| File name: | Autoit3.exe |
| Full analysis: | https://app.any.run/tasks/bc9578e7-da64-4823-b6c8-b60bdceff8b8 |
| Verdict: | Malicious activity |
| Threats: | DarkGate is a loader, which possesses extensive functionality, ranging from keylogging to crypto mining. Written in Delphi, this malware is known for the use of AutoIT scripts in its infection process. Thanks to this malicious software’s versatile architecture, it is widely used by established threat actors. |
| Analysis date: | November 06, 2024, 01:54:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | C56B5F0201A3B3DE53E561FE76912BFD |
| SHA1: | 2A4062E10A5DE813F5688221DBEB3F3FF33EB417 |
| SHA256: | 237D1BCA6E056DF5BB16A1216A434634109478F882D3B1D58344C801D184F95D |
| SSDEEP: | 12288:6pVWeOV7GtINsegA/hMyyzlcqikvAfcN9b2MyZa31twoPTdFxgawV2M01:6T3E53Myyzl0hMf1tr7Caw8M01 |
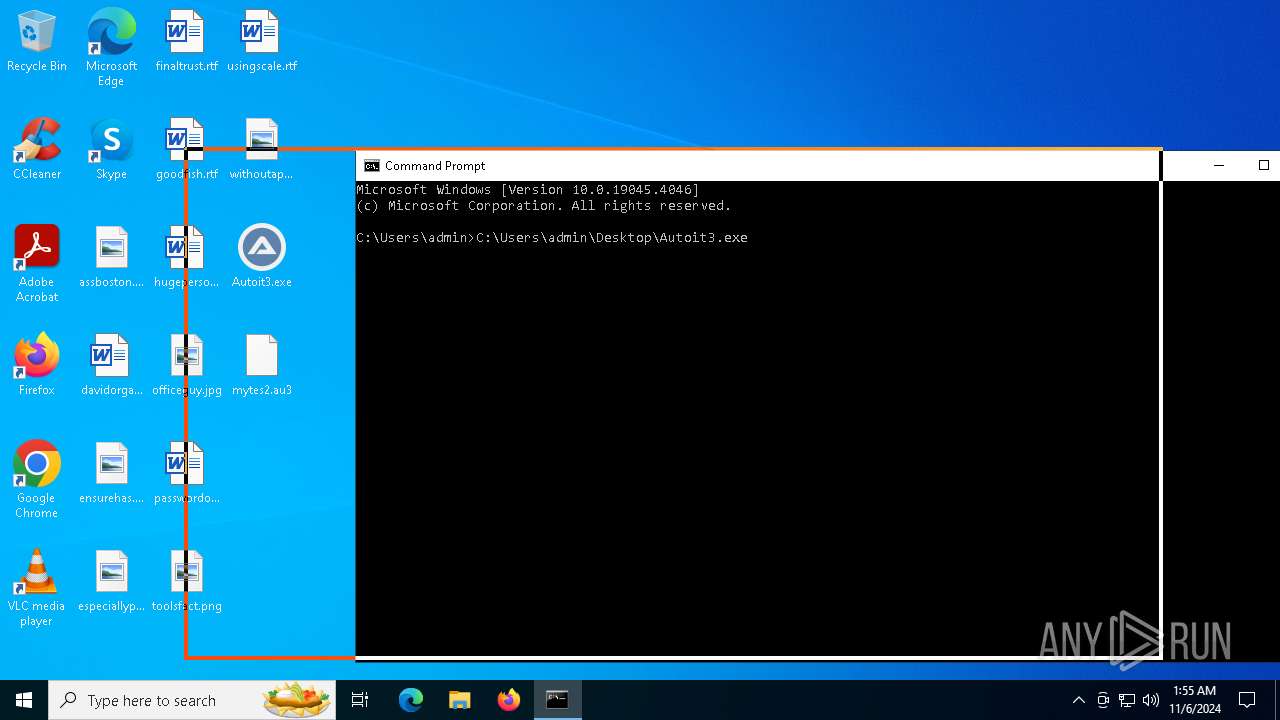
MALICIOUS
Runs injected code in another process
- Autoit3.exe (PID: 2928)
Application was injected by another process
- MicrosoftEdgeUpdateCore.exe (PID: 7060)
DARKGATE has been detected (YARA)
- MicrosoftEdgeUpdateCore.exe (PID: 5516)
- MicrosoftEdgeUpdateCore.exe (PID: 3568)
SUSPICIOUS
Reads security settings of Internet Explorer
- Autoit3.exe (PID: 3276)
- Autoit3.exe (PID: 1576)
Detected use of alternative data streams (AltDS)
- Autoit3.exe (PID: 1332)
- Autoit3.exe (PID: 6148)
- Autoit3.exe (PID: 5168)
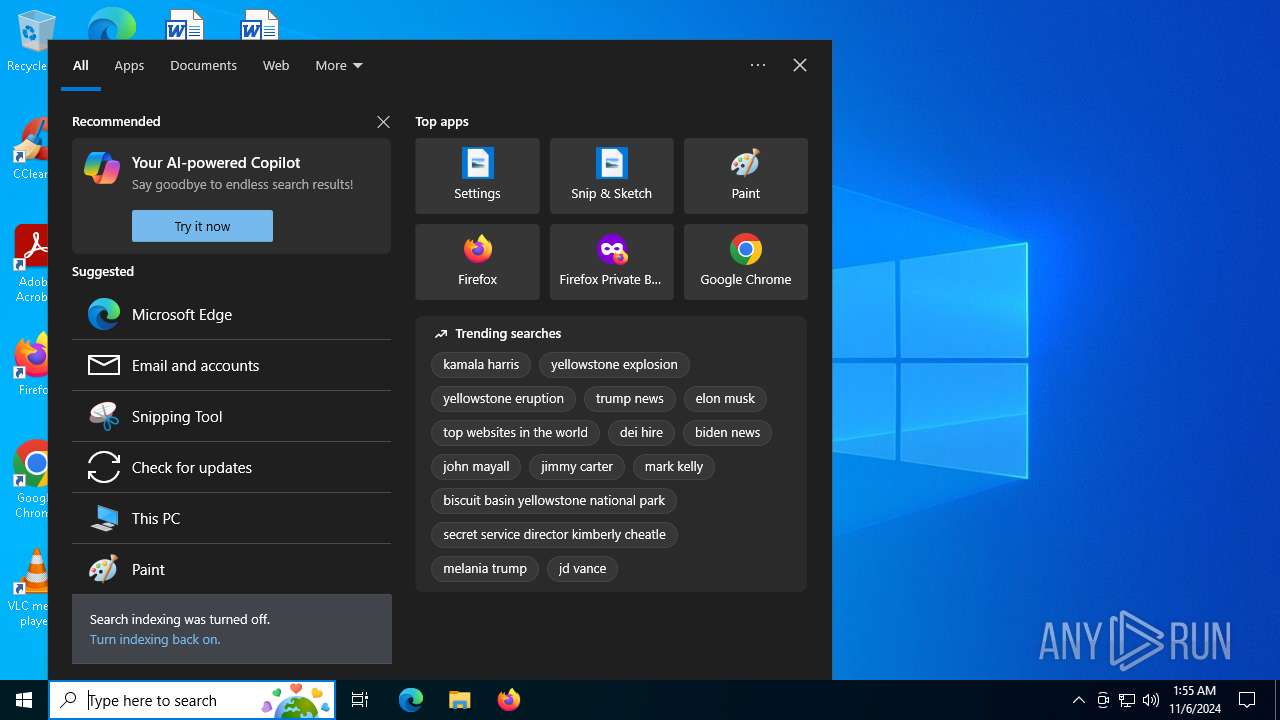
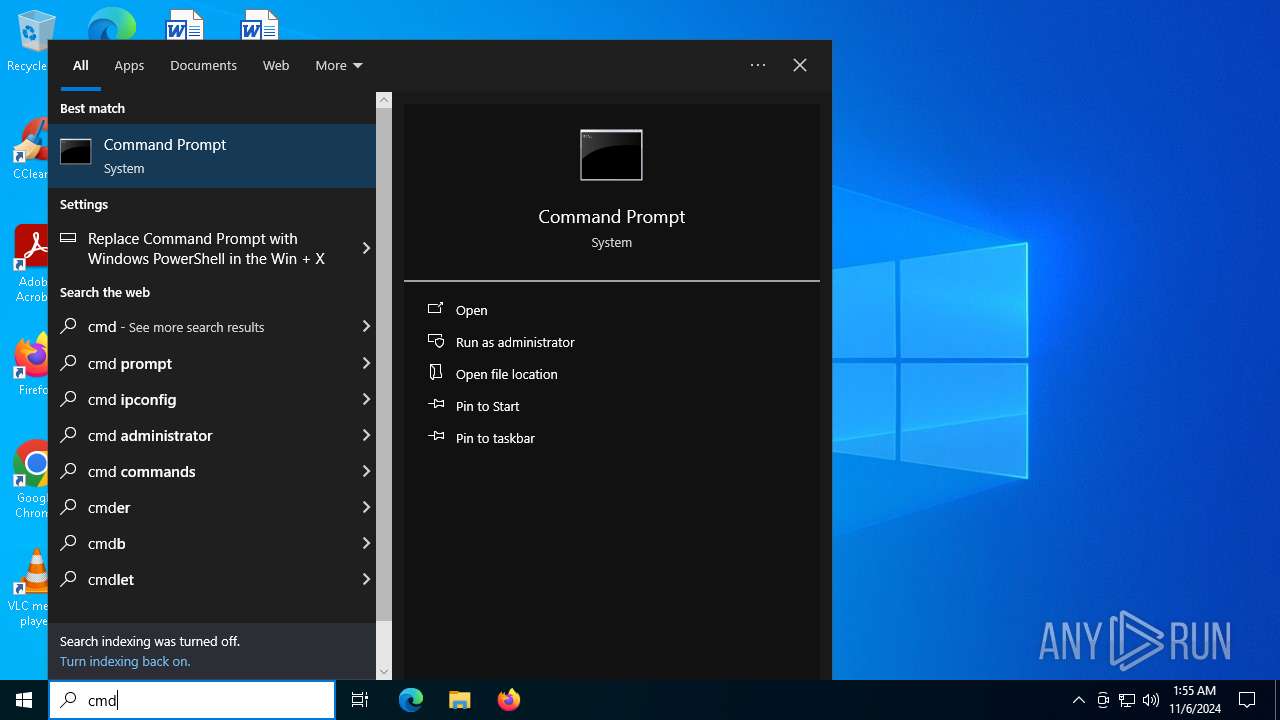
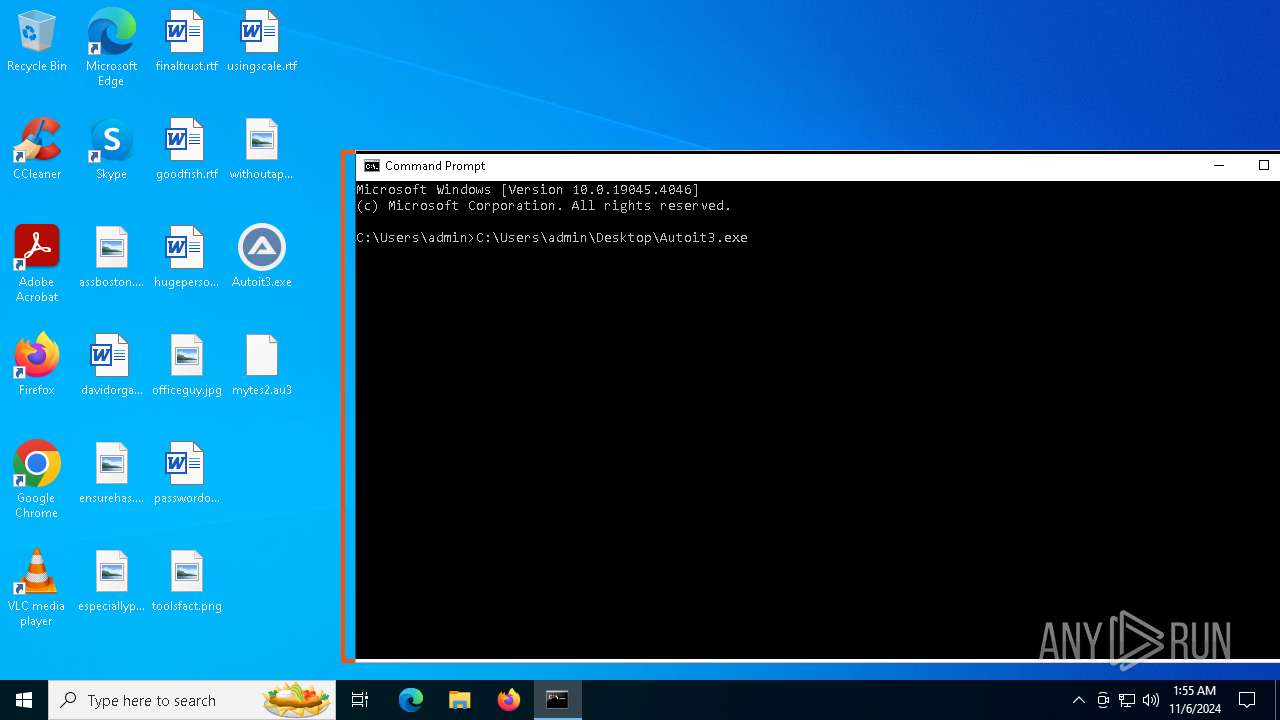
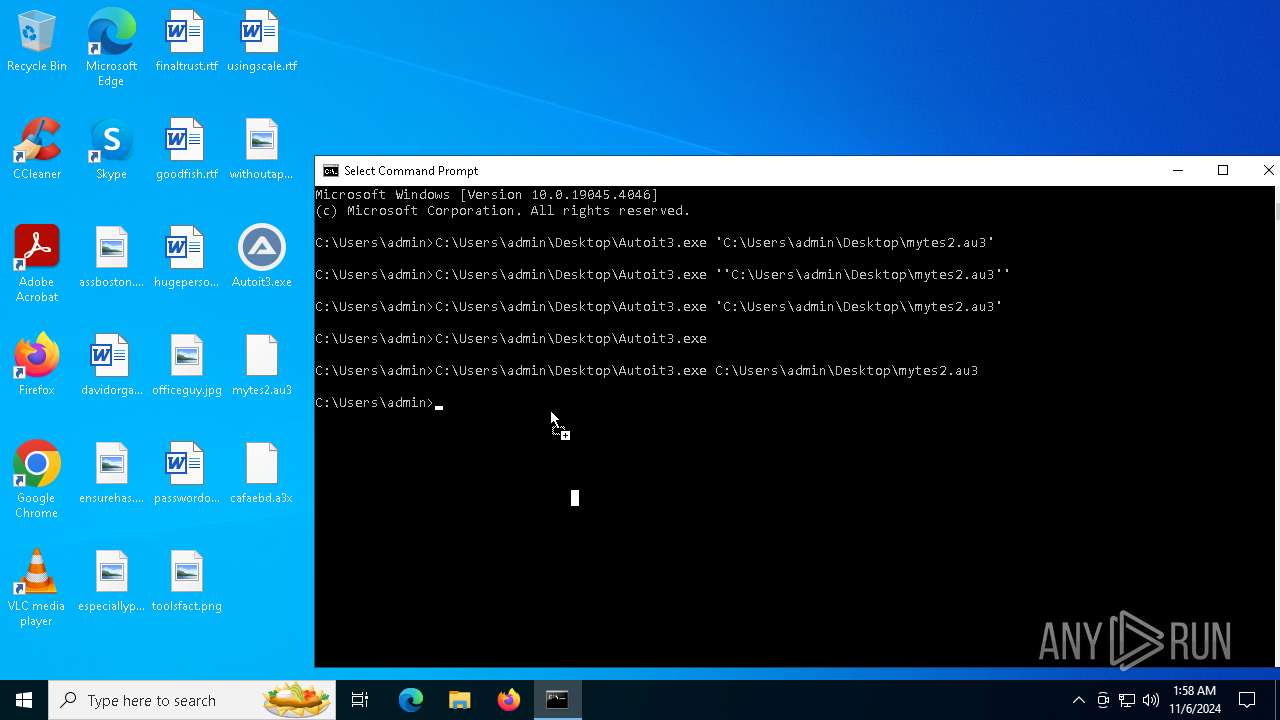
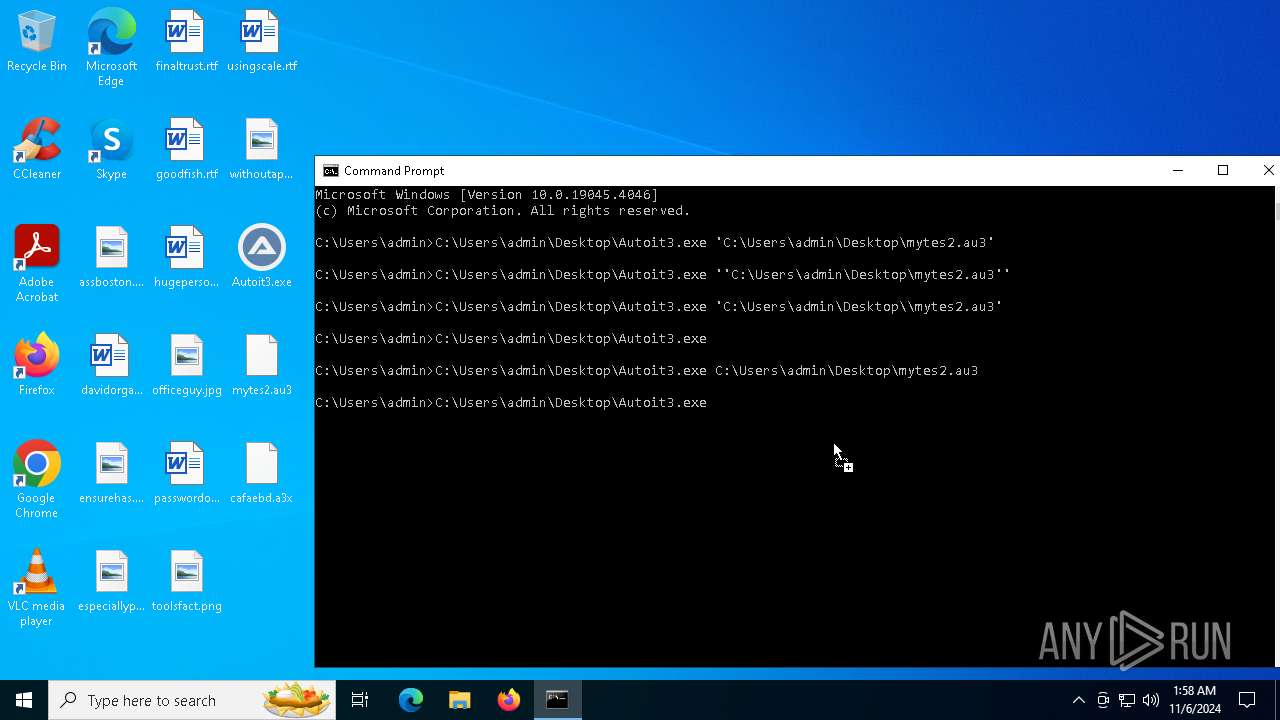
Starts CMD.EXE for commands execution
- Autoit3.exe (PID: 2928)
The process verifies whether the antivirus software is installed
- Autoit3.exe (PID: 2928)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6132)
Accesses domain name via WMI (SCRIPT)
- WMIC.exe (PID: 4692)
Executable content was dropped or overwritten
- Autoit3.exe (PID: 2928)
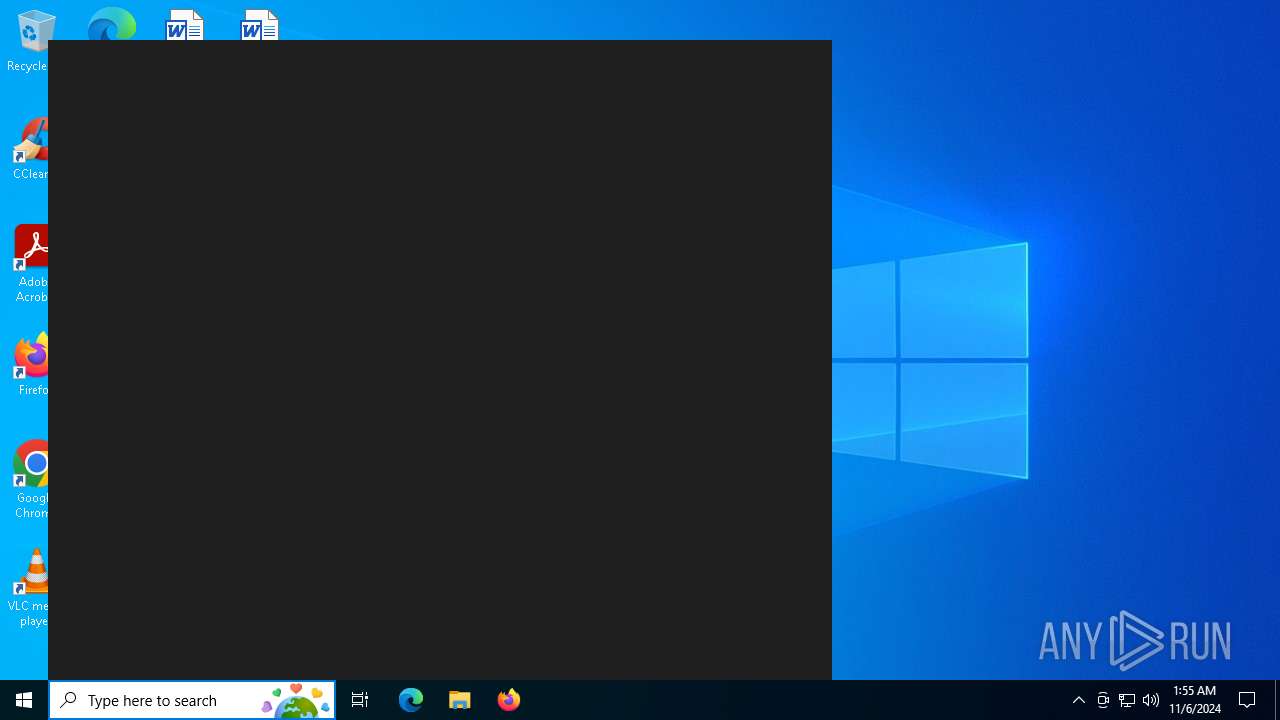
Executes application which crashes
- MicrosoftEdgeUpdateCore.exe (PID: 7060)
INFO
Reads mouse settings
- Autoit3.exe (PID: 3276)
- Autoit3.exe (PID: 1576)
- Autoit3.exe (PID: 1332)
- Autoit3.exe (PID: 6148)
- Autoit3.exe (PID: 2928)
- Autoit3.exe (PID: 5168)
Reads the computer name
- Autoit3.exe (PID: 5168)
- Autoit3.exe (PID: 3276)
- Autoit3.exe (PID: 1332)
- Autoit3.exe (PID: 1576)
- Autoit3.exe (PID: 2928)
- Autoit3.exe (PID: 6148)
Checks supported languages
- Autoit3.exe (PID: 3276)
- Autoit3.exe (PID: 1332)
- Autoit3.exe (PID: 6148)
- Autoit3.exe (PID: 1576)
- Autoit3.exe (PID: 2928)
- MicrosoftEdgeUpdateCore.exe (PID: 7060)
- Autoit3.exe (PID: 5168)
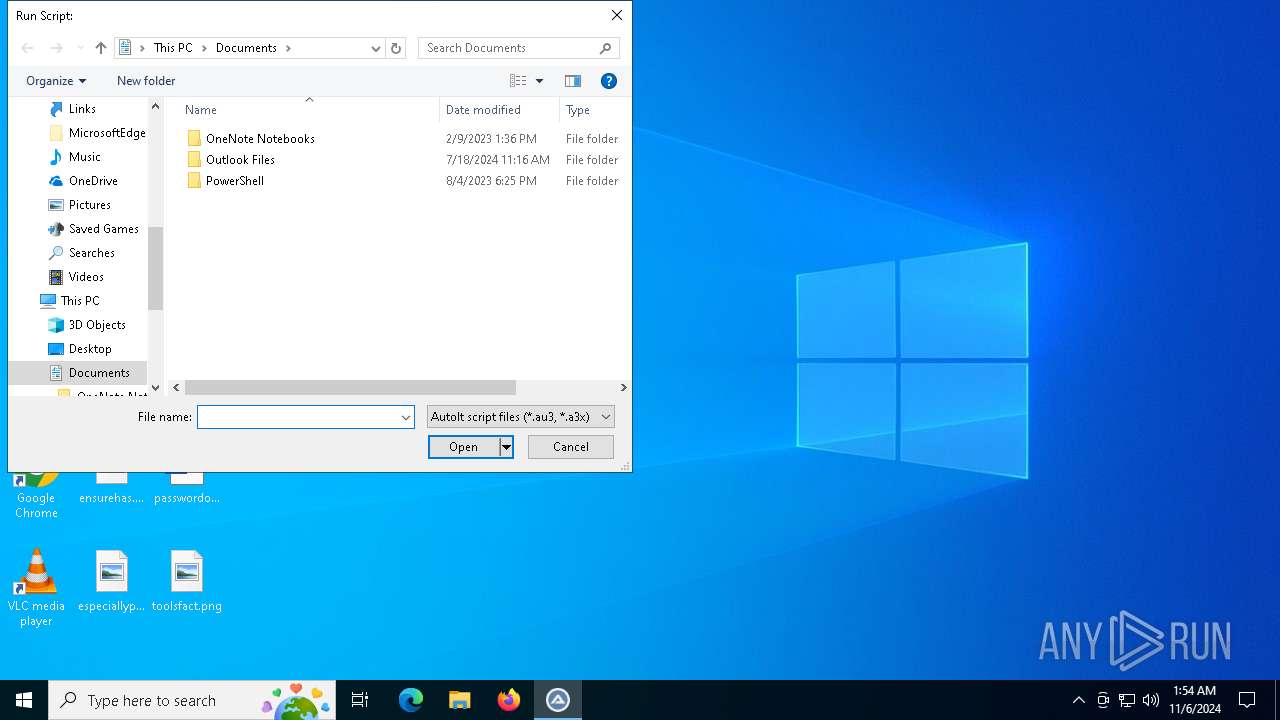
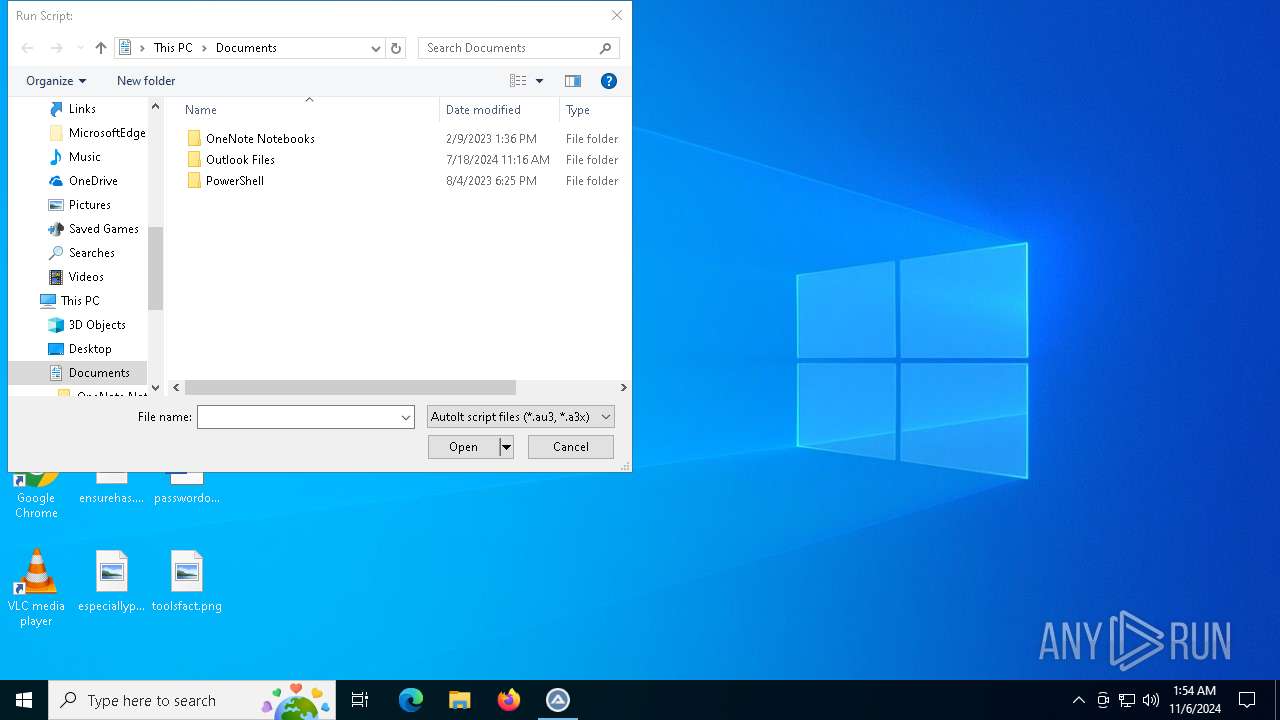
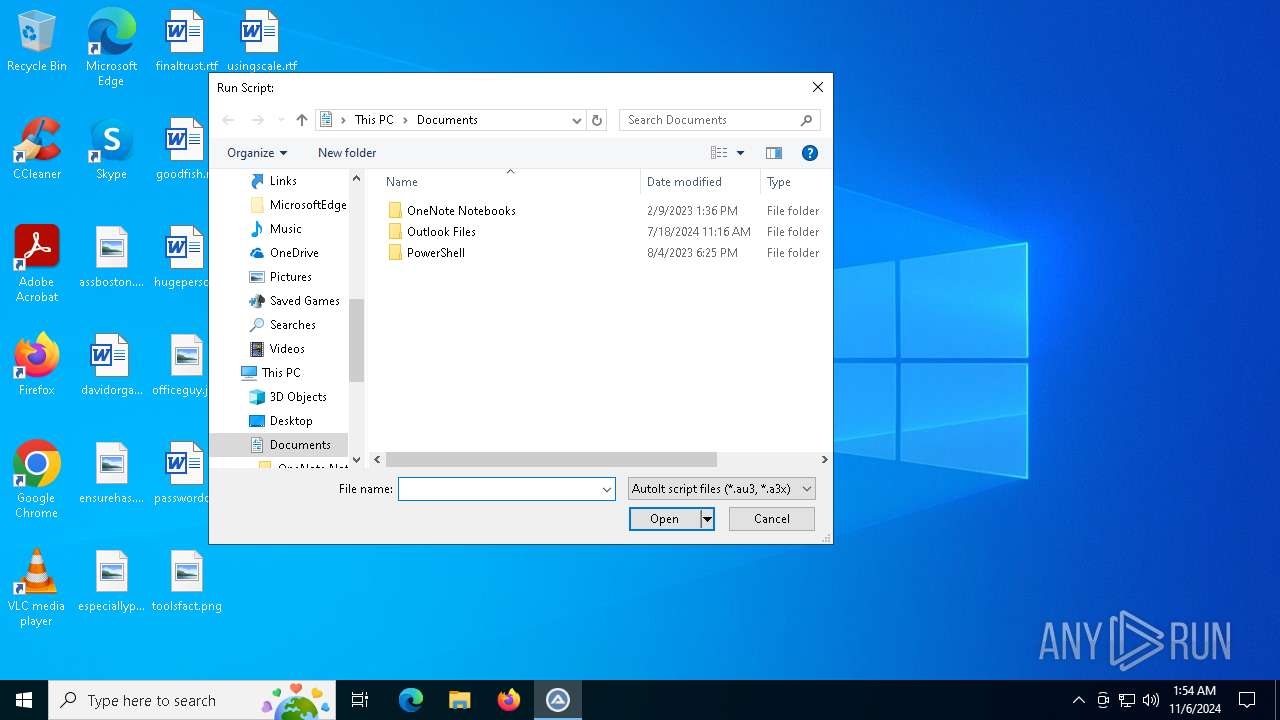
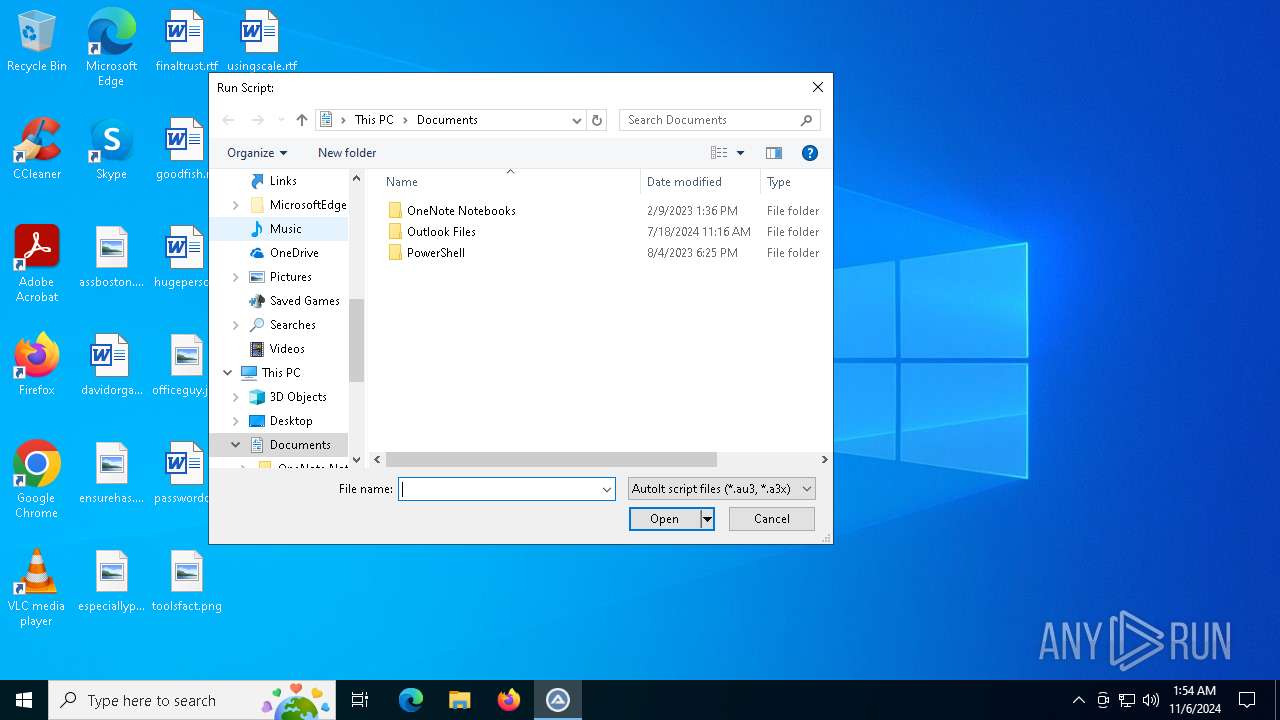
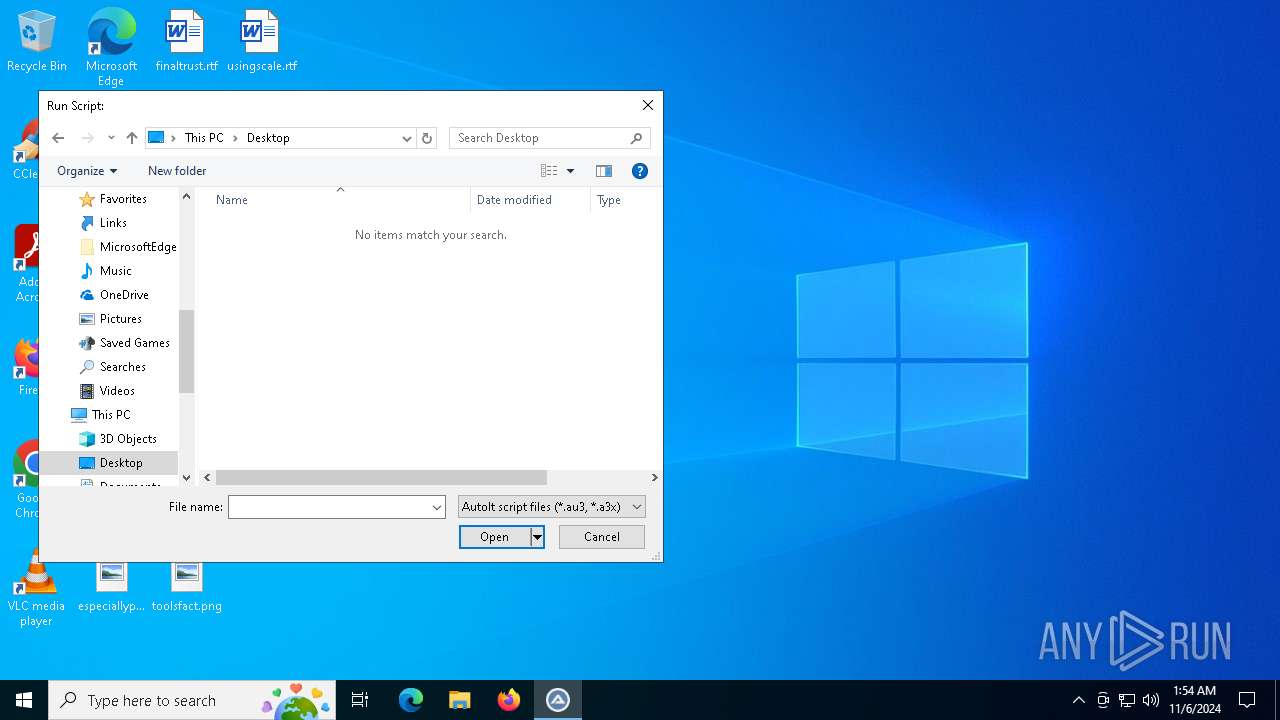
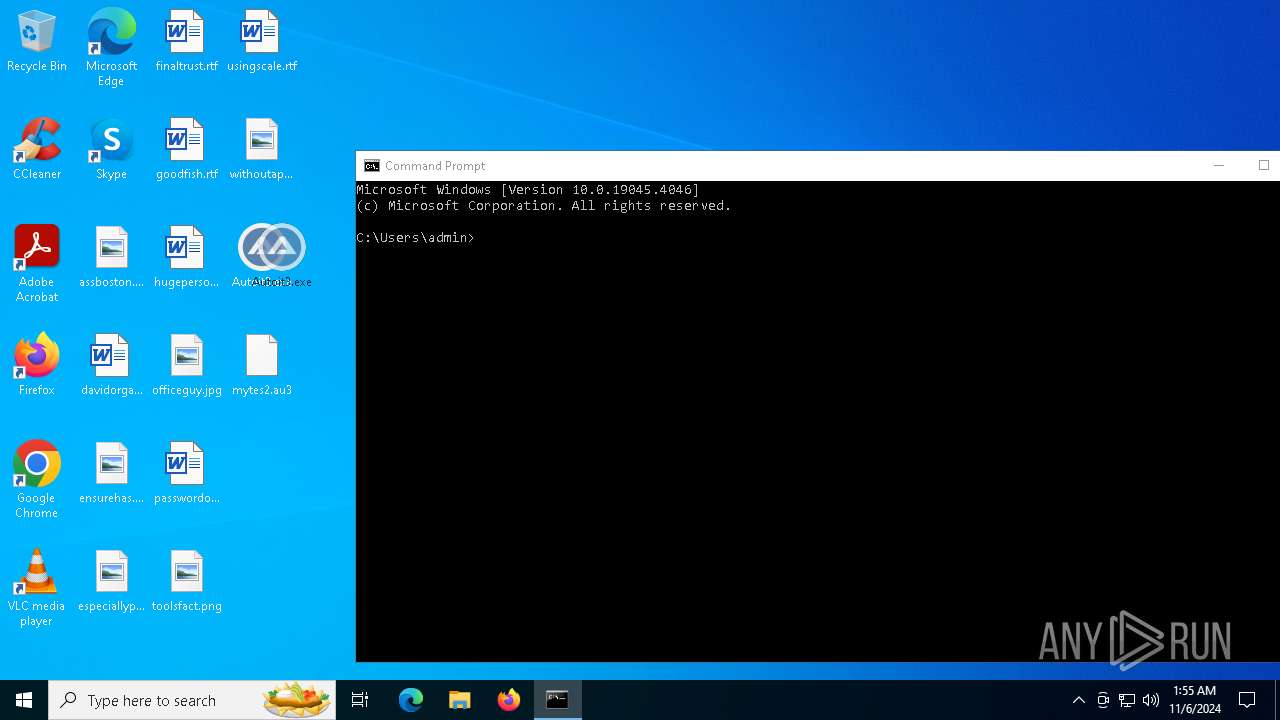
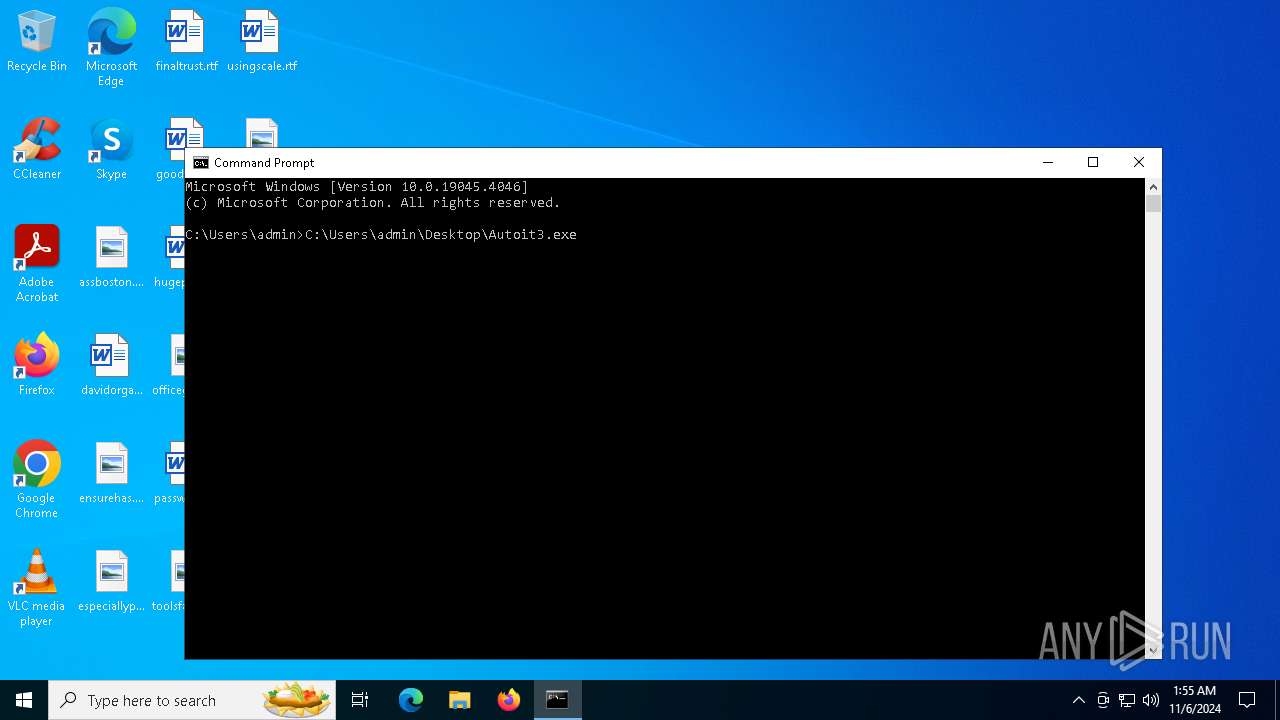
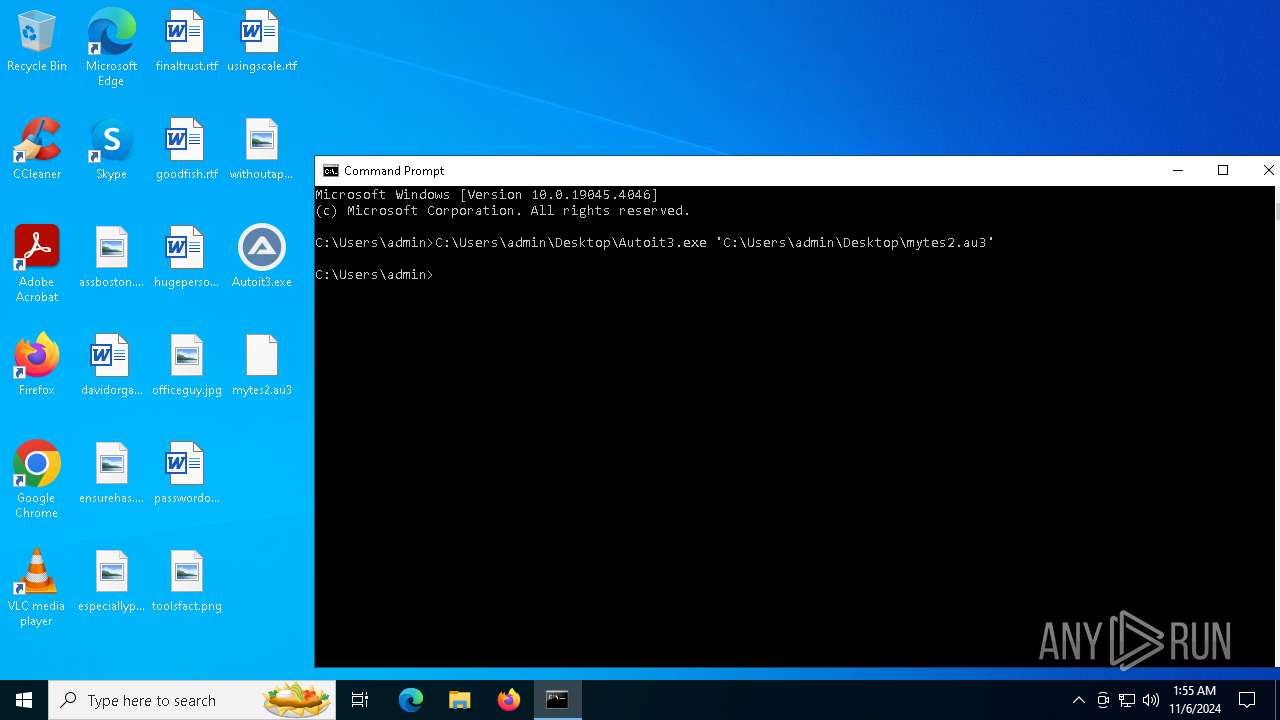
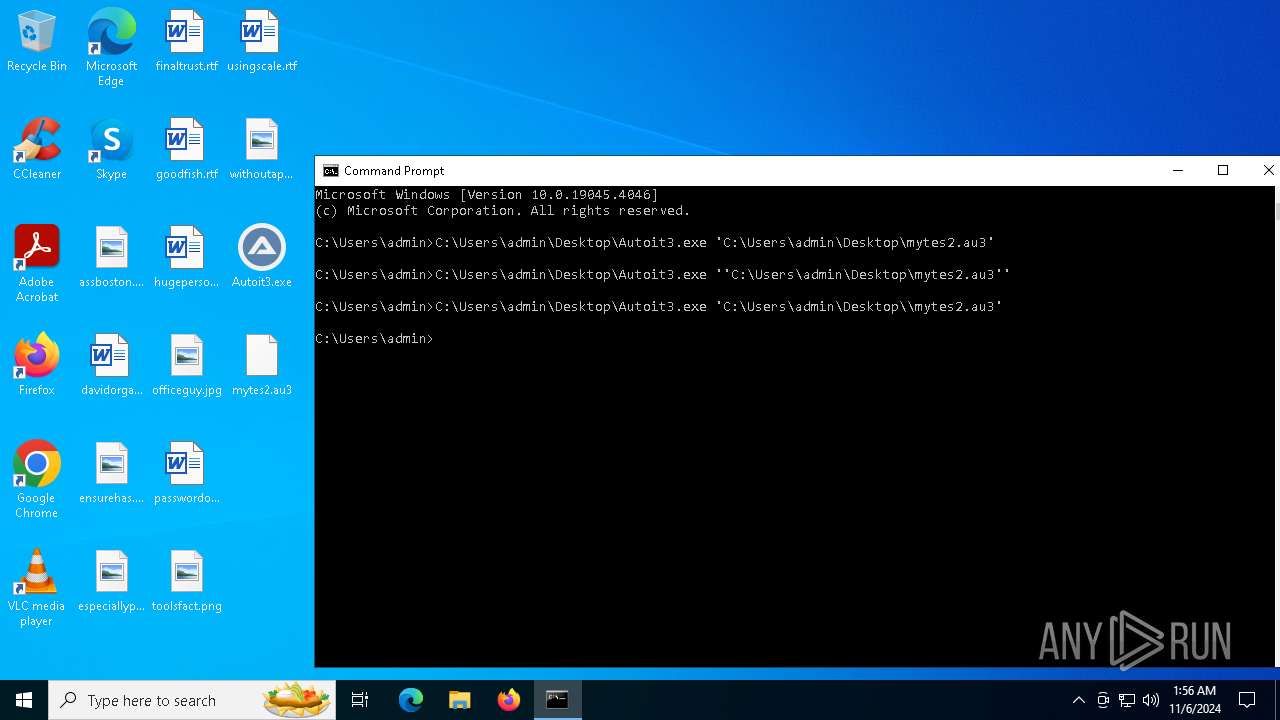
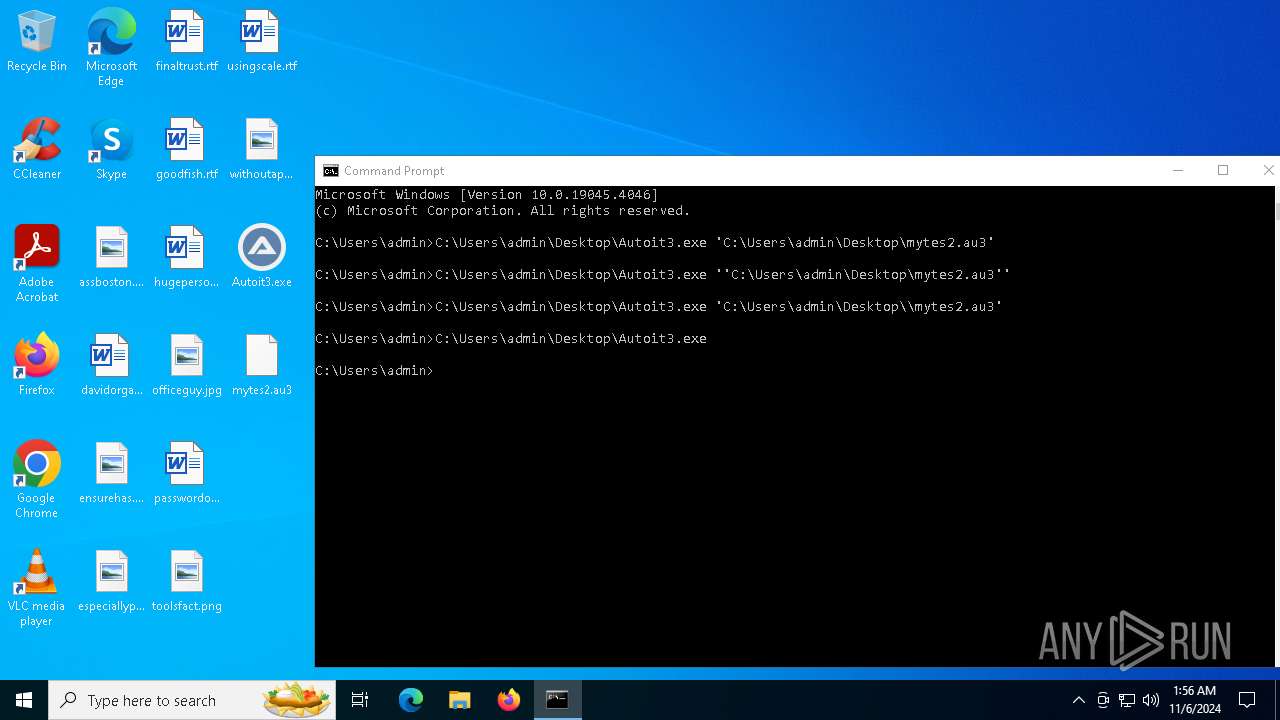
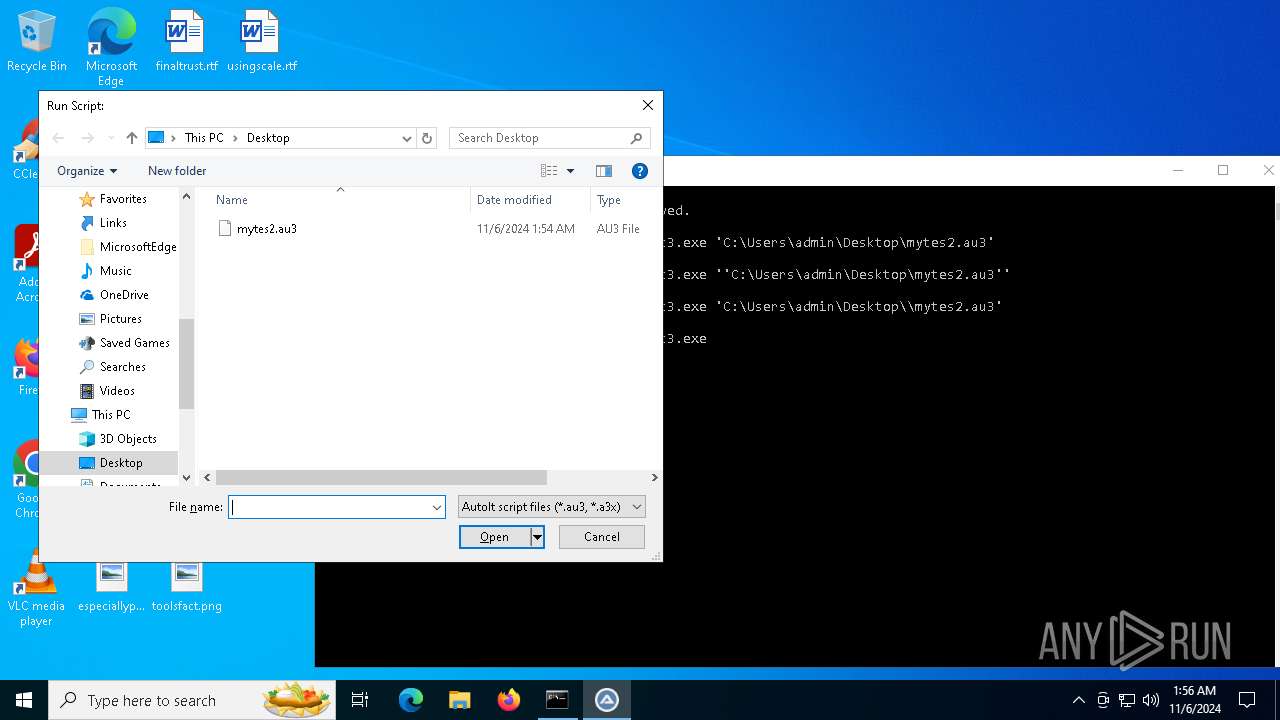
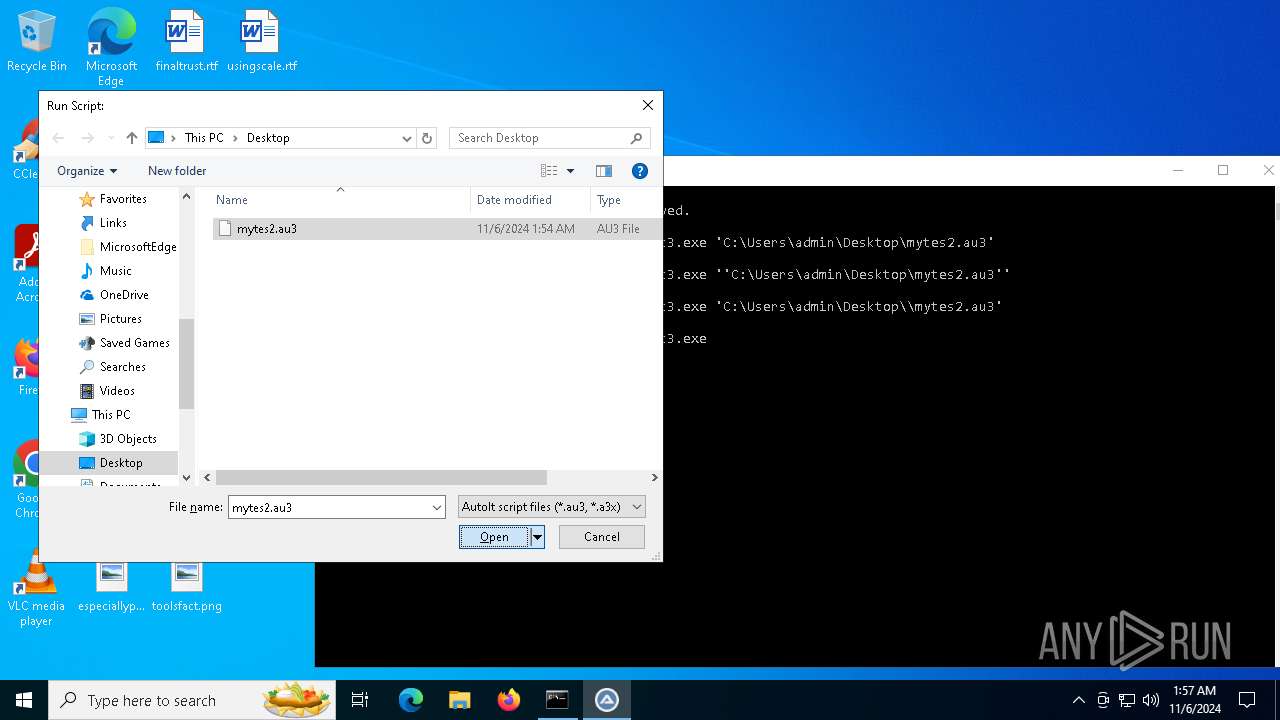
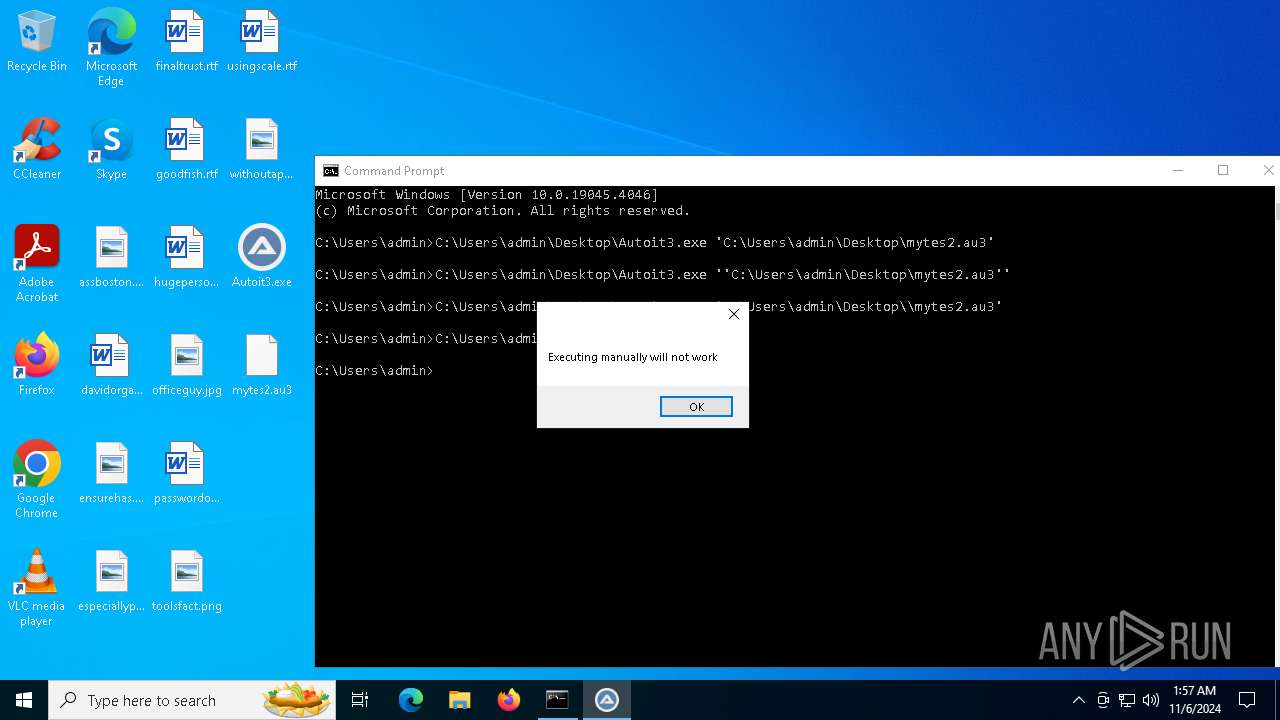
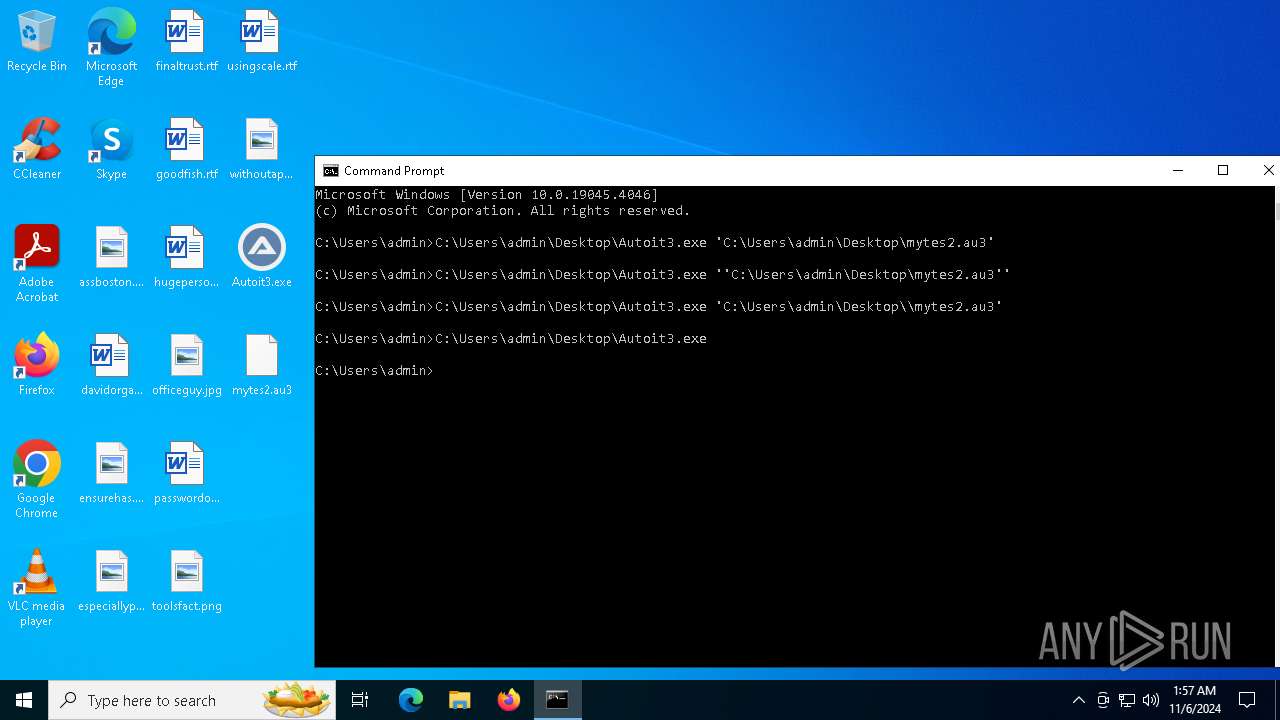
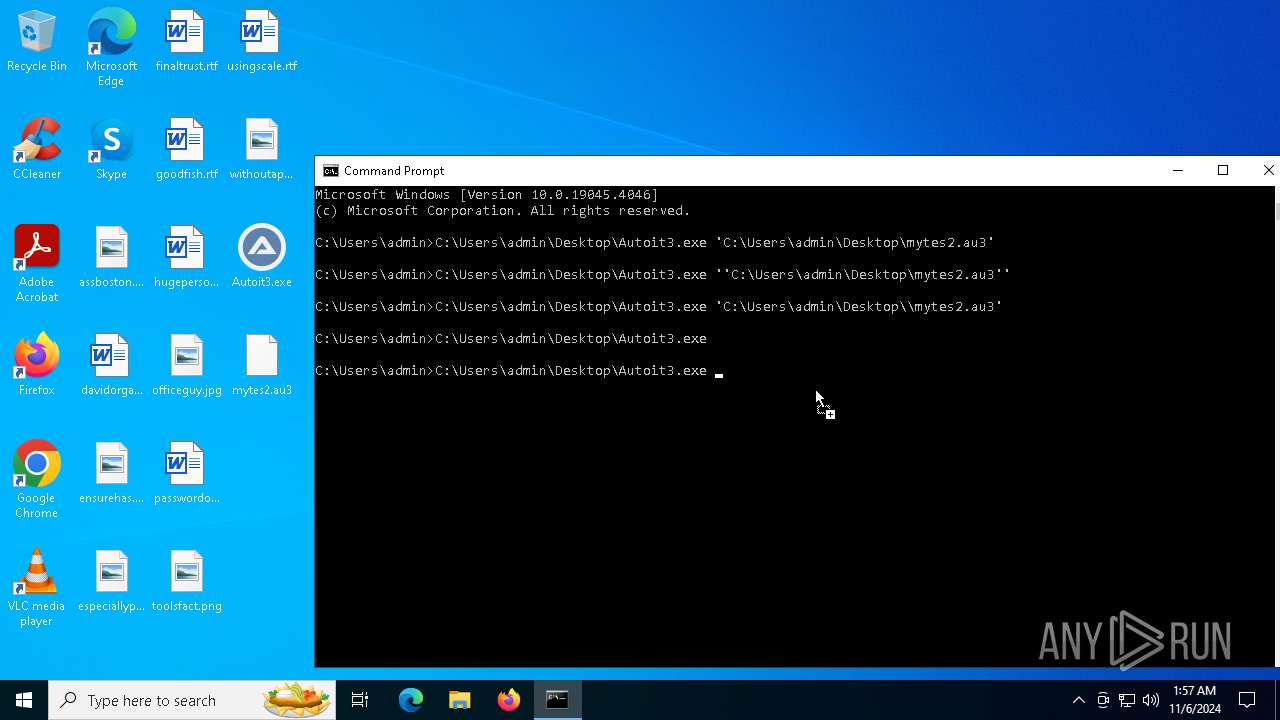
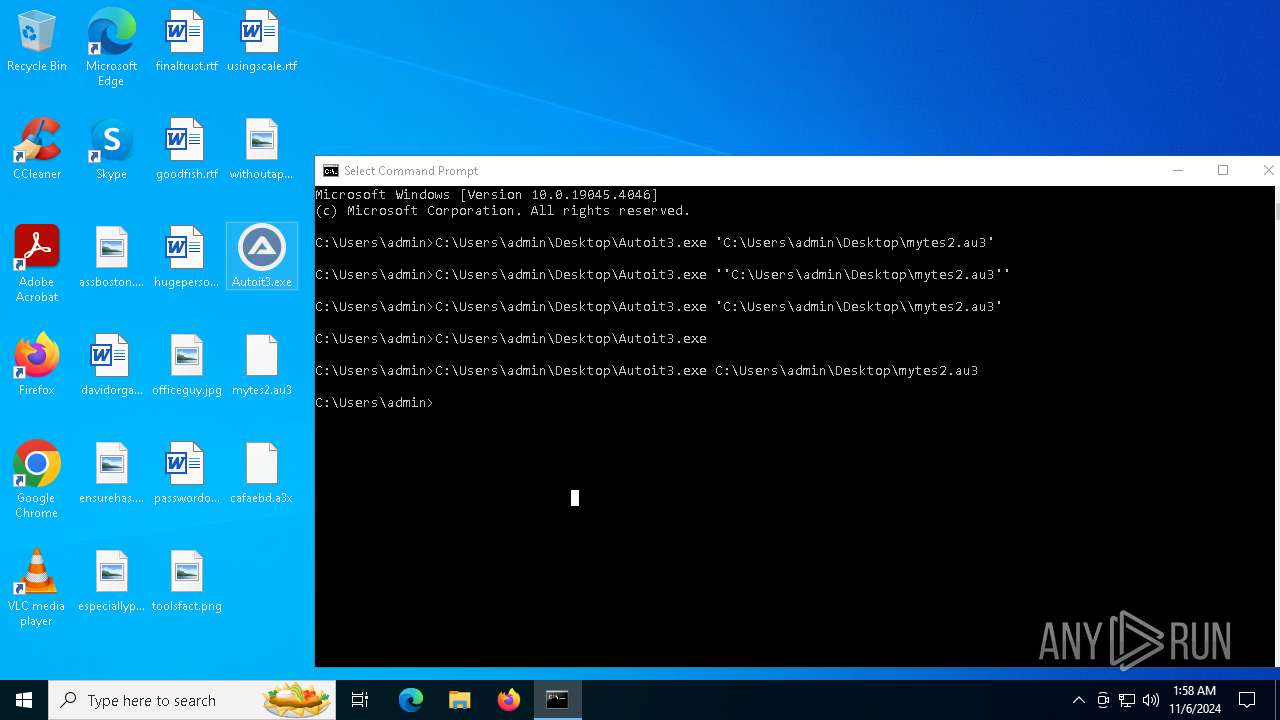
Manual execution by a user
- cmd.exe (PID: 4316)
Reads Windows Product ID
- Autoit3.exe (PID: 2928)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 4692)
Creates files in the program directory
- Autoit3.exe (PID: 2928)
- cmd.exe (PID: 6132)
Reads CPU info
- Autoit3.exe (PID: 2928)
Creates files or folders in the user directory
- Autoit3.exe (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:15 13:14:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 583680 |
| InitializedDataSize: | 317440 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27ffa |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.14.5 |
| ProductVersionNumber: | 3.3.14.5 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | AutoIt Team |
| Comments: | http://www.autoitscript.com/autoit3/ |
| FileDescription: | AutoIt v3 Script |
| FileVersion: | 3, 3, 14, 5 |
| InternalName: | AutoIt3.exe |
| LegalCopyright: | ©1999-2018 Jonathan Bennett & AutoIt Team |
| OriginalFileName: | AutoIt3.exe |
| ProductName: | AutoIt v3 Script |
| ProductVersion: | 3, 3, 14, 5 |
Total processes
145
Monitored processes
16
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
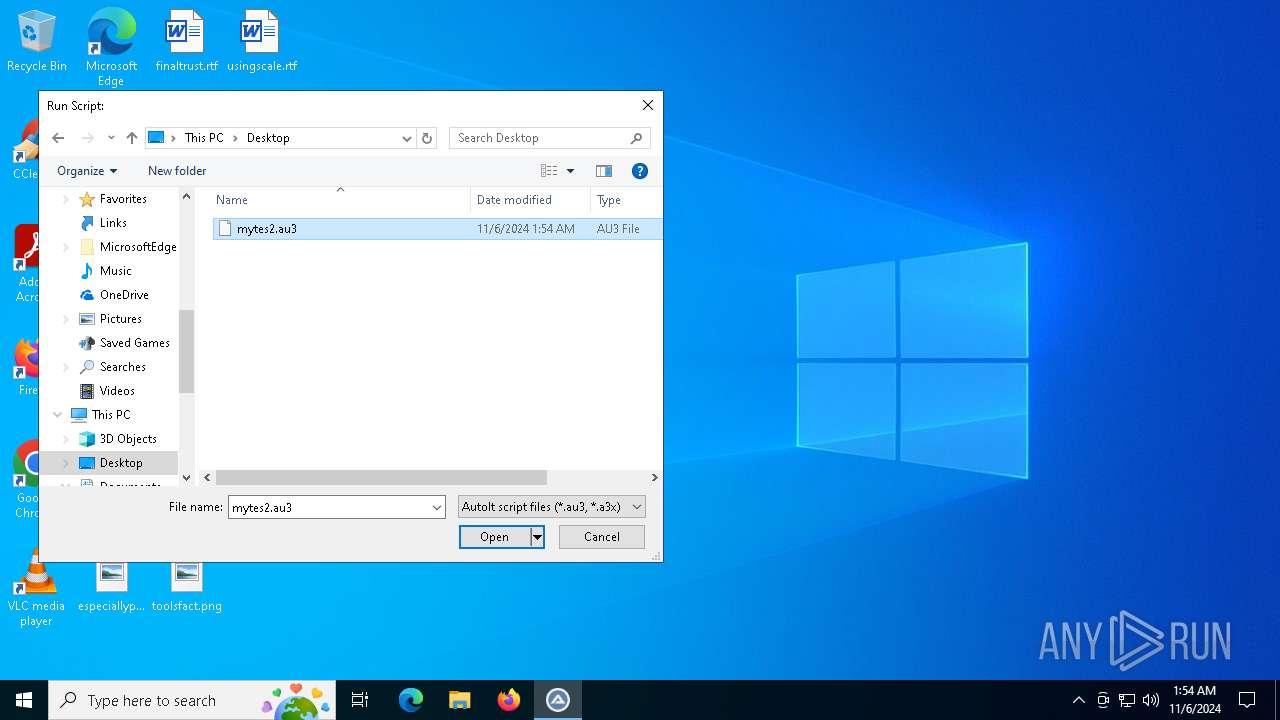
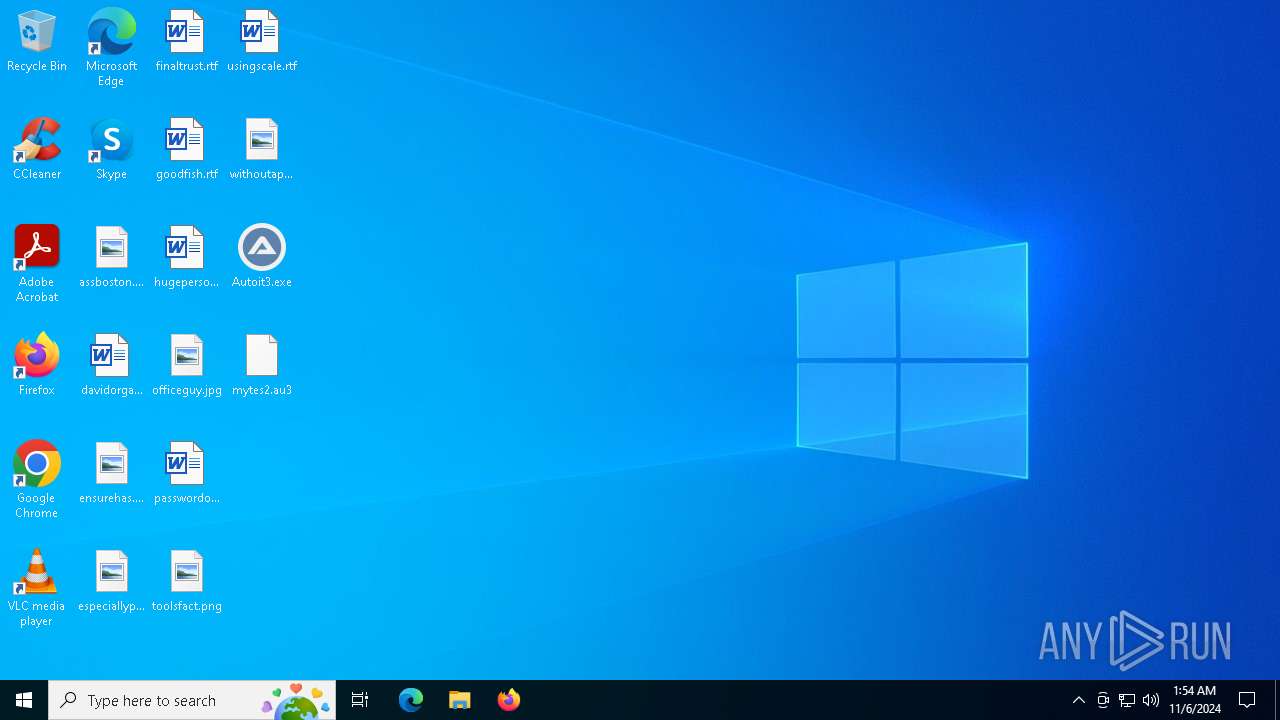
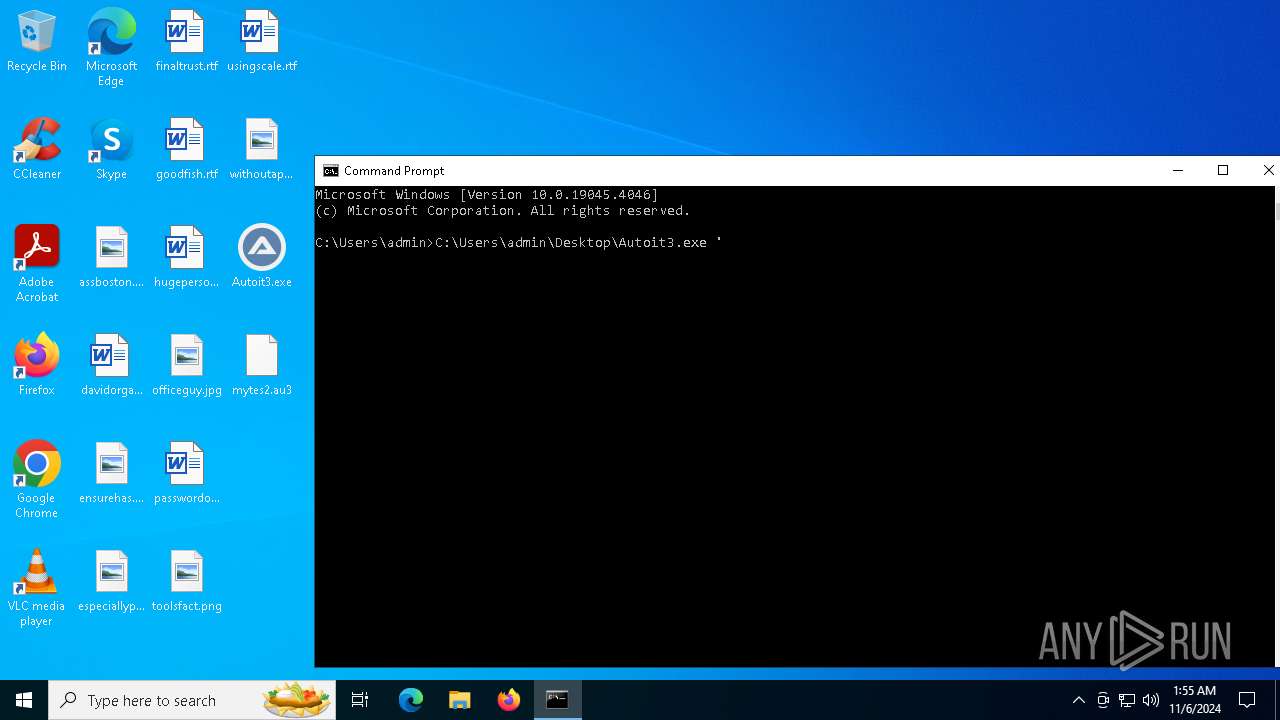
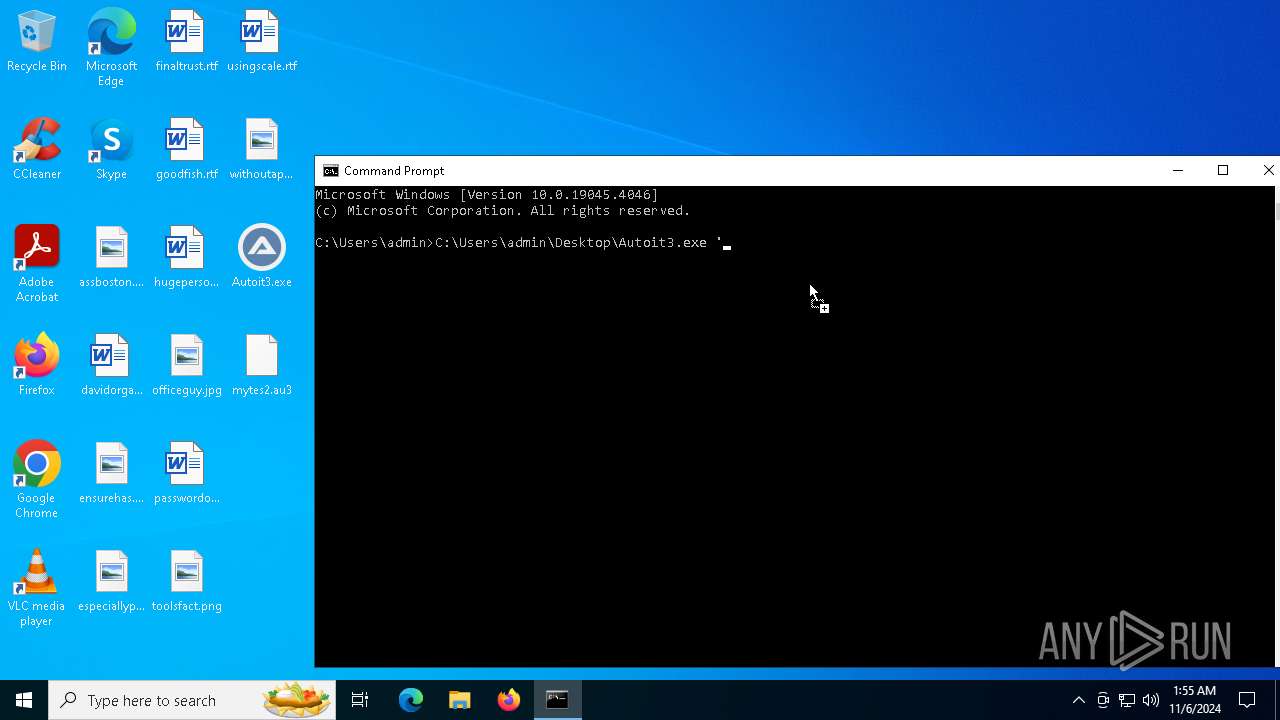
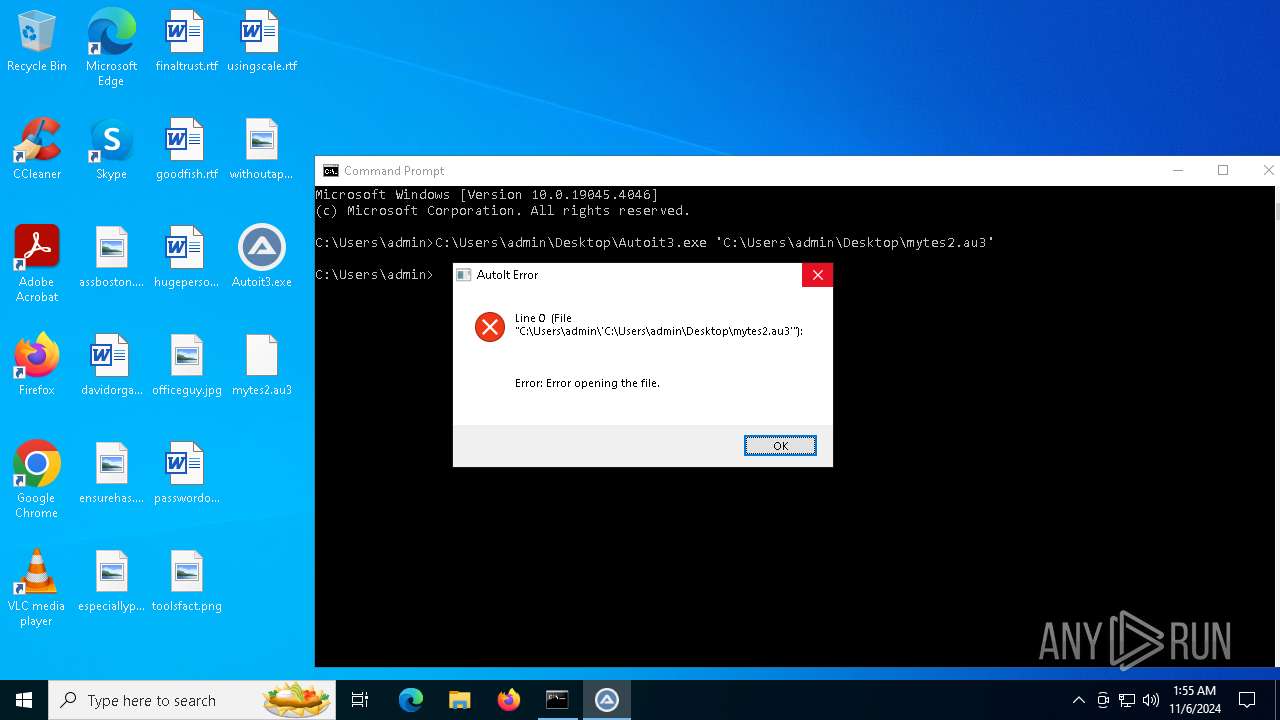
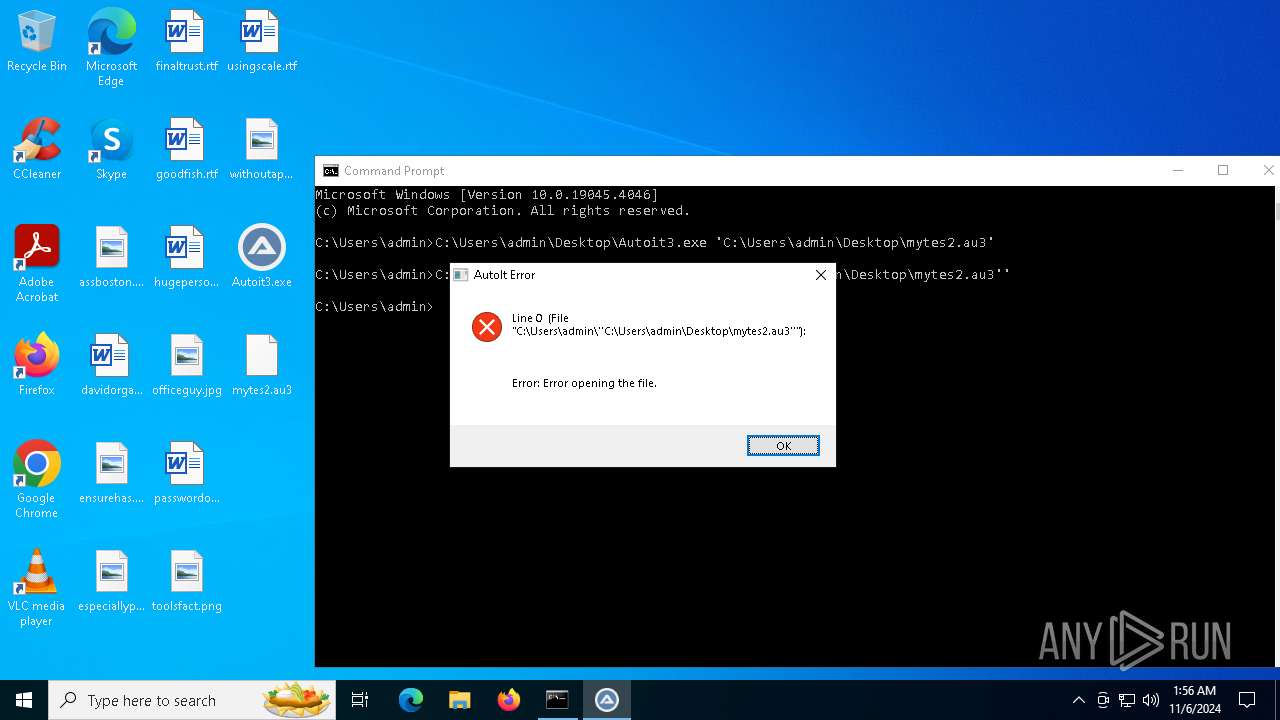
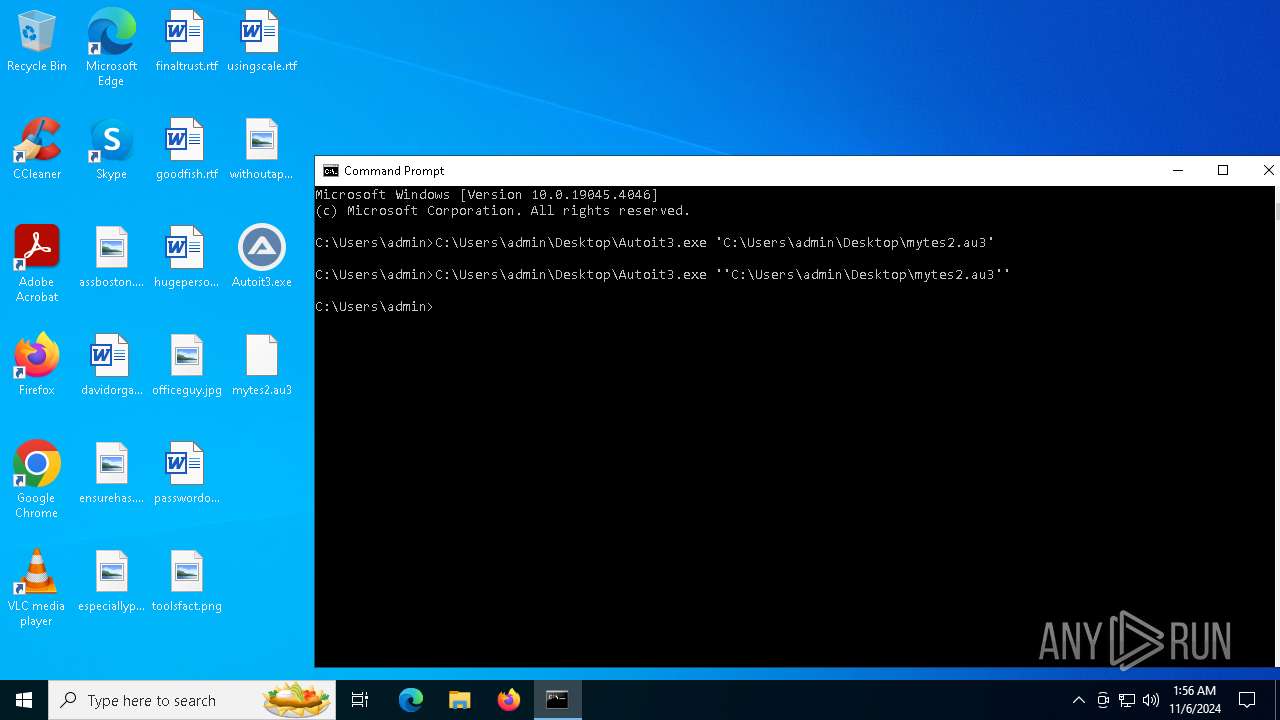
| 1332 | C:\Users\admin\Desktop\Autoit3.exe 'C:\Users\admin\Desktop\mytes2.au3' | C:\Users\admin\Desktop\Autoit3.exe | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 1 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 1576 | C:\Users\admin\Desktop\Autoit3.exe | C:\Users\admin\Desktop\Autoit3.exe | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 2484 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
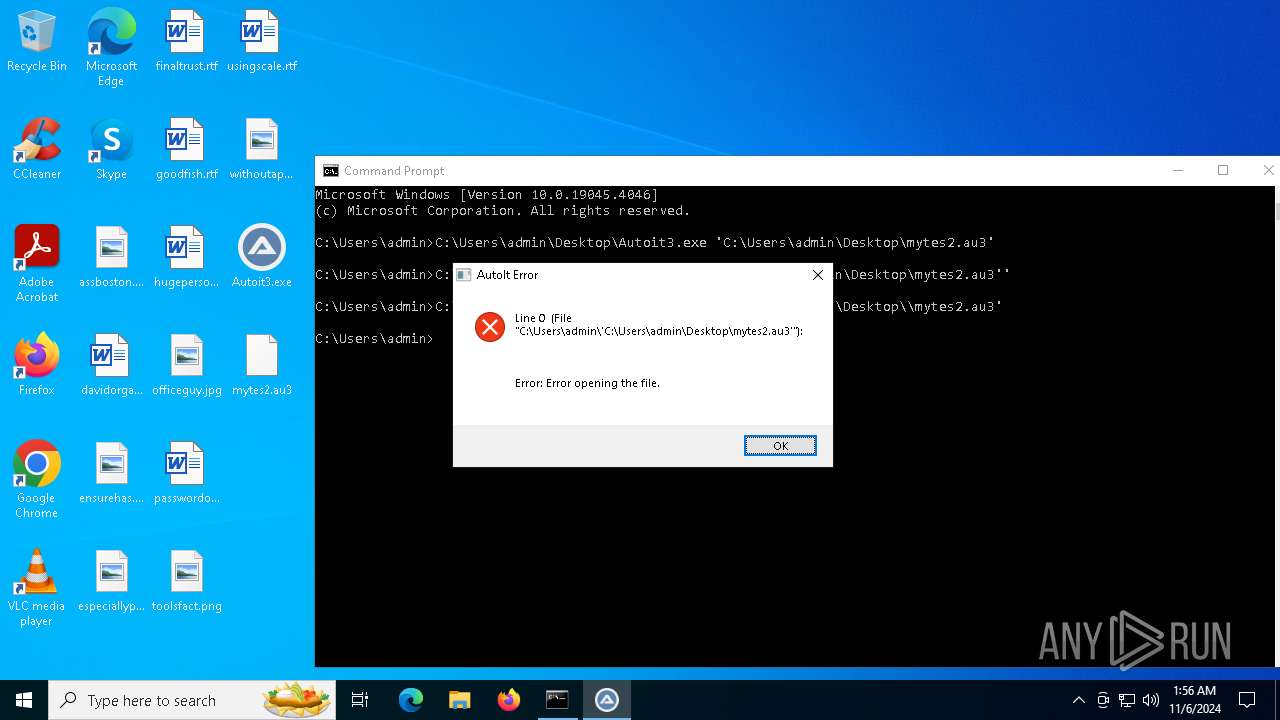
| 2928 | C:\Users\admin\Desktop\Autoit3.exe C:\Users\admin\Desktop\mytes2.au3 | C:\Users\admin\Desktop\Autoit3.exe | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 3108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\Desktop\Autoit3.exe" | C:\Users\admin\Desktop\Autoit3.exe | — | explorer.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
| |||||||||||||||
| 3568 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.185.17 Modules
| |||||||||||||||
| 3676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4316 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4692 | wmic ComputerSystem get domain | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 931
Read events
12 786
Write events
139
Delete events
6
Modification events
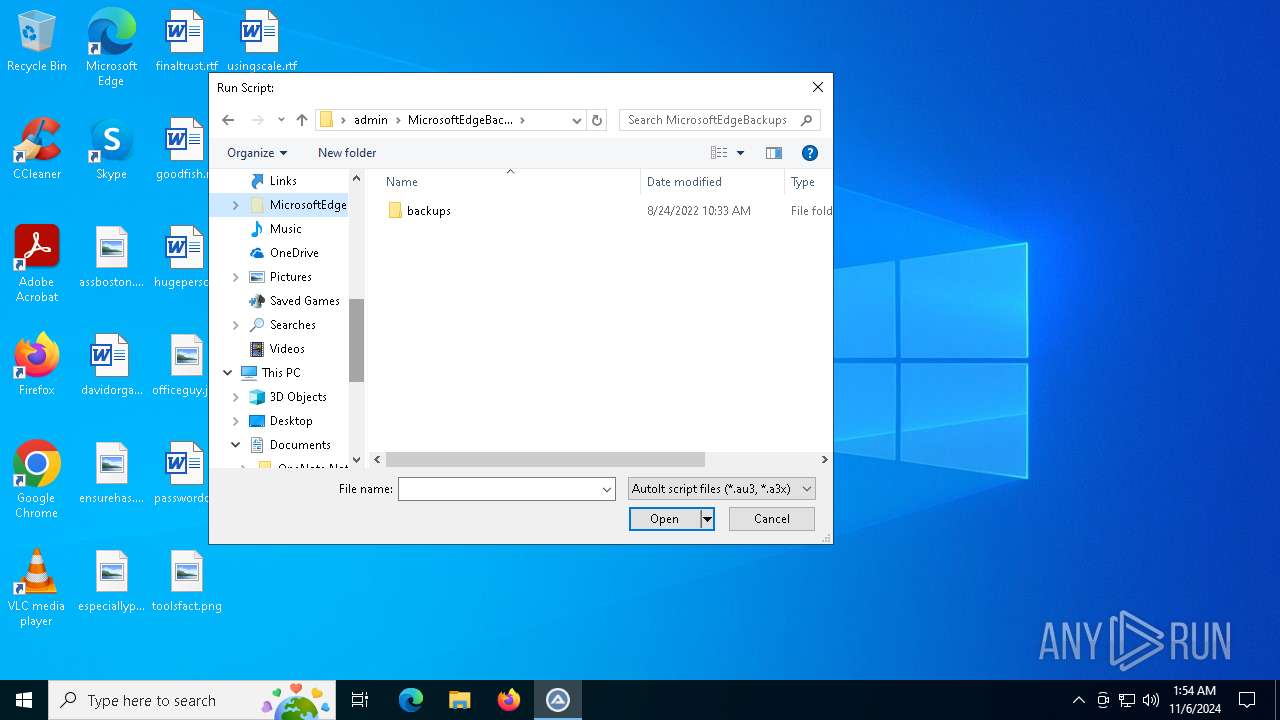
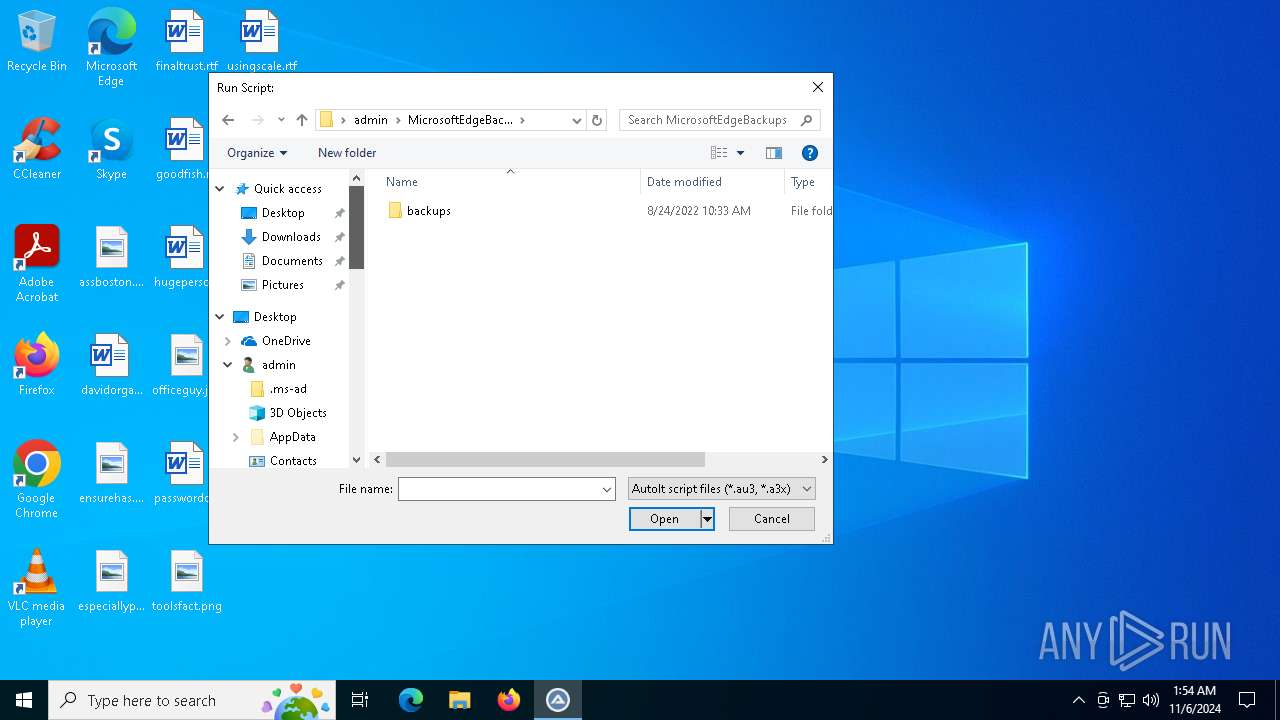
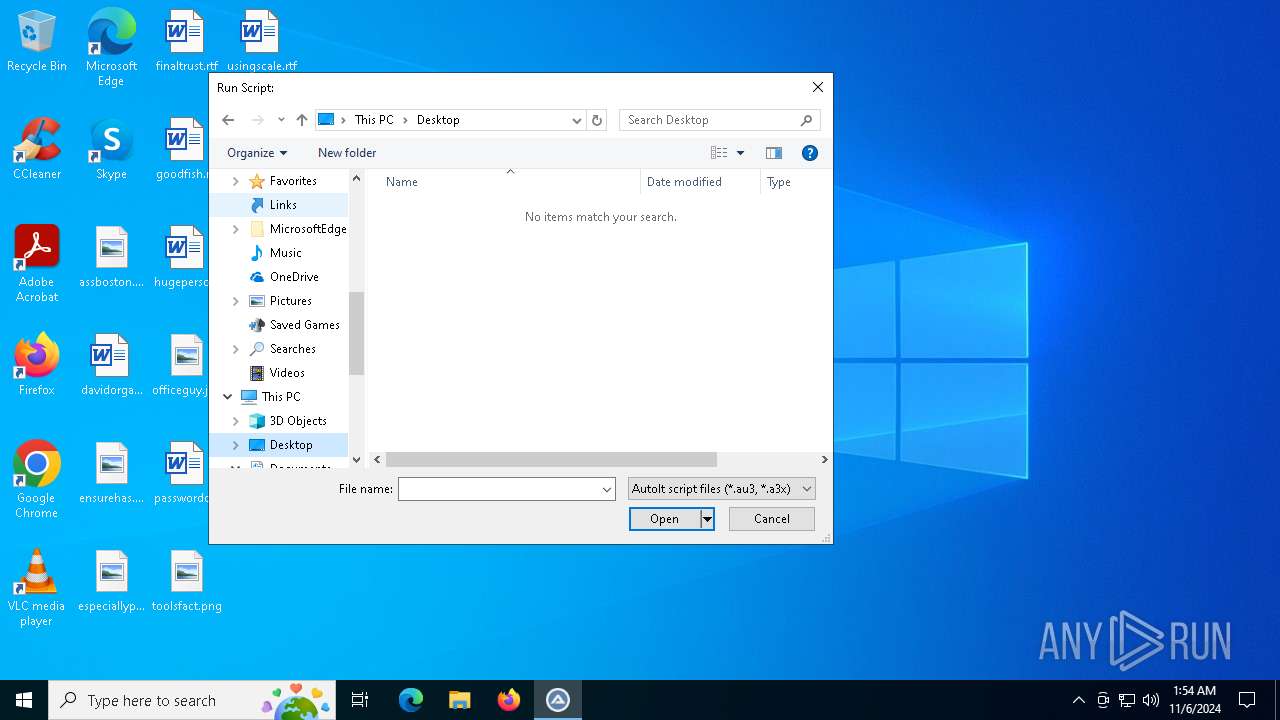
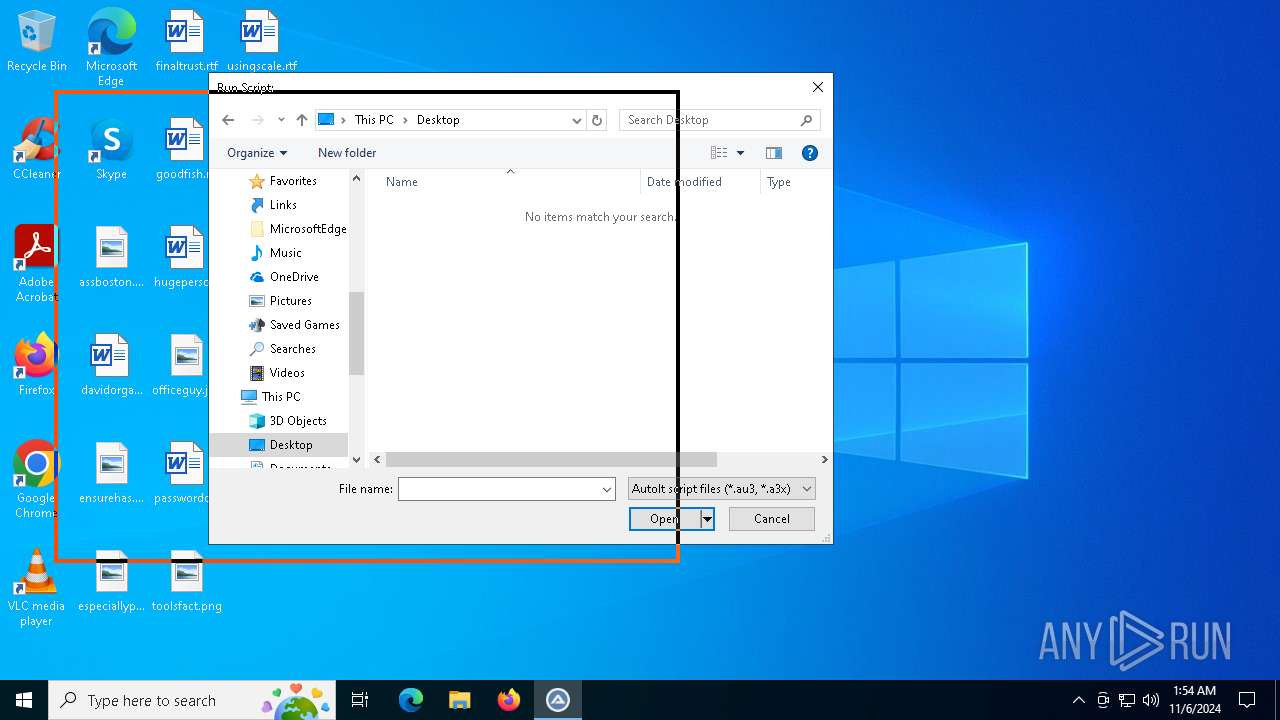
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000030000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 96 | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0E000000040000000000000003000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000000000003000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (3276) Autoit3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlg\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | FFlags |
Value: | |||
Executable files
1
Suspicious files
3
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6132 | cmd.exe | C:\ProgramData\geghfeh\bfaebcb | text | |
MD5:C8BBAD190EAAA9755C8DFB1573984D81 | SHA256:7F136265128B7175FB67024A6DDD7524586B025725A878C07D76A9D8AD3DC2AC | |||
| 2928 | Autoit3.exe | C:\Users\admin\AppData\Roaming\KBEFBbD | text | |
MD5:0755F5848D23B16DB97711A1899933E9 | SHA256:E6A6DB38BBEFB662A55E76C5F5D3AE64921E4ADE9E818CA6C5D7156D6187AAAE | |||
| 2928 | Autoit3.exe | C:\temp\gbaccab | text | |
MD5:597F2F4F63473B32EDF5D7B31378E3D8 | SHA256:A2700110A7CA00A1DFC65E13810F09F8BB2B5F5F129B3463CBB49129703B396C | |||
| 2928 | Autoit3.exe | C:\ProgramData\geghfeh\Autoit3.exe | executable | |
MD5:C56B5F0201A3B3DE53E561FE76912BFD | SHA256:237D1BCA6E056DF5BB16A1216A434634109478F882D3B1D58344C801D184F95D | |||
| 2928 | Autoit3.exe | C:\temp\dhcfcdg | text | |
MD5:B0691528BB93D4BEEC25DB1E8861600F | SHA256:E2A8EE6A0F8F6C6B57A16C934A7500B6772583FD2DA3AB4ADD5C36A18C06379F | |||
| 5516 | MicrosoftEdgeUpdateCore.exe | C:\ProgramData\geghfeh\fghakdc | binary | |
MD5:825036640F6001E15797E9D9FC9A6624 | SHA256:BE8890807EBF98ADF4CA521B123BCD8A83D4C0C793A507D6A2EE3510B5428FA6 | |||
| 5516 | MicrosoftEdgeUpdateCore.exe | C:\temp\dhcfcdg | text | |
MD5:49854568F39FFE6A92F19E8C264E5F83 | SHA256:3B686C29B6206EFF6ED6ACF5AA6C320D31FE678B138AFB7B6D7DC82AF52F4C10 | |||
| 5516 | MicrosoftEdgeUpdateCore.exe | C:\temp\dhchcaa | text | |
MD5:B2E519A54B24FD7FA02E300279950F65 | SHA256:C48ADEEECF53717C072B1A3C7CF9967C436FADB3EF6A27D8D4DA18EE903CDD53 | |||
| 3568 | MicrosoftEdgeUpdateCore.exe | C:\temp\dhchcaa | text | |
MD5:3C976C92605931A55ED9D4AC7F622EB4 | SHA256:F1E346469B694B9EAAC6A21E3E4FB9148943D7F10377B34F242DC105DE4716B9 | |||
| 2928 | Autoit3.exe | C:\ProgramData\geghfeh\eaabkek.a3x | binary | |
MD5:D91891CAE02A24735853100A3511D74F | SHA256:E2C3B31EE3615E2F39843D035F1990B94C12AF1E42C34CE8E83C28B29C85567D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
44
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.123.41.162:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.209.125.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 104.123.41.162:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5172 | WerFault.exe | GET | 200 | 23.209.125.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.209.125.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5748 | SIHClient.exe | GET | 200 | 104.123.41.162:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.16.27.215:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.209.125.34:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.209.125.34:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 104.123.41.162:80 | www.microsoft.com | AKAMAI-AS | NL | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5488 | MoUsoCoreWorker.exe | 104.123.41.162:80 | www.microsoft.com | AKAMAI-AS | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |