| download: | index.html |
| Full analysis: | https://app.any.run/tasks/1846eee5-ef1c-4a4b-b7d3-b92186f97bd2 |
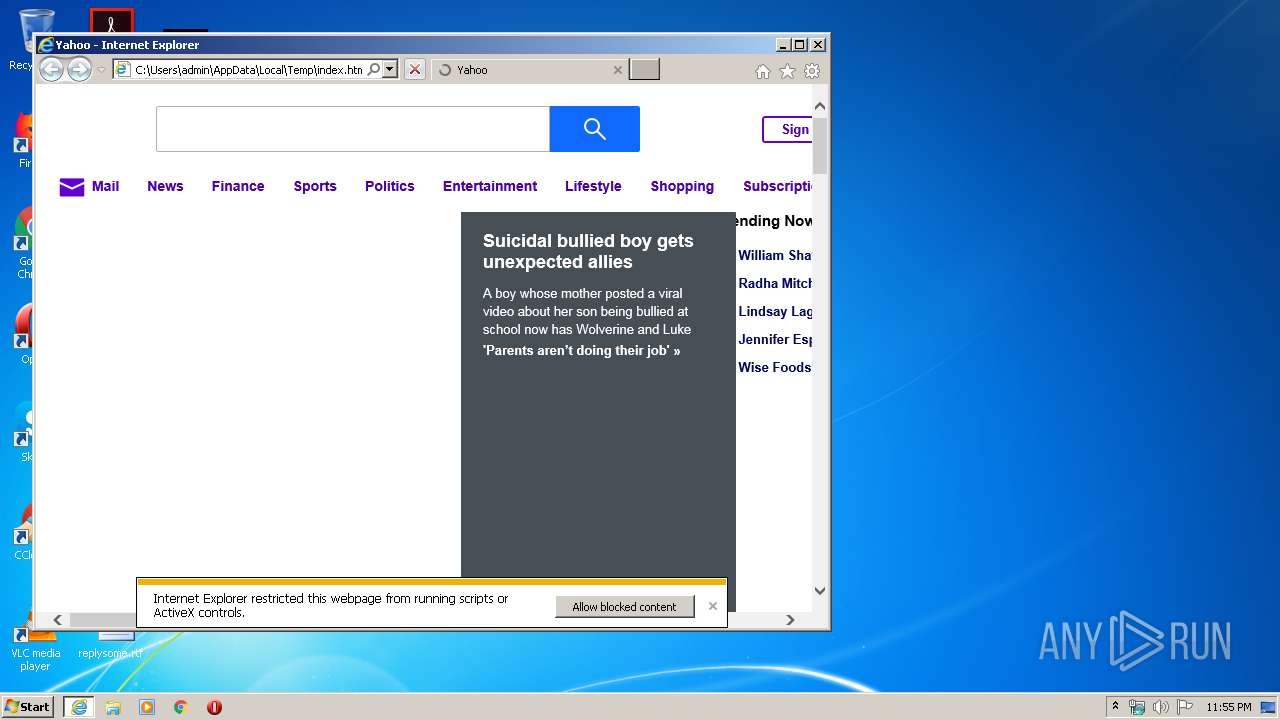
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 23:55:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | CF8B30771E395A6D9BD51EB388ABA44D |
| SHA1: | 6926F0B70C6F5CDBC38FDBEAE587085DE84C1371 |
| SHA256: | 235A461A4DB29EB5FA298F44F8195376AF32B034F8CB03E98A49A00F517D6C90 |
| SSDEEP: | 6144:MA5eZ6dw8WNt/iOhPcWpdQa4dqJ/eqaJo45w:H5eZNNtv2qJ+5w |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2864)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3924)
Reads internet explorer settings
- iexplore.exe (PID: 2944)
Manual execution by user
- chrome.exe (PID: 2864)
Changes internet zones settings
- iexplore.exe (PID: 3924)
Application launched itself
- iexplore.exe (PID: 3924)
- chrome.exe (PID: 2864)
Reads the hosts file
- chrome.exe (PID: 2864)
- chrome.exe (PID: 2708)
Reads settings of System Certificates
- chrome.exe (PID: 2708)
- iexplore.exe (PID: 2944)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2944)
Changes settings of System certificates
- iexplore.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .aiml | | | Artificial Intelligence Markup Language (48.3) |
|---|---|---|
| .htm/html | | | HyperText Markup Language with DOCTYPE (41.6) |
| .html | | | HyperText Markup Language (9.9) |
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| Title: | Yahoo |
| HTTPEquivXDnsPrefetchControl: | on |
| ContentType: | text/html; charset=utf-8 |
| viewport: | width=device-width, initial-scale=1.0 |
| msapplicationNavbuttonColor: | red |
| msapplicationTileColor: | #ffffff |
| msapplicationTileImage: | https://s.yimg.com/cv/apiv2/social/images/yahoo_default_logo.png |
| applicationName: | Yahoo |
| msapplicationTapHighlight: | no |
| fullScreen: | yes |
| browsermode: | application |
| nightmode: | disable |
| layoutmode: | fitscreen |
| imagemode: | force |
| Description: | News, email and search are just the beginning. Discover more every day. Find your yodel. |
| Keywords: | yahoo, yahoo home page, yahoo homepage, yahoo search, yahoo mail, yahoo messenger, yahoo games, news, finance, sport, entertainment |
| formatDetection: | telephone=no |
| themeColor: | #400090 |
| referrer: | unsafe-url |
| oathGuceConsentHost: | guce.yahoo.com |
Total processes
72
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14121556739902761417 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2491433222614076531 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15285419299193688666 --mojo-platform-channel-handle=2984 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6078734484785152232 --mojo-platform-channel-handle=4388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4410191169000891381 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=563081458336406382 --mojo-platform-channel-handle=2208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17571795265695614014 --mojo-platform-channel-handle=3396 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13726639618378628449 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15419711338927812043 --mojo-platform-channel-handle=3048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,7273398566510923877,17763040525713715282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16862922409345435186 --mojo-platform-channel-handle=2472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 274
Read events
1 694
Write events
1 760
Delete events
820
Modification events
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1930830450 | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796050 | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
26
Text files
268
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3F706D53834D4FDF.TMP | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC41E657ADC721A97.TMP | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF88AE9A130D5E0A41.TMP | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{9ED2BD33-5505-11EA-972D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8676F2B2453D2666.TMP | — | |
MD5:— | SHA256:— | |||
| 3924 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{9ED2BD31-5505-11EA-972D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E506DF3-B30.pma | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bfdf8058-2f9d-40ba-990b-2ea47b22a2e4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
55
DNS requests
32
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
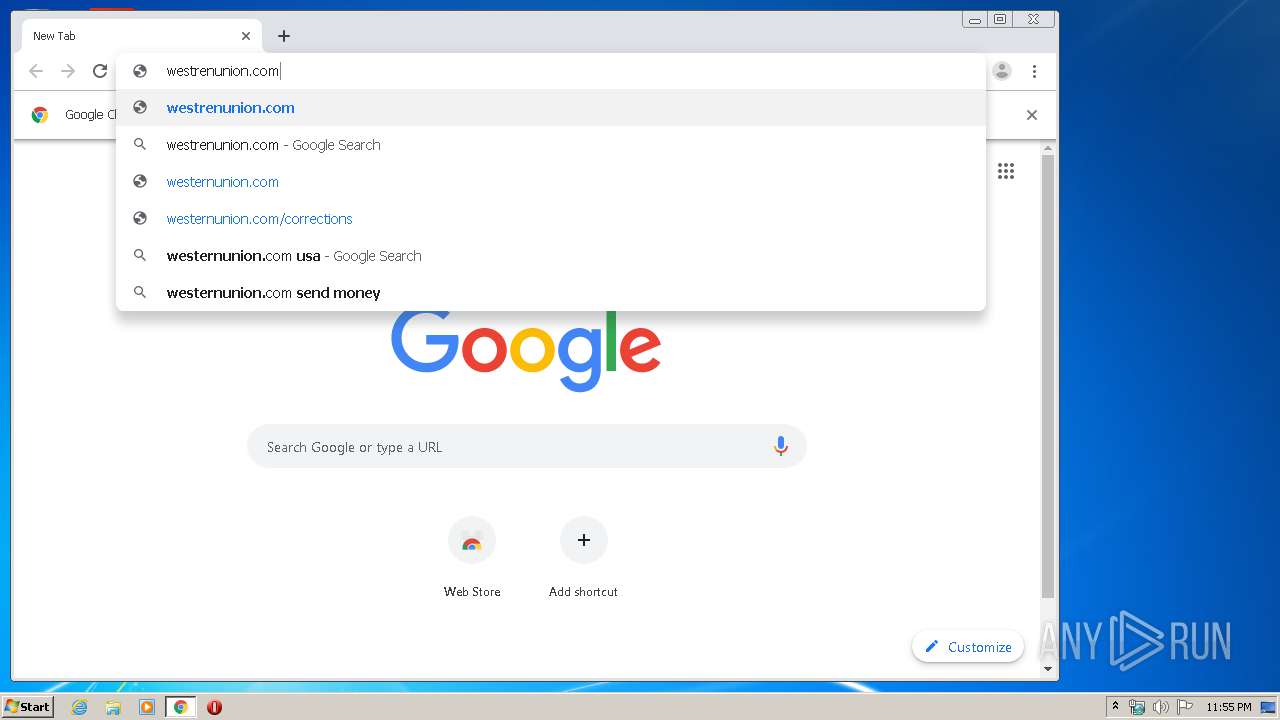
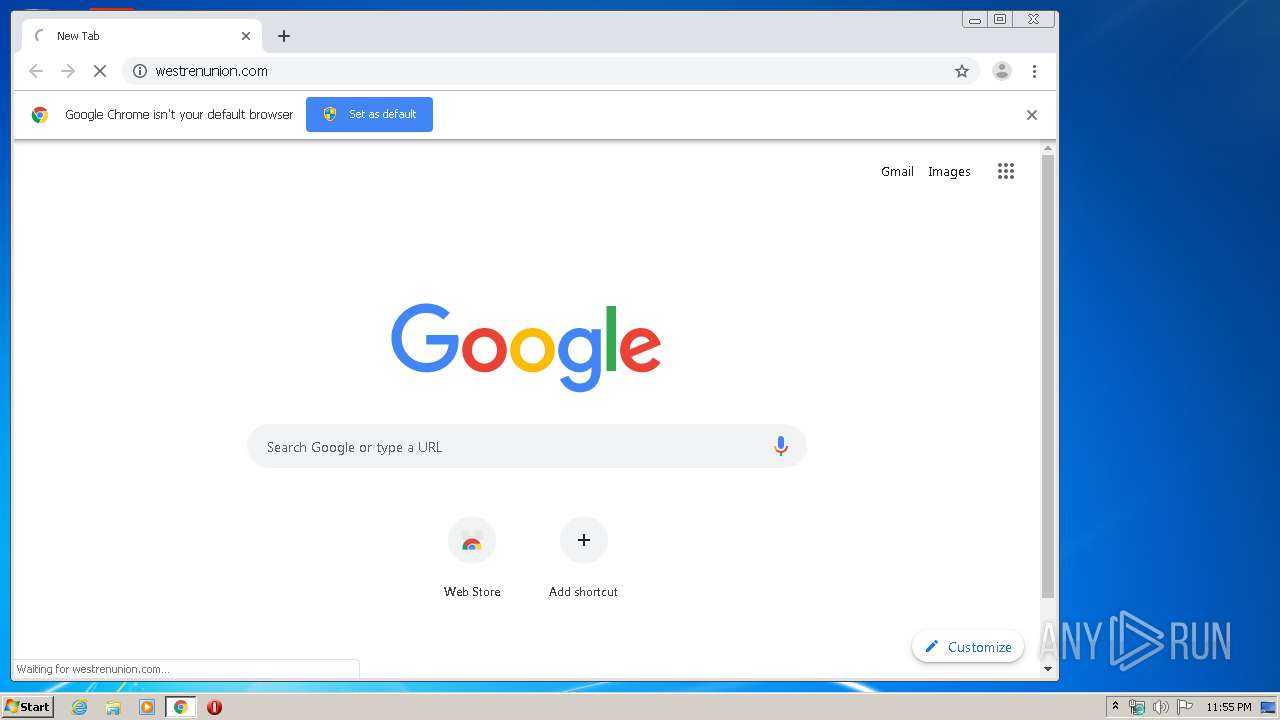
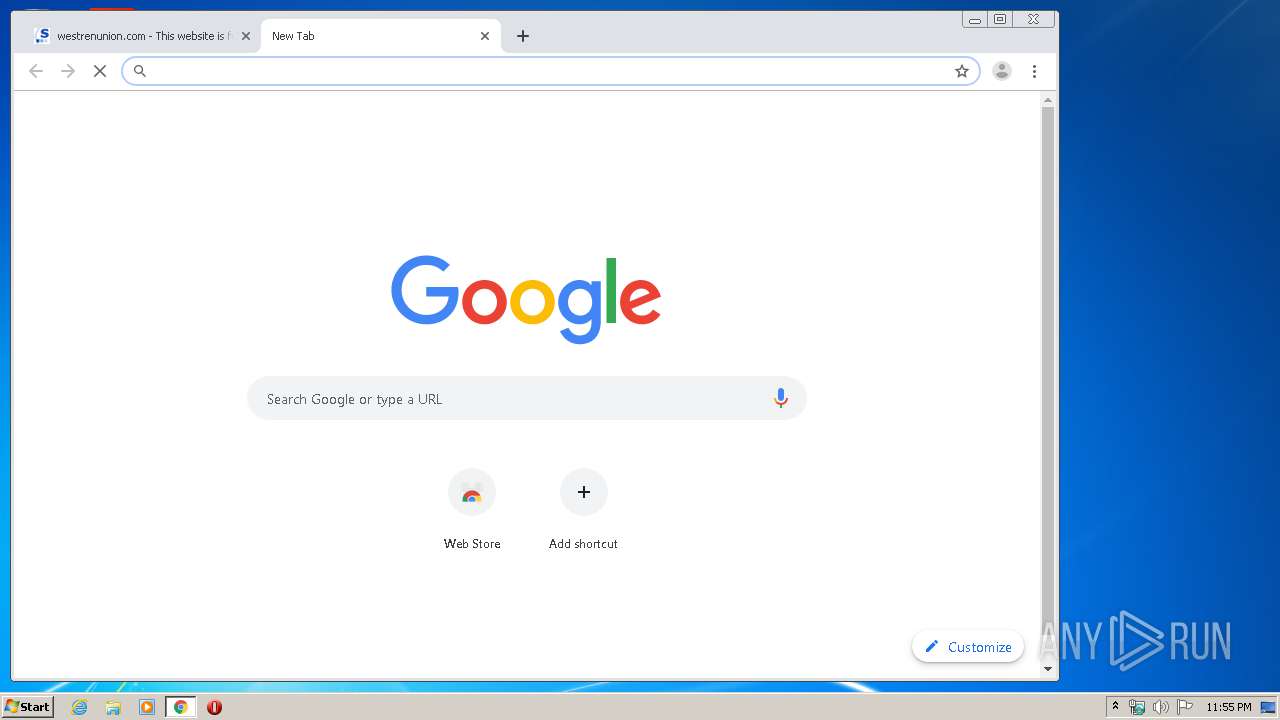
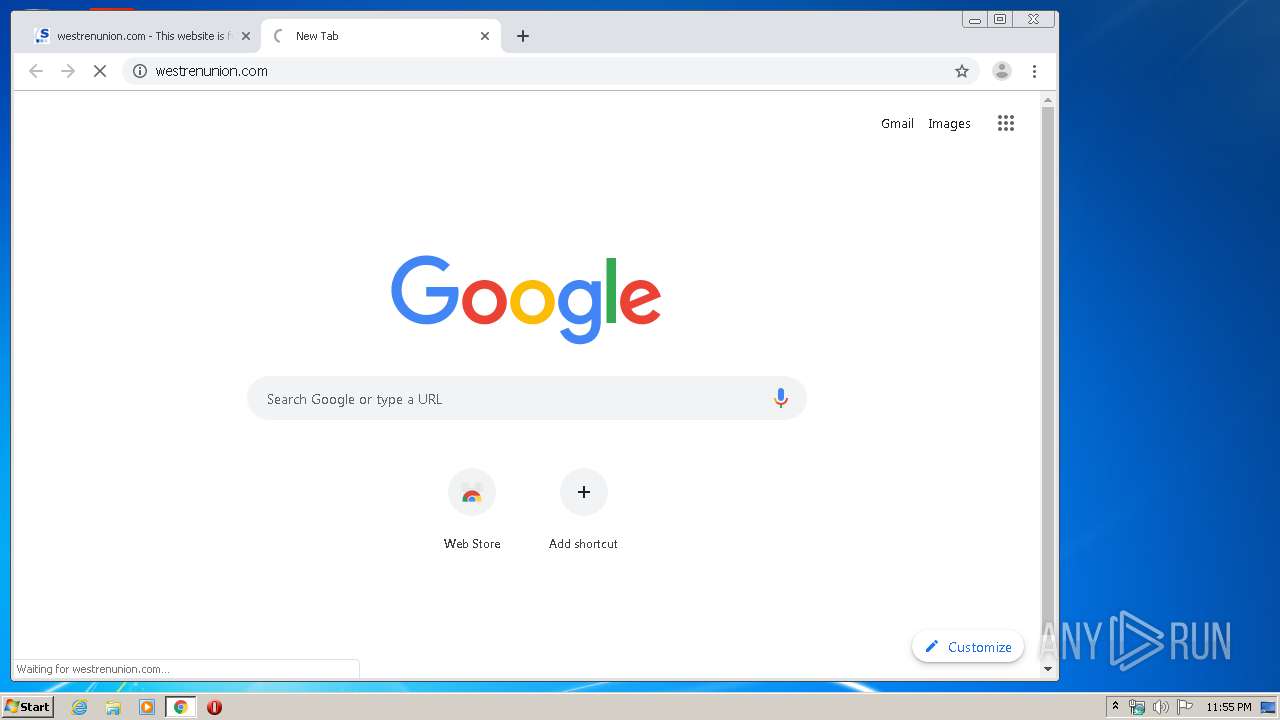
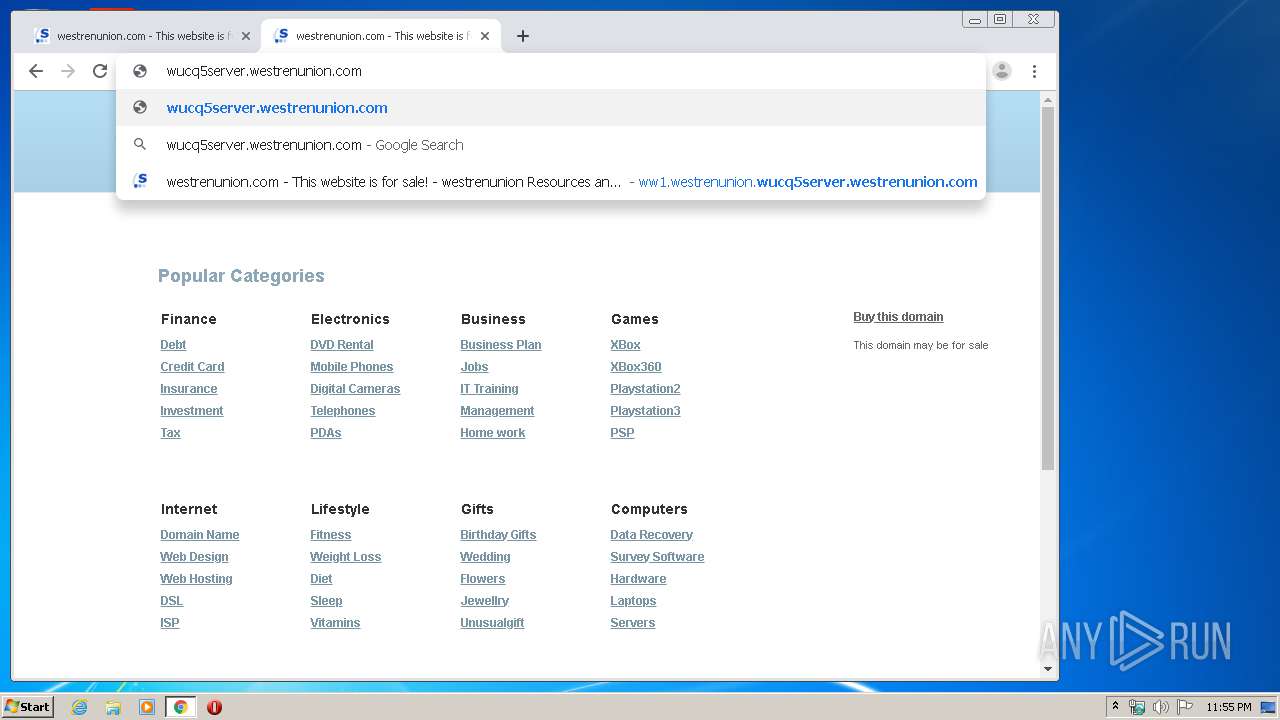
2708 | chrome.exe | GET | 302 | 103.224.182.239:80 | http://westrenunion.com/ | AU | — | — | malicious |
2708 | chrome.exe | GET | 302 | 103.224.182.239:80 | http://westrenunion.com/ | AU | — | — | malicious |
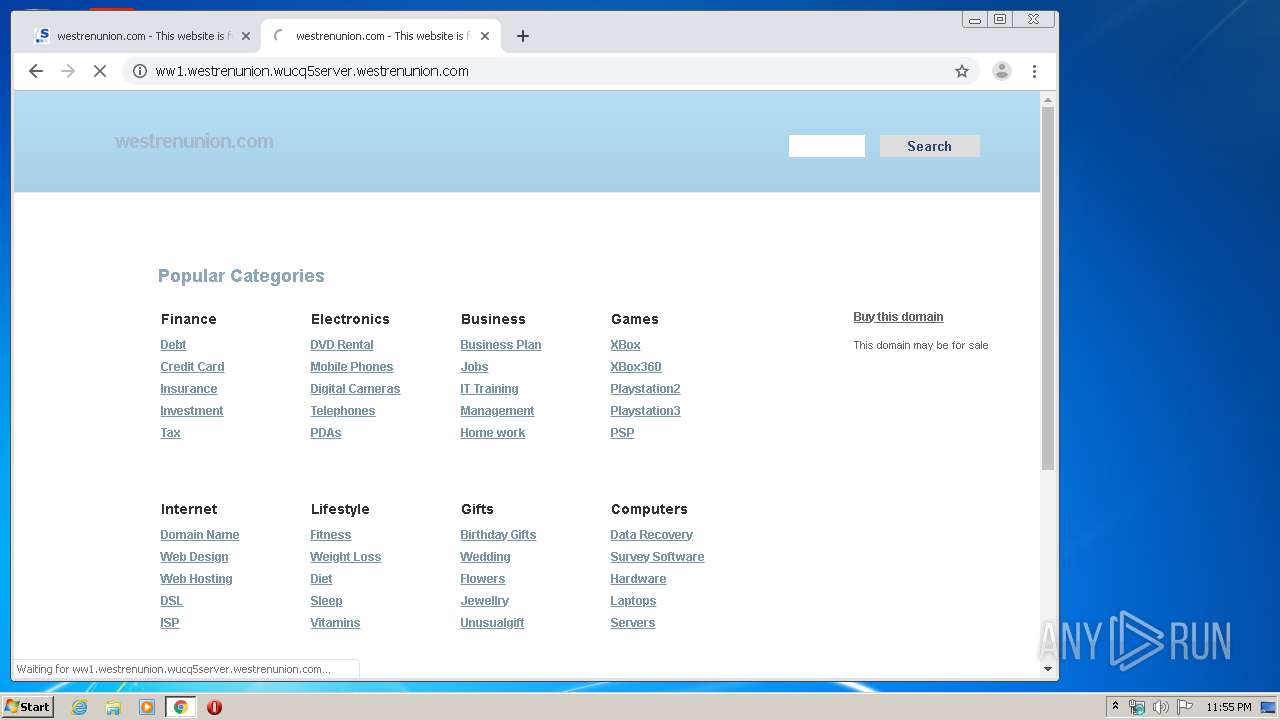
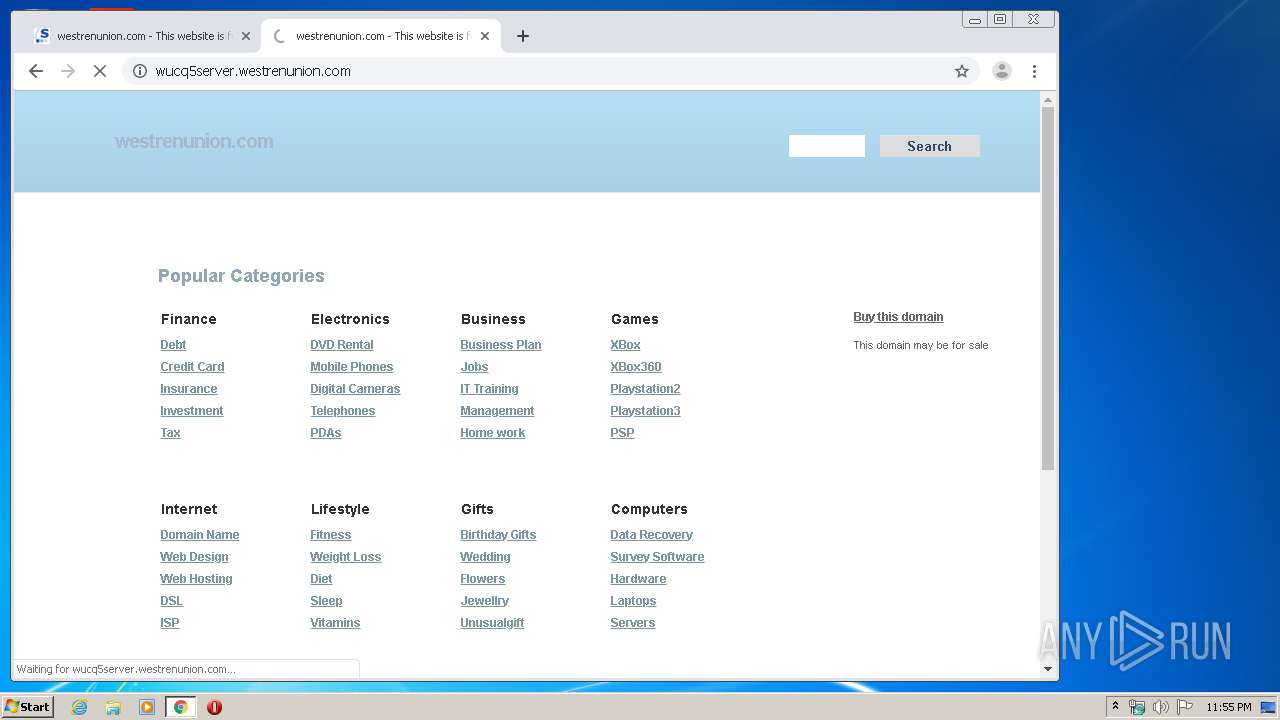
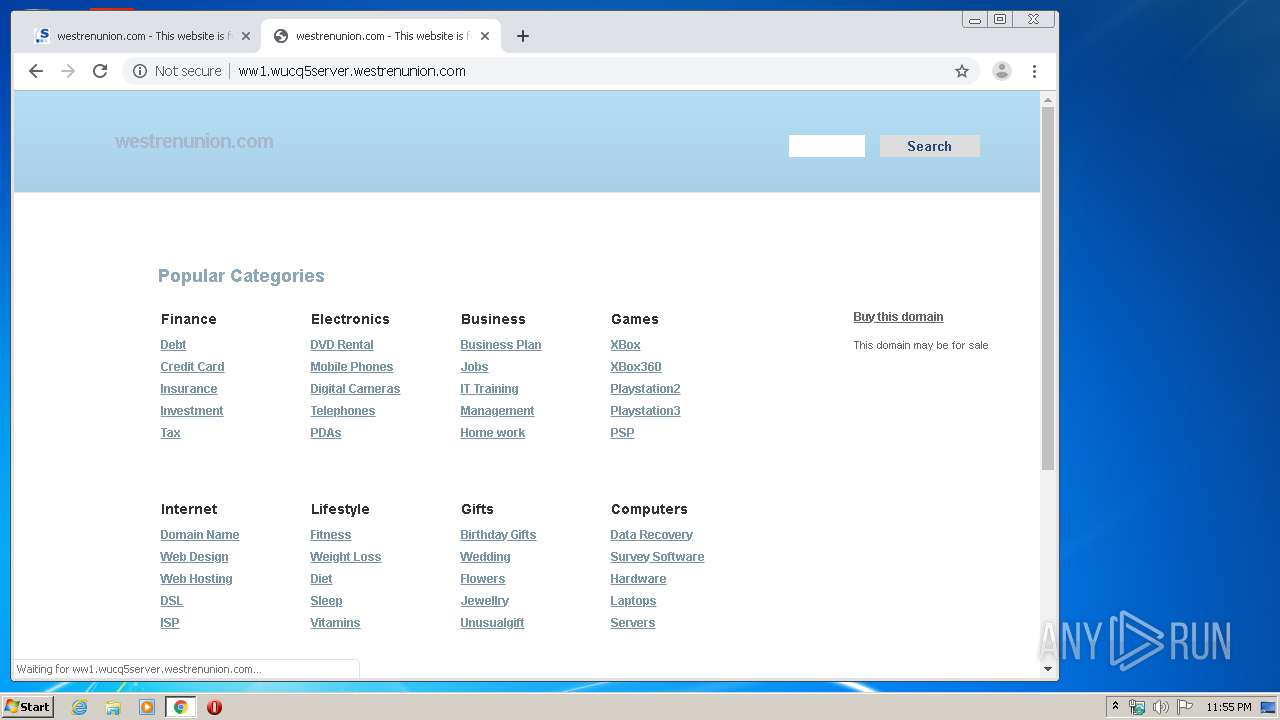
2708 | chrome.exe | GET | 200 | 91.195.240.96:80 | http://ww1.westrenunion.wucq5server.westrenunion.com/search/tsc.php?200=MzEzOTU1MjM0&21=ODUuMjA2LjE2Ni44Mg==&681=MTU4MjMyOTM0N2MzOTI3MzU1MmIxOTk0ZTk4YjQ2MWFhZGM2ZjRkYjBm&crc=1494589e2e35cd24501c7c7aefbebde4e601e408&cv=1 | DE | — | — | unknown |
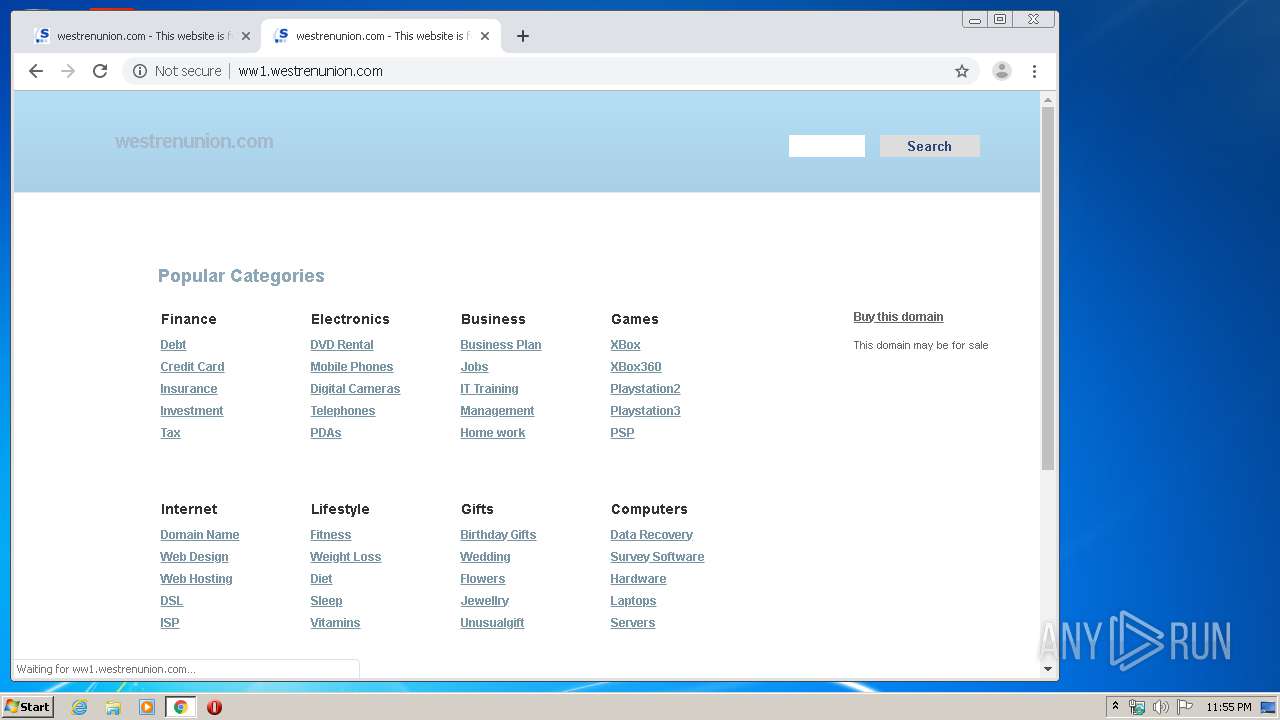
2708 | chrome.exe | GET | 302 | 103.224.182.239:80 | http://wucq5server.westrenunion.com/ | AU | — | — | malicious |
2708 | chrome.exe | GET | 200 | 91.195.240.96:80 | http://ww1.wucq5server.westrenunion.com/search/tsc.php?200=MzEzOTU1MjM0&21=ODUuMjA2LjE2Ni44Mg==&681=MTU4MjMyOTM1MWQ1NGI3ODBkMzBiMjM0OTJmNTc2MWIyNDkxOGFiYjI0&crc=24e1a85f9336d162544f450495512d249e7e4b25&cv=1 | DE | — | — | unknown |
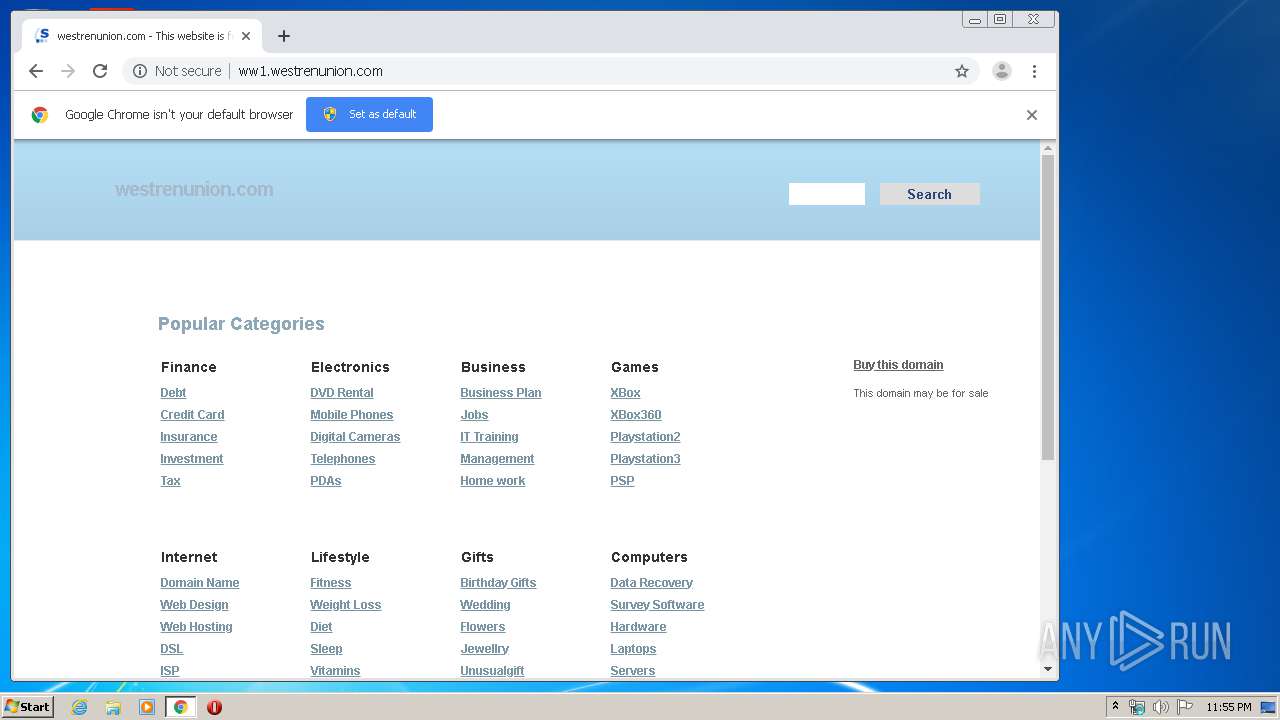
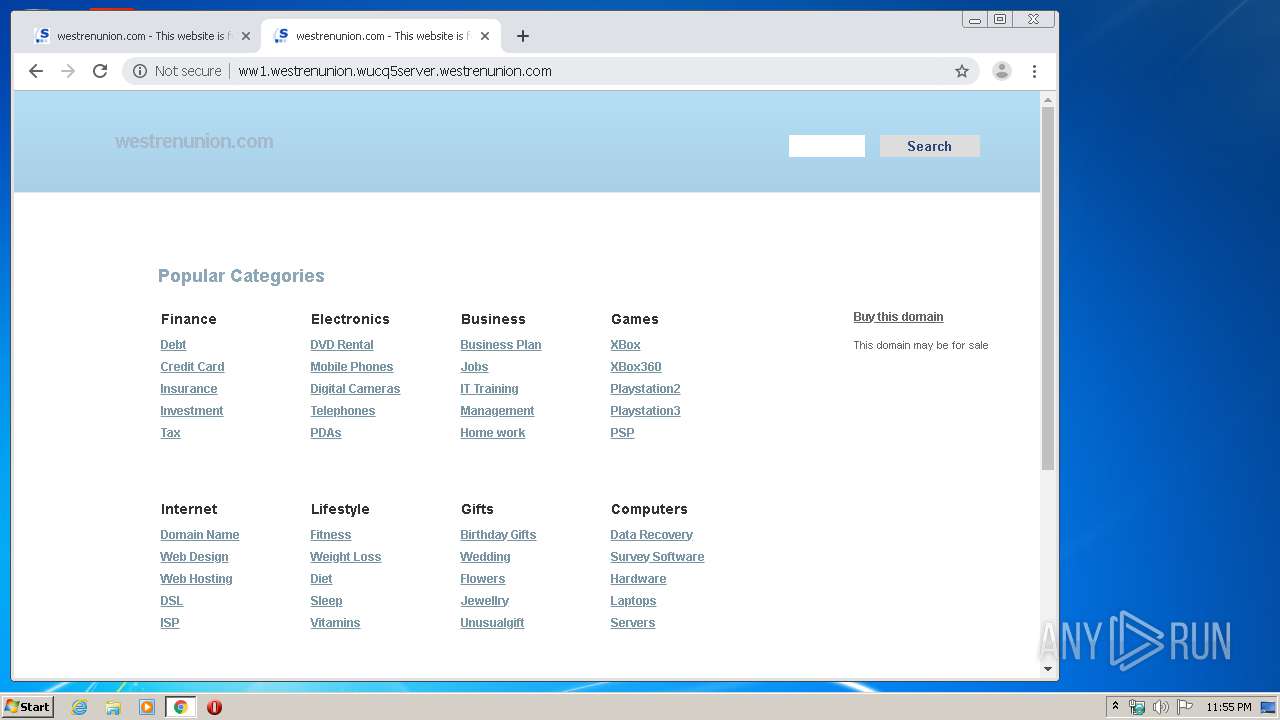
2708 | chrome.exe | GET | 200 | 91.195.240.96:80 | http://ww1.westrenunion.com/ | DE | html | 21.3 Kb | unknown |
2708 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 536 b | whitelisted |
2708 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 515 b | whitelisted |
2708 | chrome.exe | GET | 200 | 91.195.240.96:80 | http://ww1.westrenunion.com/ | DE | html | 21.2 Kb | unknown |
2708 | chrome.exe | GET | 200 | 91.195.240.96:80 | http://ww1.westrenunion.com/search/portal.php?l=OAllZjYxZDJkMTAzYTdmNDM5MWZjZjQxM2U5MDZhZDUwZAkJMzAJMAkJMzEzOTU1MjM0CXdlc3RyZW51bmlvbgkyMDQzCQkyMAkyNQkxNTgyMzI5MzM3CTAJTgkwCTEJMAkxMjA1CTc5OTA4NTAyCTg1LjIwNi4xNjYuODIJMA%3D%3D | DE | text | 1.20 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | iexplore.exe | 87.248.118.22:443 | s.yimg.com | Yahoo! UK Services Limited | GB | shared |
2944 | iexplore.exe | 152.199.21.71:443 | us.y.atwola.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | unknown |
2944 | iexplore.exe | 104.111.214.103:443 | sb.scorecardresearch.com | Akamai International B.V. | NL | whitelisted |
3924 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2708 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2708 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2708 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2708 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2708 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2708 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s.yimg.com |
| shared |
us.y.atwola.com |
| whitelisted |
sb.scorecardresearch.com |
| shared |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2708 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2708 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |