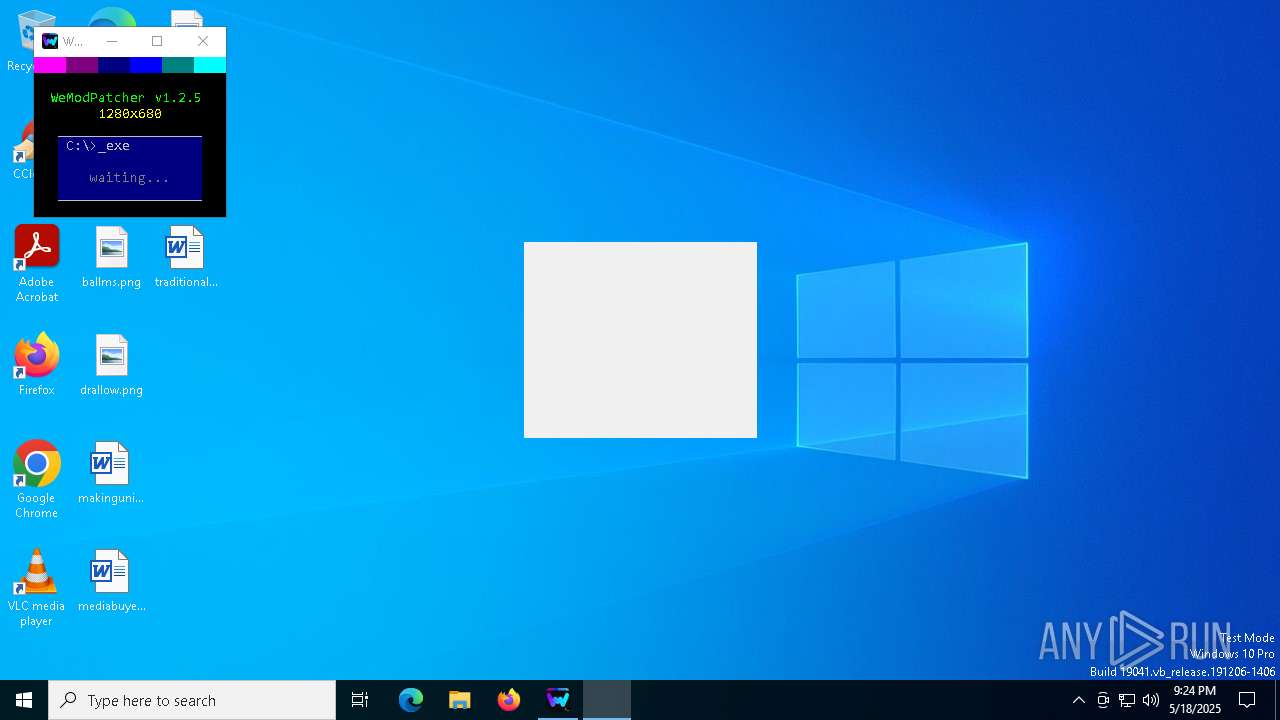
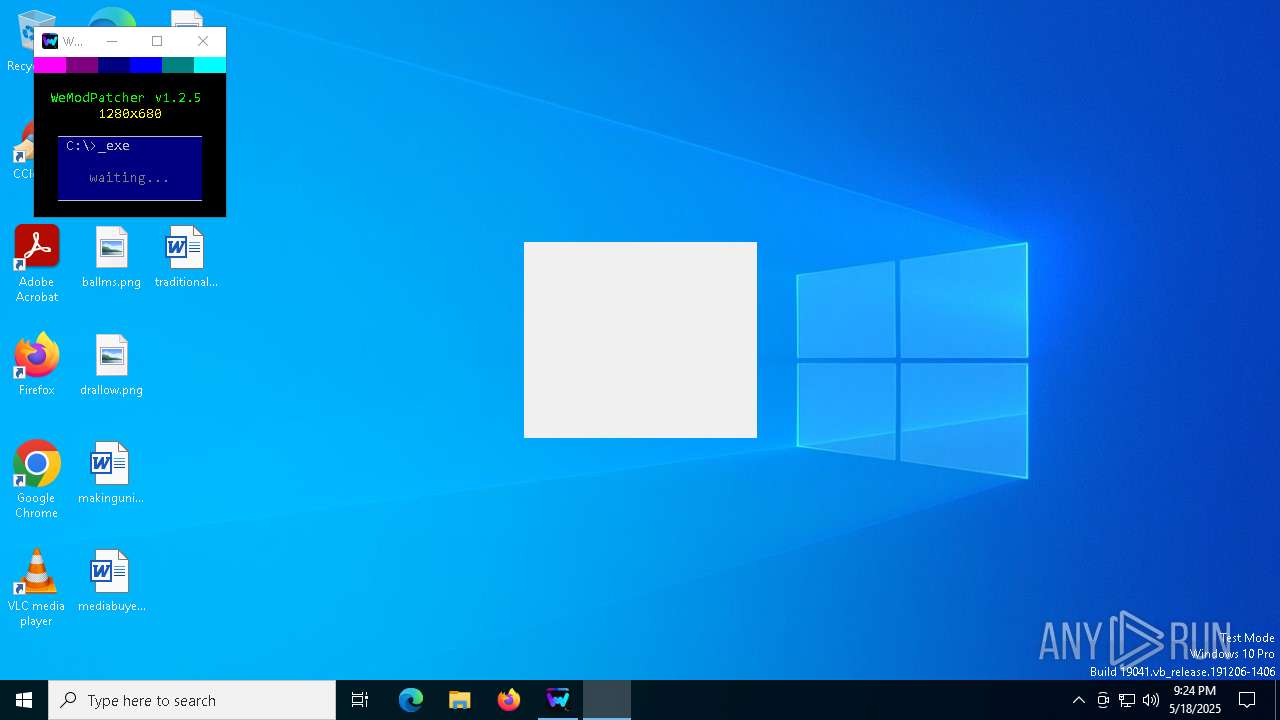
| File name: | WeModPatcher.exe |
| Full analysis: | https://app.any.run/tasks/1c64f3e5-e059-4392-8986-dcc27ec5af51 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 21:23:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 2D2B9C759730A8B30107748A3FDF9F09 |
| SHA1: | 229B793724849EBC236D1352D8ABAE6C825FE256 |
| SHA256: | 23EF62989C2210F05BD598C64EC995B96C381EE15FF78ECDD6225FB163C0A388 |
| SSDEEP: | 98304:40RcUTfCh2HVNYDly8O54AFy9iH1Md2AV3OeghbDE5CdXkVe1NpHHvpUyt80P36t:rB/wOs |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops 7-zip archiver for unpacking
- WeModPatcher.exe (PID: 7516)
Executing commands from a ".bat" file
- WeModPatcher.exe (PID: 7516)
Starts CMD.EXE for commands execution
- WeModPatcher.exe (PID: 7516)
- cmd.exe (PID: 7580)
Application launched itself
- cmd.exe (PID: 7580)
Execution of CURL command
- cmd.exe (PID: 7580)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 7764)
- cmd.exe (PID: 7580)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7580)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 6032)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 5800)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 5668)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 7684)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 6560)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 1764)
- cmd.exe (PID: 6820)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 1020)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 4988)
Starts application with an unusual extension
- cmd.exe (PID: 6564)
- cmd.exe (PID: 7580)
Get information on the list of running processes
- cmd.exe (PID: 7580)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 6032)
- cmd.exe (PID: 7696)
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 5352)
- mshta.exe (PID: 7020)
- mshta.exe (PID: 7640)
Executes application which crashes
- mshta.exe (PID: 5352)
- mshta.exe (PID: 7020)
- mshta.exe (PID: 7640)
- mshta.exe (PID: 7448)
- mshta.exe (PID: 6540)
- mshta.exe (PID: 7656)
- mshta.exe (PID: 2644)
- mshta.exe (PID: 904)
- mshta.exe (PID: 7236)
- mshta.exe (PID: 5360)
- mshta.exe (PID: 8164)
- mshta.exe (PID: 7756)
- mshta.exe (PID: 3024)
- mshta.exe (PID: 7552)
- mshta.exe (PID: 4728)
- mshta.exe (PID: 7272)
- mshta.exe (PID: 6424)
- mshta.exe (PID: 4244)
- mshta.exe (PID: 7732)
- mshta.exe (PID: 1272)
- mshta.exe (PID: 3884)
- mshta.exe (PID: 3124)
- mshta.exe (PID: 5244)
- mshta.exe (PID: 4724)
- mshta.exe (PID: 236)
- mshta.exe (PID: 7728)
- mshta.exe (PID: 6988)
- mshta.exe (PID: 7412)
- mshta.exe (PID: 7356)
- mshta.exe (PID: 5360)
The process creates files with name similar to system file names
- WerFault.exe (PID: 5436)
