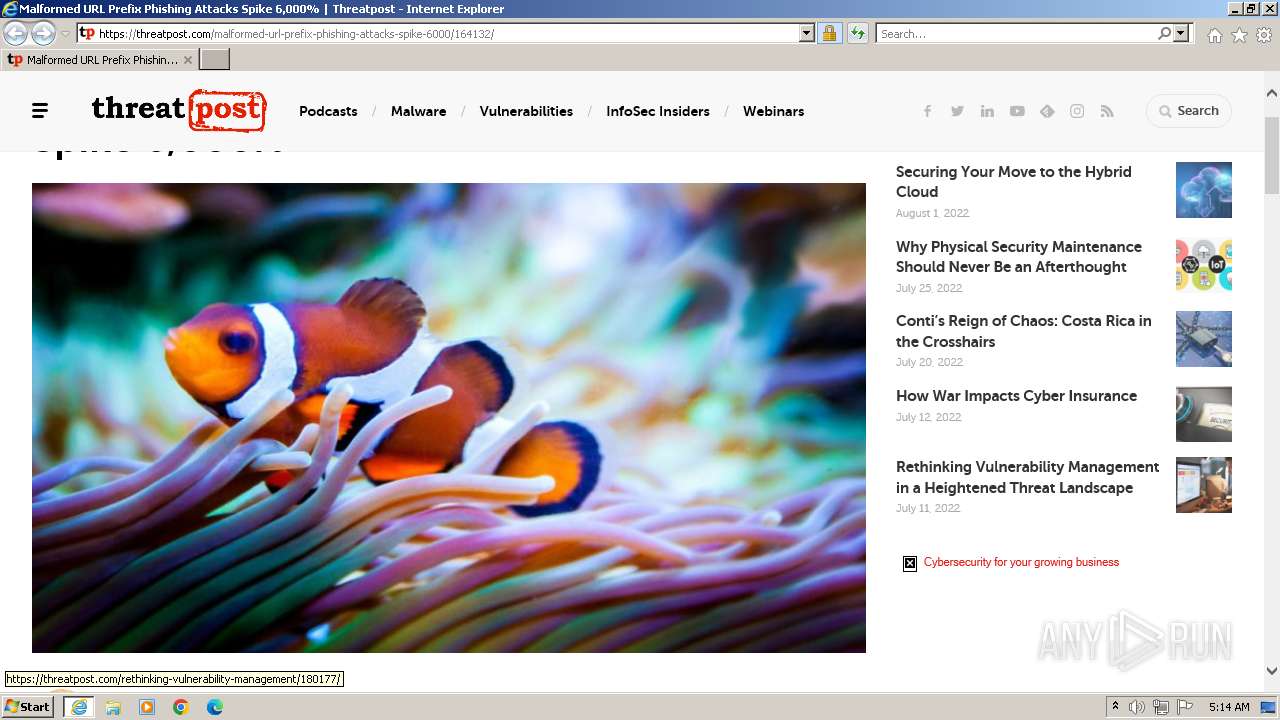
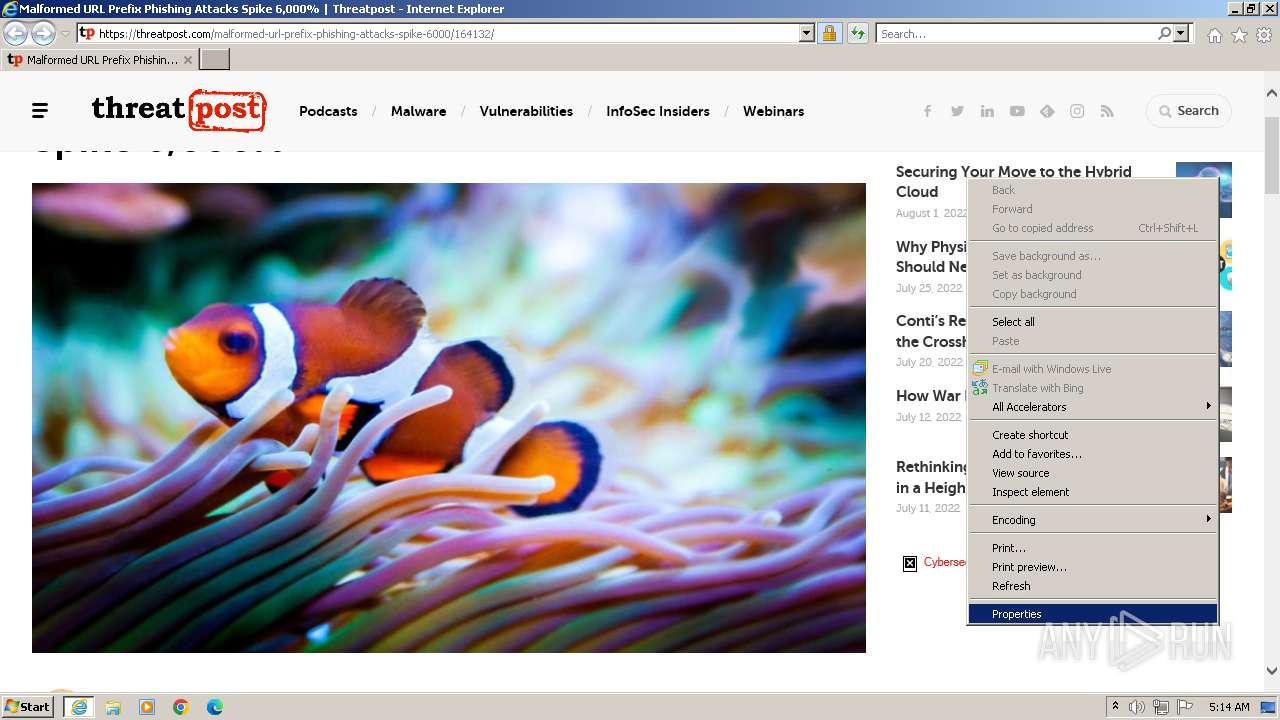
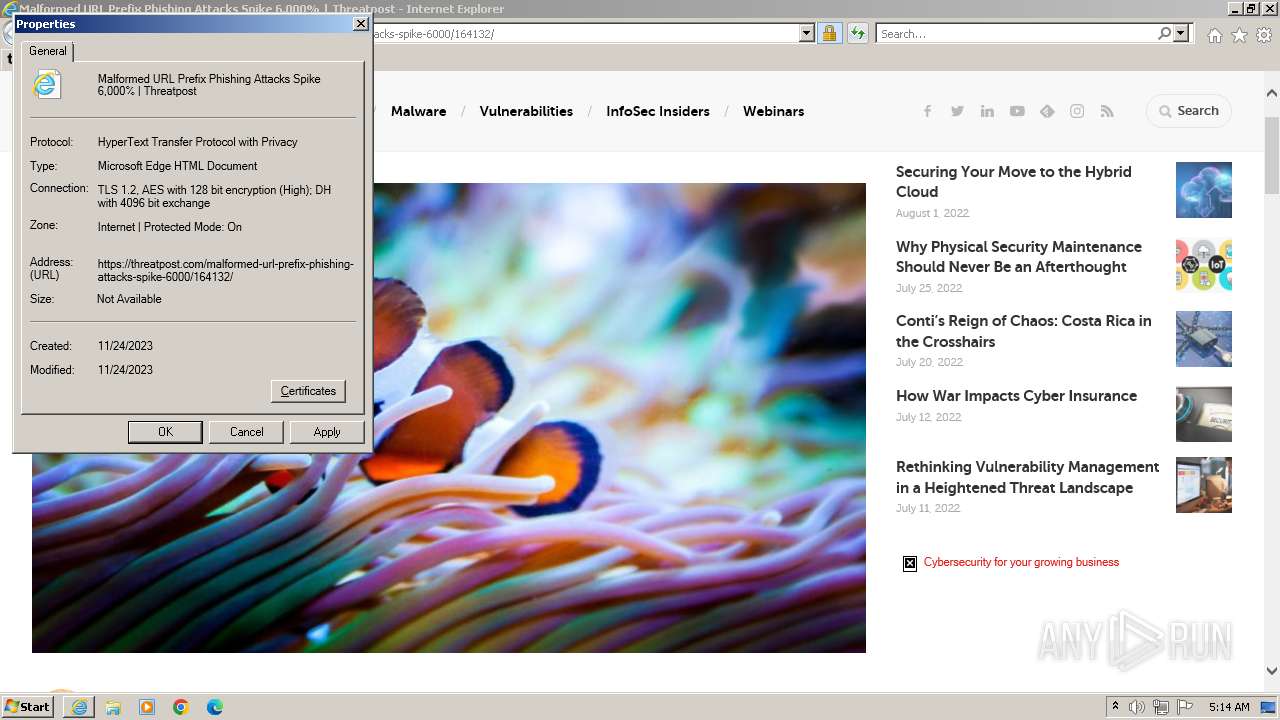
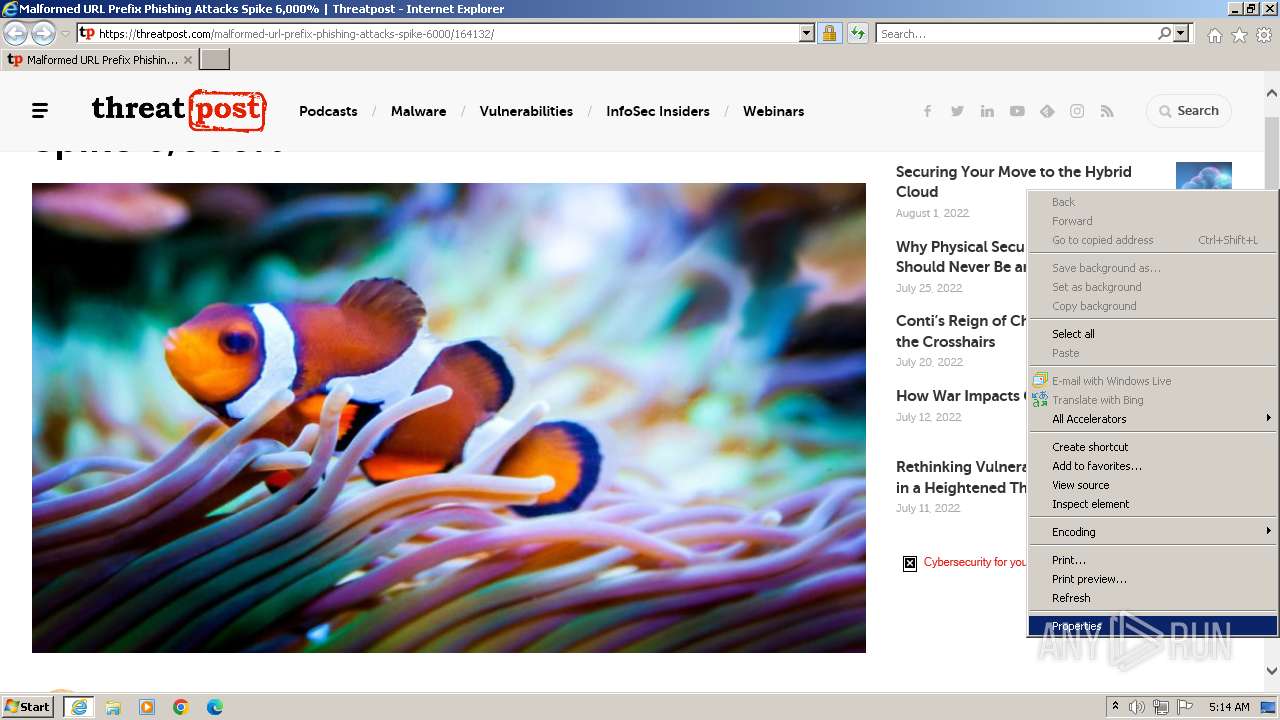
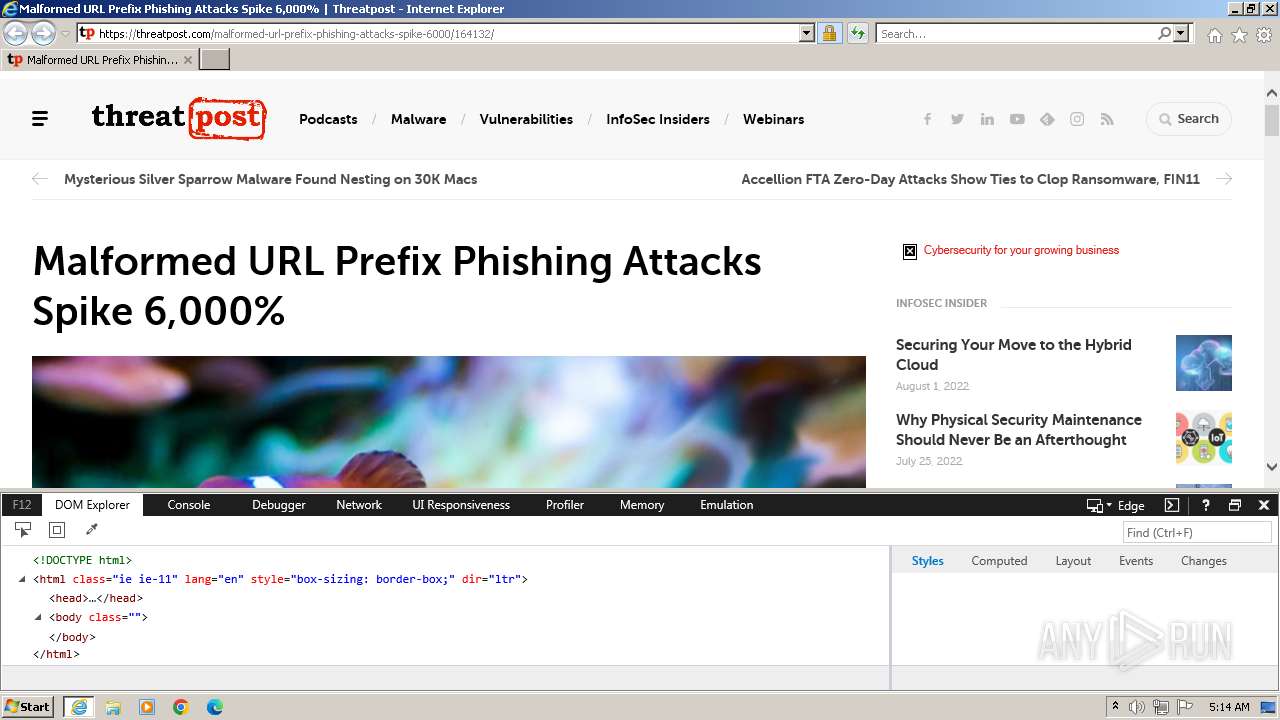
| URL: | https://threatpost.com/malformed-url-prefix-phishing-attacks-spike-6000/164132/ |
| Full analysis: | https://app.any.run/tasks/1e4168ae-dc34-4a96-87c2-9a9bfbbf4d48 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 05:14:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | E87FBC3E3F951CB444EDCD249DF0E1A81B8B5F9F |
| SHA256: | 23C1B981A6DF184CE99C6D87F20915B156C46FDE0AC9FBF319EC48EA8F631AA6 |
| SSDEEP: | 3:N8FXpKHXCpoec3vOuxKPQK:2tpKHhvOyk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes as Windows Service
- IEEtwCollector.exe (PID: 3556)
INFO
Application launched itself
- iexplore.exe (PID: 2168)
Manual execution by a user
- wmpnscfg.exe (PID: 3372)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3372)
Checks supported languages
- wmpnscfg.exe (PID: 3372)
Reads the computer name
- wmpnscfg.exe (PID: 3372)
Reads the time zone
- IEEtwCollector.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://threatpost.com/malformed-url-prefix-phishing-attacks-spike-6000/164132/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2168 CREDAT:2888981 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2168 CREDAT:3216662 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2168 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3372 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3556 | C:\Windows\system32\IEEtwCollector.exe /V | C:\Windows\System32\IEEtwCollector.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: IE ETW Collector Service Exit code: 0 Version: 11.00.9600.19597 (winblue_ltsb_escrow.191216-1311) Modules
| |||||||||||||||
Total events
30 150
Read events
30 071
Write events
76
Delete events
3
Modification events
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2168) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
115
Text files
183
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:E0D0F1FCA3B24CC7C5B8EE5B88BABB1A | SHA256:BDC3C3D7B7F94C8E74B8A796E6CAEE2DCCC0468C366475207A505365D000737F | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:5DB805A64CCFD81B7EC4C1342429DEA8 | SHA256:95E9E6A87955F8D3195C468E6FFED4E6F65501430ABB3CC47506FE91D5D8D7DC | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\59D76868C250B3240414CE3EFBB12518_2B25FADED2DA9F381F380A4E8E70997B | binary | |
MD5:61BACBE0E2B0D346E4A30131E85F1C6D | SHA256:0F045866E23A88EFA4B98533CFC87D59D87741F3A63F901F6EB7B737B3CA338F | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:D4150FA971908AE807010D387345D31B | SHA256:39675ABDD39198DE5D4704EC50BF35B328A770AC666E3EC8ECE9B94CF644BF30 | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\59D76868C250B3240414CE3EFBB12518_2B25FADED2DA9F381F380A4E8E70997B | binary | |
MD5:E9A91F49953E566DAB204EBEB8BAE6E1 | SHA256:7F4F656496CD9F3D3FFF033FF1B598428A16F46564535EA7430195502FFEA0B3 | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jquery-1.12.4-wp[1].js | text | |
MD5:455F4240B81915EA051B23D783291B6B | SHA256:3BB2621A4C0C710F6E78404473AEBFF8E115A28F8D53F44339B867C63AD93B26 | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\min[1].css | text | |
MD5:DA48D5BAA0AF764D73C5A21259268D52 | SHA256:B666F3487F9EEB1640E4F69171BCFC6E92E5487DC213E93BD2E8165A3CA42608 | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\164132[1].htm | html | |
MD5:385073D206628201FC5387EF11421B8E | SHA256:6E54AA52CEFE2441A86B5B4EC1B083D0F73F579E36FBB2869E88370307104237 | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\lazyload[1].js | text | |
MD5:AECFFFB30EDBAA504F663DD4391FB7EB | SHA256:3307268982E18BAE27FB0691DEA184C6A6CE845DB0F6CE1F41CA63E948DDE8A6 | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
162
DNS requests
49
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3320 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | binary | 471 b | unknown |
3320 | iexplore.exe | GET | 200 | 108.138.2.107:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
3320 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.51 Kb | unknown |
3320 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQChuVoVf7HVAxLxWCb2kXo7 | unknown | binary | 472 b | unknown |
3320 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | unknown | binary | 471 b | unknown |
3320 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3320 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEkpLy9ROx7U76vGUhC06D6E%3D | unknown | binary | 1.39 Kb | unknown |
3320 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEF2rtEA6xK7GEl4nbt8ZZfk%3D | unknown | binary | 471 b | unknown |
3320 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAYXNz%2FIHHkVvXOSWAF6FRE%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 304 | 67.27.159.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?60b2f43ad8cf70d9 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3320 | iexplore.exe | 35.173.160.135:443 | threatpost.com | AMAZON-AES | US | unknown |
3320 | iexplore.exe | 67.27.159.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | malicious |
3320 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 67.27.159.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | malicious |
3320 | iexplore.exe | 18.66.97.114:443 | media.kasperskycontenthub.com | — | US | unknown |
3320 | iexplore.exe | 108.138.7.86:443 | media.threatpost.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
threatpost.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
media.kasperskycontenthub.com |
| whitelisted |
media.threatpost.com |
| whitelisted |
kasperskycontenthub.com |
| unknown |
www.google.com |
| whitelisted |
media.kaspersky.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3320 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |