| File name: | 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f |
| Full analysis: | https://app.any.run/tasks/56718718-5169-47fb-bc7c-8630485b117f |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2025, 20:59:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 27A87C77151AB7A48A883C8B56D2B46B |
| SHA1: | 524DBC873FC62B34E2CCA4CD713B20DC211927F5 |
| SHA256: | 2346701C8FF4761C434D1993500FE46BD983D5D26BDC88A689213F97BC7CA41F |
| SSDEEP: | 6144:05444EcVgVwVqVJPV7DgVydV0bcJx7c//bV9BCc0bmuSYjnjbSfj6jqiGO4P:c444EcVgVwVqVJPV/gVOVQc2PiGR |
MALICIOUS
VOBFUS mutex has been found
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
- beimis.exe (PID: 6540)
Changes the autorun value in the registry
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
- beimis.exe (PID: 6540)
VOBFUS has been detected
- beimis.exe (PID: 6540)
SUSPICIOUS
Executable content was dropped or overwritten
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
Reads security settings of Internet Explorer
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
INFO
The sample compiled with english language support
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
Reads the computer name
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
- beimis.exe (PID: 6540)
Process checks computer location settings
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
Checks supported languages
- 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe (PID: 6988)
- beimis.exe (PID: 6540)
Checks proxy server information
- slui.exe (PID: 3156)
Reads the software policy settings
- slui.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:11:15 06:55:43+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 200704 |
| InitializedDataSize: | 24576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3c60 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| ProductName: | - |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | - |
| OriginalFileName: | - |
Total processes
125
Monitored processes
3
Malicious processes
2
Suspicious processes
0
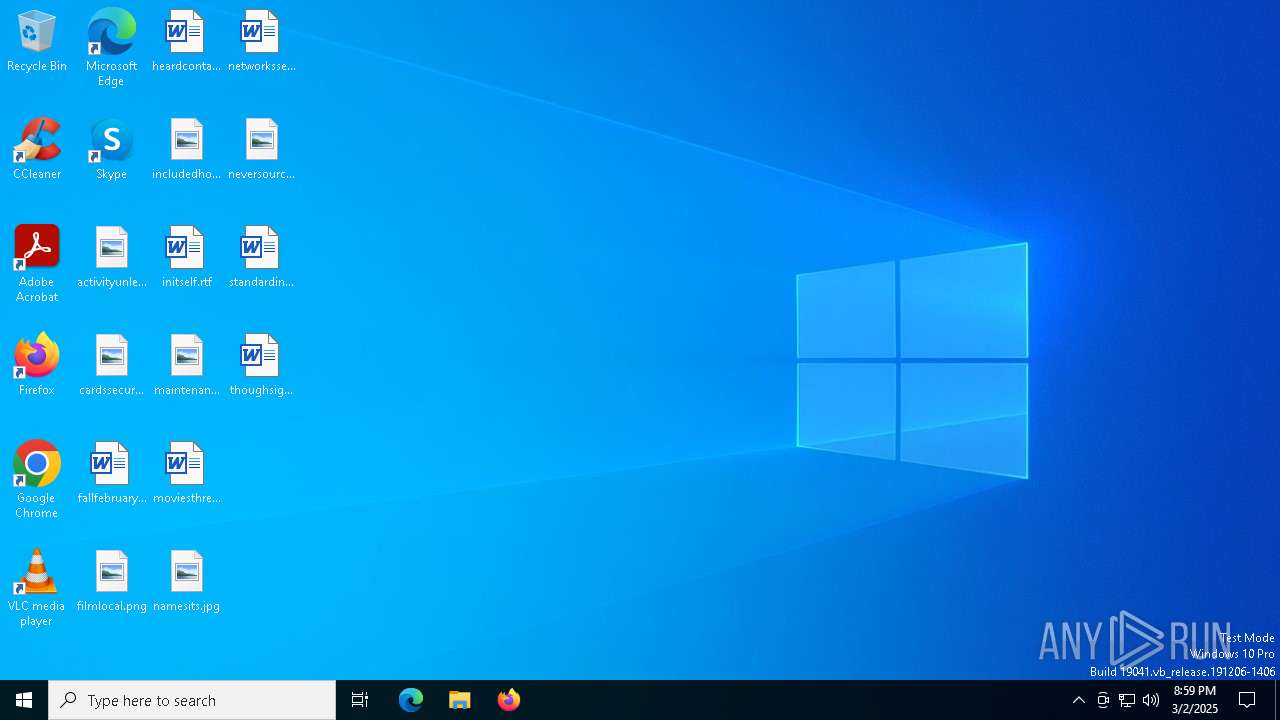
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3156 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6540 | "C:\Users\admin\beimis.exe" | C:\Users\admin\beimis.exe | 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6988 | "C:\Users\admin\Desktop\2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe" | C:\Users\admin\Desktop\2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
4 239
Read events
4 018
Write events
221
Delete events
0
Modification events
| (PID) Process: | (6988) 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6988) 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /i | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /v | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /z | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /y | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /s | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /I | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /D | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /p | |||
| (PID) Process: | (6540) beimis.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | beimis |
Value: C:\Users\admin\beimis.exe /r | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6988 | 2346701c8ff4761c434d1993500fe46bd983d5d26bdc88a689213f97bc7ca41f.exe | C:\Users\admin\beimis.exe | executable | |
MD5:C9954A8C0CECA3A855003337814F9747 | SHA256:CE39A15C3119060C0A018C4B76E6203BFEDC51CEEC6384FC4A1BF5683AEAED5A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
21
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
896 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3156 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ns1.player1352.com |
| malicious |
ns1.player1352.net |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |