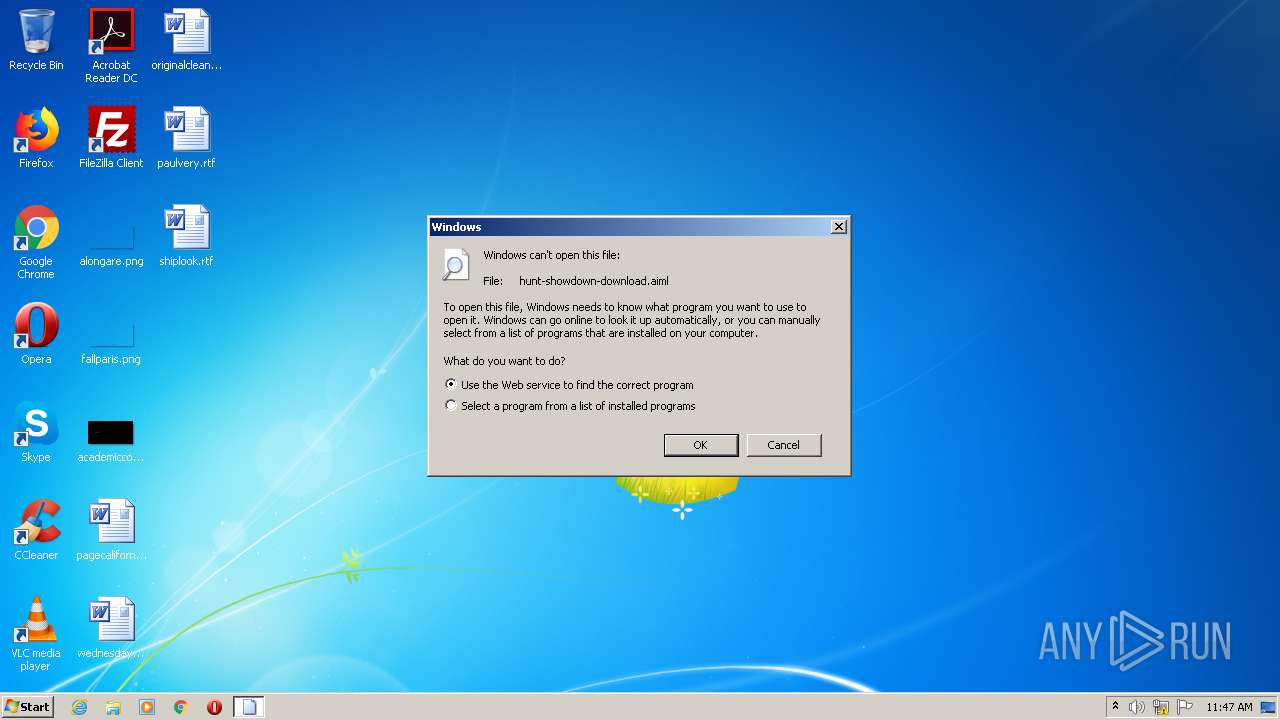
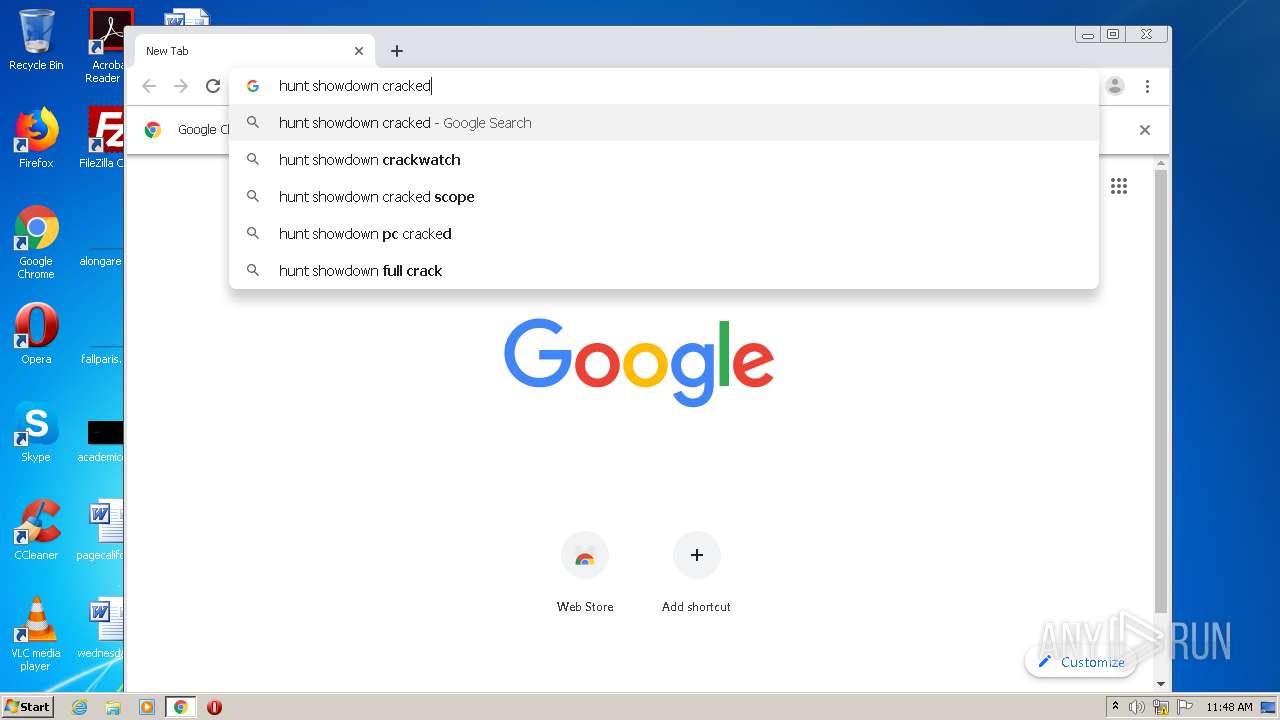
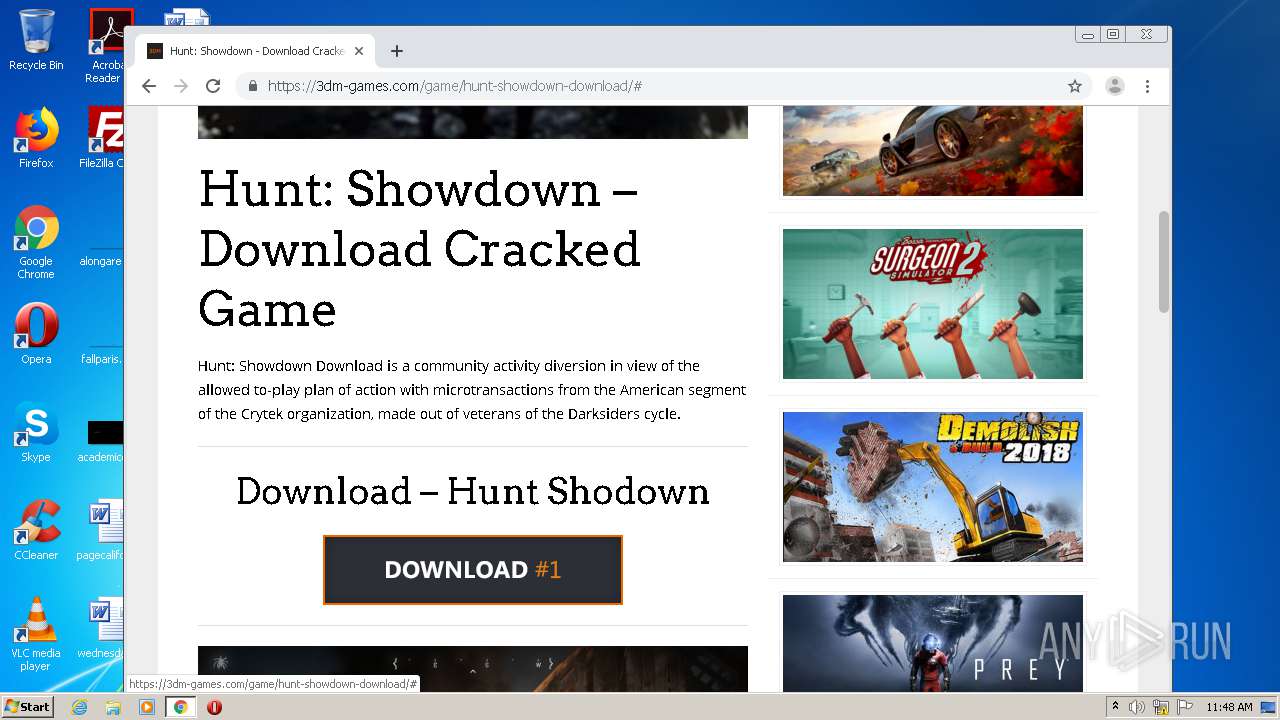
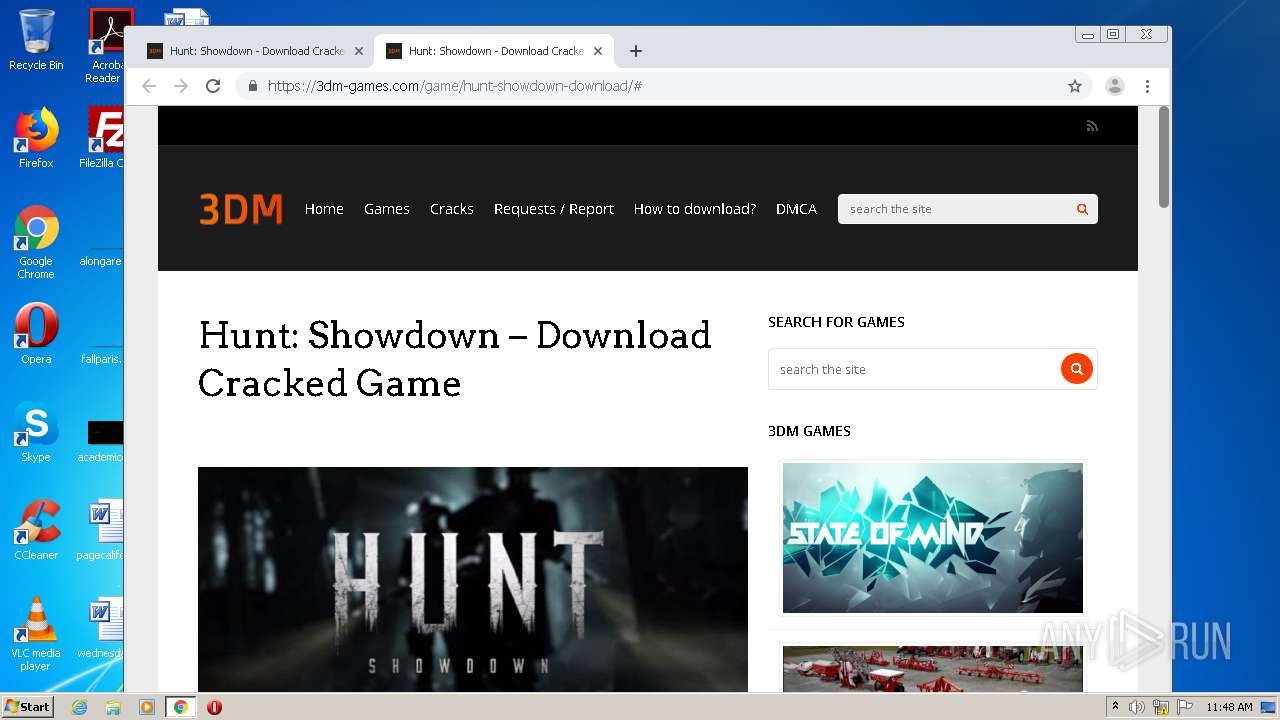
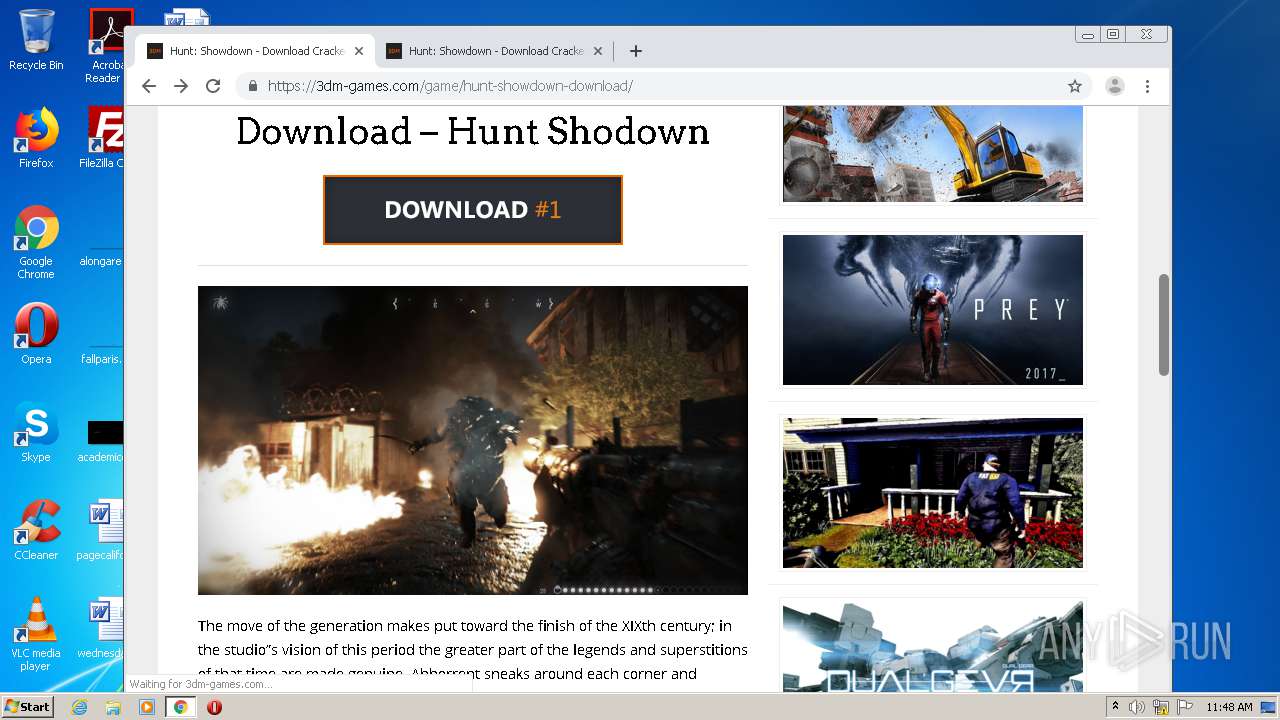
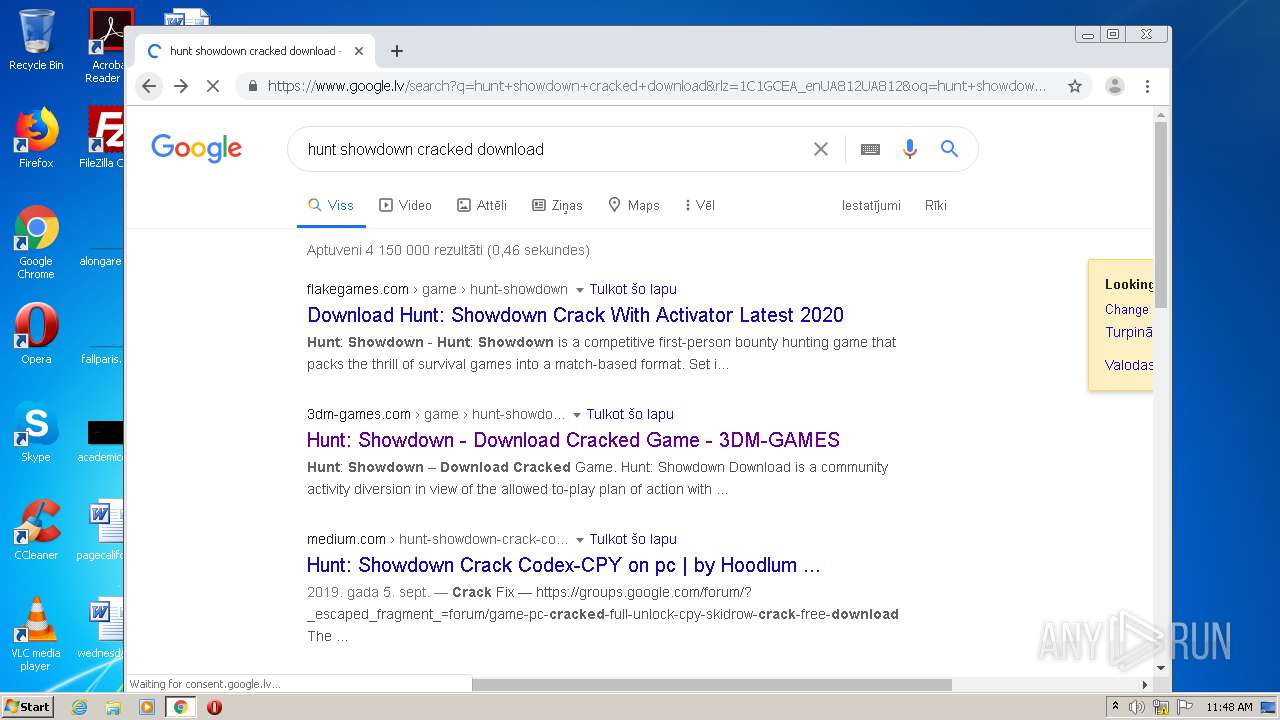
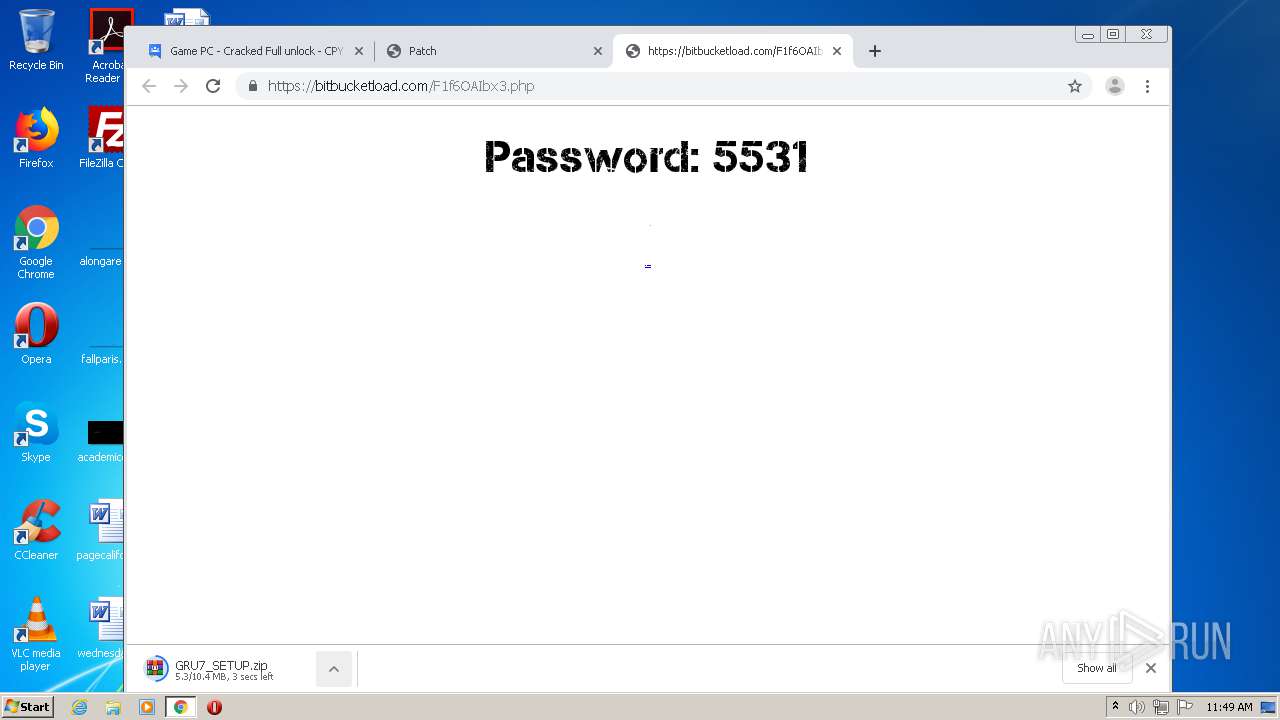
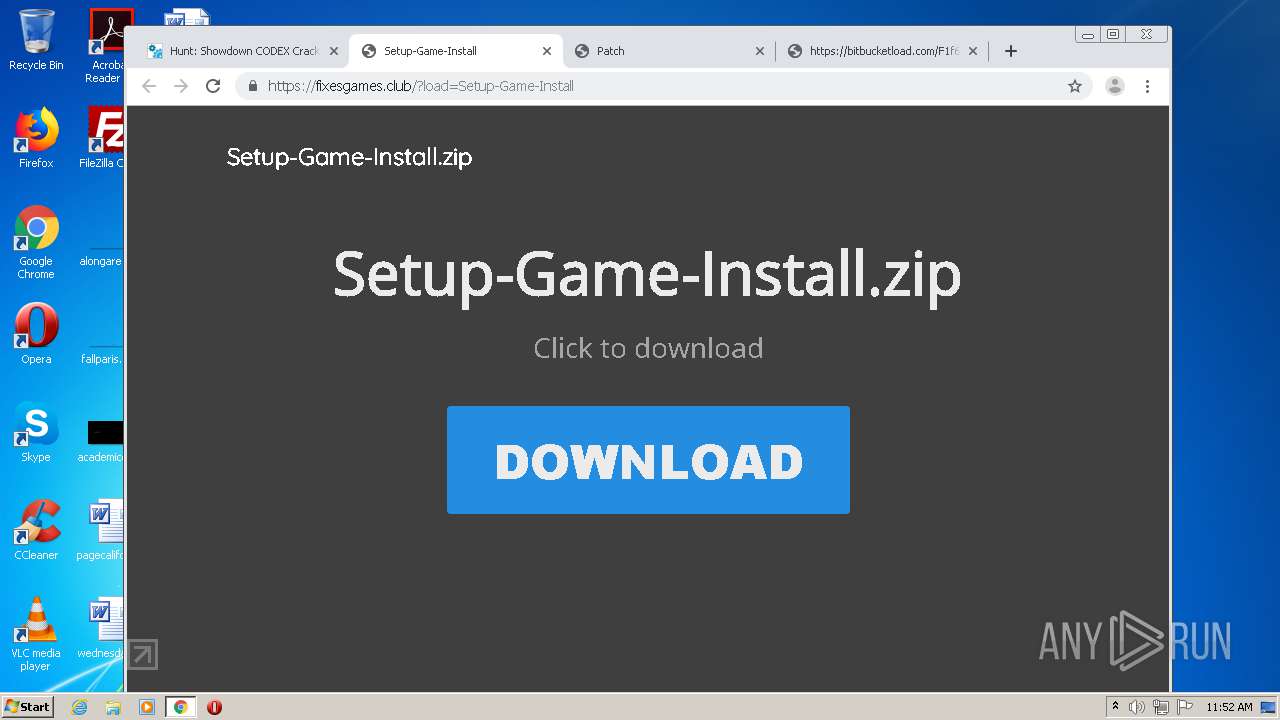
| download: | hunt-showdown-download |
| Full analysis: | https://app.any.run/tasks/2e99da61-21ed-4759-9185-d45bfd66d659 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 11:47:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | BBD86C491A1D7BEE111AD1BC89B2492E |
| SHA1: | DE716FBA7E9B90C4753B03ACB4B8A74862DB72AD |
| SHA256: | 233DA82CE3F1A3E1FB282FB25C723633C3F4E5BA6A282852D6E874AF47B3C779 |
| SSDEEP: | 3072:l+IfMhvHFbOQIFl+28ljjn6V0voa7yAJ3nQJtQ5WVEHzvSJ:l+IfT+28eAJ3nQJtQ5WVwqJ |
MALICIOUS
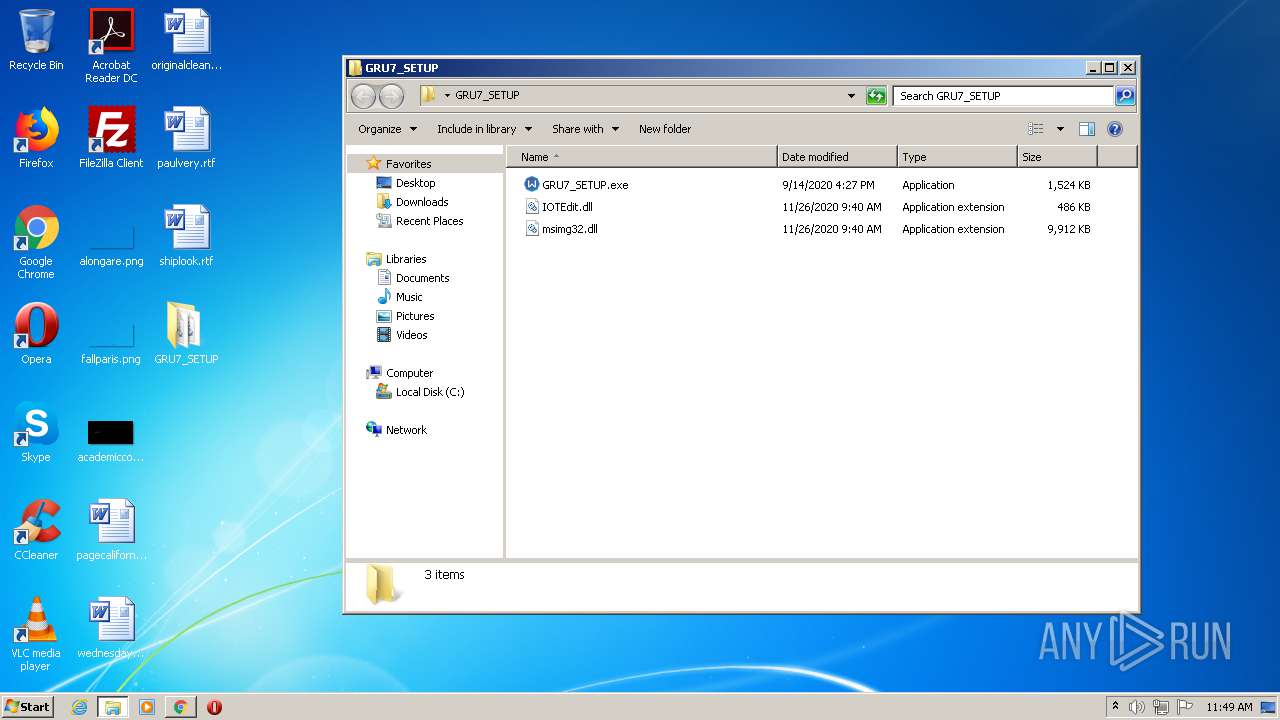
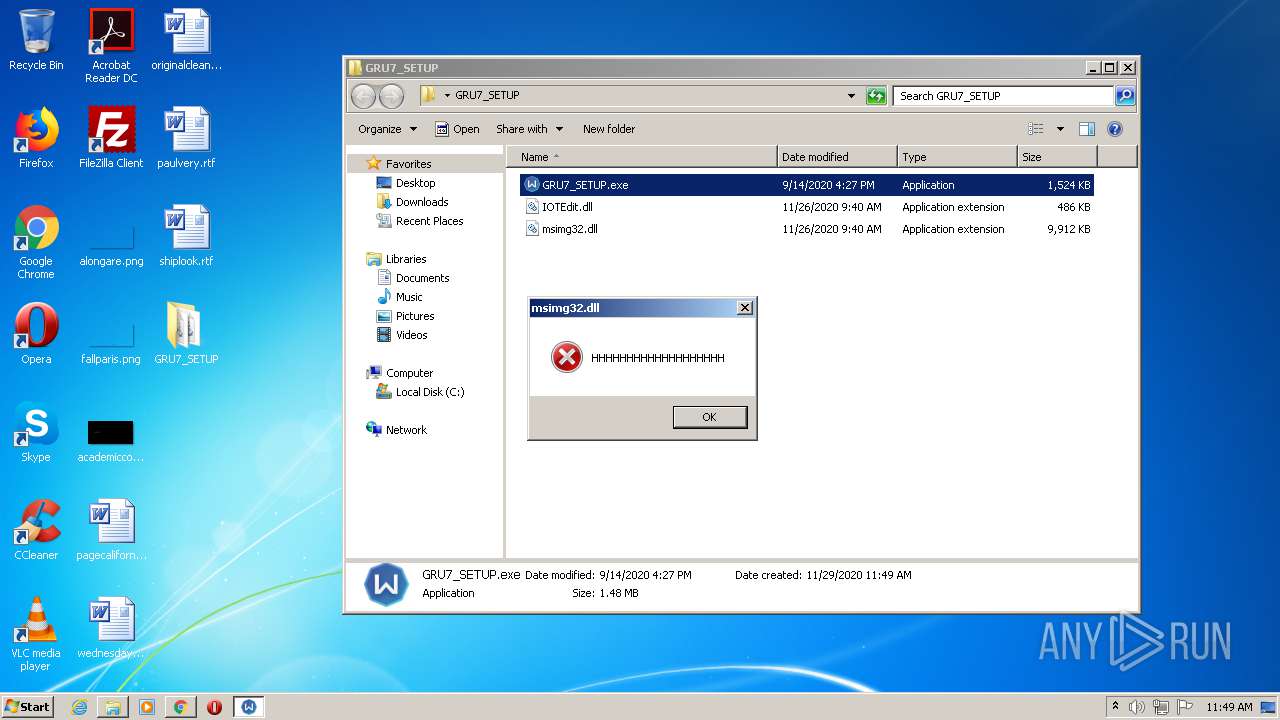
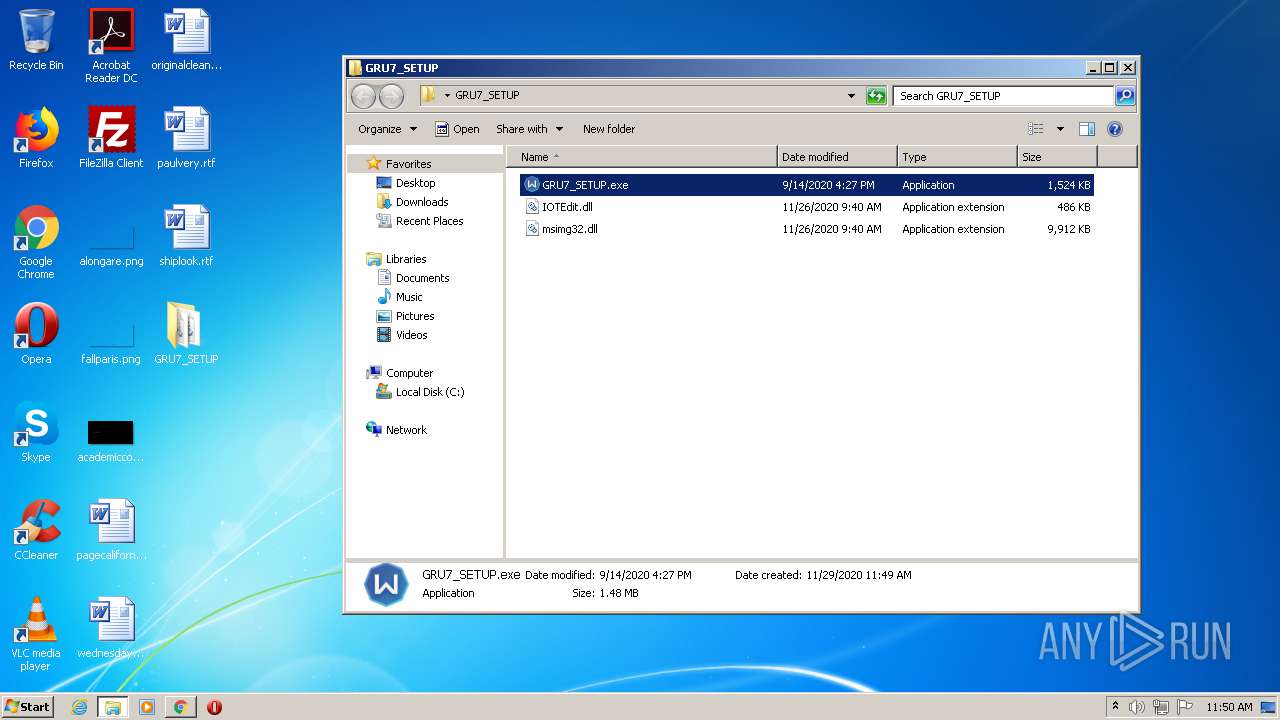
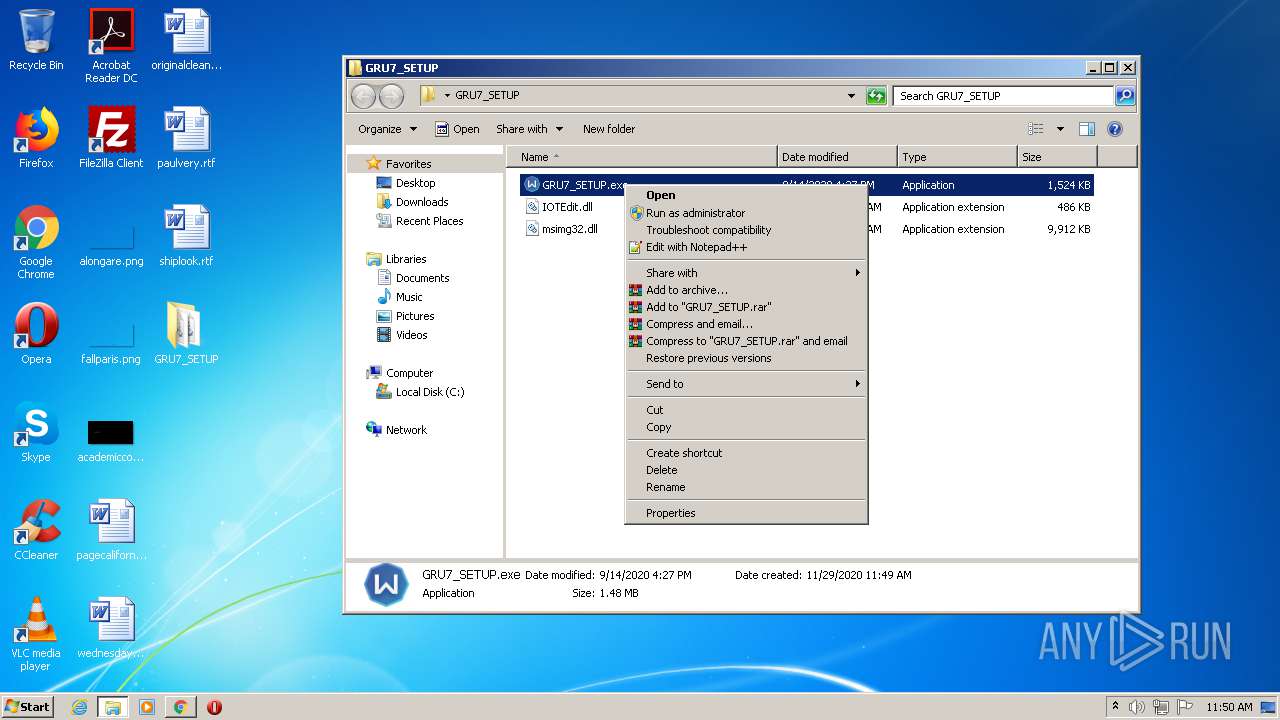
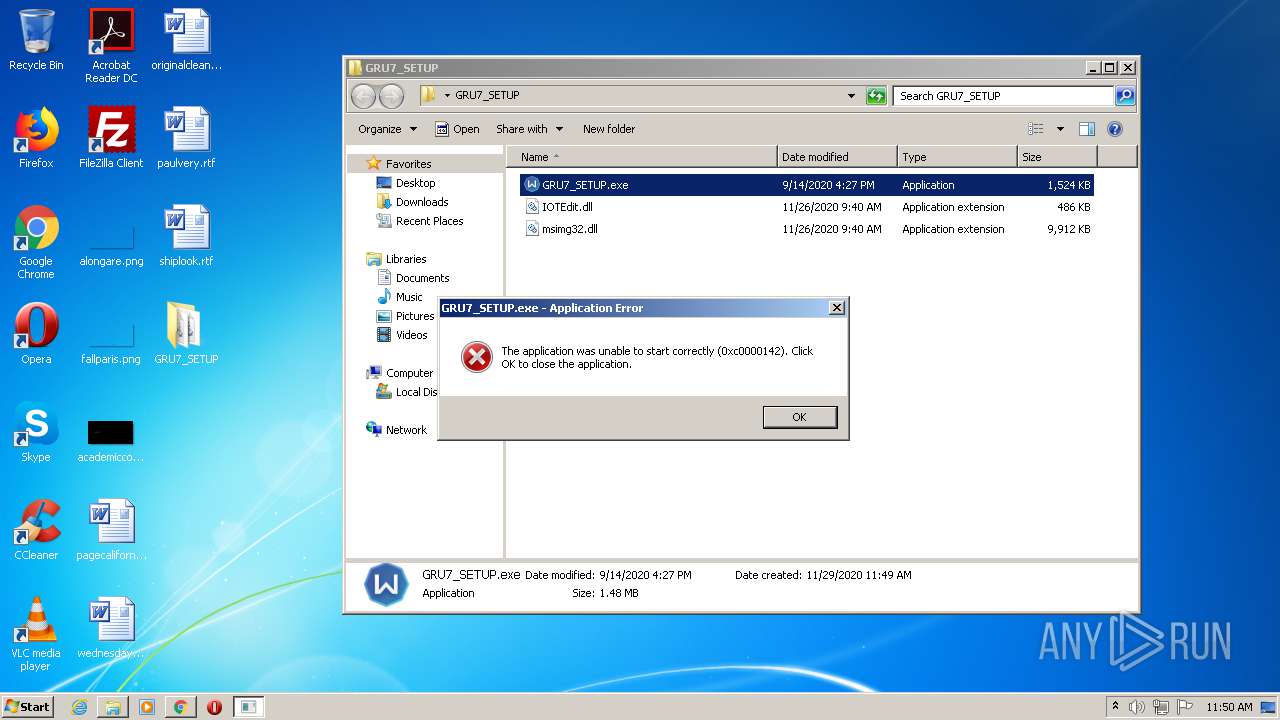
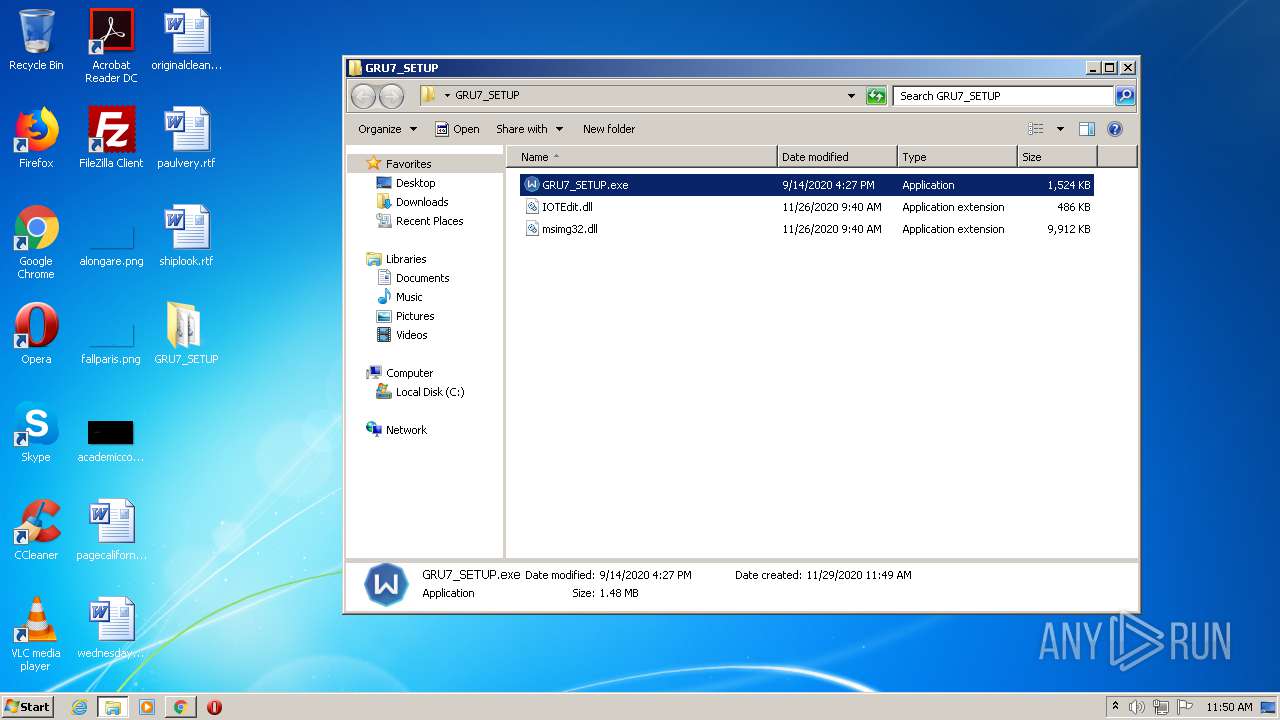
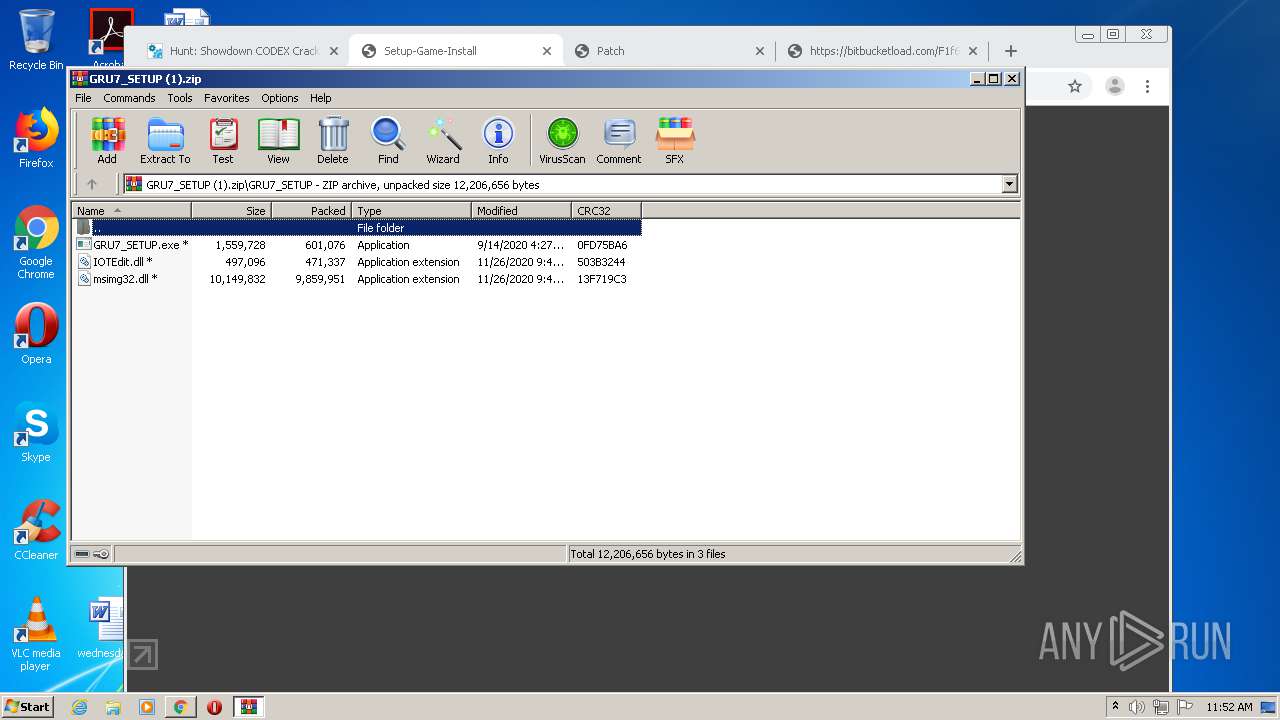
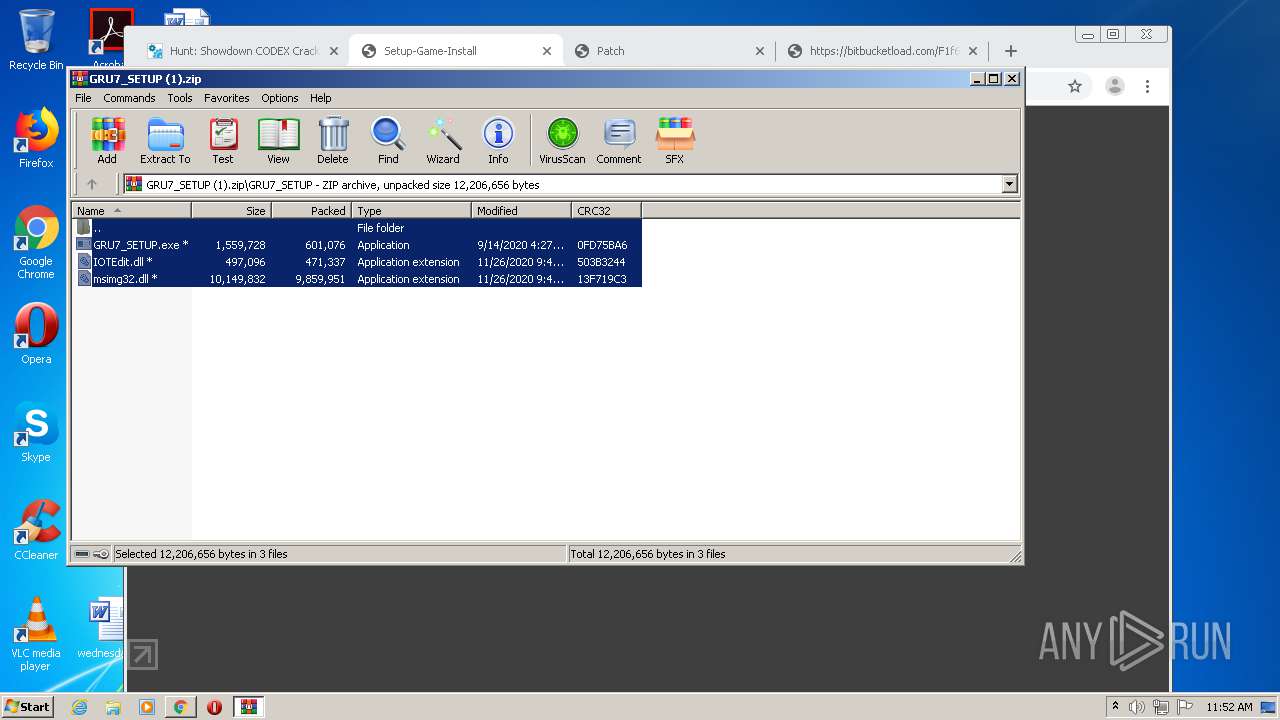
Loads dropped or rewritten executable
- GRU7_SETUP.exe (PID: 2256)
- SearchProtocolHost.exe (PID: 2364)
- GRU7_SETUP.exe (PID: 1704)
- explorer.exe (PID: 292)
- SearchProtocolHost.exe (PID: 3924)
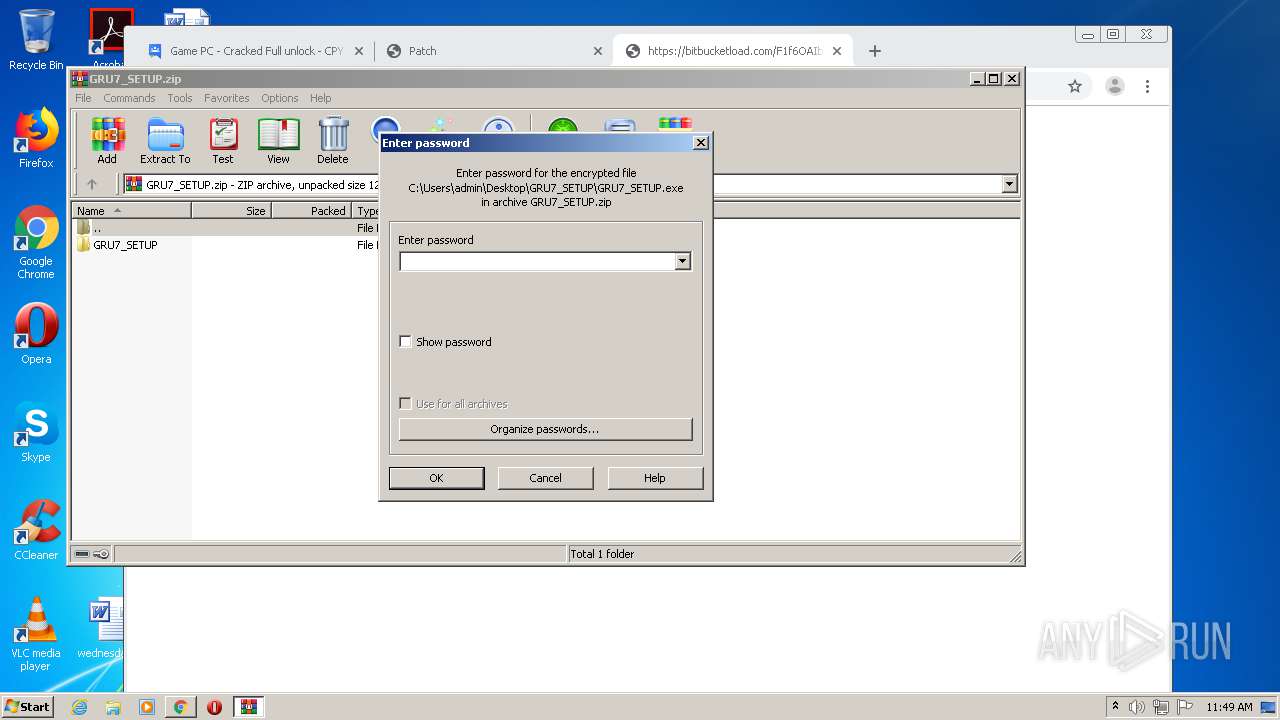
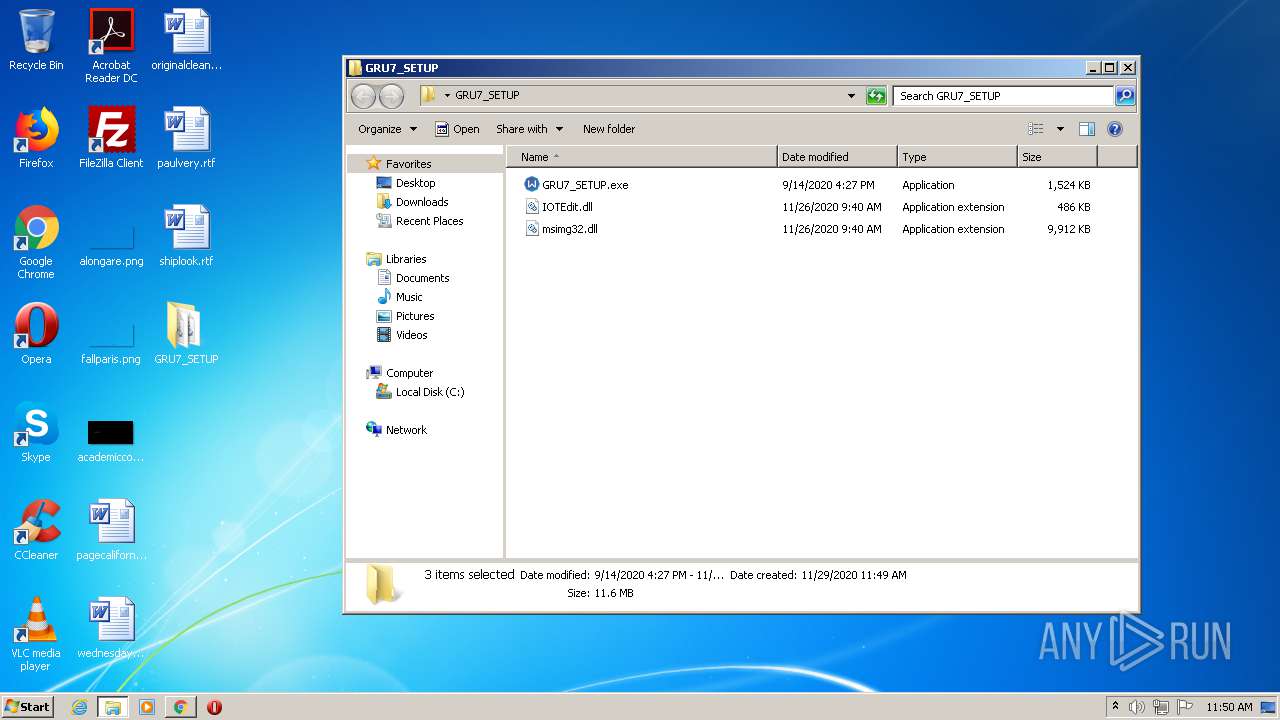
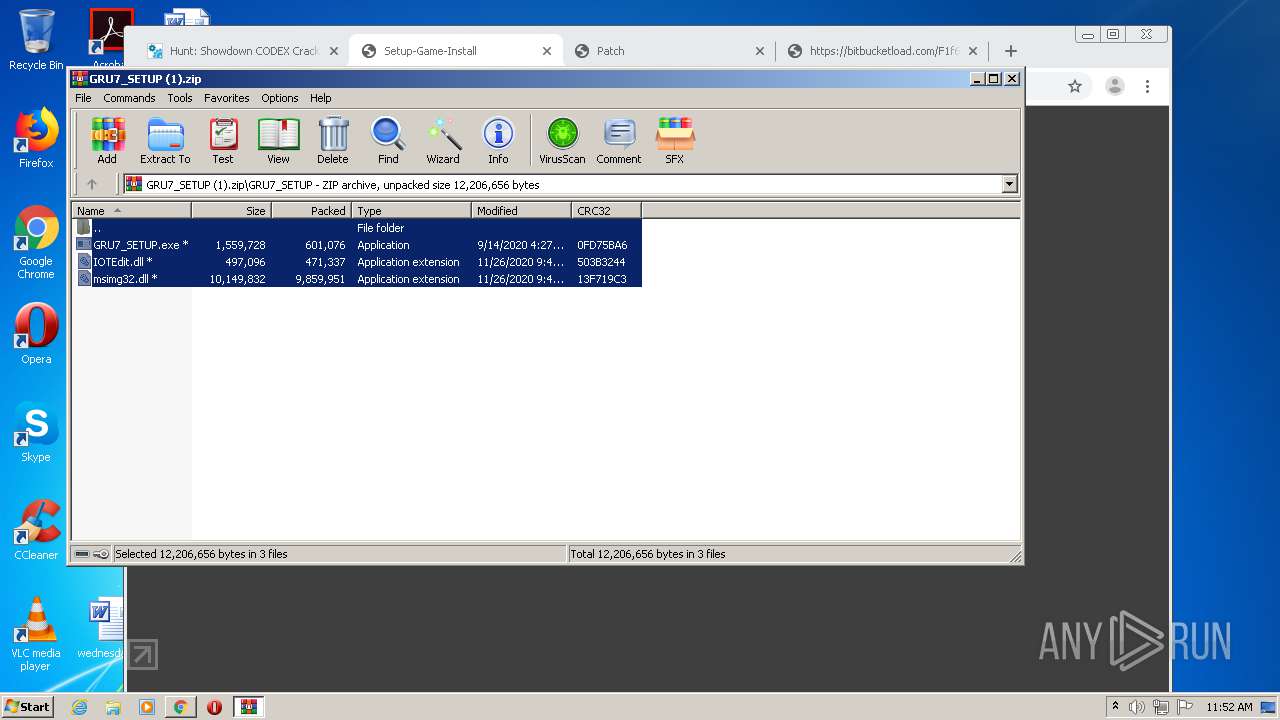
Application was dropped or rewritten from another process
- GRU7_SETUP.exe (PID: 2256)
- GRU7_SETUP.exe (PID: 1704)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 292)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2076)
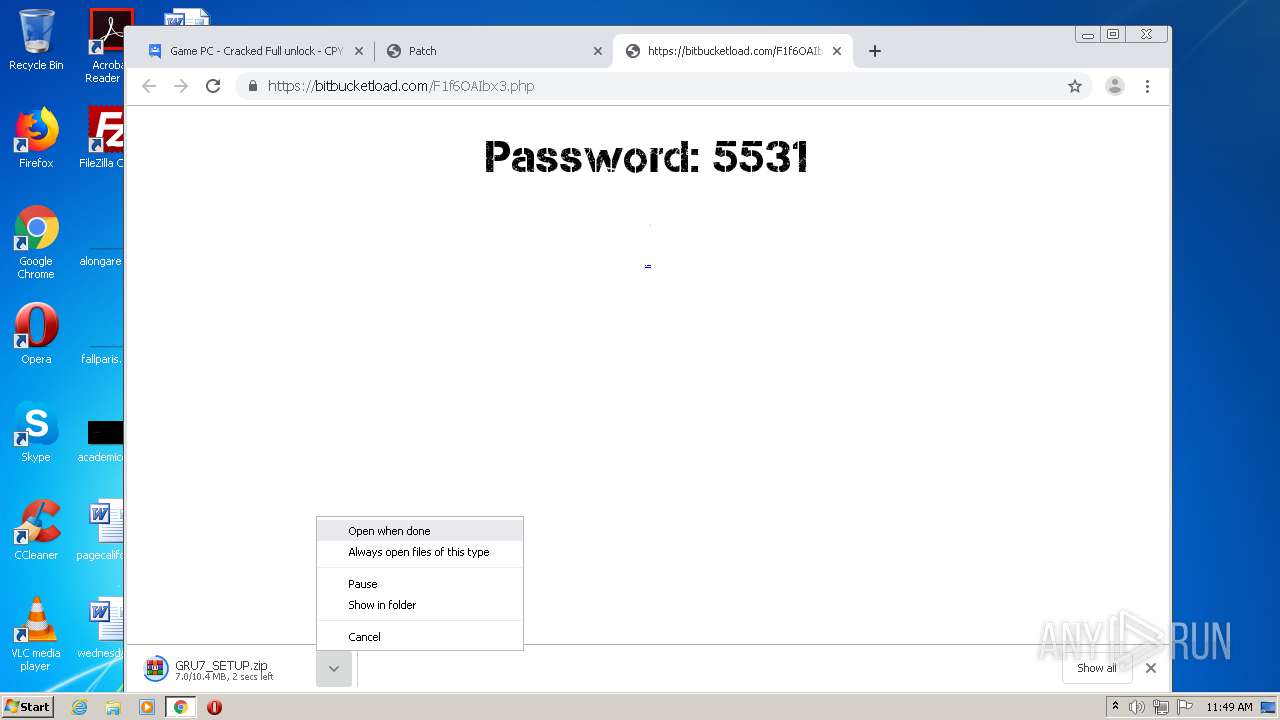
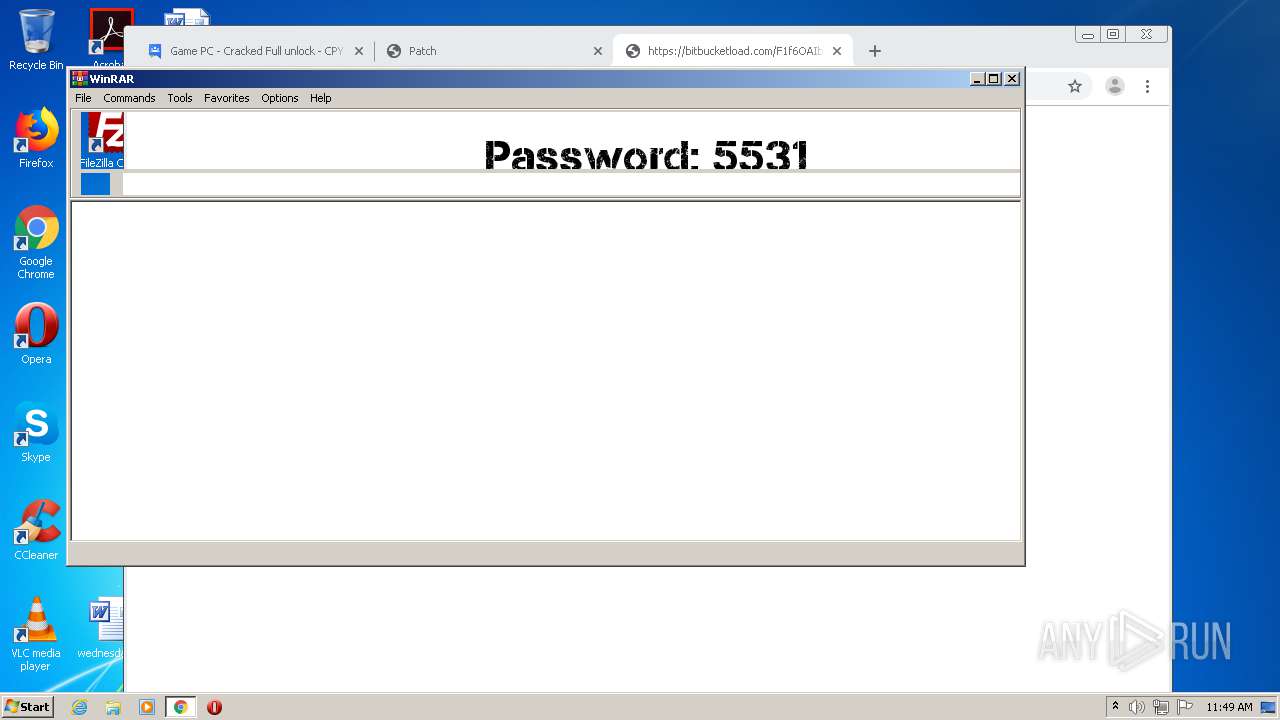
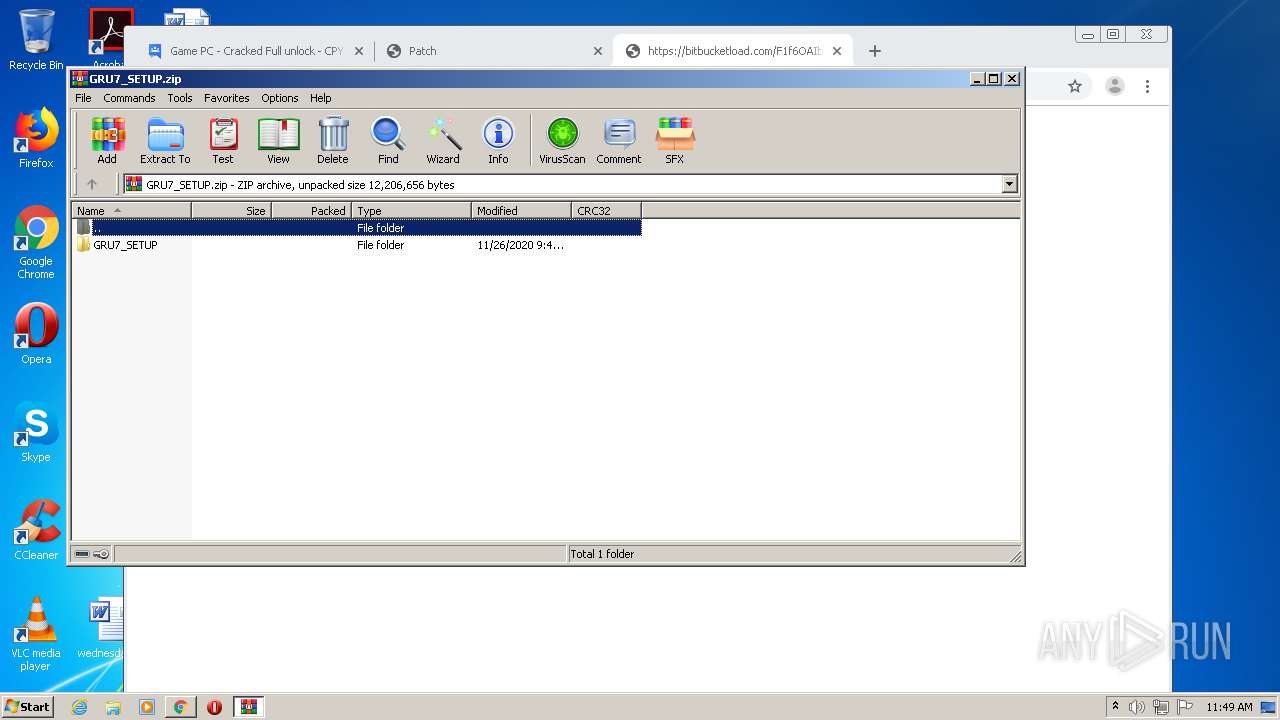
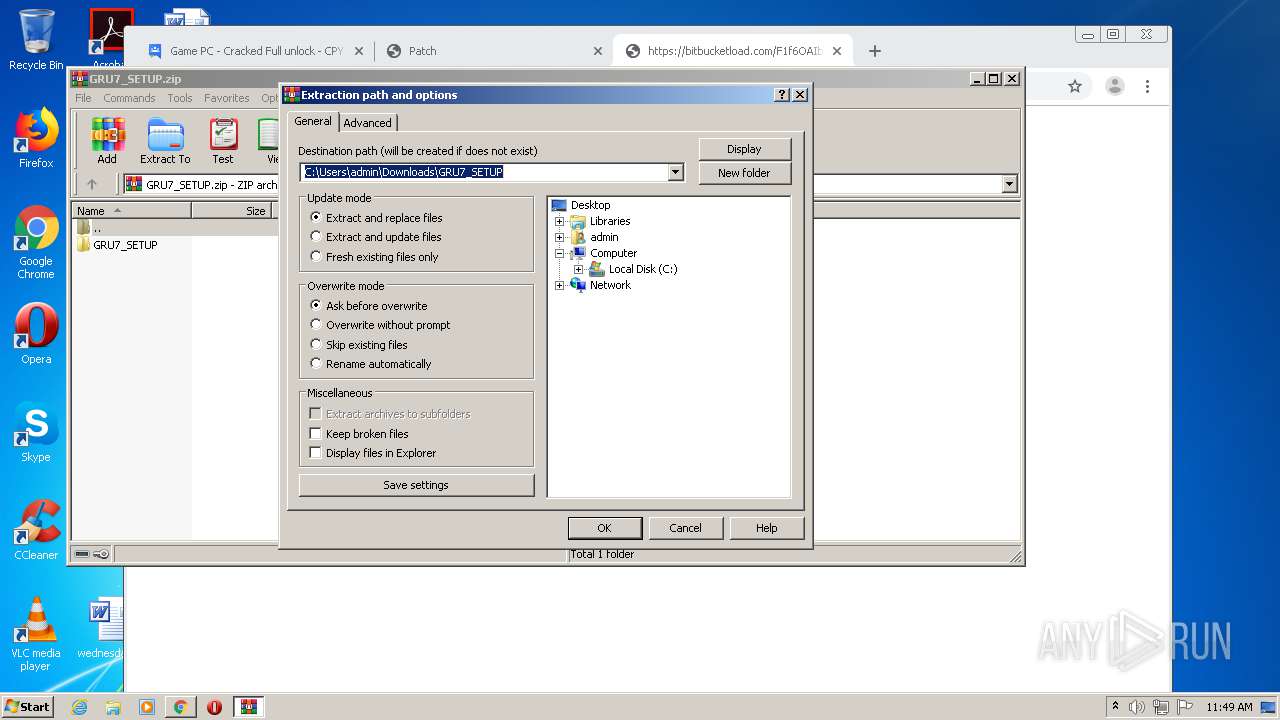
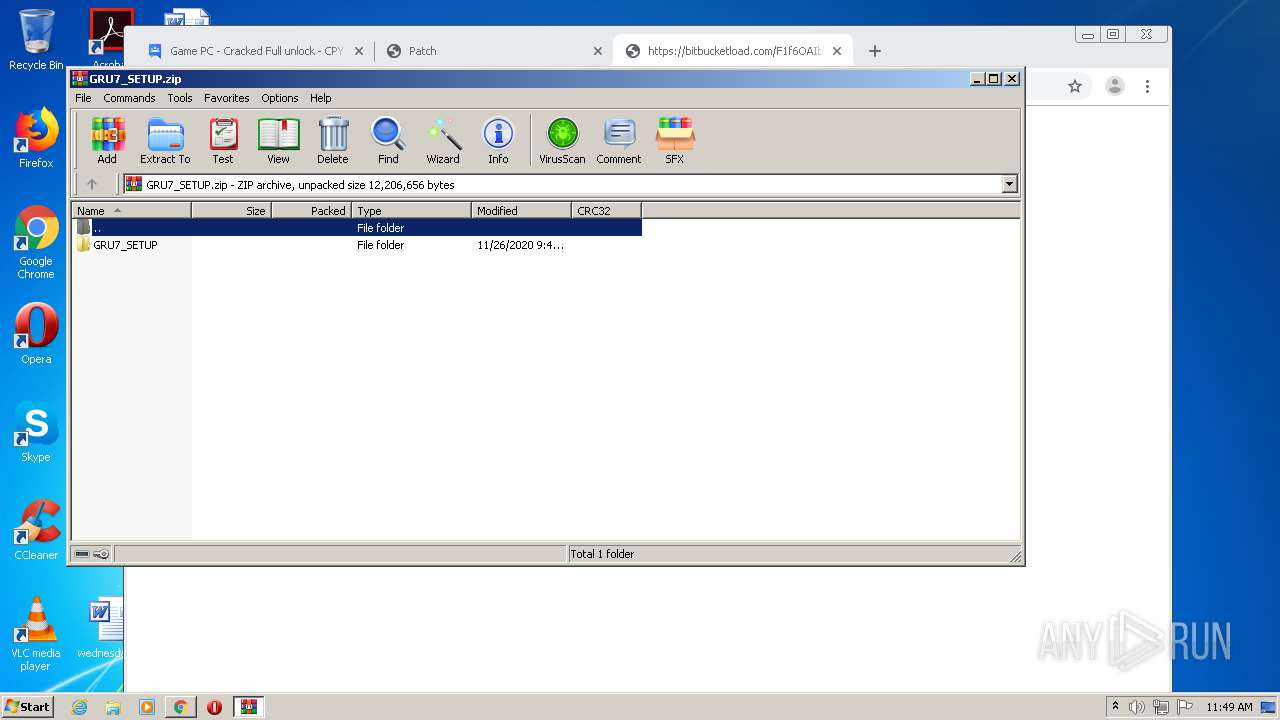
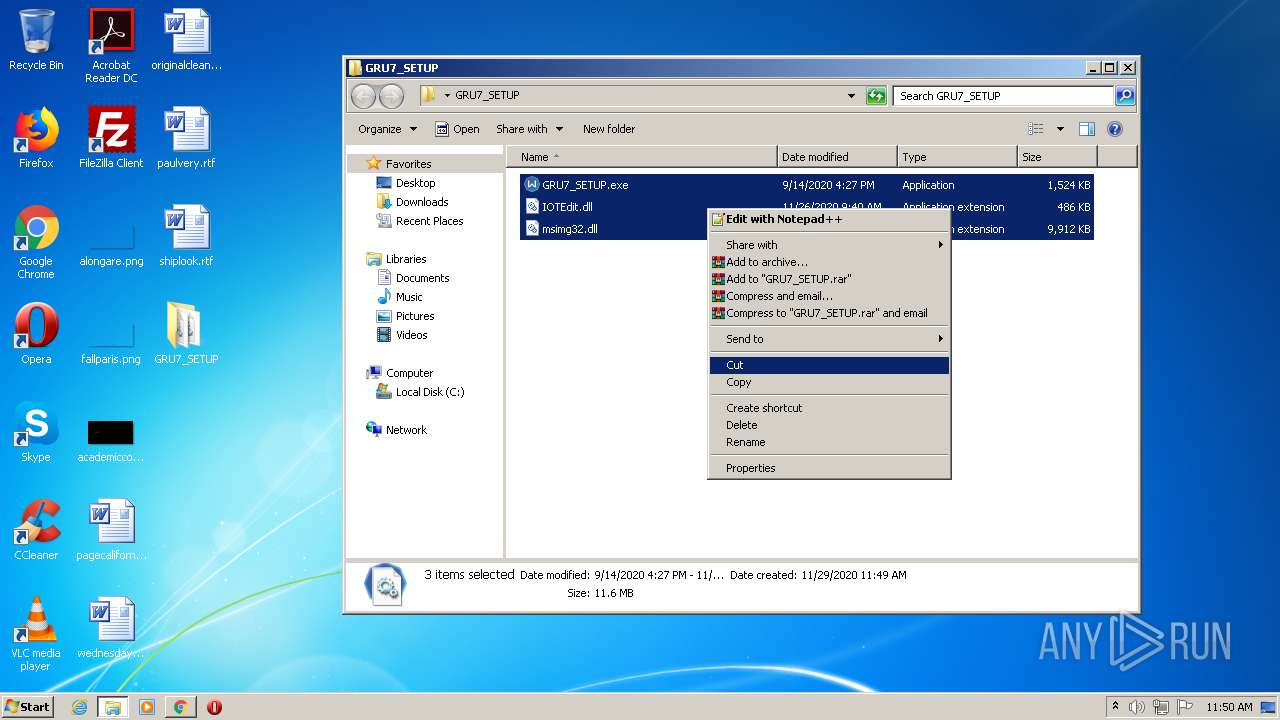
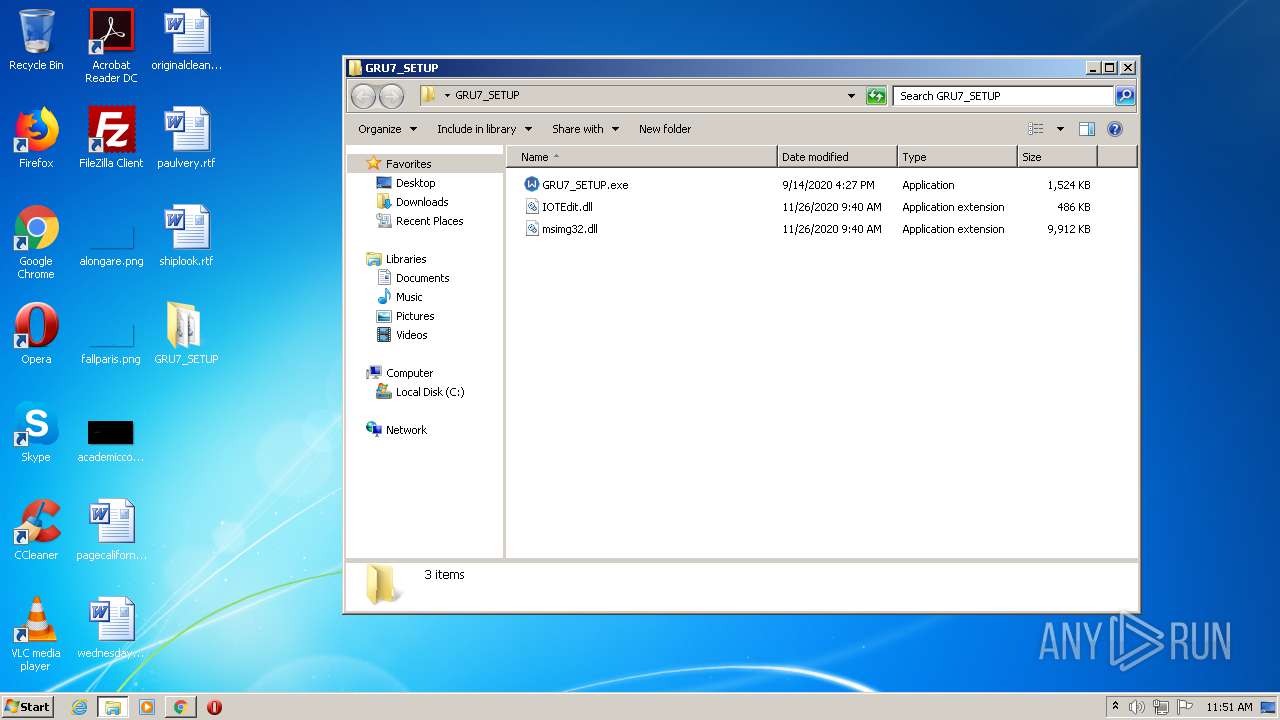
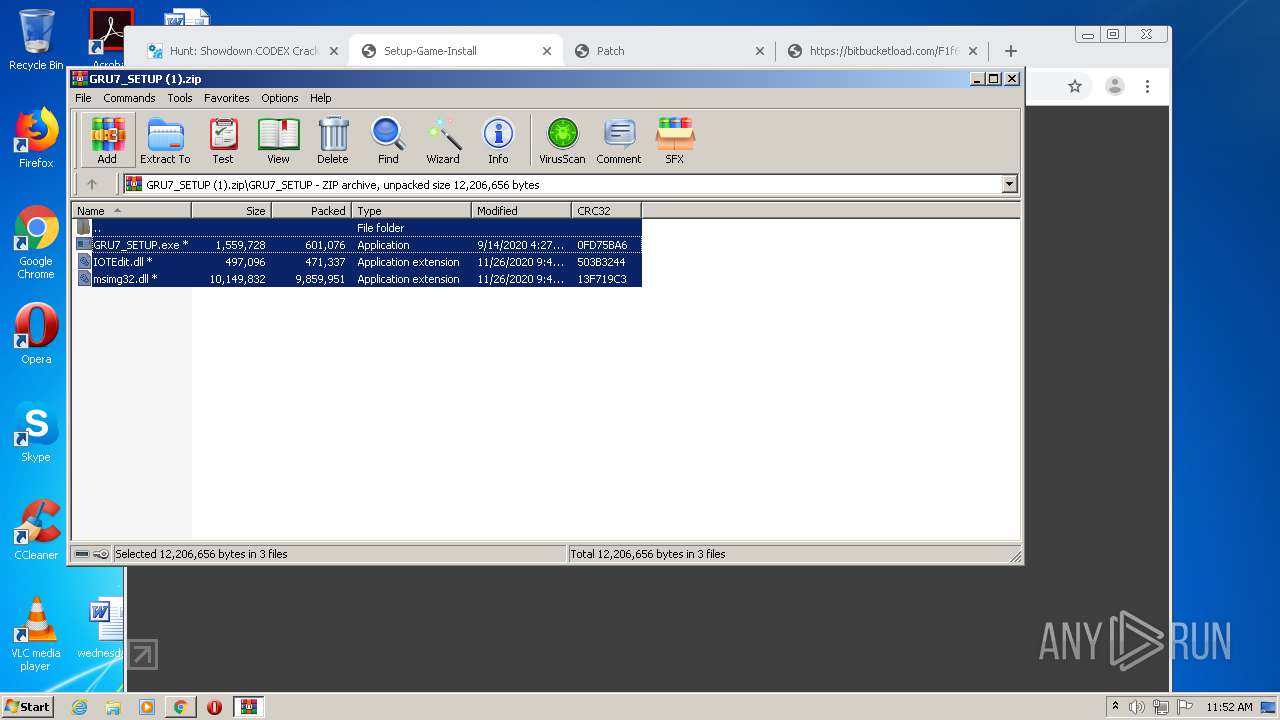
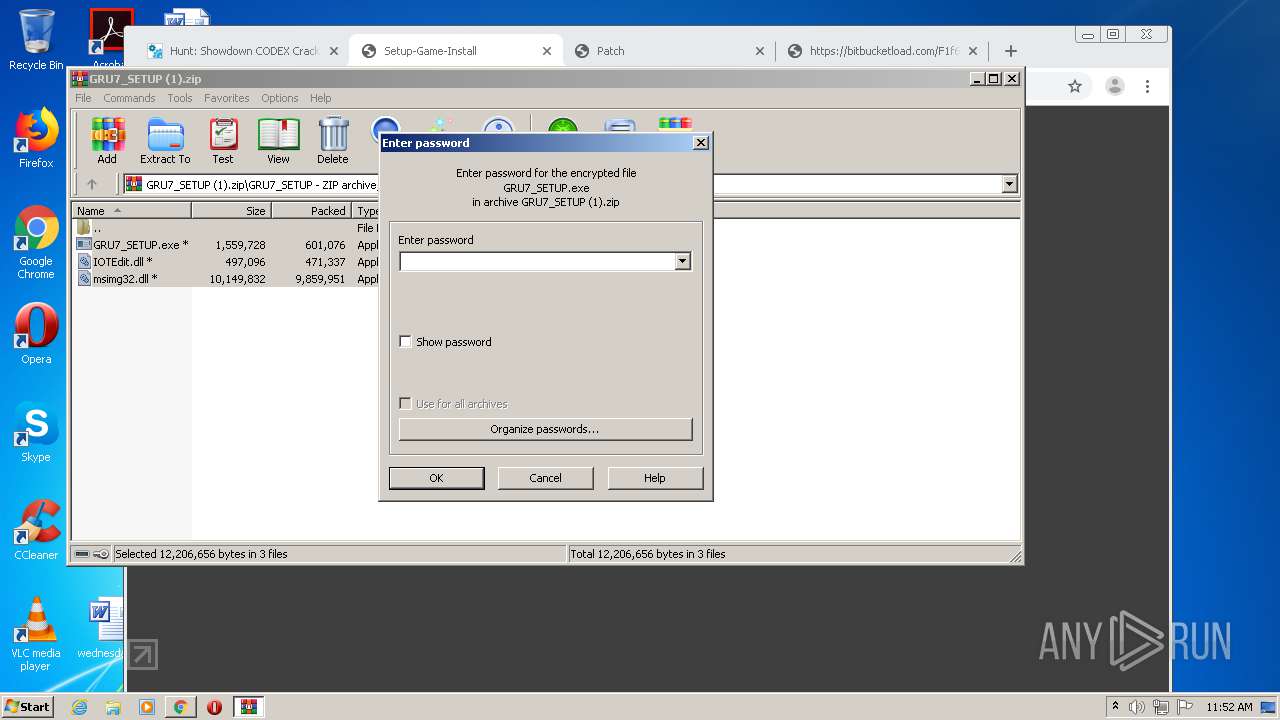
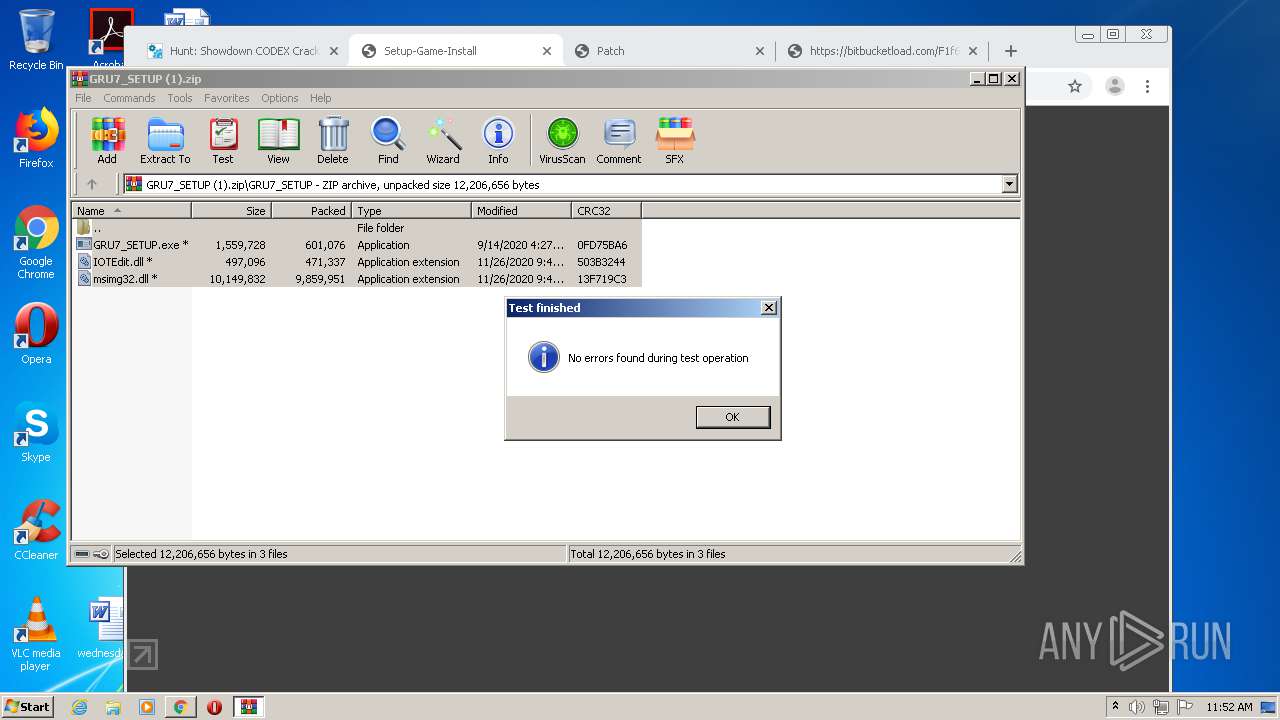
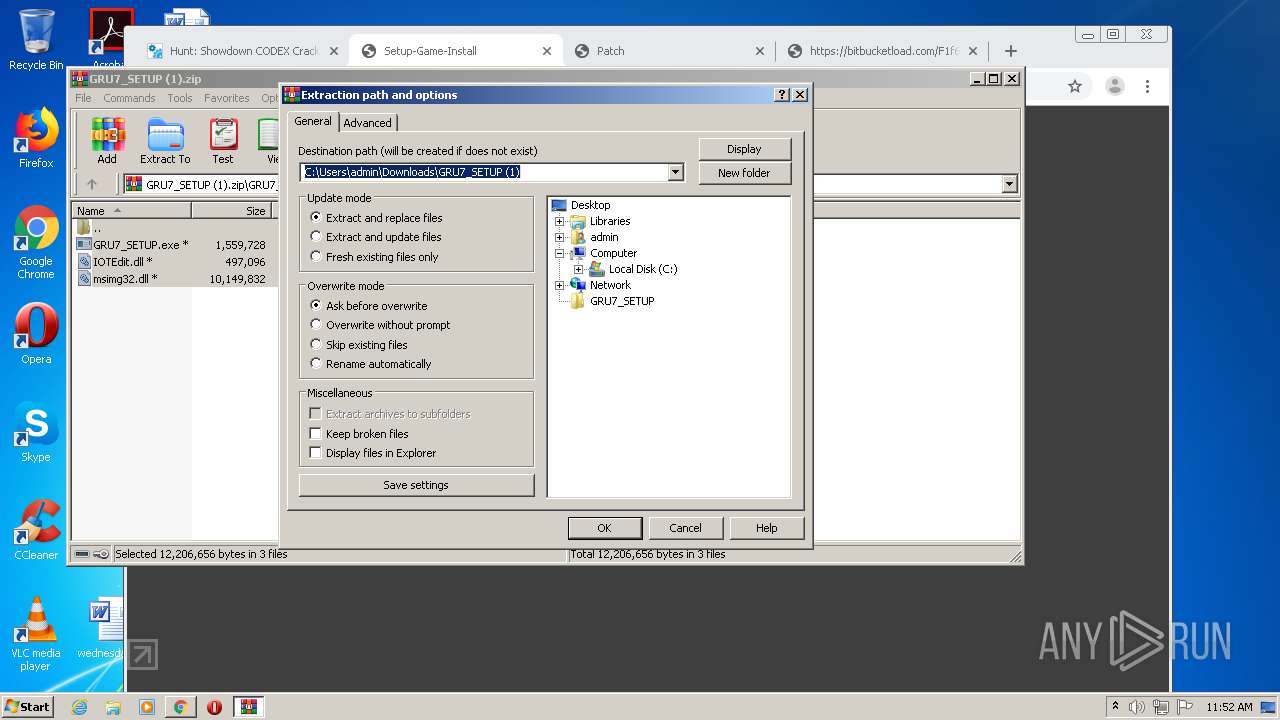
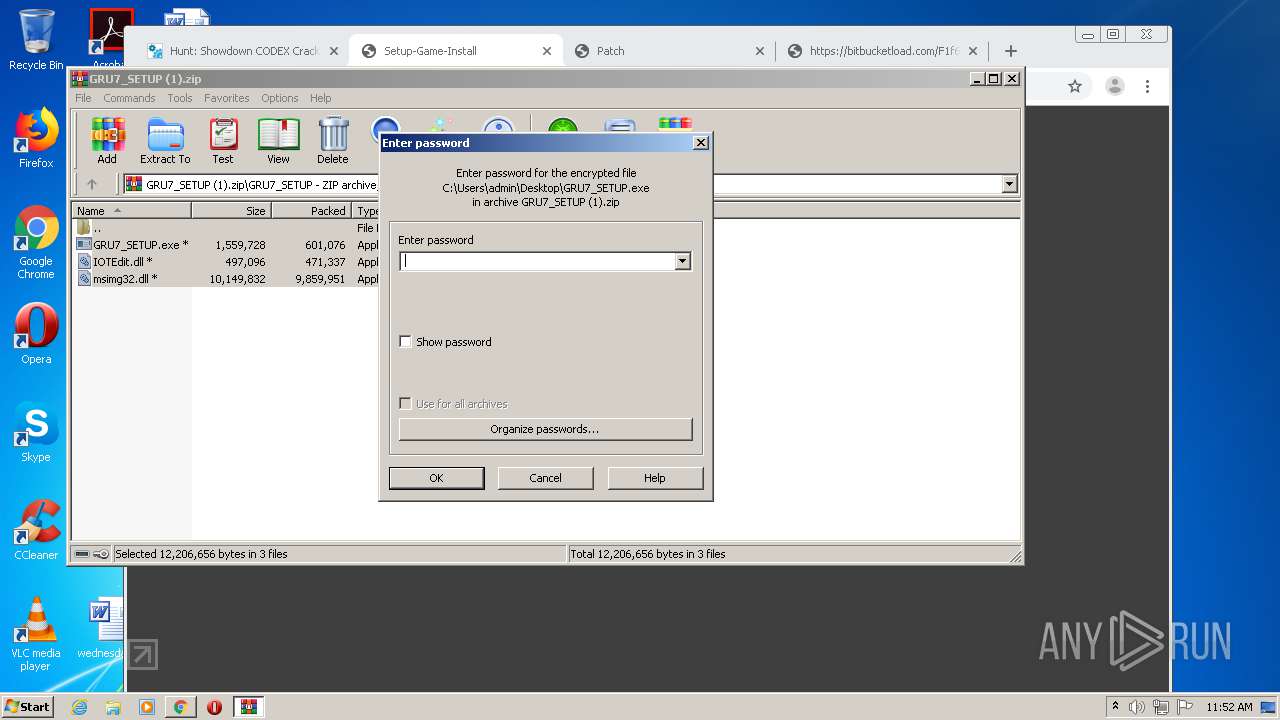
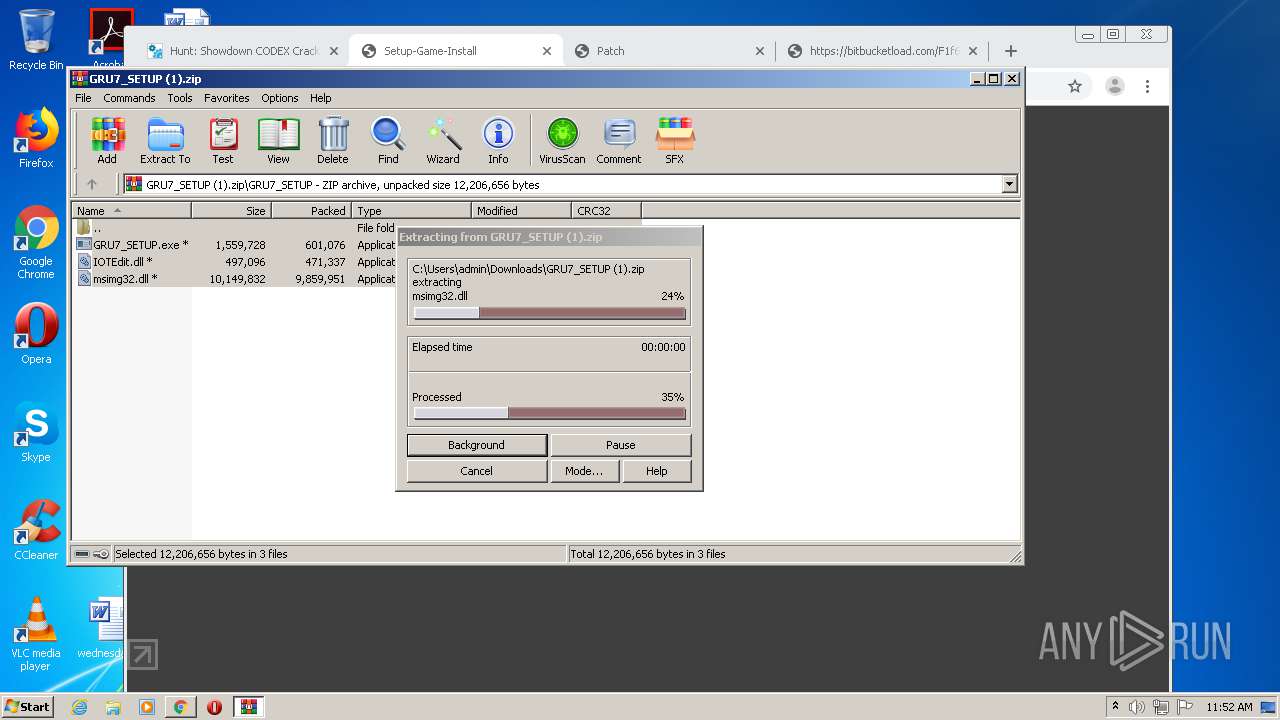
Executable content was dropped or overwritten
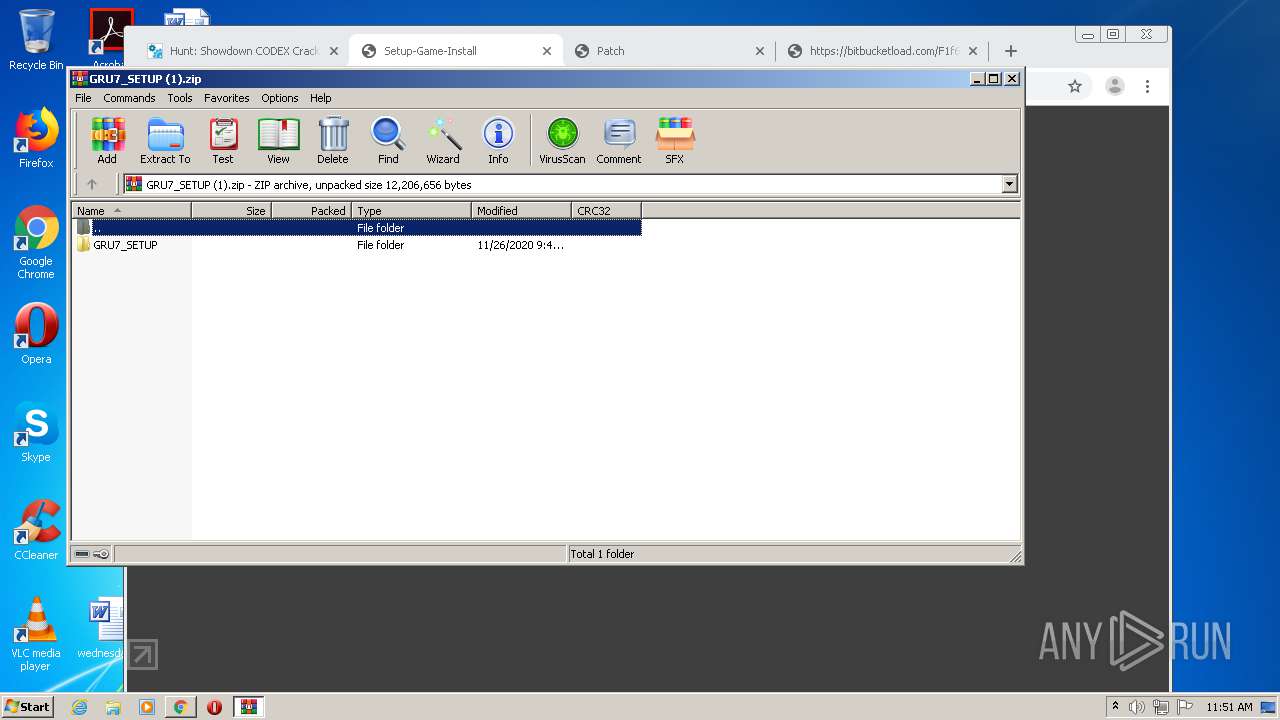
- WinRAR.exe (PID: 2248)
- WinRAR.exe (PID: 3784)
Creates files in the user directory
- explorer.exe (PID: 292)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2248)
- WinRAR.exe (PID: 3784)
INFO
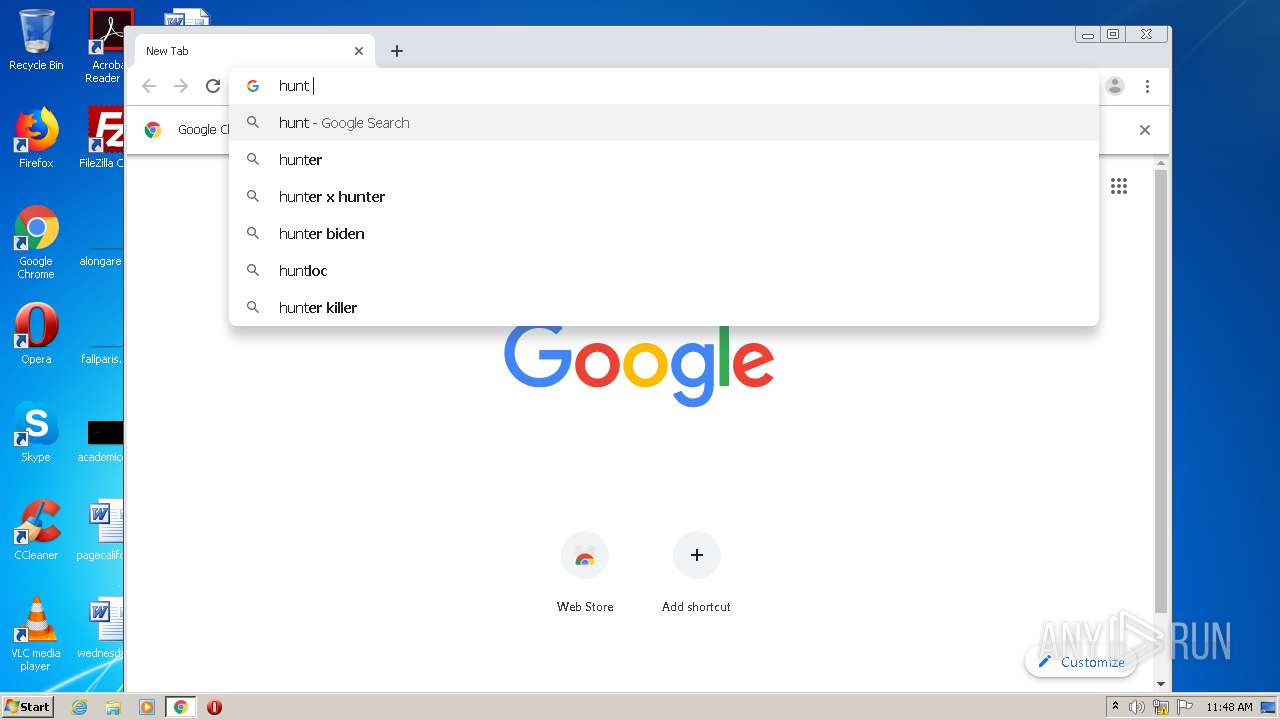
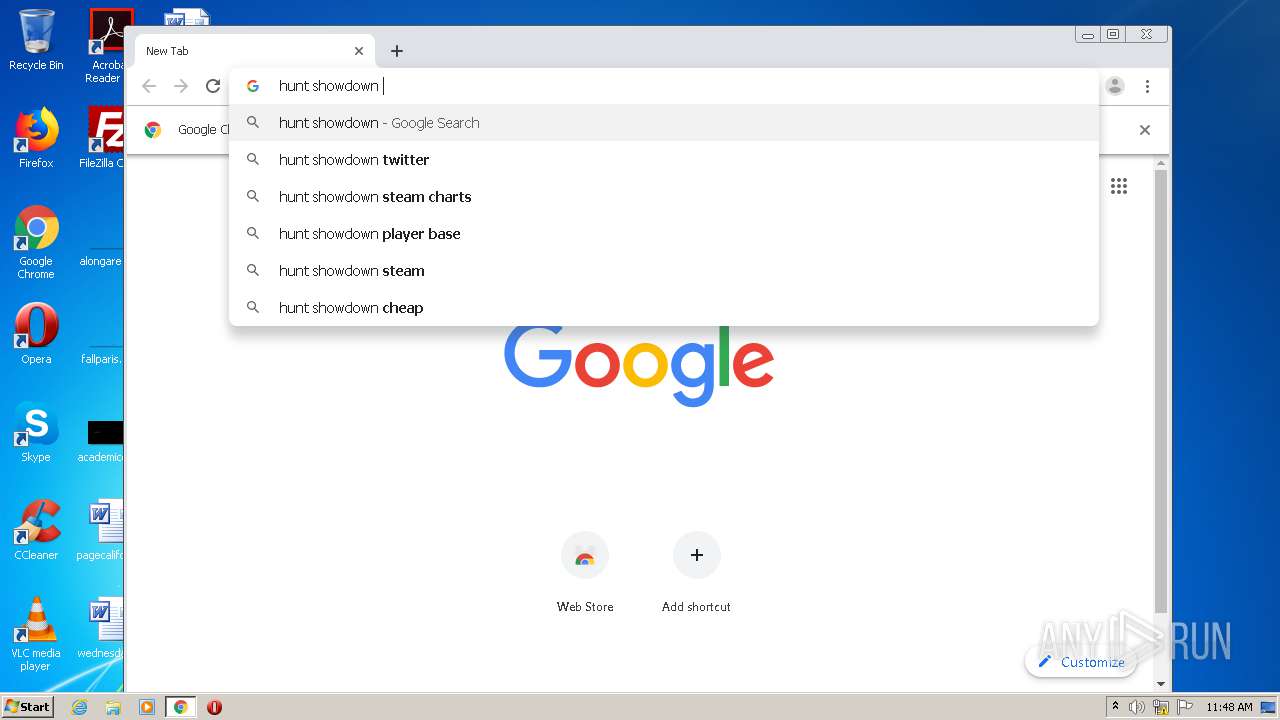
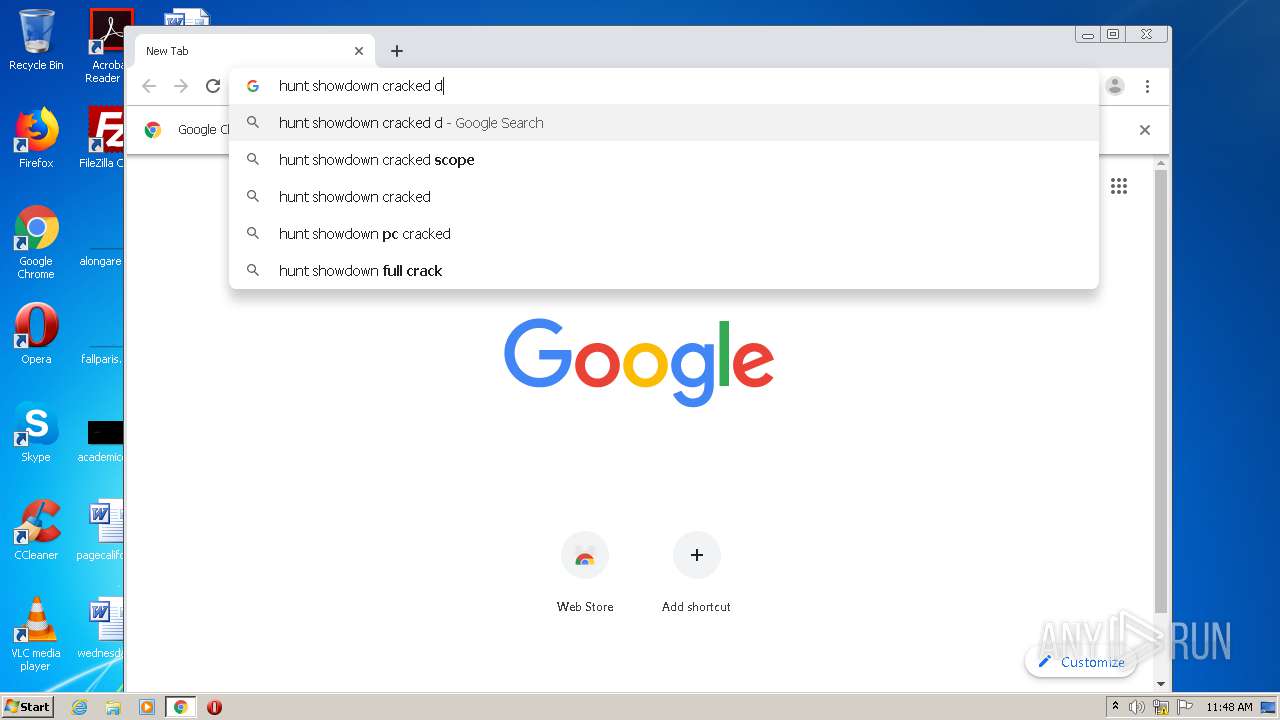
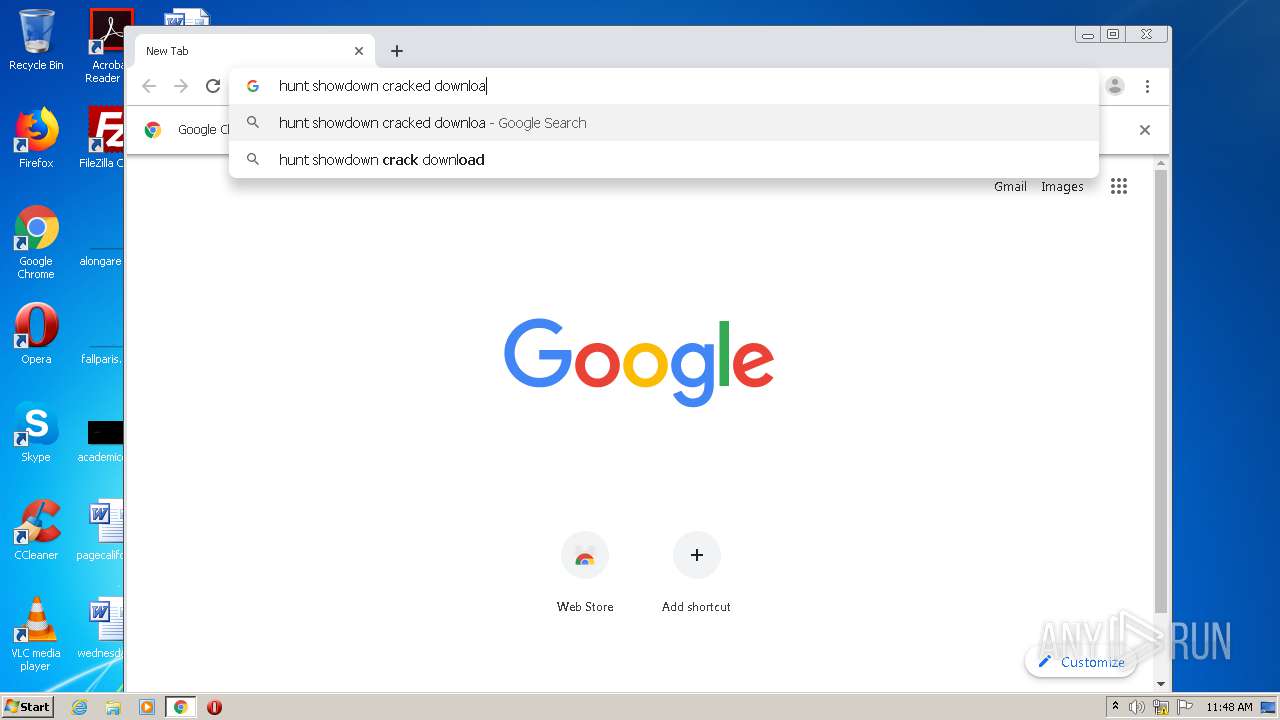
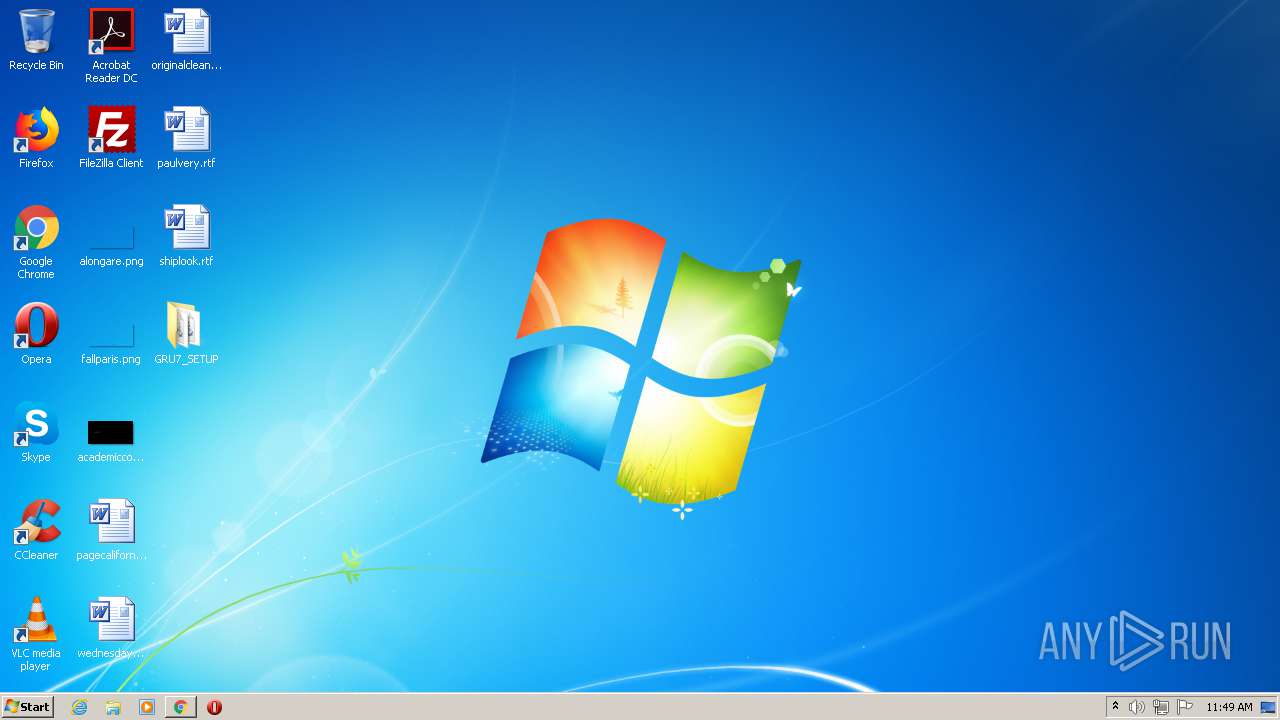
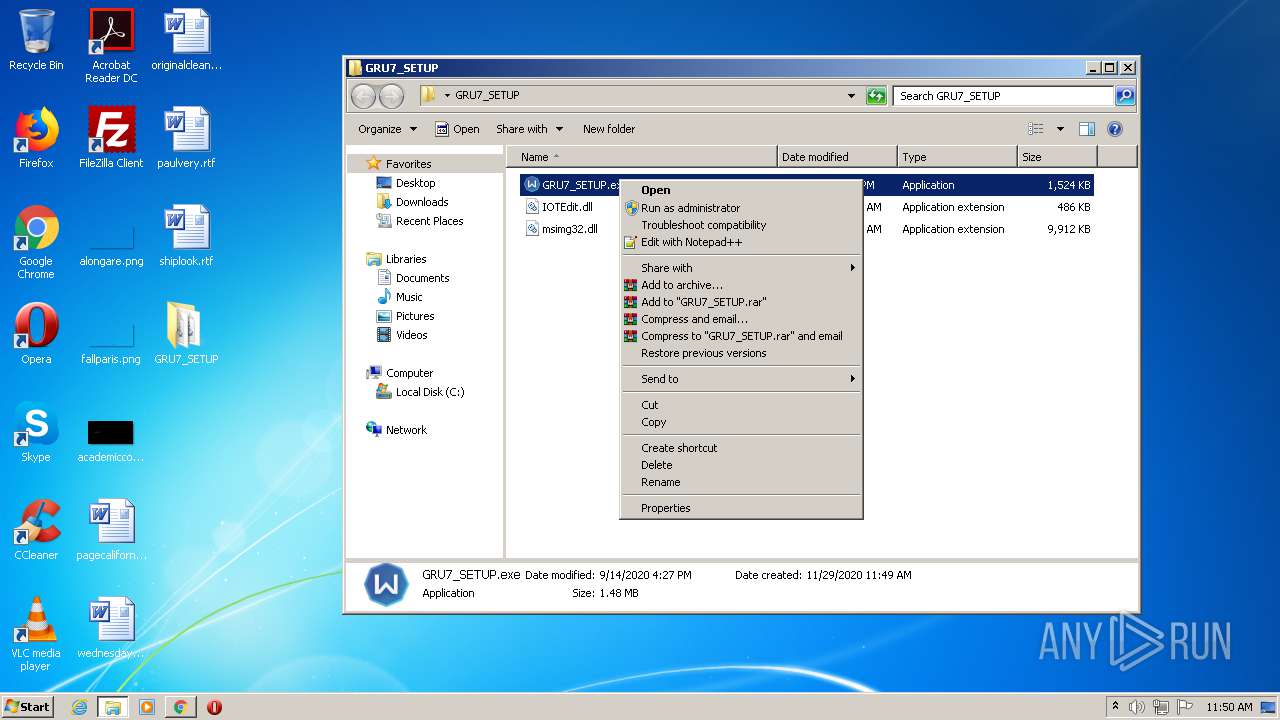
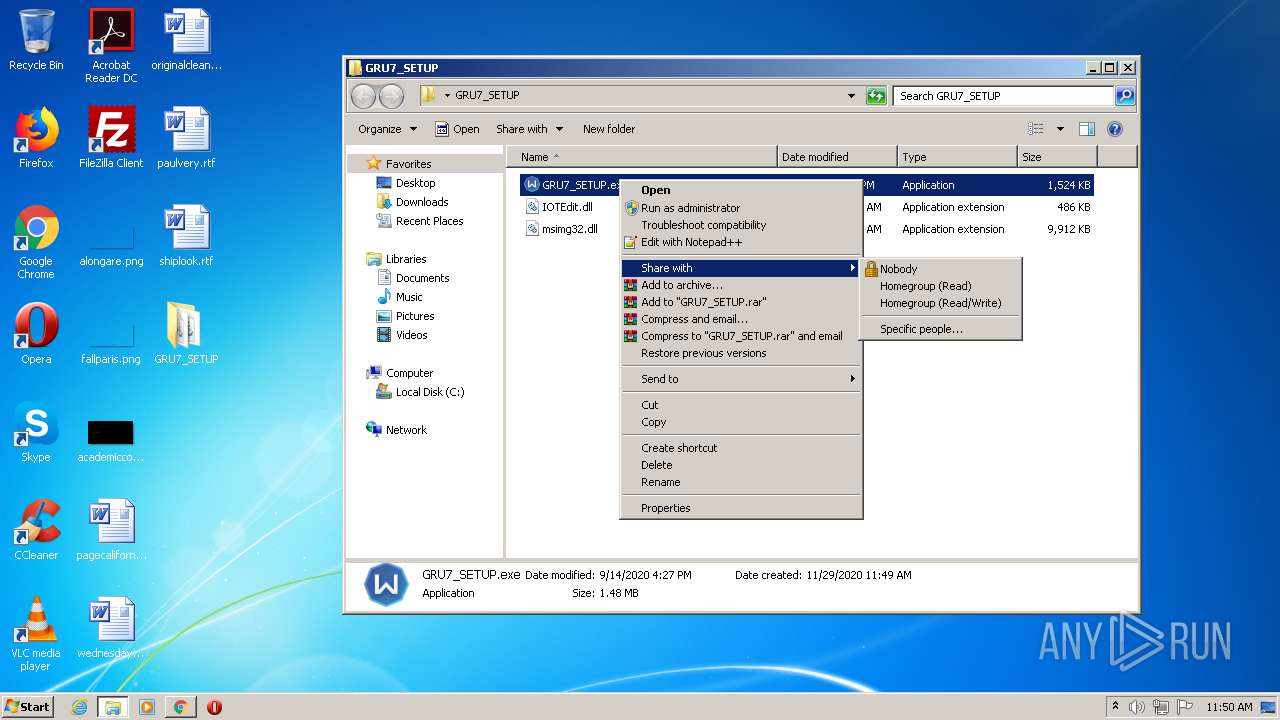
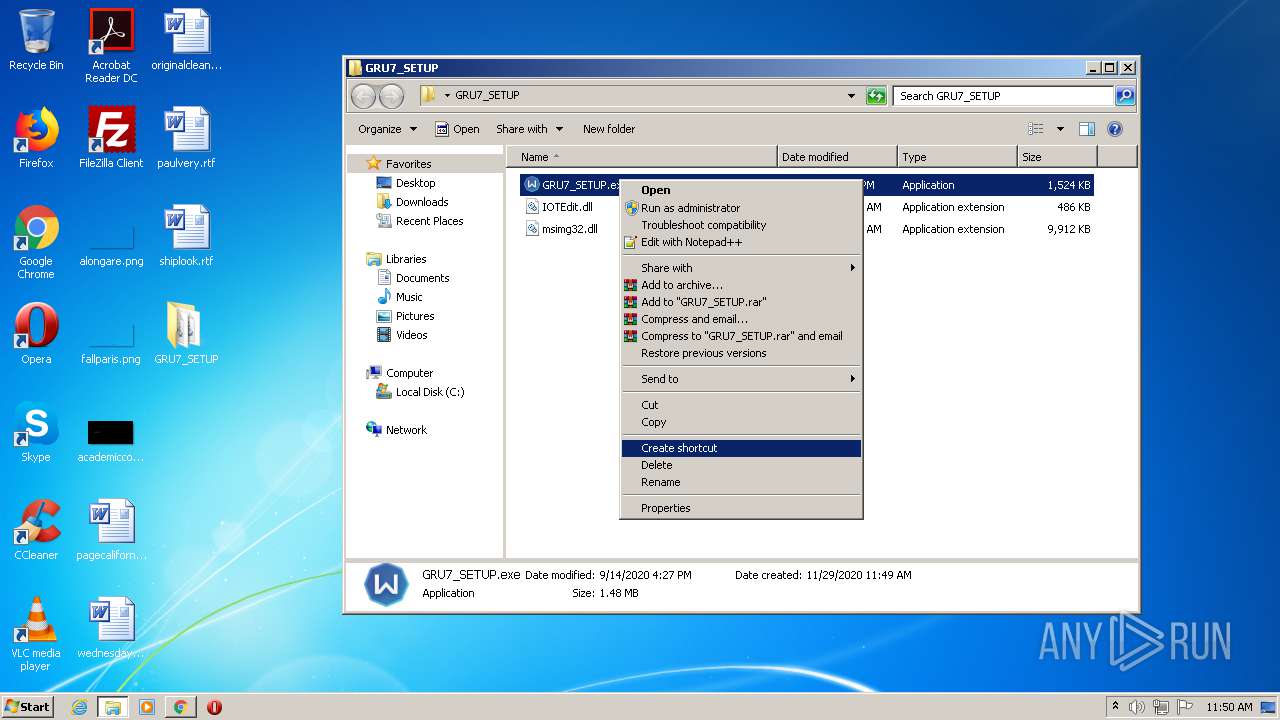
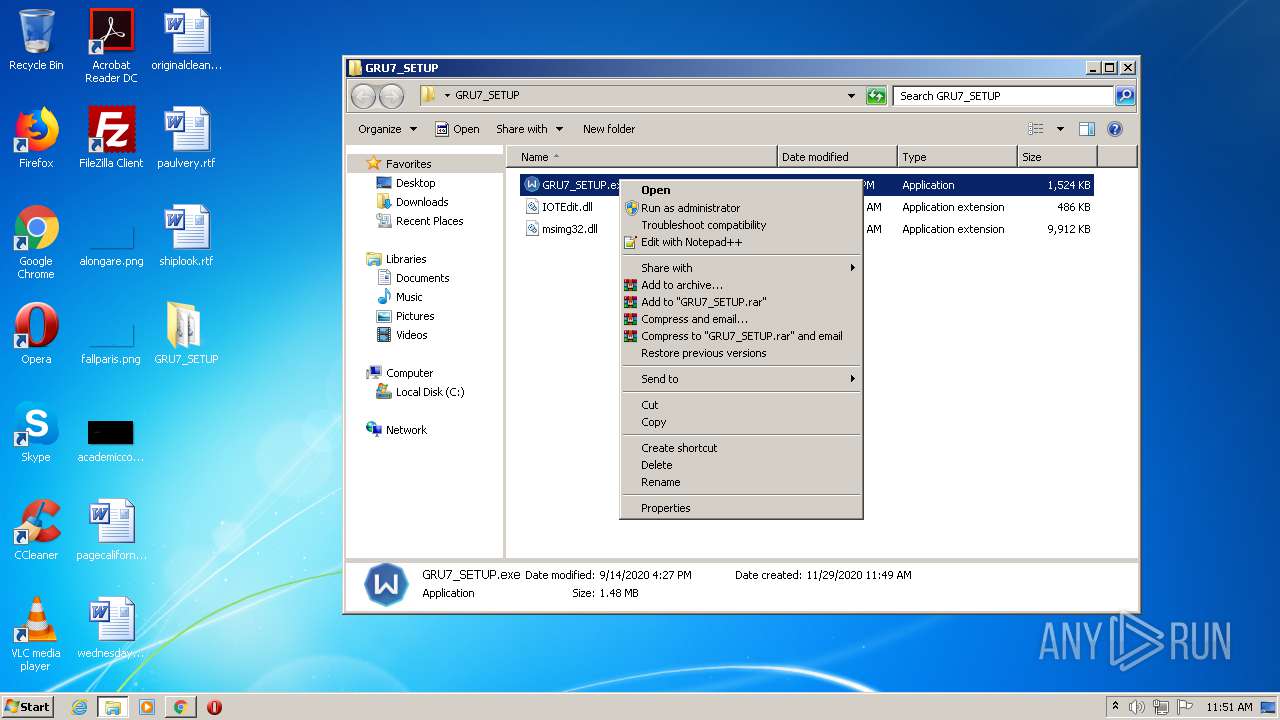
Manual execution by user
- chrome.exe (PID: 2076)
- GRU7_SETUP.exe (PID: 2256)
- GRU7_SETUP.exe (PID: 1704)
Reads the hosts file
- chrome.exe (PID: 2076)
- chrome.exe (PID: 3552)
Application launched itself
- chrome.exe (PID: 2076)
Reads settings of System Certificates
- chrome.exe (PID: 3552)
Changes settings of System certificates
- chrome.exe (PID: 3552)
Creates files in the user directory
- chrome.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .aiml | | | Artificial Intelligence Markup Language (82.8) |
|---|---|---|
| .html | | | HyperText Markup Language (17.1) |
Total processes
104
Monitored processes
62
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17303681766610072232 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2407324089707087132 --mojo-platform-channel-handle=3868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13702384581718201817 --mojo-platform-channel-handle=3440 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16701292359736267745 --mojo-platform-channel-handle=4084 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5079106320727469356 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11018384611160230609 --mojo-platform-channel-handle=3916 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7052559906765782643 --mojo-platform-channel-handle=3624 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,50450932101038393,13457148727975518885,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9952172161445037283 --mojo-platform-channel-handle=4296 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Users\admin\Desktop\GRU7_SETUP\GRU7_SETUP.exe" | C:\Users\admin\Desktop\GRU7_SETUP\GRU7_SETUP.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 3221225794 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
5 543
Read events
5 180
Write events
354
Delete events
9
Modification events
| (PID) Process: | (1780) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2076-13251124071619250 |
Value: 259 | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Puebzr |
Value: 000000000E0000001D000000403B1400000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFD035C67745C6D60100000000 | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000006A0000009D000000D55146001000000034000000869716007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000001CE5A3009B62D0760B7C6697FEFFFFFFFA53CB76F5F3C774E6F4C774245C13E1A8E5A300C110000000000000C00001000000000000000000A8E5A30024E5A3003851CB76C0000100820200000100000000000000000000006CE5A300D150CB76C00001008202000001000000E850CB7667CD0EE182020000E8A21C000000000000000000000000003CE5A300D0E5A300A8E7A3009B62D076FB786697FEFFFFFFE850CB762A00C874C000010082020000010000000000000000000000E8A21C0054FFC774C000010001000000FFFFFFFFFFFFFFFF90C5CB7641C6CB764E00000000000000000000000000000074E5A30011000000483D1700403D170003EE66971CA31C00FEC5CB7640E6000007C90EE1F4E5A3008291167740