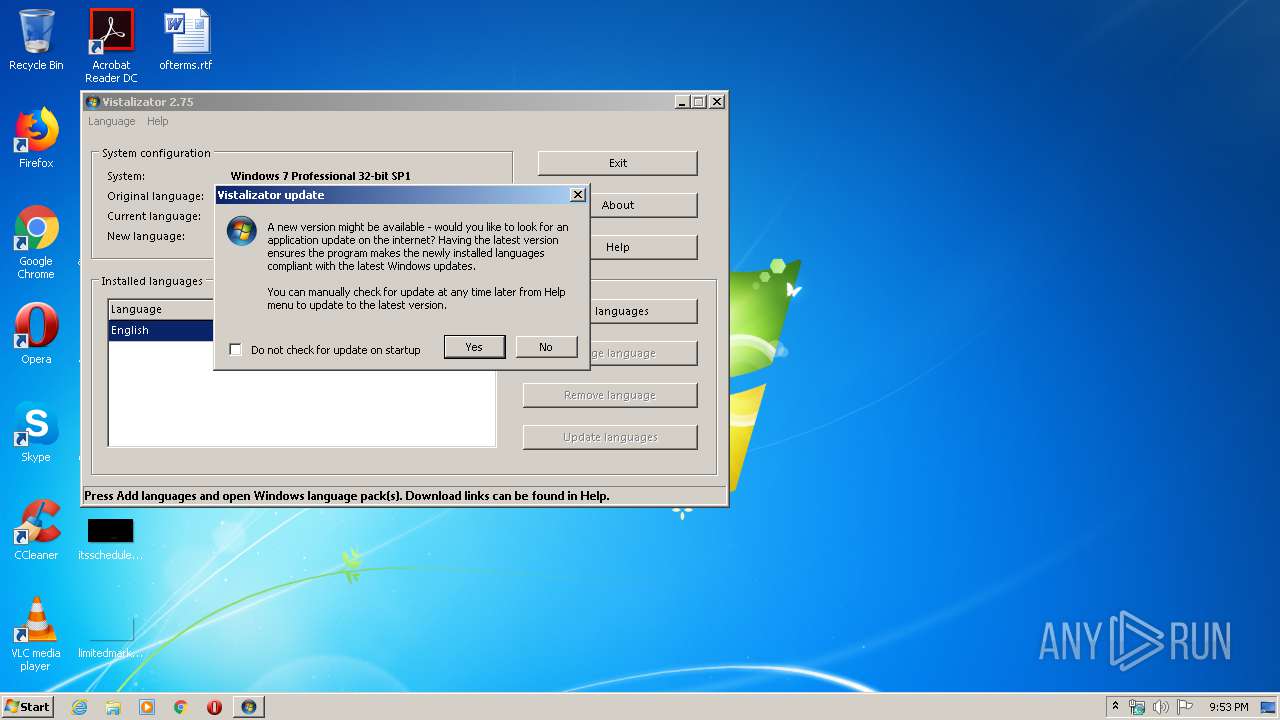
| File name: | Vistalizator.exe |
| Full analysis: | https://app.any.run/tasks/1e594c33-371d-4359-9419-47e73fec4fa1 |
| Verdict: | No threats detected |
| Analysis date: | May 24, 2020, 20:53:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, InstallShield self-extracting archive |
| MD5: | AE423F631CE0D0167109AF2416E3E69F |
| SHA1: | CFF58B4054E784B8F1F7F93142EE7BEFF0EE2214 |
| SHA256: | 23956112BF319A1E357B2B451D62C30E1B41DD3861AF3E1340A404562736ECC7 |
| SSDEEP: | 24576:siqEJ7W1/3L3xmBm6ko9epyn7GJzxDSJX22RAGeM+Tt5mJiAas:1kT3Mmfo9epyaJz9SYoMlAas |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Vistalizator.exe (PID: 1928)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (40.1) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (25.2) |
| .exe | | | Win32 EXE Yoda's Crypter (24.7) |
| .exe | | | Win32 Executable (generic) (4.2) |
| .exe | | | Win16/32 Executable Delphi generic (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:25 14:18:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 700416 |
| InitializedDataSize: | 110592 |
| UninitializedDataSize: | 4227072 |
| EntryPoint: | 0x4b36b0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.5.0 |
| ProductVersionNumber: | 2.7.5.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | www.froggie.sk |
| FileDescription: | Language Pack Installer for Vista and Windows 7 |
| FileVersion: | 2.7.5.0 |
| InternalName: | Vistalizator.exe |
| LegalCopyright: | (c) froggie 2008-2016 (www.froggie.sk) |
| LegalTrademarks: | - |
| OriginalFileName: | Vistalizator.exe |
| ProductName: | Vistalizator |
| ProductVersion: | 2.75 |
| Comments: | vistalizator@gmail.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Mar-2016 13:18:33 |
| Detected languages: |
|
| CompanyName: | www.froggie.sk |
| FileDescription: | Language Pack Installer for Vista and Windows 7 |
| FileVersion: | 2.7.5.0 |
| InternalName: | Vistalizator.exe |
| LegalCopyright: | (c) froggie 2008-2016 (www.froggie.sk) |
| LegalTrademarks: | - |
| OriginalFilename: | Vistalizator.exe |
| ProductName: | Vistalizator |
| ProductVersion: | 2.75 |
| Comments: | vistalizator@gmail.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Mar-2016 13:18:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00408000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00409000 | 0x000AB000 | 0x000AAA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92314 |
.rsrc | 0x004B4000 | 0x0001B000 | 0x0001AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.08589 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29158 | 1578 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.86466 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 3.88248 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 6.01839 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 6.31558 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 4.84341 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 7.97195 | 59667 | UNKNOWN | English - United States | RT_ICON |
8 | 6.11788 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 6.13948 | 4264 | UNKNOWN | English - United States | RT_ICON |
10 | 6.14829 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
mpr.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
Total processes
43
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1928 | "C:\Users\admin\AppData\Local\Temp\Vistalizator.exe" | C:\Users\admin\AppData\Local\Temp\Vistalizator.exe | explorer.exe | ||||||||||||
User: admin Company: www.froggie.sk Integrity Level: HIGH Description: Language Pack Installer for Vista and Windows 7 Exit code: 0 Version: 2.7.5.0 Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\AppData\Local\Temp\Vistalizator.exe" | C:\Users\admin\AppData\Local\Temp\Vistalizator.exe | — | explorer.exe | |||||||||||
User: admin Company: www.froggie.sk Integrity Level: MEDIUM Description: Language Pack Installer for Vista and Windows 7 Exit code: 3221226540 Version: 2.7.5.0 Modules
| |||||||||||||||
Total events
10
Read events
6
Write events
4
Delete events
0
Modification events
| (PID) Process: | (1928) Vistalizator.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Nls\Language |
| Operation: | write | Name: | DefaultLanguage |
Value: 0409 | |||
| (PID) Process: | (1928) Vistalizator.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\UILanguages\en-US |
| Operation: | write | Name: | Version |
Value: 1 | |||
| (PID) Process: | (1928) Vistalizator.exe | Key: | HKEY_CURRENT_USER\Software\Froggie\Vistalizator |
| Operation: | write | Name: | GUILanguage |
Value: english | |||
| (PID) Process: | (1928) Vistalizator.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\UILanguages\en-US |
| Operation: | write | Name: | Mode |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\languages.cab | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\Arabic.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\Armenian.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\ChineseSim.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\ChineseTra.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\Czech.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\Danish.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\English.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\French.lang | — | |
MD5:— | SHA256:— | |||
| 1928 | Vistalizator.exe | C:\Users\admin\AppData\Local\Temp\Vistalizator\Languages\German.lang | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report