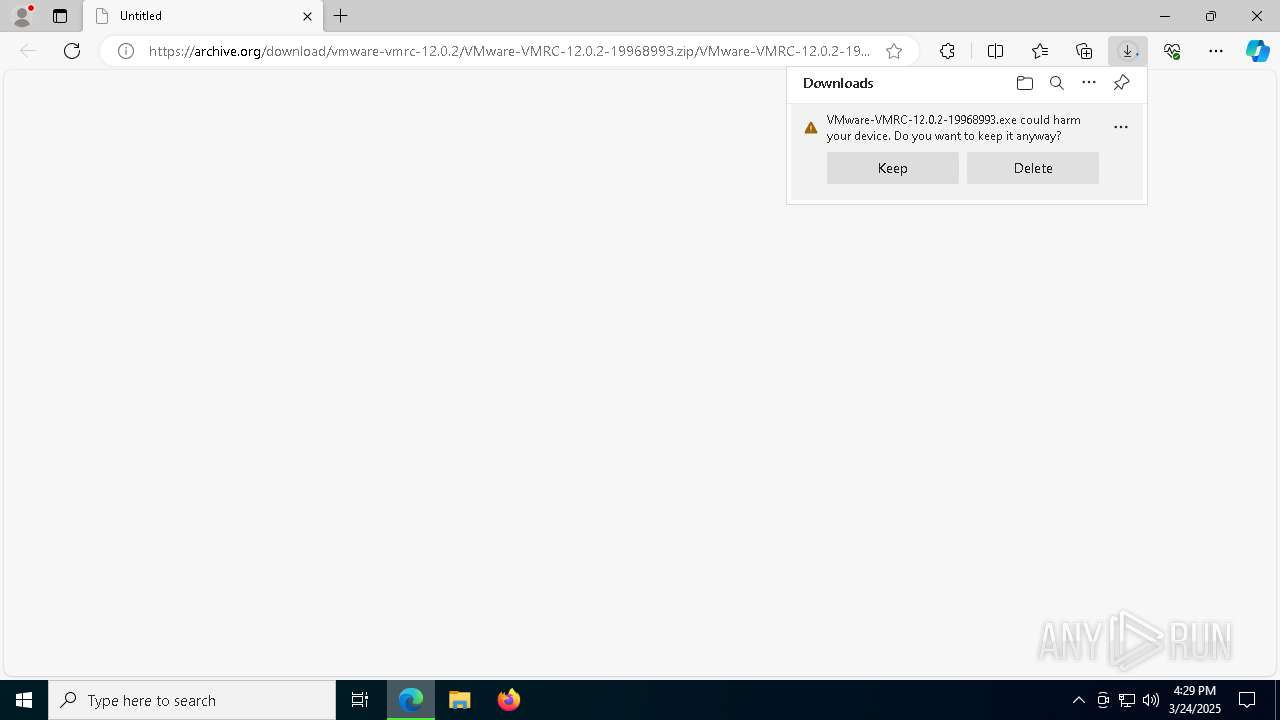
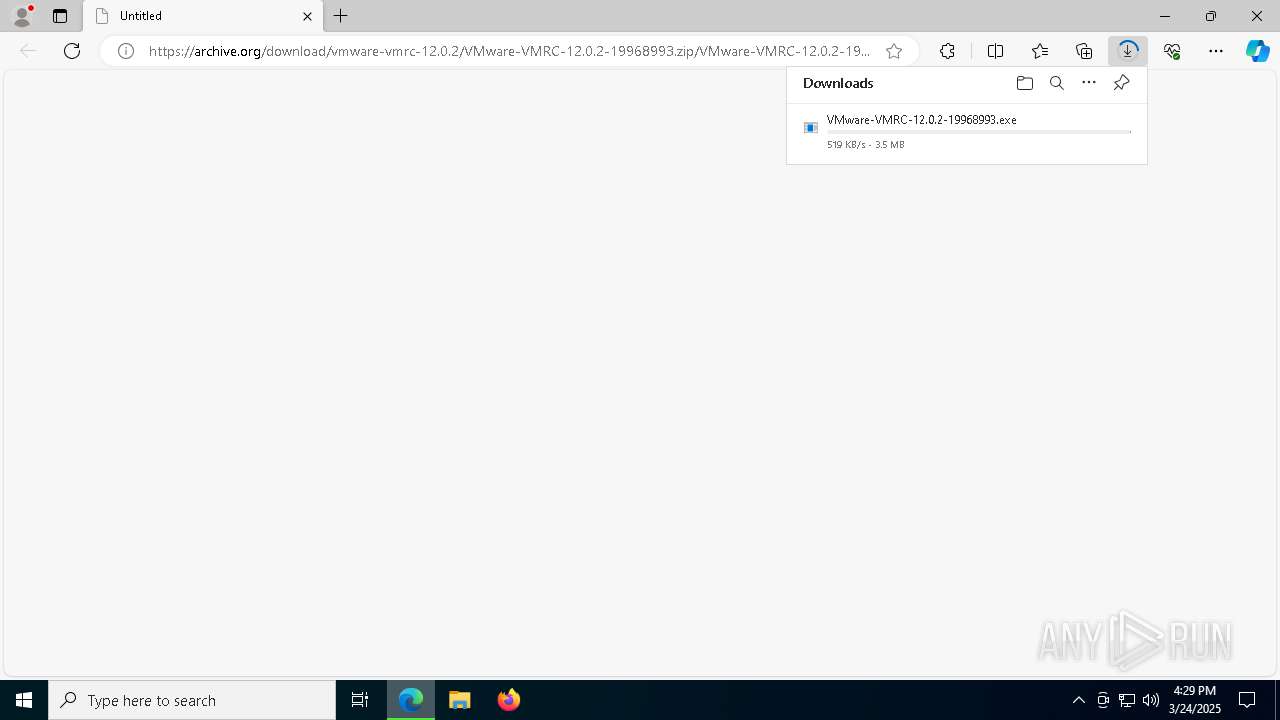
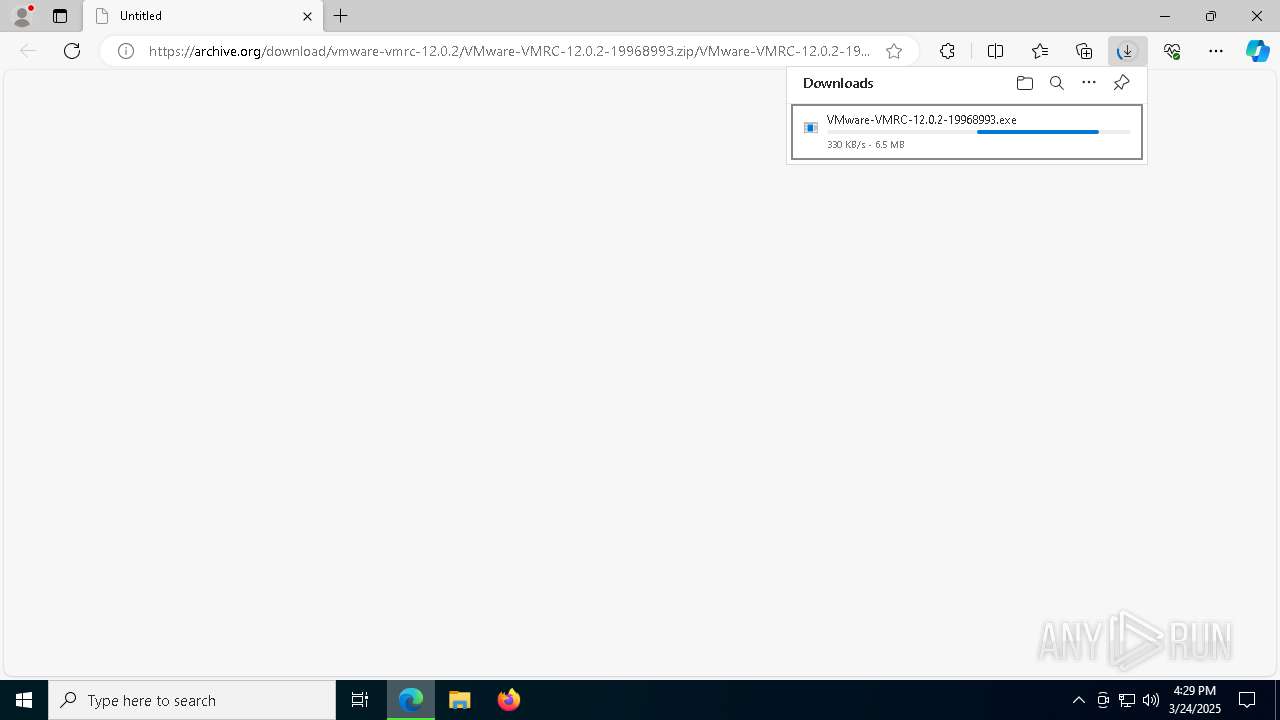
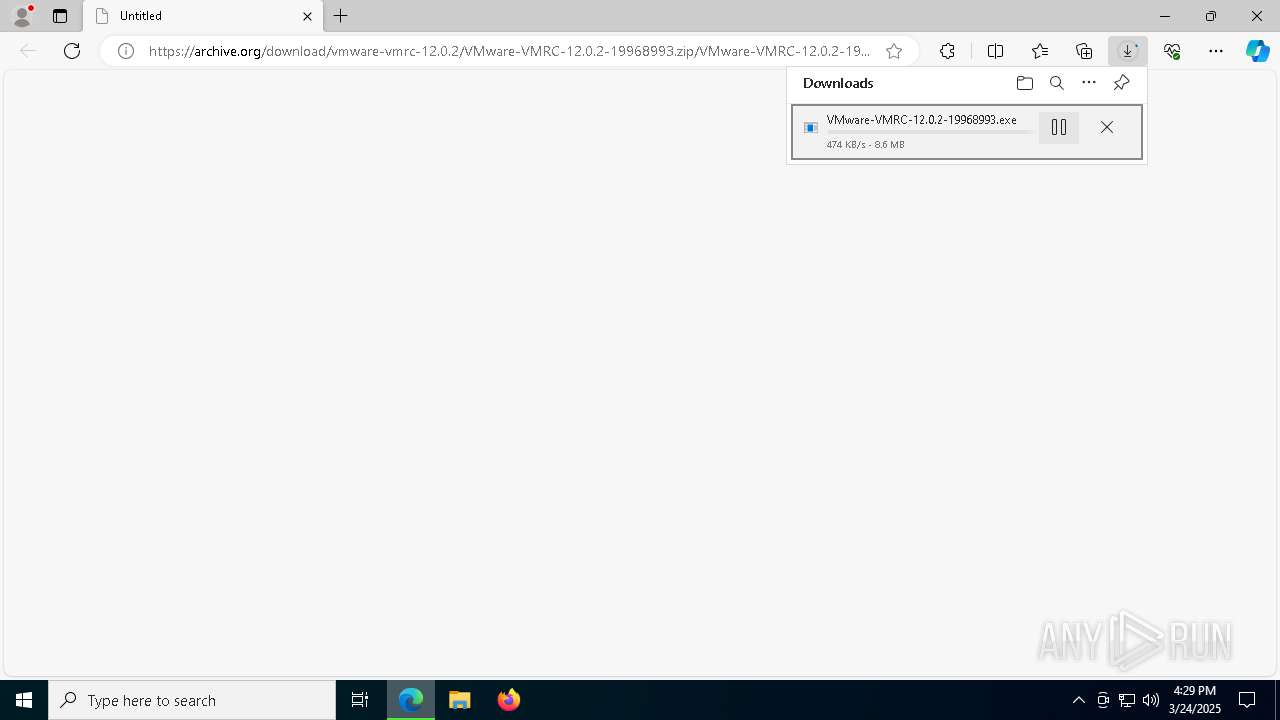
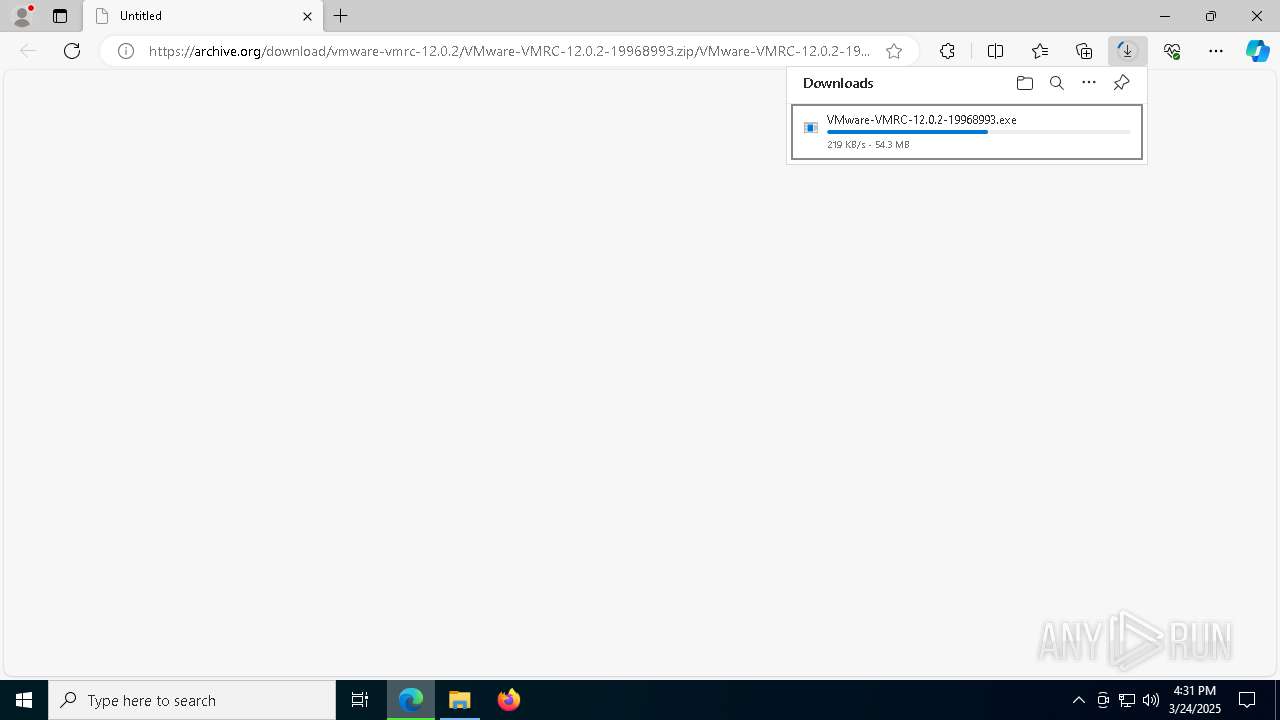
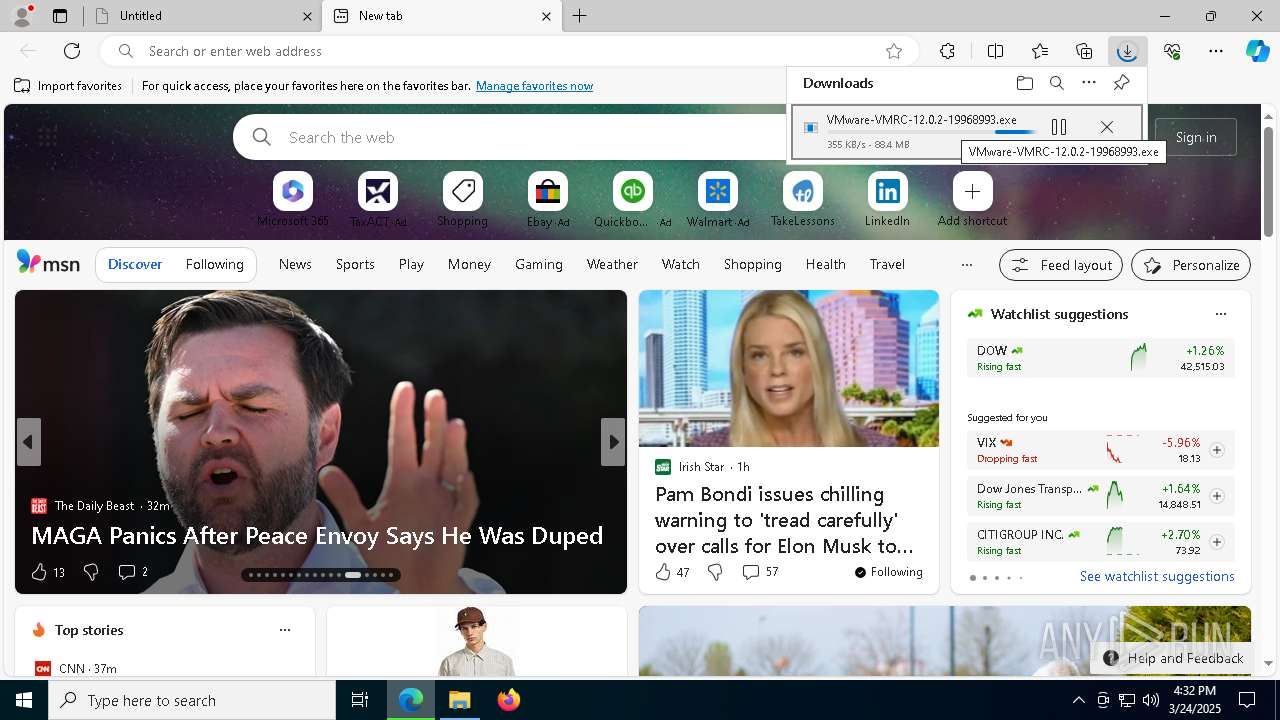
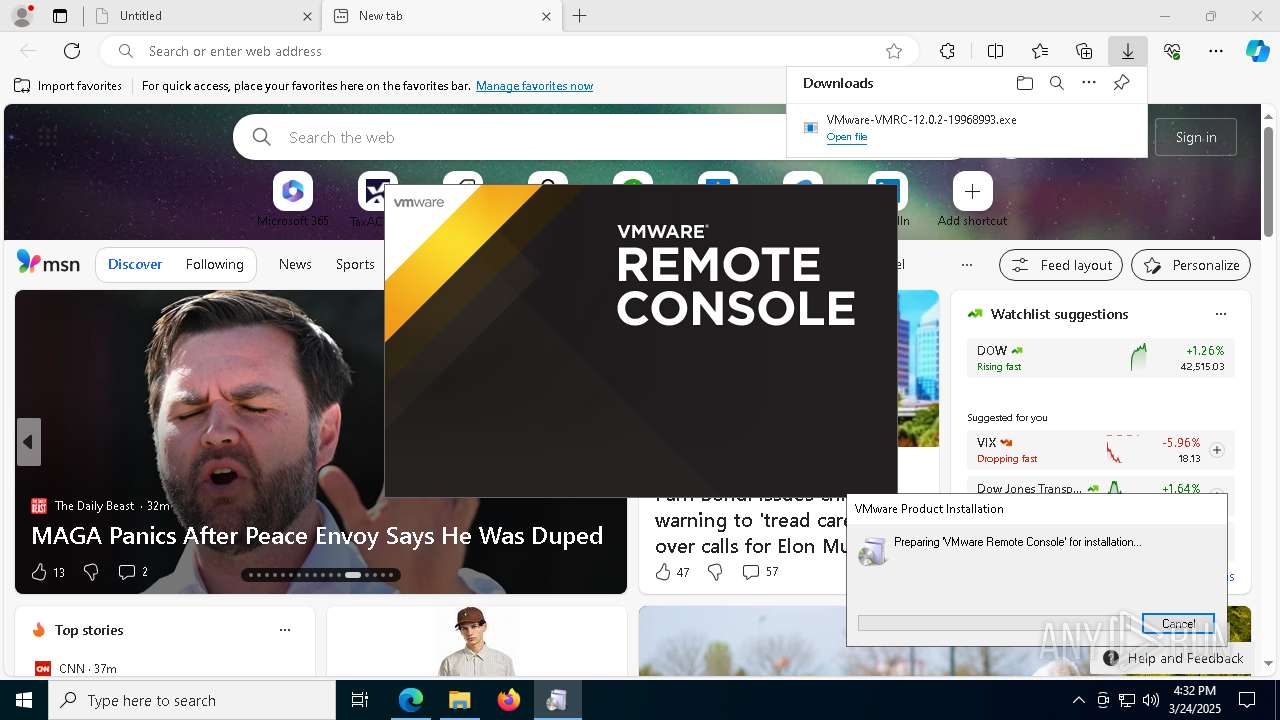
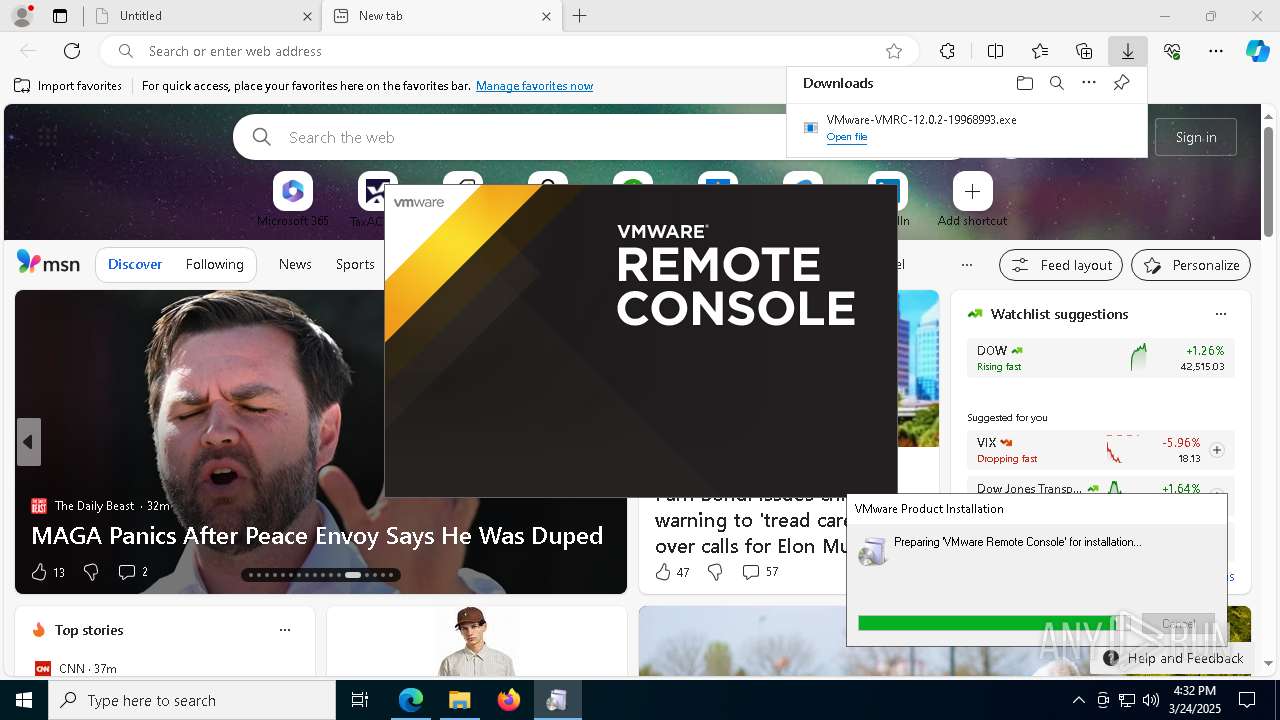
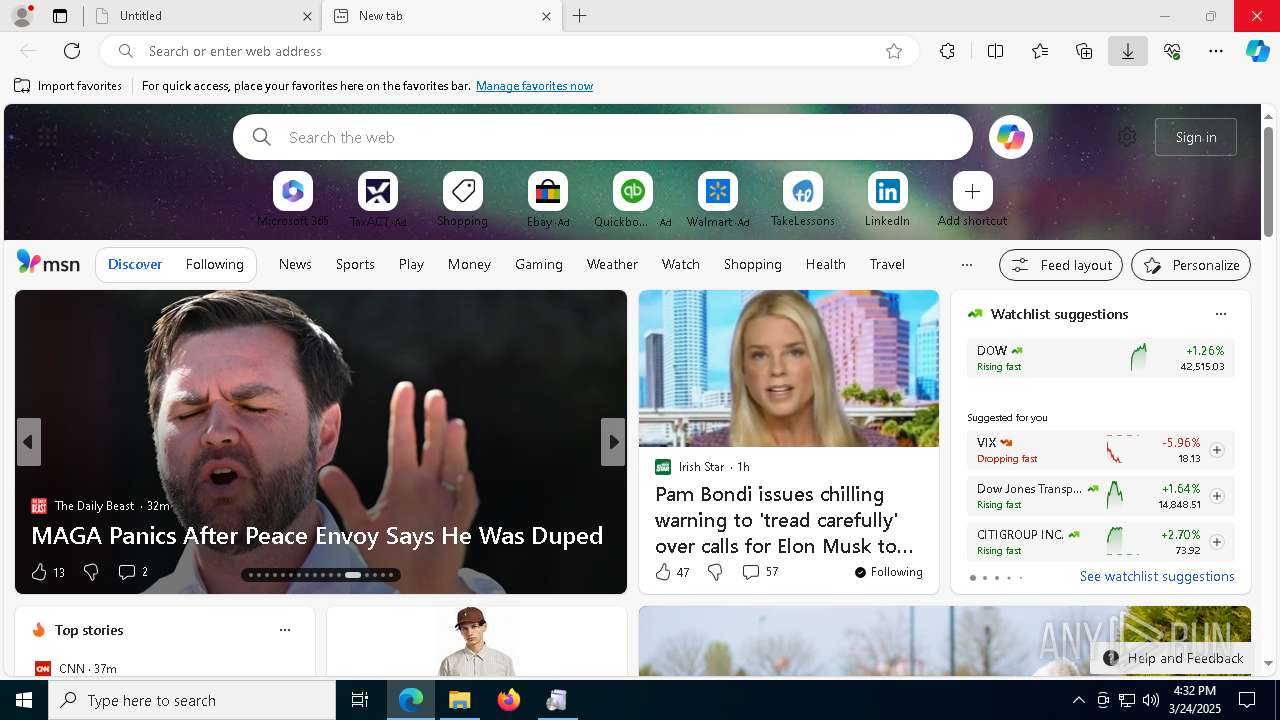
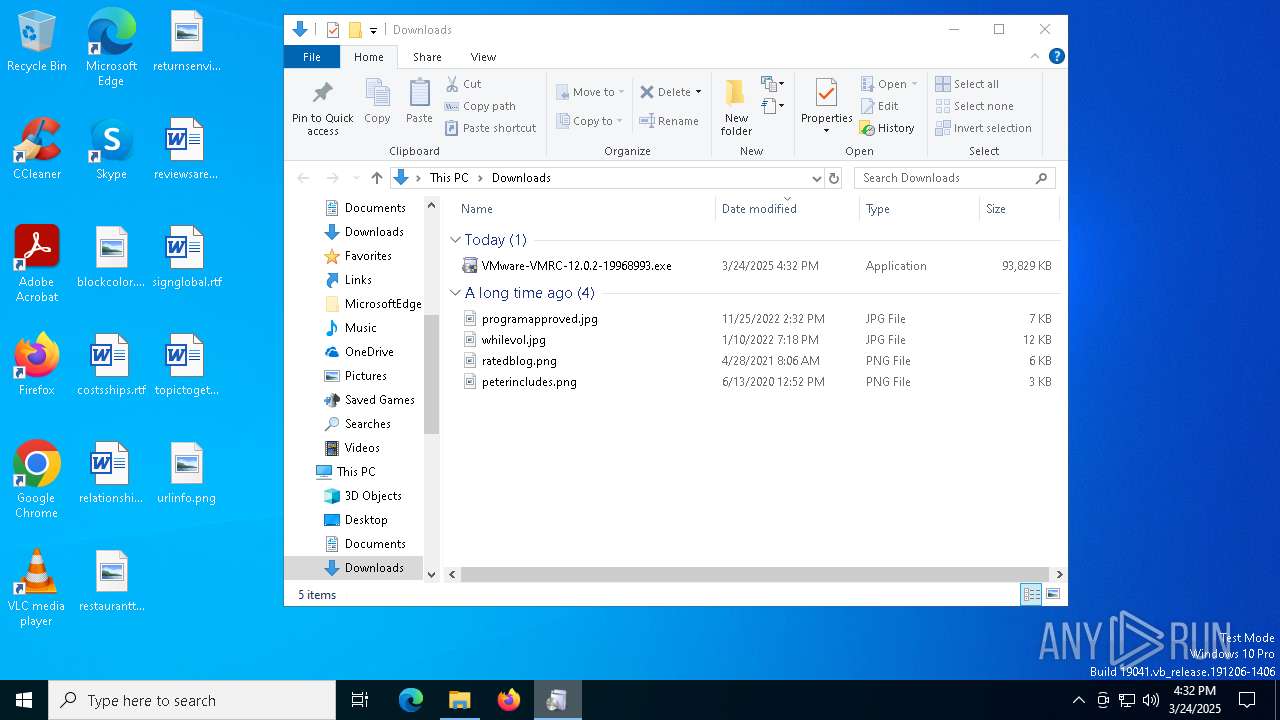
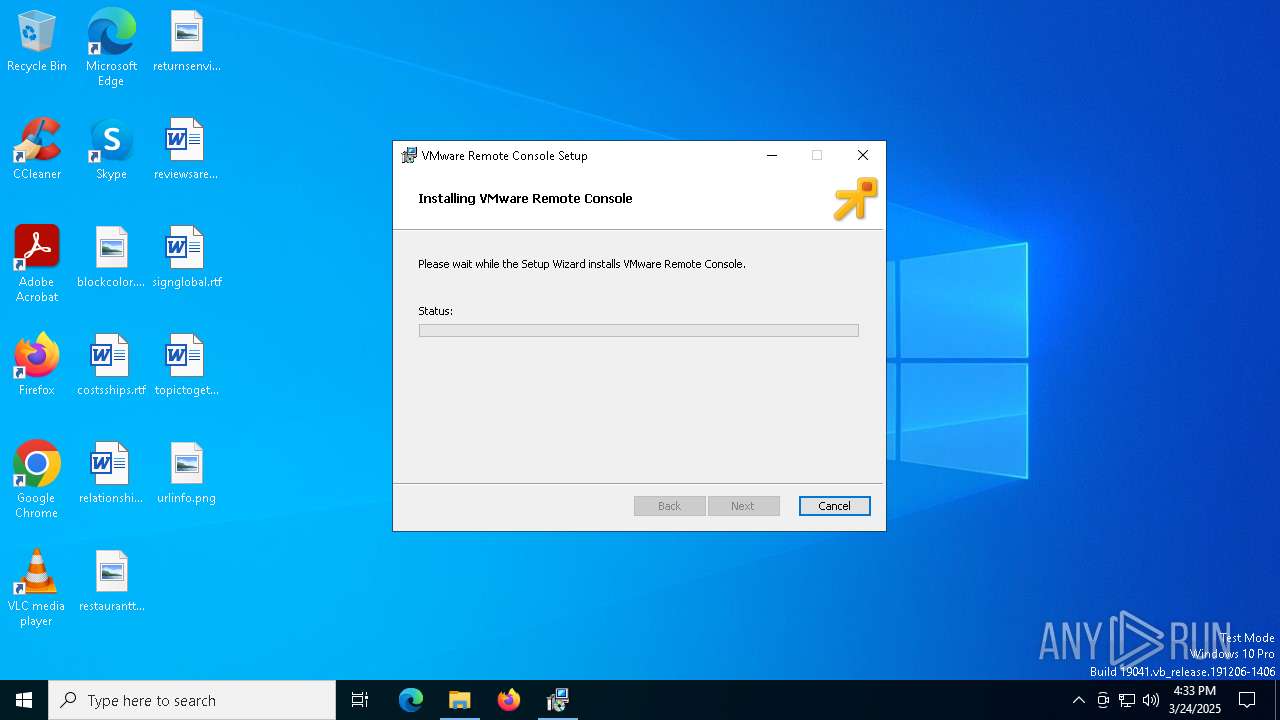
| URL: | https://archive.org/download/vmware-vmrc-12.0.2/VMware-VMRC-12.0.2-19968993.zip/VMware-VMRC-12.0.2-19968993.exe |
| Full analysis: | https://app.any.run/tasks/9e68cc69-6e50-4bf8-bc88-8175aa3191cf |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 16:29:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 07069EAD1593508A1269E2D1E1C899EC |
| SHA1: | 59B4BE9BC165B9B3E162A1C0835B683D2145CC54 |
| SHA256: | 2399F788A054E832E74C7F3FAE35005271DEF18689976FE48CAE44954C519AE1 |
| SSDEEP: | 3:N8MFXJ2AXhqGVKAxqiXIF+tMf/eqiXIF+tMAdA:2MFXP9VKWXIme6XImrA |
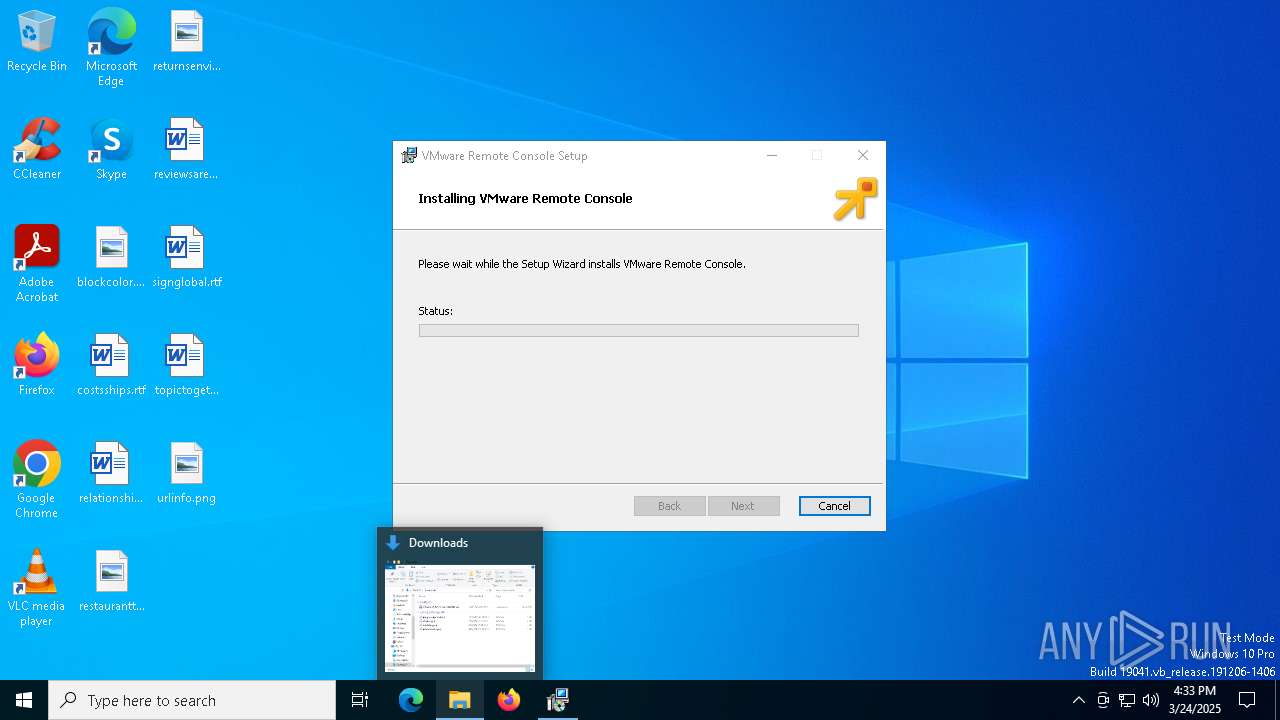
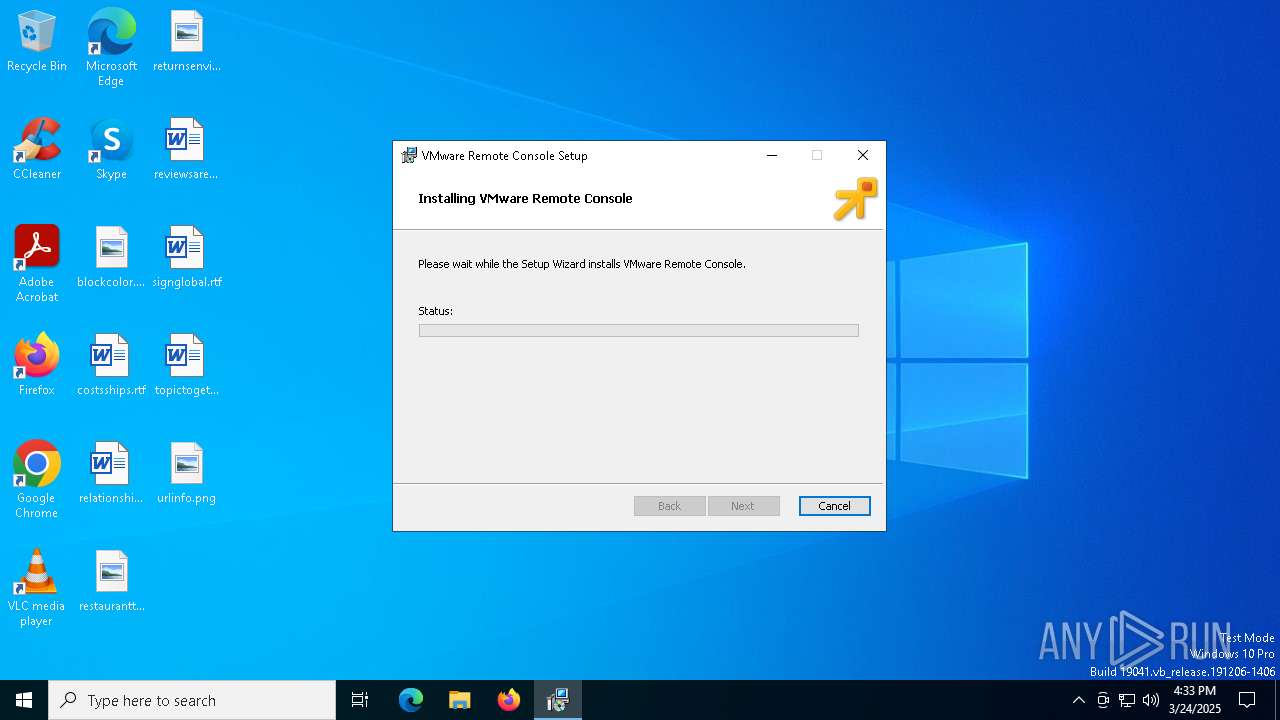
MALICIOUS
Reads a specific registry key of the VM
- msiexec.exe (PID: 1628)
- vnetlib64.exe (PID: 7568)
- vnetlib64.exe (PID: 8716)
- msiexec.exe (PID: 7776)
- msiexec.exe (PID: 3956)
SUSPICIOUS
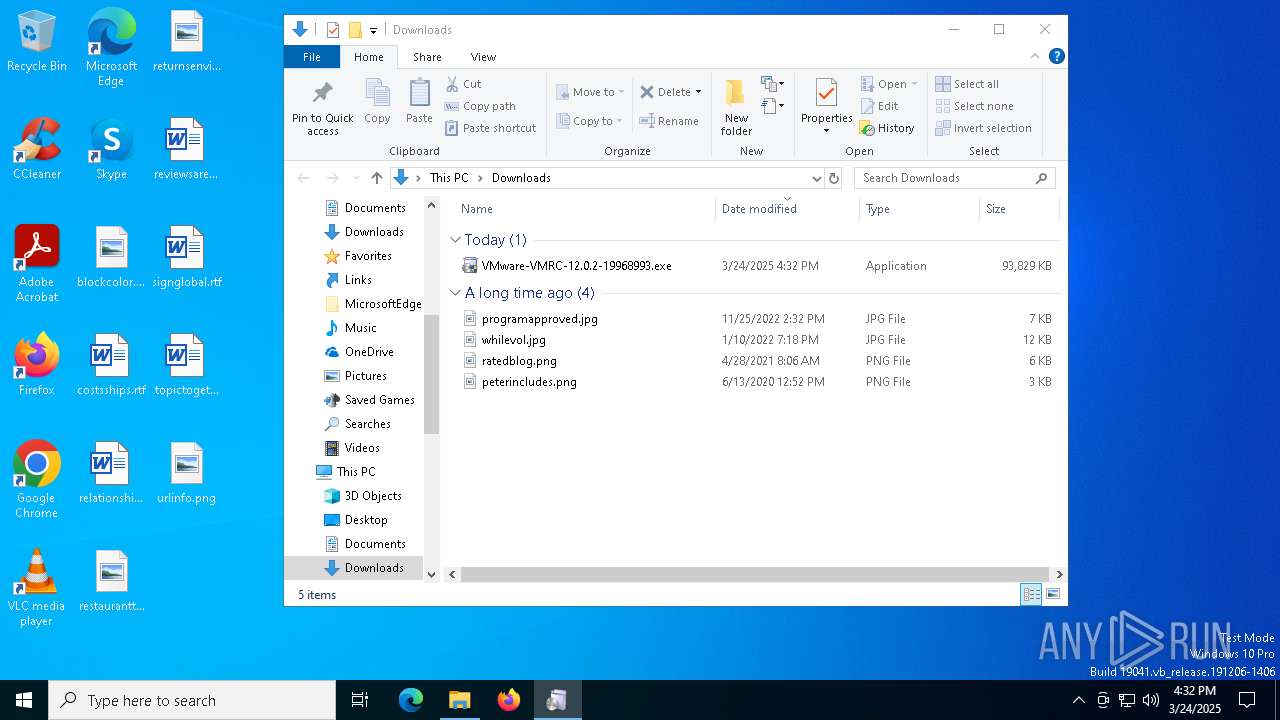
Executable content was dropped or overwritten
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- vcredist_x64.exe (PID: 4040)
- vcredist_x64.exe (PID: 672)
- drvinst.exe (PID: 7532)
- vnetlib64.exe (PID: 8716)
Process drops legitimate windows executable
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- vcredist_x64.exe (PID: 672)
- msiexec.exe (PID: 1628)
Searches for installed software
- vcredist_x64.exe (PID: 4040)
Starts a Microsoft application from unusual location
- vcredist_x64.exe (PID: 672)
- vcredist_x64.exe (PID: 4040)
Reads security settings of Internet Explorer
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- ShellExperienceHost.exe (PID: 8000)
Executes as Windows Service
- VSSVC.exe (PID: 7652)
- vmware-usbarbitrator64.exe (PID: 9120)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1628)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 1628)
- drvinst.exe (PID: 7532)
- vnetlib64.exe (PID: 8716)
The process drops C-runtime libraries
- msiexec.exe (PID: 1628)
Creates files in the driver directory
- drvinst.exe (PID: 7532)
Adds/modifies Windows certificates
- vnetlib64.exe (PID: 8716)
Creates or modifies Windows services
- vnetlib64.exe (PID: 8716)
INFO
Checks supported languages
- identity_helper.exe (PID: 1052)
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- vcredist_x64.exe (PID: 4040)
- vcredist_x64.exe (PID: 672)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 3956)
- identity_helper.exe (PID: 7936)
- ShellExperienceHost.exe (PID: 8000)
- drvinst.exe (PID: 7532)
- msiexec.exe (PID: 7776)
- vnetlib64.exe (PID: 7568)
- vnetlib64.exe (PID: 8716)
Executable content was dropped or overwritten
- msedge.exe (PID: 6272)
- msedge.exe (PID: 7940)
- msiexec.exe (PID: 1628)
Reads the computer name
- identity_helper.exe (PID: 1052)
- identity_helper.exe (PID: 7936)
- msiexec.exe (PID: 7776)
- vnetlib64.exe (PID: 7568)
- vnetlib64.exe (PID: 6456)
- drvinst.exe (PID: 7532)
- vnetlib64.exe (PID: 8716)
- vmware-usbarbitrator64.exe (PID: 9120)
Reads Environment values
- identity_helper.exe (PID: 1052)
- identity_helper.exe (PID: 7936)
The sample compiled with english language support
- msedge.exe (PID: 7940)
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- vcredist_x64.exe (PID: 4040)
- vcredist_x64.exe (PID: 672)
- msiexec.exe (PID: 1628)
- drvinst.exe (PID: 7532)
- vnetlib64.exe (PID: 8716)
Reads the software policy settings
- slui.exe (PID: 1188)
- slui.exe (PID: 9132)
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- drvinst.exe (PID: 7532)
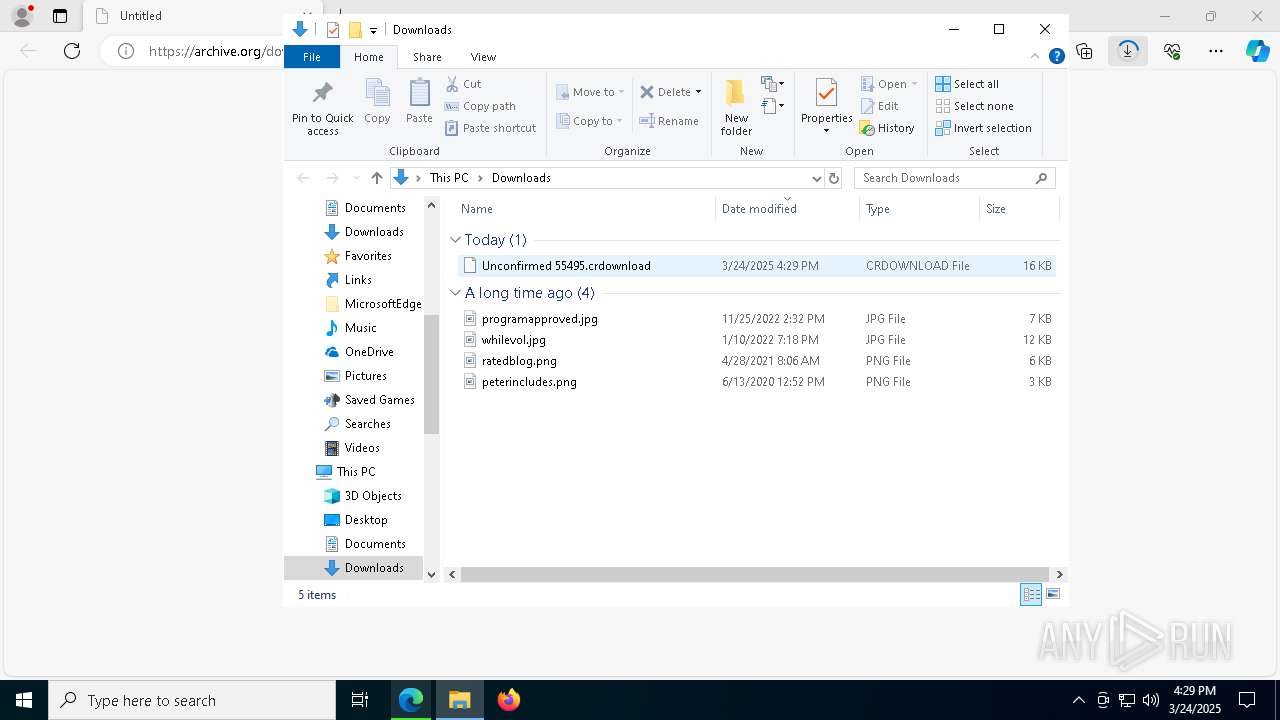
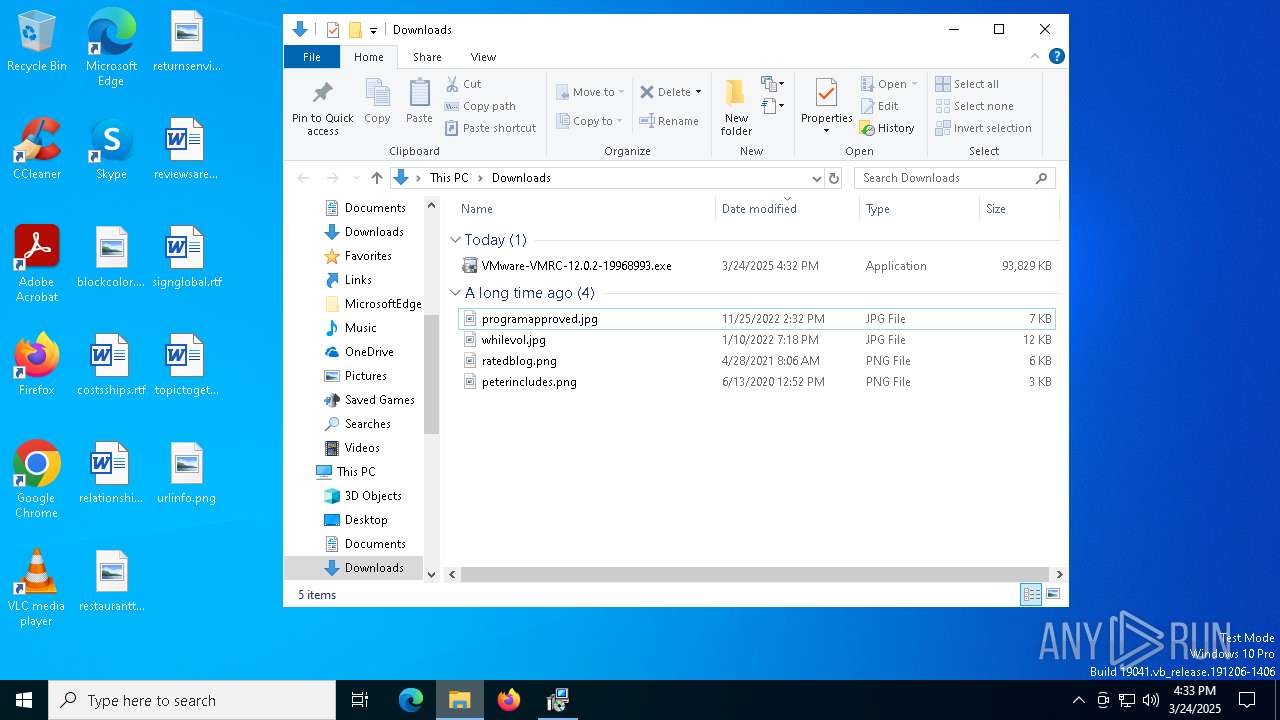
Autorun file from Downloads
- msedge.exe (PID: 1748)
Create files in a temporary directory
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- vcredist_x64.exe (PID: 4040)
Application launched itself
- msedge.exe (PID: 5776)
- msedge.exe (PID: 6272)
Reads the machine GUID from the registry
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
- drvinst.exe (PID: 7532)
- vnetlib64.exe (PID: 8716)
Manages system restore points
- SrTasks.exe (PID: 2332)
Checks proxy server information
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
Creates files or folders in the user directory
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
Creates files in the program directory
- VMware-VMRC-12.0.2-19968993.exe (PID: 1600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
243
Monitored processes
95
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Users\admin\AppData\Local\Temp\{BB5D80D4-AC3C-4B81-8F2C-1B24E29C7179}~setup\vcredist_x64.exe" /Q /norestart | C:\Users\admin\AppData\Local\Temp\{BB5D80D4-AC3C-4B81-8F2C-1B24E29C7179}~setup\vcredist_x64.exe | VMware-VMRC-12.0.2-19968993.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.27.29016 Exit code: 1638 Version: 14.27.29016.0 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6564 --field-trial-handle=2268,i,16654386910525974103,23492605488385533,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6564 --field-trial-handle=2268,i,16654386910525974103,23492605488385533,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1188 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5812 --field-trial-handle=2268,i,16654386910525974103,23492605488385533,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
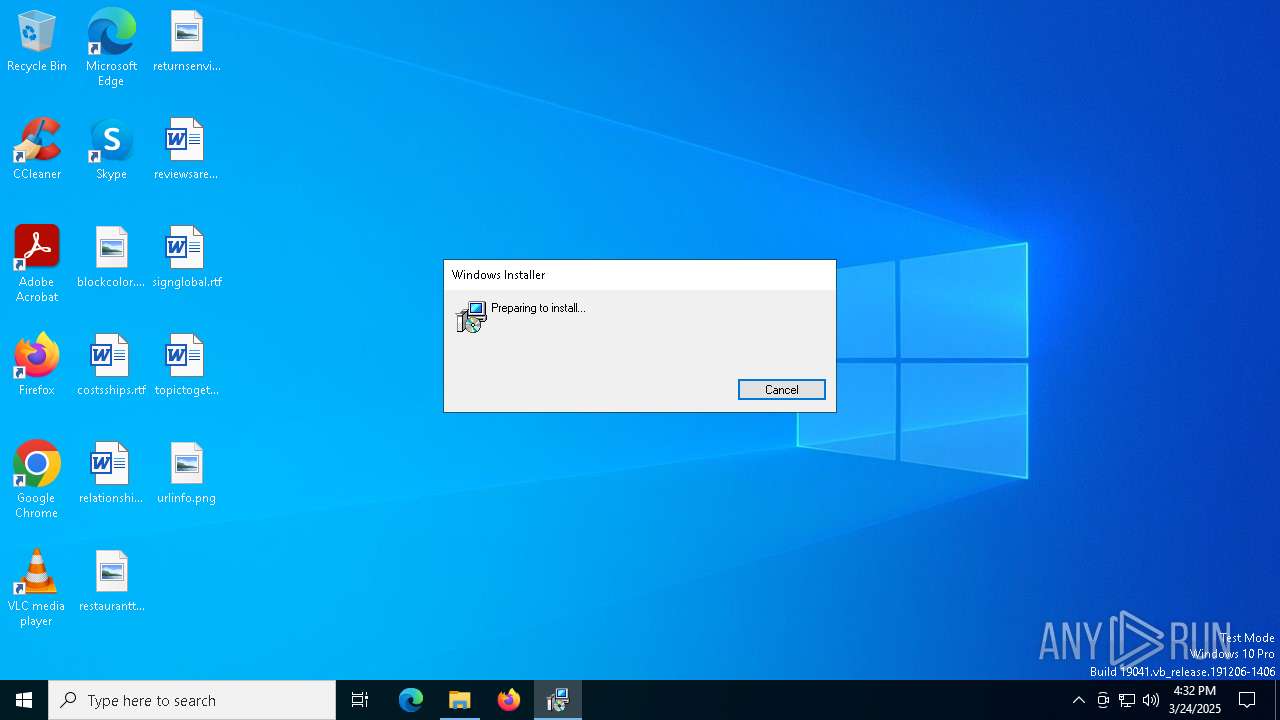
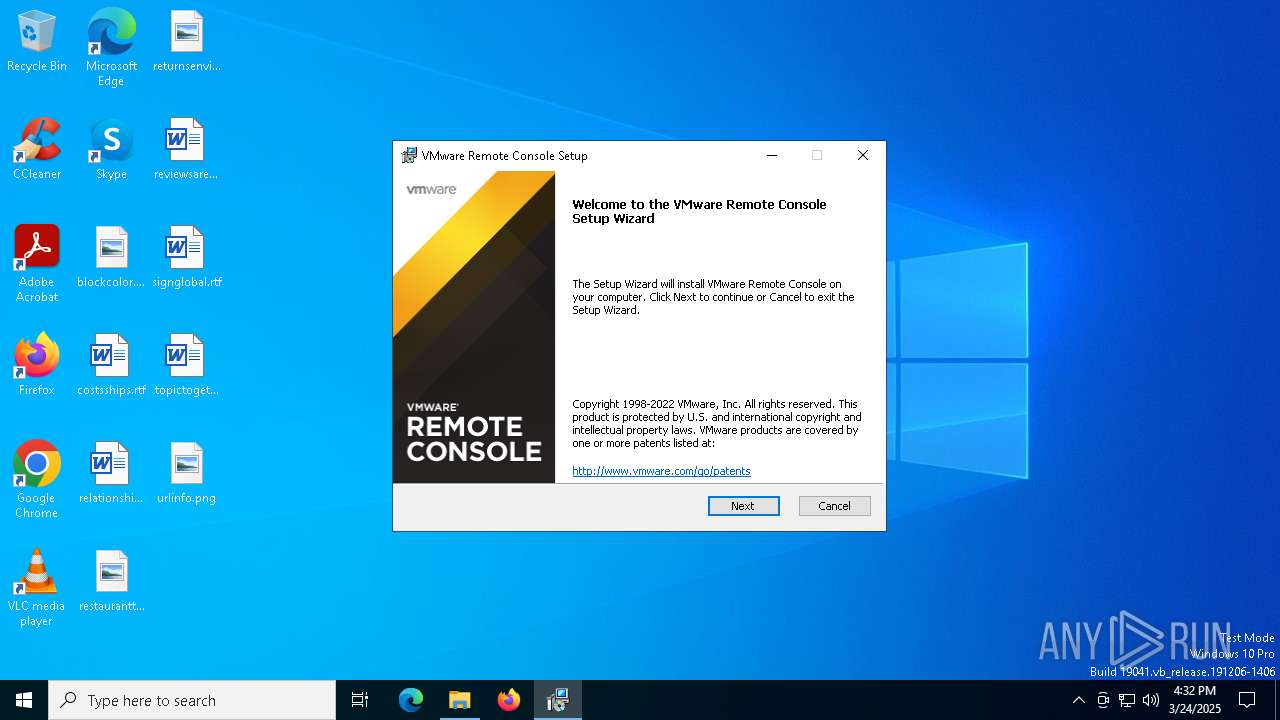
| 1324 | "C:\Users\admin\Downloads\VMware-VMRC-12.0.2-19968993.exe" | C:\Users\admin\Downloads\VMware-VMRC-12.0.2-19968993.exe | — | msedge.exe | |||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware installation launcher Exit code: 3221226540 Version: 12.0.2 Modules
| |||||||||||||||
| 1600 | "C:\Users\admin\Downloads\VMware-VMRC-12.0.2-19968993.exe" | C:\Users\admin\Downloads\VMware-VMRC-12.0.2-19968993.exe | msedge.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: HIGH Description: VMware installation launcher Exit code: 0 Version: 12.0.2 Modules
| |||||||||||||||
| 1628 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5152 --field-trial-handle=2268,i,16654386910525974103,23492605488385533,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5976 --field-trial-handle=2268,i,16654386910525974103,23492605488385533,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
25 660
Read events
25 134
Write events
510
Delete events
16
Modification events
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FFB38063AF8F2F00 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1BFCA363AF8F2F00 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {256E1808-A974-4ED3-AF82-614AF75177C4} | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262916 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A9E67890-4DDE-4C0F-9F6D-20026A8F1864} | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7DC1D763AF8F2F00 | |||
| (PID) Process: | (6272) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
137
Suspicious files
994
Text files
255
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bd95.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bd95.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bda5.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bdb4.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bdb4.TMP | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6272 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
116
DNS requests
127
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | svchost.exe | HEAD | 200 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1743009283&P2=404&P3=2&P4=nNNppVAcdOmFIYHGgv2wNcFzUSjkruDp%2fuDmTpfaGsBjyFq877u%2fpurmC90X%2fR9dIPyA5jHA%2fFZkF40UBUS5bw%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7968 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7748 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1743009283&P2=404&P3=2&P4=nNNppVAcdOmFIYHGgv2wNcFzUSjkruDp%2fuDmTpfaGsBjyFq877u%2fpurmC90X%2fR9dIPyA5jHA%2fFZkF40UBUS5bw%3d%3d | unknown | — | — | whitelisted |