E6A300944C00002BC90EE108E6A300B69C1677984CCE024C06000020E6A3000848CE022CE6A30011000000483D1700403D170020E6A3002848CE0290E60000F3CA0EE140E6A3008291167790E6A30044E6A3002795167700000000944CCE026CE6A300CD941677944CCE0218E7A3000848CE02E1941677000000000848CE0218E7A30074E6A3001000000034000000869716007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000001CE5A3009B62D0760B7C6697FEFFFFFFFA53CB76F5F3C774E6F4C774245C13E1A8E5A300C110000000000000C00001000000000000000000A8E5A30024E5A3003851CB76C0000100820200000100000000000000000000006CE5A300D150CB76C00001008202000001000000E850CB7667CD0EE182020000E8A21C000000000000000000000000003CE5A300D0E5A300A8E7A3009B62D076FB786697FEFFFFFFE850CB762A00C874C000010082020000010000000000000000000000E8A21C0054FFC774C000010001000000FFFFFFFFFFFFFFFF90C5CB7641C6CB764E00000000000000000000000000000074E5A30011000000483D1700403D170003EE66971CA31C00FEC5CB7640E6000007C90EE1F4E5A3008291167740E6A300944C00002BC90EE108E6A300B69C1677984CCE024C06000020E6A3000848CE022CE6A30011000000483D1700403D170020E6A3002848CE0290E60000F3CA0EE140E6A3008291167790E6A30044E6A3002795167700000000944CCE026CE6A300CD941677944CCE0218E7A3000848CE02E1941677000000000848CE0218E7A30074E6A3001000000034000000869716007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000001CE5A3009B62D0760B7C6697FEFFFFFFFA53CB76F5F3C774E6F4C774245C13E1A8E5A300C110000000000000C00001000000000000000000A8E5A30024E5A3003851CB76C0000100820200000100000000000000000000006CE5A300D150CB76C00001008202000001000000E850CB7667CD0EE182020000E8A21C000000000000000000000000003CE5A300D0E5A300A8E7A3009B62D076FB786697FEFFFFFFE850CB762A00C874C000010082020000010000000000000000000000E8A21C0054FFC774C000010001000000FFFFFFFFFFFFFFFF90C5CB7641C6CB764E00000000000000000000000000000074E5A30011000000483D1700403D170003EE66971CA31C00FEC5CB7640E6000007C90EE1F4E5A3008291167740E6A300944C00002BC90EE108E6A300B69C1677984CCE024C06000020E6A3000848CE022CE6A30011000000483D1700403D170020E6A3002848CE0290E60000F3CA0EE140E6A3008291167790E6A30044E6A3002795167700000000944CCE026CE6A300CD941677944CCE0218E7A3000848CE02E1941677000000000848CE0218E7A30074E6A300 | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000080000000000000007000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFD035C67745C6D60100000000 | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003300000000000000320000001000000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000000000000C4D4B4030BA03476E01F3A0310612C03800200000D0000002F000000AF020000E01F3A03E4D4B40343194F768F223A03D8002B035E000000E01F3A0310612C03AF020000B8F94E7690EB330690EB3306F4D4B40364194F7610612C03D8002B038CD9B403BF434F7610612C030000000000000000FFFFFFFF000000000000000000000000D8002B03F0002B03D8002B031A012B0300000000000000000000000000004F76F024280688062B03D8D9B403BF434F76F02428060000000000000000FFFFFFFF00000000000000000000000088062B03A0062B0388062B03CA062B03A6000000A8138C0198D5B40333AB7577A8C744040C0C0000102700001B000000DB560200CCD5B403F8AA7577DB560200A8138C01ECD5B403400F23026CD6B40300000000A40100002CD60000153E7714DCD5B40382914F762CD6B403E0D5B40327954F7600000000CC13230208D6B403CD944F76CC132302B4D6B403400F2302E1944F7600000000400F2302B4D6B40310D6B4031000000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000000000000C4D4B4030BA03476E01F3A0310612C03800200000D0000002F000000AF020000E01F3A03E4D4B40343194F768F223A03D8002B035E000000E01F3A0310612C03AF020000B8F94E7690EB330690EB3306F4D4B40364194F7610612C03D8002B038CD9B403BF434F7610612C030000000000000000FFFFFFFF000000000000000000000000D8002B03F0002B03D8002B031A012B0300000000000000000000000000004F76F024280688062B03D8D9B403BF434F76F02428060000000000000000FFFFFFFF00000000000000000000000088062B03A0062B0388062B03CA062B03A6000000A8138C0198D5B40333AB7577A8C744040C0C0000102700001B000000DB560200CCD5B403F8AA7577DB560200A8138C01ECD5B403400F23026CD6B40300000000A40100002CD60000153E7714DCD5B40382914F762CD6B403