| File name: | 01767717_4 |
| Full analysis: | https://app.any.run/tasks/3f41ef8a-7a0d-4622-9151-332082f1448b |
| Verdict: | Malicious activity |
| Analysis date: | January 13, 2020, 05:05:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
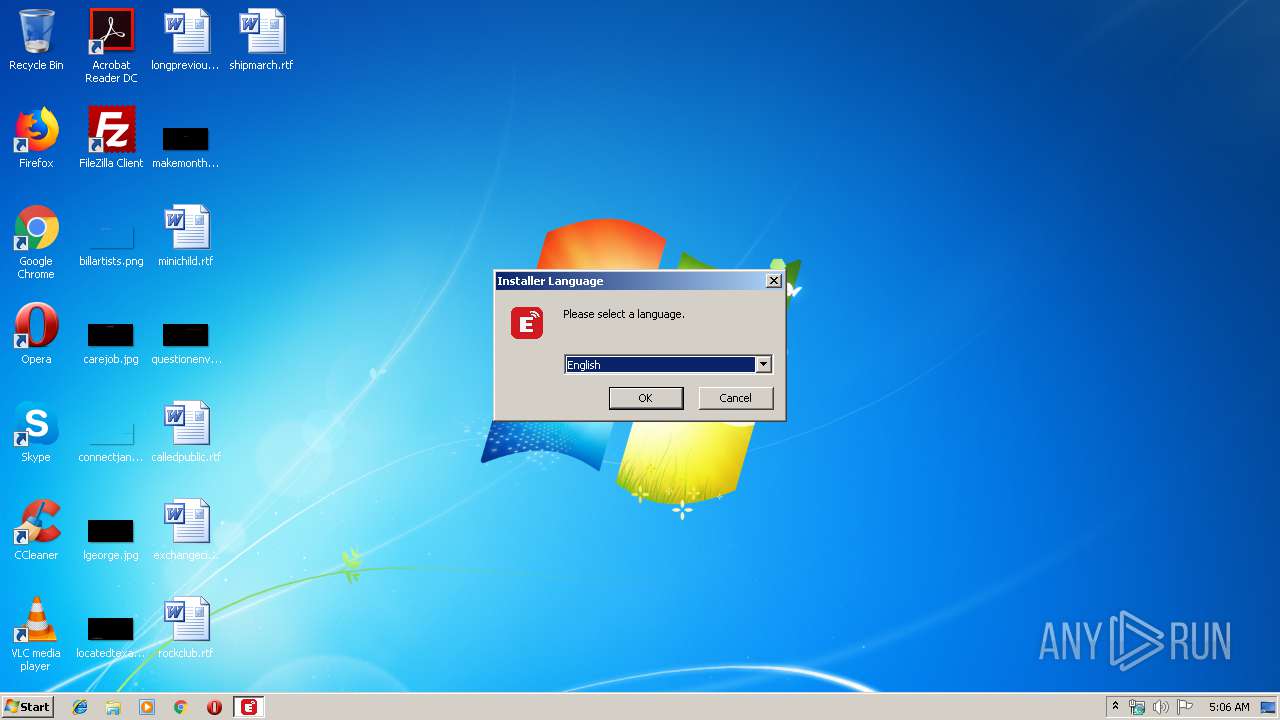
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | FAE5439ED3C78FEA1B1EEE2EF8A6871C |
| SHA1: | 600534AC93BB4C18CB02CB3A8DD6D6EDED80E6B4 |
| SHA256: | 239B0734928B32D90FB9E63EB49DC26871022273424F025C16D57C70B2A4D3B2 |
| SSDEEP: | 196608:PHVyDiVgV9cfQhawHn7KguLgpr/ssgyxxqZoFjA+2jfTMw4fxq4Wt12jj0QSZ5kX:PQWgVafqrHdhIyLqZSA+Y6WX2jAQSTZw |
MALICIOUS
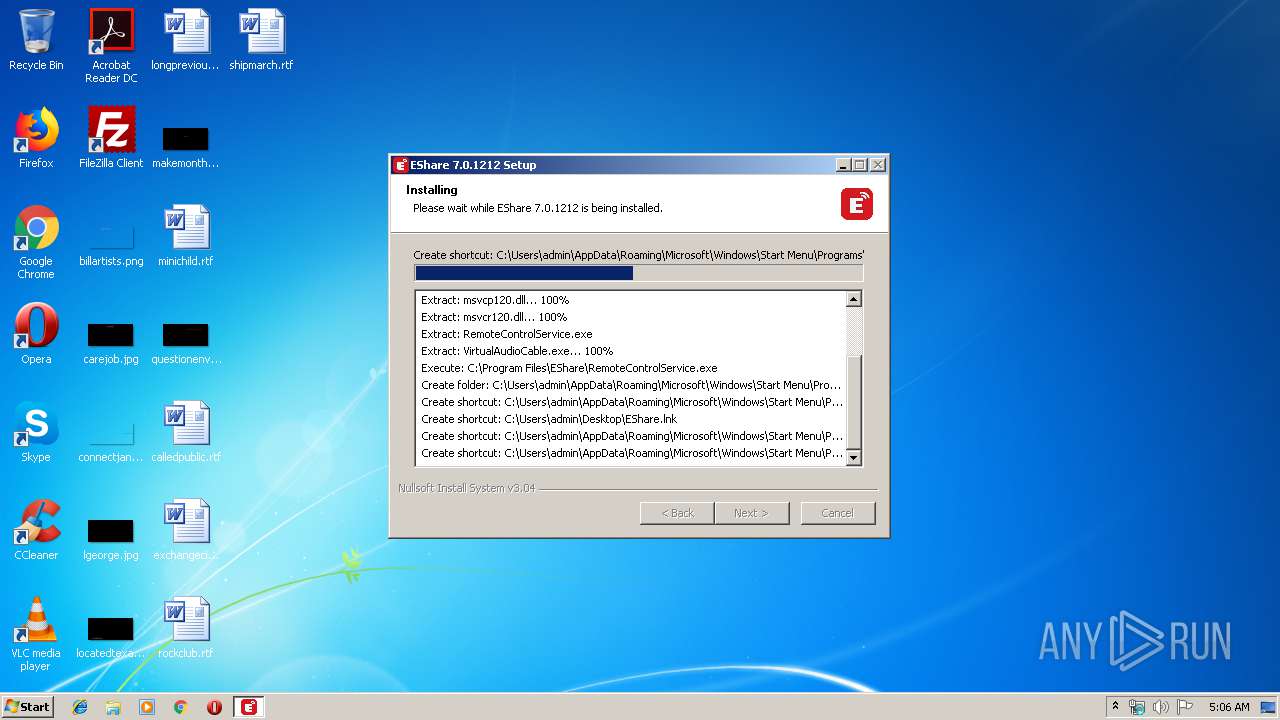
Loads dropped or rewritten executable
- 01767717_4.exe (PID: 328)
Application was dropped or rewritten from another process
- RemoteControlService.exe (PID: 3012)
- EDesktop.exe (PID: 3680)
- EShare.exe (PID: 388)
- EDesktopUAC.exe (PID: 2960)
- ESystemRemoteService.exe (PID: 2040)
SUSPICIOUS
Executable content was dropped or overwritten
- 01767717_4.exe (PID: 328)
