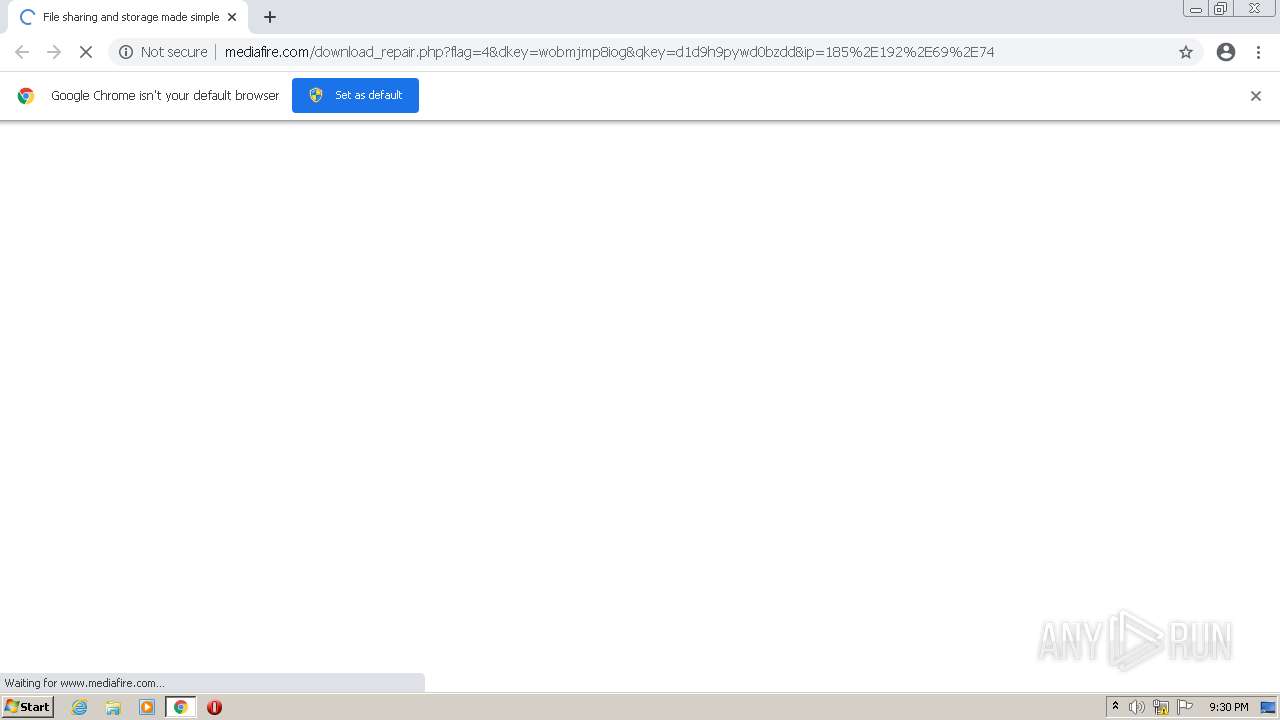
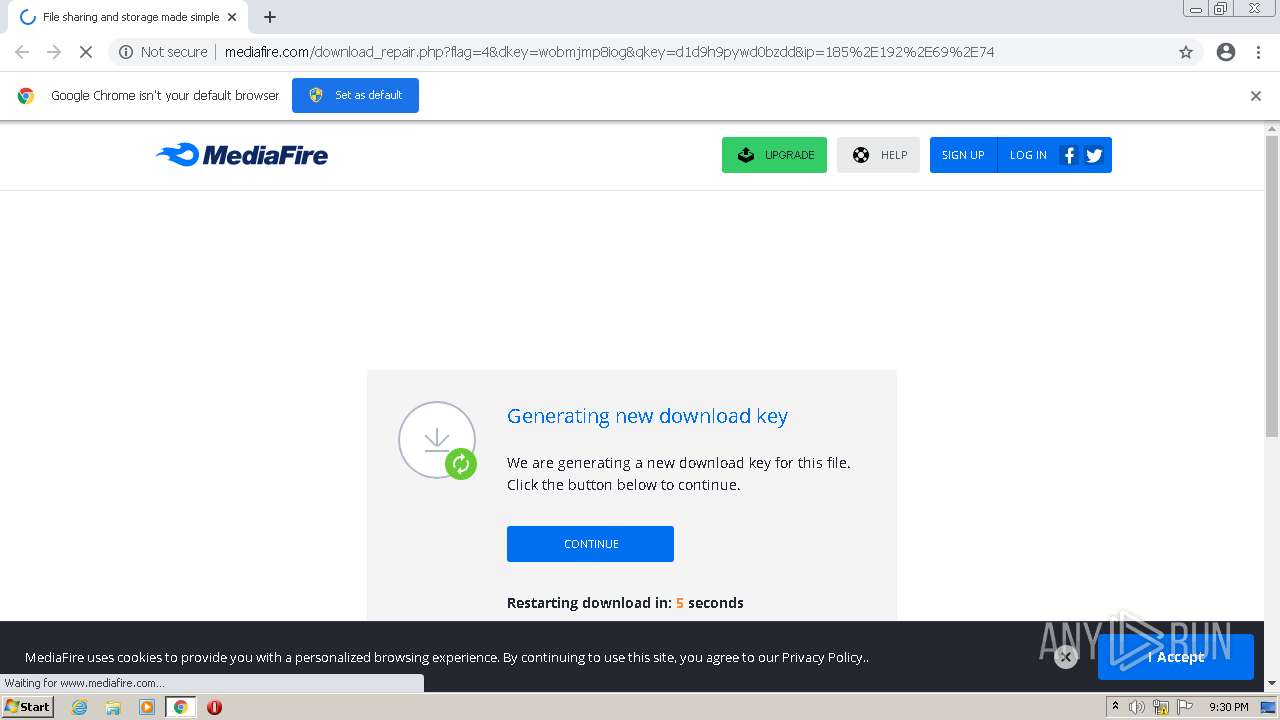
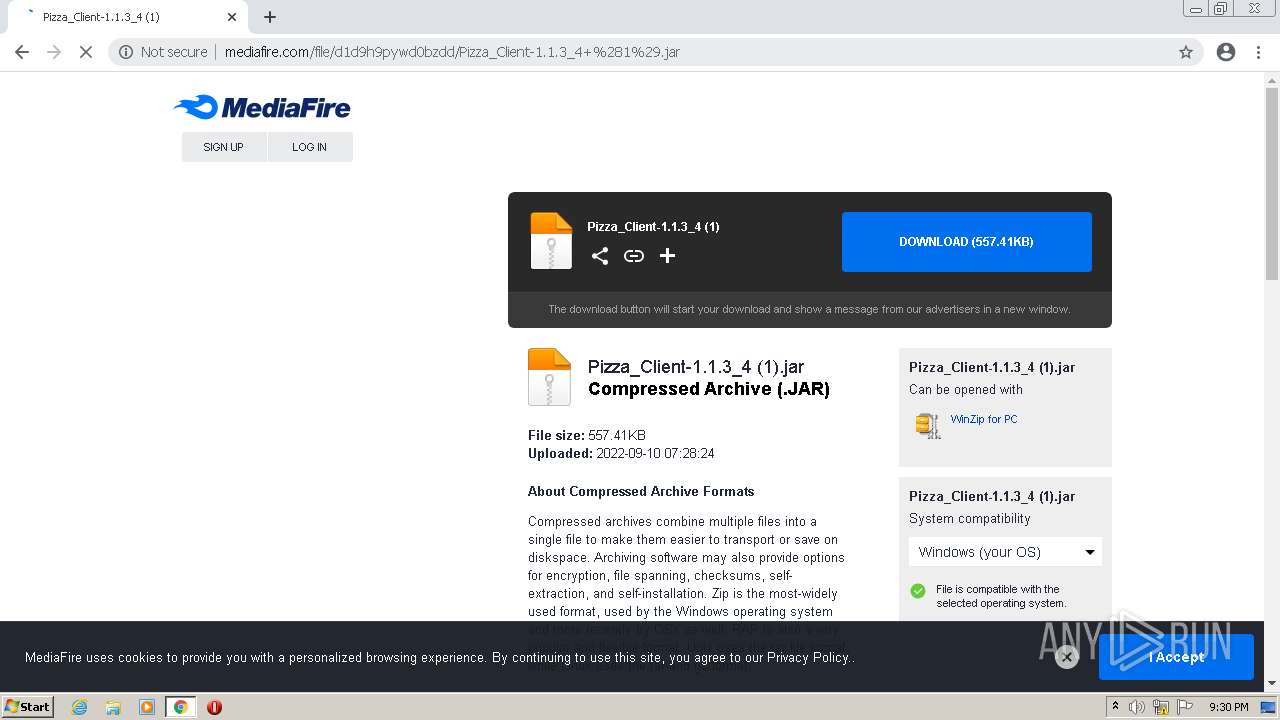
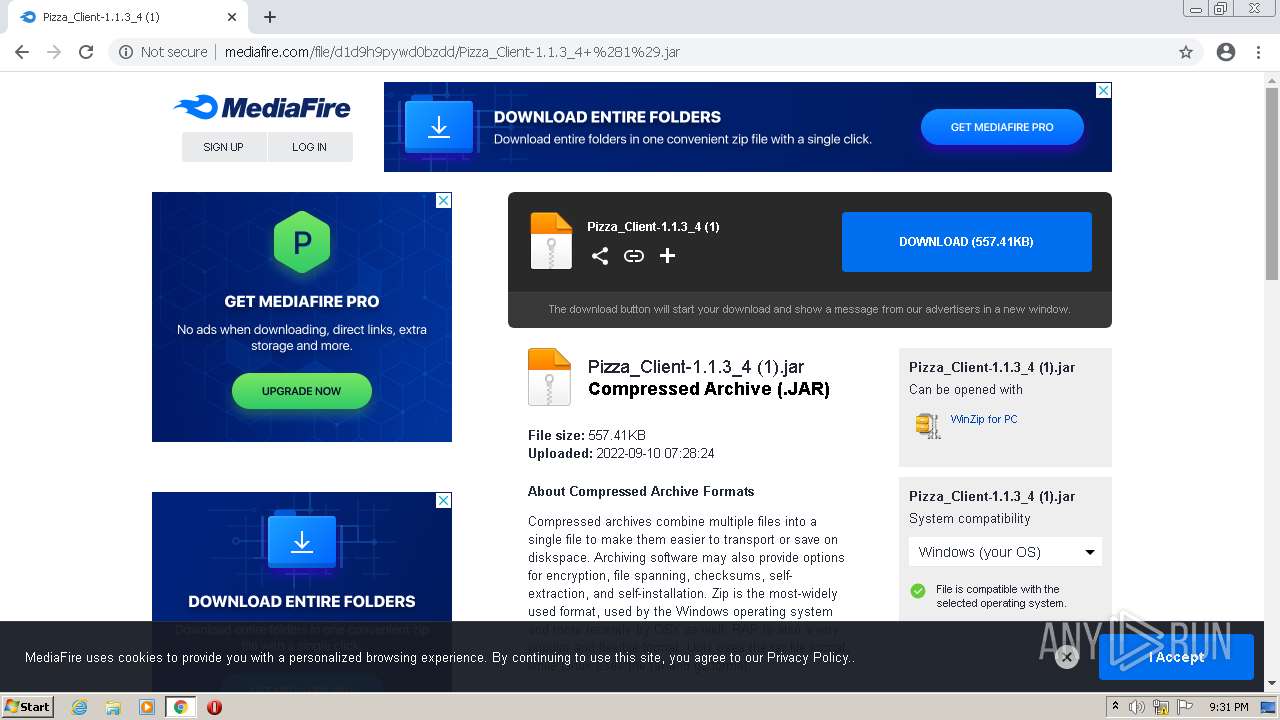
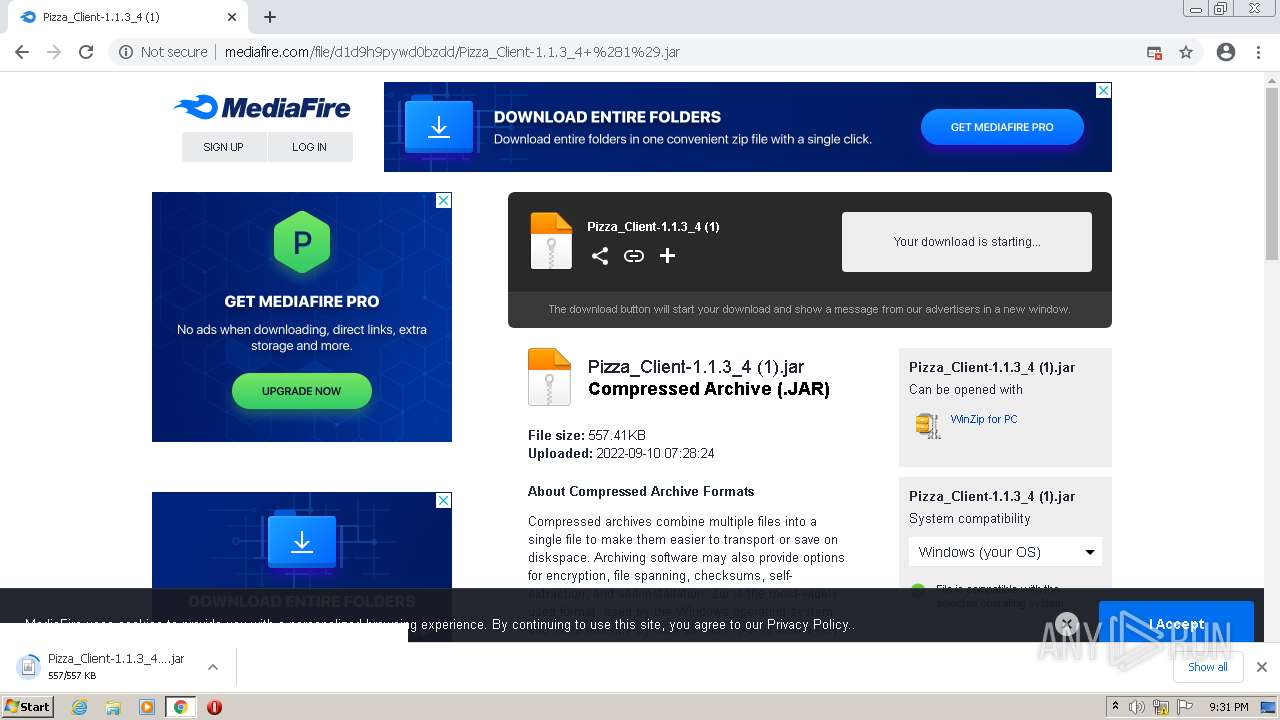
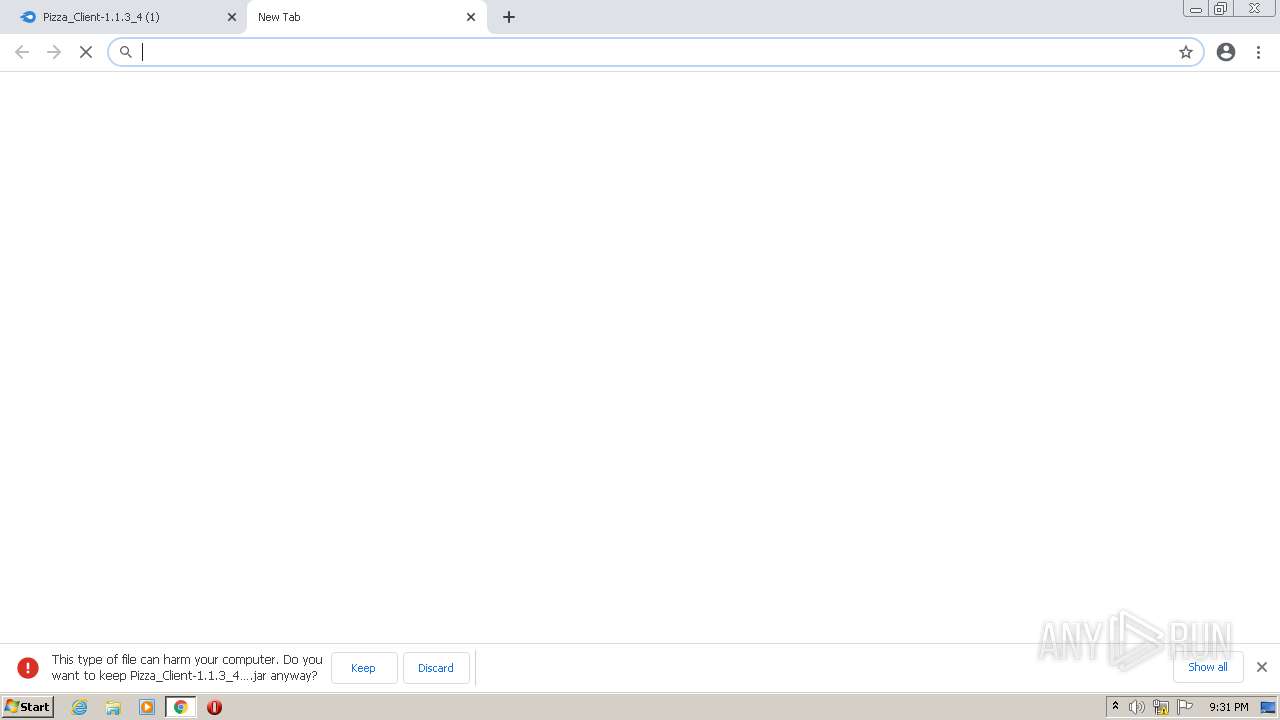
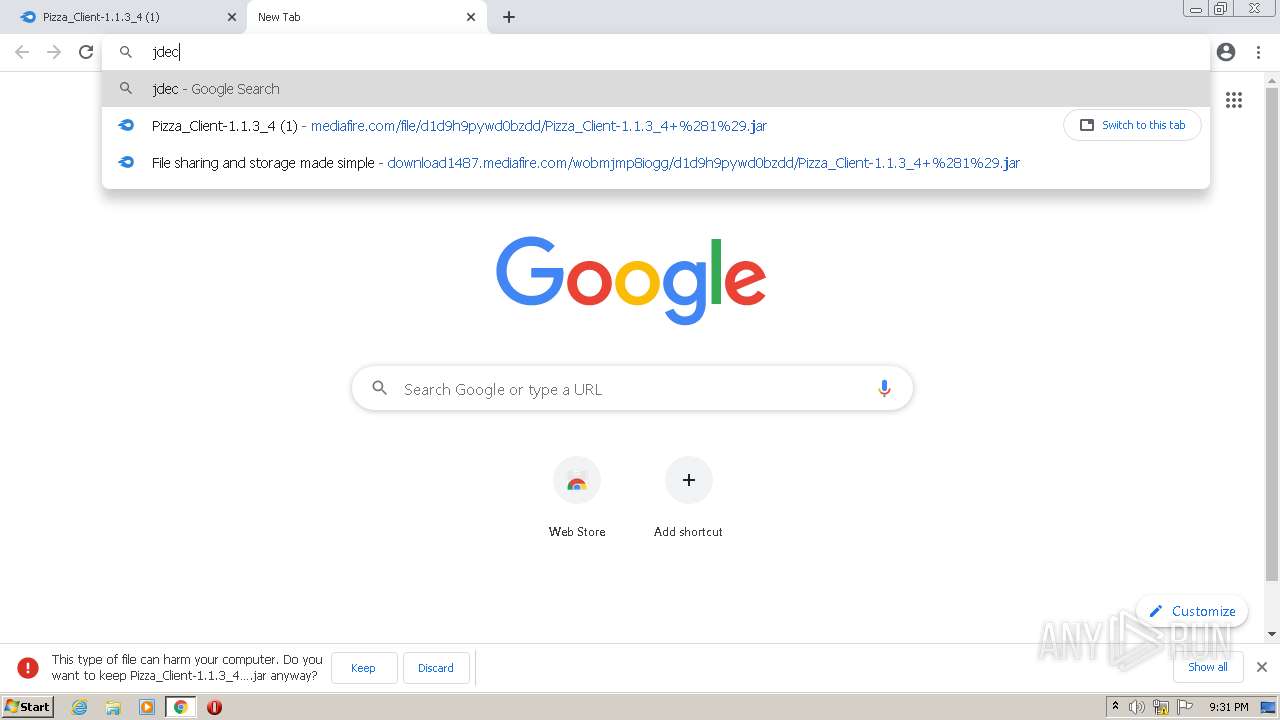
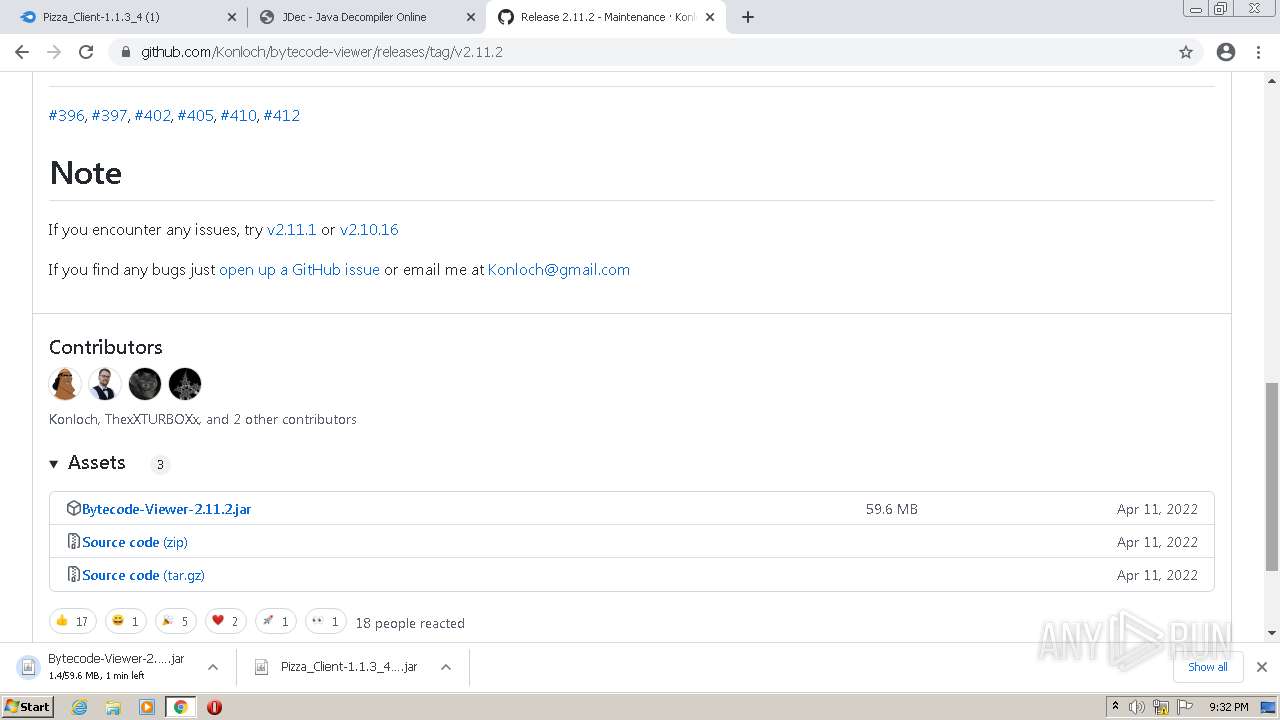
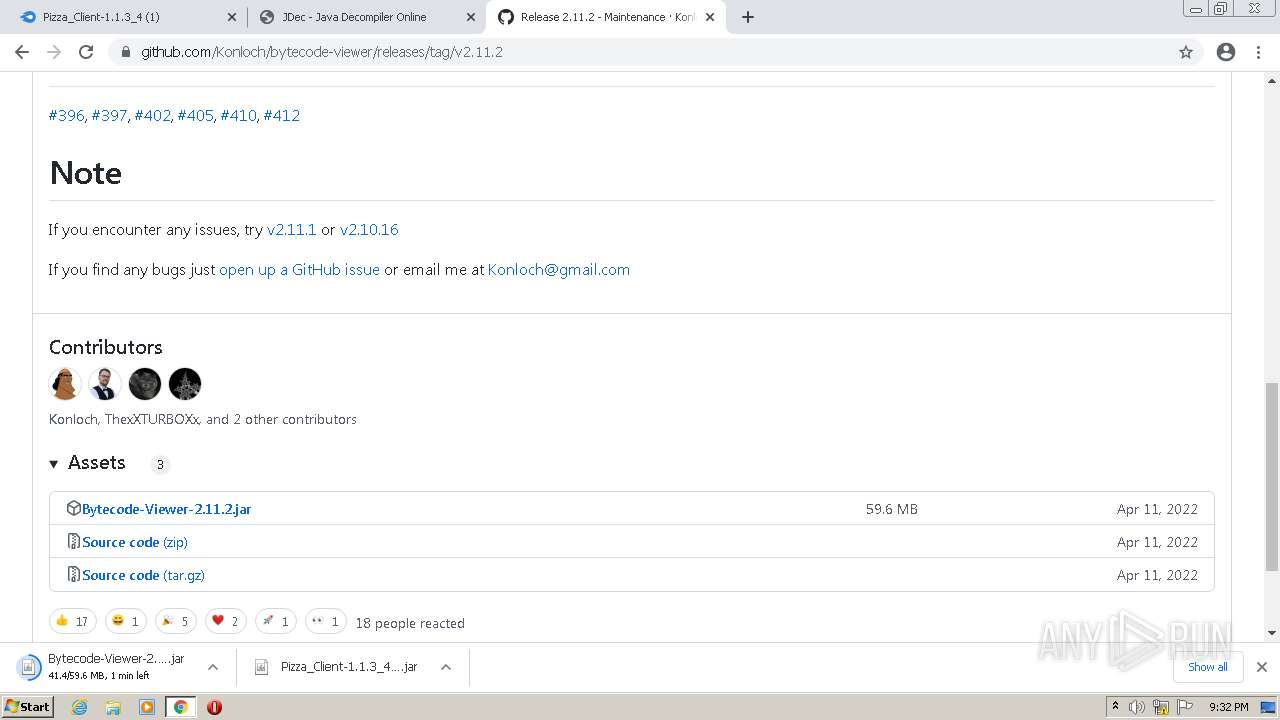
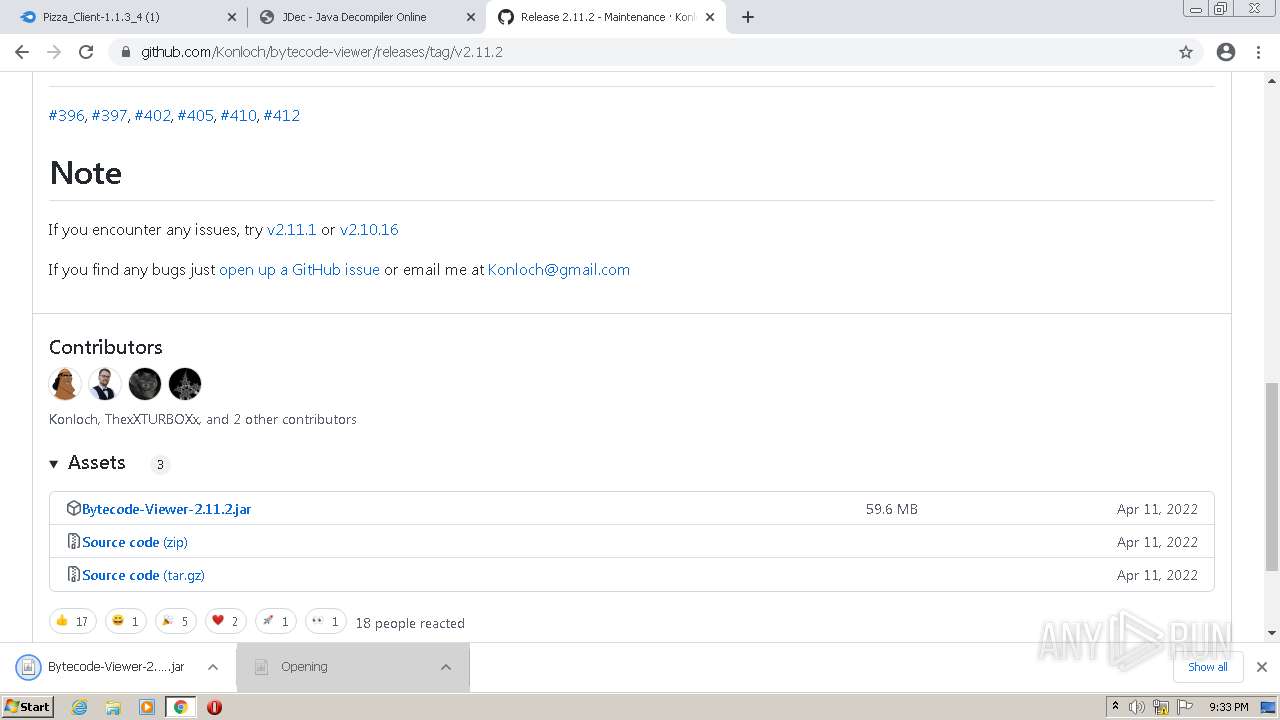
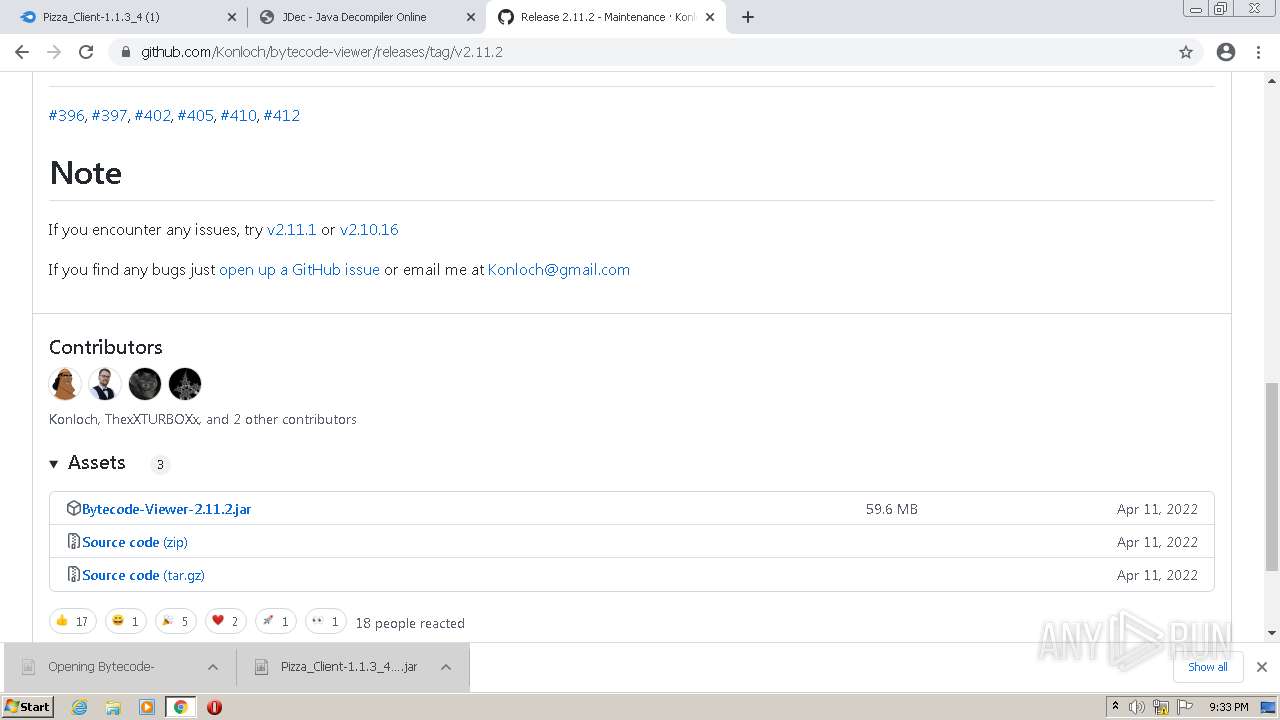
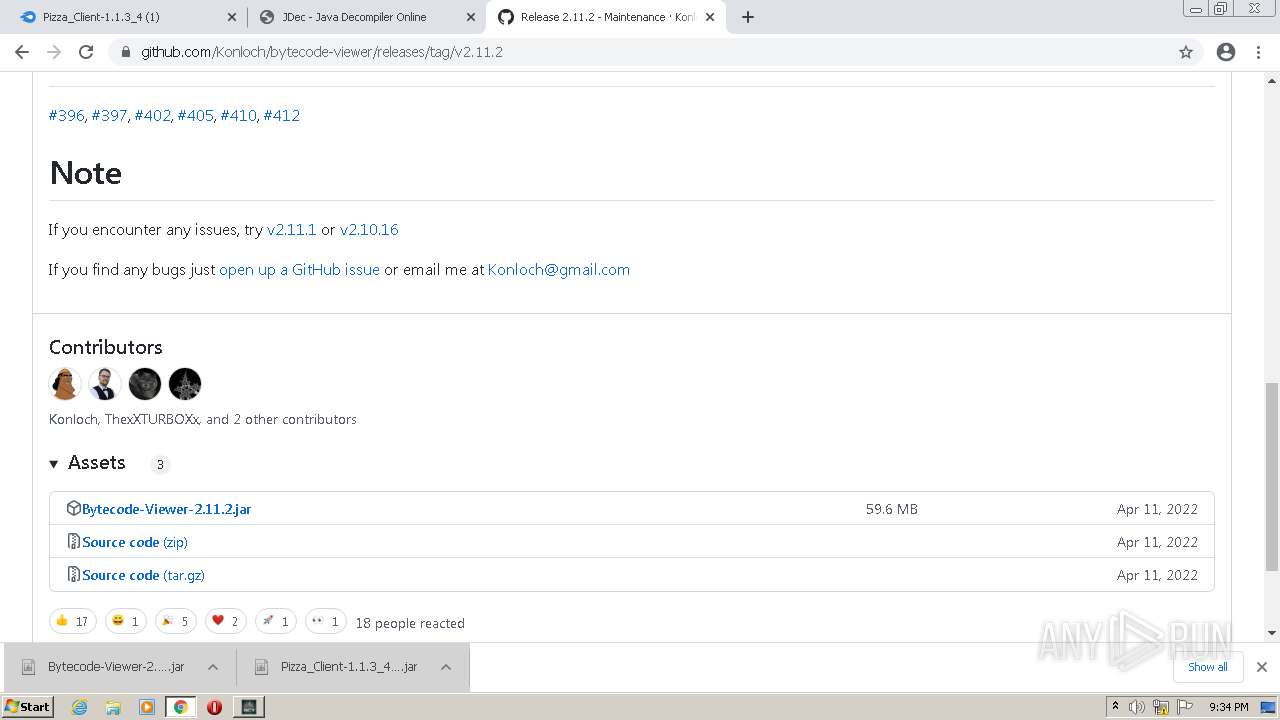
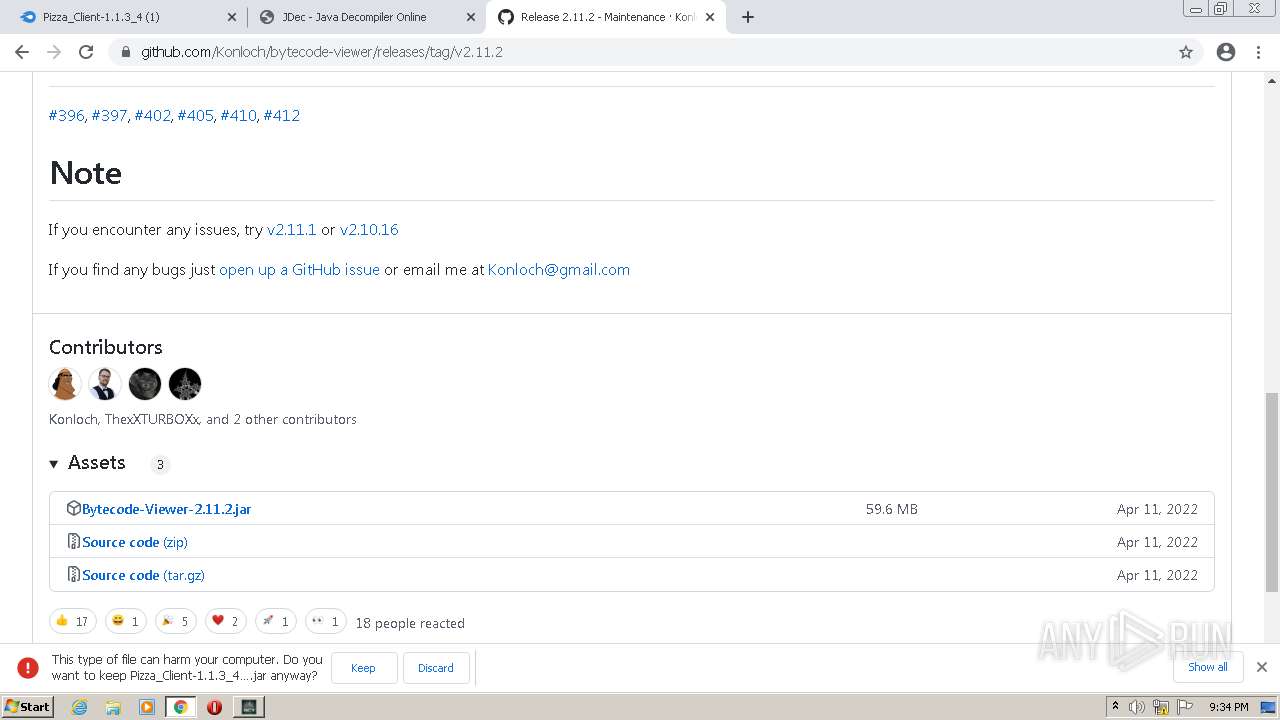
| URL: | https://download1487.mediafire.com/wobmjmp8iogg/d1d9h9pywd0bzdd/Pizza_Client-1.1.3_4+%281%29.jar |
| Full analysis: | https://app.any.run/tasks/04da6a8f-fdd9-40b0-96e1-1e7f9a751423 |
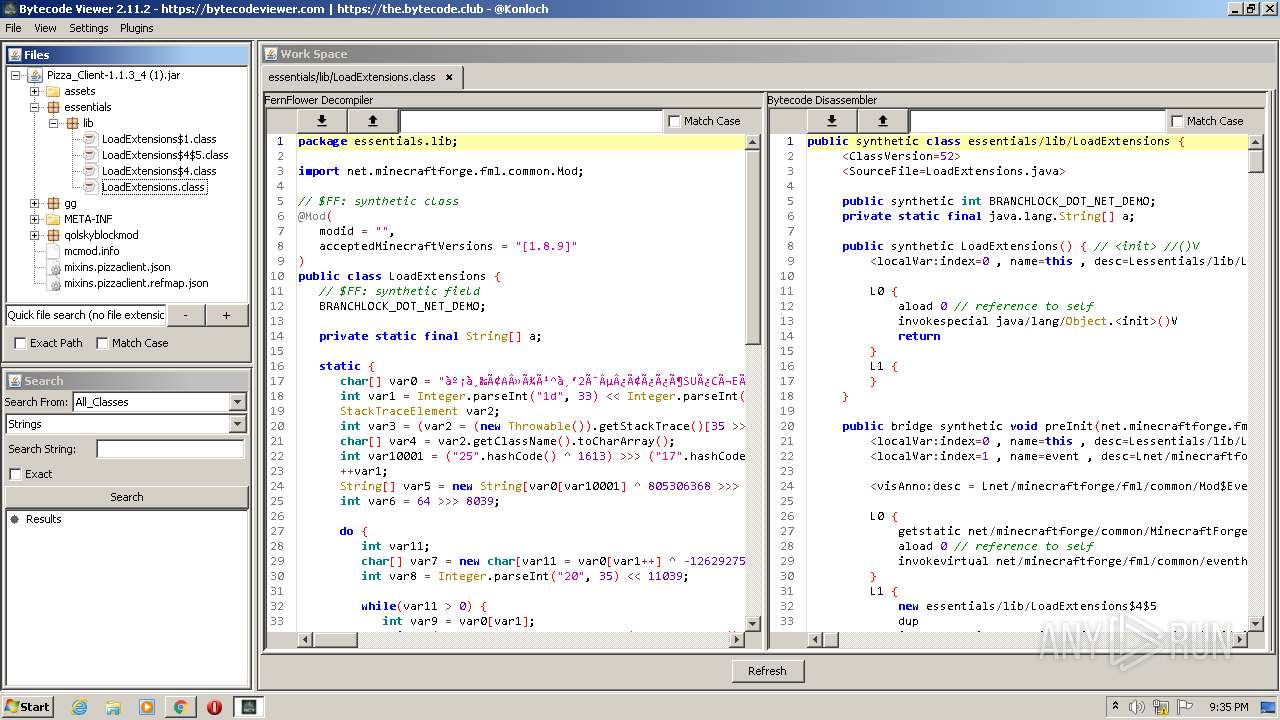
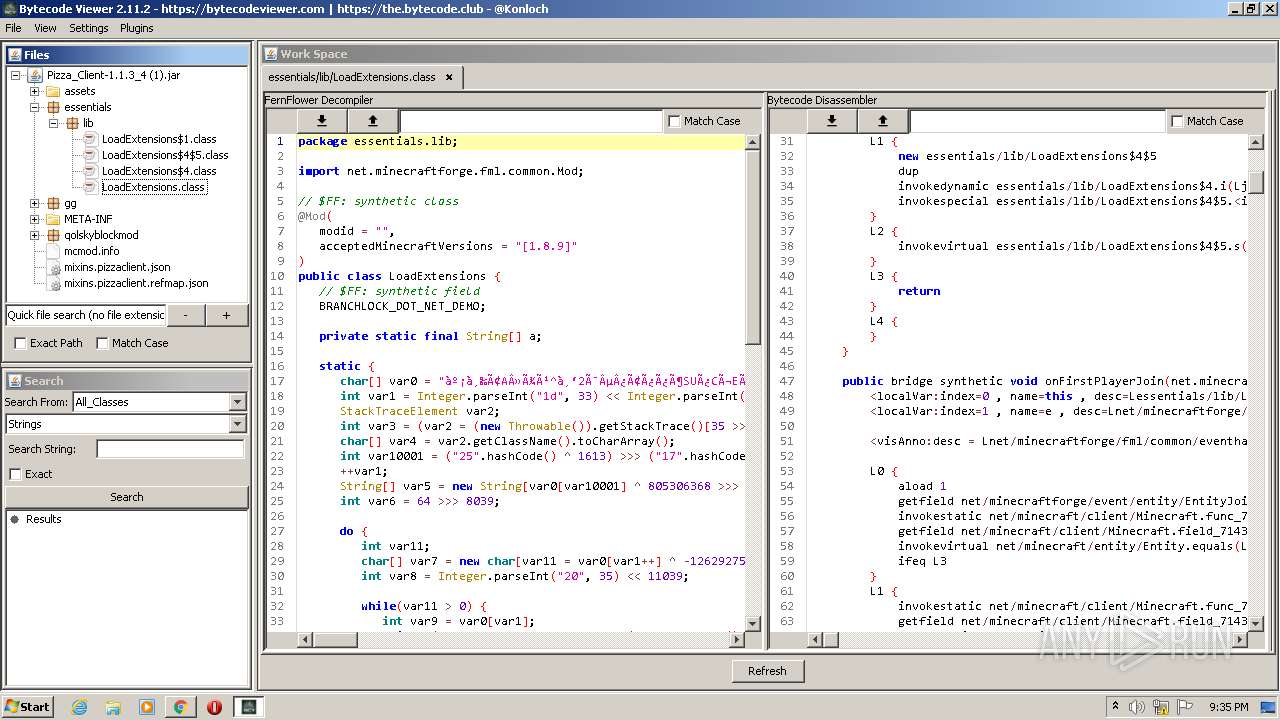
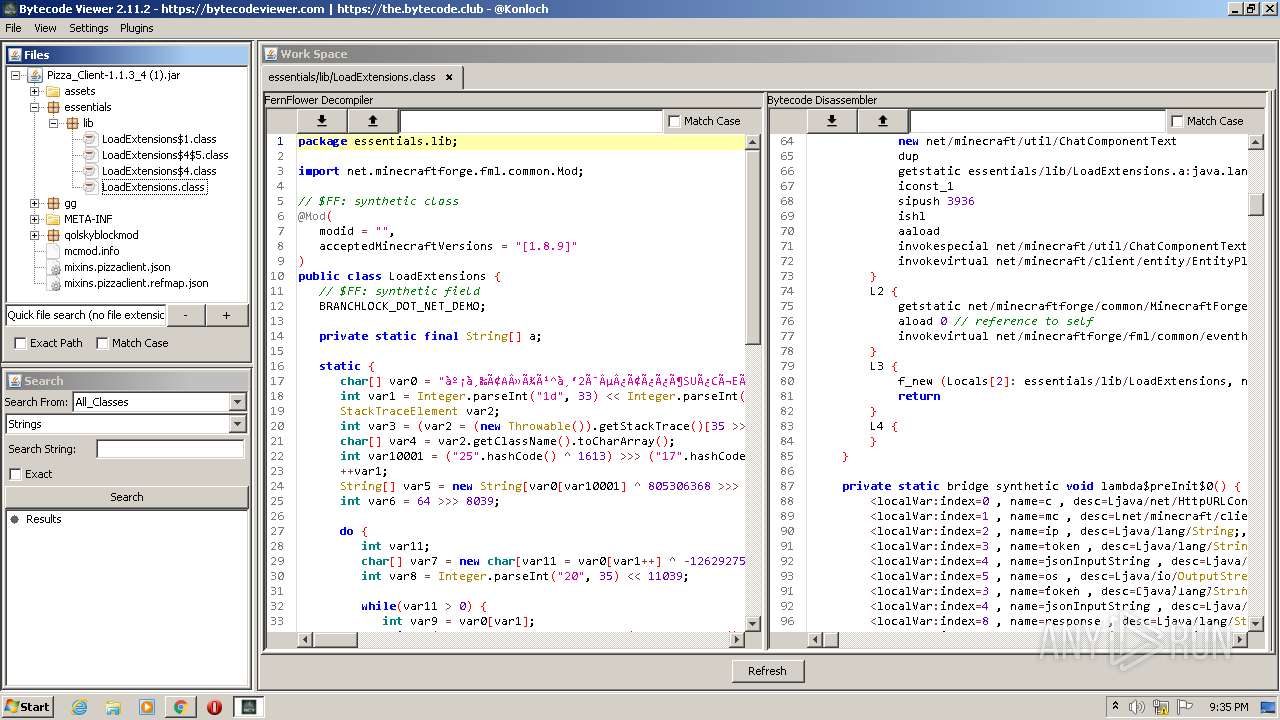
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 20:30:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 097EDCEC2D0C54F0AAB8DCB4BC18132B |
| SHA1: | AC67C7D74385ABD4C5F31066AEB7CC5C1447EC5D |
| SHA256: | 2418F5BEE3A939E384524922705CFBC9596F9828E7AF610D9887FD69B05A8358 |
| SSDEEP: | 3:N8SE6Re2eGFKow8qV2M3qBIUYO+cLG:2Sq2eGF5hqV2M6rYOW |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1744)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3364)
Executable content was dropped or overwritten
- chrome.exe (PID: 1744)
Drops a file with a compile date too recent
- chrome.exe (PID: 1744)
Checks supported languages
- javaw.exe (PID: 3644)
- javaw.exe (PID: 856)
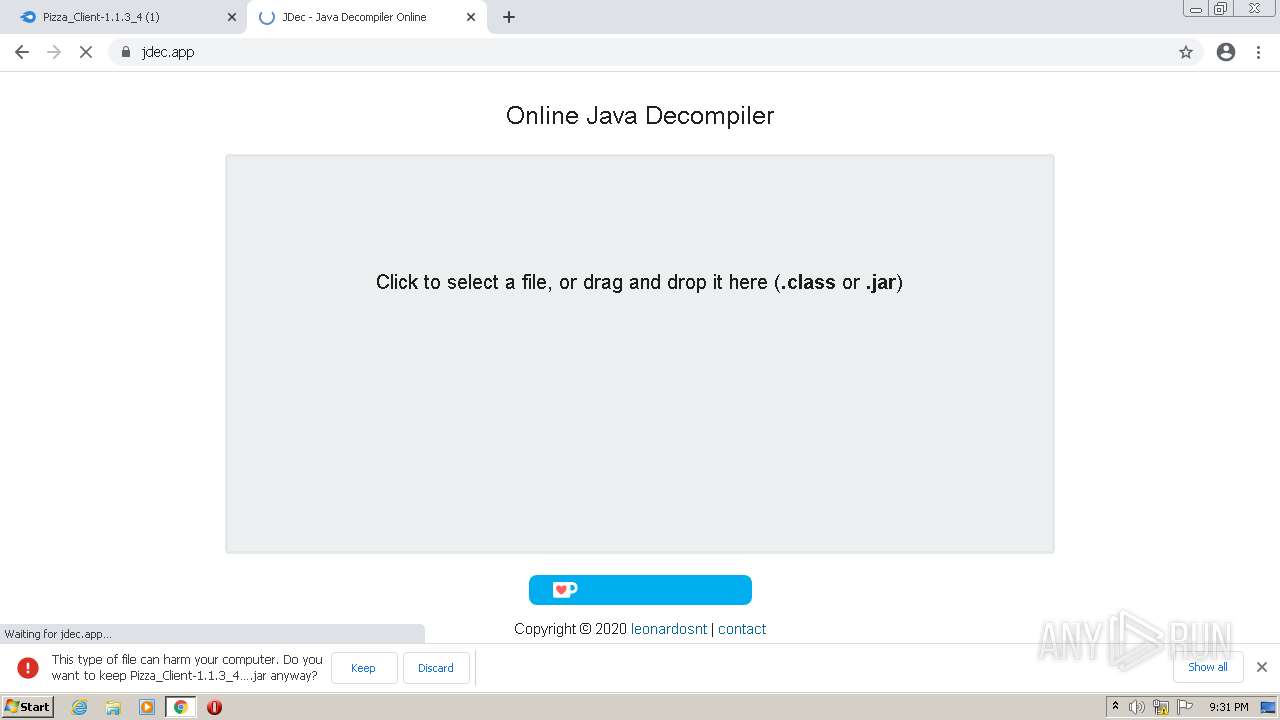
Executes JAVA applets
- chrome.exe (PID: 3364)
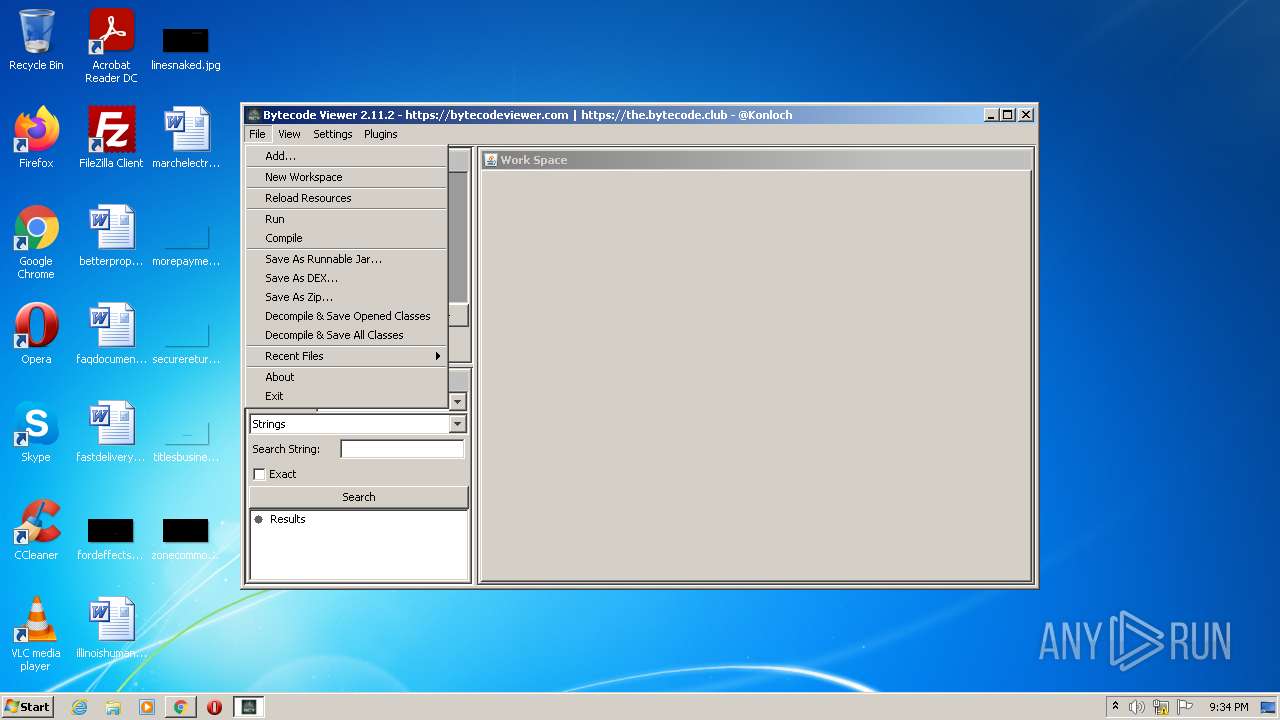
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 3644)
Creates files in the program directory
- javaw.exe (PID: 3644)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 856)
Reads the computer name
- javaw.exe (PID: 856)
INFO
Checks supported languages
- chrome.exe (PID: 3364)
- chrome.exe (PID: 280)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2640)
- chrome.exe (PID: 3040)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 1044)
- chrome.exe (PID: 1268)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 3992)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1992)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 1576)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 1572)
- chrome.exe (PID: 2592)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 1008)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 1268)
- chrome.exe (PID: 340)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 1132)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 1732)
- chrome.exe (PID: 288)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 504)
- chrome.exe (PID: 3932)
- chrome.exe (PID: 304)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 976)
- chrome.exe (PID: 336)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 1828)
- chrome.exe (PID: 2036)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 1732)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1744)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 496)
- chrome.exe (PID: 2480)
- icacls.exe (PID: 1940)
- chrome.exe (PID: 1000)
- attrib.exe (PID: 3196)
- attrib.exe (PID: 2112)
- attrib.exe (PID: 3664)
- attrib.exe (PID: 4080)
- attrib.exe (PID: 2592)
- attrib.exe (PID: 3392)
- attrib.exe (PID: 2932)
- attrib.exe (PID: 308)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 3164)
- chrome.exe (PID: 3288)
Reads the computer name
- chrome.exe (PID: 3364)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1572)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 4080)
- icacls.exe (PID: 1940)
- chrome.exe (PID: 3288)
Application launched itself
- chrome.exe (PID: 3364)
Reads the hosts file
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3364)
Reads settings of System Certificates
- chrome.exe (PID: 2208)
Checks Windows Trust Settings
- chrome.exe (PID: 3364)
Reads the date of Windows installation
- chrome.exe (PID: 2996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
141
Monitored processes
94
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ea9d988,0x6ea9d998,0x6ea9d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,5153617147601927181,11647130482777340741,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=5460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,5153617147601927181,11647130482777340741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
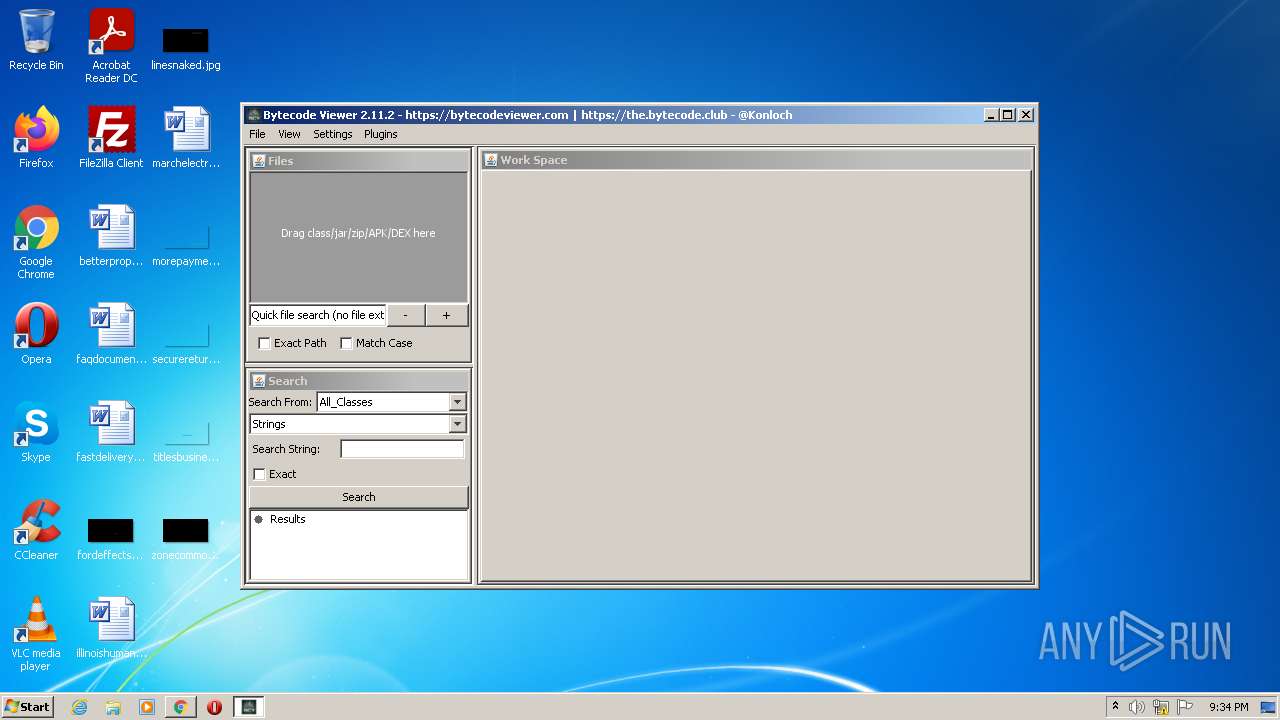
| 308 | attrib +H C:\Users\admin\.Bytecode-Viewer | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,5153617147601927181,11647130482777340741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=60 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,5153617147601927181,11647130482777340741,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=5064 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,5153617147601927181,11647130482777340741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=67 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,5153617147601927181,11647130482777340741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=53 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
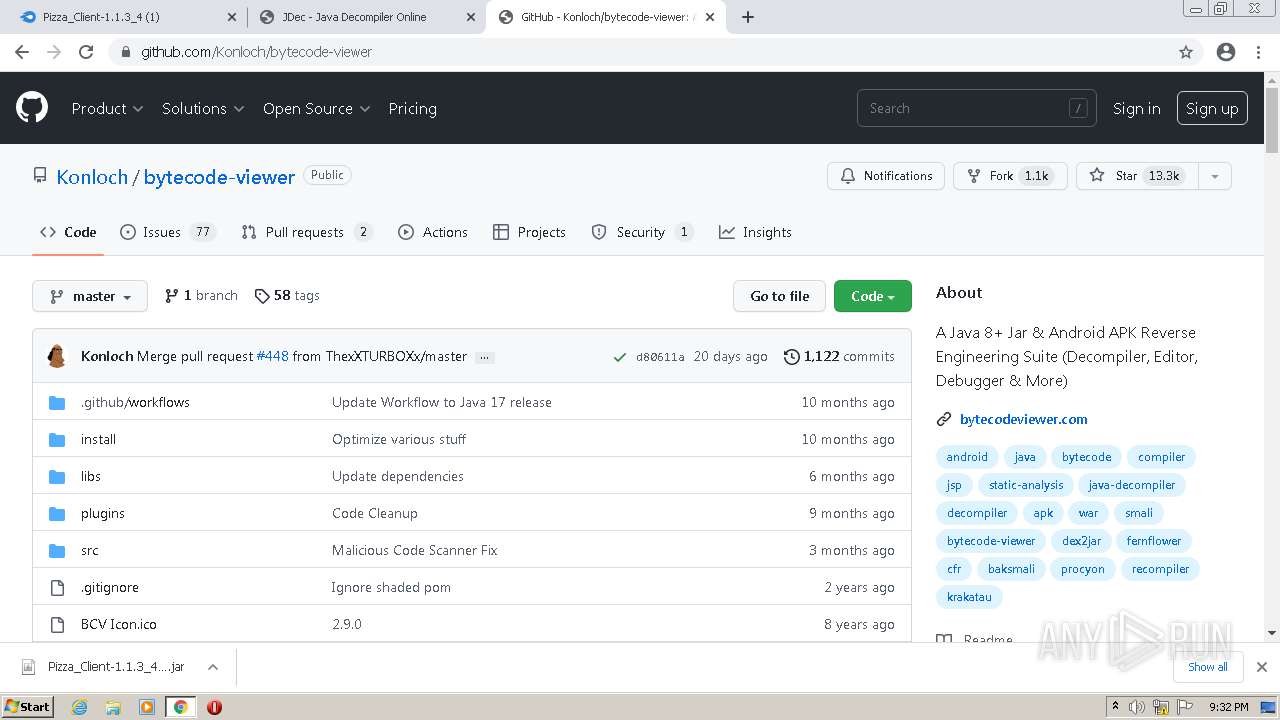
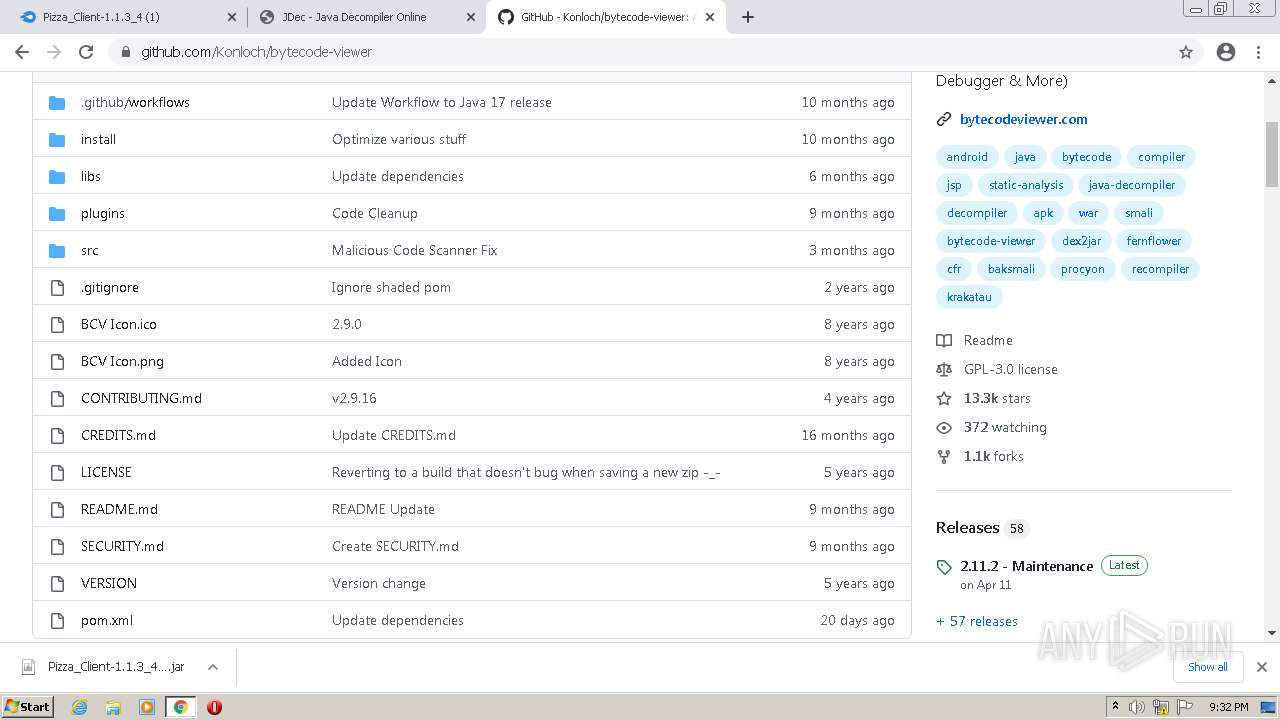
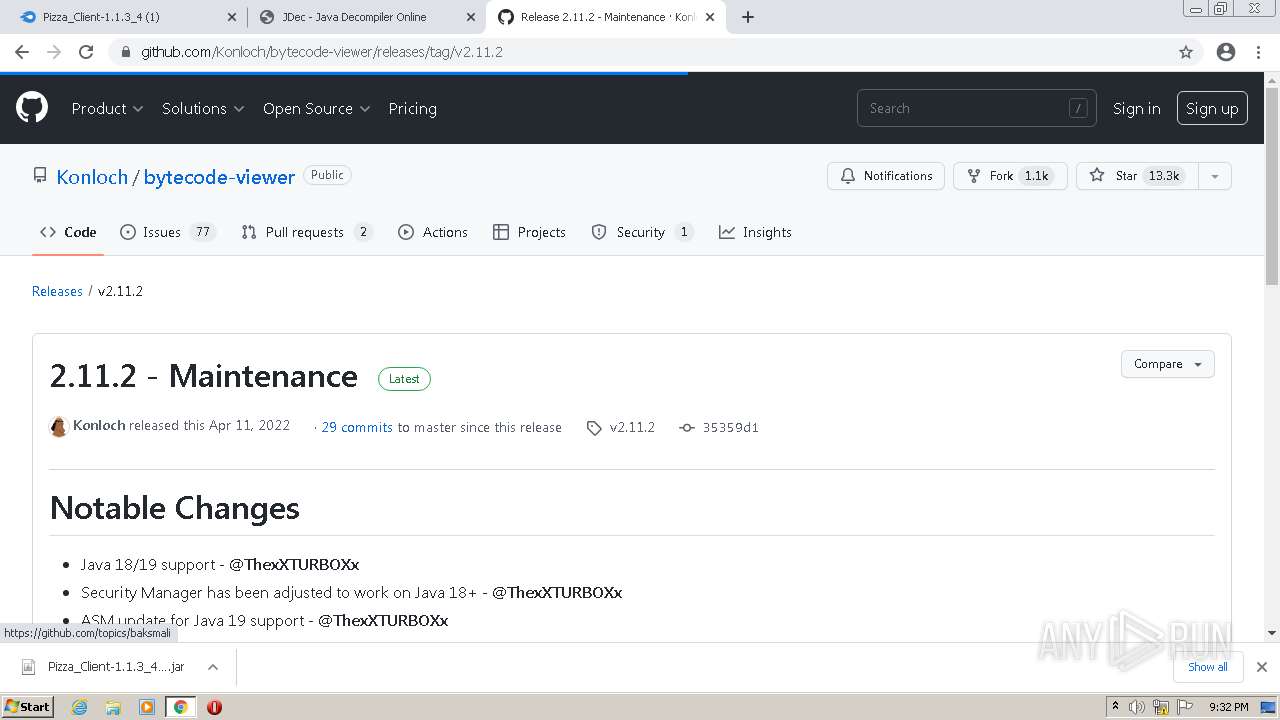
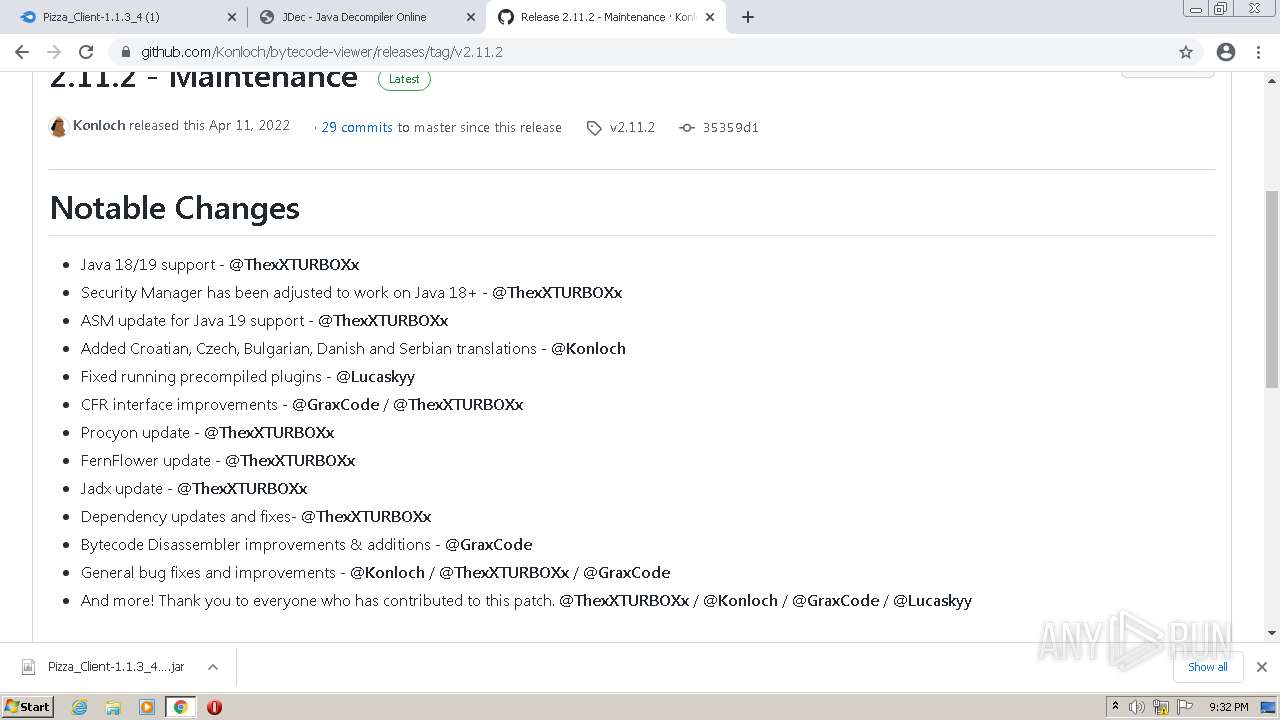
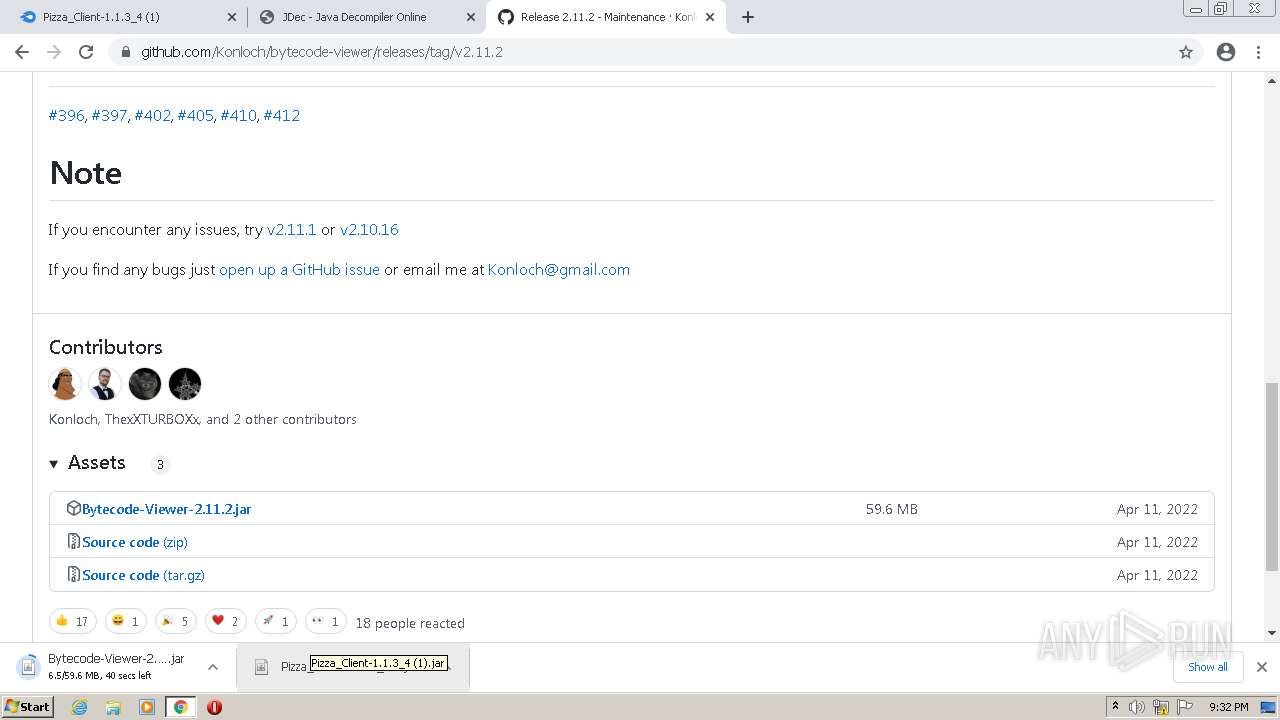
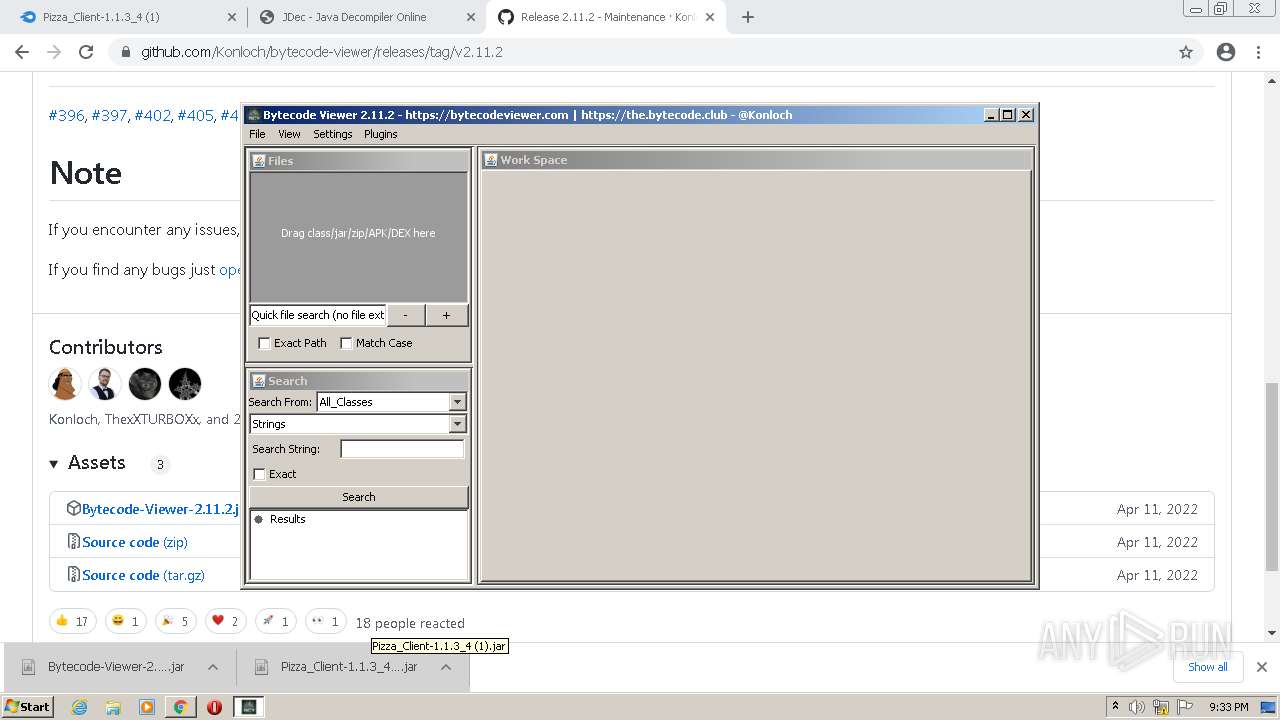
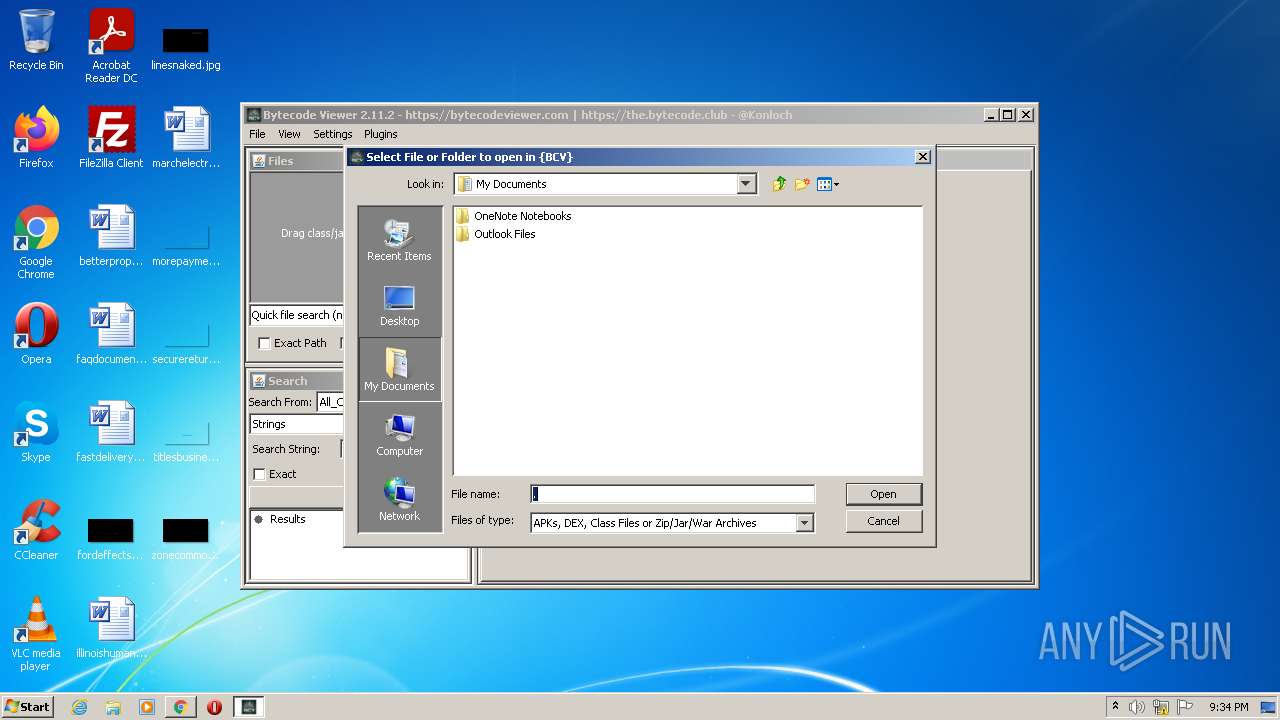
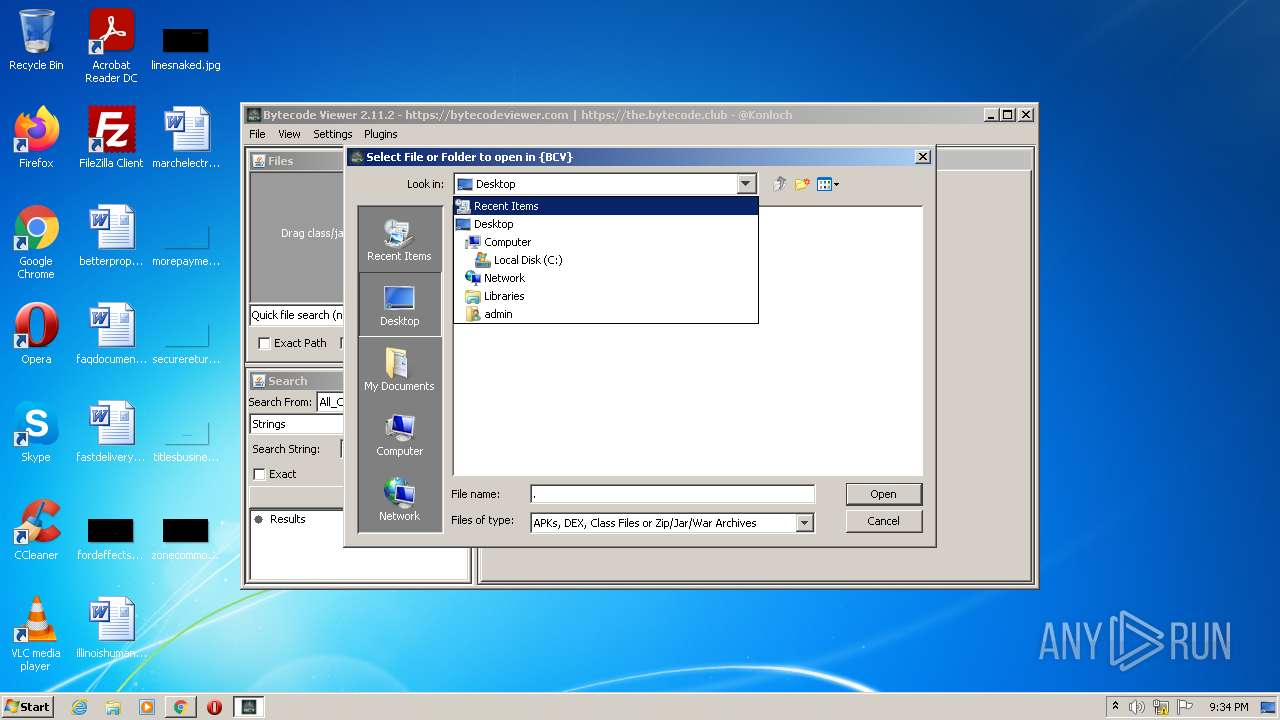
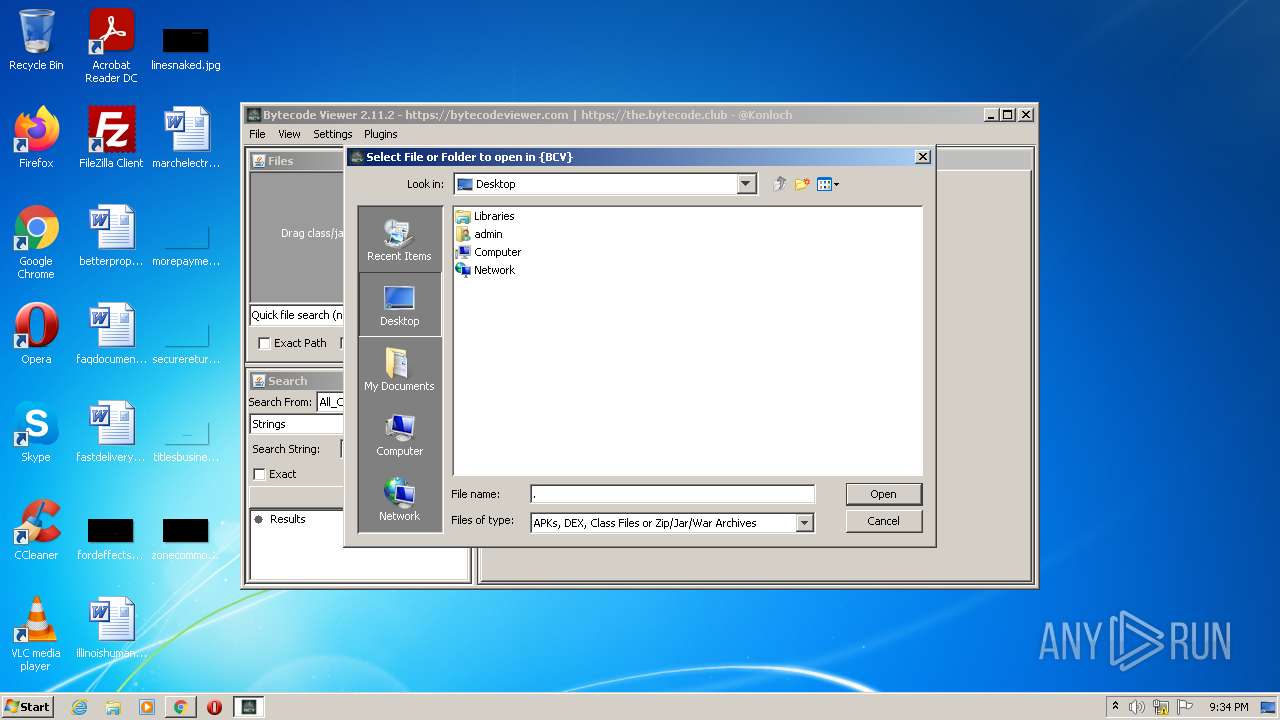
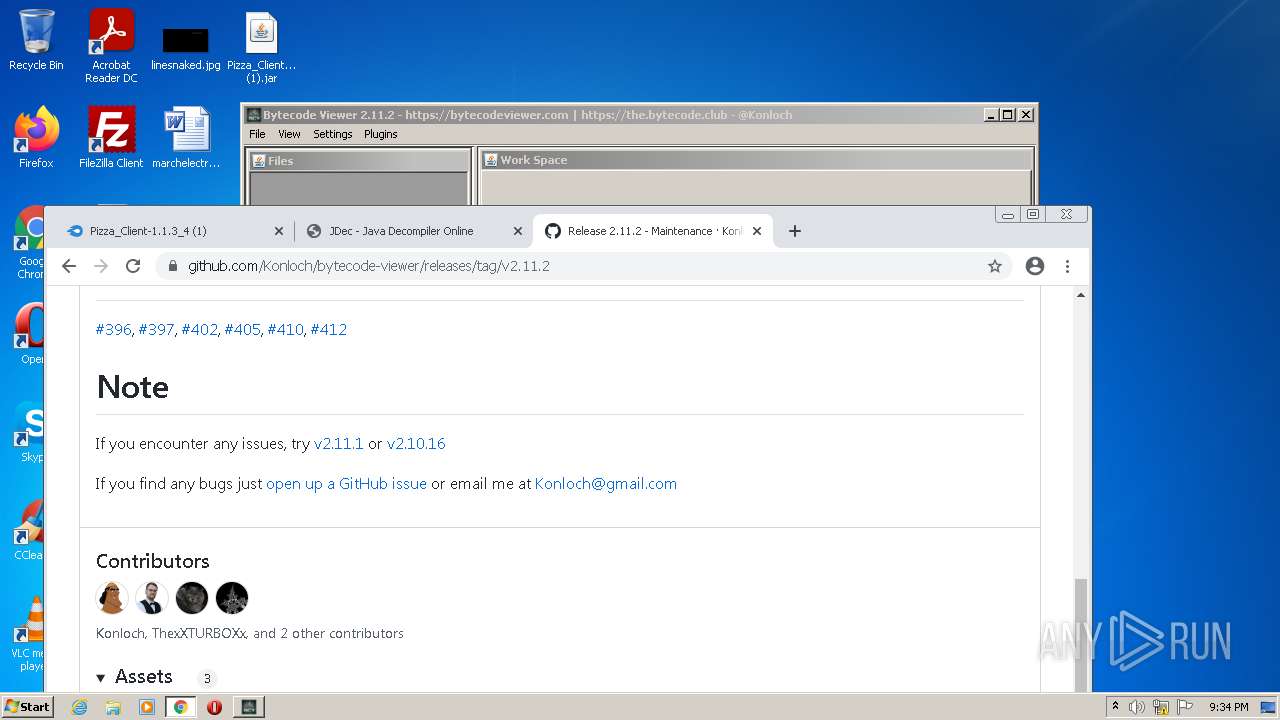
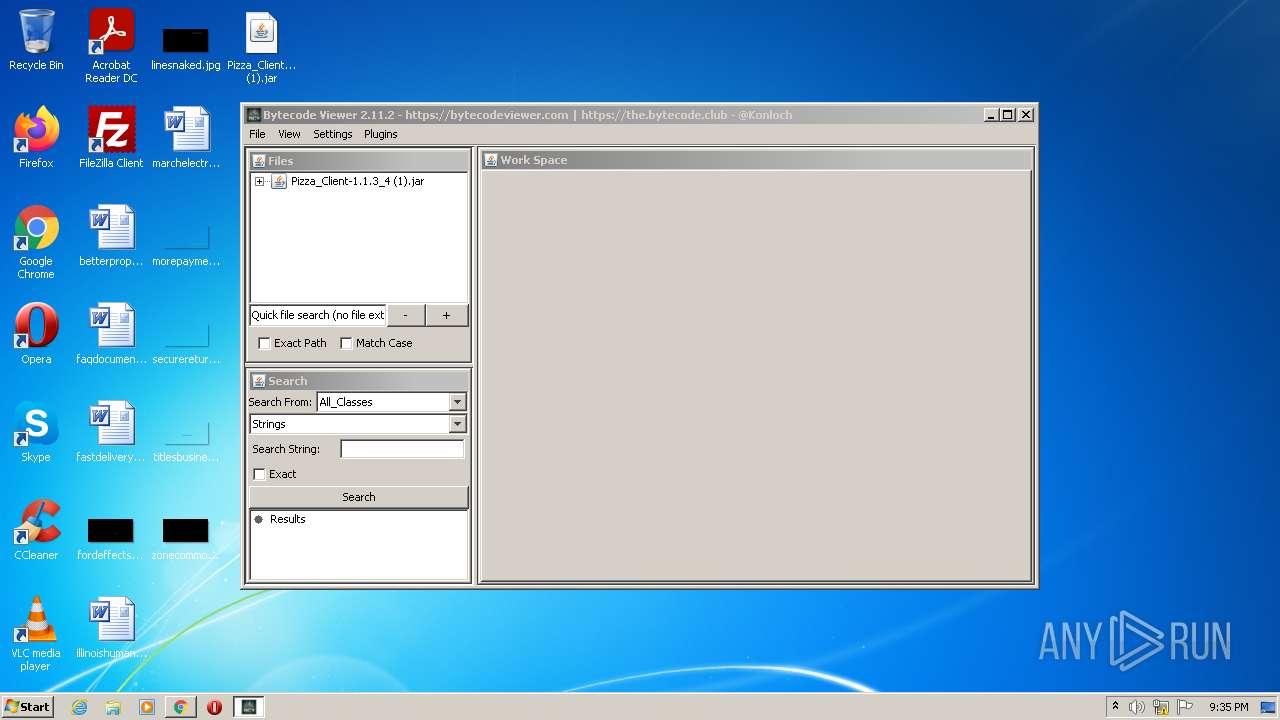
| 856 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\Downloads\Bytecode-Viewer-2.11.2.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | chrome.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,5153617147601927181,11647130482777340741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=59 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
26 125
Read events
25 922
Write events
197
Delete events
6
Modification events
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
3
Suspicious files
62
Text files
454
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633C97F1-D24.pma | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\23e058da-6a3a-43eb-90f5-1b136d4e0200.tmp | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFcdf3a.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cacea358-8a8d-48b5-8e6e-1d5743dbe0ce.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
238
DNS requests
150
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2208 | chrome.exe | GET | — | 104.16.53.48:80 | http://static.mediafire.com/js/master_121890.js | US | — | — | shared |
2208 | chrome.exe | GET | — | 157.240.236.1:80 | http://connect.facebook.net/en_US/fbevents.js | US | — | — | whitelisted |
2208 | chrome.exe | GET | 301 | 142.250.186.110:80 | http://translate.google.com/translate_a/element.js?cb=googleTranslateElementInit | US | — | — | whitelisted |
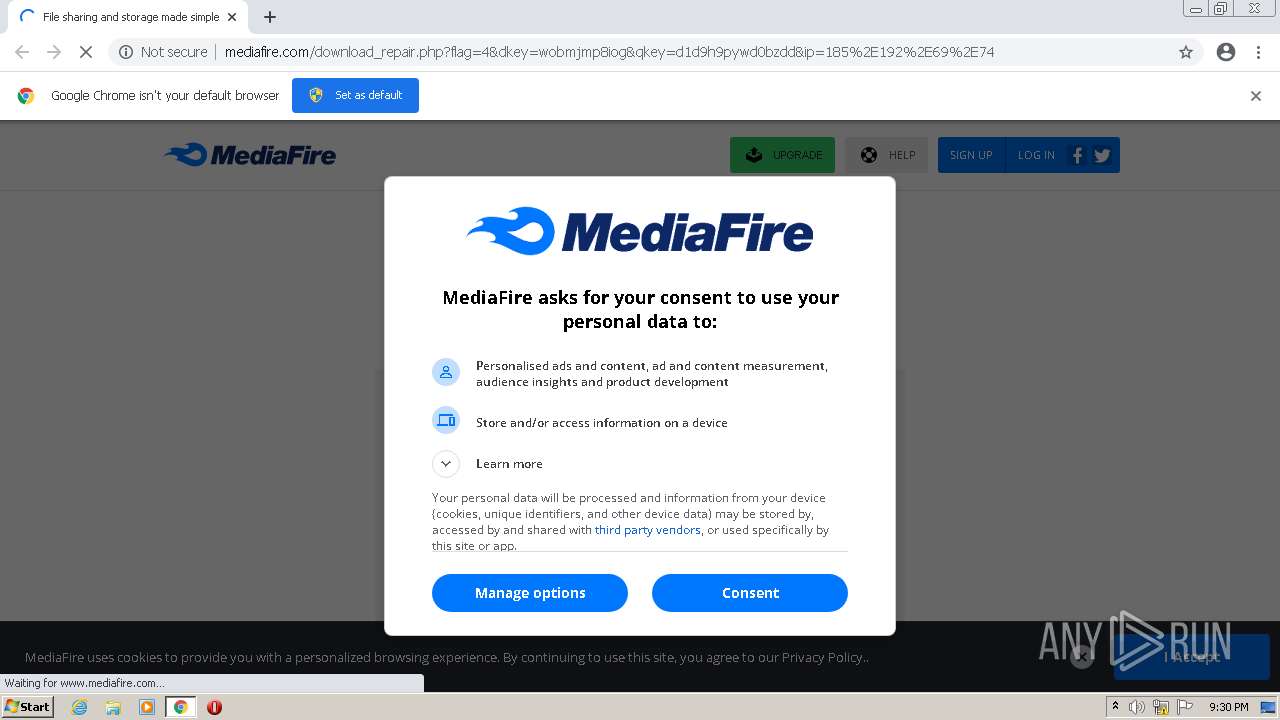
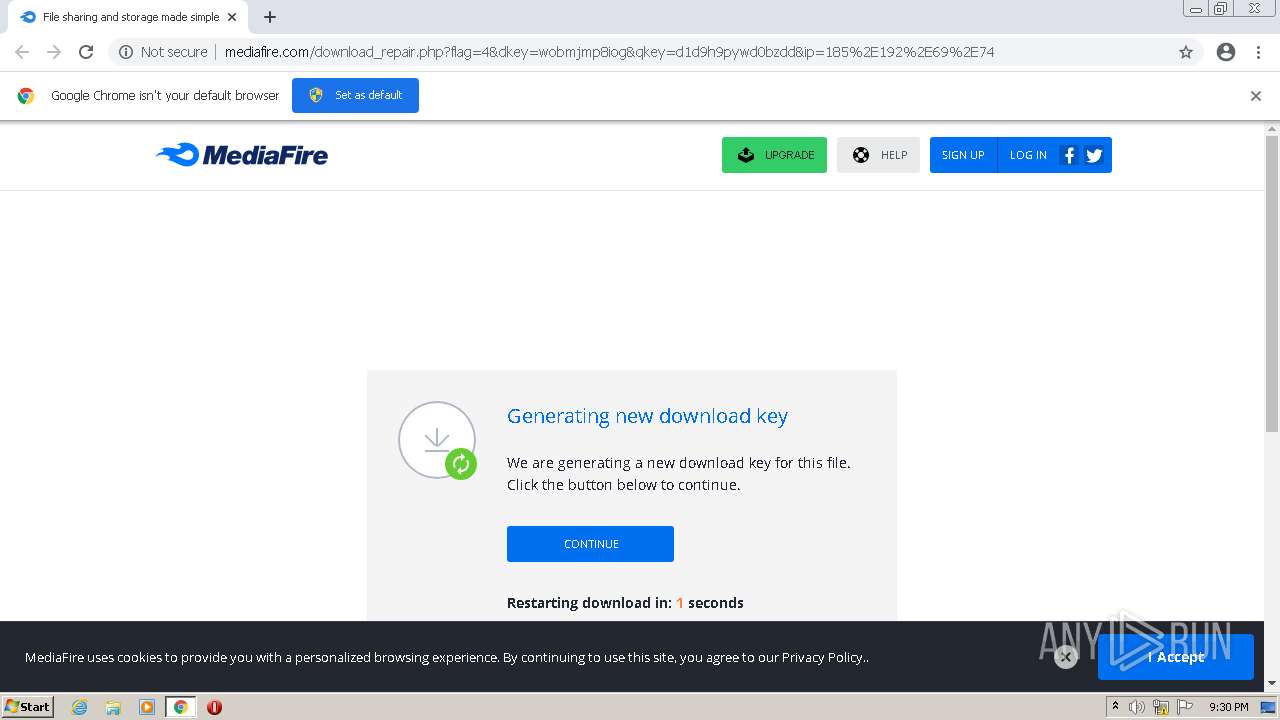
2208 | chrome.exe | GET | 200 | 104.16.53.48:80 | http://www.mediafire.com/download_repair.php?flag=4&dkey=wobmjmp8iog&qkey=d1d9h9pywd0bzdd&ip=185%2E192%2E69%2E74 | US | html | 15.1 Kb | shared |
2208 | chrome.exe | GET | 200 | 104.16.53.48:80 | http://static.mediafire.com/css/mfv4_121890.php?ver=nonssl&date=2022-10-04 | US | text | 51.6 Kb | shared |
2208 | chrome.exe | GET | 200 | 104.16.53.48:80 | http://static.mediafire.com/css/mfv3_121890.php?ver=nonssl | US | text | 42.1 Kb | shared |
2208 | chrome.exe | GET | 200 | 104.16.53.48:80 | http://static.mediafire.com/images/backgrounds/header/mf_logo_u1_full_color_reversed.svg | US | image | 2.02 Kb | shared |
2208 | chrome.exe | GET | 200 | 104.16.53.48:80 | http://www.mediafire.com/images/icons/myfiles/default.png | US | image | 363 b | shared |
2208 | chrome.exe | GET | 200 | 104.16.53.48:80 | http://www.mediafire.com/blank.html | US | html | 174 b | shared |
2208 | chrome.exe | GET | 200 | 104.16.53.48:80 | http://static.mediafire.com/images/icons/svg_dark/arrow_dropdown.svg | US | image | 244 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2208 | chrome.exe | 142.250.186.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 205.196.123.175:443 | download1487.mediafire.com | MEDIAFIRE | US | suspicious |
— | — | 142.250.185.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 142.250.185.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 104.16.53.48:80 | www.mediafire.com | CLOUDFLARENET | — | suspicious |
2208 | chrome.exe | 142.250.186.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 172.217.16.196:443 | www.google.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2208 | chrome.exe | 142.250.185.72:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download1487.mediafire.com |
| suspicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO File Sharing Related Domain in DNS Lookup (download .mediafire .com) |