| File name: | cmd2.cmd |
| Full analysis: | https://app.any.run/tasks/d1eaeddc-eb8d-4c49-b216-7e9a5d92e742 |
| Verdict: | Malicious activity |
| Analysis date: | May 11, 2025, 06:08:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | exported SGML document, ASCII text, with CRLF line terminators |
| MD5: | 0B9B0EF81AC677A5C0BA9A7276382AD4 |
| SHA1: | 563A05C2265FA604D898F07BC6BC278CF13F4C28 |
| SHA256: | 2362A406AC0DB3D4E9C858FA17889AB60C29D79C42C21E014946A258B7304F25 |
| SSDEEP: | 3072:W5Jd5MJ/nu6tE0Aawm0khHR5nEn/GnkSzM+7EYGKGBt28eKl4:sJ0J/nu6Sfm0t/GnkSzM4fK6 |
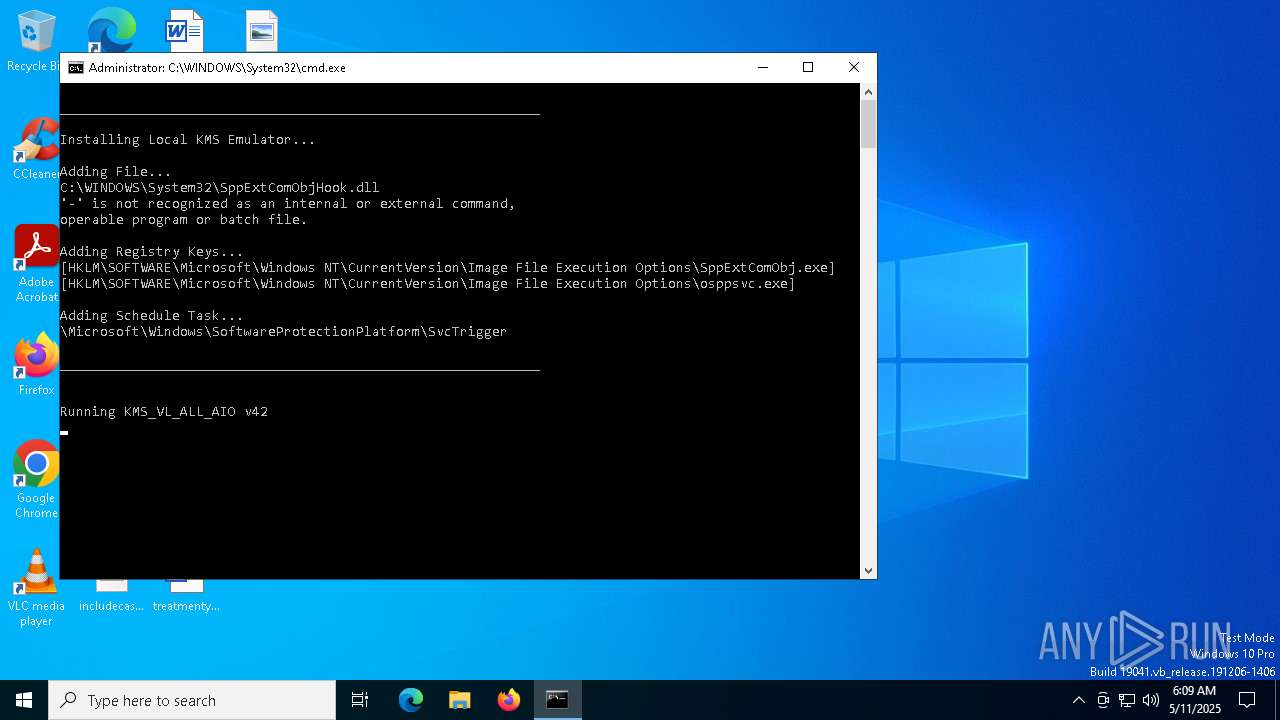
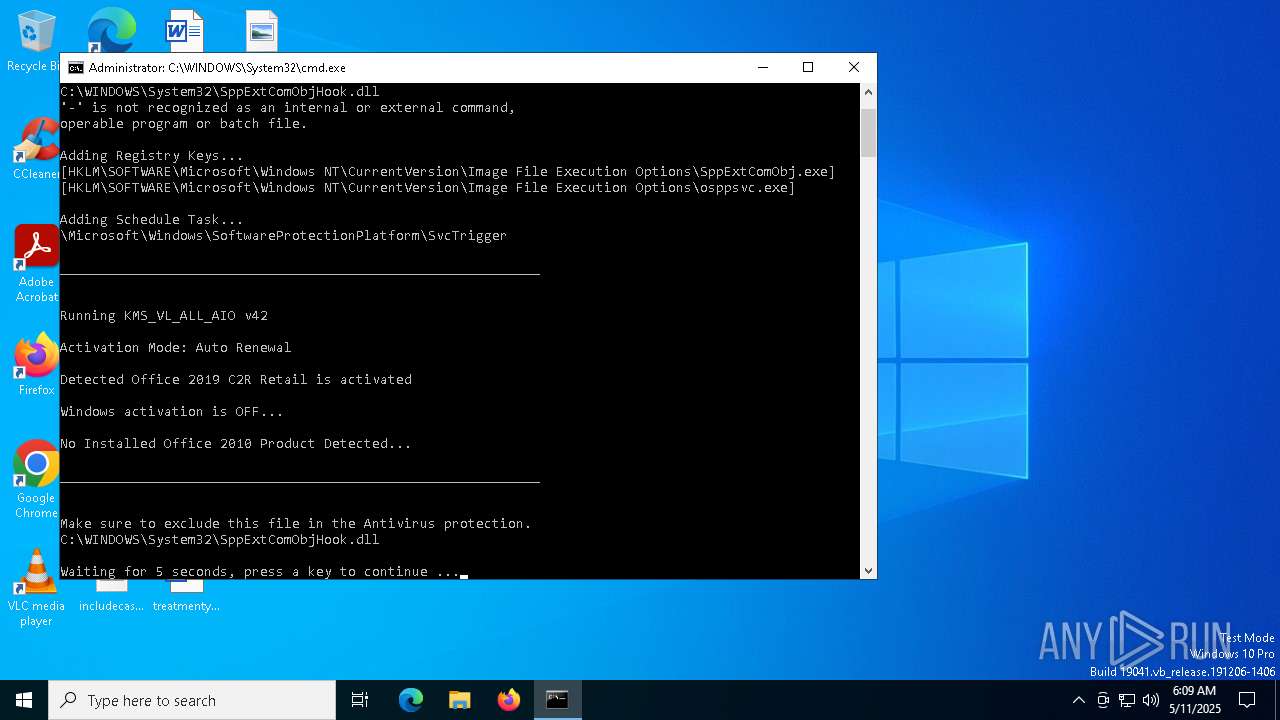
MALICIOUS
Starts NET.EXE for service management
- net.exe (PID: 6516)
- cmd.exe (PID: 4724)
- net.exe (PID: 1184)
- net.exe (PID: 1244)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4724)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4724)
- powershell.exe (PID: 2236)
Application launched itself
- cmd.exe (PID: 4724)
Windows service management via SC.EXE
- sc.exe (PID: 4428)
- sc.exe (PID: 6656)
- sc.exe (PID: 1760)
- sc.exe (PID: 4868)
- sc.exe (PID: 3272)
- sc.exe (PID: 6488)
- sc.exe (PID: 6640)
- sc.exe (PID: 4688)
- sc.exe (PID: 2420)
- sc.exe (PID: 896)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4724)
- cmd.exe (PID: 4024)
Starts SC.EXE for service management
- cmd.exe (PID: 4724)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4724)
- cmd.exe (PID: 4024)
Executes script without checking the security policy
- powershell.exe (PID: 5072)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 664)
- powershell.exe (PID: 5436)
Executing commands from ".cmd" file
- powershell.exe (PID: 2236)
Executing commands from a ".bat" file
- powershell.exe (PID: 2236)
Stops a currently running service
- sc.exe (PID: 1660)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 664)
Lists all scheduled tasks
- schtasks.exe (PID: 7148)
- schtasks.exe (PID: 5352)
- schtasks.exe (PID: 4224)
- schtasks.exe (PID: 3008)
- schtasks.exe (PID: 5936)
Modifies existing scheduled task
- schtasks.exe (PID: 5984)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4724)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 664)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4724)
Hides command output
- cmd.exe (PID: 5452)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 4452)
- cmd.exe (PID: 5380)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6032)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 6644)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 4448)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2268)
- cmd.exe (PID: 4724)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4724)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4724)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 6044)
- cmd.exe (PID: 4400)
- cmd.exe (PID: 4724)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4724)
INFO
Reads security settings of Internet Explorer
- cscript.exe (PID: 5576)
- WMIC.exe (PID: 4068)
- WMIC.exe (PID: 1180)
- WMIC.exe (PID: 5984)
- WMIC.exe (PID: 4988)
- WMIC.exe (PID: 4868)
- WMIC.exe (PID: 5376)
- WMIC.exe (PID: 2236)
- WMIC.exe (PID: 1676)
- WMIC.exe (PID: 1348)
- WMIC.exe (PID: 6244)
- WMIC.exe (PID: 1672)
- WMIC.exe (PID: 6028)
- WMIC.exe (PID: 5556)
Starts MODE.COM to configure console settings
- mode.com (PID: 2392)
Checks operating system version
- cmd.exe (PID: 4724)
Checks supported languages
- mode.com (PID: 2392)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 664)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 664)
Reads Microsoft Office registry keys
- reg.exe (PID: 4244)
- reg.exe (PID: 6816)
- reg.exe (PID: 3272)
- reg.exe (PID: 728)
- reg.exe (PID: 5204)
- reg.exe (PID: 3768)
- reg.exe (PID: 3240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
535
Monitored processes
403
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | findstr /I /C:"WordVolume" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | findstr /I /C:"O365HomePremRetail" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | findstr /I /C:"HomeStudent2019Retail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | find /i "STOPPED" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | findstr /I /C:"OneNoteVolume" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | findstr /I /C:"ProfessionalRetail" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | findstr /I /C:"PowerPoint2021Volume" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | findstr /I /C:"VisioPro2019Retail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | find /i "Office21Professional2019R_Retail" "C:\WINDOWS\Temp\crvRetail.txt" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 662
Read events
23 633
Write events
29
Delete events
0
Modification events
| (PID) Process: | (4980) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | VerifierDlls |
Value: SppExtComObjHook.dll | |||
| (PID) Process: | (5668) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | VerifierDebug |
Value: 0 | |||
| (PID) Process: | (6876) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | VerifierFlags |
Value: | |||
| (PID) Process: | (2392) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe |
| Operation: | write | Name: | VerifierDlls |
Value: SppExtComObjHook.dll | |||
| (PID) Process: | (4448) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe |
| Operation: | write | Name: | VerifierDebug |
Value: 0 | |||
| (PID) Process: | (728) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe |
| Operation: | write | Name: | VerifierFlags |
Value: | |||
| (PID) Process: | (1184) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe |
| Operation: | write | Name: | KMS_RenewalInterval |
Value: 10080 | |||
| (PID) Process: | (1072) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | GlobalFlag |
Value: 256 | |||
| (PID) Process: | (6620) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | KMS_Emulation |
Value: 1 | |||
| (PID) Process: | (4896) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe |
| Operation: | write | Name: | KMS_ActivationInterval |
Value: 120 | |||
Executable files
0
Suspicious files
1
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5072 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xww3s5nu.p0l.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4724 | cmd.exe | C:\Windows\Temp\sppchk.txt | text | |
MD5:1F3EA1427D787A6420BFF6B8E1FD1EA4 | SHA256:BE033784A227FFA2F367E6B23893D45654FC5FFF24A95CDDA0DD03821BDE109F | |||
| 2236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_55spsqyr.5as.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_let3dq4k.vya.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lkvdzwu4.tqq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5436 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tc5mv4gh.q3e.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5072 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wmnha5s0.1yi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4724 | cmd.exe | C:\Windows\Temp\crvProductIds.txt | text | |
MD5:D57FBDD4D9B2D0BBACC4088E18EAF010 | SHA256:D4F290F488267D8076273CD57451947C2EAF895E6DDB28BD41F252955C236E8F | |||
| 664 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jp1r0fz3.mwv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5436 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fnp0yw1j.eas.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6112 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6112 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |