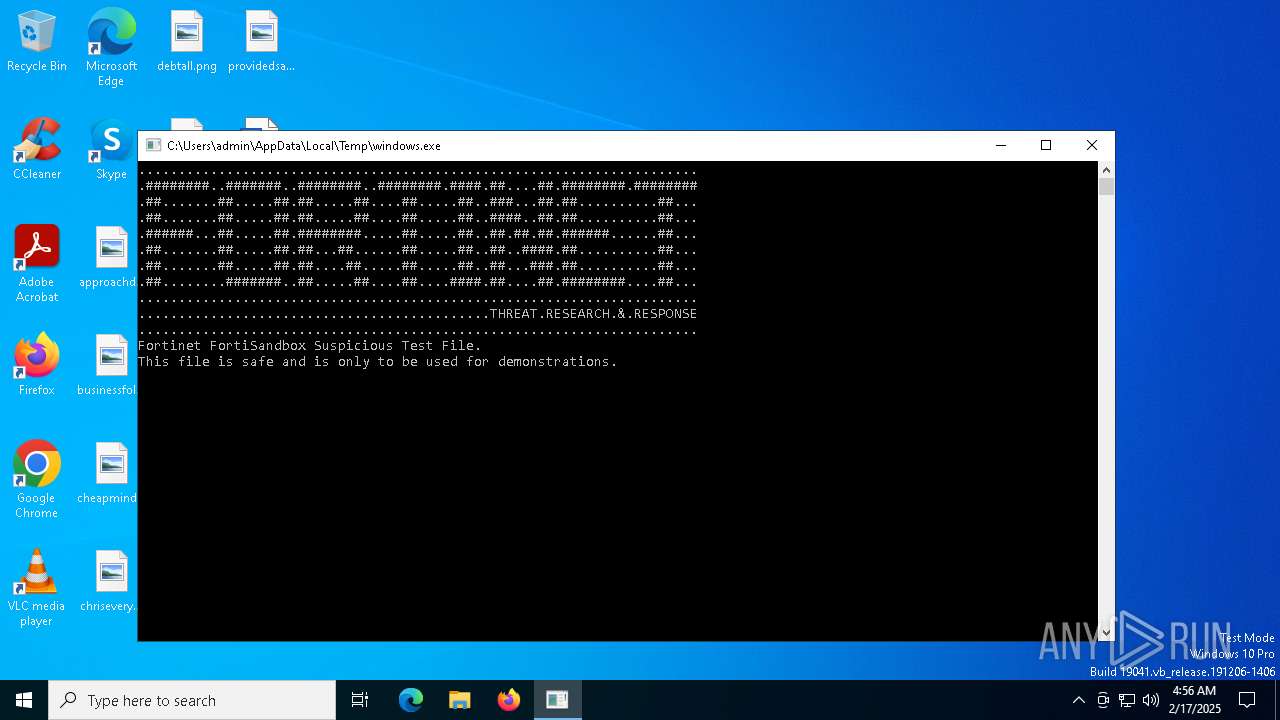
| File name: | windows.exe |
| Full analysis: | https://app.any.run/tasks/fd36156f-bd74-478f-ae6b-e9efafdc7c1c |
| Verdict: | Malicious activity |
| Analysis date: | February 17, 2025, 04:56:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 4 sections |
| MD5: | 74B08C57FC59DE662C4F34FB66A435D7 |
| SHA1: | 44C823B9F62EB51FB47EED58B12DE9B58B063980 |
| SHA256: | 239AAC4569DCD6C9F1FE1DC435E9215BA148AE913902B9A60F531B804CA4B569 |
| SSDEEP: | 48:0F+pxwOZv1wOZGZdPkwOW1wAPFsXEJfmbJuoH5BPs:zxwOZv1wOZGZdPkwOW1wAPF+Ofmduy5 |
MALICIOUS
The EICAR Standard Anti-Virus Test File is detected
- windows.exe (PID: 3988)
SUSPICIOUS
Reads security settings of Internet Explorer
- windows.exe (PID: 3988)
INFO
Creates files or folders in the user directory
- windows.exe (PID: 3988)
Checks supported languages
- windows.exe (PID: 3988)
Create files in a temporary directory
- windows.exe (PID: 3988)
Reads the computer name
- windows.exe (PID: 3988)
Checks proxy server information
- windows.exe (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1973:05:23 20:33:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 0.4 |
| CodeSize: | 512 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
125
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\AppData\Local\Temp\windows.exe" | C:\Users\admin\AppData\Local\Temp\windows.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
473
Read events
470
Write events
3
Delete events
0
Modification events
| (PID) Process: | (3988) windows.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3988) windows.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3988) windows.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | windows.exe | C:\Users\admin\AppData\Local\Temp\drop.com | text | |
MD5:69630E4574EC6798239B091CDA43DCA0 | SHA256:131F95C51CC819465FA1797F6CCACF9D494AAAFF46FA3EAC73AE63FFBDFD8267 | |||
| 3988 | windows.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\eicar[1].com | text | |
MD5:69630E4574EC6798239B091CDA43DCA0 | SHA256:131F95C51CC819465FA1797F6CCACF9D494AAAFF46FA3EAC73AE63FFBDFD8267 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
12
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3988 | windows.exe | GET | 200 | 192.241.205.137:80 | http://rb3.ftnt.io/download00/eicar.com | US | text | 69 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3988 | windows.exe | 192.241.205.137:80 | rb3.ftnt.io | DIGITALOCEAN-ASN | US | suspicious |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 23.51.98.7:80 | ocsp.digicert.com | Akamai International B.V. | US | whitelisted |
1076 | svchost.exe | 2.19.106.8:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rb3.ftnt.io |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |