| URL: | http://schemas.microsoft.com/ |
| Full analysis: | https://app.any.run/tasks/e5490e66-ab48-44c4-b23f-358877ef7dd4 |
| Verdict: | Malicious activity |
| Analysis date: | September 26, 2023, 02:21:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6C366A647D6E2841716D9F3627C02A68 |
| SHA1: | 6B8C2E71D10288DDE9858CD607576C7D6D7D0D7B |
| SHA256: | 23463198A22F9A0F4197B991BE93D6018EDE89B70E259B5B264D4D038AB7B527 |
| SSDEEP: | 3:N1KNGzE+tRn:CUA+Dn |
MALICIOUS
Application was injected by another process
- svchost.exe (PID: 868)
- svchost.exe (PID: 1088)
- SearchIndexer.exe (PID: 2172)
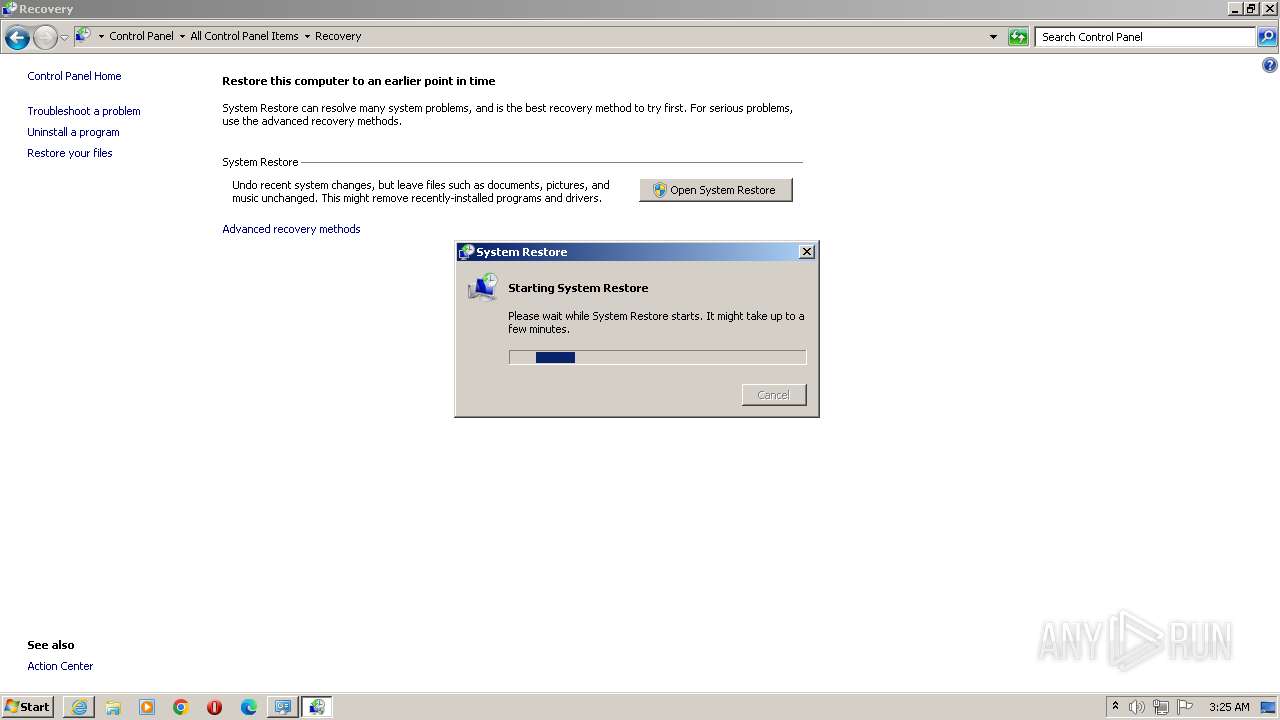
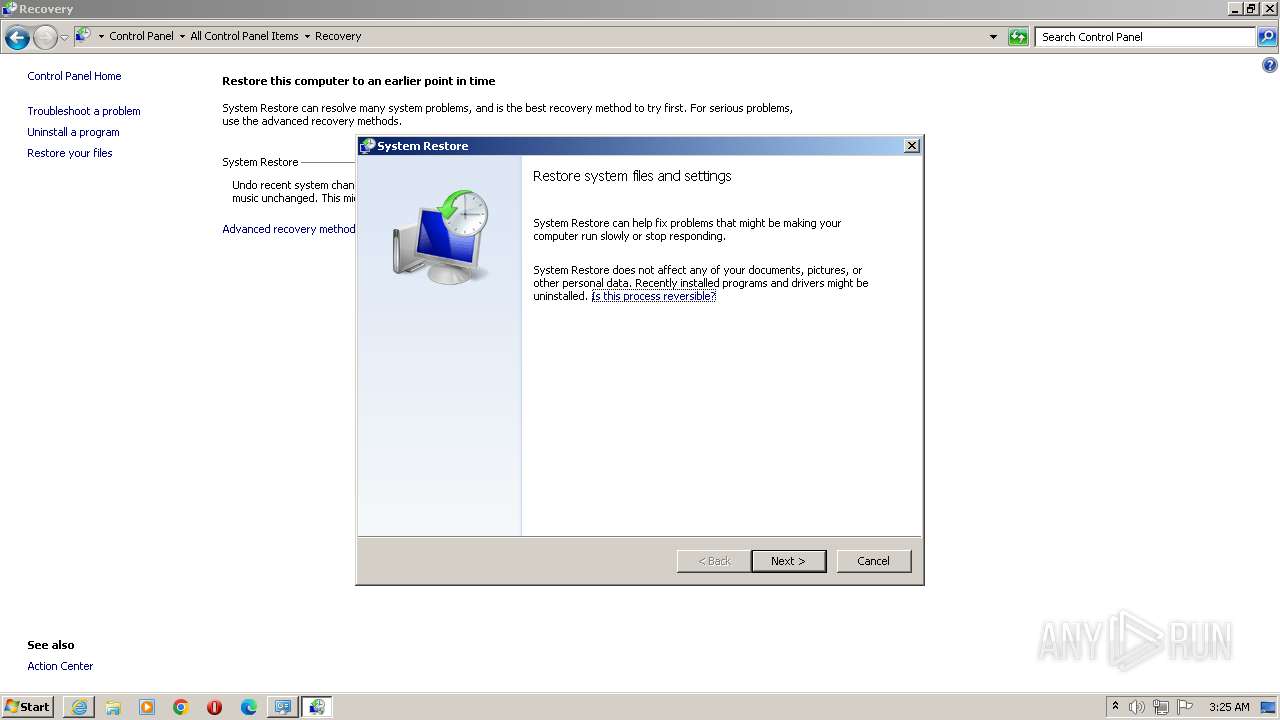
Runs injected code in another process
- rstrui.exe (PID: 1664)
SUSPICIOUS
Reads settings of System Certificates
- msdt.exe (PID: 3492)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 372)
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 372)
Reads the Internet Settings
- sdiagnhost.exe (PID: 372)
- msdt.exe (PID: 3492)
- rundll32.exe (PID: 124)
Executes as Windows Service
- wbengine.exe (PID: 1040)
- VSSVC.exe (PID: 3720)
- vds.exe (PID: 2100)
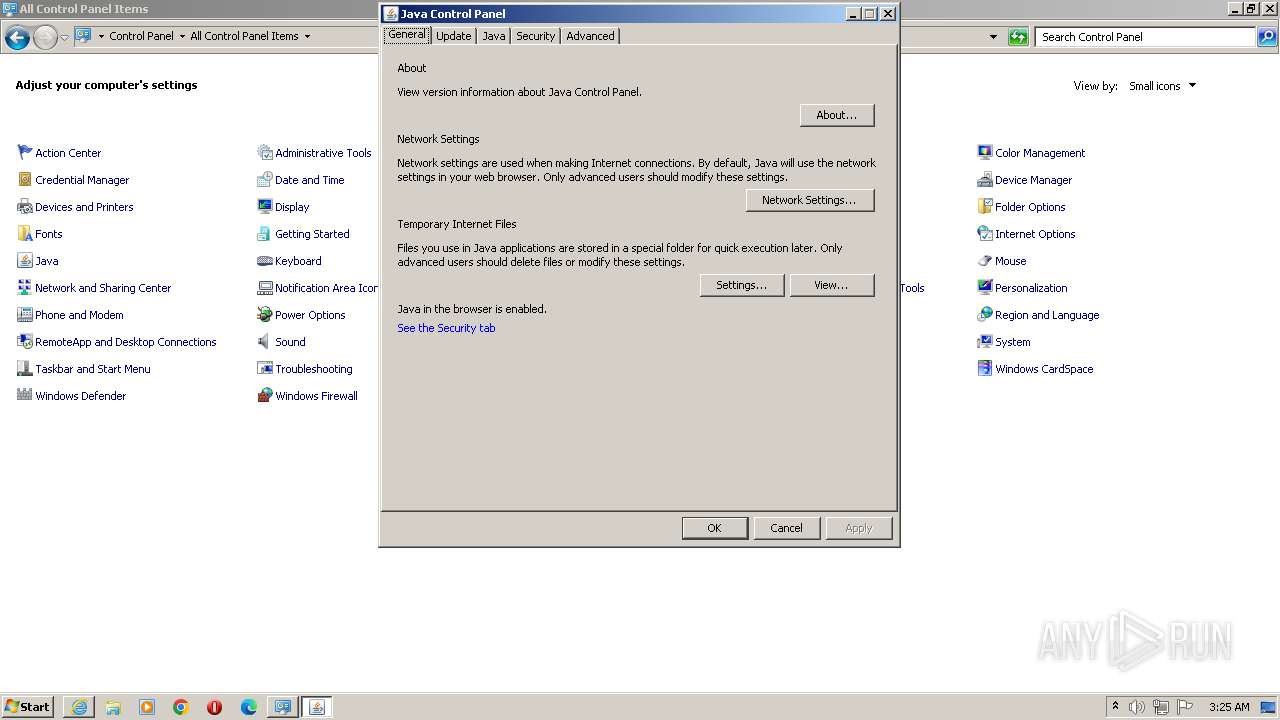
Checks for Java to be installed
- javaw.exe (PID: 4060)
- jucheck.exe (PID: 2000)
- jucheck.exe (PID: 3644)
- jucheck.exe (PID: 2972)
Reads Mozilla Firefox installation path
- javaw.exe (PID: 4060)
INFO
Application launched itself
- iexplore.exe (PID: 2968)
Reads security settings of Internet Explorer
- sdiagnhost.exe (PID: 372)
- msdt.exe (PID: 3492)
Create files in a temporary directory
- sdiagnhost.exe (PID: 372)
- makecab.exe (PID: 1444)
- msdt.exe (PID: 3492)
- jucheck.exe (PID: 2000)
- javaw.exe (PID: 4060)
Creates files or folders in the user directory
- msdt.exe (PID: 3492)
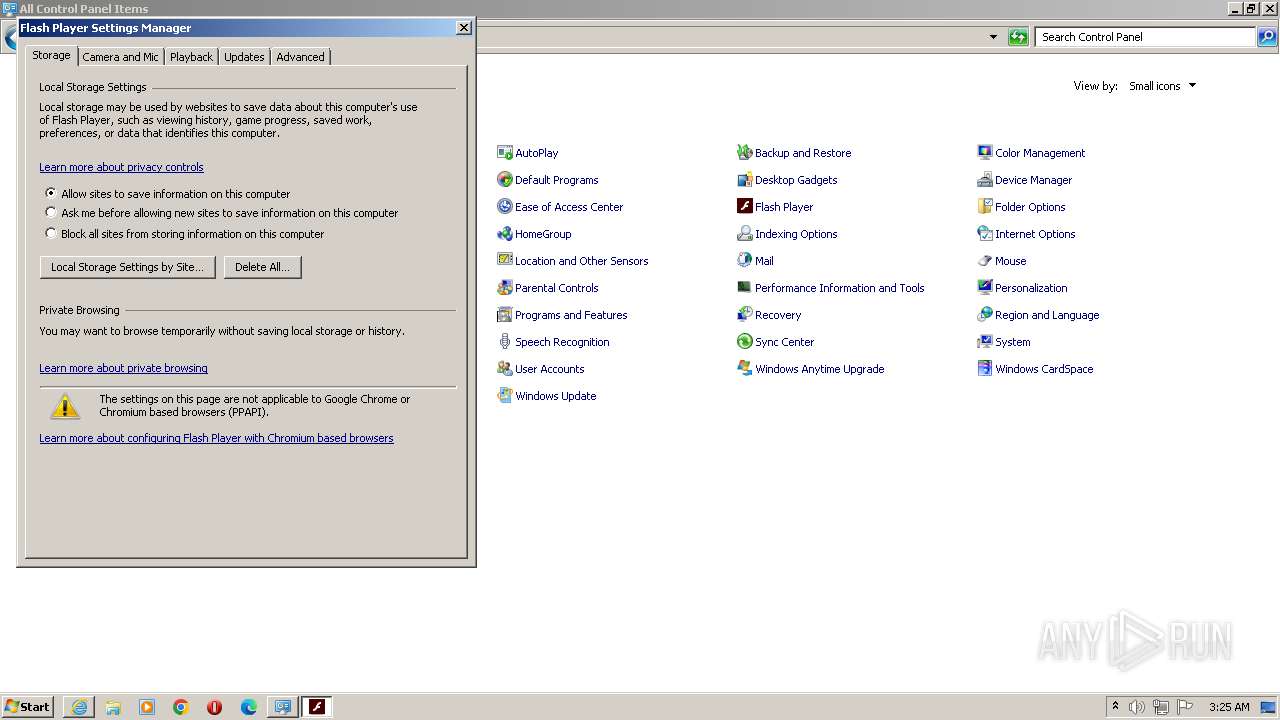
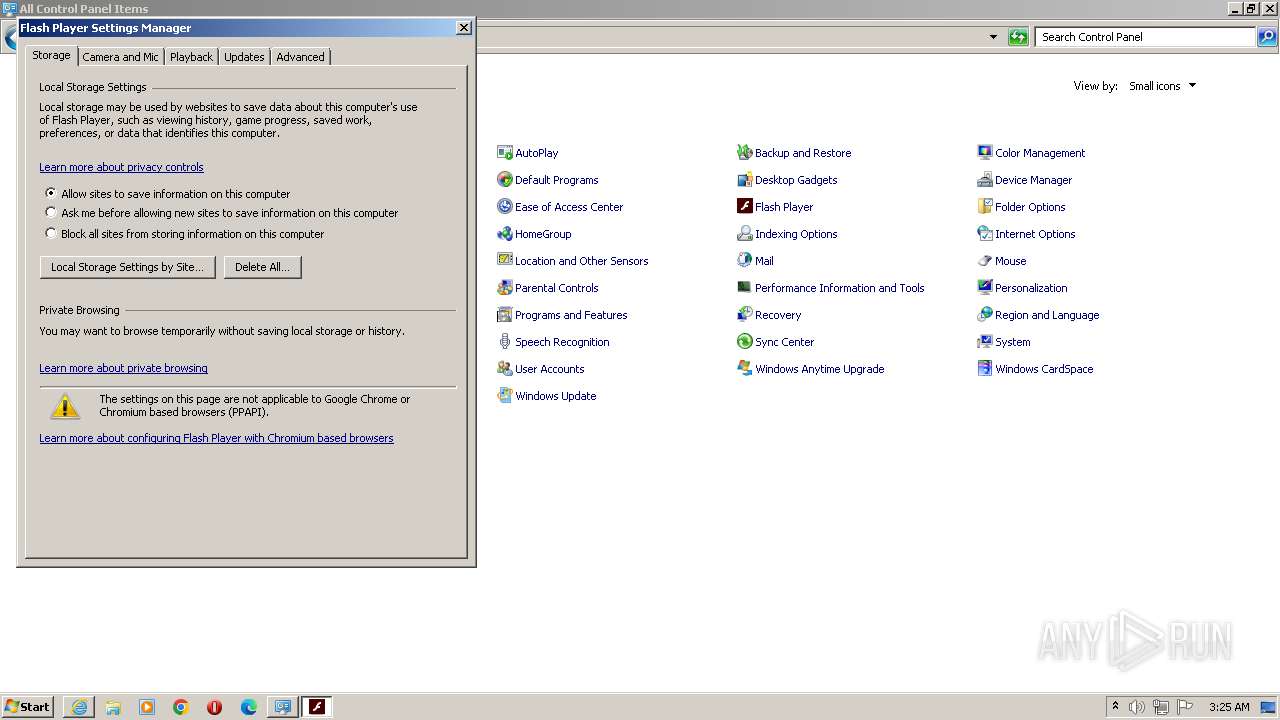
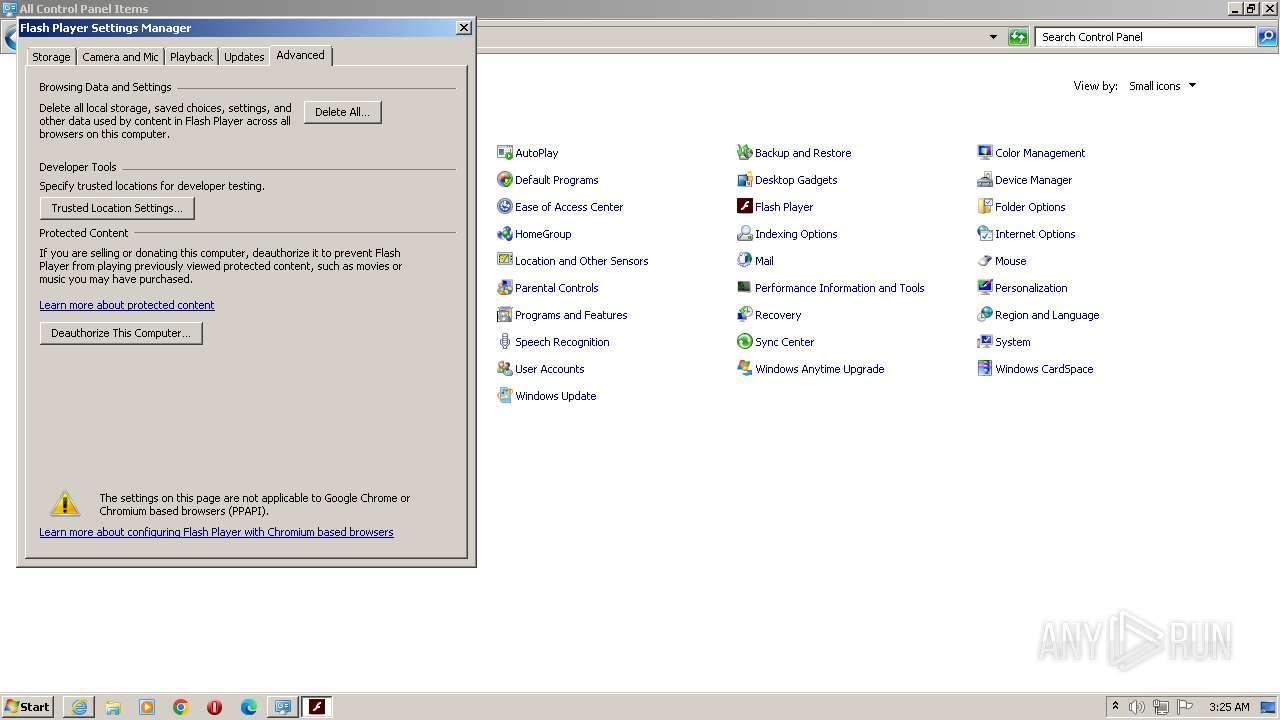
- FlashPlayerApp.exe (PID: 3332)
- javaw.exe (PID: 4060)
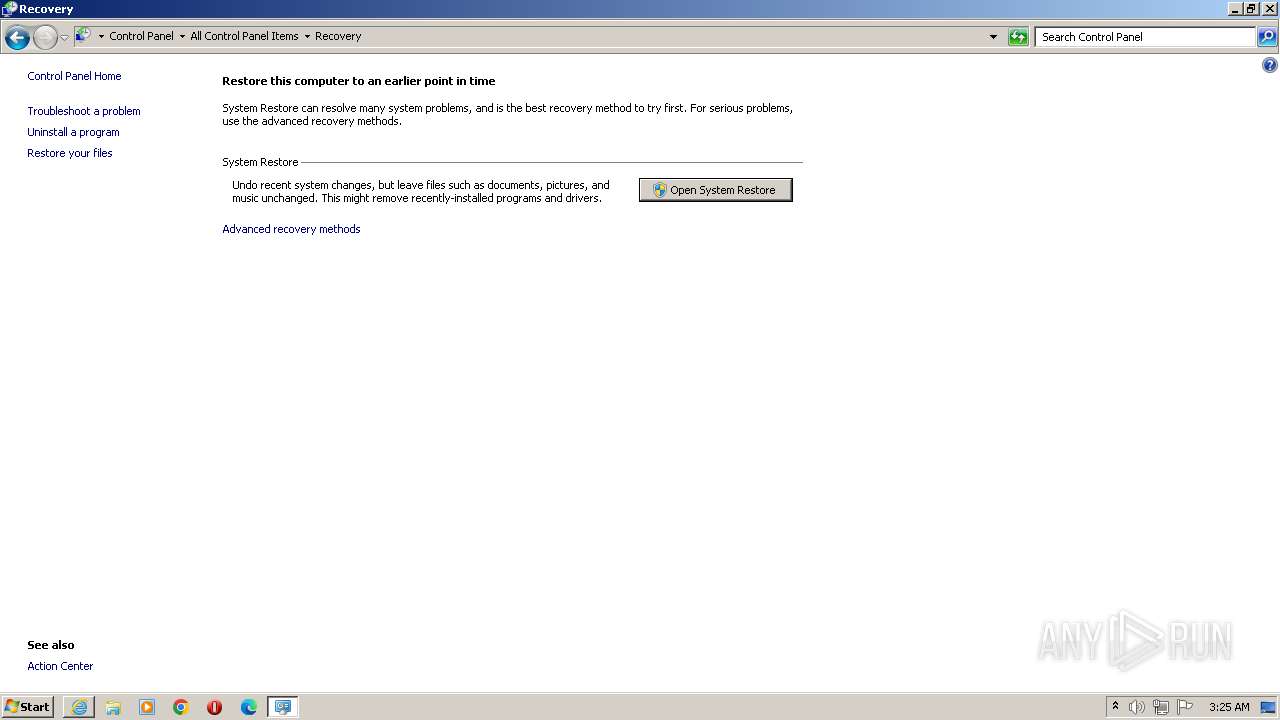
Manual execution by a user
- rundll32.exe (PID: 124)
- javacpl.exe (PID: 2564)
- rundll32.exe (PID: 2352)
- rstrui.exe (PID: 1664)
Checks supported languages
- javacpl.exe (PID: 2564)
- FlashPlayerApp.exe (PID: 3332)
- jucheck.exe (PID: 2000)
- jucheck.exe (PID: 3644)
- jucheck.exe (PID: 2972)
- javaw.exe (PID: 4060)
Reads the computer name
- FlashPlayerApp.exe (PID: 3332)
- jucheck.exe (PID: 2000)
- jucheck.exe (PID: 2972)
- javaw.exe (PID: 4060)
- jucheck.exe (PID: 3644)
Reads the machine GUID from the registry
- FlashPlayerApp.exe (PID: 3332)
- javaw.exe (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
24
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
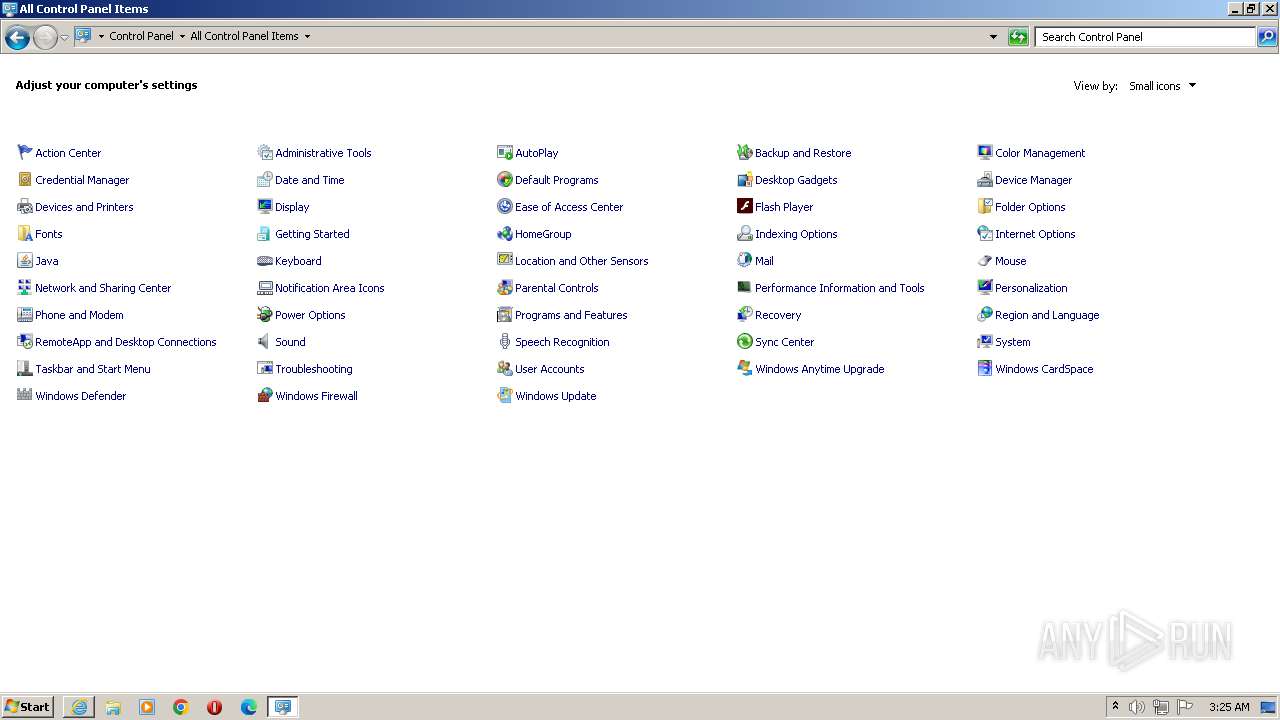
| 124 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,Control_RunDLL "C:\Windows\system32\FlashPlayerCPLApp.cpl",Flash Player | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 372 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2968 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 868 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | "C:\Windows\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1312 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\System32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1444 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\System32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1664 | "C:\Windows\system32\rstrui.exe" | C:\Windows\System32\rstrui.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Restore Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Common Files\Java\Java Update\jucheck.exe" -getconfig=1 | C:\Program Files\Common Files\Java\Java Update\jucheck.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Update Checker Exit code: 0 Version: 2.8.271.9 Modules
| |||||||||||||||
Total events
22 615
Read events
22 475
Write events
137
Delete events
3
Modification events
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
55
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | binary | |
MD5:3DEC87C3CC141E14CB4251CCC58A1B62 | SHA256:70132A8E464816DDD02D84AA0DEF65FEBBBD50A0FACFEB5D56CBB3D49E80CAF1 | |||
| 1088 | svchost.exe | C:\Windows\SERVIC~2\NETWOR~1\AppData\Local\Temp\Cab891C.tmp | compressed | |
MD5:24BE8A92460B5B7A555B1DA559296958 | SHA256:77A3CFE6B7EB676AF438D5DE88C7EFCB6ABCC494E0B65DA90201969E6D79B2A3 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:4DBFCBC3DA70849D6590D6D53A79C685 | SHA256:5B4085C8521049F0030BD1A6B7E244D099146A6CC6724F4CCDF8A2022407B818 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\NDF1986.tmp | binary | |
MD5:E494E9C8D49B8C1DE1F003114CDE1719 | SHA256:662893EC08CF58D5AF6392F1D7BD0E3551D4D4410D646B64AFB3FD995972017E | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:A20F499DBF416C39F0A102D8CB039581 | SHA256:084C4EBF828886860AC8FFCA5E72A6030659EA071CF0037D3522A3DF37B52FF3 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:21389D84648D6CFAC65F5EA61573CBAC | SHA256:749E4E469E9A8CD9E677A88AC9A80BB0D3A85253379311E70559A94CE7C68616 | |||
| 1088 | svchost.exe | C:\Windows\SERVIC~2\NETWOR~1\AppData\Local\Temp\Tar891D.tmp | binary | |
MD5:DF5FB73979D905234CE451F1CF8A9071 | SHA256:F1ED8E8C181DD800EF4181D53F9852E428F6239630DC8CE897EE1D9427AD8B0A | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:24BE8A92460B5B7A555B1DA559296958 | SHA256:77A3CFE6B7EB676AF438D5DE88C7EFCB6ABCC494E0B65DA90201969E6D79B2A3 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
20
DNS requests
66
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
532 | iexplore.exe | GET | 307 | 13.107.213.67:80 | http://schemas.microsoft.com/ | unknown | — | — | unknown |
836 | svchost.exe | GET | 307 | 13.107.213.67:80 | http://schemas.microsoft.com/ | unknown | — | — | unknown |
532 | iexplore.exe | GET | 307 | 13.107.213.67:80 | http://schemas.microsoft.com/ | unknown | — | — | unknown |
532 | iexplore.exe | GET | 200 | 117.18.232.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?103eb0c2a40c009d | unknown | compressed | 4.66 Kb | unknown |
532 | iexplore.exe | GET | 200 | 152.195.38.76:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | unknown | der | 471 b | unknown |
2968 | iexplore.exe | GET | 200 | 152.195.38.76:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | der | 471 b | unknown |
532 | iexplore.exe | GET | 200 | 152.195.38.76:80 | http://crl4.digicert.com/DigiCertGlobalRootG2.crl | unknown | der | 1.10 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | iexplore.exe | 13.107.213.67:80 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
532 | iexplore.exe | 13.107.213.67:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
532 | iexplore.exe | 117.18.232.240:80 | ctldl.windowsupdate.com | EDGECAST | AU | unknown |
532 | iexplore.exe | 152.195.38.76:80 | ocsp.digicert.com | EDGECAST | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2968 | iexplore.exe | 117.18.232.200:443 | iecvlist.microsoft.com | EDGECAST | AU | unknown |
2968 | iexplore.exe | 152.195.38.76:80 | ocsp.digicert.com | EDGECAST | US | unknown |
836 | svchost.exe | 13.107.213.67:80 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| unknown |
crl3.digicert.com |
| unknown |
dns.msftncsi.com |
| shared |
crl4.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| unknown |
Threats
2 ETPRO signatures available at the full report