7748 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1743009283&P2=404&P3=2&P4=nNNppVAcdOmFIYHGgv2wNcFzUSjkruDp%2fuDmTpfaGsBjyFq877u%2fpurmC90X%2fR9dIPyA5jHA%2fFZkF40UBUS5bw%3d%3d | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1743009283&P2=404&P3=2&P4=nNNppVAcdOmFIYHGgv2wNcFzUSjkruDp%2fuDmTpfaGsBjyFq877u%2fpurmC90X%2fR9dIPyA5jHA%2fFZkF40UBUS5bw%3d%3d | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1743009283&P2=404&P3=2&P4=nNNppVAcdOmFIYHGgv2wNcFzUSjkruDp%2fuDmTpfaGsBjyFq877u%2fpurmC90X%2fR9dIPyA5jHA%2fFZkF40UBUS5bw%3d%3d | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 206 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1743009283&P2=404&P3=2&P4=nNNppVAcdOmFIYHGgv2wNcFzUSjkruDp%2fuDmTpfaGsBjyFq877u%2fpurmC90X%2fR9dIPyA5jHA%2fFZkF40UBUS5bw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6272 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7232 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 207.241.224.2:443 | archive.org | INTERNET-ARCHIVE | US | whitelisted |
7232 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
archive.org |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
ia601701.us.archive.org |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vmware-usbarbitrator64.exe | CodeSet_Init: no ICU
|