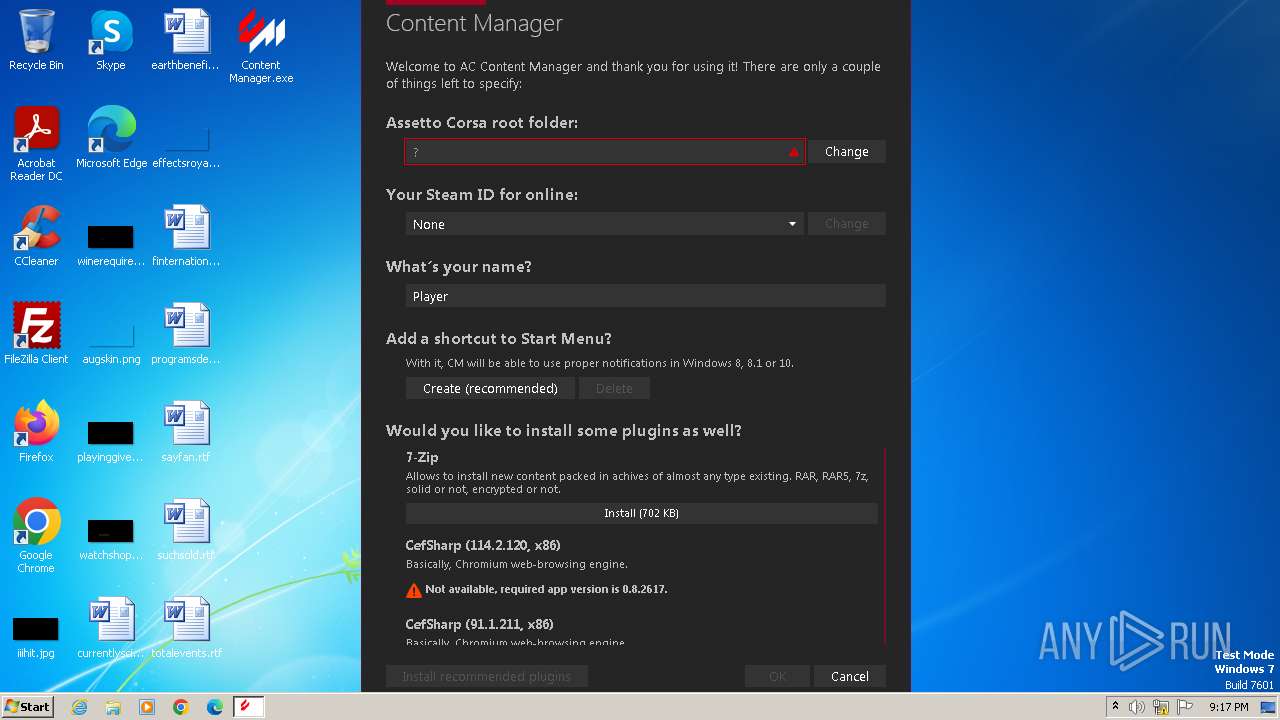
| File name: | Content Manager.exe |
| Full analysis: | https://app.any.run/tasks/51a13aa1-a721-4395-9b14-e5853d59c9c6 |
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2024, 20:17:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 60ED4BFBD48A0D1C161D123749BA6586 |
| SHA1: | F21F2D4B038602EBF923FADCB4CBE07CD3B4979A |
| SHA256: | 2367612DB7C754BF4F07A0F71188C0CC7ED0E39BEF12B7DC3F4AF3D0B3EC5BD4 |
| SSDEEP: | 98304:whhE1x5HHrsEs4deFIls0LoaRLlFmzH0Fcwa6PoI+49U2ay8iACS+9yBrS7caHfX:sSKGijKU02asxc |
MALICIOUS
Drops the executable file immediately after the start
- Content Manager.exe (PID: 3968)
Actions looks like stealing of personal data
- Content Manager.exe (PID: 3968)
SUSPICIOUS
Reads the Internet Settings
- Content Manager.exe (PID: 3968)
Changes Internet Explorer settings (feature browser emulation)
- Content Manager.exe (PID: 3968)
Reads security settings of Internet Explorer
- Content Manager.exe (PID: 3968)
Reads settings of System Certificates
- Content Manager.exe (PID: 3968)
Executable content was dropped or overwritten
- Content Manager.exe (PID: 3968)
INFO
Reads the computer name
- Content Manager.exe (PID: 3968)
- wmpnscfg.exe (PID: 748)
Checks supported languages
- Content Manager.exe (PID: 3968)
- wmpnscfg.exe (PID: 748)
Reads the machine GUID from the registry
- Content Manager.exe (PID: 3968)
Reads Environment values
- Content Manager.exe (PID: 3968)
Create files in a temporary directory
- Content Manager.exe (PID: 3968)
Reads the software policy settings
- Content Manager.exe (PID: 3968)
Manual execution by a user
- wmpnscfg.exe (PID: 748)
Creates files or folders in the user directory
- Content Manager.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:17 23:21:18+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 11182080 |
| InitializedDataSize: | 114176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaabe6e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.8.2594.39678 |
| ProductVersionNumber: | 0.8.2594.39678 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Custom launcher and content manager for Assetto Corsa |
| CompanyName: | AcClub |
| FileDescription: | Content Manager |
| FileVersion: | 0.8.2594.39678 |
| InternalName: | Content Manager.exe |
| LegalCopyright: | Copyright © AcClub, 2015-2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Content Manager.exe |
| ProductName: | Content Manager |
| ProductVersion: | 0.8.2594.39678 |
| AssemblyVersion: | 0.8.2594.39678 |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 748 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\Desktop\Content Manager.exe" | C:\Users\admin\Desktop\Content Manager.exe | explorer.exe | ||||||||||||
User: admin Company: AcClub Integrity Level: MEDIUM Description: Content Manager Version: 0.8.2594.39678 Modules
| |||||||||||||||
Total events
4 978
Read events
4 946
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Content Manager.exe | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | Content Manager.exe |
Value: 11999 | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_96DPI_PIXEL |
| Operation: | write | Name: | Content Manager.exe |
Value: 1 | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CLASSES_ROOT\acmanager |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3968) Content Manager.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.kn5\OpenWithProgids |
| Operation: | write | Name: | acmanager.kn5 |
Value: | |||
Executable files
16
Suspicious files
63
Text files
949
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\Temp\Costura\80020E73785608EBC4CC66D86D9D69C2\32\interop.d3dimageex.dll | executable | |
MD5:D924C109DA0F7A9E1DEBC63CB6D9B30B | SHA256:D9EAB44547374B7A7AC21FE4A36BF79049B3373865FA319C371578368E716AB5 | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\Temp\Costura\80020E73785608EBC4CC66D86D9D69C2\32\nvidia.texturetools.compress.dll | executable | |
MD5:74654ED00F7E89F80DD1BBBF4D02C402 | SHA256:D8ED3A09E150D8608940497267AB6BCBD3CDC9D59FE4B50B849E1FF8344141BA | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\Temp\Costura\80020E73785608EBC4CC66D86D9D69C2\32\slimdx.dll | executable | |
MD5:BA01667F0579AEC6E0F9C702431A23B5 | SHA256:C54DBA6B35525BE2D1A7DFF11954423DACA65EBB3F7022A9F58389F899956205 | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\AcTools Content Manager\Temporary\CUP\71cde14f3bfec1d96045b0d8e6a604372c351f15 | binary | |
MD5:921970E2B27822951423FF436AF6C17E | SHA256:E71D8E3477393879D92486D91409135EA94FF0898C275E047E51AA4E994258B8 | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\AcTools Content Manager\Websites.data.new | binary | |
MD5:BBC48D16849630A83B3B7B0215FBBE80 | SHA256:495EF03E18BB5BBD17CDD26E86A05B7127D6D4A7CACA4058589688B11422252F | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\AcTools Content Manager\Temporary\Patch\Manifest.json | text | |
MD5:631267FD6BC10B8B3F4A8BD802A526CE | SHA256:2A87BC3012D56984C297D9B334BE7B40D6C772CEB7522702ECF4469702A51F32 | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\AcTools Content Manager\Websites.data | binary | |
MD5:BBC48D16849630A83B3B7B0215FBBE80 | SHA256:495EF03E18BB5BBD17CDD26E86A05B7127D6D4A7CACA4058589688B11422252F | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\AcTools Content Manager\Values.data | binary | |
MD5:5E156CECDAA9251FCD44BF6400F18225 | SHA256:35E32211FC616C3C40559A7CF1BBEC0A78582A0657895FC5802C25489300808E | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\AcTools Content Manager\Logs\Main Log_240606_211741.log | text | |
MD5:2EB19B925AE13A305021FBEC68B58382 | SHA256:94EC4DCE7DDB9FE78C336579E69A869D2740641C348A86A4D1462DC7B0A13025 | |||
| 3968 | Content Manager.exe | C:\Users\admin\AppData\Local\AcTools Content Manager\Values.data.new | binary | |
MD5:5E156CECDAA9251FCD44BF6400F18225 | SHA256:35E32211FC616C3C40559A7CF1BBEC0A78582A0657895FC5802C25489300808E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | Content Manager.exe | GET | 301 | 172.67.71.70:80 | http://acstuff.ru/f/api/posts/content-extra?filter[discussion]=24&filter[type]=comment&sort=-time&page[size]=99999 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3968 | Content Manager.exe | 172.67.71.70:80 | acstuff.ru | CLOUDFLARENET | US | unknown |
3968 | Content Manager.exe | 172.67.71.70:443 | acstuff.ru | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acstuff.ru |
| unknown |