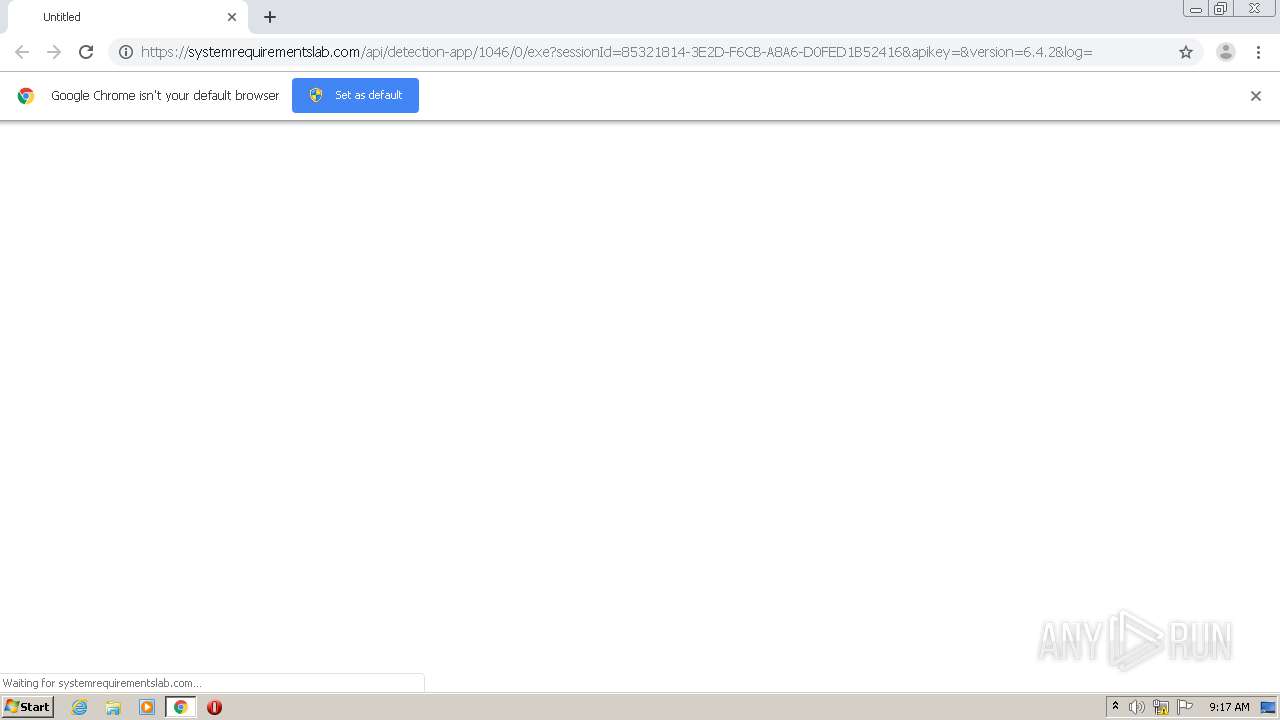
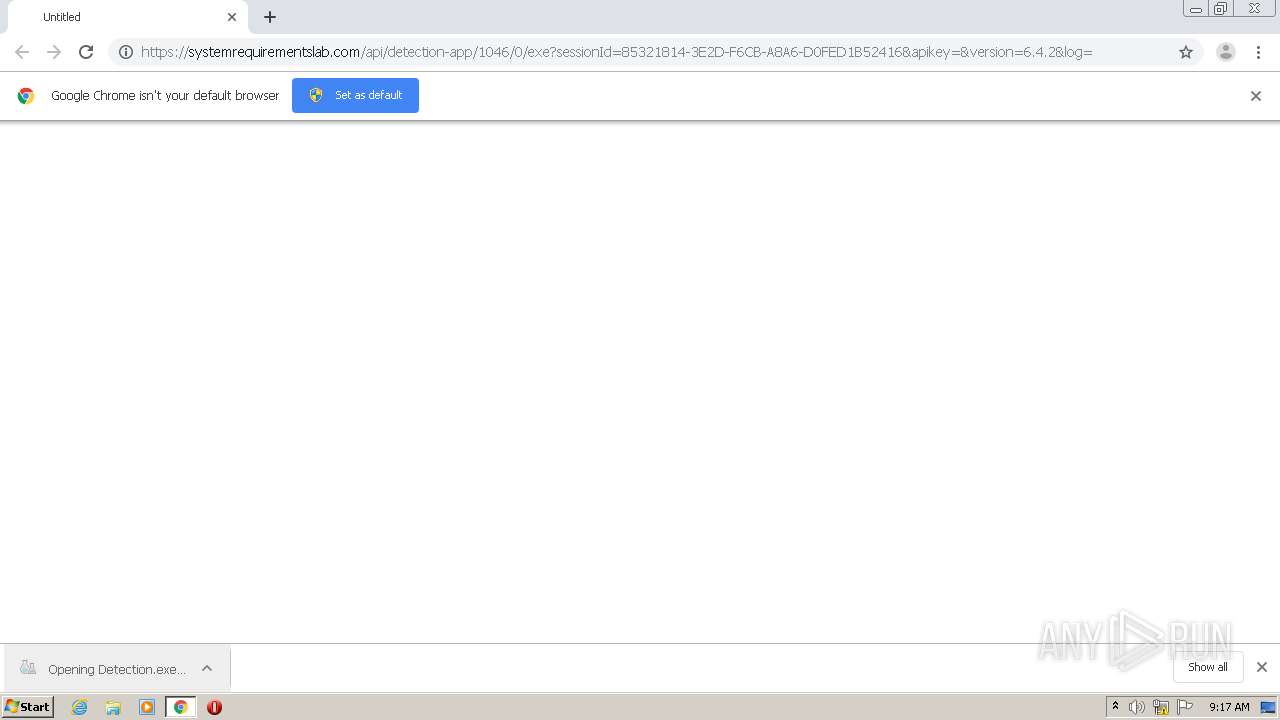
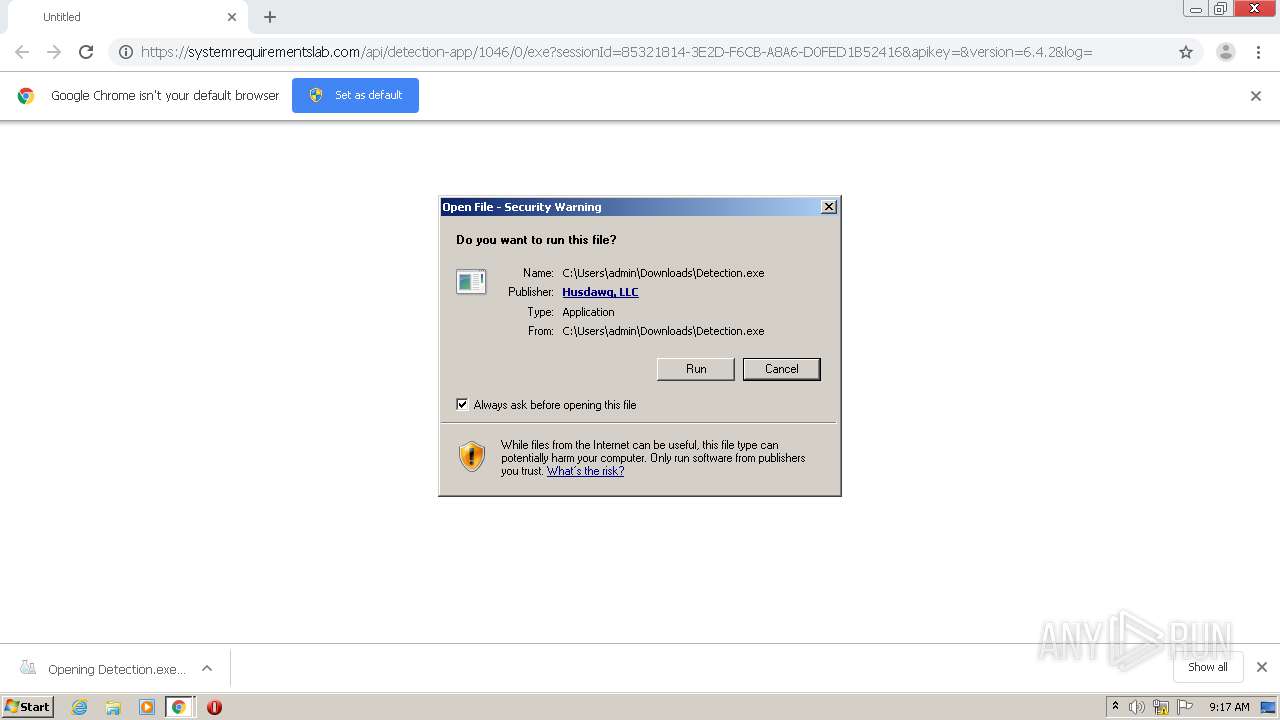
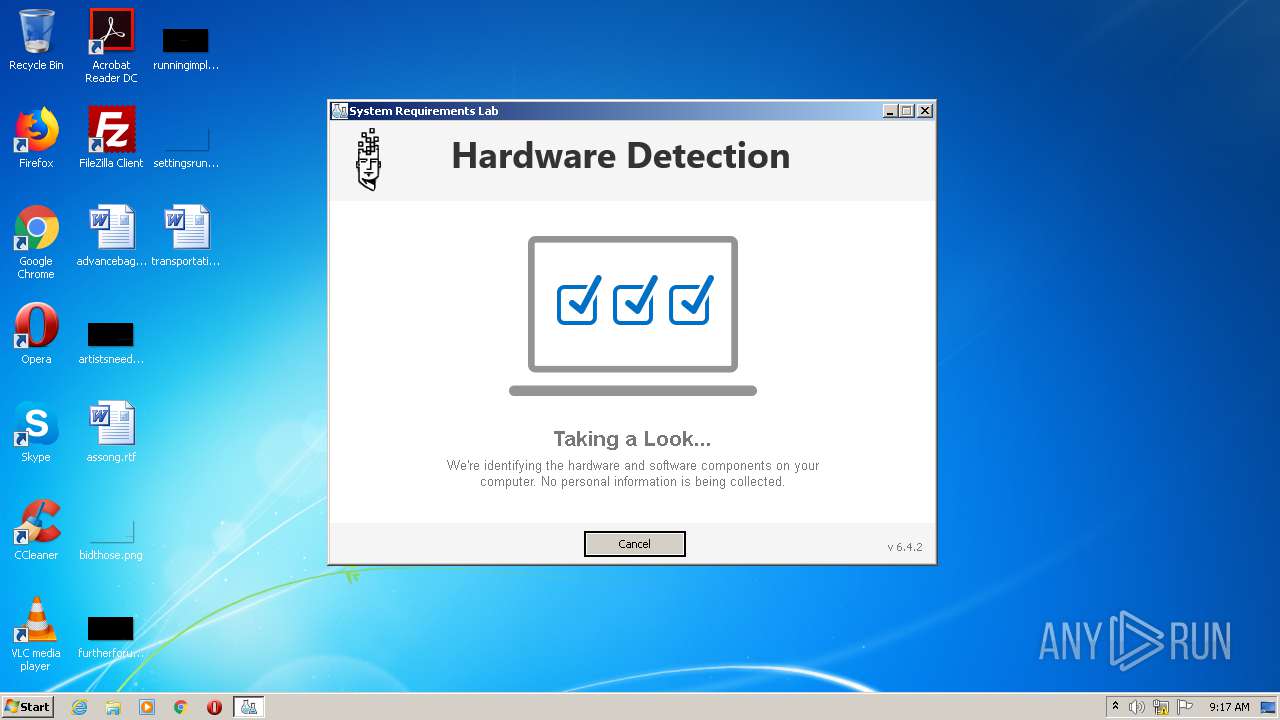
| URL: | https://systemrequirementslab.com/api/detection-app/1046/0/exe?sessionId=85321814-3E2D-F6CB-A8A6-D0FED1B52416&apikey=&version=6.4.2&log= |
| Full analysis: | https://app.any.run/tasks/df6c65f0-e866-4921-8d2c-0a912d6042ad |
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2020, 08:16:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B4E85E1C2B024AC813EF02BE8DDA8871 |
| SHA1: | 57EC28C504E8F7DB2B75E49A4F3986EC720737CA |
| SHA256: | 2333008FBC65EF503086E78C24C51922F3395C1D807D62E4545758BF4058EFCB |
| SSDEEP: | 3:N8RWtQUY8OE92TzRyfW+swQQgFaMEYPFLsTLtTECY:2kaL3E8Ry+rwQPa+sL6b |
MALICIOUS
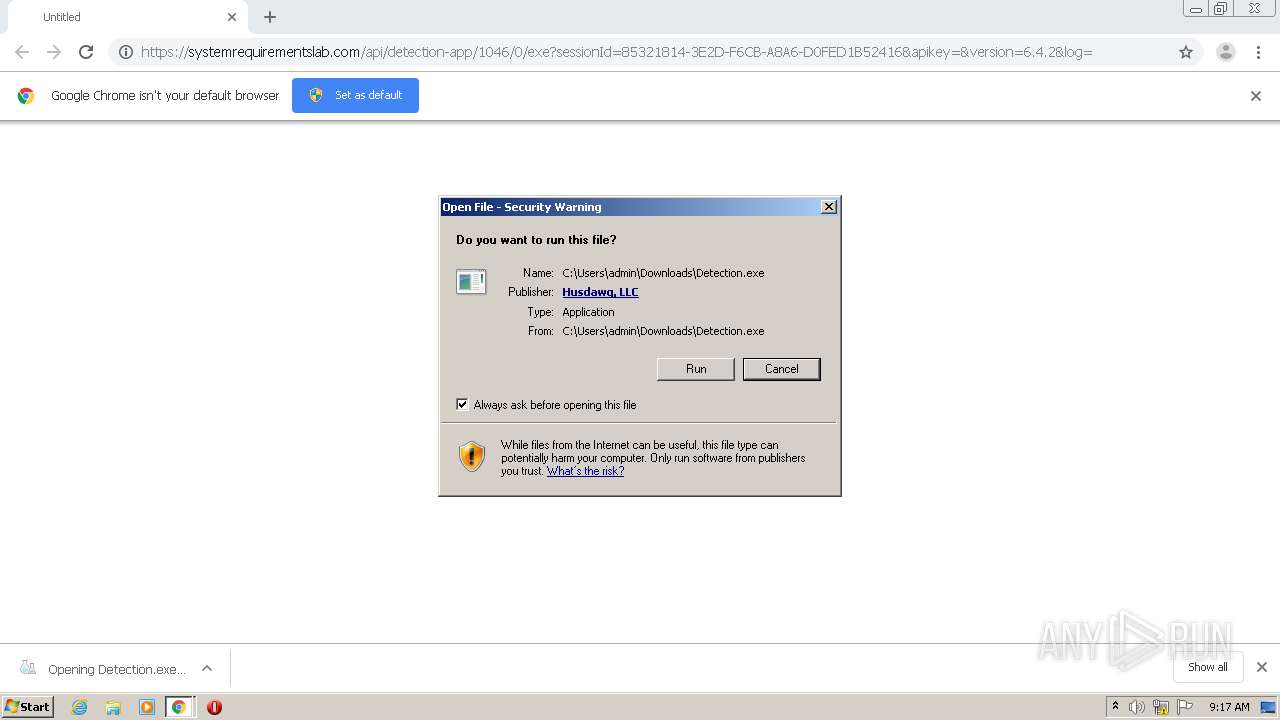
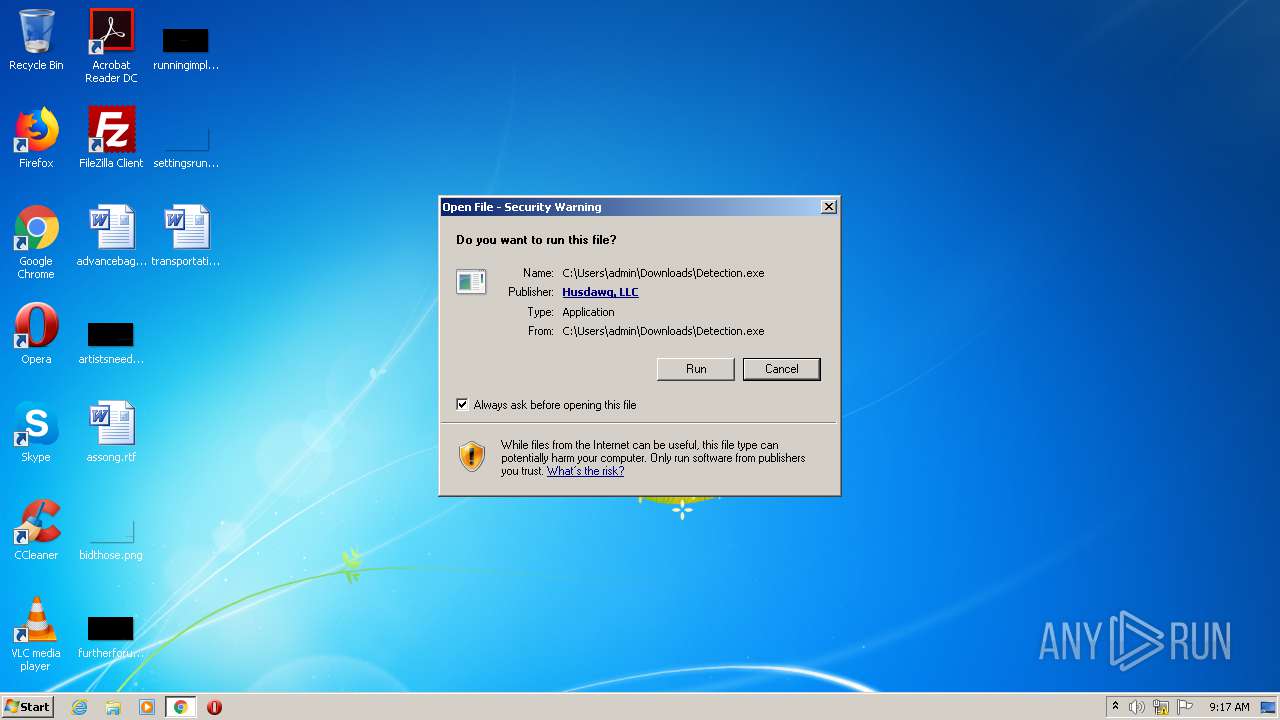
Application was dropped or rewritten from another process
- Detection.exe (PID: 1464)
SUSPICIOUS
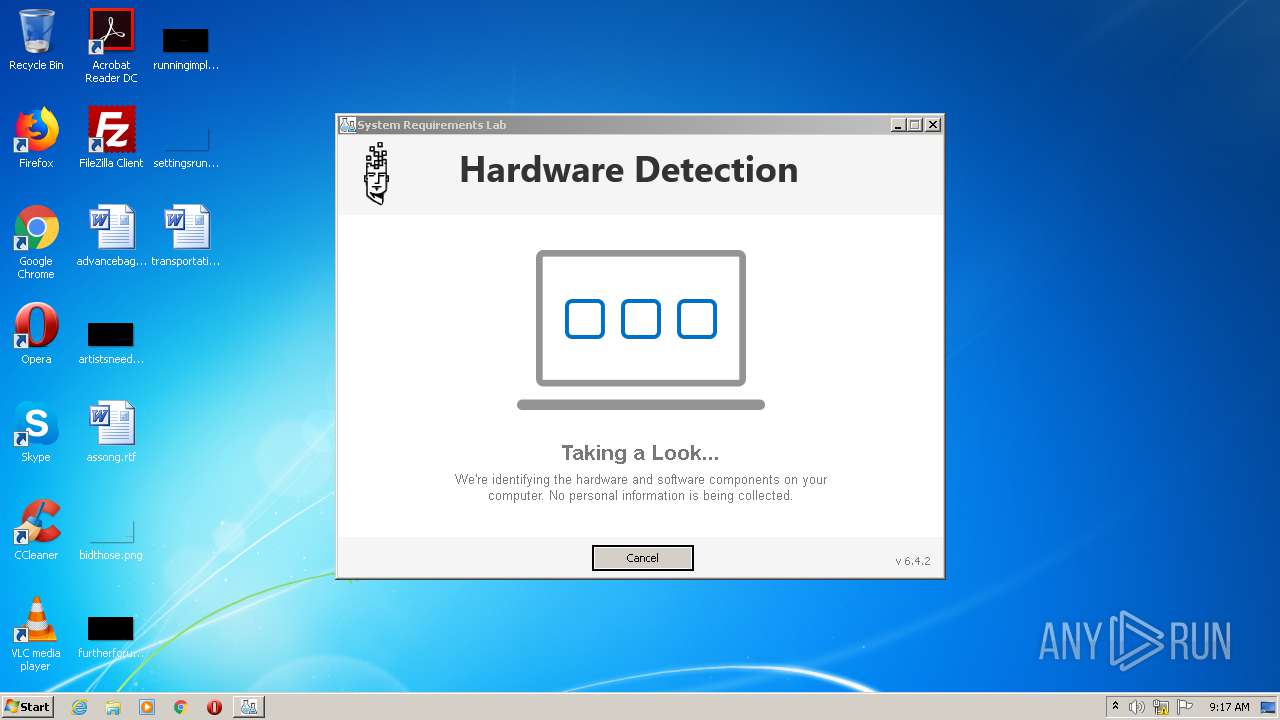
Executable content was dropped or overwritten
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3112)
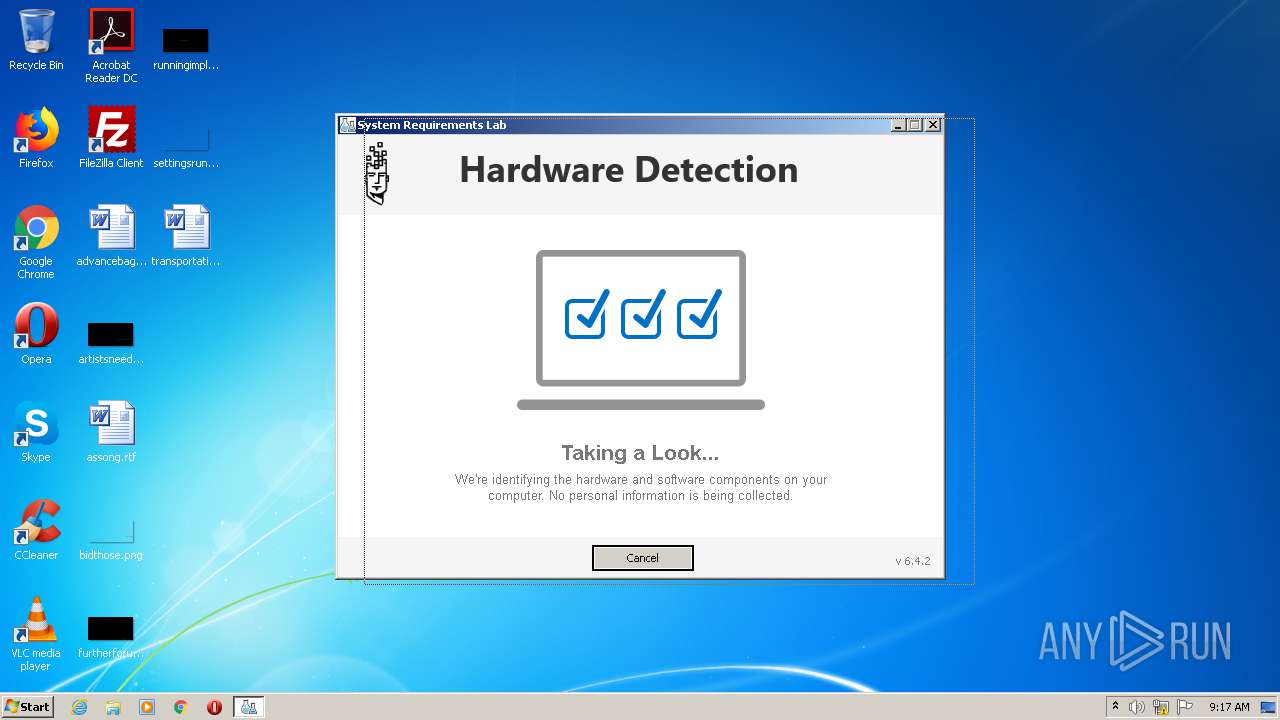
Reads Internet Cache Settings
- Detection.exe (PID: 1464)
Creates files in the user directory
- Detection.exe (PID: 1464)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3112)
Reads the hosts file
- chrome.exe (PID: 2660)
- chrome.exe (PID: 3112)
Reads Internet Cache Settings
- chrome.exe (PID: 2660)
Application launched itself
- chrome.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17691999530870517772,14007146514352527022,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=498686228963412593 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\Downloads\Detection.exe" | C:\Users\admin\Downloads\Detection.exe | chrome.exe | ||||||||||||
User: admin Company: Husdawg, LLC Integrity Level: MEDIUM Description: System Requirements Lab Detection Exit code: 0 Version: 6,4,2 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x717fa9d0,0x717fa9e0,0x717fa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17691999530870517772,14007146514352527022,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4531681672912920226 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,17691999530870517772,14007146514352527022,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16123613677230323764 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,17691999530870517772,14007146514352527022,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5535828424811623284 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://systemrequirementslab.com/api/detection-app/1046/0/exe?sessionId=85321814-3E2D-F6CB-A8A6-D0FED1B52416&apikey=&version=6.4.2&log=" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,17691999530870517772,14007146514352527022,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15991182665302026644 --mojo-platform-channel-handle=1672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2628 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
566
Read events
499
Write events
64
Delete events
3
Modification events
| (PID) Process: | (3208) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2660-13244113030478750 |
Value: 259 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2660-13244113030478750 |
Value: 259 | |||
Executable files
5
Suspicious files
21
Text files
73
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF193176.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF193176.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF193186.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4ed29746-d99f-4364-839c-7205ba8ce9bf.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF19334b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
12
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1464 | Detection.exe | GET | 404 | 3.229.116.209:80 | http://www.systemrequirementslab.com/services/session/85321814-3E2D-F6CB-A8A6-D0FED1B52416/?apikey=9972FAF8-F36D-4FAA-9EF1-4301C3D354C0 | US | — | — | suspicious |
1464 | Detection.exe | POST | 201 | 3.229.116.209:80 | http://www.systemrequirementslab.com/services/session/85321814-3E2D-F6CB-A8A6-D0FED1B52416/?apikey=9972FAF8-F36D-4FAA-9EF1-4301C3D354C0 | US | text | 214 b | suspicious |
1464 | Detection.exe | POST | 204 | 3.229.116.209:80 | http://www.systemrequirementslab.com/cyri/api/LogUserEvent | US | — | — | suspicious |
1464 | Detection.exe | GET | 404 | 3.229.116.209:80 | http://www.systemrequirementslab.com/services/session/85321814-3E2D-F6CB-A8A6-D0FED1B52416/?apikey=9972FAF8-F36D-4FAA-9EF1-4301C3D354C0 | US | — | — | suspicious |
1464 | Detection.exe | GET | 200 | 3.229.116.209:80 | http://www.systemrequirementslab.com/services/configuration/1046/0/?apikey=0 | US | text | 1.35 Kb | suspicious |
1464 | Detection.exe | POST | 404 | 3.229.116.209:80 | http://www.systemrequirementslab.com/services/session//?apikey=9972FAF8-F36D-4FAA-9EF1-4301C3D354C0 | US | text | 1.35 Kb | suspicious |
1464 | Detection.exe | POST | 204 | 3.229.116.209:80 | http://www.systemrequirementslab.com/cyri/api/LogUserEvent | US | text | 1.35 Kb | suspicious |
1464 | Detection.exe | POST | 204 | 3.229.116.209:80 | http://www.systemrequirementslab.com/cyri/api/LogUserEvent | US | text | 1.35 Kb | suspicious |
1464 | Detection.exe | POST | 404 | 3.229.116.209:80 | http://www.systemrequirementslab.com/services/session//?apikey=9972FAF8-F36D-4FAA-9EF1-4301C3D354C0 | US | text | 1.35 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3112 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 3.229.116.209:443 | systemrequirementslab.com | — | US | unknown |
3112 | chrome.exe | 216.58.205.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1464 | Detection.exe | 3.229.116.209:80 | systemrequirementslab.com | — | US | unknown |
3112 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
systemrequirementslab.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.systemrequirementslab.com |
| suspicious |