| File name: | savniaskw4y.exe |
| Full analysis: | https://app.any.run/tasks/1aac8480-da13-46cf-99a9-306a2770e84c |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2019, 19:01:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E0C57F5E02C7D3ECA05EA3DC11428A66 |
| SHA1: | 6C5246F19A5511F60F006B5ADBD347C898B753A1 |
| SHA256: | 23B652FF28EE44120334A7D0A6DBE7C56F104BE04B5AF40F449B8764E838DB16 |
| SSDEEP: | 3072:Xh09TuK9ps1SzcOCFXmPXSt/Ji7n739w69bjWKszmPsgQrV:xw9CCcHmPX2JN69WvzmTQ |
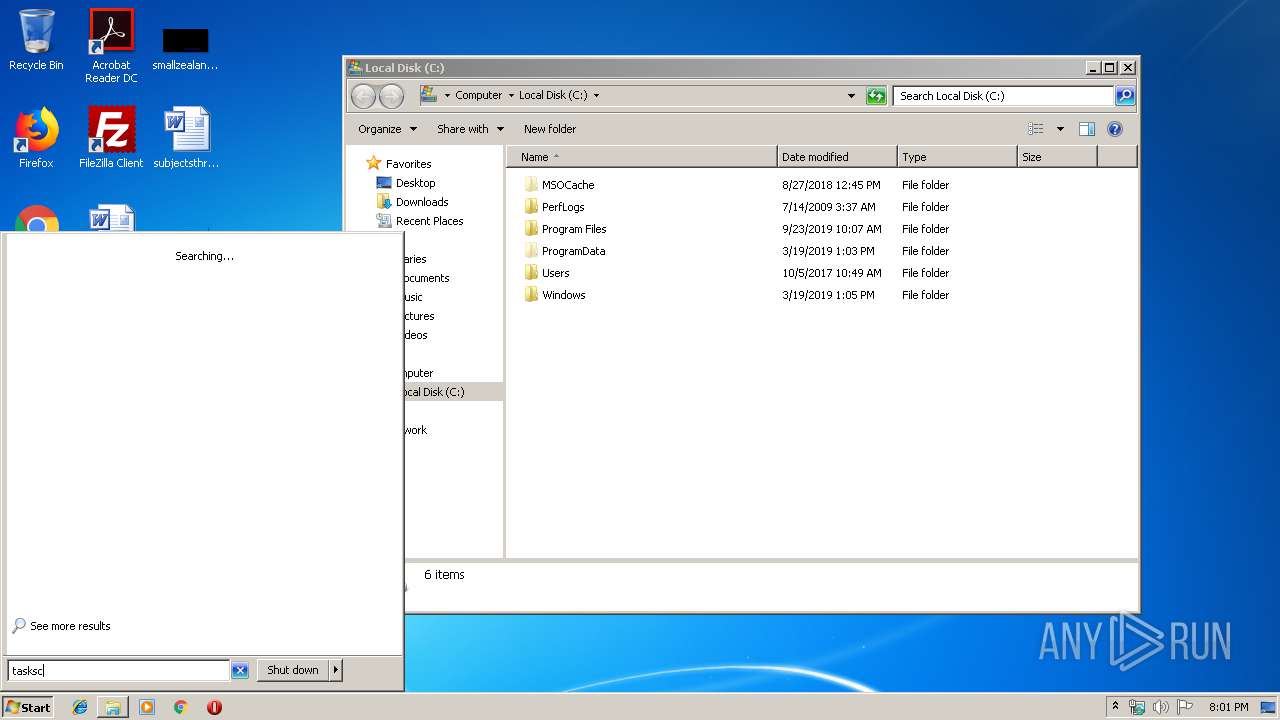
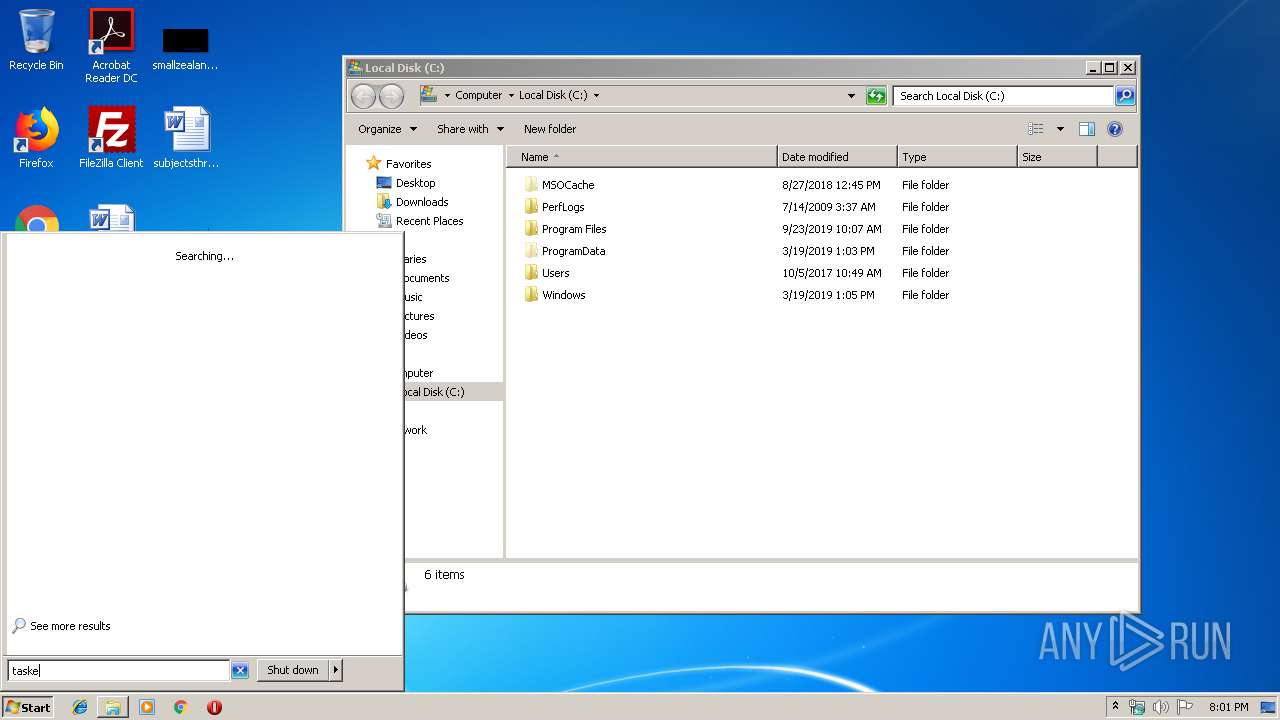
MALICIOUS
Application was injected by another process
- taskeng.exe (PID: 2032)
- explorer.exe (PID: 352)
Runs injected code in another process
- savniaskw4y.exe (PID: 2768)
Changes the login/logoff helper path in the registry
- explorer.exe (PID: 352)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 352)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:09:27 00:04:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 163840 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 172032 |
| EntryPoint: | 0x52a20 |
| OSVersion: | 4 |
| ImageVersion: | 4 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 60.15.119.125 |
| ProductVersionNumber: | 60.15.119.125 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ds SOFTWIN Fas |
| FileDescription: | Bxhqc Ncxatl Mviallse |
| FileVersion: | 60, 15, 119, 125 |
| InternalName: | Bxhqc |
| LegalCopyright: | Copyright © Bxhqc Vucgbjdq 2004-2005 |
| OriginalFileName: | Bxhqc.exe |
| ProductName: | Bxhqc Ncxatl Mviallse |
| ProductVersion: | 60, 15, 119, 125 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Sep-2008 22:04:17 |
| Detected languages: |
|
| CompanyName: | ds SOFTWIN Fas |
| FileDescription: | Bxhqc Ncxatl Mviallse |
| FileVersion: | 60, 15, 119, 125 |
| InternalName: | Bxhqc |
| LegalCopyright: | Copyright © Bxhqc Vucgbjdq 2004-2005 |
| OriginalFilename: | Bxhqc.exe |
| ProductName: | Bxhqc Ncxatl Mviallse |
| ProductVersion: | 60, 15, 119, 125 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Sep-2008 22:04:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0002A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0002B000 | 0x00028000 | 0x00027C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94187 |
.rsrc | 0x00053000 | 0x00002000 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.2807 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.53506 | 928 | UNKNOWN | English - United States | RT_VERSION |
2 | 5.16817 | 584 | UNKNOWN | English - United States | RT_ICON |
3 | 5.80767 | 872 | UNKNOWN | English - United States | RT_ICON |
Imports
KERNEL32.DLL |
user32.dll |
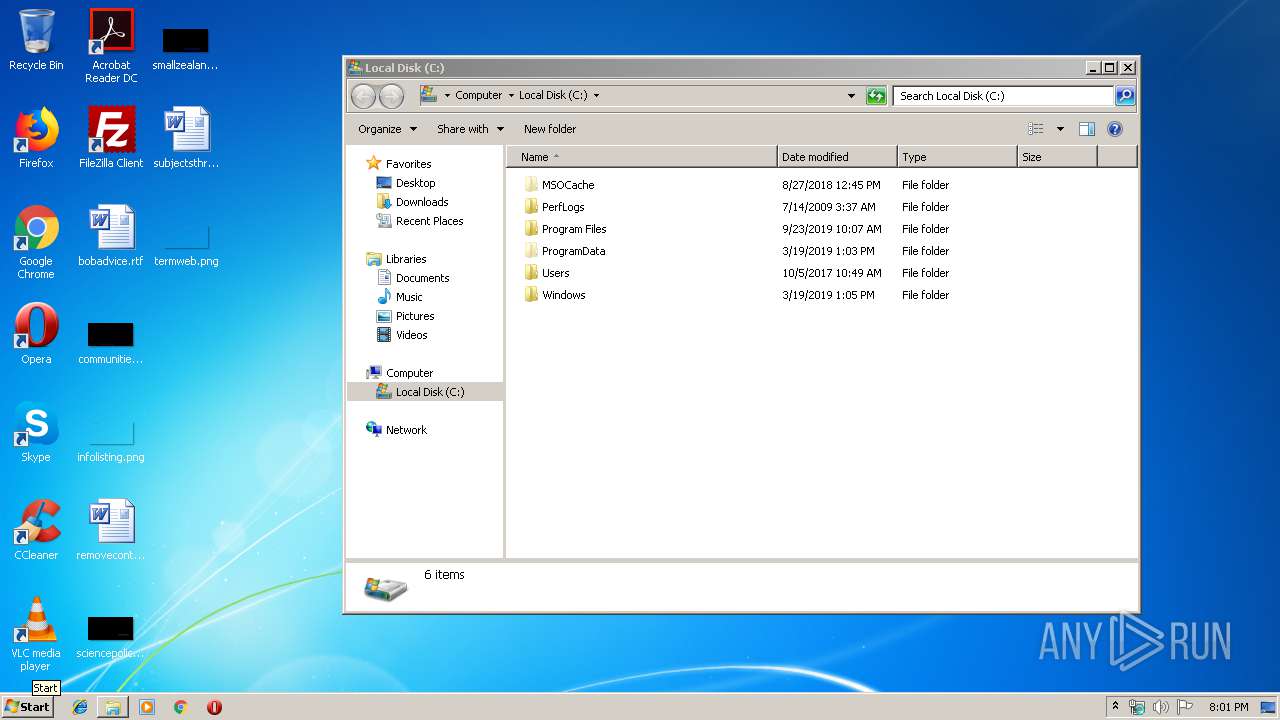
Total processes
35
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
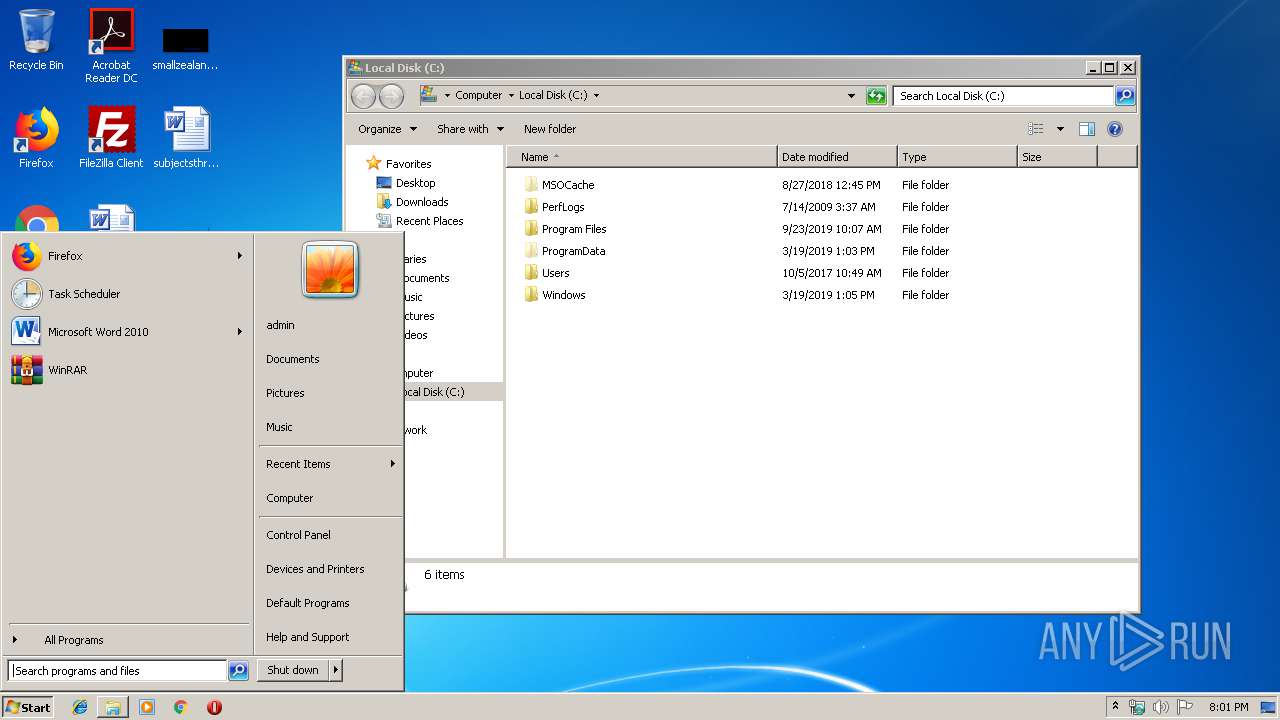
| 2032 | taskeng.exe {532150F8-214C-4D30-9483-0A3BC3E44D0E} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Windows\system32\taskeng.exe" | C:\Windows\system32\taskeng.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 1639 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\savniaskw4y.exe" | C:\Users\admin\AppData\Local\Temp\savniaskw4y.exe | — | explorer.exe | |||||||||||
User: admin Company: Bxhqc Vucgbjdq Integrity Level: MEDIUM Description: Bxhqc Ncxatl Mviallse Exit code: 0 Version: 60, 15, 119, 125 Modules
| |||||||||||||||
Total events
1 784
Read events
490
Write events
1 294
Delete events
0
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000070000000200000009000000080000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\34\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 00000000060000000900000007DB0500000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFF0BB7188FC71D50100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000320000003700000061E61200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\windows journal\journal.exe,-62005 |
Value: Tablet PC | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%windir%\system32\miguiresource.dll,-202 |
Value: Schedule computer tasks to run automatically. | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 352 | explorer.exe | C:\RECYCLER\S-1-5-21-1019142525-4443656465-483704204-0889\winlogon.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
xoco666.com |
| unknown |
tlaloc666.com |
| malicious |