- WerFault.exe (PID: 7600)
INFO
The sample compiled with english language support
- WeModPatcher.exe (PID: 7516)
Reads the computer name
- curl.exe (PID: 7616)
- curl.exe (PID: 7676)
- curl.exe (PID: 7732)
Execution of CURL command
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7712)
Create files in a temporary directory
- WeModPatcher.exe (PID: 7516)
Checks supported languages
- WeModPatcher.exe (PID: 7516)
- curl.exe (PID: 7616)
- curl.exe (PID: 7676)
- curl.exe (PID: 7732)
- mode.com (PID: 2692)
- chcp.com (PID: 6744)
- chcp.com (PID: 4976)
- chcp.com (PID: 4120)
- chcp.com (PID: 7196)
- chcp.com (PID: 1052)
- chcp.com (PID: 3768)
Changes the display of characters in the console
- cmd.exe (PID: 6564)
- cmd.exe (PID: 7580)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7880)
Starts MODE.COM to configure console settings
- mode.com (PID: 2692)
Checks proxy server information
- mshta.exe (PID: 5352)
- mshta.exe (PID: 7020)
- mshta.exe (PID: 7640)
Reads Internet Explorer settings
- mshta.exe (PID: 5352)
- mshta.exe (PID: 7020)
- mshta.exe (PID: 7640)
Creates files or folders in the user directory
- WerFault.exe (PID: 5436)
- WerFault.exe (PID: 7600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:07:30 08:52:08+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 92672 |
| InitializedDataSize: | 1956352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.2.5.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 1.2.5.0 |
| ProductVersion: | 1.2.5 |
| ProductName: | WeModPatcher |
| OriginalFileName: | WeModPatcher.bat |
| FileDescription: | WeModPatcher |
| LegalCopyright: | brunolee® |
Total processes
383
Monitored processes
223
Malicious processes
2
Suspicious processes
30
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | C:\WINDOWS\system32\cmd.exe /c mshta.exe "C:\Users\admin\Downloads\Launcher.hta" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | mshta.exe "C:\Users\admin\Downloads\Launcher.hta" | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 3221225477 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | chcp 850 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | chcp 850 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | chcp 850 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\WerFault.exe -u -p 4724 -s 1984 | C:\Windows\System32\WerFault.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | chcp 850 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | C:\WINDOWS\system32\cmd.exe /c mshta.exe "C:\Users\admin\Downloads\Launcher.hta" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
250 964
Read events
250 964
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
92
Text files
122
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\Options.hta | html | |
MD5:C0826786D1B58B03C4C134865CD0A0A6 | SHA256:E4CDEA4433591103E4C416165B9B7EEBFF79C30B011EEE839064C0621FE0B209 | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\WeModPatcherTools | compressed | |
MD5:7D2DBEC2395D4CF262EAF10C9B944F4C | SHA256:43F2B4E8D63A62055E8A2CDF80C8809ED6A9FE1574141A9083CA998B65C7E082 | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\lang\lang_de.ini | text | |
MD5:56F718D833D85B64D368A746CEC7D311 | SHA256:9296A56AE3F33183E5DD78159EEDC14E7C55D58B6FF984D30480927F3491A0A6 | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\Options.ini | text | |
MD5:83503A2A8B9F78CFFA4ED444885C4959 | SHA256:E217B87EA4F57FA0FBF70BED27EDA1DA7FF3A4D3B7A989BF15B1261E6735387A | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\AppData\Local\Temp\B509.tmp\B50A.tmp\B50B.bat | binary | |
MD5:A11E36537E59303FD2D217D30C310F21 | SHA256:312EEF935DFB4A14D9997555C1921BE0EAD0AB209FEE2D655148C91C9A60EA0D | |||
| 7580 | cmd.exe | C:\Users\admin\Downloads\IsAdminNecessary | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\lang\lang_tr.ini | text | |
MD5:BC7CBB4ADA04CE76B890600EADBBA4D7 | SHA256:A85BD038A89BE70A95278E4C06980E89254EAEA8D3F6DA667F35A84749F10215 | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\lang\lang_en.ini | text | |
MD5:DA7F78CEA561177B4593E43E472B8A61 | SHA256:5CE043FA53863E2FC94E42D72D870DA746D94CA5CDBC1E1F6FBD364681D69F26 | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\lang\lang_es.ini | text | |
MD5:EFE851D125CBF4EA90D87CF1F469E331 | SHA256:5D75679F3A5CD60EA5700C5F83AF9411D404B1A6077EB994D90597BDFE9855D9 | |||
| 7516 | WeModPatcher.exe | C:\Users\admin\Downloads\lang\lang_pt.ini | text | |
MD5:98D8CB666E73522D7478520D685183CC | SHA256:E56FB42EA5361EDF06D352ADCB3C46CD2A675C59D455B2FAF7D14727ACA1ADE3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
40
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4164 | firefox.exe | GET | 404 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4164 | firefox.exe | GET | 404 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4164 | firefox.exe | GET | 404 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4164 | firefox.exe | GET | 404 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4164 | firefox.exe | GET | 404 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4164 | firefox.exe | GET | 404 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7616 | curl.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
7676 | curl.exe | 172.65.251.78:443 | gitlab.com | CLOUDFLARENET | US | whitelisted |
7732 | curl.exe | 104.22.68.199:443 | pastebin.com | CLOUDFLARENET | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4164 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
gitlab.com |
| whitelisted |
pastebin.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |