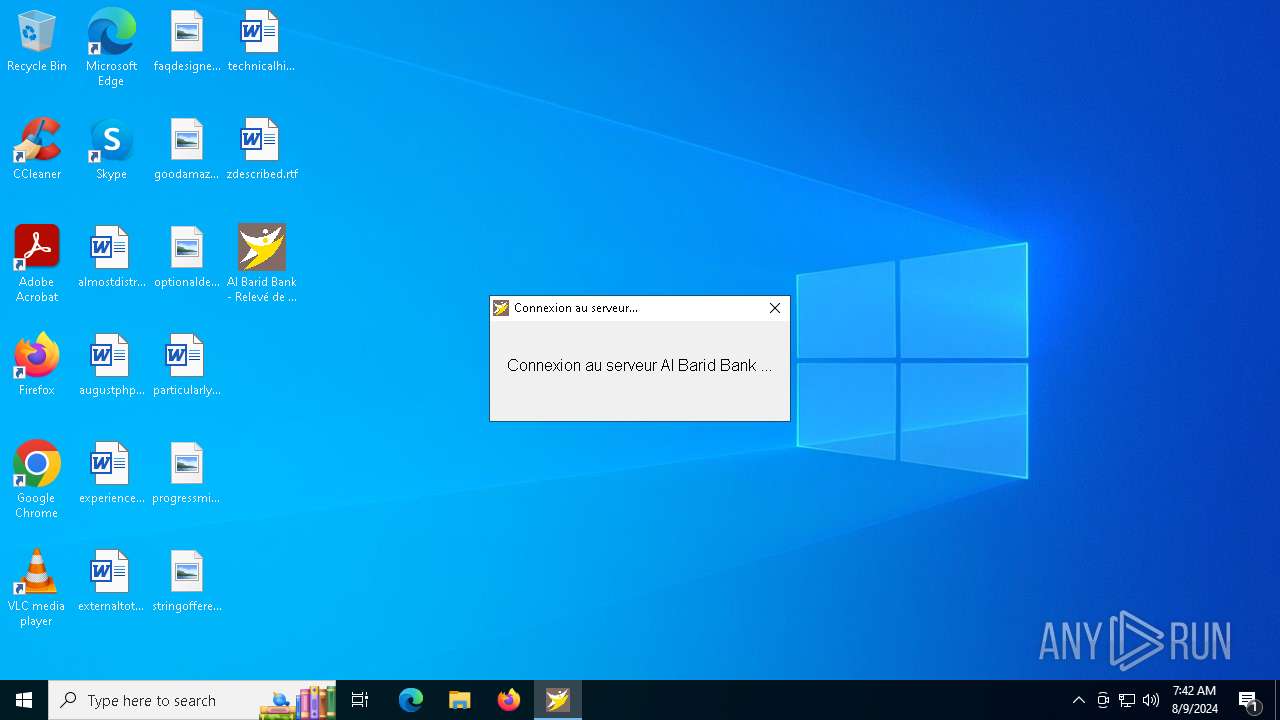
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2256)
Connects to unusual port
- admin_microsoft_account.exe (PID: 460)
- Al Barid Bank - Relevé de compte.exe (PID: 6532)
- AlBaridBank_Relevé.exe (PID: 1536)
- Al Barid Bank - Relevé de compte.exe (PID: 5484)
- Al Barid Bank - Relevé de compte.exe (PID: 320)
The process executes via Task Scheduler
- admin_microsoft_account.exe (PID: 1076)
INFO
Create files in a temporary directory
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6504)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6400)
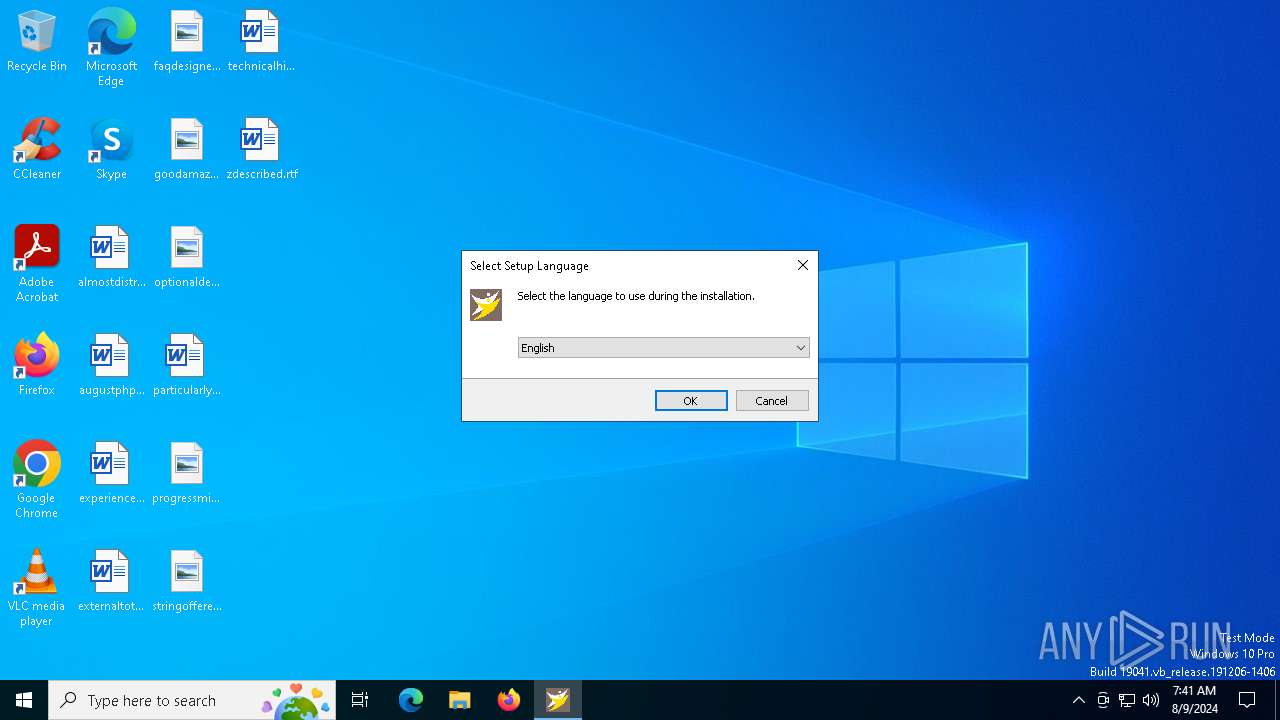
Checks supported languages
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6504)
- Al Barid Bank Relevé de compte_Setup.exe (PID: 6400)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6420)
- admin_microsoft_account.exe (PID: 460)
- admin_microsoft_account.exe (PID: 1076)
- ShellExperienceHost.exe (PID: 6364)
- AlBaridBank_Relevé.exe (PID: 1536)
- Al Barid Bank - Relevé de compte.exe (PID: 5484)
- Al Barid Bank - Relevé de compte.exe (PID: 320)
- Al Barid Bank - Relevé de compte.exe (PID: 6532)
Process checks computer location settings
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6420)
Reads the computer name
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6420)
- admin_microsoft_account.exe (PID: 460)
- ShellExperienceHost.exe (PID: 6364)
- AlBaridBank_Relevé.exe (PID: 1536)
- Al Barid Bank - Relevé de compte.exe (PID: 5484)
- Al Barid Bank - Relevé de compte.exe (PID: 320)
- Al Barid Bank - Relevé de compte.exe (PID: 6532)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6552)
- powershell.exe (PID: 1688)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6552)
- powershell.exe (PID: 1688)
Creates files in the program directory
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
Creates a software uninstall entry
- Al Barid Bank Relevé de compte_Setup.tmp (PID: 6528)
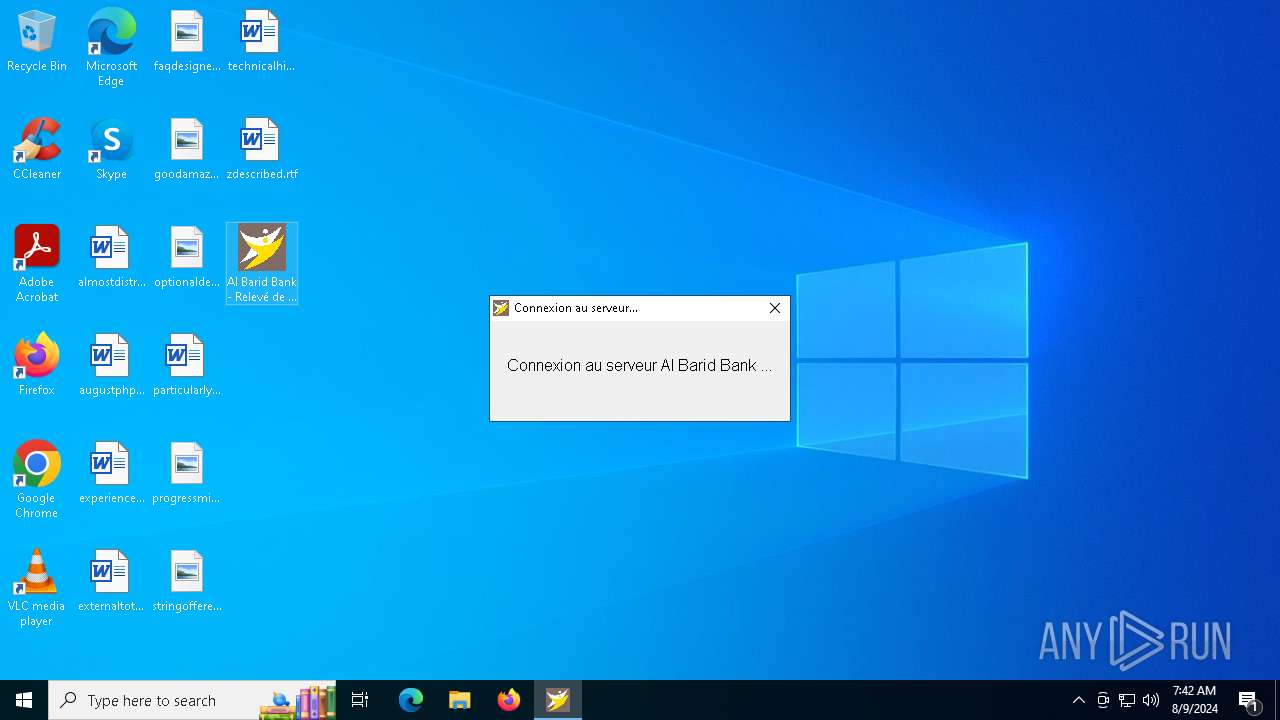
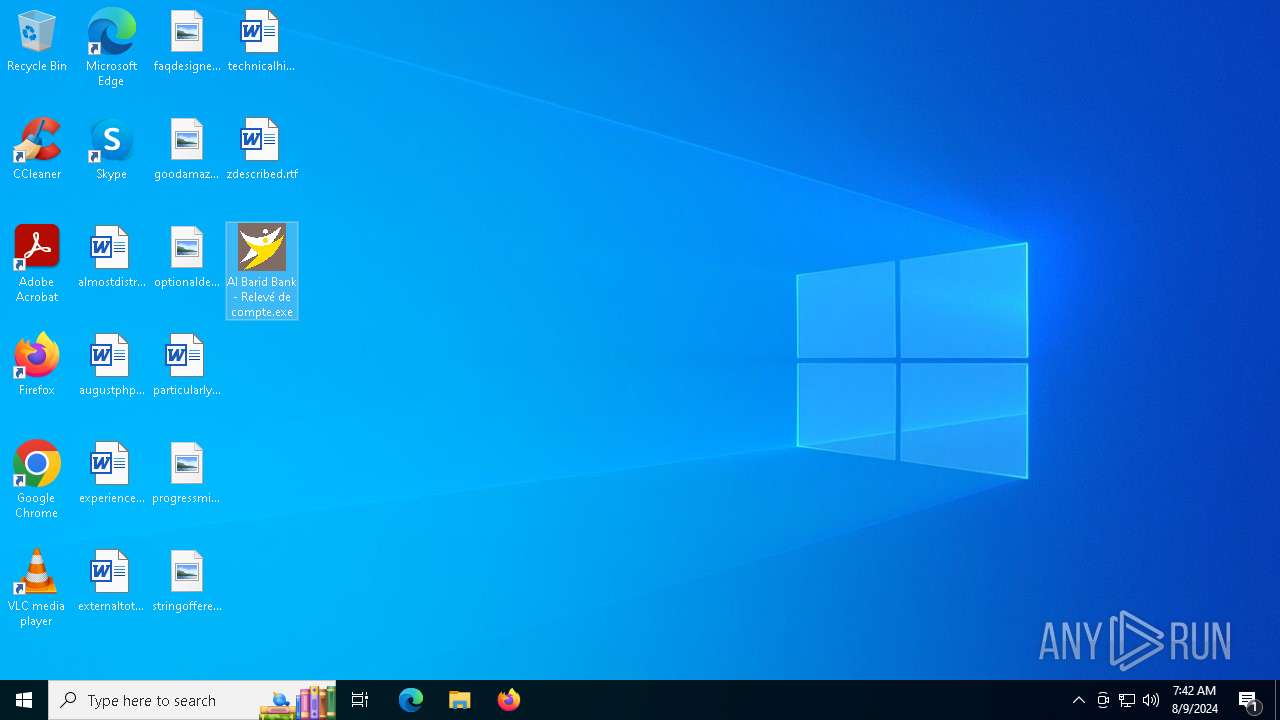
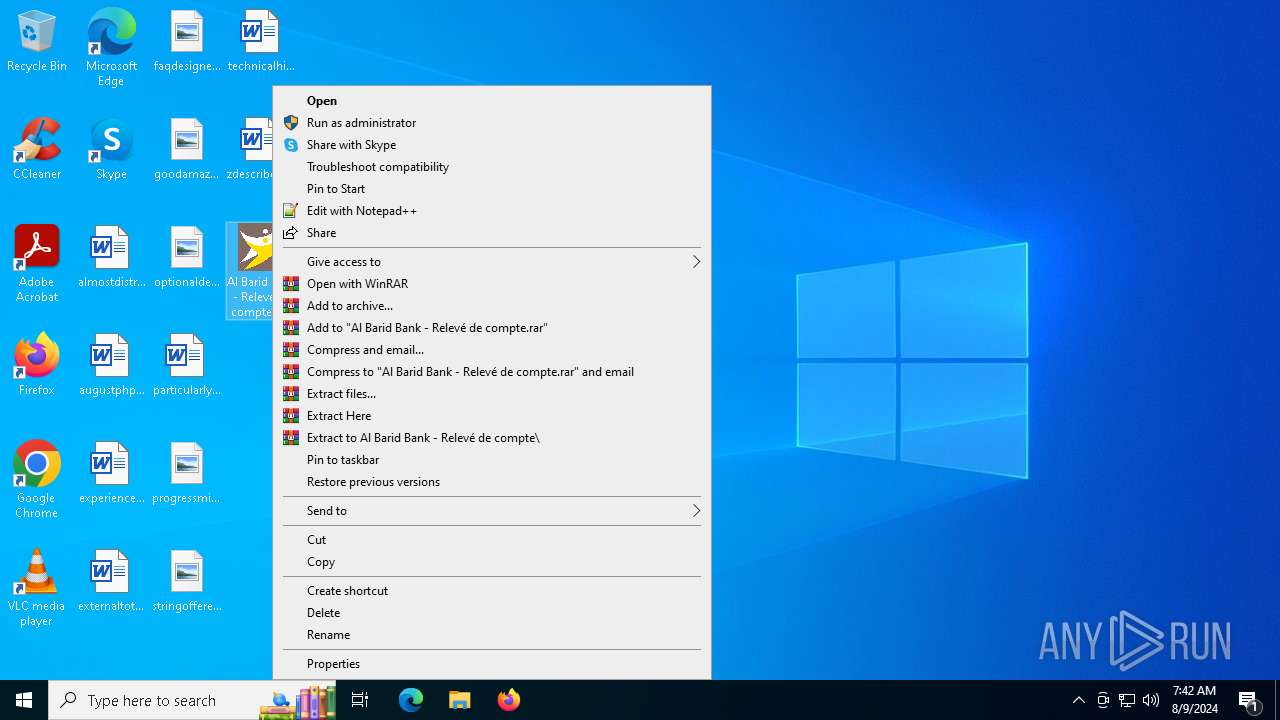
Manual execution by a user
- Al Barid Bank - Relevé de compte.exe (PID: 6532)
- Al Barid Bank - Relevé de compte.exe (PID: 5484)
- Al Barid Bank - Relevé de compte.exe (PID: 320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 52224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
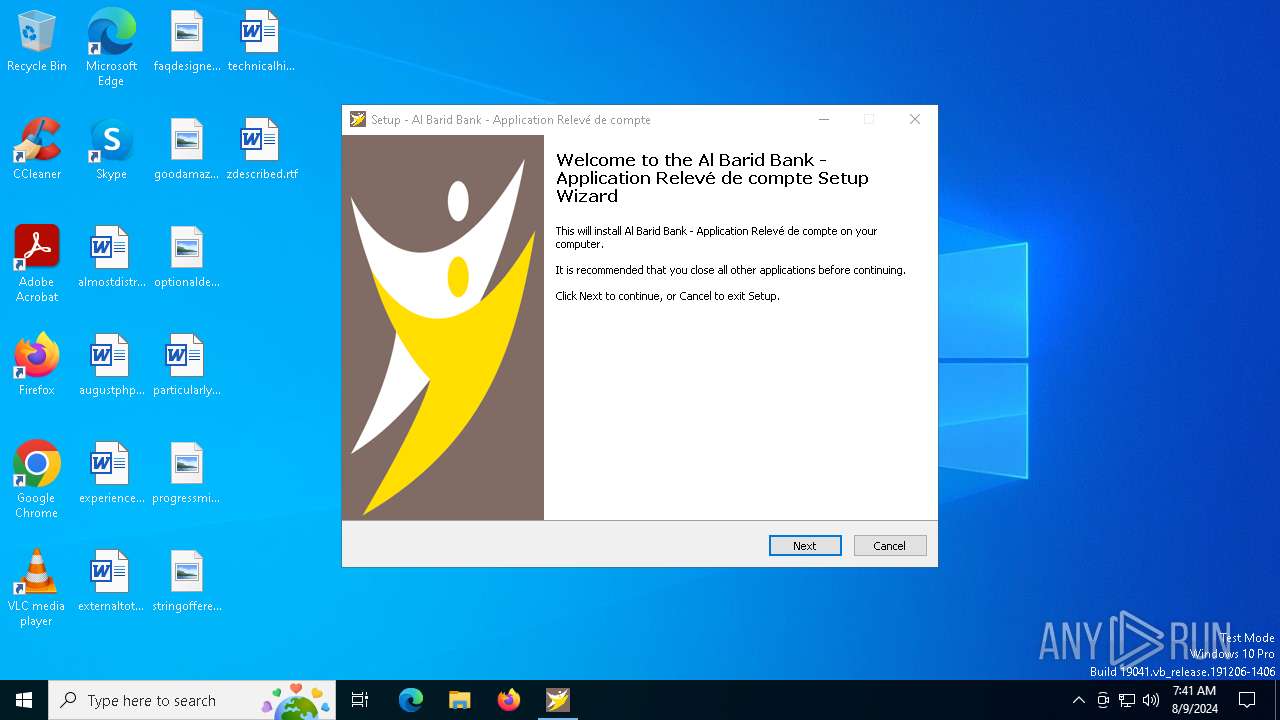
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Al Barid Bank |
| FileDescription: | Al Barid Bank - Application Relevé de compte Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Al Barid Bank - Application Relevé de compte |
| ProductVersion: |
Total processes
160
Monitored processes
26
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Users\admin\Desktop\Al Barid Bank - Relevé de compte.exe" | C:\Users\admin\Desktop\Al Barid Bank - Relevé de compte.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 460 | "C:\WINDOWS\Security\updateagent\admin_microsoft_account.exe" lnrm5$+wu4j%=vogu | C:\Windows\security\updateagent\admin_microsoft_account.exe | Al Barid Bank Relevé de compte_Setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1076 | "C:\WINDOWS\Security\updateagent\admin_microsoft_account.exe" lnrm5$+wu4j%=vogu | C:\Windows\security\updateagent\admin_microsoft_account.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | "C:\Program Files (x86)\Al Barid Bank\AlBaridBank_Relevé.exe" | C:\Program Files (x86)\Al Barid Bank\AlBaridBank_Relevé.exe | Al Barid Bank Relevé de compte_Setup.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1688 | "powershell" -ex bypass -C "Add-MpPreference -ExclusionPath 'C:','d:','e:','f:','g:','h:', 'C:\WINDOWS\Security\updateagent\'" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | admin_microsoft_account.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2080 | "taskkill" /f /im securitysvc.exe | C:\Windows\SysWOW64\taskkill.exe | — | admin_microsoft_account.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | "taskkill" /f /im netsvc.exe | C:\Windows\SysWOW64\taskkill.exe | — | admin_microsoft_account.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 541
Read events
20 437
Write events
98
Delete events
6
Modification events
| (PID) Process: | (6528) Al Barid Bank Relevé de compte_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 80190000EEC1C0982FEADA01 | |||
| (PID) Process: | (6528) Al Barid Bank Relevé de compte_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: DF6C0DE5AB7540B3601B20D50F9AADE45791416F69C77F4B1FEA7765C5E7CE0D | |||
| (PID) Process: | (6528) Al Barid Bank Relevé de compte_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6552) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6552) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6552) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6552) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6528) Al Barid Bank Relevé de compte_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files (x86)\Al Barid Bank\AlBaridBank_Relevé.exe | |||
| (PID) Process: | (6528) Al Barid Bank Relevé de compte_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 13F15354C730C178D01096B481C8D1F9C7D2B626B56B9FA77D34D52FCAD26CDA | |||
| (PID) Process: | (6528) Al Barid Bank Relevé de compte_Setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Al Barid Bank - Application Relevé de compte_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
Executable files
12
Suspicious files
4
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6528 | Al Barid Bank Relevé de compte_Setup.tmp | C:\Program Files (x86)\Al Barid Bank\unins000.exe | executable | |
MD5:7ACD3E6D086C4291ABA6D7C34DA21926 | SHA256:D1A5264A76AE4568BB22EFF71D86BC8BC20C00352A81C5ADD3FB68BF872DDA26 | |||
| 6400 | Al Barid Bank Relevé de compte_Setup.exe | C:\Users\admin\AppData\Local\Temp\is-2RCFE.tmp\Al Barid Bank Relevé de compte_Setup.tmp | executable | |
MD5:4B9FD952A26896609E0D2380E7A40712 | SHA256:02FB145C6C3BA0E33791148CFE5B80B065A0359121038347BC4FFDC60F4AE07F | |||
| 6528 | Al Barid Bank Relevé de compte_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-32BGM.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6504 | Al Barid Bank Relevé de compte_Setup.exe | C:\Users\admin\AppData\Local\Temp\is-8LCIH.tmp\Al Barid Bank Relevé de compte_Setup.tmp | executable | |
MD5:4B9FD952A26896609E0D2380E7A40712 | SHA256:02FB145C6C3BA0E33791148CFE5B80B065A0359121038347BC4FFDC60F4AE07F | |||
| 6528 | Al Barid Bank Relevé de compte_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-32BGM.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 6552 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jf3lba2m.u2r.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6552 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_degdj44s.vho.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6552 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jgpqtmon.4g3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6552 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_coof3kfd.ck1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6528 | Al Barid Bank Relevé de compte_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-32BGM.tmp\agent.exe | executable | |
MD5:4C168C3E04B0C0F73ABB3FA2A2A95104 | SHA256:9D28AB1200BA8C2B2C80C56AEB4FA0D57E1999BACB58532D141D93906752AC8A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
58
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
6984 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
7032 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
1948 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4788 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4788 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1948 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
albaridbank.freedynamicdns.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.freedynamicdns .org |
1 ETPRO signatures available at the full report