- RemoteControlService.exe (PID: 3012)
Creates files in the program directory
- 01767717_4.exe (PID: 328)
- RemoteControlService.exe (PID: 3012)
Creates a software uninstall entry
- RemoteControlService.exe (PID: 3012)
- 01767717_4.exe (PID: 328)
Executed as Windows Service
- ESystemRemoteService.exe (PID: 2040)
Creates files in the user directory
- 01767717_4.exe (PID: 328)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3359 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:27 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000062A5 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43142 |
.rdata | 0x00008000 | 0x00001396 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15971 |
.data | 0x0000A000 | 0x00020318 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.90464 |
.ndata | 0x0002B000 | 0x00012000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003D000 | 0x00011730 | 0x00011800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.58516 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29734 | 1318 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.98048 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
206 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
211 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
44
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
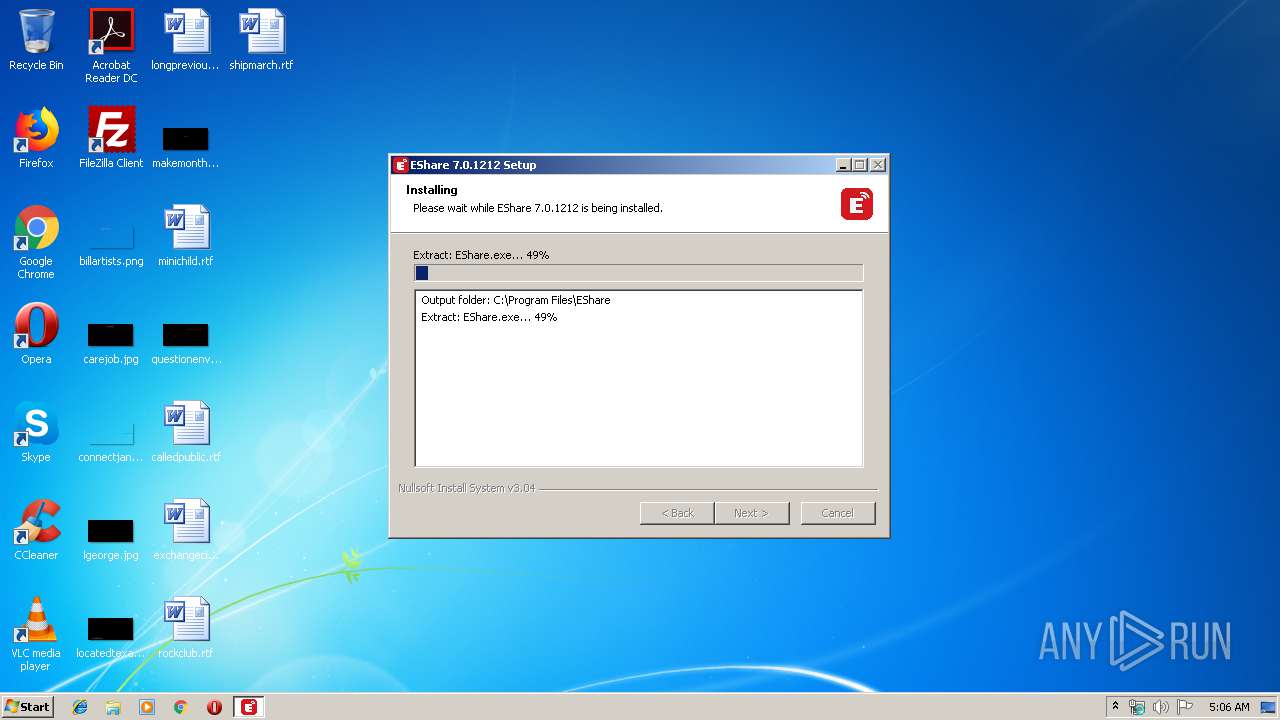
| 328 | "C:\Users\admin\AppData\Local\Temp\01767717_4.exe" | C:\Users\admin\AppData\Local\Temp\01767717_4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
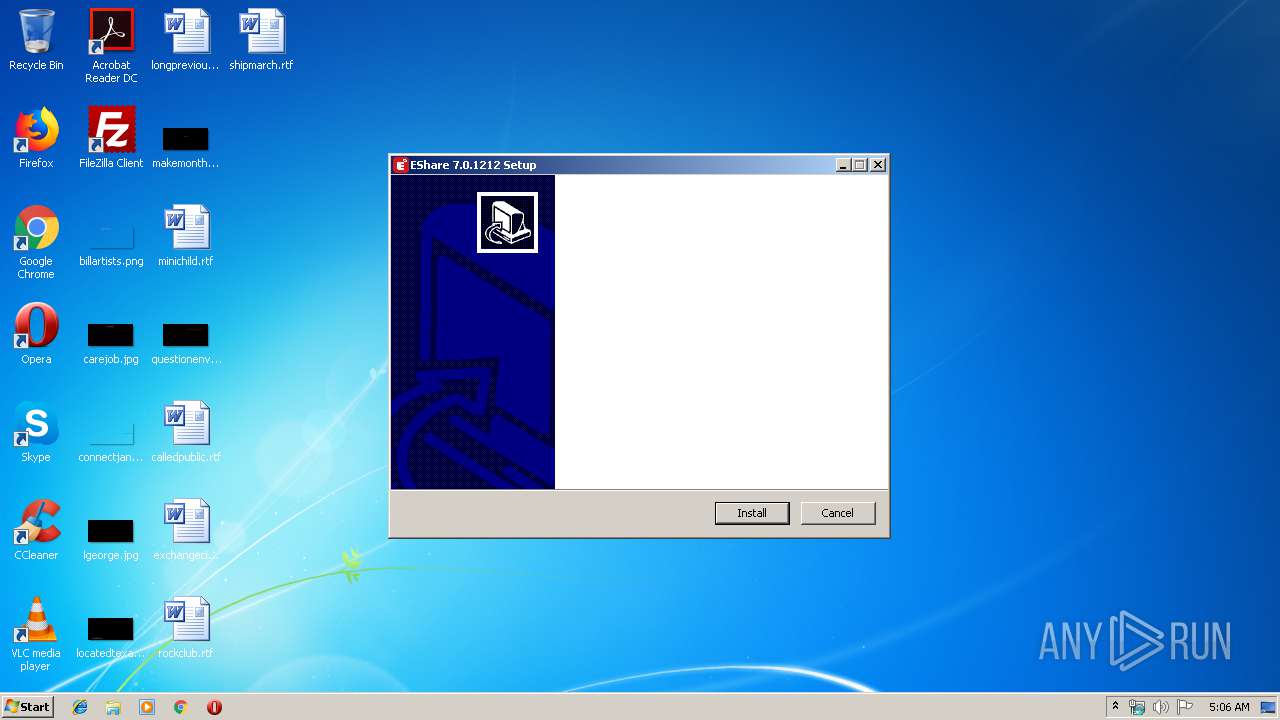
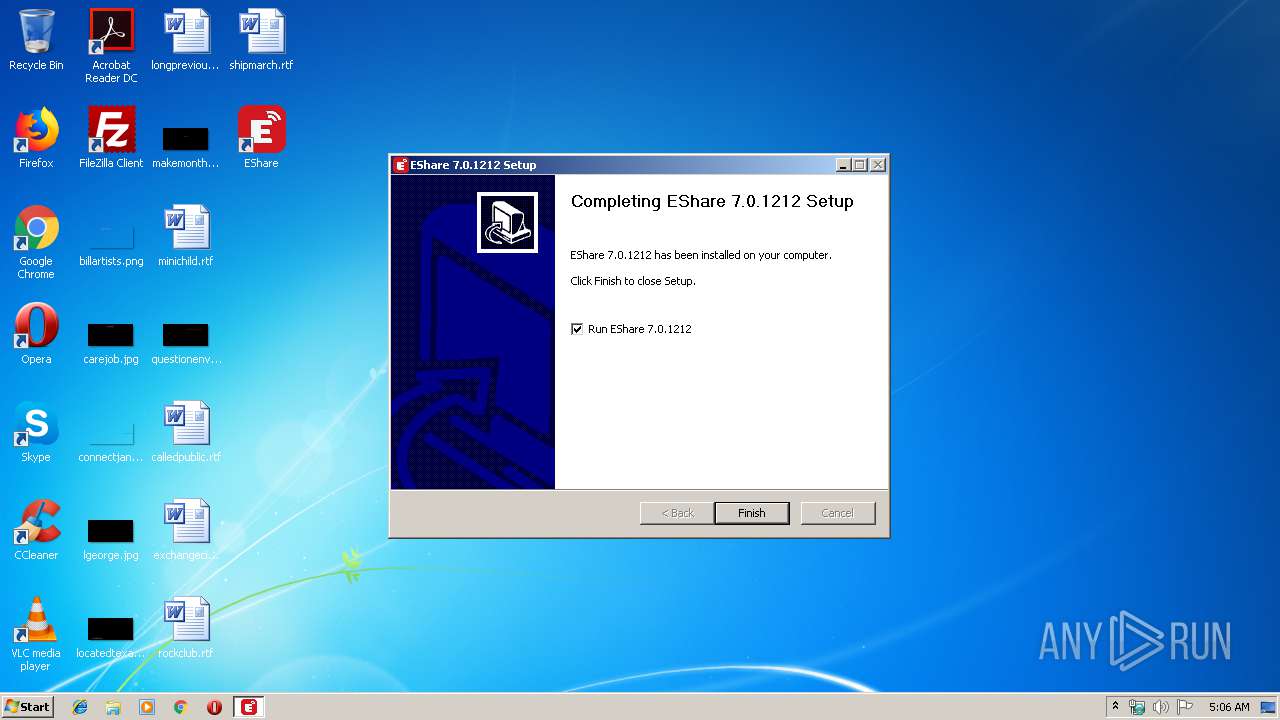
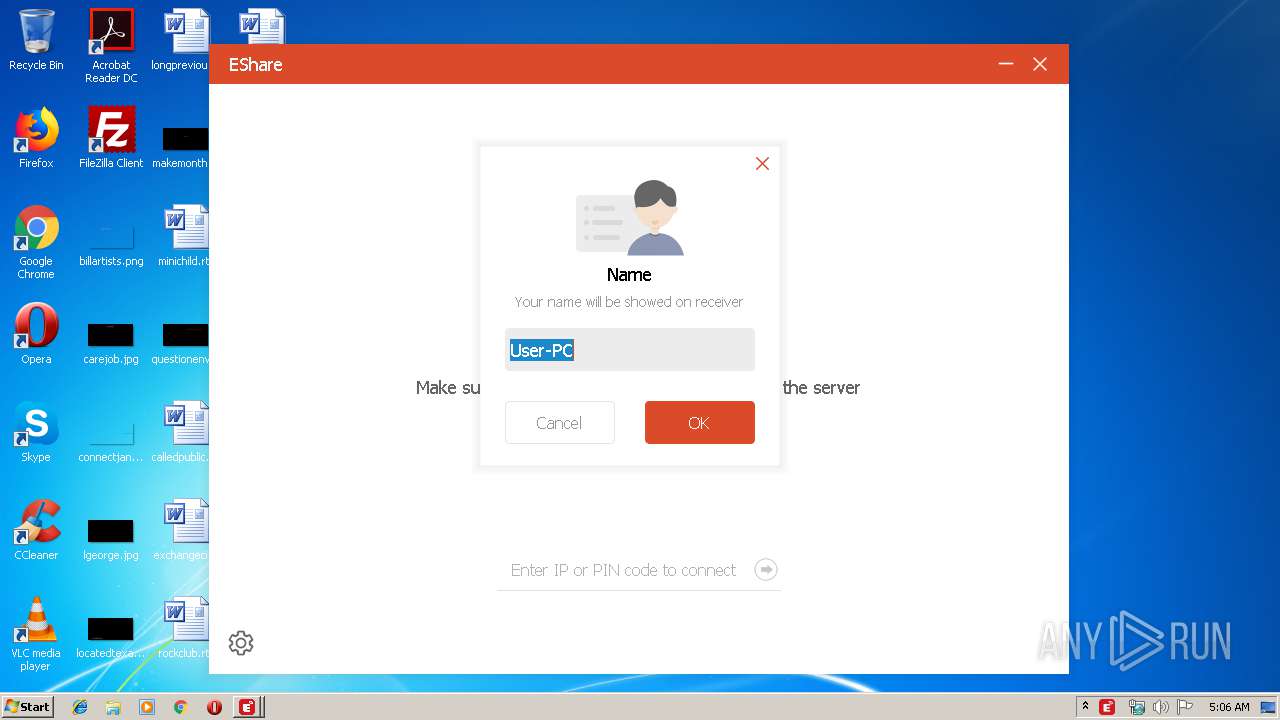
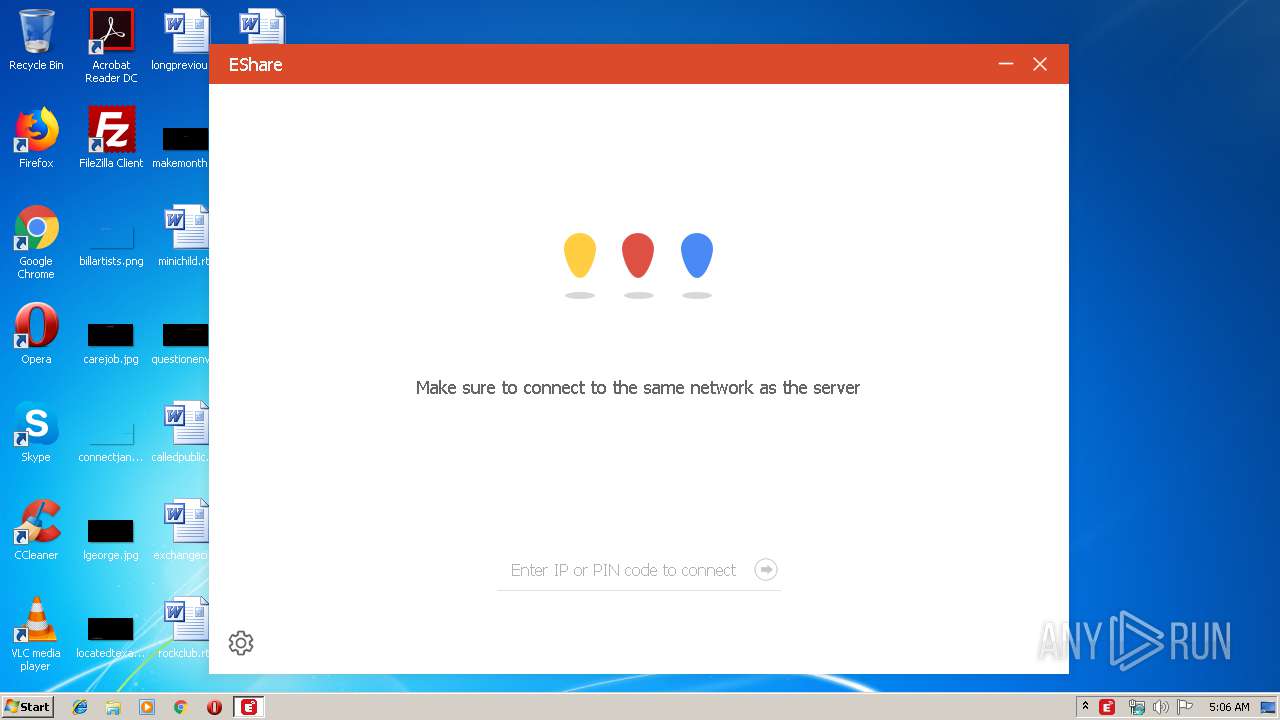
| 388 | "C:\Program Files\EShare\EShare.exe" | C:\Program Files\EShare\EShare.exe | 01767717_4.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 7.0.1212 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\ESystemRemoteService\ESystemRemoteService.exe" | C:\Program Files\ESystemRemoteService\ESystemRemoteService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 1.0.2.928 Modules
| |||||||||||||||
| 2960 | "C:/Program Files/ESystemRemoteService/EDesktopUAC.exe" | C:\Program Files\ESystemRemoteService\EDesktopUAC.exe | — | ESystemRemoteService.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3012 | "C:\Program Files\EShare\RemoteControlService.exe" | C:\Program Files\EShare\RemoteControlService.exe | 01767717_4.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\AppData\Local\Temp\01767717_4.exe" | C:\Users\admin\AppData\Local\Temp\01767717_4.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3680 | "C:/Program Files/ESystemRemoteService/EDesktop.exe" | C:\Program Files\ESystemRemoteService\EDesktop.exe | — | ESystemRemoteService.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
Total events
414
Read events
398
Write events
16
Delete events
0
Modification events
| (PID) Process: | (328) 01767717_4.exe | Key: | HKEY_CURRENT_USER\Software\EShare |
| Operation: | write | Name: | audio |
Value: true | |||
| (PID) Process: | (3012) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\EDesktop.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\ESystemRemoteService\EDesktop.exe | |||
| (PID) Process: | (3012) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | DisplayName |
Value: ESystemRemoteService 1.0 | |||
| (PID) Process: | (3012) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\ESystemRemoteService\uninst.exe | |||
| (PID) Process: | (3012) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\ESystemRemoteService\EDesktop.exe | |||
| (PID) Process: | (3012) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0 | |||
| (PID) Process: | (3012) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | URLInfoAbout |
Value: www.ee-share.com | |||
| (PID) Process: | (3012) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | Publisher |
Value: EShare | |||
| (PID) Process: | (328) 01767717_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\EShare.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\EShare\EShare.exe | |||
| (PID) Process: | (328) 01767717_4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EShare |