E0D5B40327954F7600000000CC13230208D6B403CD944F76CC132302B4D6B403400F2302E1944F7600000000400F2302B4D6B40310D6B4031000000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000000000000C4D4B4030BA03476E01F3A0310612C03800200000D0000002F000000AF020000E01F3A03E4D4B40343194F768F223A03D8002B035E000000E01F3A0310612C03AF020000B8F94E7690EB330690EB3306F4D4B40364194F7610612C03D8002B038CD9B403BF434F7610612C030000000000000000FFFFFFFF000000000000000000000000D8002B03F0002B03D8002B031A012B0300000000000000000000000000004F76F024280688062B03D8D9B403BF434F76F02428060000000000000000FFFFFFFF00000000000000000000000088062B03A0062B0388062B03CA062B03A6000000A8138C0198D5B40333AB7577A8C744040C0C0000102700001B000000DB560200CCD5B403F8AA7577DB560200A8138C01ECD5B403400F23026CD6B40300000000A40100002CD60000153E7714DCD5B40382914F762CD6B403E0D5B40327954F7600000000CC13230208D6B403CD944F76CC132302B4D6B403400F2302E1944F7600000000400F2302B4D6B40310D6B403 | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Tbbtyr Puebzr.yax |
Value: 00000000080000000000000008000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFD035C67745C6D60100000000 | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003300000000000000330000001000000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000000000000C4D4B4030BA03476E01F3A0310612C03800200000D0000002F000000AF020000E01F3A03E4D4B40343194F768F223A03D8002B035E000000E01F3A0310612C03AF020000B8F94E7690EB330690EB3306F4D4B40364194F7610612C03D8002B038CD9B403BF434F7610612C030000000000000000FFFFFFFF000000000000000000000000D8002B03F0002B03D8002B031A012B0300000000000000000000000000004F76F024280688062B03D8D9B403BF434F76F02428060000000000000000FFFFFFFF00000000000000000000000088062B03A0062B0388062B03CA062B03A6000000A8138C0198D5B40333AB7577A8C744040C0C0000102700001B000000DB560200CCD5B403F8AA7577DB560200A8138C01ECD5B403400F23026CD6B40300000000A40100002CD60000153E7714DCD5B40382914F762CD6B403E0D5B40327954F7600000000CC13230208D6B403CD944F76CC132302B4D6B403400F2302E1944F7600000000400F2302B4D6B40310D6B4031000000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000000000000C4D4B4030BA03476E01F3A0310612C03800200000D0000002F000000AF020000E01F3A03E4D4B40343194F768F223A03D8002B035E000000E01F3A0310612C03AF020000B8F94E7690EB330690EB3306F4D4B40364194F7610612C03D8002B038CD9B403BF434F7610612C030000000000000000FFFFFFFF000000000000000000000000D8002B03F0002B03D8002B031A012B0300000000000000000000000000004F76F024280688062B03D8D9B403BF434F76F02428060000000000000000FFFFFFFF00000000000000000000000088062B03A0062B0388062B03CA062B03A6000000A8138C0198D5B40333AB7577A8C744040C0C0000102700001B000000DB560200CCD5B403F8AA7577DB560200A8138C01ECD5B403400F23026CD6B40300000000A40100002CD60000153E7714DCD5B40382914F762CD6B403E0D5B40327954F7600000000CC13230208D6B403CD944F76CC132302B4D6B403400F2302E1944F7600000000400F2302B4D6B40310D6B4031000000000000000100000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B00000000000000C4D4B4030BA03476E01F3A0310612C03800200000D0000002F000000AF020000E01F3A03E4D4B40343194F768F223A03D8002B035E000000E01F3A0310612C03AF020000B8F94E7690EB330690EB3306F4D4B40364194F7610612C03D8002B038CD9B403BF434F7610612C030000000000000000FFFFFFFF000000000000000000000000D8002B03F0002B03D8002B031A012B0300000000000000000000000000004F76F024280688062B03D8D9B403BF434F76F02428060000000000000000FFFFFFFF00000000000000000000000088062B03A0062B0388062B03CA062B03A6000000A8138C0198D5B40333AB7577A8C744040C0C0000102700001B000000DB560200CCD5B403F8AA7577DB560200A8138C01ECD5B403400F23026CD6B40300000000A40100002CD60000153E7714DCD5B40382914F762CD6B403E0D5B40327954F7600000000CC13230208D6B403CD944F76CC132302B4D6B403400F2302E1944F7600000000400F2302B4D6B40310D6B403 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
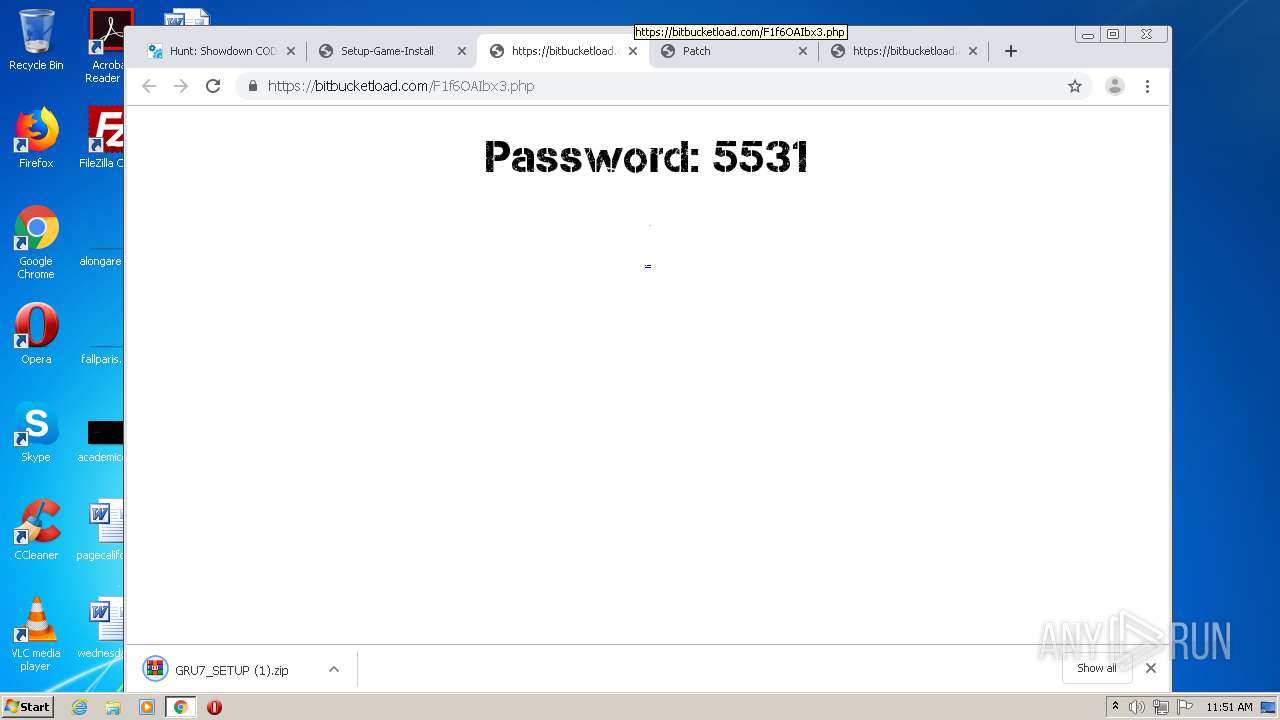
Executable files
6
Suspicious files
189
Text files
333
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC38A68-81C.pma | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3c9614ec-5917-4d3a-9e98-61678d0a73f7.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF128f57.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1290ce.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
88
DNS requests
66
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
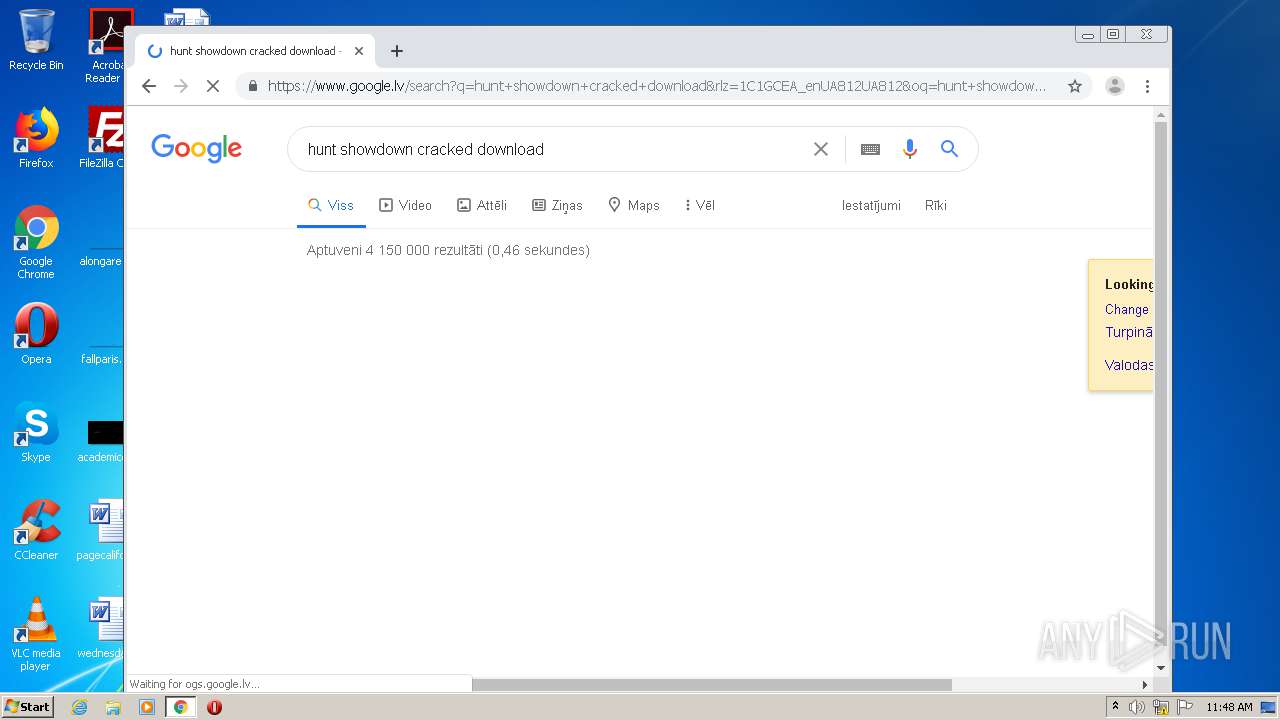
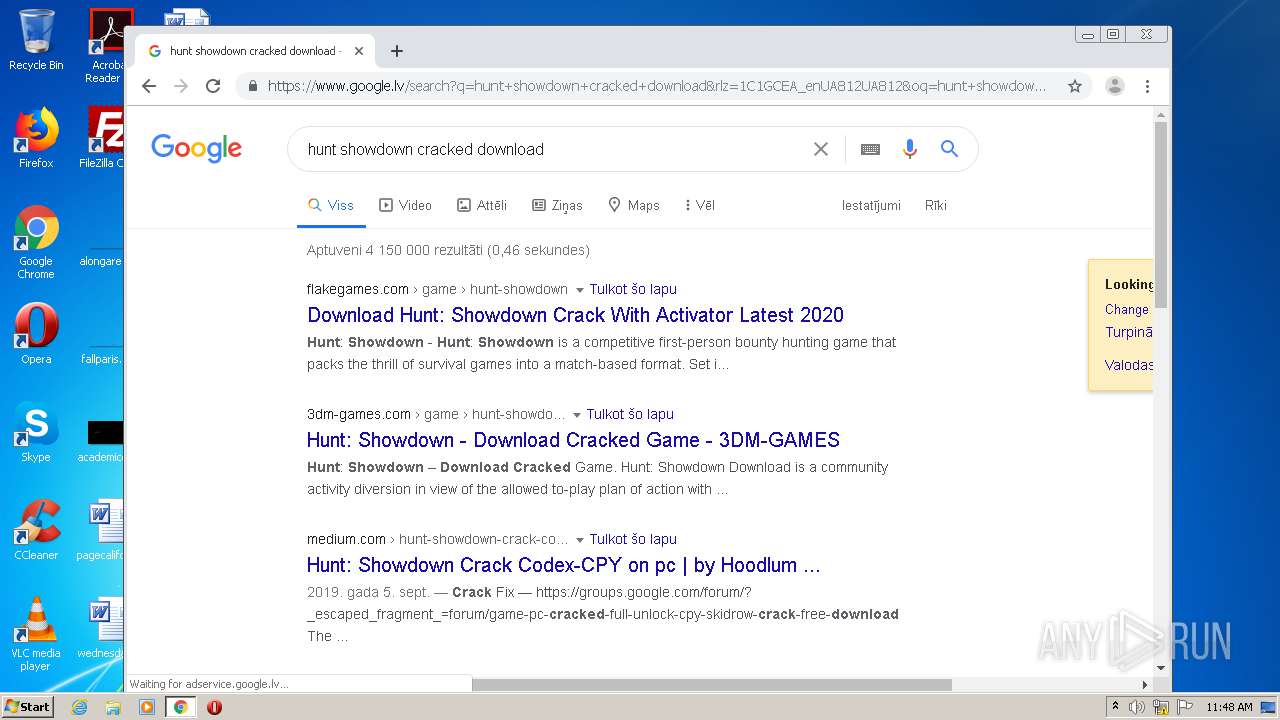
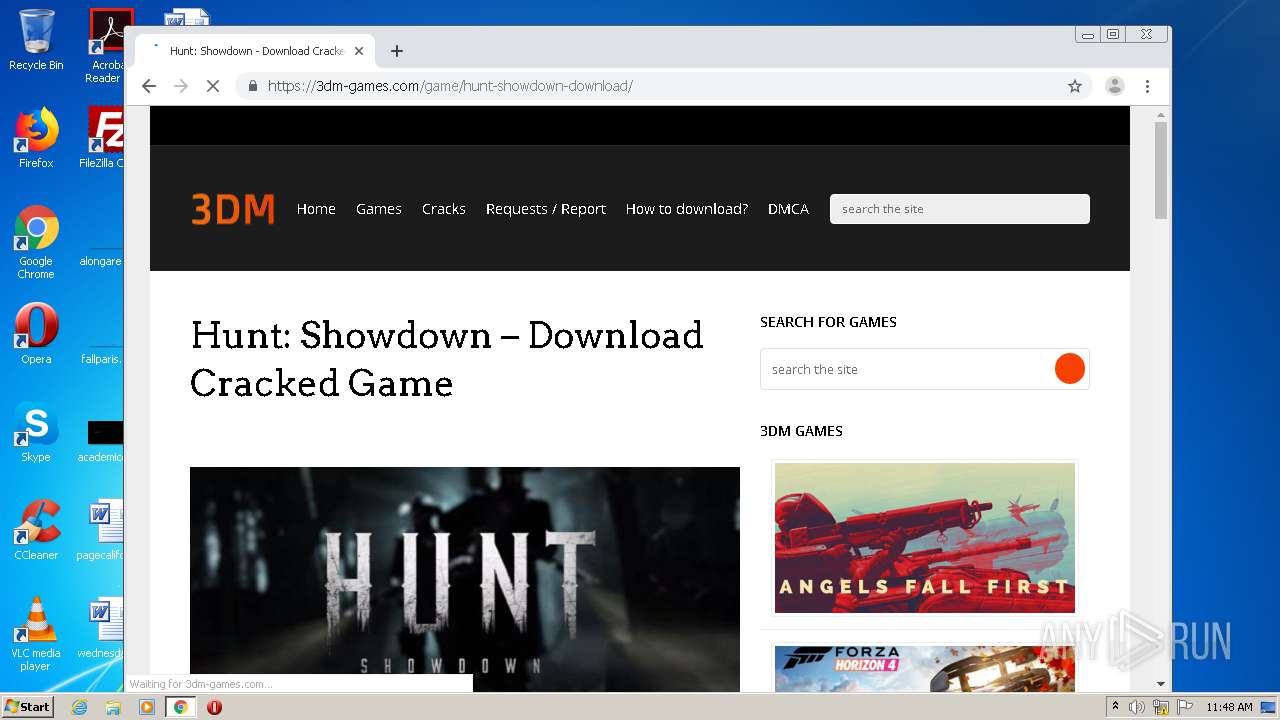
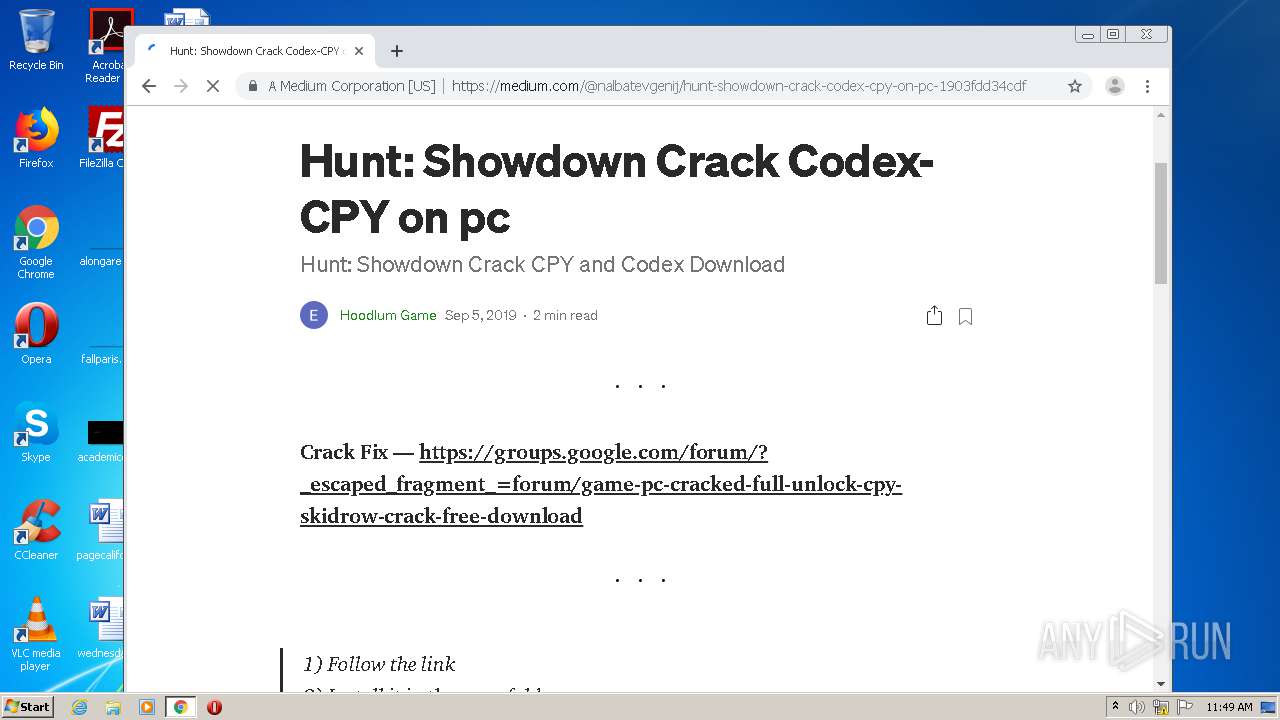
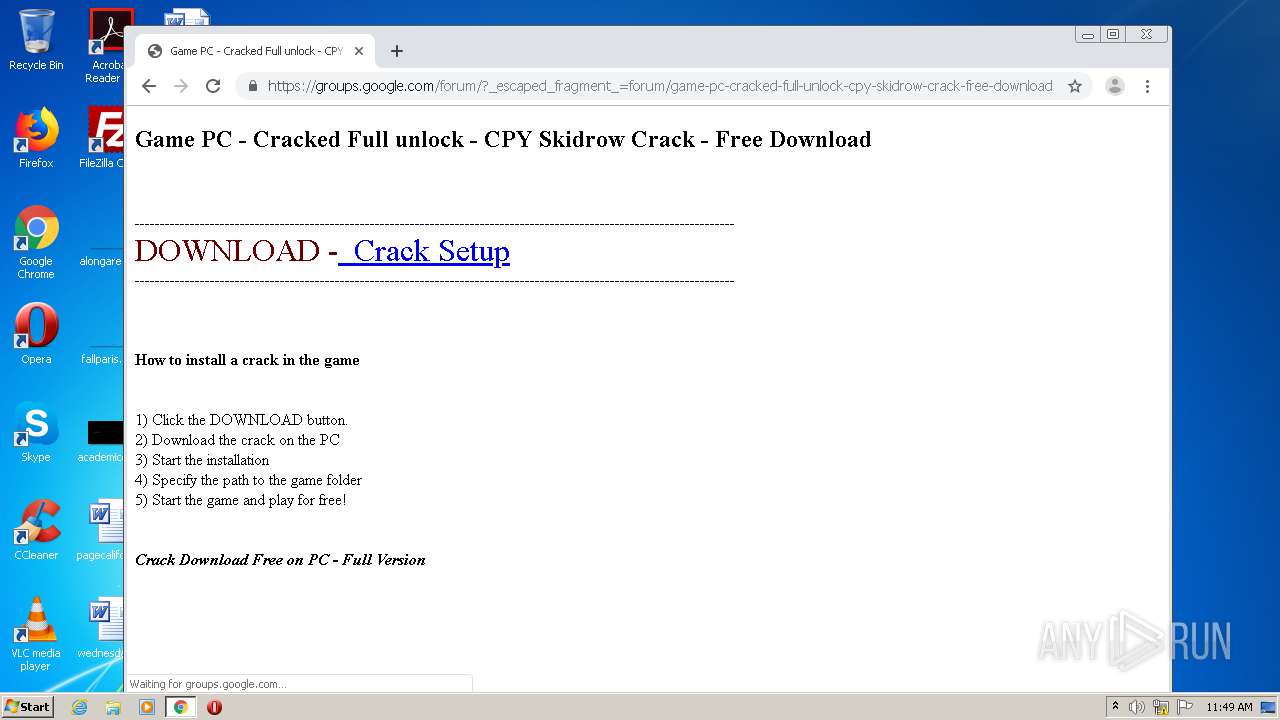
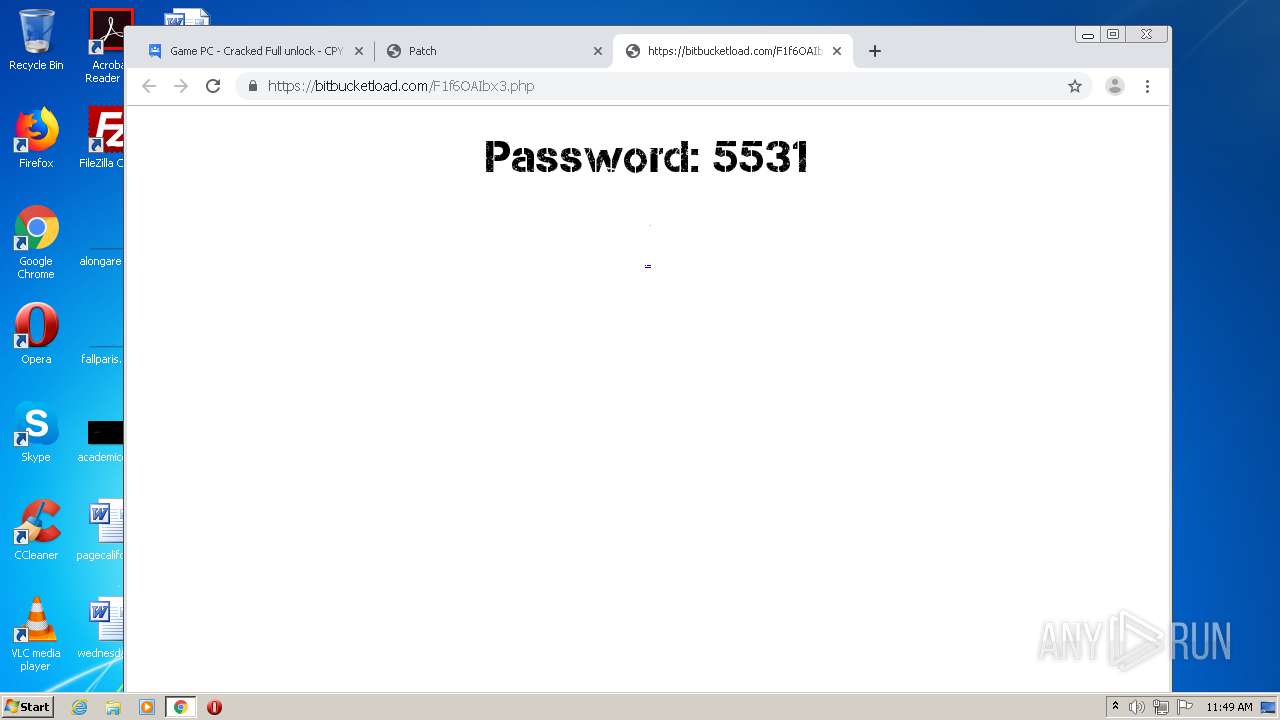
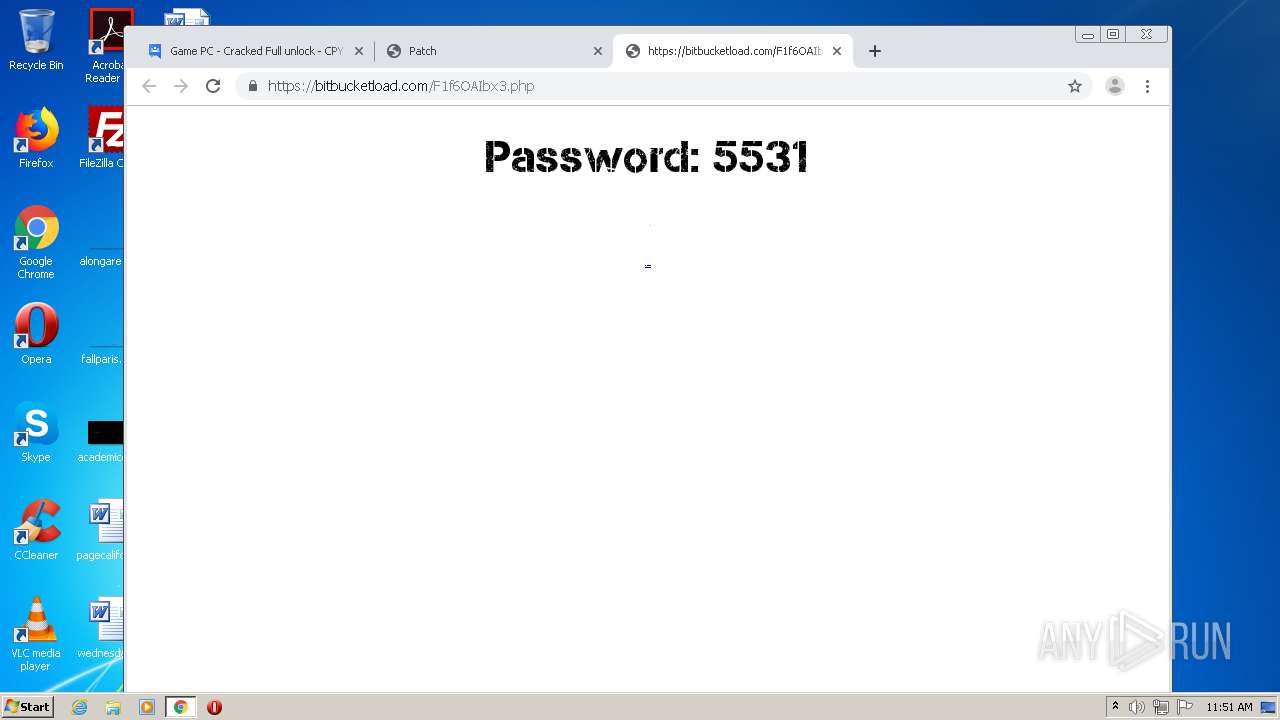
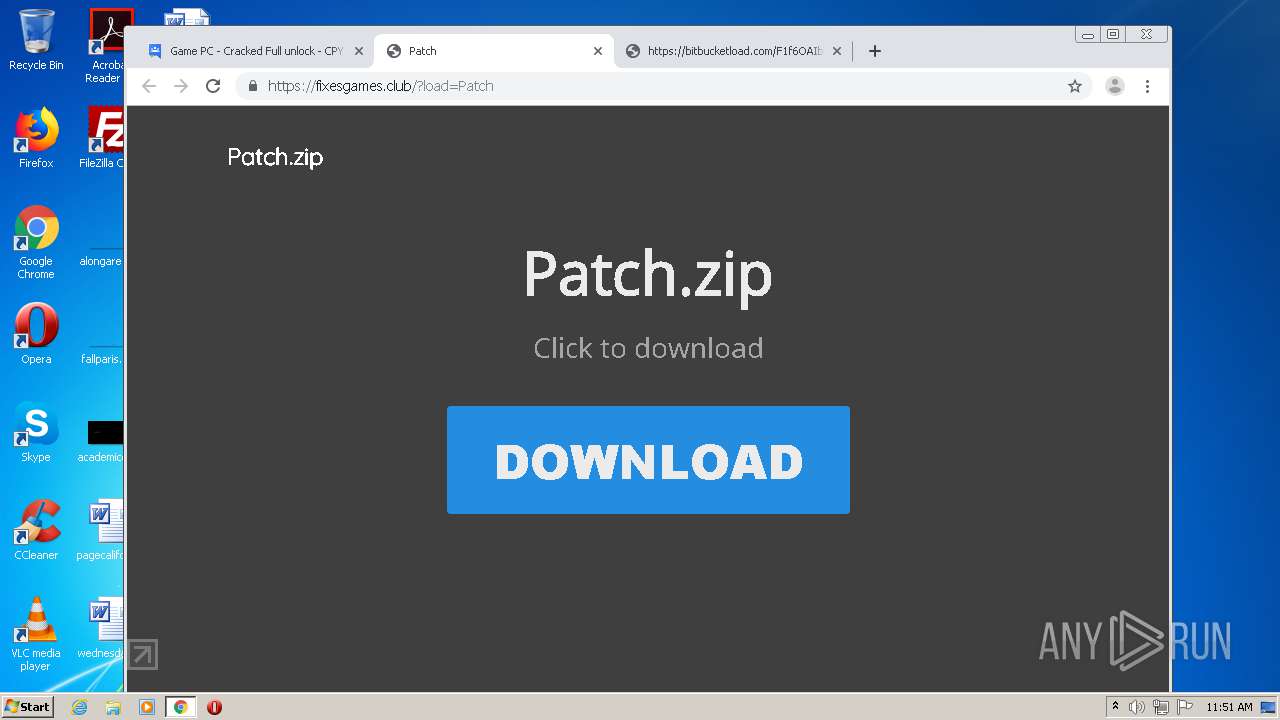
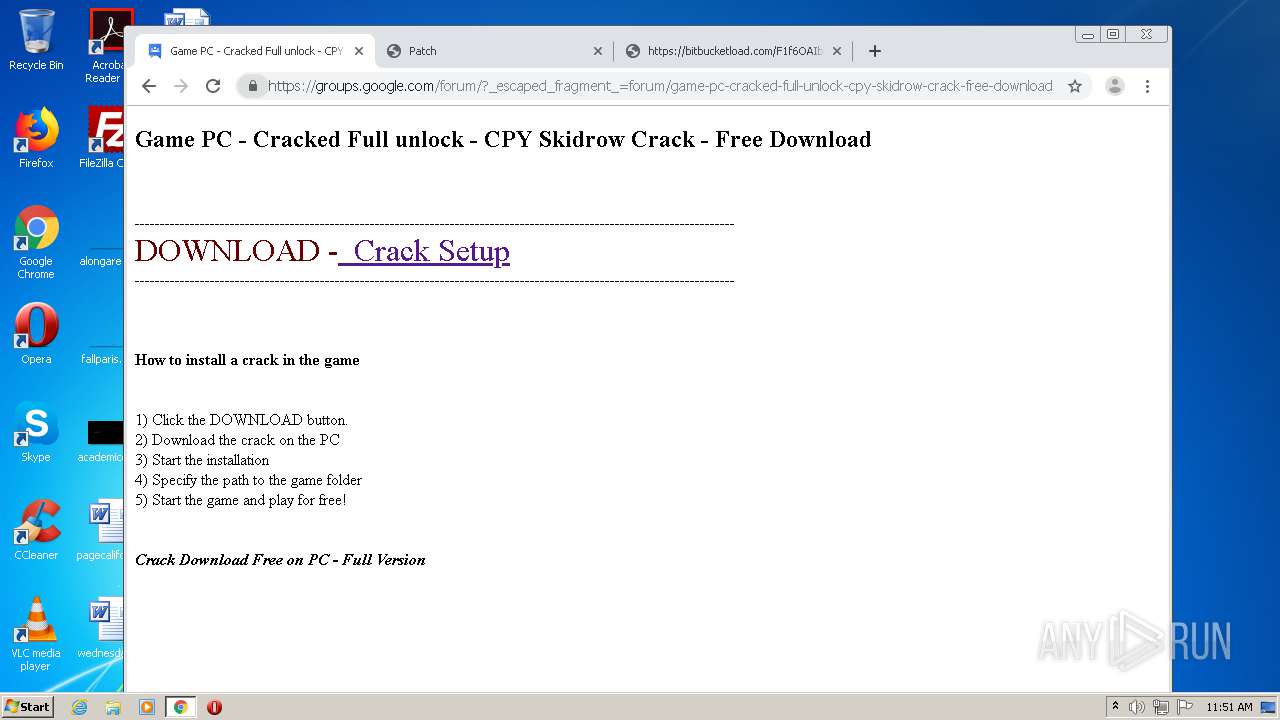
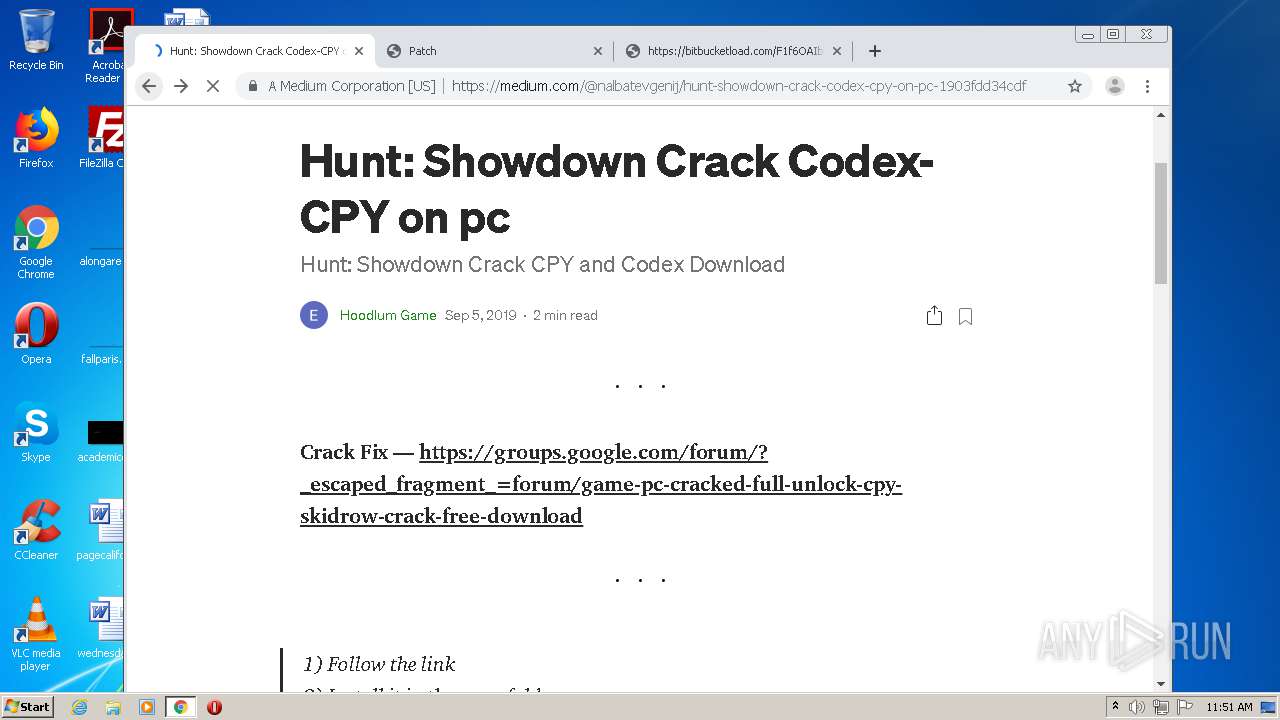
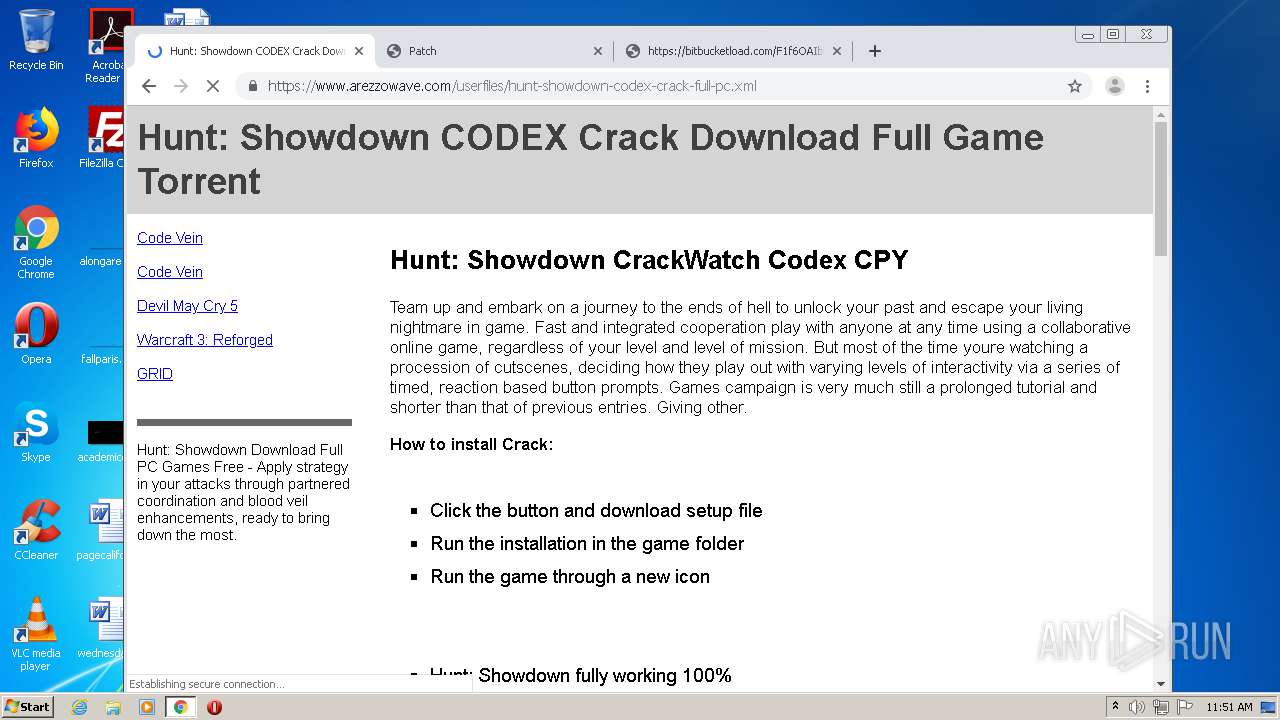
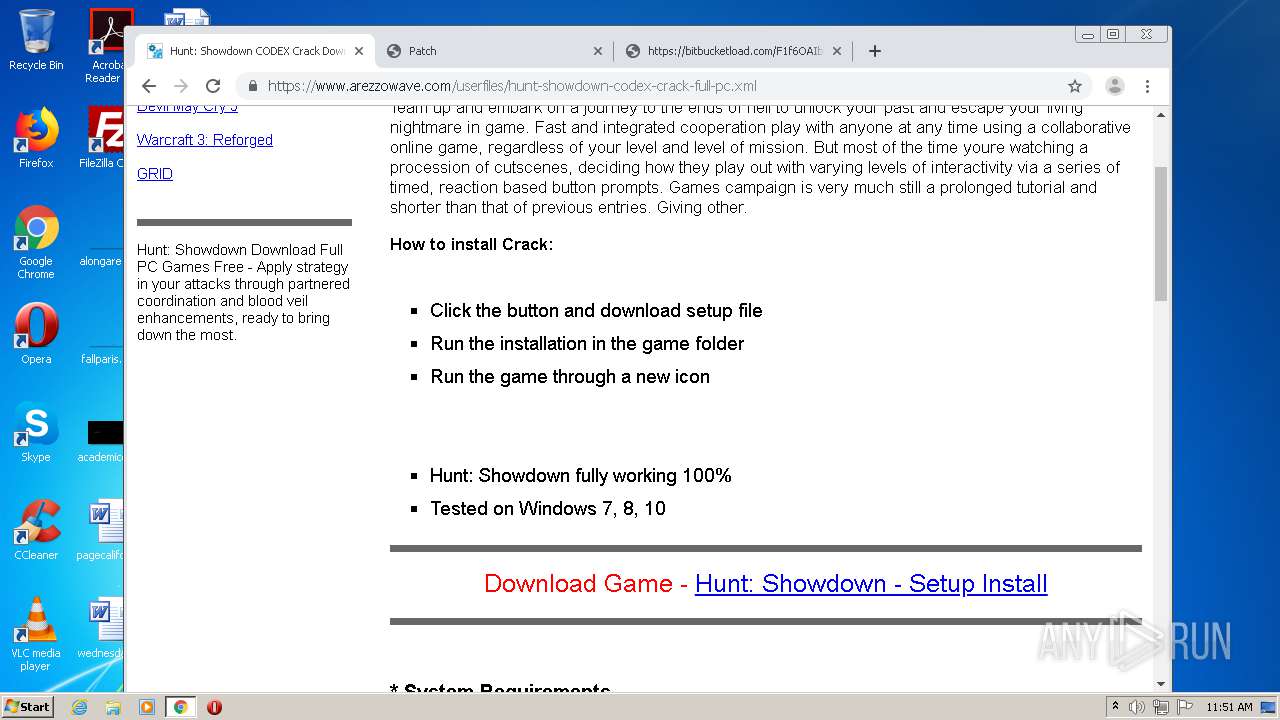
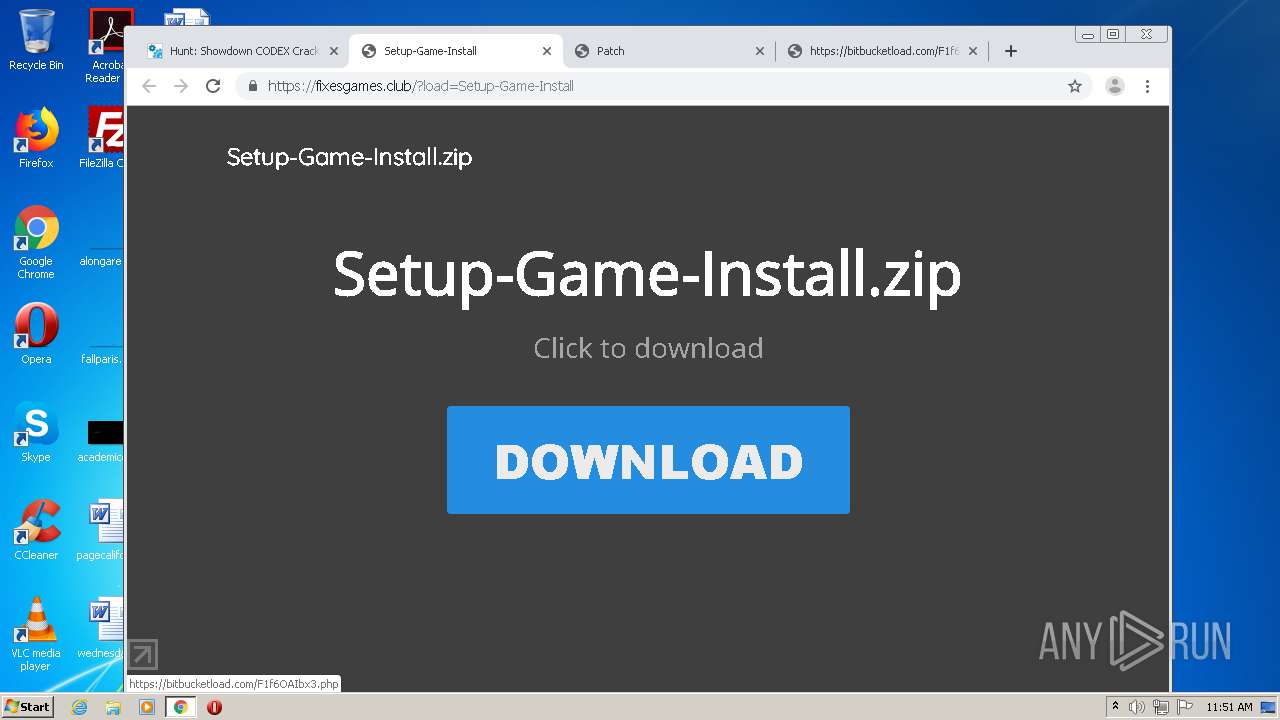
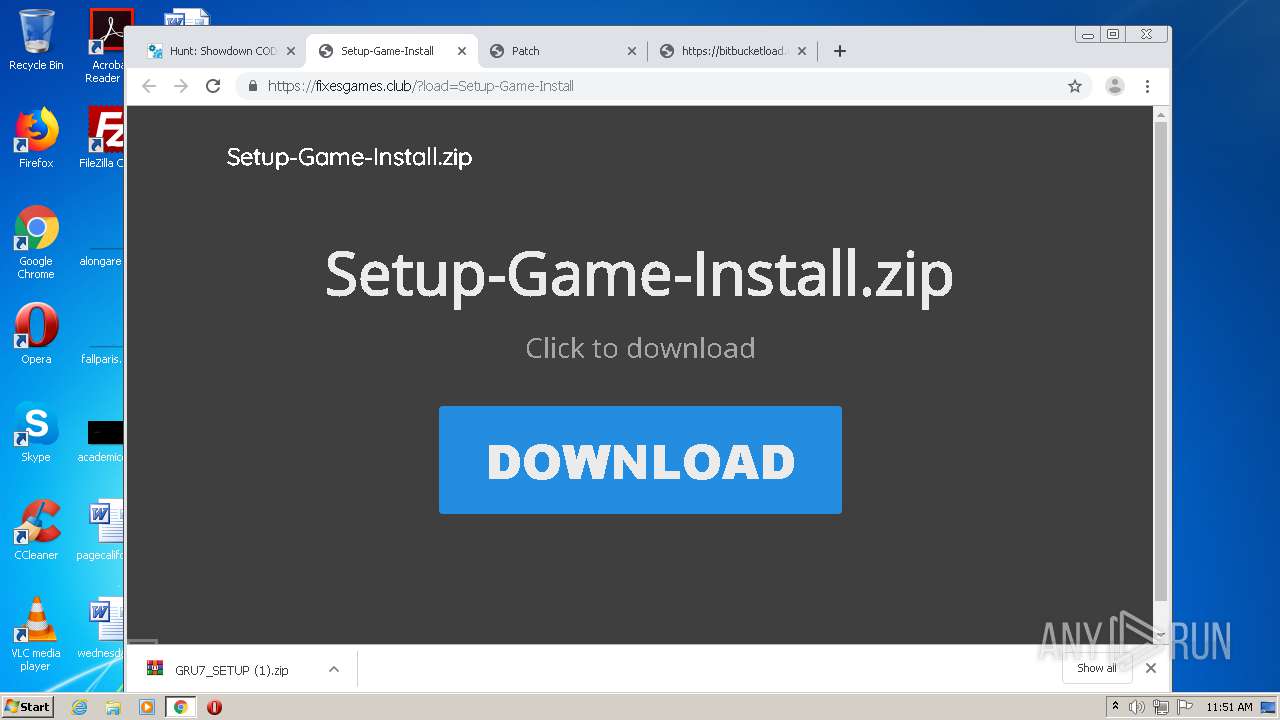
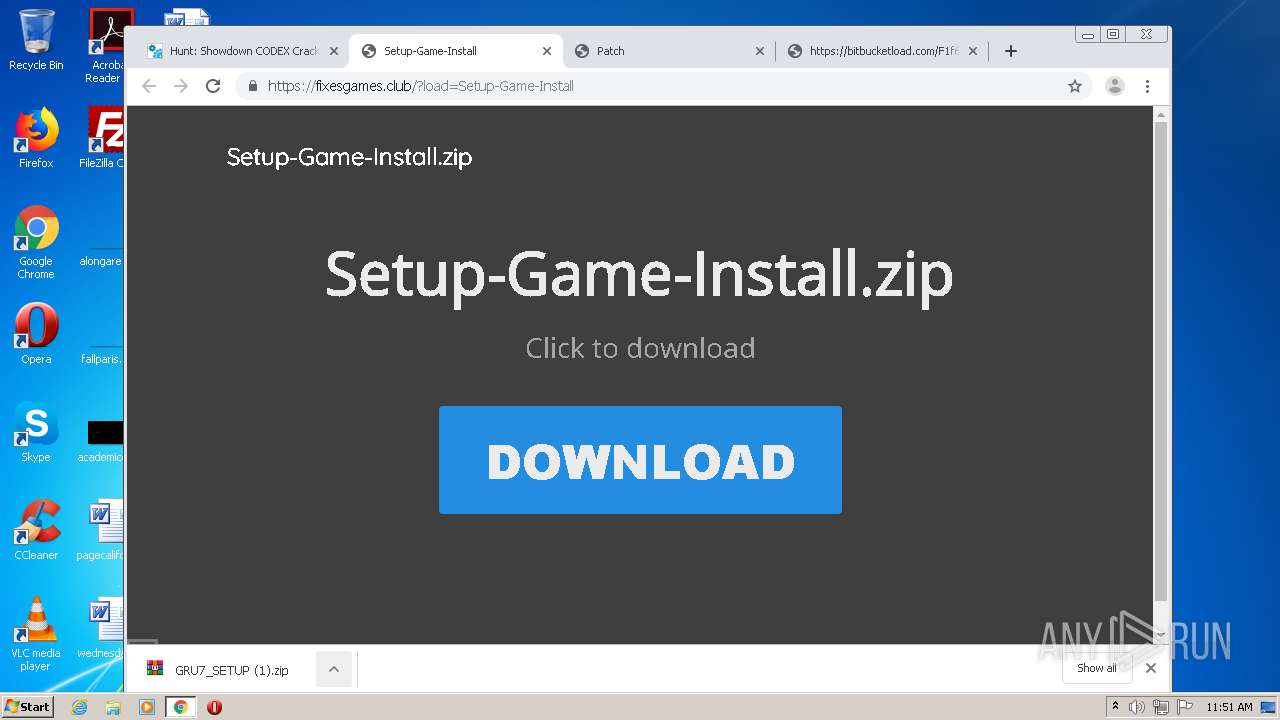
3552 | chrome.exe | GET | 302 | 104.27.130.174:80 | http://game03-com.ru/?load=Setup-Game-Install | US | — | — | suspicious |
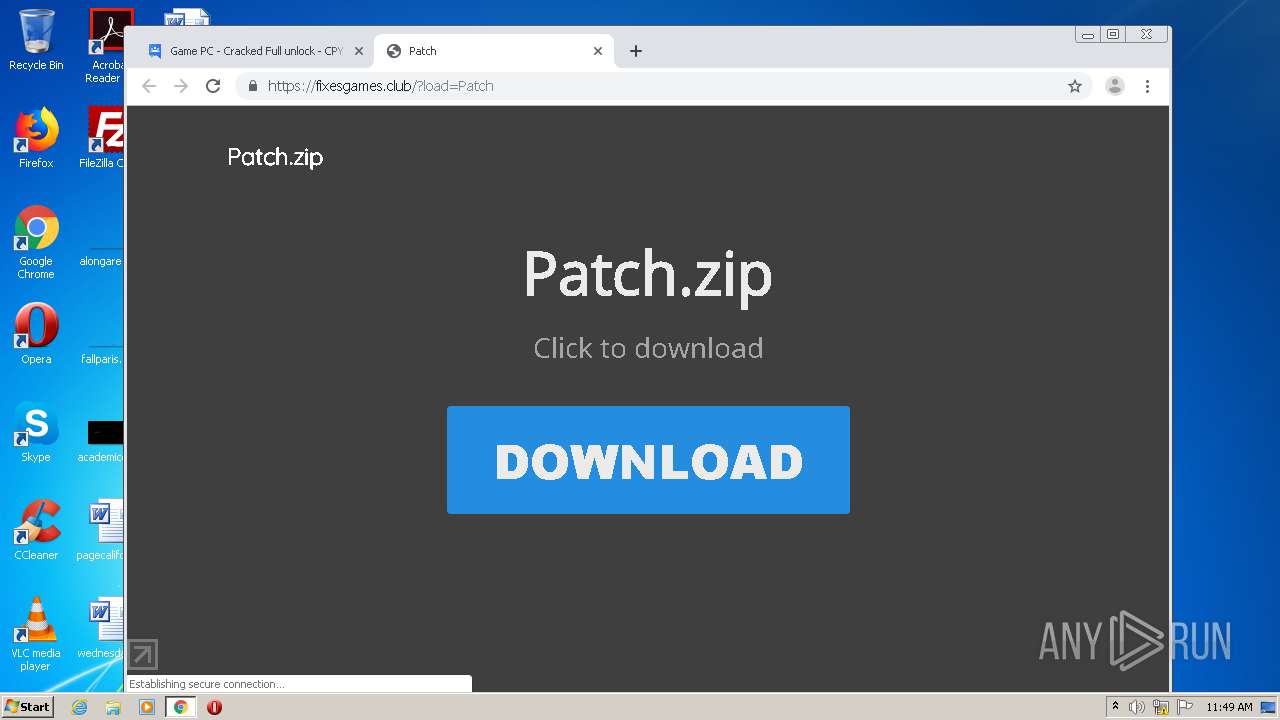
3552 | chrome.exe | GET | 302 | 104.28.20.155:80 | http://game01-com.ru/?load=Patch | US | — | — | shared |
3552 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAin4%2FbvIHa7uGRi8LVPooE%3D | US | der | 471 b | whitelisted |
3552 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3552 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSADomainValidationSecureServerCA.crt | GB | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3552 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 216.58.207.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.16.174:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3552 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3552 | chrome.exe | 216.58.210.14:443 | consent.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |