| URL: | https://yandex.ru/clck/jsredir?bu=5s0f6f&from=yandex.ru%3Bsearch%2F%3Bweb%3B%3B&text=&etext=2202.wMO5l7QvzIOLSQlWwPyJ_VpG9j7_p_Rmz4mpbi0fK2KWxrThWkRA4kGFmwV_Gd3DdXJmb3FqeXJ5emh2bGF6cw.2f925b93d33ad28d0deede090e47b0becf38b126&uuid=&state=jLT9ScZ_wbo,&&cst=AiuY0DBWFJ5fN_r-AEszk46dBy3pngvgirO--sZZQfS3ZWQhE6GHSxVqBCb9merIwLMilkNKYbi-gTyIY1byMTQ79ap8EHTBtzQ9mgLFKbPaytXU2PKWYqmZoNUQdlHN2WfZ395IPXg3ShmWoWQxIX41J8_iA9uXVuyMOifMZ-pOWQ9Kb6DRRmYNtT83v3lU8qtHDIaTVKNQaBHSmr_vwjUSciQAhn4-_7zWI5sph26zlQhooQl4sv0z1cEU6e-yqwh_o0uKWIjFxpC4vMegdgJHCfwhTvw0aSGiHU-p2e3PuHamsg6RXrbpJqnuLvVqS8vOCiQBNPPm6dRF9XvUjvaPyMzrd8WeVE1pbEhW9hTL1tCVH7IffImqu7XiI5bMQzw97cEXeA3KnP77nB83ubx5ypLO40gxP-I0eBhXyckdyTLY_doZRwHk5KU5ZjbvcsUJrUgsWDQ3990dBkgolNn1n24m9mNOdejPKlSaLzRKvZXWXQh00TU9BnWLMmTwmBlqzZq0WTp6juKeHhlFpMChw9AdWZ9dT3Tn5_Ibuw3kbagJktem4XCAJtpEm8kZq-aGDwUxRNrprPoyDsWrSzuuiiQxuOGGKsAAKxwz2IPB1fzswZXGa0dFkYTk1mFcvWBGhQRm_Ejs0qNn0qfPBdRL8m5_iSjrk5Zog5huMbWjYydcvu3fYensG1Yf1fPtG8mvI8xxxvc3Y7Vcc1ViuF69Ow8rFThMPfWHMz-7SWWJwBJzkLThJWpU3flUysB3UX6KXLaIcj2FDoPxomUq0Iu9fCO0JihVhqHPVRXuG7T0ivl3bv0c-fcQVejtLLznbm0eDfgzAiLymf7uOLeqL-a6Vs-t3UxAM37VpUHK1eOP6eU2uXVkEq6xGIhxELcFTeBIiqfoDuQwYMEecRTtySFxV8fFiSx5rYeyptzT0mHacpWKSGXQRUU9LVBgw4DuWCyhAVd4UT4QFvbYv8OLxrrYYlTuWzz7ZEfneSiw2Pf8F2WANpfPu2-B08uO8oKWvub4W9I8cYLJMSulFEc8SgW3Hrg3Z1MRBFlKf_cfDvLgNOe3c3Yc57R9YDH7ZqxT&data=UlNrNmk5WktYejY4cHFySjRXSWhXUFEtR2RWZzc4bl9WOV9KSXUwWHJzRGtGb3Ria25nZ2FHUXhsTWtnbDFPanliQmNMUG1USzN1akdnVkE1R2pCOFF1Nzg2Y1VReTFi&sign=f5f907d601389040392018937d2c5647&keyno=0&b64e=2&ref=orjY4mGPRjk5boDnW0uvlrrd71vZw9kp5QDJ4no8UYqZZbVy3V2g5DaGT_H3qRceg22YCe94Ri3vKBc56QXGilpMYDlGg5aWeky3XAWVKheUo_gVJfItS7vqeej9jw45&l10n=ru&cts=1592509090307%40%40events%3D%5B%7B%22event%22%3A%22click%22%2C%22id%22%3A%225s0f6f%22%2C%22cts%22%3A1592509090307%2C%22fast%22%3A%7B%22organic%22%3A1%7D%2C%22service%22%3A%22web%22%2C%22event-id%22%3A%22kbl6smbndm%22%7D%5D&mc=2.9219280948873623&hdtime=10189.475 |
| Full analysis: | https://app.any.run/tasks/911caa06-2c33-4115-9981-63ec619b9dce |
| Verdict: | No threats detected |
| Analysis date: | July 31, 2020, 17:26:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A75F9363F5A13B684F6EC77DAB440EA5 |
| SHA1: | 9EF94D61A480B1702758CDFE150BB3C816F0F9B0 |
| SHA256: | 235BCD21CB2E46BF5EA01CDF4619D1D32B5BB1DC09B6030FDE50AD9AB0287D82 |
| SSDEEP: | 48:qQh6O6+qB/YcD3XDxumU/N8W2L2/Ae87O1DeaqUSDZXV5TQ:h/6fdYci/Ns2/787UDhqUSD5rQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2476)
Reads Internet Cache Settings
- iexplore.exe (PID: 2476)
- iexplore.exe (PID: 852)
Changes internet zones settings
- iexplore.exe (PID: 2476)
Reads settings of System Certificates
- iexplore.exe (PID: 852)
- iexplore.exe (PID: 2476)
Creates files in the user directory
- iexplore.exe (PID: 852)
Reads internet explorer settings
- iexplore.exe (PID: 852)
Changes settings of System certificates
- iexplore.exe (PID: 2476)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 852 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2476 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Internet Explorer\iexplore.exe" https://yandex.ru/clck/jsredir?bu=5s0f6f&from=yandex.ru%3Bsearch%2F%3Bweb%3B%3B&text=&etext=2202.wMO5l7QvzIOLSQlWwPyJ_VpG9j7_p_Rmz4mpbi0fK2KWxrThWkRA4kGFmwV_Gd3DdXJmb3FqeXJ5emh2bGF6cw.2f925b93d33ad28d0deede090e47b0becf38b126&uuid=&state=jLT9ScZ_wbo,&&cst=AiuY0DBWFJ5fN_r-AEszk46dBy3pngvgirO--sZZQfS3ZWQhE6GHSxVqBCb9merIwLMilkNKYbi-gTyIY1byMTQ79ap8EHTBtzQ9mgLFKbPaytXU2PKWYqmZoNUQdlHN2WfZ395IPXg3ShmWoWQxIX41J8_iA9uXVuyMOifMZ-pOWQ9Kb6DRRmYNtT83v3lU8qtHDIaTVKNQaBHSmr_vwjUSciQAhn4-_7zWI5sph26zlQhooQl4sv0z1cEU6e-yqwh_o0uKWIjFxpC4vMegdgJHCfwhTvw0aSGiHU-p2e3PuHamsg6RXrbpJqnuLvVqS8vOCiQBNPPm6dRF9XvUjvaPyMzrd8WeVE1pbEhW9hTL1tCVH7IffImqu7XiI5bMQzw97cEXeA3KnP77nB83ubx5ypLO40gxP-I0eBhXyckdyTLY_doZRwHk5KU5ZjbvcsUJrUgsWDQ3990dBkgolNn1n24m9mNOdejPKlSaLzRKvZXWXQh00TU9BnWLMmTwmBlqzZq0WTp6juKeHhlFpMChw9AdWZ9dT3Tn5_Ibuw3kbagJktem4XCAJtpEm8kZq-aGDwUxRNrprPoyDsWrSzuuiiQxuOGGKsAAKxwz2IPB1fzswZXGa0dFkYTk1mFcvWBGhQRm_Ejs0qNn0qfPBdRL8m5_iSjrk5Zog5huMbWjYydcvu3fYensG1Yf1fPtG8mvI8xxxvc3Y7Vcc1ViuF69Ow8rFThMPfWHMz-7SWWJwBJzkLThJWpU3flUysB3UX6KXLaIcj2FDoPxomUq0Iu9fCO0JihVhqHPVRXuG7T0ivl3bv0c-fcQVejtLLznbm0eDfgzAiLymf7uOLeqL-a6Vs-t3UxAM37VpUHK1eOP6eU2uXVkEq6xGIhxELcFTeBIiqfoDuQwYMEecRTtySFxV8fFiSx5rYeyptzT0mHacpWKSGXQRUU9LVBgw4DuWCyhAVd4UT4QFvbYv8OLxrrYYlTuWzz7ZEfneSiw2Pf8F2WANpfPu2-B08uO8oKWvub4W9I8cYLJMSulFEc8SgW3Hrg3Z1MRBFlKf_cfDvLgNOe3c3Yc57R9YDH7ZqxT&data=UlNrNmk5WktYejY4cHFySjRXSWhXUFEtR2RWZzc4bl9WOV9KSXUwWHJzRGtGb3Ria25nZ2FHUXhsTWtnbDFPanliQmNMUG1USzN1akdnVkE1R2pCOFF1Nzg2Y1VReTFi&sign=f5f907d601389040392018937d2c5647&keyno=0&b64e=2&ref=orjY4mGPRjk5boDnW0uvlrrd71vZw9kp5QDJ4no8UYqZZbVy3V2g5DaGT_H3qRceg22YCe94Ri3vKBc56QXGilpMYDlGg5aWeky3XAWVKheUo_gVJfItS7vqeej9jw45&l10n=ru&cts=1592509090307%40%40events%3D%5B%7B%22event%22%3A%22click%22%2C%22id%22%3A%225s0f6f%22%2C%22cts%22%3A1592509090307%2C%22fast%22%3A%7B%22organic%22%3A1%7D%2C%22service%22%3A%22web%22%2C%22event-id%22%3A%22kbl6smbndm%22%7D%5D&mc=2.9219280948873623&hdtime=10189.475 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
611
Read events
521
Write events
88
Delete events
2
Modification events
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3638696382 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30828383 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
14
Text files
20
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6DDD.tmp | — | |
MD5:— | SHA256:— | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6DDE.tmp | — | |
MD5:— | SHA256:— | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1F4BA66CDBFEC85A20E11BF729AF23_AA85F8F9DAFF33153B5AEC2E983B94B6 | binary | |
MD5:— | SHA256:— | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\68FAF71AF355126BCA00CE2E73CC7374_77B682CF3AAC7B00161DFFF7DEA4CC8C | der | |
MD5:— | SHA256:— | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E887E036775F4159E2816B7B9E527E5F_DDB5826C150879BBC32D74AAF7683726 | der | |
MD5:— | SHA256:— | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\68FAF71AF355126BCA00CE2E73CC7374_77B682CF3AAC7B00161DFFF7DEA4CC8C | binary | |
MD5:— | SHA256:— | |||
| 2476 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB96A960F7AB6B5FC.TMP | — | |
MD5:— | SHA256:— | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E887E036775F4159E2816B7B9E527E5F_DDB5826C150879BBC32D74AAF7683726 | binary | |
MD5:— | SHA256:— | |||
| 852 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1F4BA66CDBFEC85A20E11BF729AF23_AA85F8F9DAFF33153B5AEC2E983B94B6 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
31
DNS requests
13
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
852 | iexplore.exe | GET | 200 | 5.45.205.243:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEBMzZnVqrI6OmVgYcb26HeA%3D | RU | der | 1.48 Kb | whitelisted |
852 | iexplore.exe | GET | 200 | 178.154.131.216:80 | http://yastatic.net/redir-warning/0xc64f40b/pages-desktop/redir-warning/_redir-warning.ru.js | RU | text | 18.4 Kb | whitelisted |
852 | iexplore.exe | GET | 200 | 178.154.131.216:80 | http://yastatic.net/lego/_/q9XD86YnfACFg65-9S7vKFNK9iE.png | RU | image | 5.86 Kb | whitelisted |
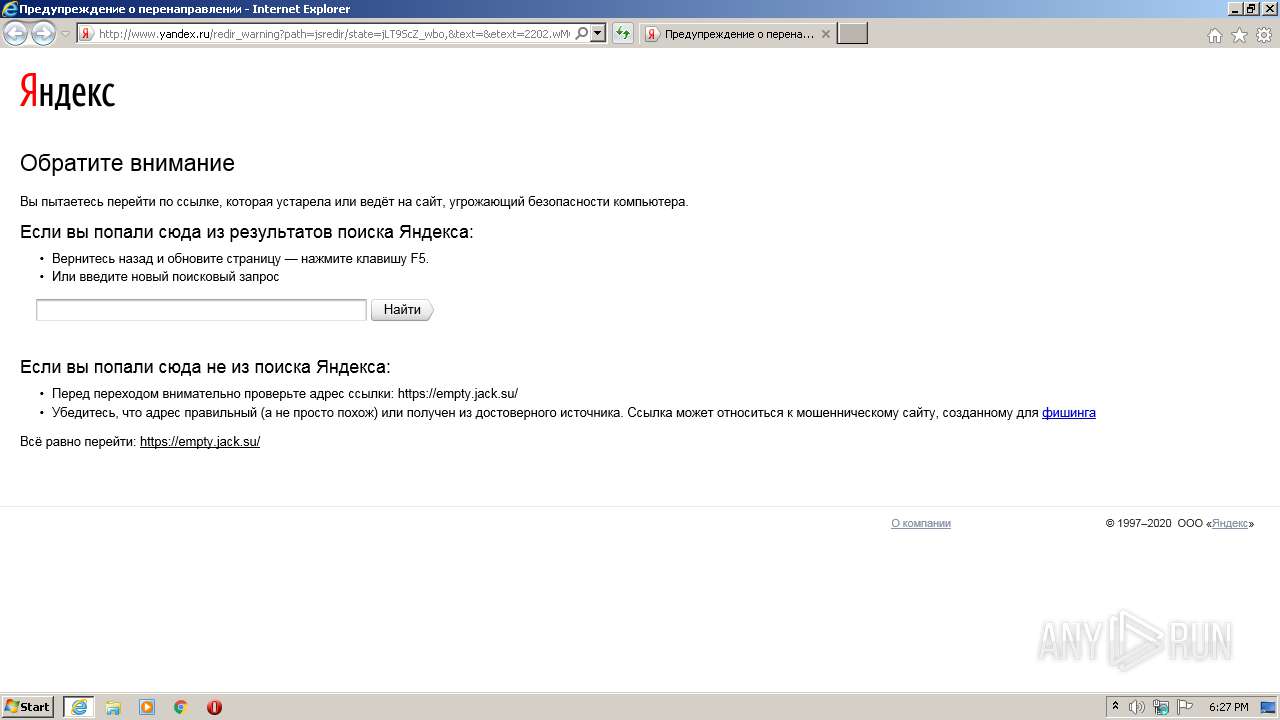
852 | iexplore.exe | GET | 200 | 5.255.255.50:80 | http://yandex.ru/clck/jsredir?from=yandex.ru%3Bsearch%2F%3Bweb%3B%3B&text=&etext=&uuid=&state=jLT9ScZ_wbo,&data=UlNrNmk5WktYejY4cHFySjRXSWhXUFEtR2RWZzc4bl9WOV9KSXUwWHJzRGtGb3Ria25nZ2FGT183anNsd2xtODR2dDdsdWNQVnBEaV9FMTZHc1NuRmZHdTU1TEVfcmd1&sign=67cd14b5ff0d5f39865e6b96dcecaf5d&keyno=0&b64e=2&l10n=ru&ref=https%3A%2F%2Fyandex.ru%2Fsearch%2F%3Ftext%3Dhttp%253A%252F%252Fempty.jack.su%253A%253A61337%26clid%3D2270455%26win%3D429%26lr%3D2 | RU | html | 473 b | whitelisted |
2476 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
852 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.58 Kb | whitelisted |
852 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkBUeDDgxkUpdvejVJwN1I | US | der | 1.63 Kb | whitelisted |
852 | iexplore.exe | GET | 200 | 178.154.131.216:80 | http://yastatic.net/redir-warning/_/x3J2-cVeS1IgBVl1pmLcdJfT4Dg.png | RU | image | 7.18 Kb | whitelisted |
852 | iexplore.exe | GET | 200 | 178.154.131.216:80 | http://yastatic.net/jquery/1.6.2/jquery.min.js | RU | html | 30.1 Kb | whitelisted |
852 | iexplore.exe | GET | 200 | 178.154.131.216:80 | http://yastatic.net/lego/_/La6qi18Z8LwgnZdsAr1qy1GwCwo.gif | RU | image | 43 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
852 | iexplore.exe | 5.255.255.50:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
852 | iexplore.exe | 151.139.236.246:80 | subca.ocsp-certum.com | netDNA | US | unknown |
852 | iexplore.exe | 5.45.205.243:80 | yandex.ocsp-responder.com | YANDEX LLC | RU | whitelisted |
852 | iexplore.exe | 5.255.255.55:80 | yandex.ru | YANDEX LLC | RU | whitelisted |
— | — | 178.154.131.216:80 | yastatic.net | YANDEX LLC | RU | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
852 | iexplore.exe | 5.255.255.50:80 | yandex.ru | YANDEX LLC | RU | whitelisted |
— | — | 185.186.247.40:443 | empty.jack.su | — | NL | suspicious |
852 | iexplore.exe | 185.186.247.40:443 | empty.jack.su | — | NL | suspicious |
2476 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yandex.ru |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
yandex.ocsp-responder.com |
| whitelisted |
www.yandex.ru |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
yastatic.net |
| whitelisted |
empty.jack.su |
| suspicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
852 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
852 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
852 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |