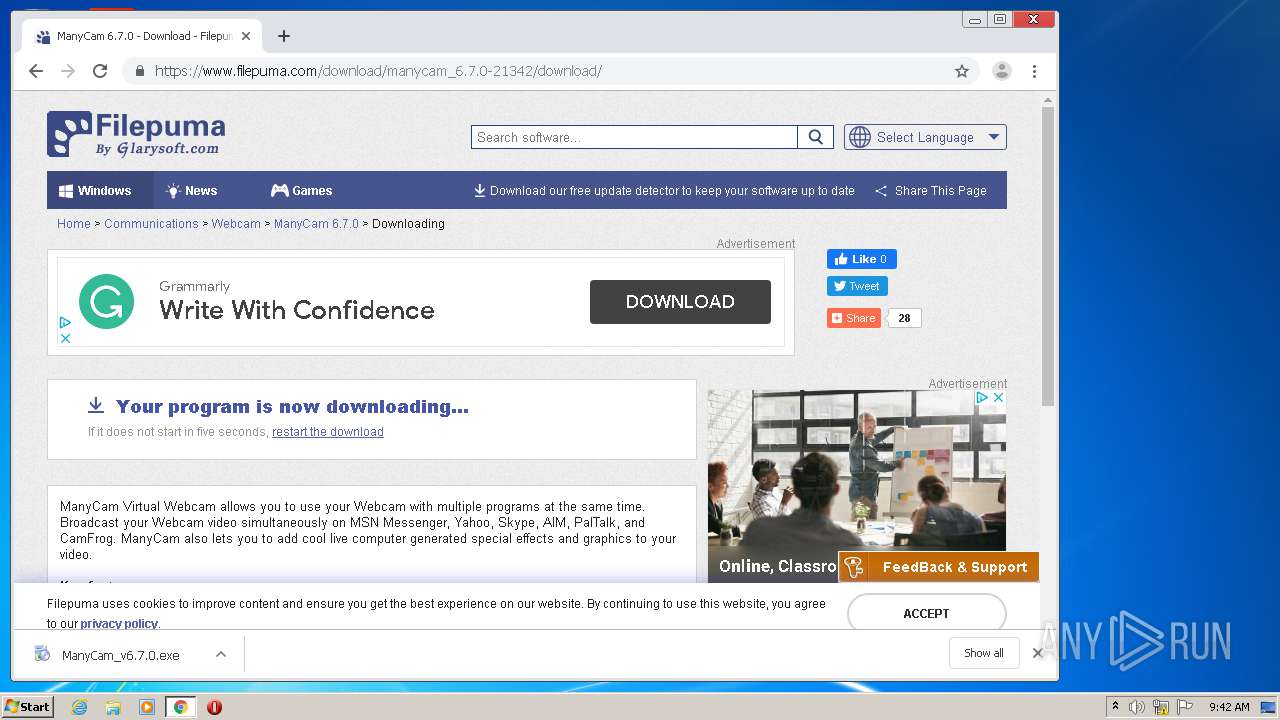
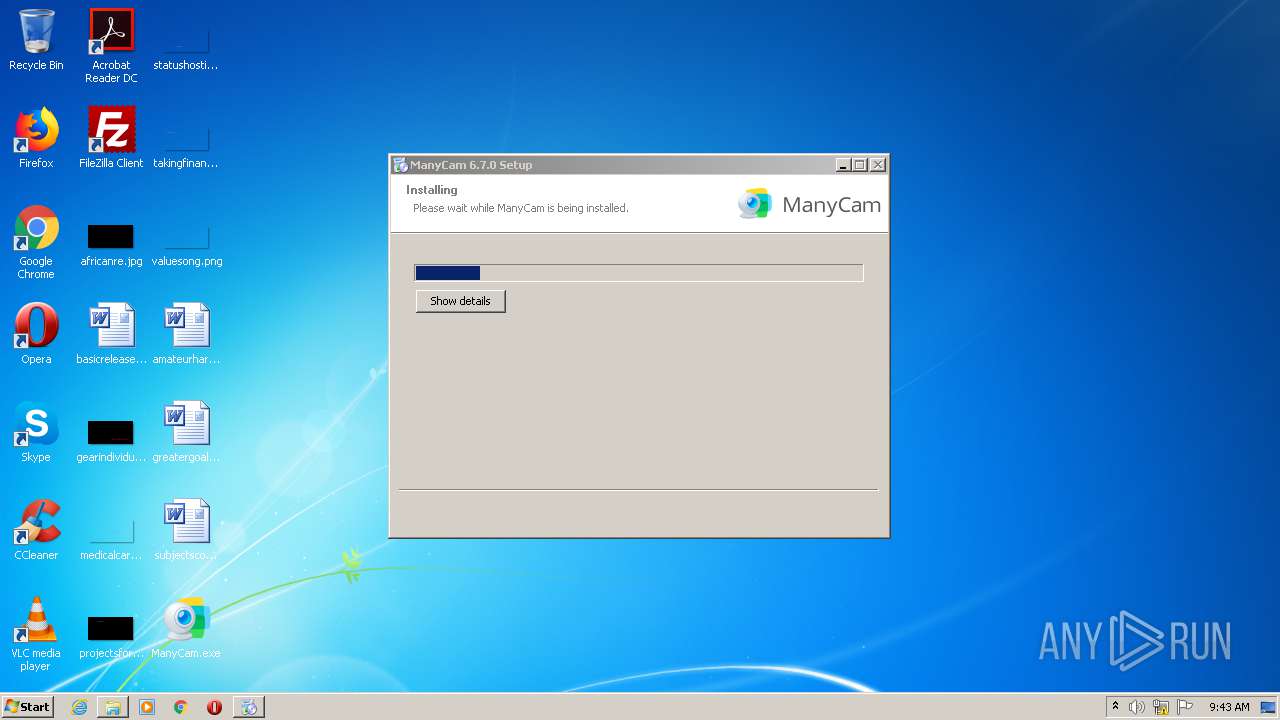
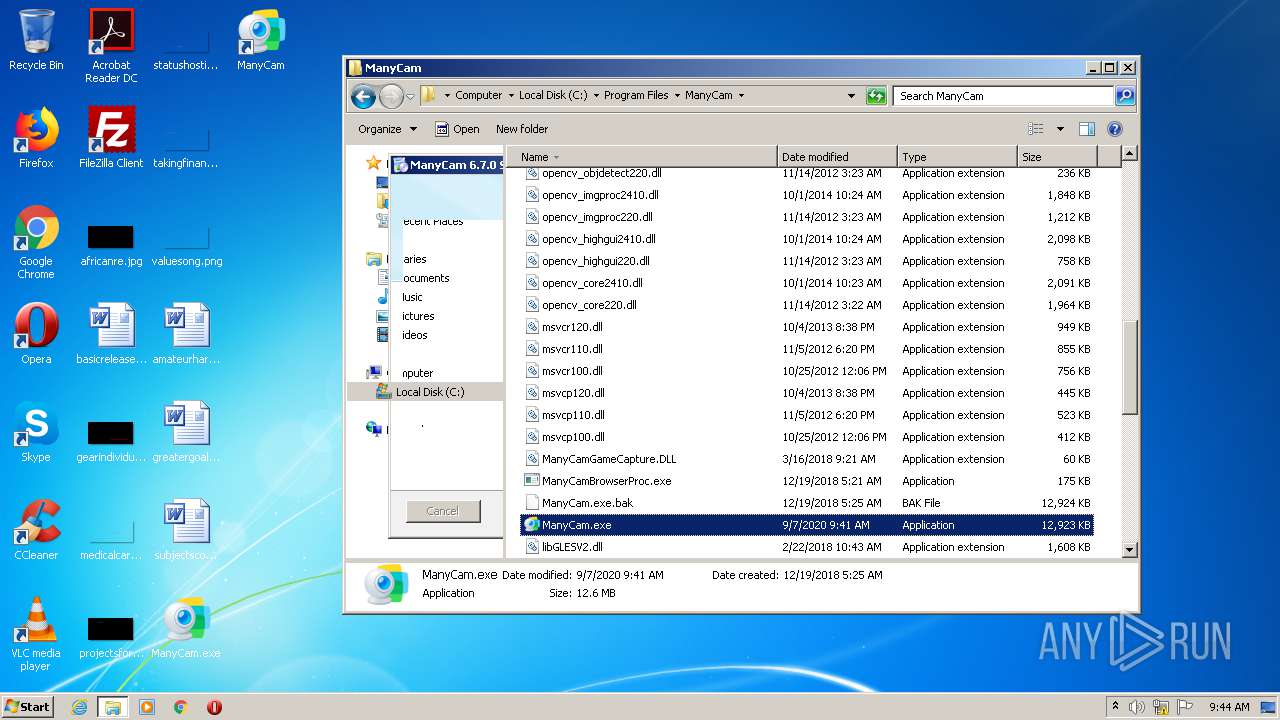
| File name: | ManyCam.exe |
| Full analysis: | https://app.any.run/tasks/77202004-0b0b-4ec8-b874-7609fc8c3da1 |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2020, 08:40:51 |
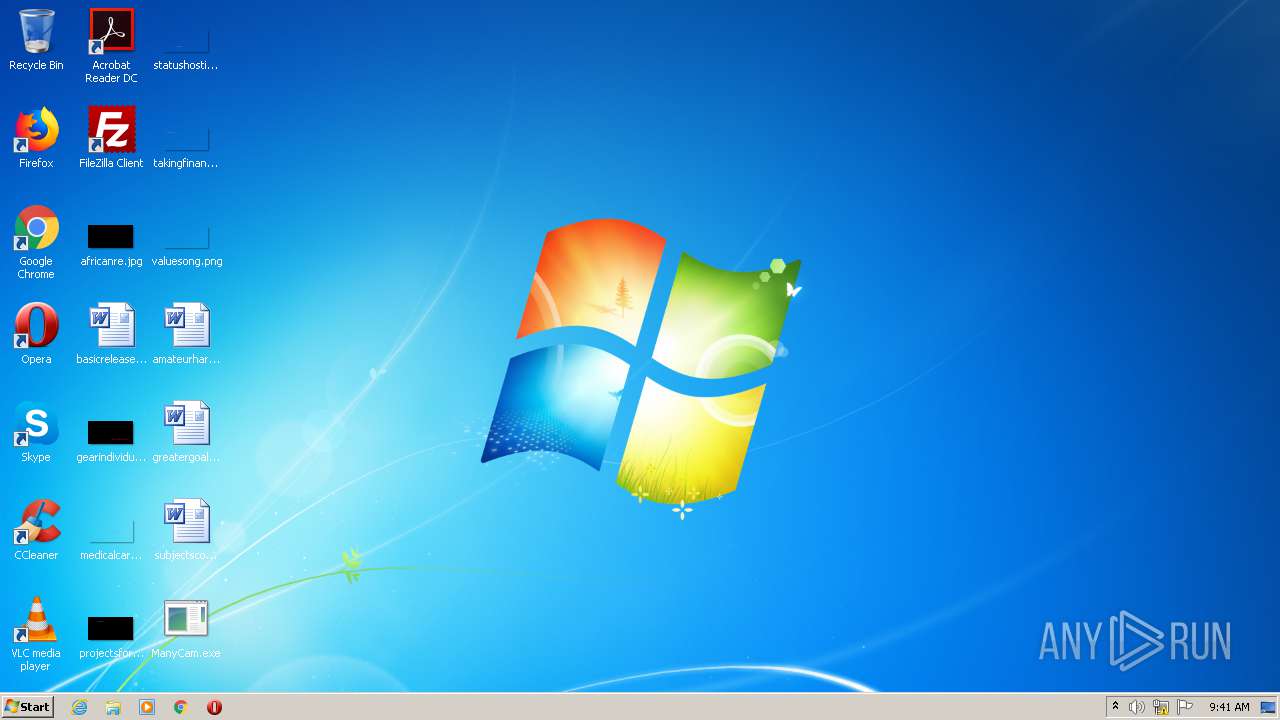
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 37CD2AB6AB9AA70F8E401B4500CB0031 |
| SHA1: | 2F9B360F7BCA2A2B9A857DE2F95786E8C885E67B |
| SHA256: | 23F69EDF9ED62A459C566FCD09C6FACA5BE5452D94070133D4ACCDA614E8DAA5 |
| SSDEEP: | 393216:ZCbFFUJ2hbqMBlIKyj6jFRFORMKTScPy0yRQZ4M:MUoqMCgFGPGcPXyzM |
MALICIOUS
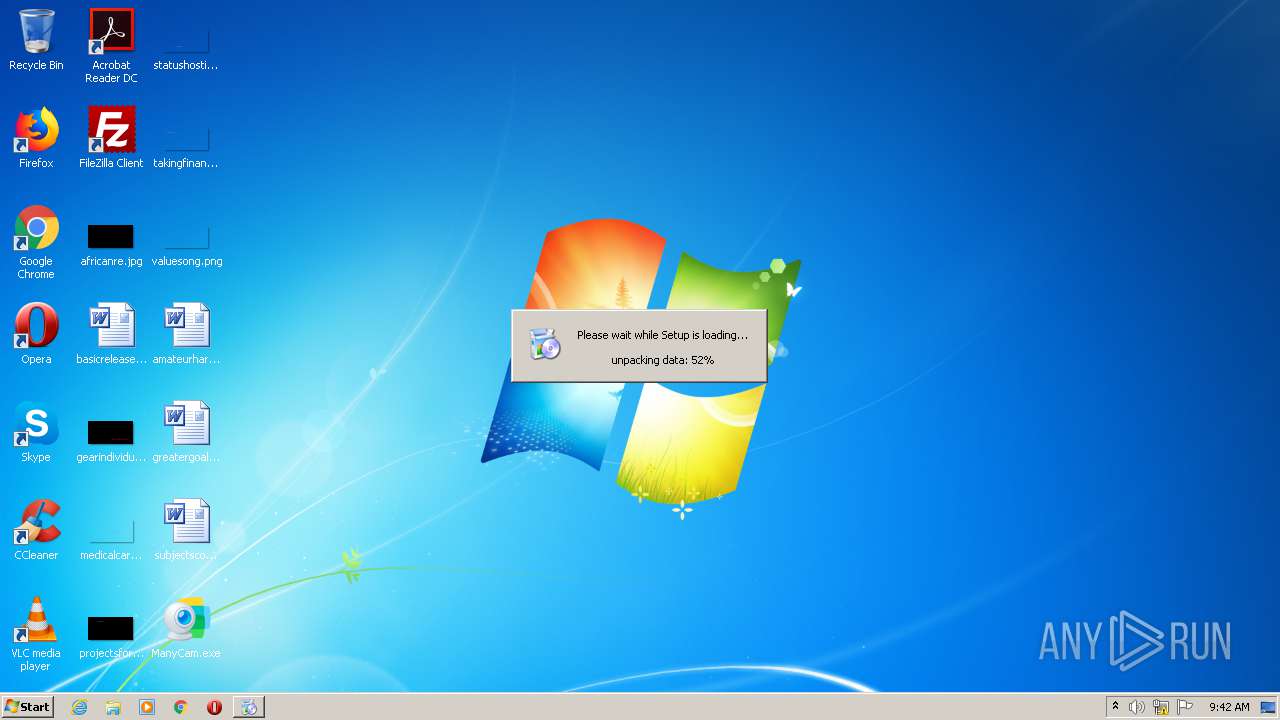
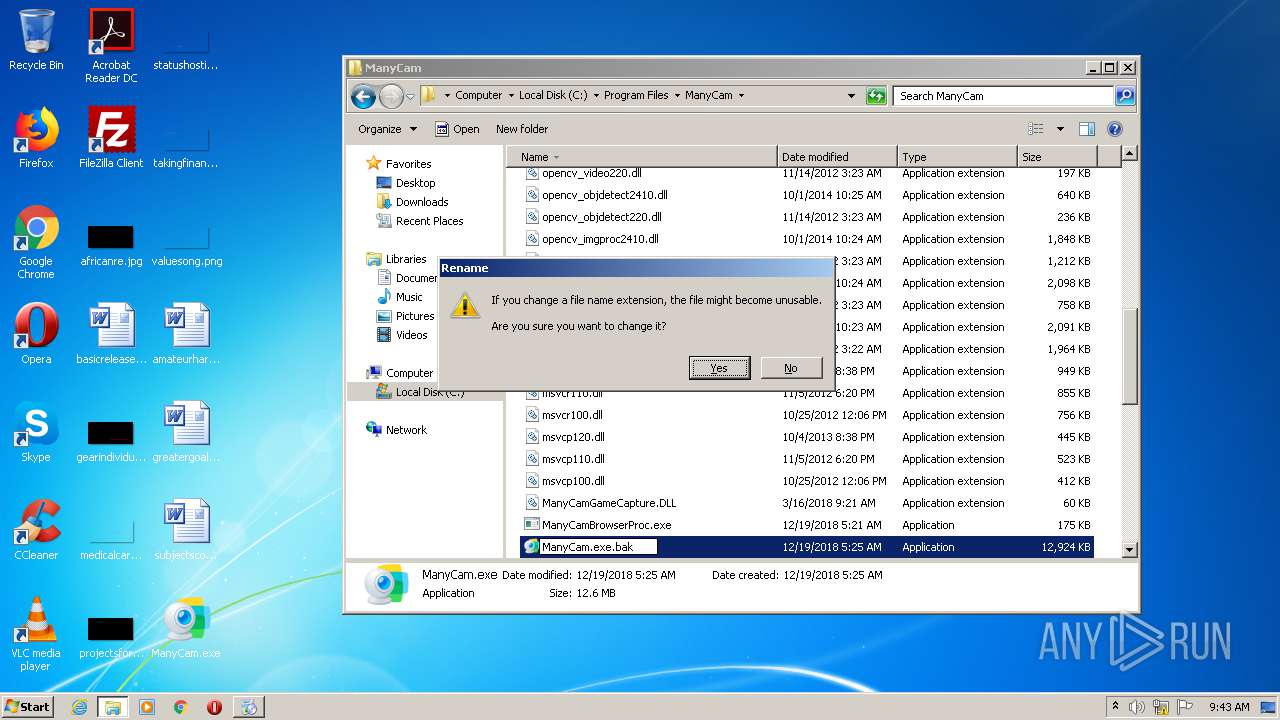
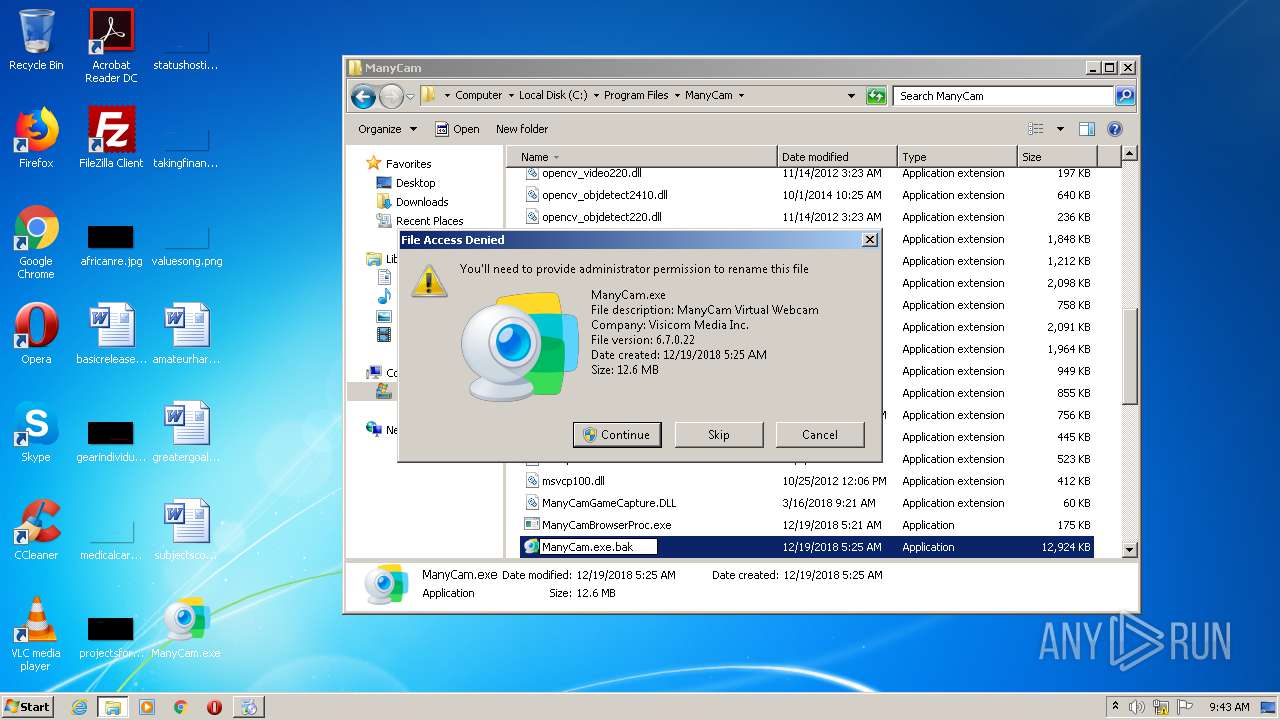
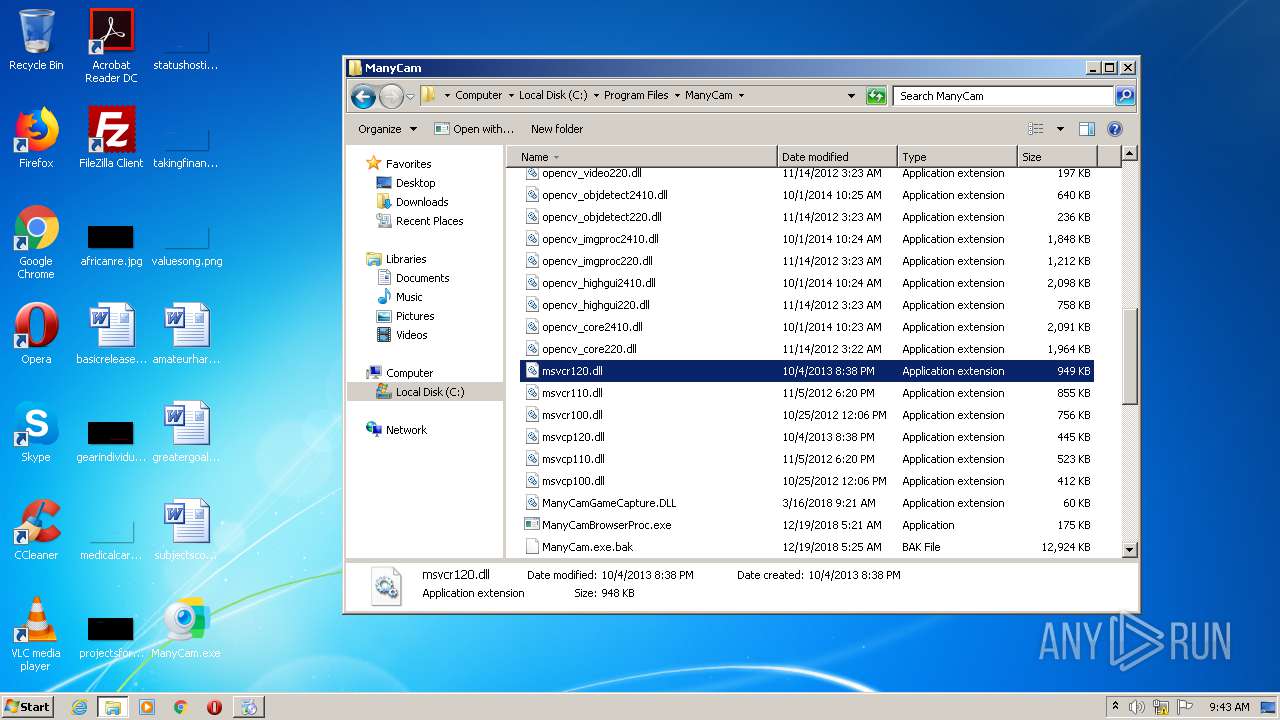
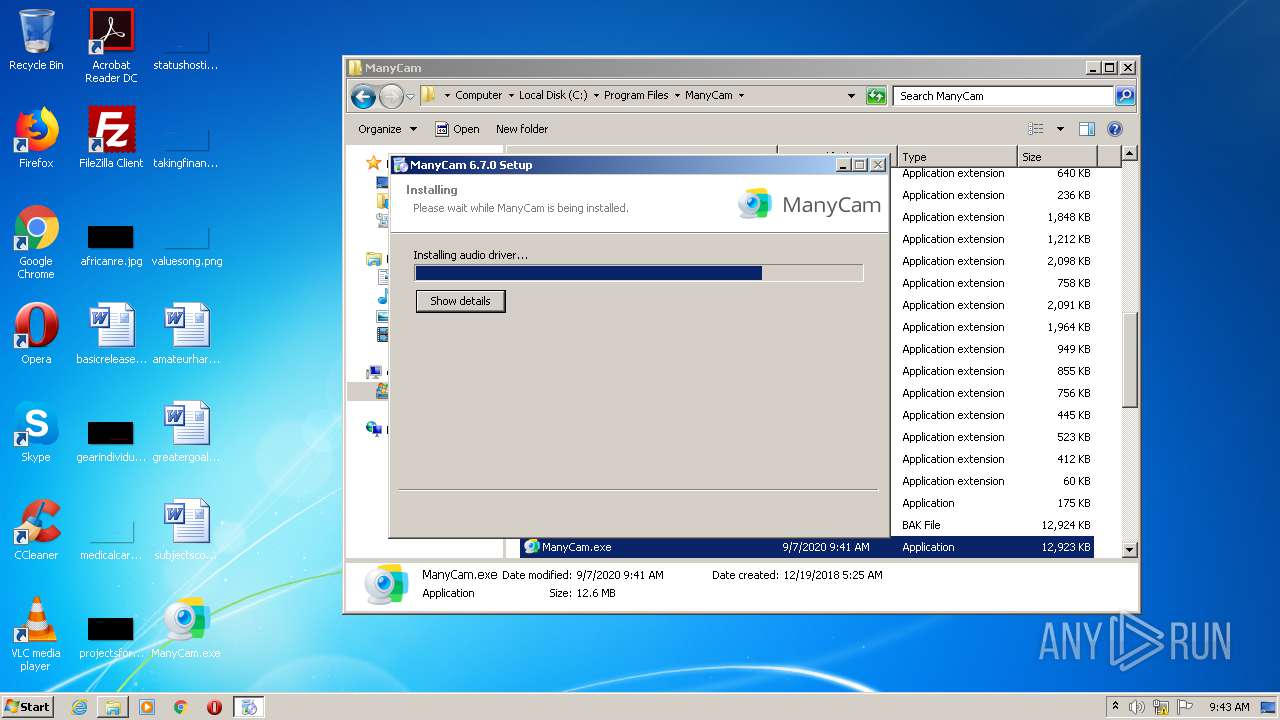
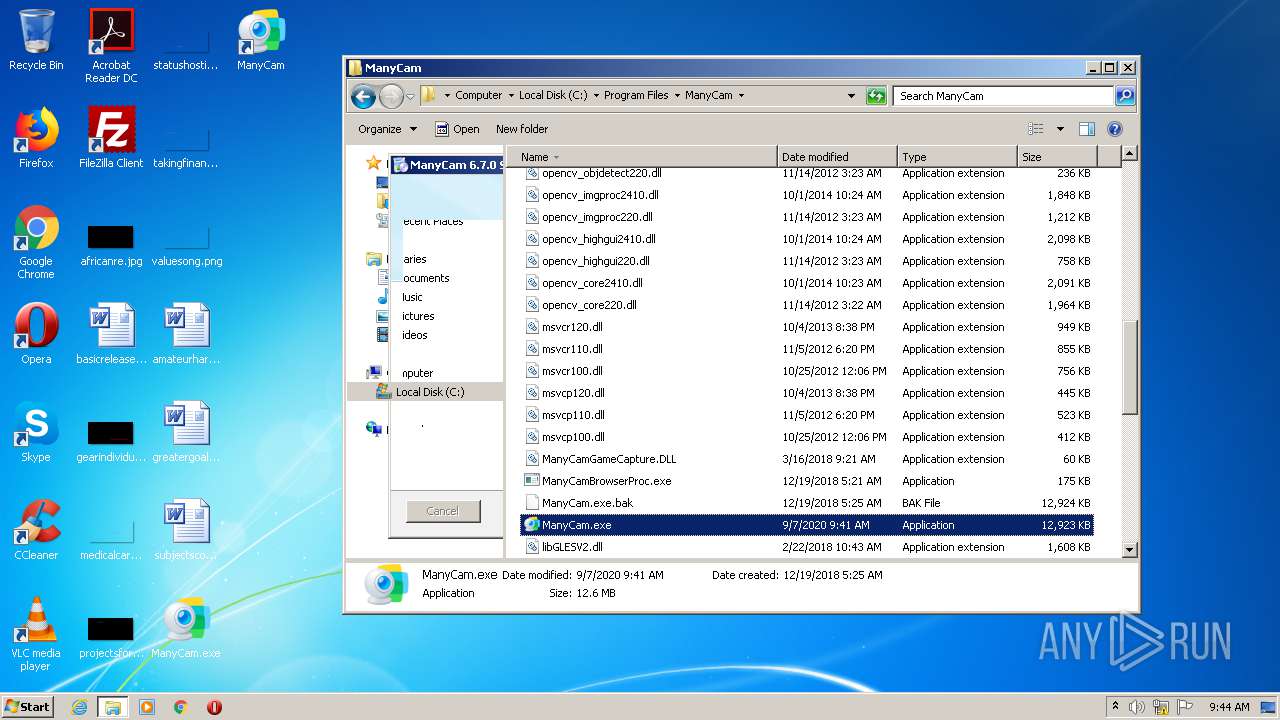
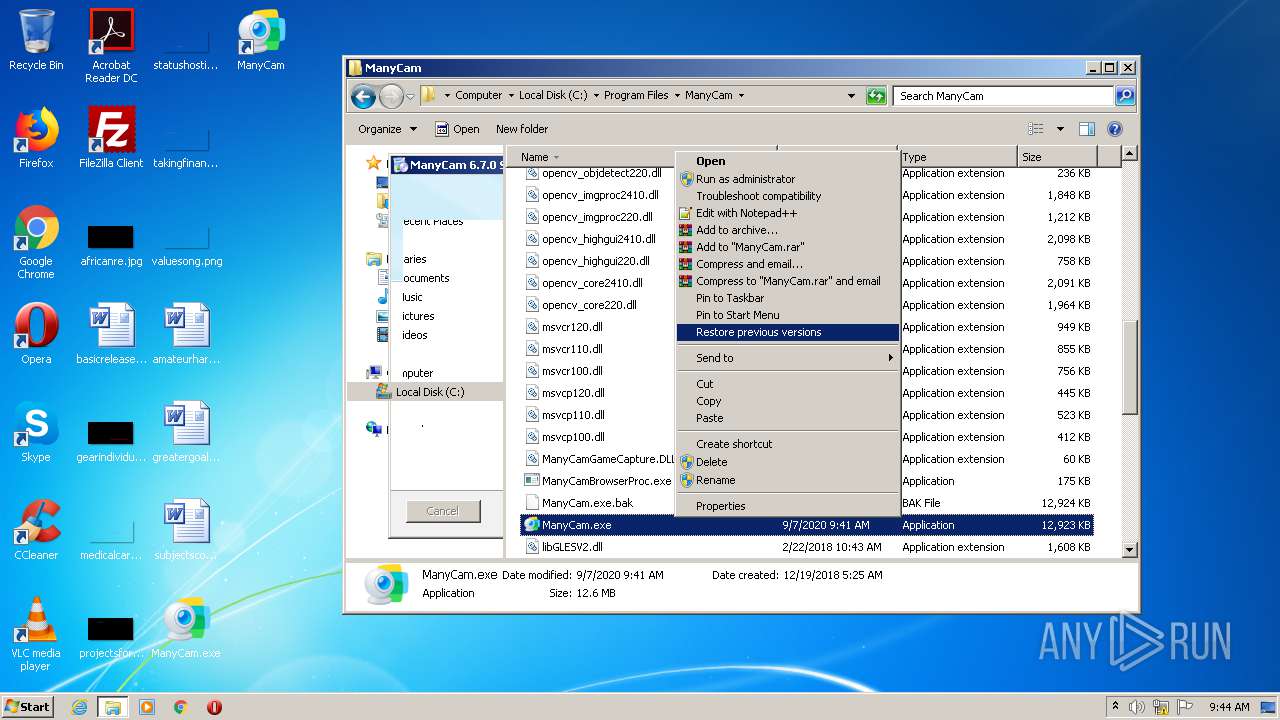
Loads dropped or rewritten executable
- ManyCam_v6.7.0.exe (PID: 3112)
- ManyCam_v6.7.0.exe (PID: 3928)
- explorer.exe (PID: 1704)
- ManyCam.exe (PID: 3168)
- WerFault.exe (PID: 4000)
- WerFault.exe (PID: 1724)
- ManyCam.exe (PID: 3600)
- ManyCam.exe (PID: 2236)
- ManyCam.exe (PID: 3292)
Application was dropped or rewritten from another process
- ManyCam_v6.7.0.exe (PID: 3112)
- ManyCam_v6.7.0.exe (PID: 3928)
- mdsu.exe (PID: 2928)
- mdsu.exe (PID: 776)
- mdsu.exe (PID: 2860)
- mdsu.exe (PID: 3672)
- ManyCamService.exe (PID: 2344)
- ManyCamService.exe (PID: 1076)
- ManyCamService.exe (PID: 2976)
- mdsu.exe (PID: 1348)
- mdsu.exe (PID: 3936)
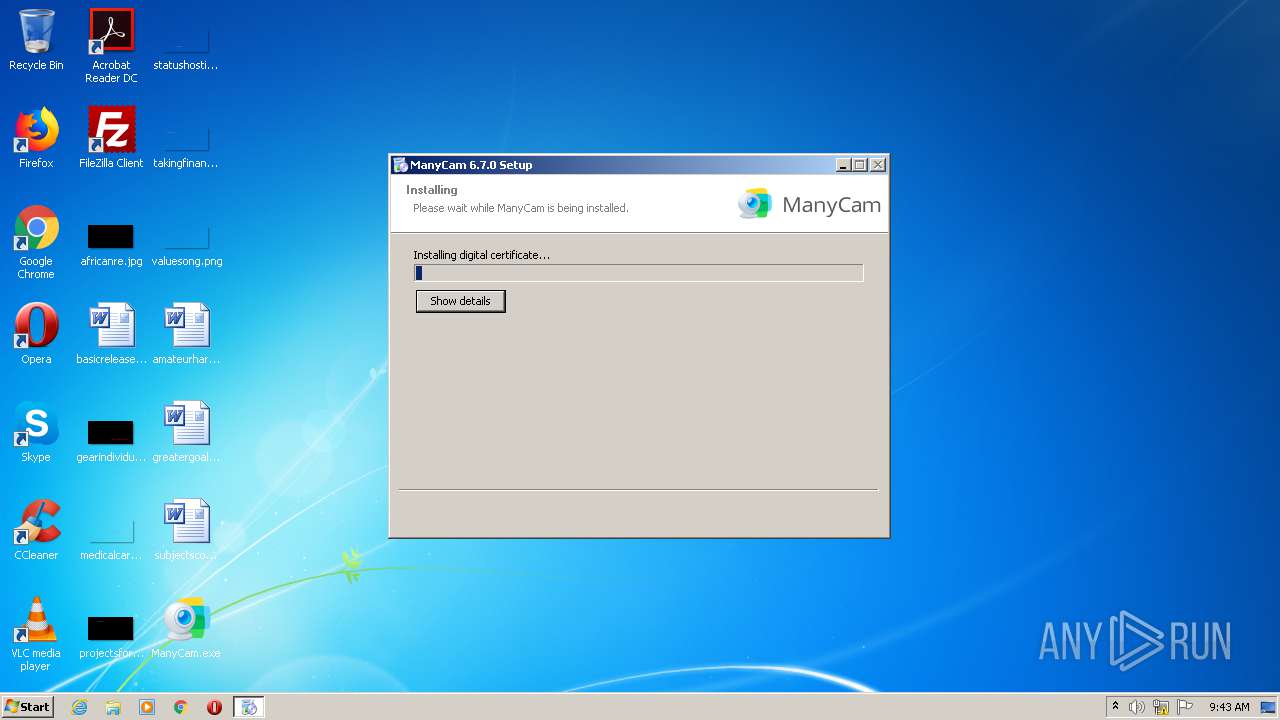
Changes settings of System certificates
- certutil.exe (PID: 2568)
- certutil.exe (PID: 2520)
- mdsu.exe (PID: 776)
- mdsu.exe (PID: 3672)
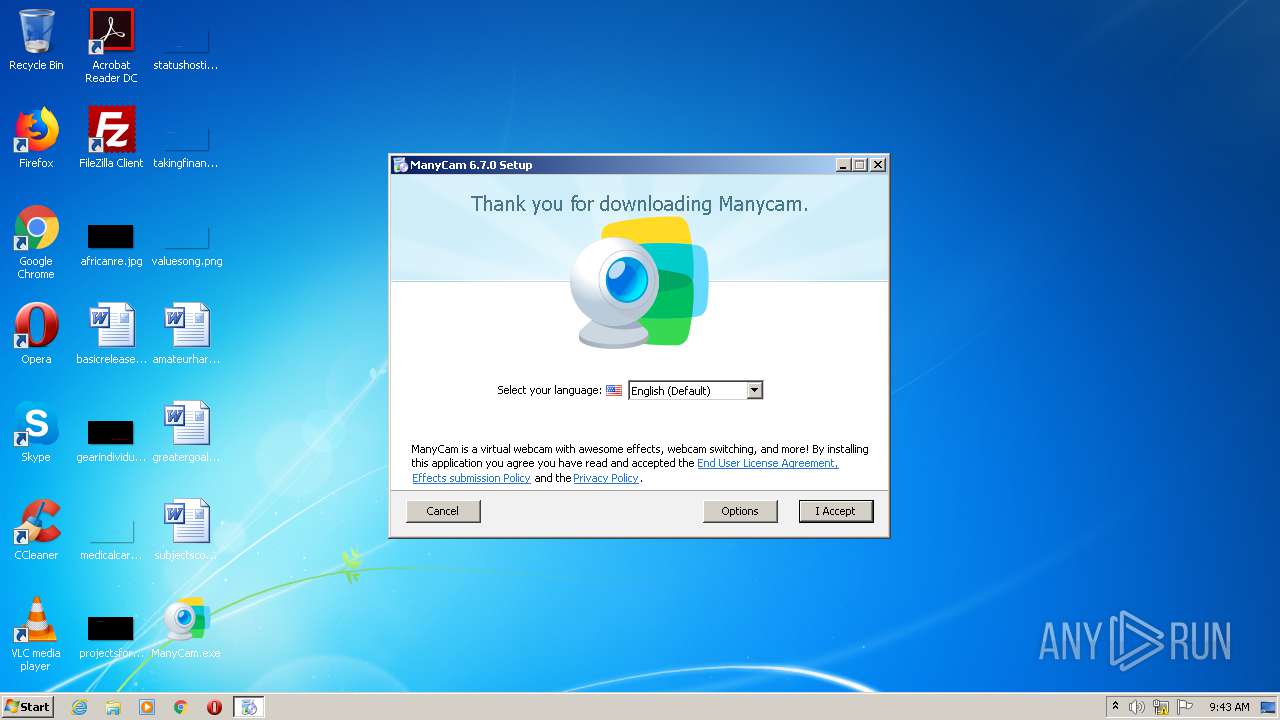
Changes the autorun value in the registry
- ManyCam_v6.7.0.exe (PID: 3112)
SUSPICIOUS
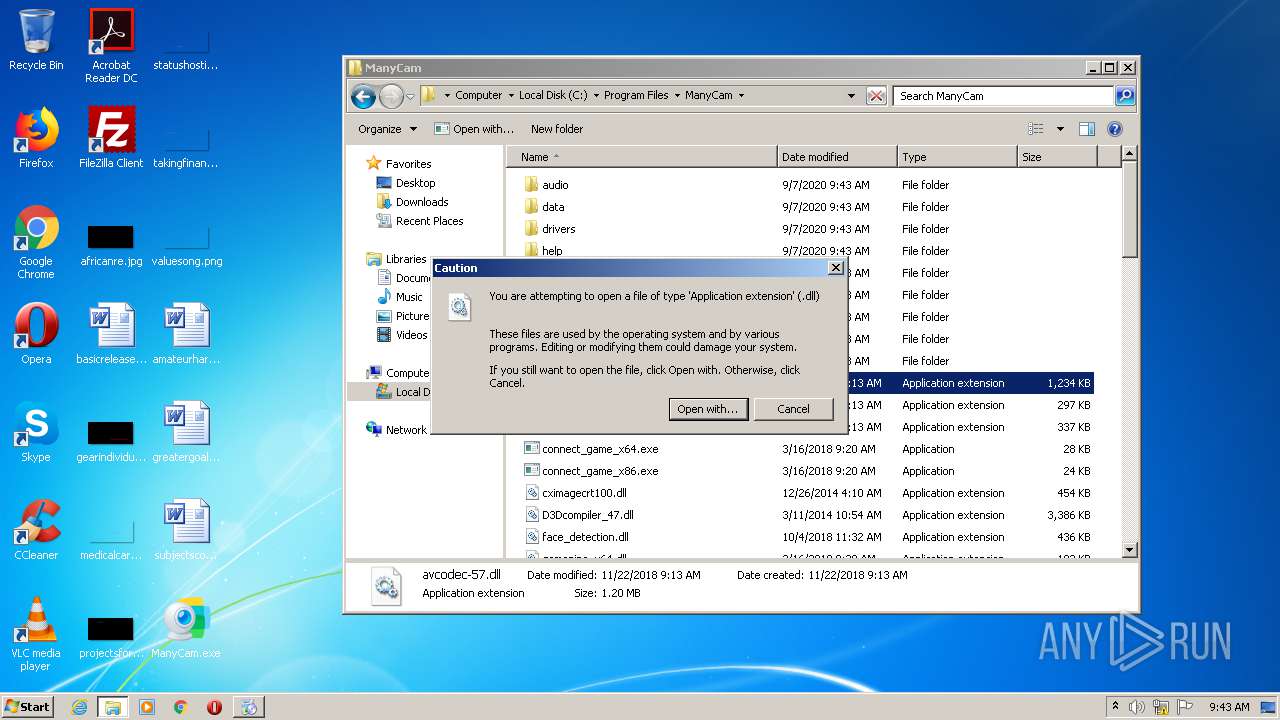
Executable content was dropped or overwritten
- chrome.exe (PID: 2676)
- ManyCam_v6.7.0.exe (PID: 3112)
- ManyCam_v6.7.0.exe (PID: 3928)
- mdsu.exe (PID: 776)
- DrvInst.exe (PID: 2312)
- DllHost.exe (PID: 764)
- DrvInst.exe (PID: 3256)
- mdsu.exe (PID: 3672)
- DrvInst.exe (PID: 444)
- DllHost.exe (PID: 704)
- DrvInst.exe (PID: 3580)
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 2676)
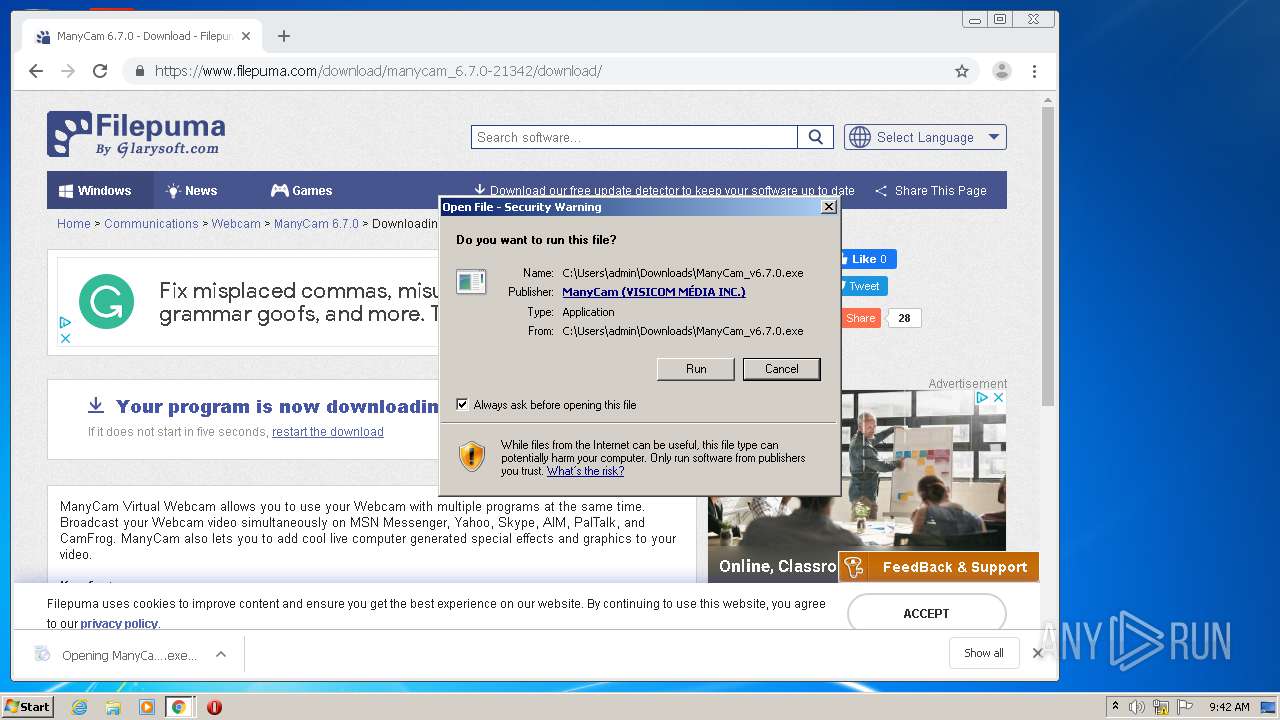
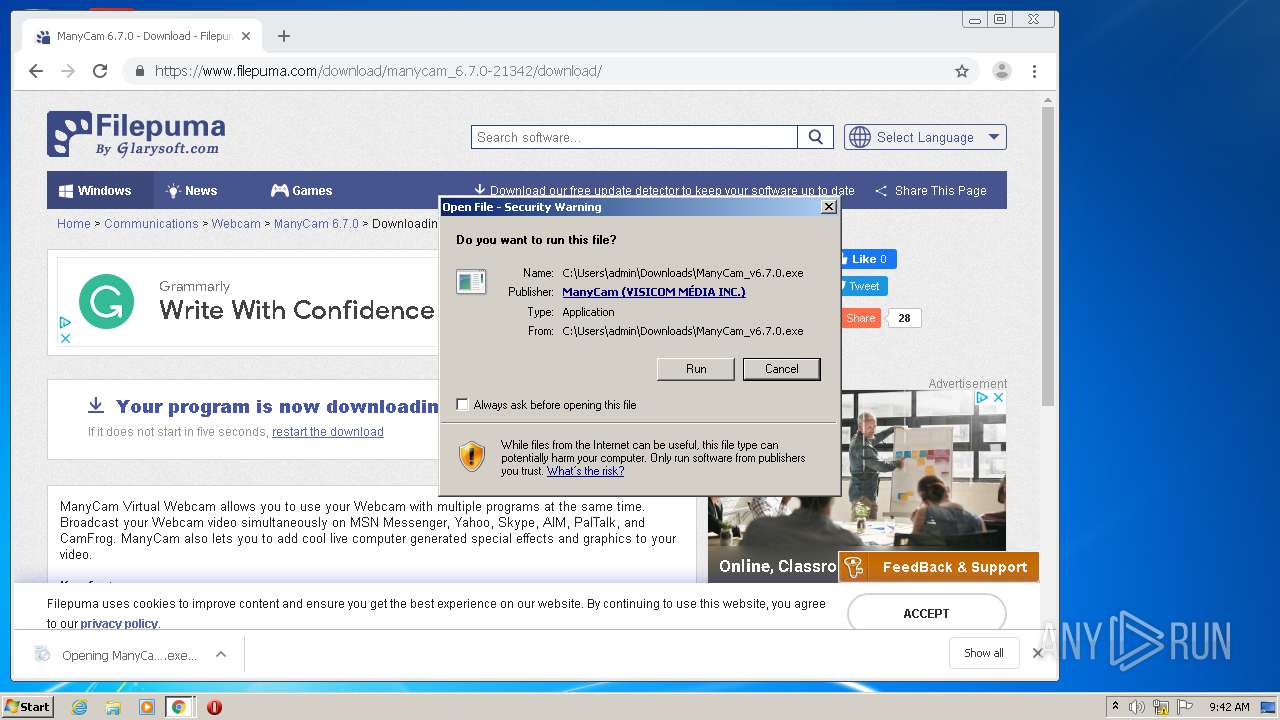
Application launched itself
- ManyCam_v6.7.0.exe (PID: 3112)
- ManyCam.exe (PID: 3168)
- taskmgr.exe (PID: 2392)
Creates files in the Windows directory
- certutil.exe (PID: 2568)
- certutil.exe (PID: 2520)
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 3256)
- DrvInst.exe (PID: 3580)
- DrvInst.exe (PID: 444)
Removes files from Windows directory
- certutil.exe (PID: 2568)
- certutil.exe (PID: 2520)
- DrvInst.exe (PID: 3256)
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 3580)
- DrvInst.exe (PID: 444)
Creates files in the user directory
- ManyCam_v6.7.0.exe (PID: 3112)
- ManyCam_v6.7.0.exe (PID: 3928)
- ManyCam.exe (PID: 3600)
- ManyCam.exe (PID: 3168)
Modifies the open verb of a shell class
- ManyCam_v6.7.0.exe (PID: 3928)
Creates a software uninstall entry
- ManyCam_v6.7.0.exe (PID: 3928)
Adds / modifies Windows certificates
- mdsu.exe (PID: 776)
- mdsu.exe (PID: 3672)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 1704)
- DrvInst.exe (PID: 2312)
Executed via COM
- DrvInst.exe (PID: 2312)
- DllHost.exe (PID: 764)
- DrvInst.exe (PID: 3256)
- DrvInst.exe (PID: 444)
- DrvInst.exe (PID: 3580)
- DllHost.exe (PID: 704)
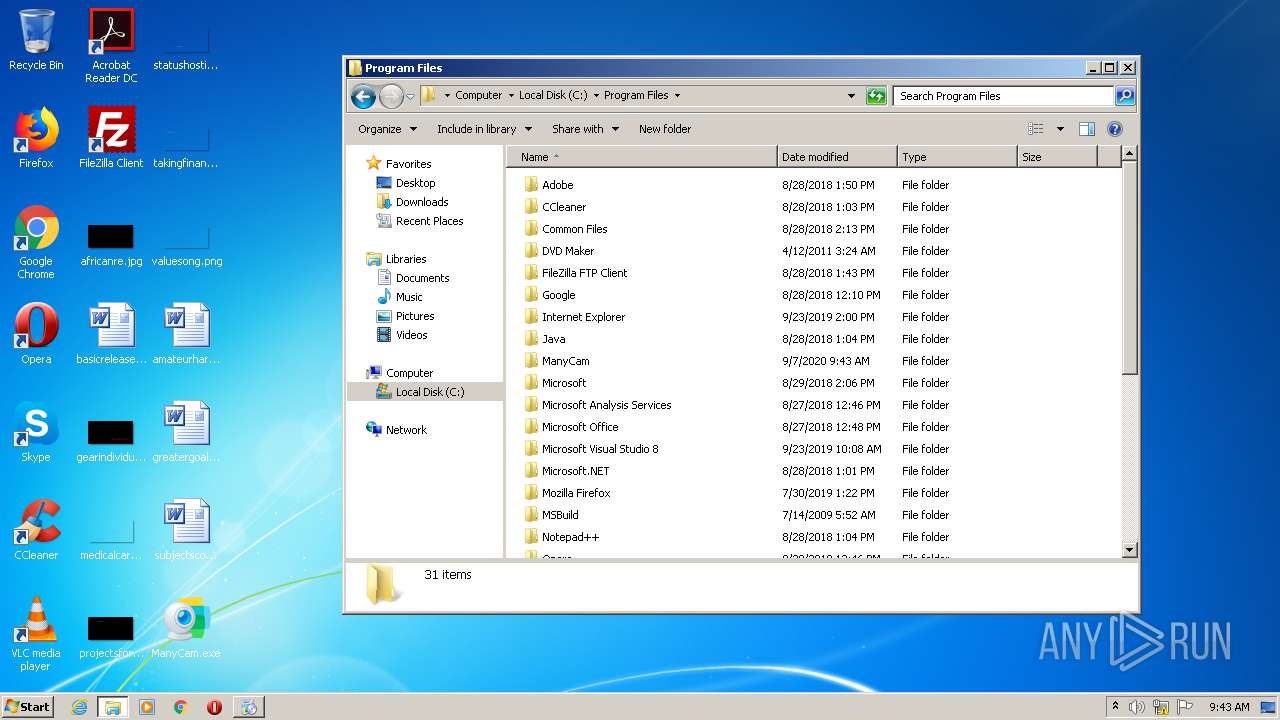
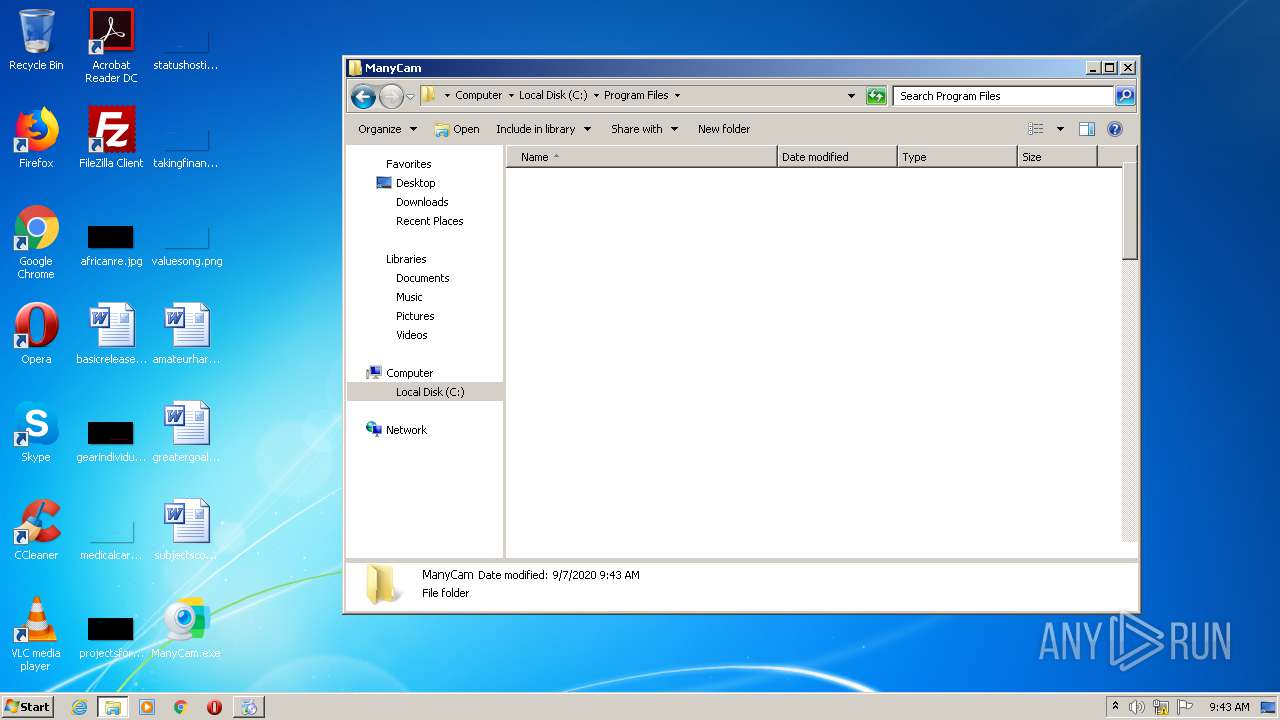
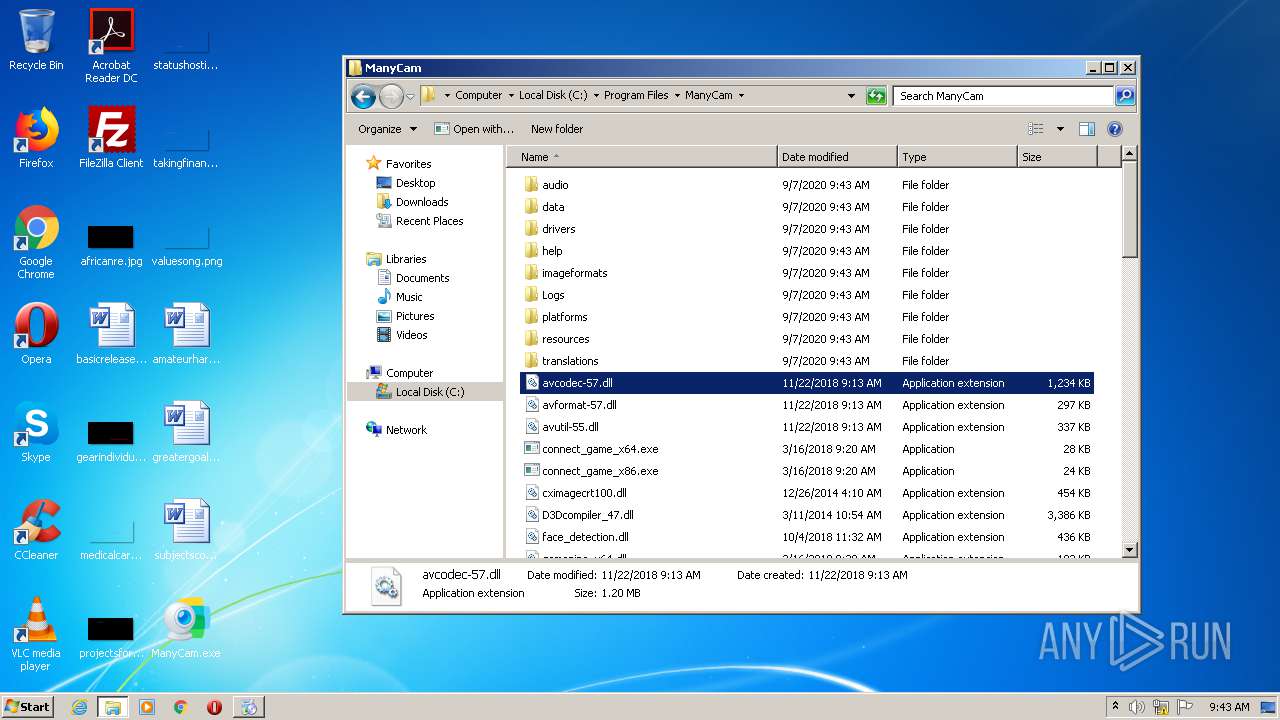
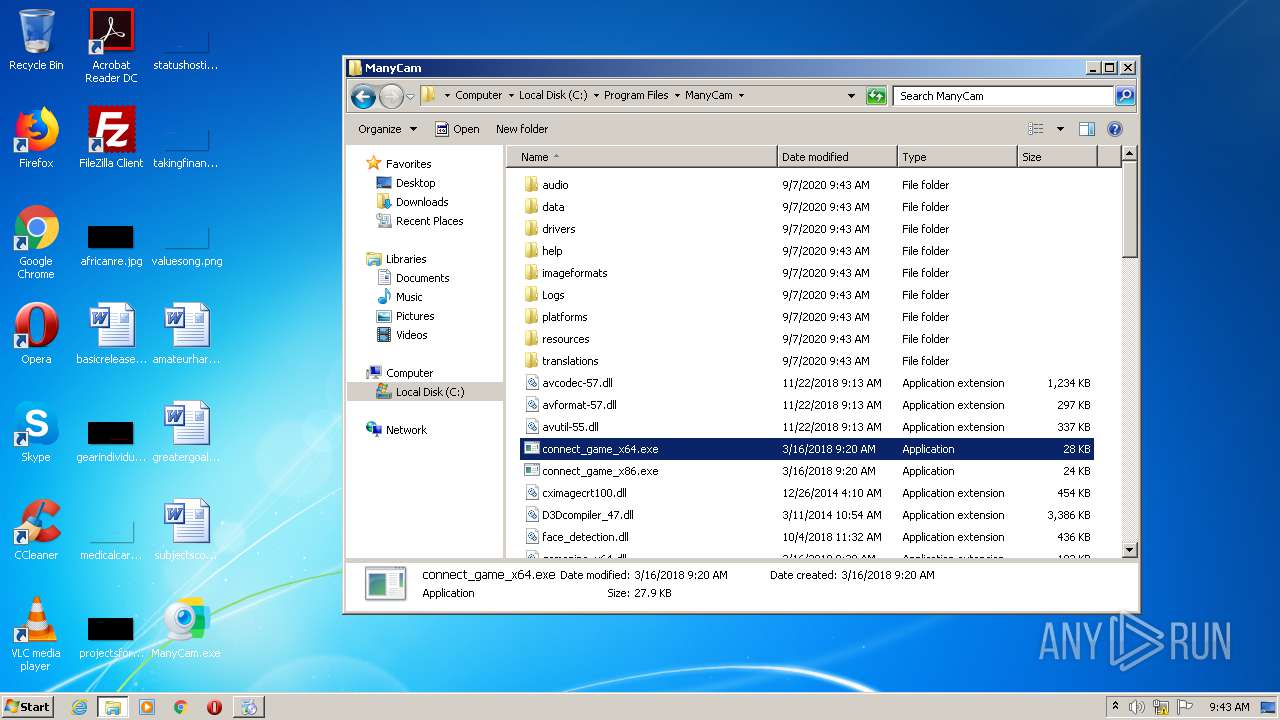
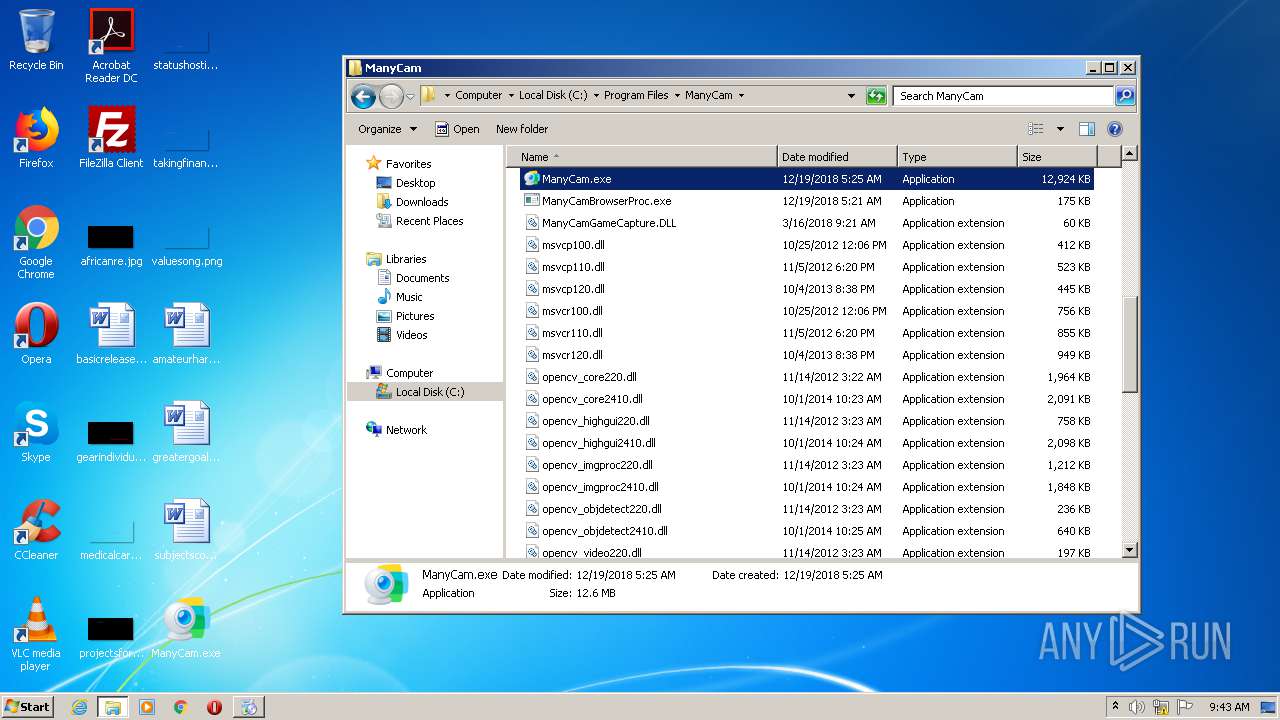
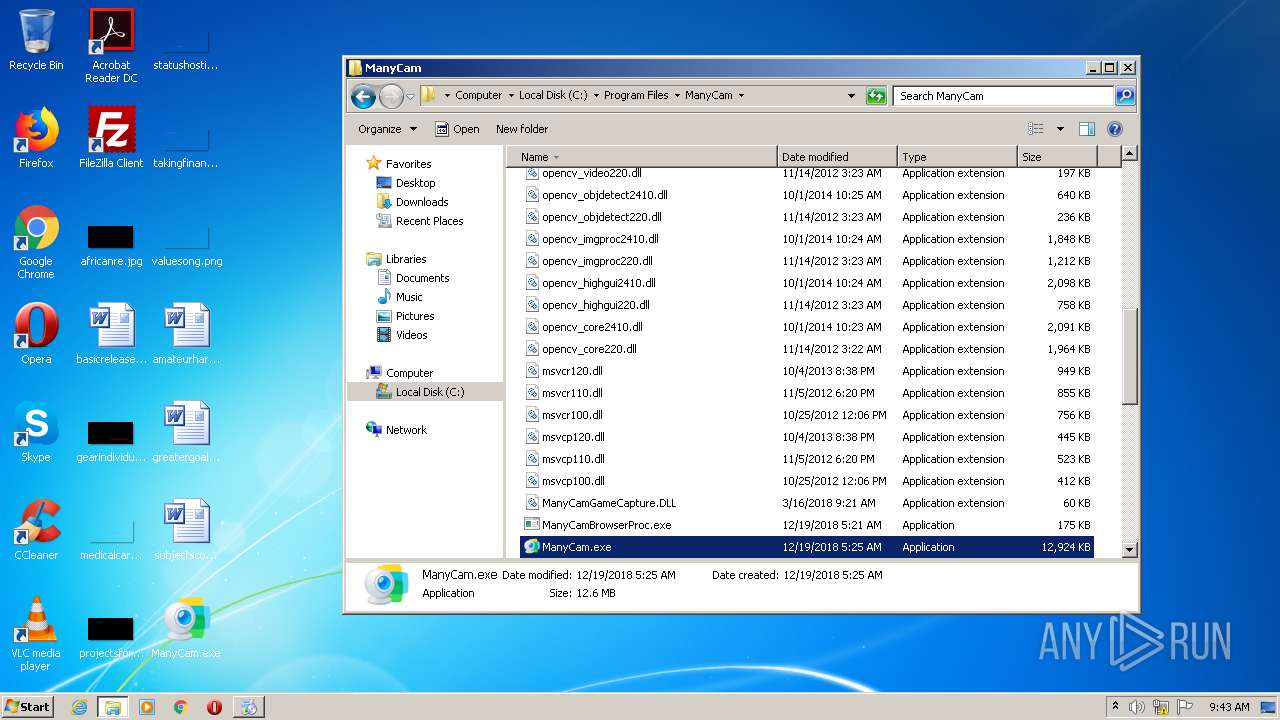
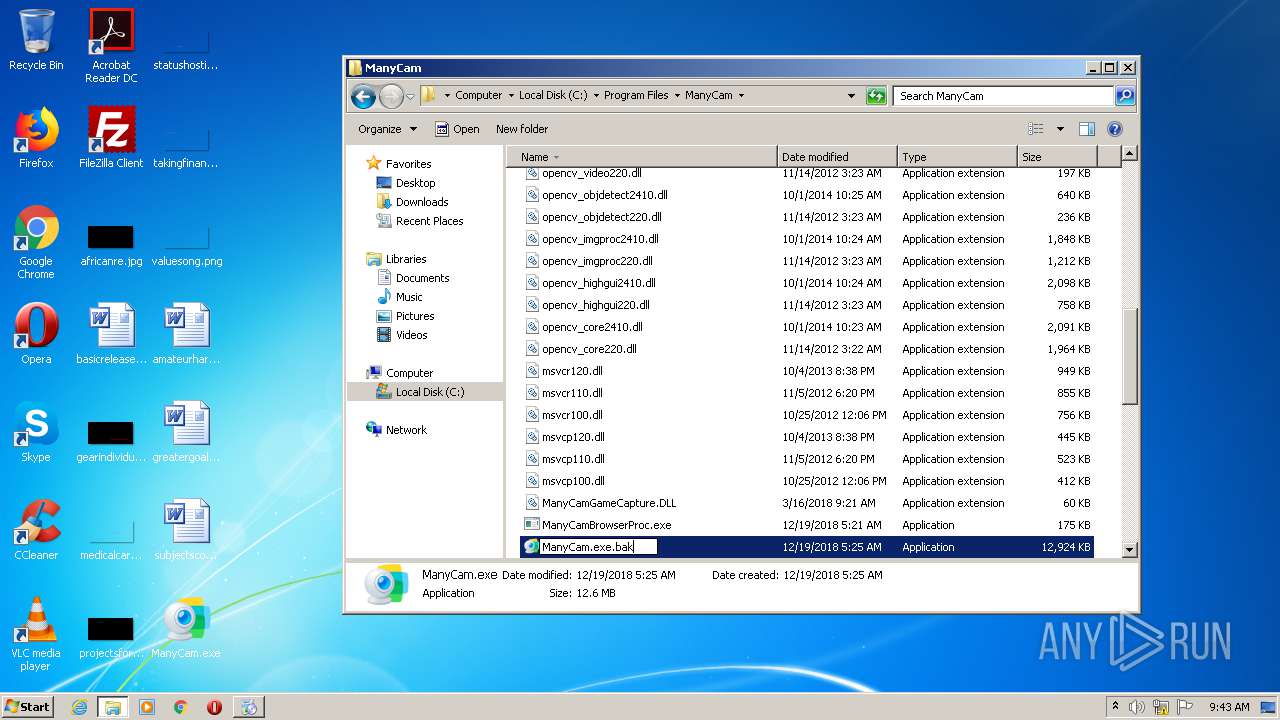
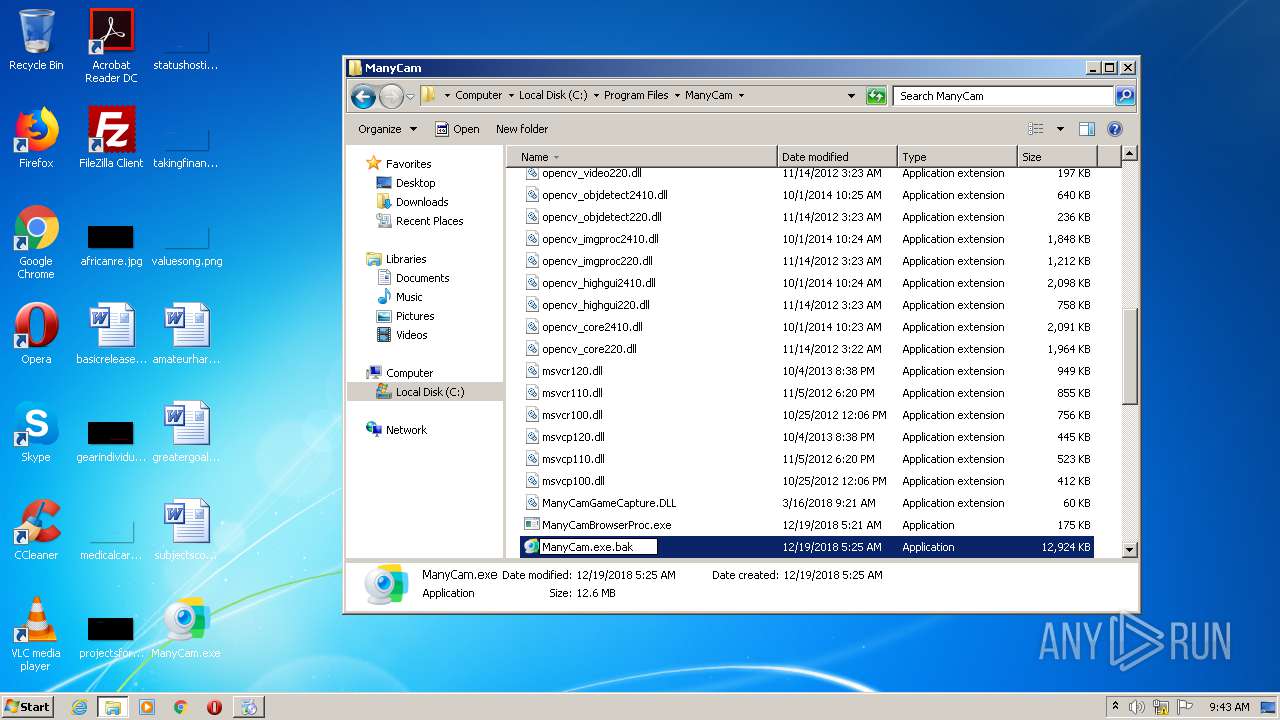
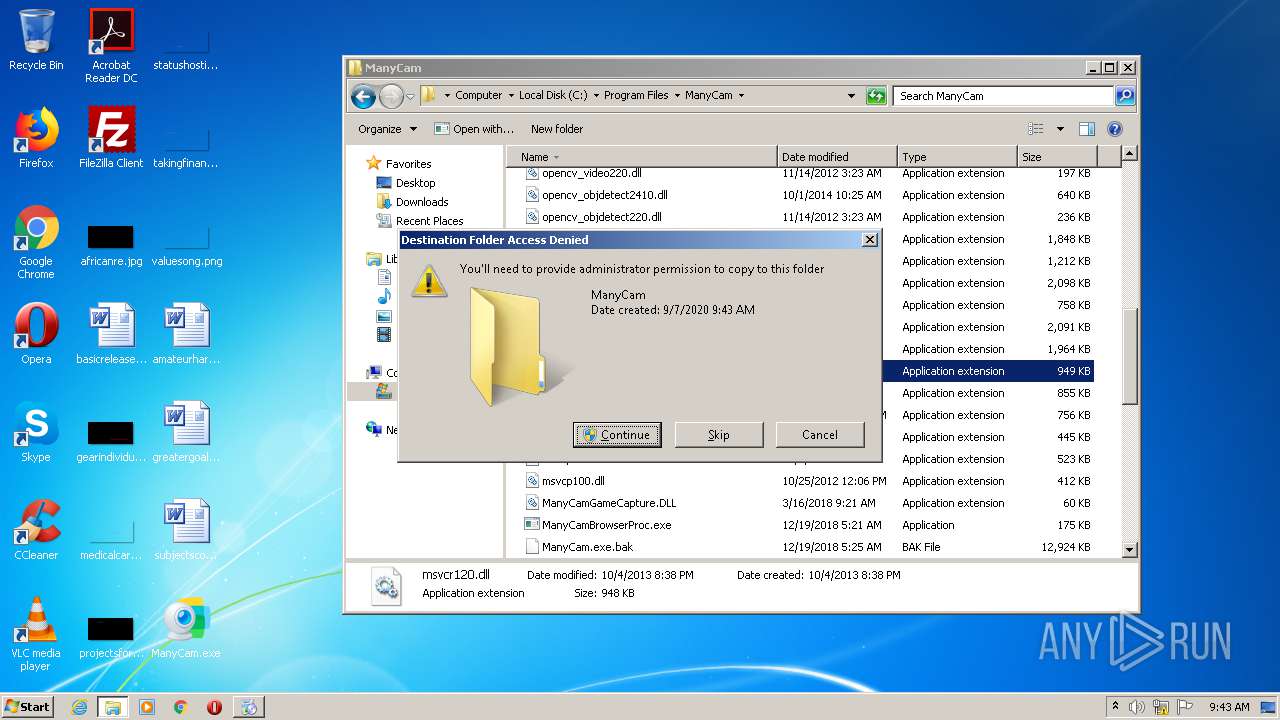
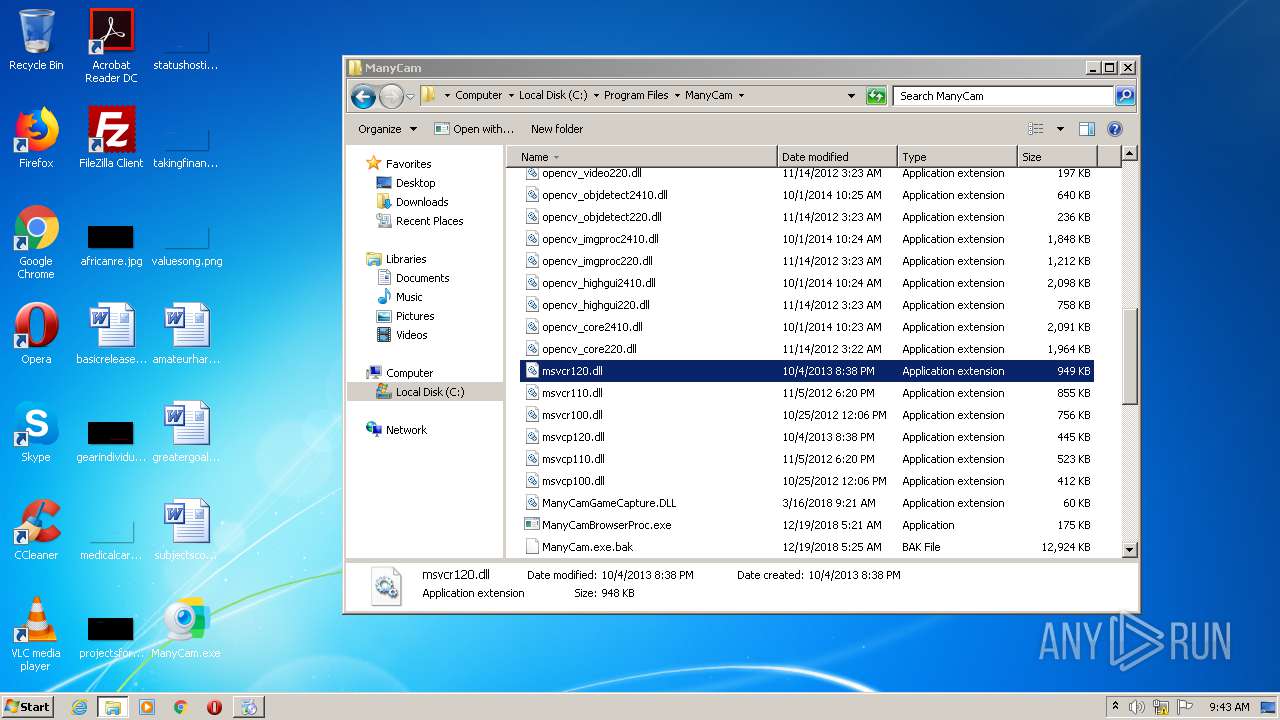
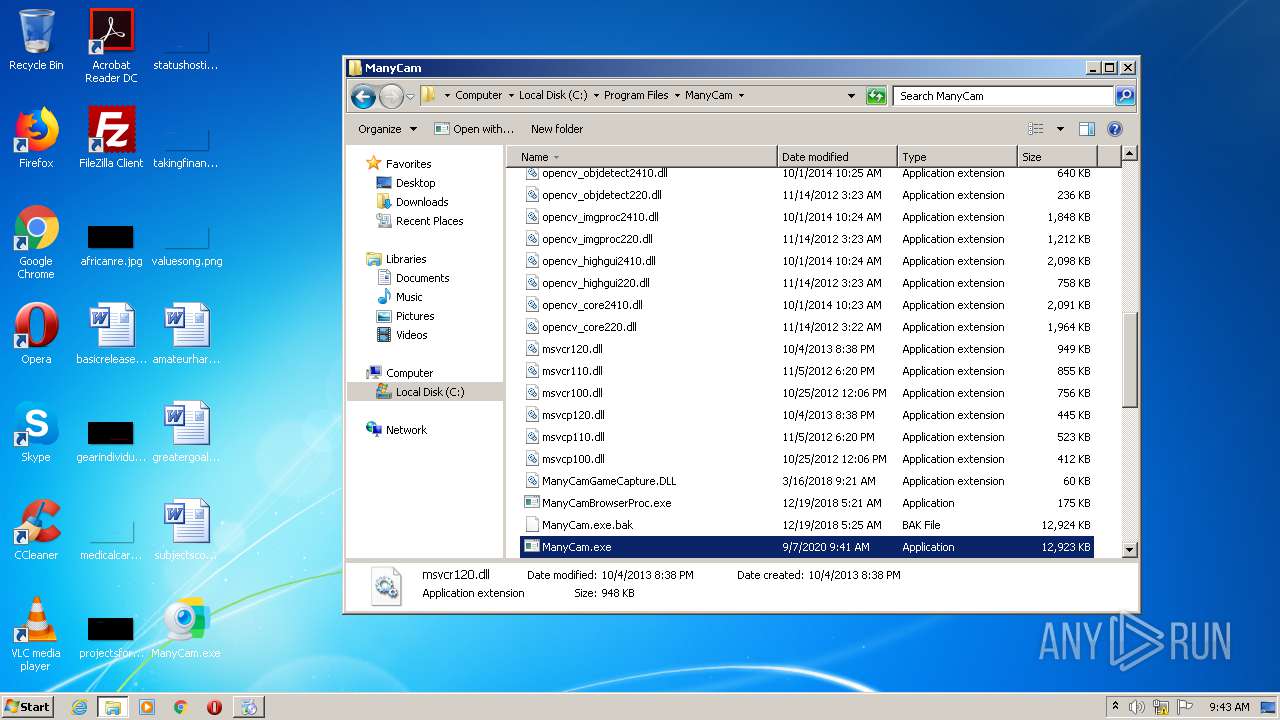
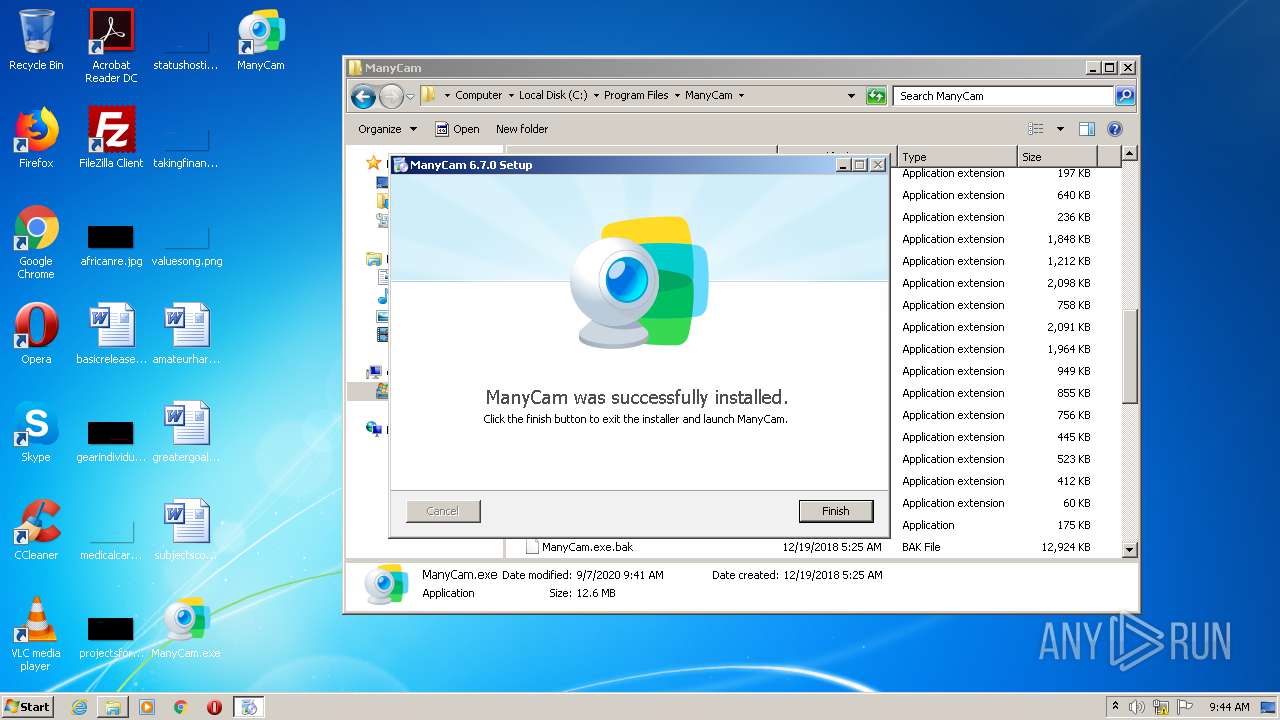
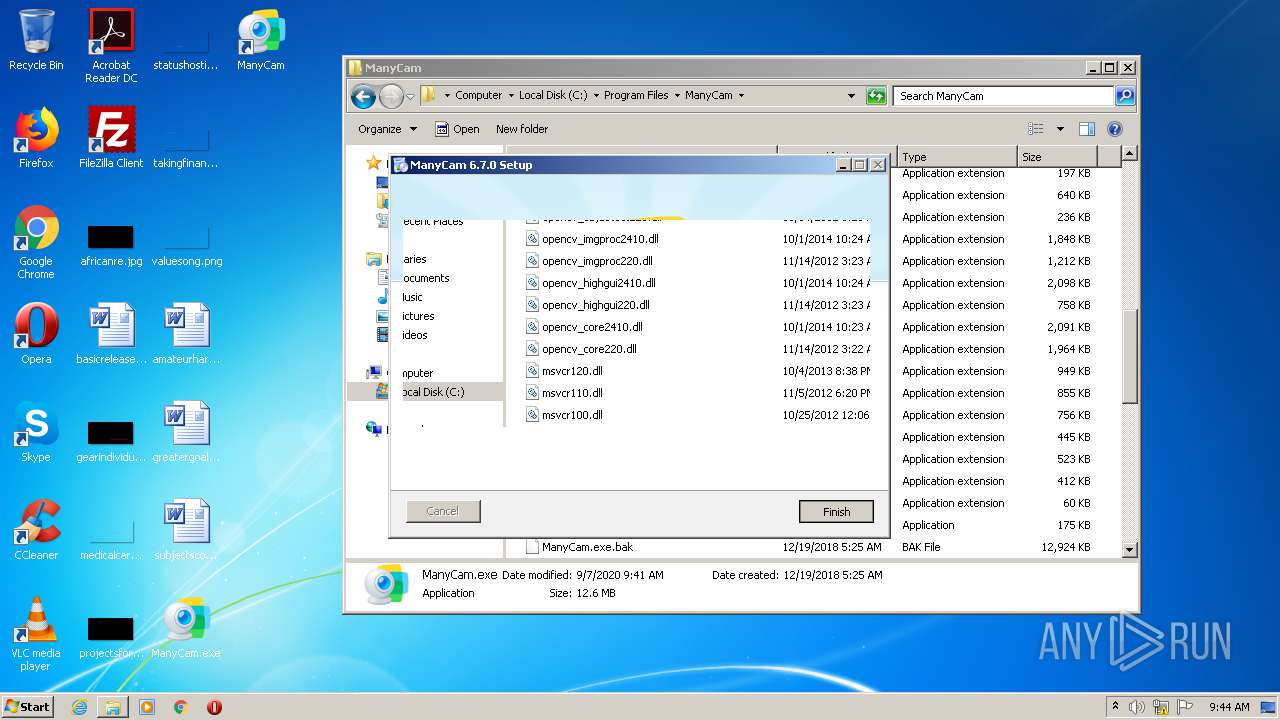
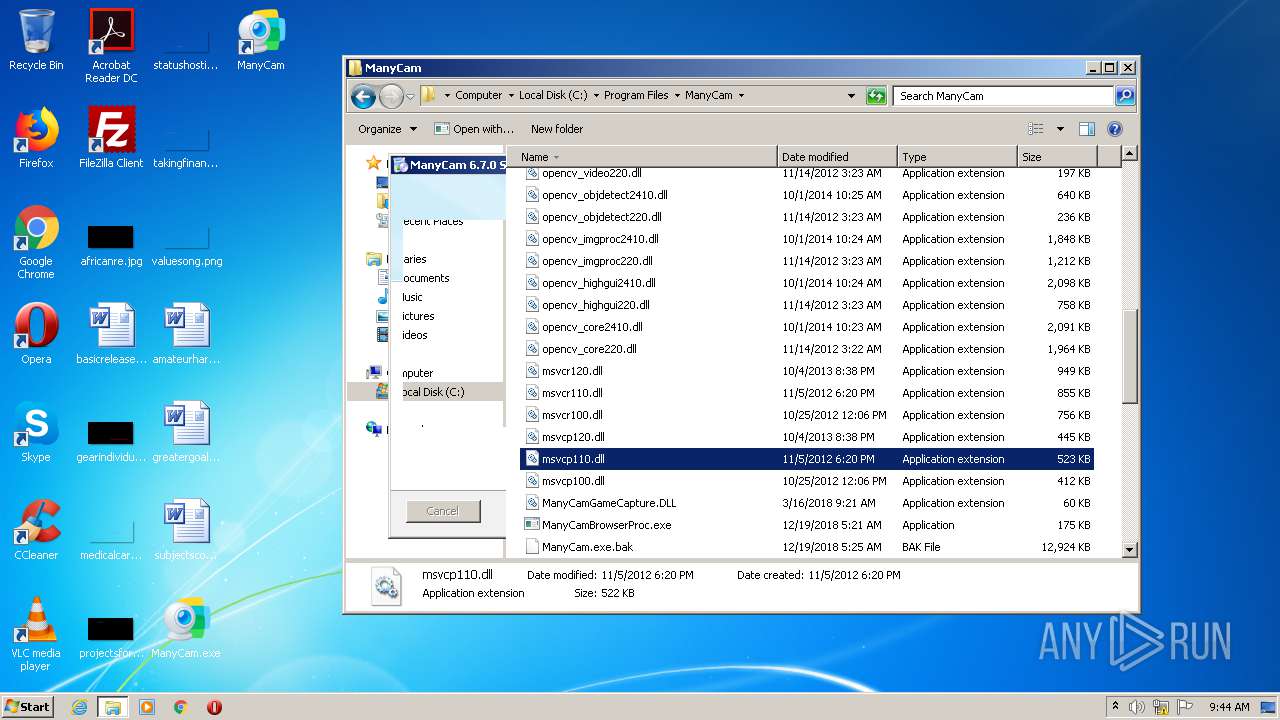
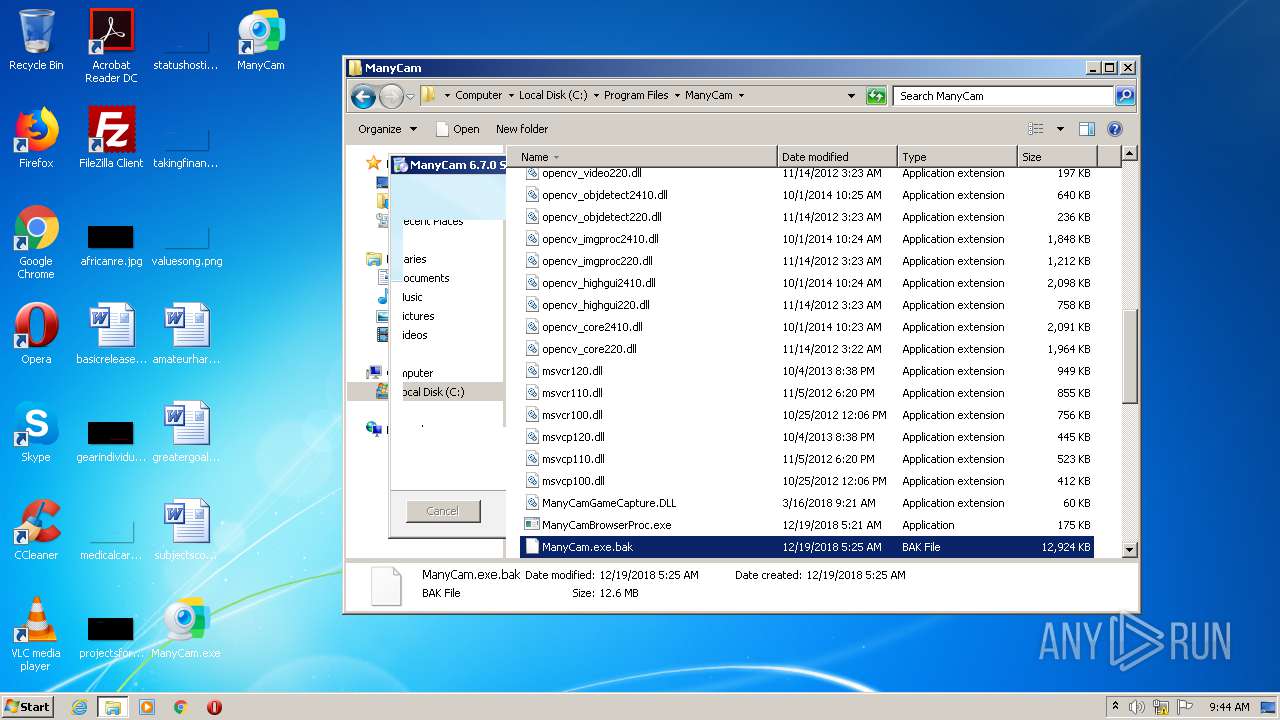
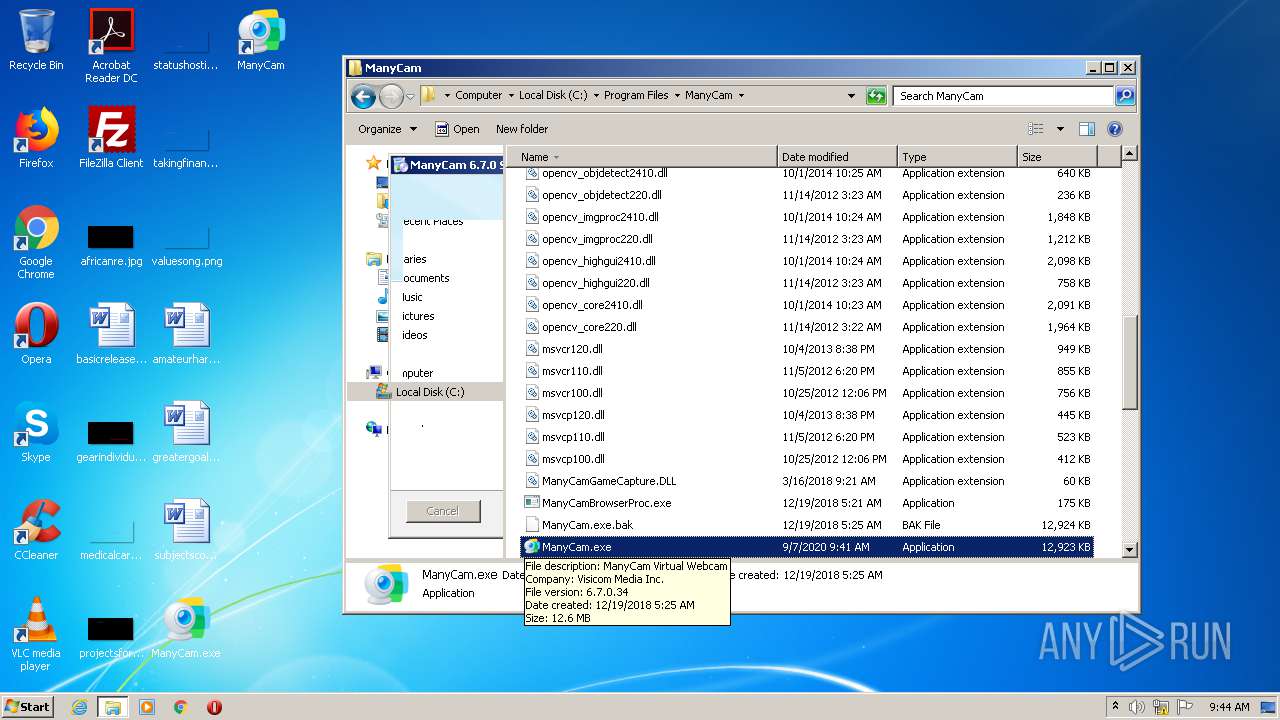
Creates files in the program directory
- ManyCam_v6.7.0.exe (PID: 3928)
- DllHost.exe (PID: 704)
- WerFault.exe (PID: 1724)
- WerFault.exe (PID: 4000)
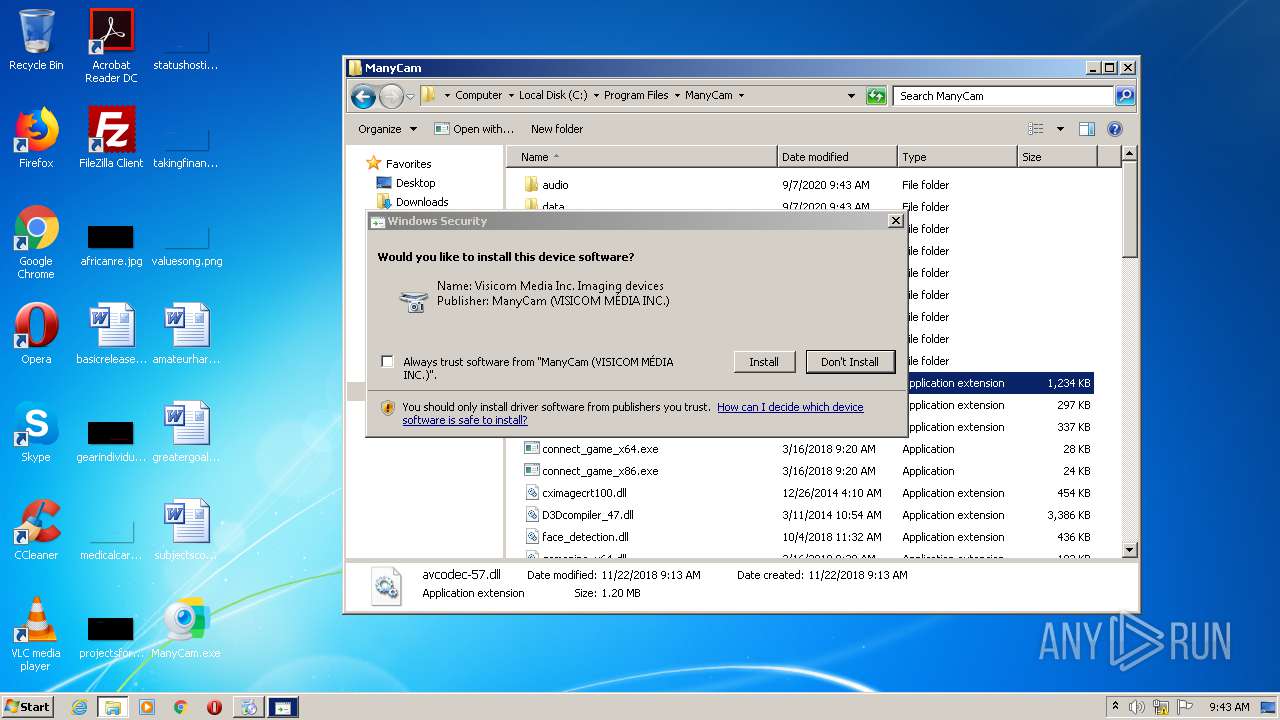
Creates files in the driver directory
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 3256)
- DrvInst.exe (PID: 444)
- DrvInst.exe (PID: 3580)
Executed as Windows Service
- ManyCamService.exe (PID: 2976)
Reads default file associations for system extensions
- explorer.exe (PID: 1704)
INFO
Reads the hosts file
- chrome.exe (PID: 2676)
- chrome.exe (PID: 2628)
Reads settings of System Certificates
- chrome.exe (PID: 2628)
- mdsu.exe (PID: 776)
- mdsu.exe (PID: 3672)
- ManyCam.exe (PID: 3600)
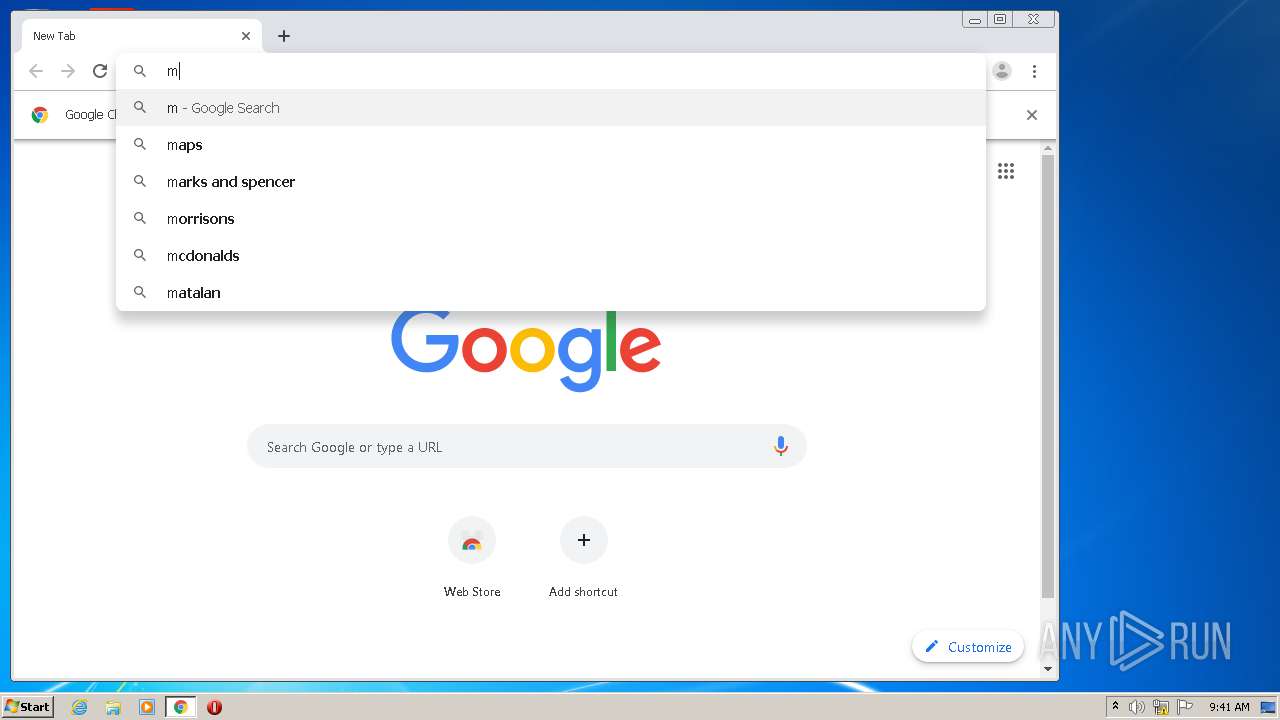
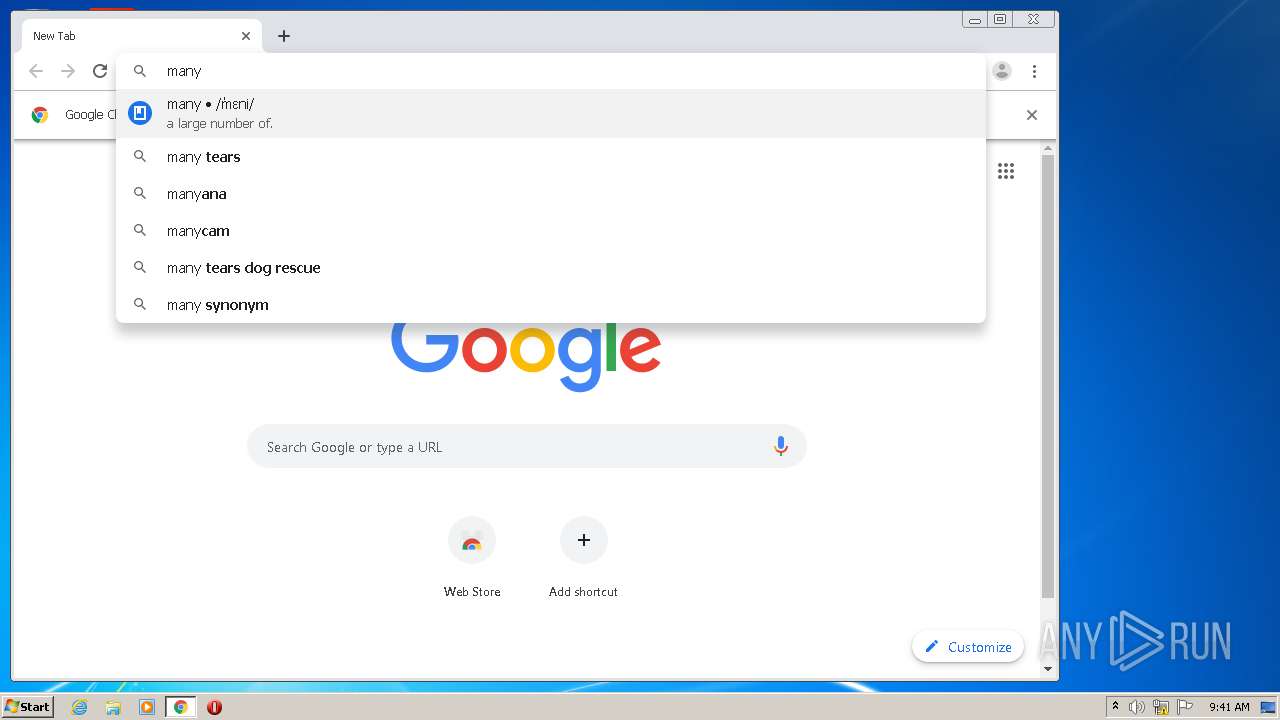
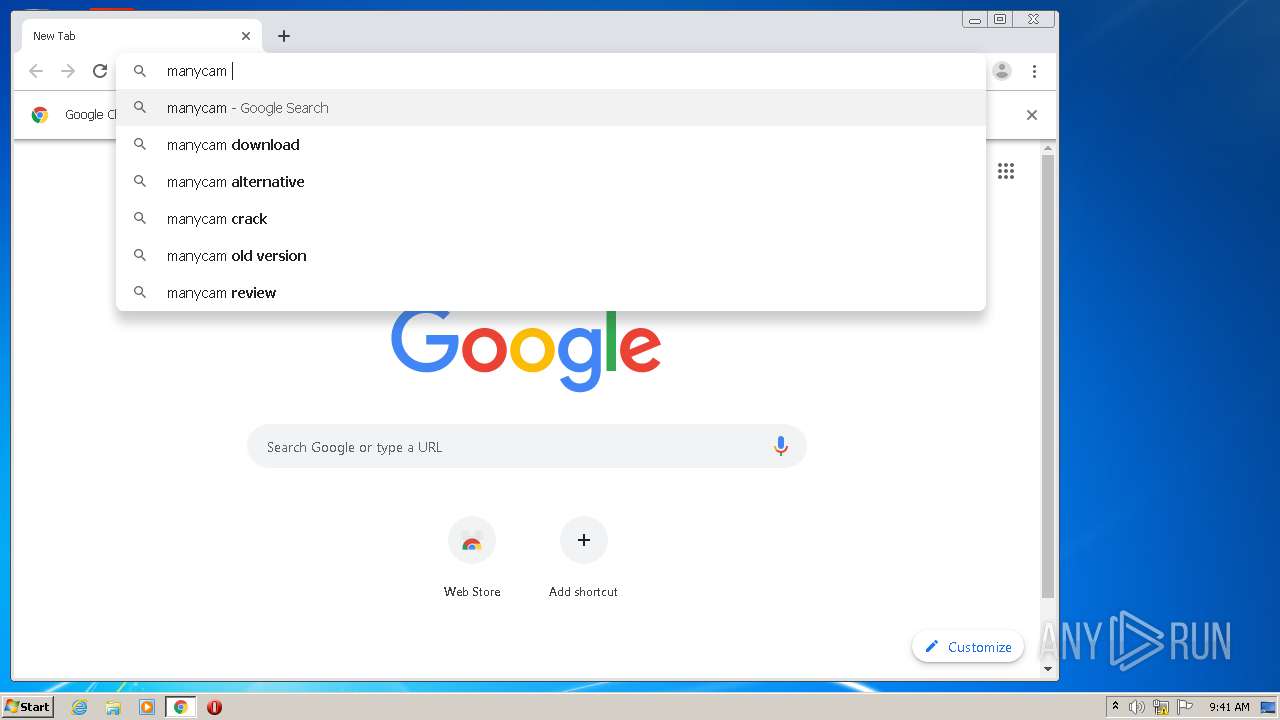
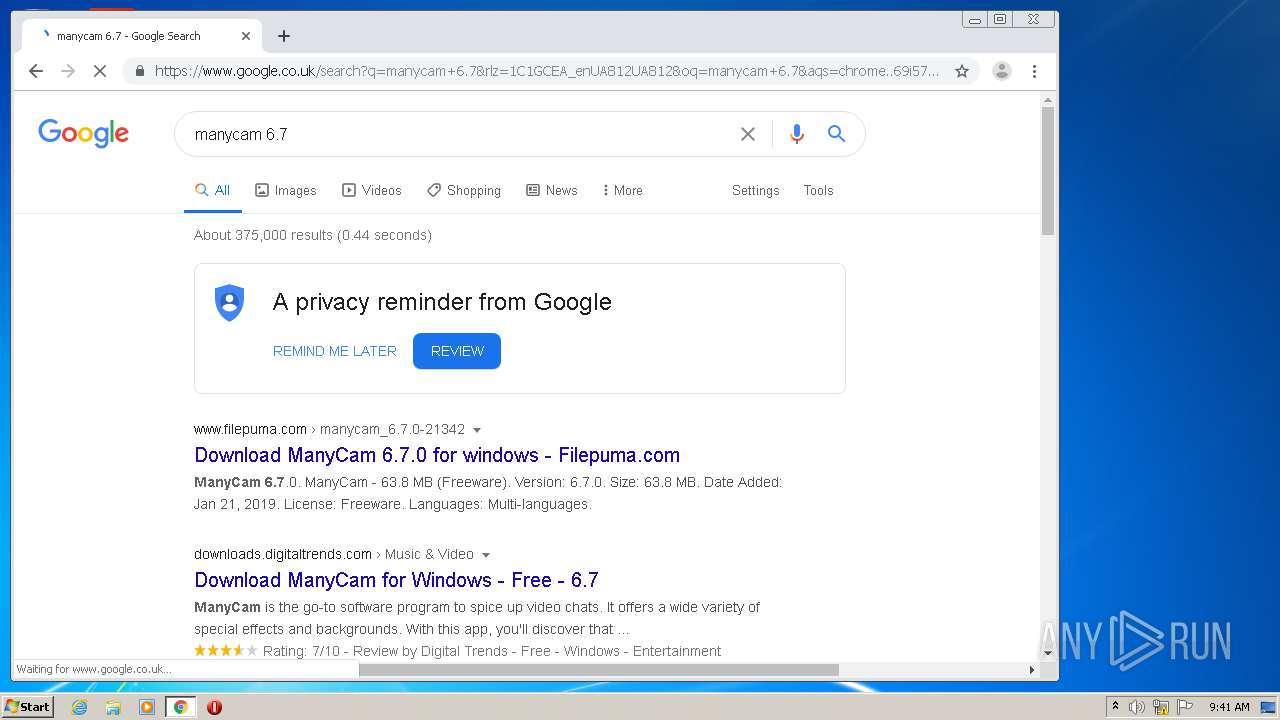
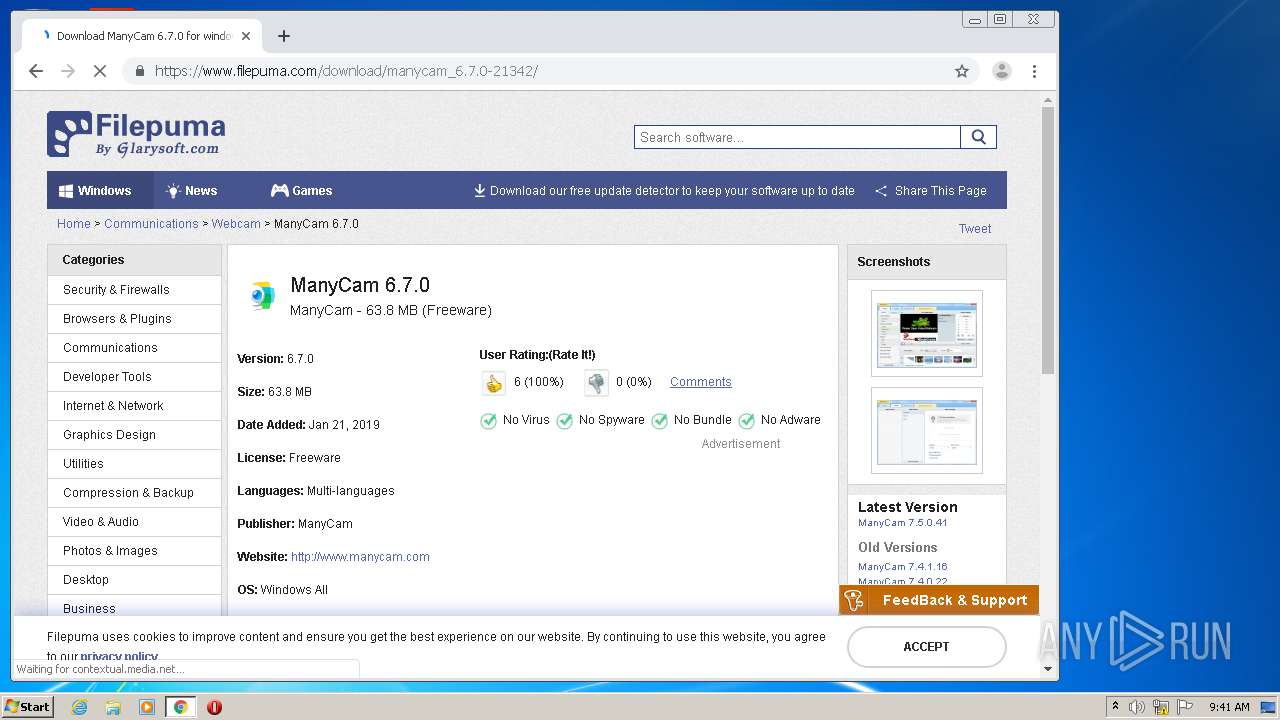
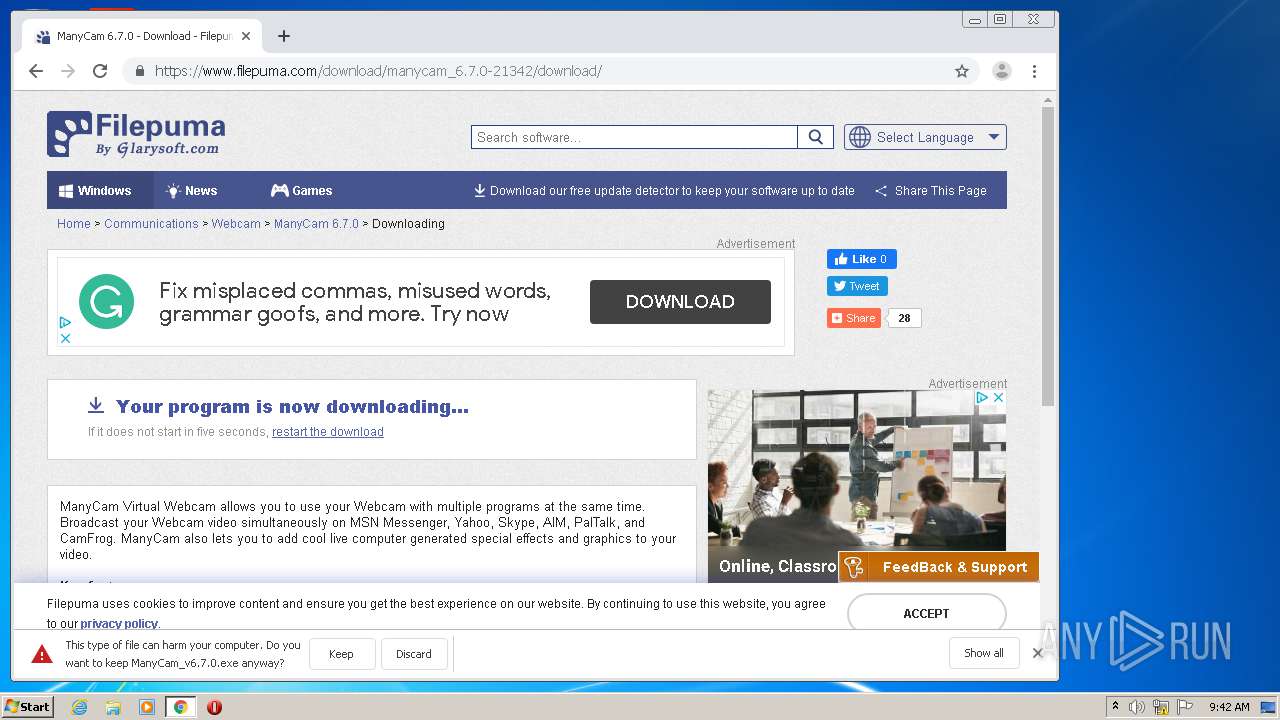
Manual execution by user
- chrome.exe (PID: 2676)
- rundll32.exe (PID: 1396)
- explorer.exe (PID: 1600)
Application launched itself
- chrome.exe (PID: 2676)
Reads Internet Cache Settings
- chrome.exe (PID: 2676)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2628)
- ManyCam_v6.7.0.exe (PID: 3928)
Searches for installed software
- DrvInst.exe (PID: 2312)
- DrvInst.exe (PID: 444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:12 09:11:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 7117824 |
| InitializedDataSize: | 12858880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c36200 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.7.0.34 |
| ProductVersionNumber: | 6.7.0.34 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Visicom Media Inc. |
| FileDescription: | ManyCam Virtual Webcam |
| FileVersion: | 6.7.0.34 |
| InternalName: | ManyCam Virtual Webcam |
| LegalCopyright: | (c) 2006-2019 Visicom Media Inc. |
| OriginalFileName: | ManyCam.exe |
| ProductName: | ManyCam Virtual Webcam |
| ProductVersion: | 6.7.0.34 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Mar-2019 08:11:16 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000168 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 12-Mar-2019 08:11:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x01215000 | 0x0083AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98108 | |
.rsrc | 0x01216000 | 0x00068EA8 | 0x0001CA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98879 |
.idata | 0x0127F000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.44268 |
0x01280000 | 0x00571000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.281092 | |
qcabzbtx | 0x017F1000 | 0x00442000 | 0x00441E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.78563 |
eayphdfd | 0x01C33000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.20443 |
.taggant | 0x01C34000 | 0x00003700 | 0x00002848 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.12033 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.07473 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.84441 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.73888 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 4.52556 | 67624 | UNKNOWN | English - United States | RT_ICON |
6 | 4.91865 | 270376 | UNKNOWN | English - United States | RT_ICON |
101 | 2.76511 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
102 | 7.90395 | 57832 | UNKNOWN | English - United States | WAVE |
Imports
comctl32.dll |
kernel32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
??0CxExifInfo@CxImageJPG@@QAE@PAUtag_ExifInfo@1@@Z | 1 | 0x00573530 |
??0CxFile@@QAE@ABV0@@Z | 2 | 0x00558920 |
??0CxFile@@QAE@XZ | 3 | 0x0042EC50 |
??0CxIOFile@@QAE@ABV0@@Z | 4 | 0x00558930 |
??0CxIOFile@@QAE@PAU_iobuf@@@Z | 5 | 0x0042EC90 |
??0CxImage@@QAE@ABV0@_N11@Z | 6 | 0x00558950 |
??0CxImage@@QAE@K@Z | 7 | 0x00558990 |
??0CxImage@@QAE@KKKK@Z | 8 | 0x005589B0 |
??0CxImage@@QAE@PAEKK@Z | 9 | 0x0056BD50 |
??0CxImage@@QAE@PAU_iobuf@@K@Z | 10 | 0x0056BDD0 |
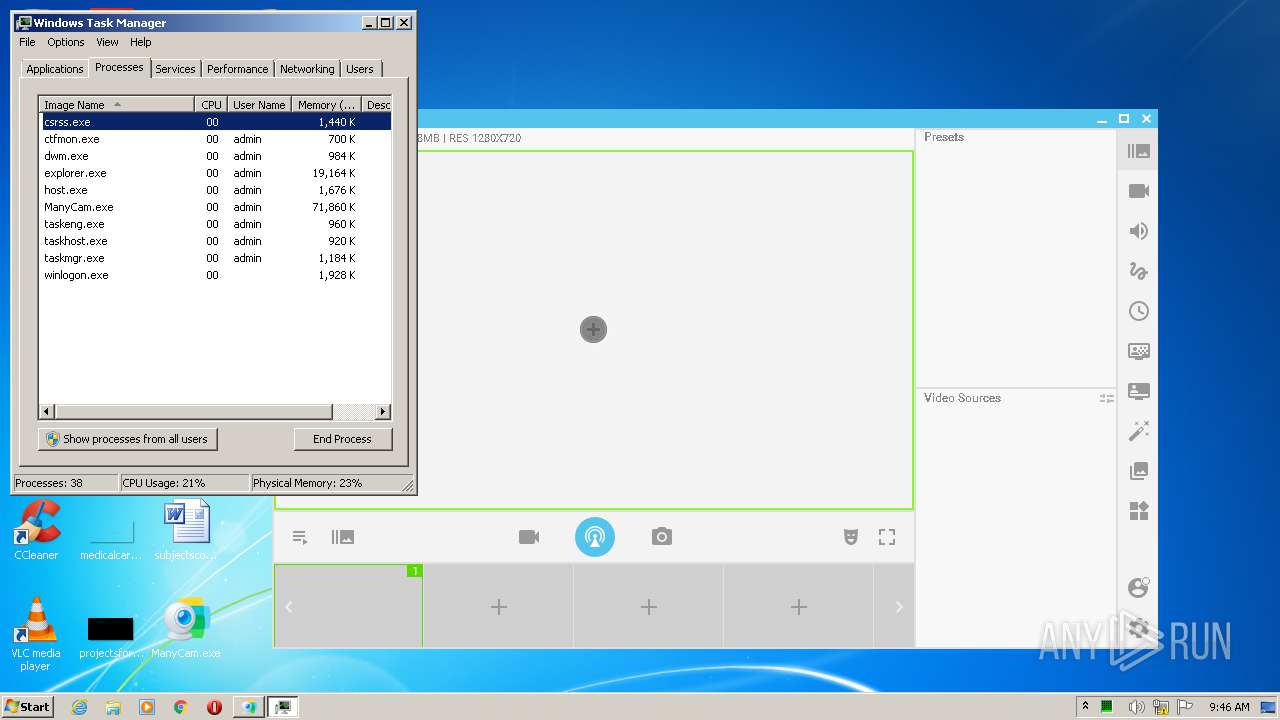
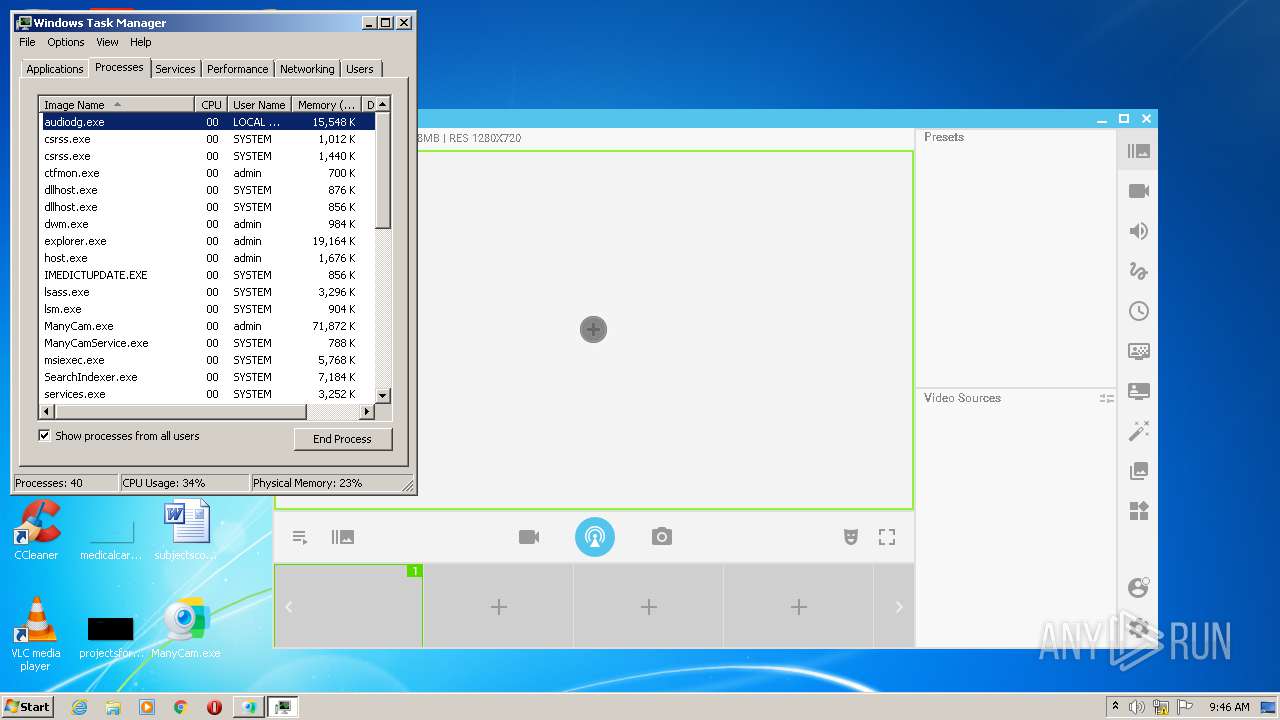
Total processes
133
Monitored processes
64
Malicious processes
15
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{1a86cb9a-a94c-1cd6-efcd-82378da20b7f}\mcaudrv.inf" "0" "6ea6deb4b" "000005E4" "WinSta0\Default" "000005C4" "208" "c:\users\admin\appdata\local\temp\nsfc2ab.tmp\mcaudrv" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,1047764921175014454,18398411709915583620,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17191167620177727942 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 704 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | "C:\Program Files\ManyCam\drivers\video\mdsu.exe" add_by_name "ManyCam Virtual Webcam" | C:\Program Files\ManyCam\drivers\video\mdsu.exe | ManyCam_v6.7.0.exe | ||||||||||||
User: admin Company: Visicom Media Inc. Integrity Level: HIGH Description: ManyCam Kernel Setup Utility Exit code: 0 Version: 2.0.1.0 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,1047764921175014454,18398411709915583620,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6540581077807452324 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,1047764921175014454,18398411709915583620,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9567978771877655886 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,1047764921175014454,18398411709915583620,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1264257735313345368 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\ProgramData\ManyCam\Service\ManyCamService.exe" start | C:\ProgramData\ManyCam\Service\ManyCamService.exe | — | ManyCam_v6.7.0.exe | |||||||||||
User: admin Company: Visicom Media Inc. Integrity Level: HIGH Description: ManyCam Service Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,1047764921175014454,18398411709915583620,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7340438421696043943 --mojo-platform-channel-handle=3480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
7 632
Read events
6 219
Write events
1 385
Delete events
28
Modification events
| (PID) Process: | (2104) ManyCam.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: ManyCam.exe | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\Qrfxgbc\ZnalPnz.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004A000000710000007C7532000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2676-13243941678868500 |
Value: 259 | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 0000000006000000070000007BBF0600000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFB0352CA8F284D60100000000 | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004B000000710000007C7532000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000010000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFB0352CA8F284D60100000000 | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002600000000000000250000000C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A03 | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000010000000000000001000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFB0352CA8F284D60100000000 | |||
| (PID) Process: | (1704) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002600000000000000260000000C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A030C000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B000000582F1303CCD59A0305AC127610271403602F1303A702000008000000C4D59A03AF02000008271403ECD59A0343193076B729140350910F035E00000008271403582F1303AF020000B8F92F769063130390631303FCD59A0364193076582F130350910F0394DA9A03BF433076582F13030000000000000000FFFFFFFF00000000000000000000000050910F0368910F0350910F0392910F0300000000000000000000000000003076A87D3100E8900F03E0DA9A03BF433076A87D31000000000000000000FFFFFFFF000000000000000000000000E8900F0300910F03E8900F032A910F03A214000082231503A0D69A0333ABD37782473987090C0000102700001A0000005F560200D4D69A03F8AAD3775F56020082231503F4D69A0390A91F0274D79A0300000000A401000034D700008720F0B4E4D69A038291307634D79A03E8D69A0327953076000000001CAE1F0210D79A03CD9430761CAE1F02BCD79A0390A91F02E19430760000000090A91F02BCD79A0318D79A03 | |||
Executable files
97
Suspicious files
290
Text files
476
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2bf428ac-0d0b-4072-8f8f-943b43c7d664.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1535cf.TMP | text | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1535ee.TMP | text | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1537c3.TMP | — | |
MD5:— | SHA256:— | |||
| 2676 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
93
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
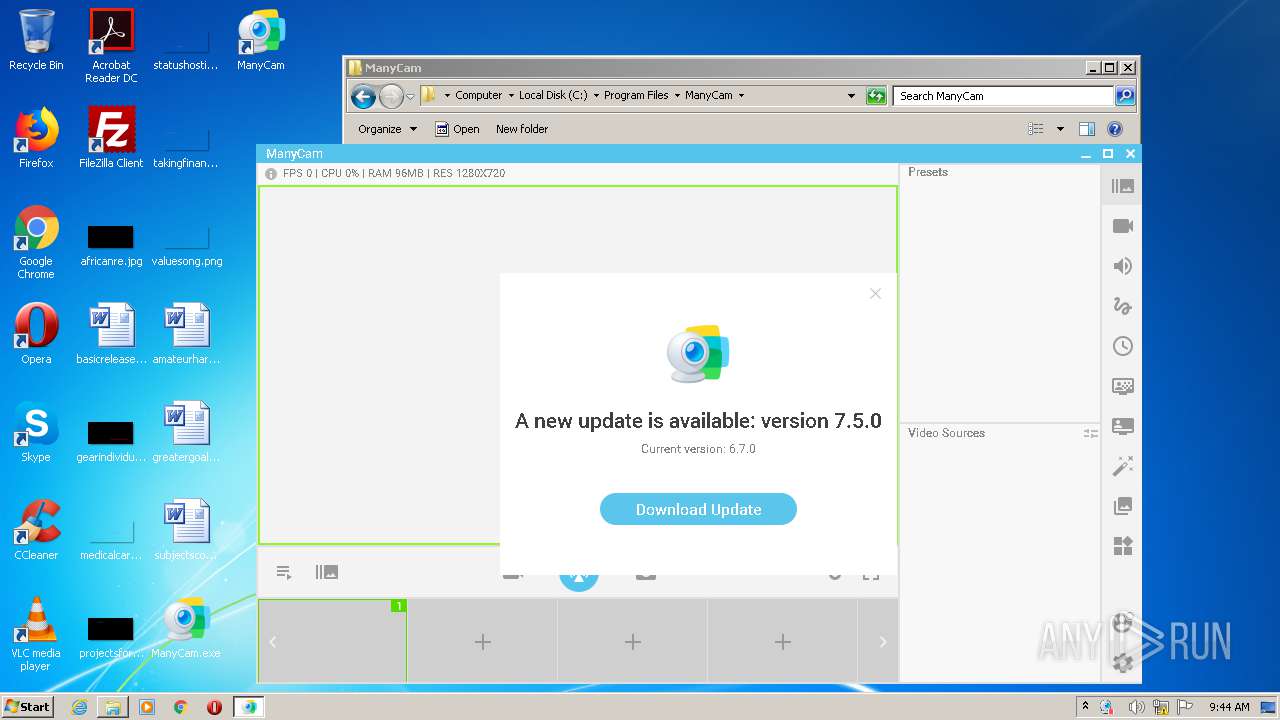
3928 | ManyCam_v6.7.0.exe | GET | 200 | 52.44.200.33:80 | http://installstat.manycam.com/dw.php?action=eula_show&version=6.7.0&uid=384bf1f771d24d0f83c1973a650f7f15 | US | — | — | malicious |
3600 | ManyCam.exe | GET | 200 | 52.44.200.33:80 | http://update.manycam.com/updateyoutubeplugin.php?appversion=6.7.0&v=6.7.0&l=en&p=9926&pi=&uid=384bf1f771d24d0f83c1973a650f7f15&pluginversion=6 | US | — | — | malicious |
3600 | ManyCam.exe | GET | 200 | 52.44.200.33:80 | http://update.ManyCam.com/get_latestversion.php?v=6.7.0&l=en&p=9926&pi=&uid=384bf1f771d24d0f83c1973a650f7f15 | US | text | 109 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2628 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 216.58.212.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.18.110:443 | consent.google.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 216.58.205.227:443 | www.google.co.uk | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |
Threats
Process | Message |
|---|---|
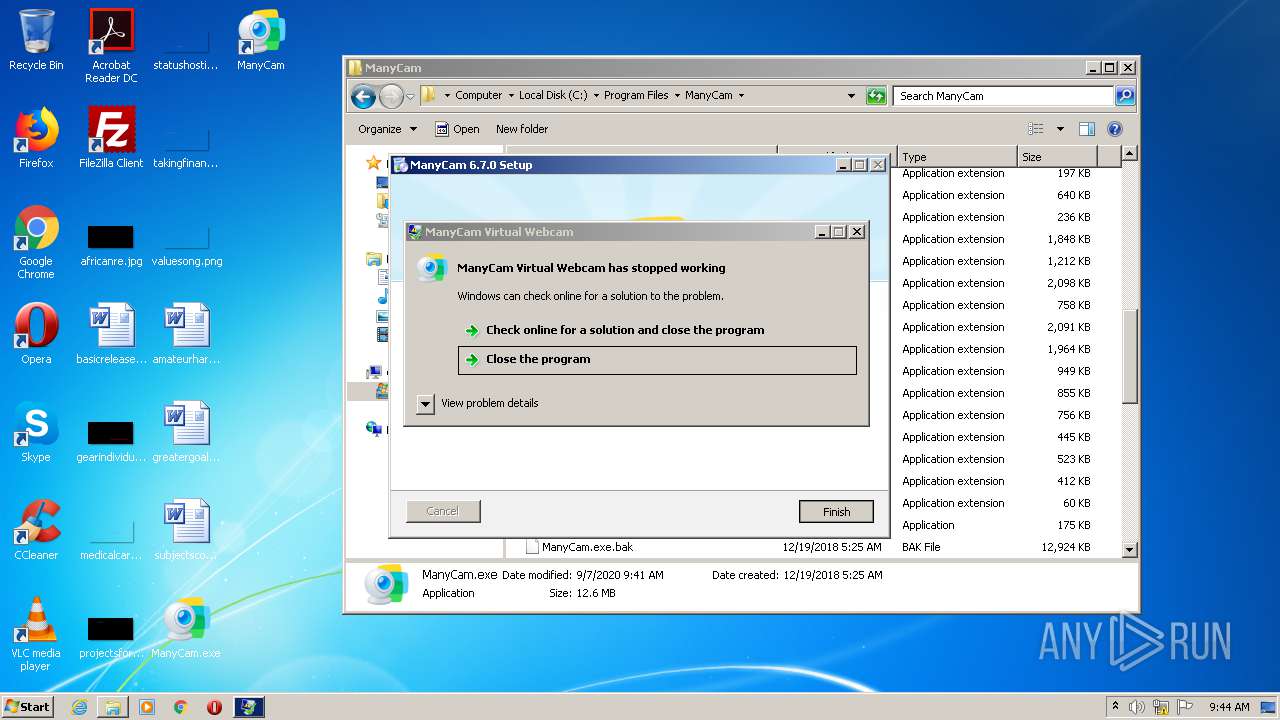
ManyCam.exe | 09:44:13:810 Warning: QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
ManyCam.exe | 09:44:13:810 Warning: QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
ManyCam.exe | 09:44:40:842 Warning: QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
ManyCam.exe | 09:44:40:842 Warning: QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
ManyCam.exe | 09:44:41:922 Warning: libpng warning: iCCP: known incorrect sRGB profile
|
ManyCam.exe | 09:44:42:011 Warning: QColor::setRgb: RGB parameters out of range
|
ManyCam.exe | 09:44:42:551 Warning: QFSFileEngine::open: No file name specified
|
ManyCam.exe | 09:44:42:575 Warning: QFSFileEngine::open: No file name specified
|
ManyCam.exe | 09:44:42:855 Warning: QObject::connect: No such slot QObject::onRedraw()
|
ManyCam.exe | 09:44:42:904 Warning: QObject::connect: signal not found in core::settings::VirtualWebcams
|