| Operation: | write | Name: | DisplayName |
Value: EShare 7.0.1212 | |||
Executable files
16
Suspicious files
0
Text files
40
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | RemoteControlService.exe | C:\Users\admin\AppData\Local\Temp\nsjF5B6.tmp\SimpleSC.dll | — | |
MD5:— | SHA256:— | |||
| 328 | 01767717_4.exe | C:\Users\admin\AppData\Local\Temp\nskC55F.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 328 | 01767717_4.exe | C:\Users\admin\AppData\Local\Temp\nskC55F.tmp\LangDLL.dll | executable | |
MD5:AB1DB56369412FE8476FEFFFD11E4CC0 | SHA256:6F14C8F01F50A30743DAC68C5AC813451463DFB427EB4E35FCDFE2410E1A913B | |||
| 328 | 01767717_4.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\EShare\EShare.lnk | lnk | |
MD5:— | SHA256:— | |||
| 328 | 01767717_4.exe | C:\Program Files\EShare\RemoteControlService.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | RemoteControlService.exe | C:\Program Files\ESystemRemoteService\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 388 | EShare.exe | C:\Users\admin\AppData\Local\EShareClient\settings.ini.Uhg388 | — | |
MD5:— | SHA256:— | |||
| 3012 | RemoteControlService.exe | C:\Program Files\ESystemRemoteService\ESystemRemoteService.exe | executable | |
MD5:— | SHA256:— | |||
| 388 | EShare.exe | C:\Users\admin\AppData\Local\EShareClient\settings.ini.lock | — | |
MD5:— | SHA256:— | |||
| 388 | EShare.exe | C:\Users\admin\AppData\Local\EShareClient\EShare.ini.NlY388 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
EShare.exe | registerRenderers...........
|
EShare.exe | load en.qm
|
EShare.exe | libpng warning: iCCP: known incorrect sRGB profile
|
EShare.exe | libpng warning: iCCP: known incorrect sRGB profile
|
EShare.exe | libpng warning: iCCP: known incorrect sRGB profile
|
EShare.exe | libpng warning: iCCP: known incorrect sRGB profile
|
EShare.exe | libpng warning: iCCP: known incorrect sRGB profile
|
EShare.exe | QObject::startTimer: Timers cannot have negative intervals
|
EShare.exe | libpng warning: iCCP: known incorrect sRGB profile
|
EShare.exe | libpng warning: iCCP: known incorrect sRGB profile
|