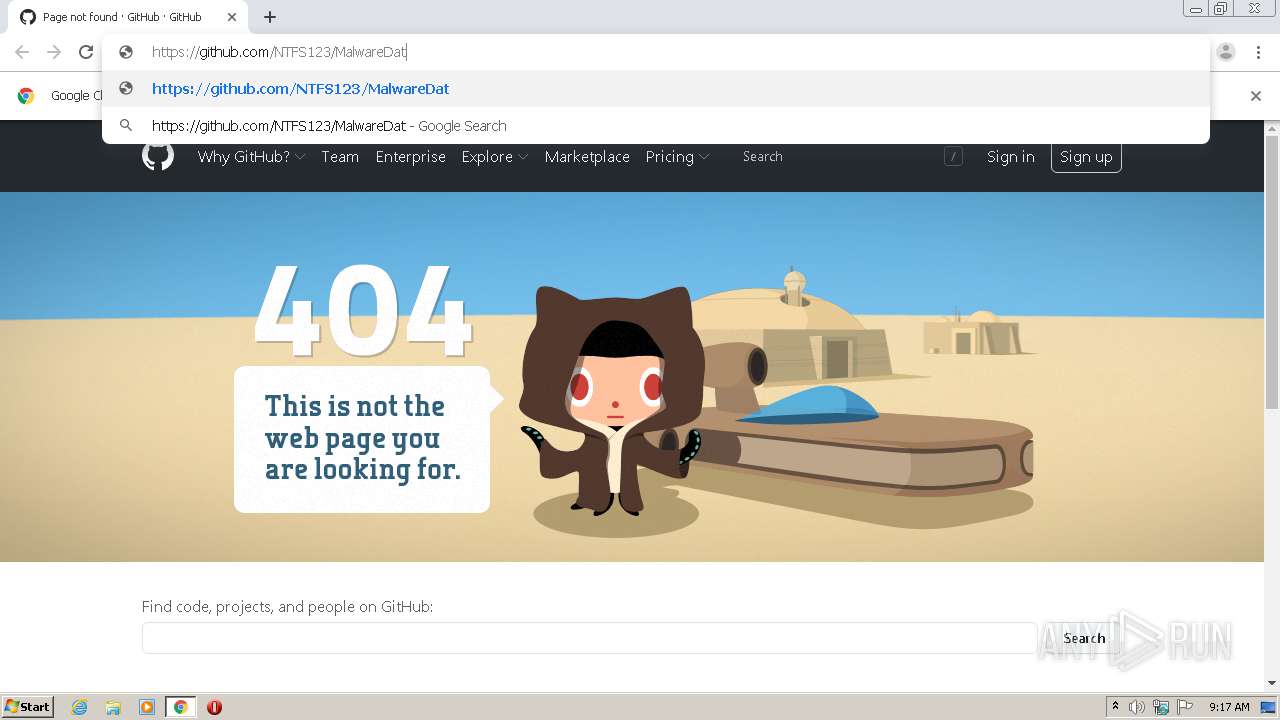
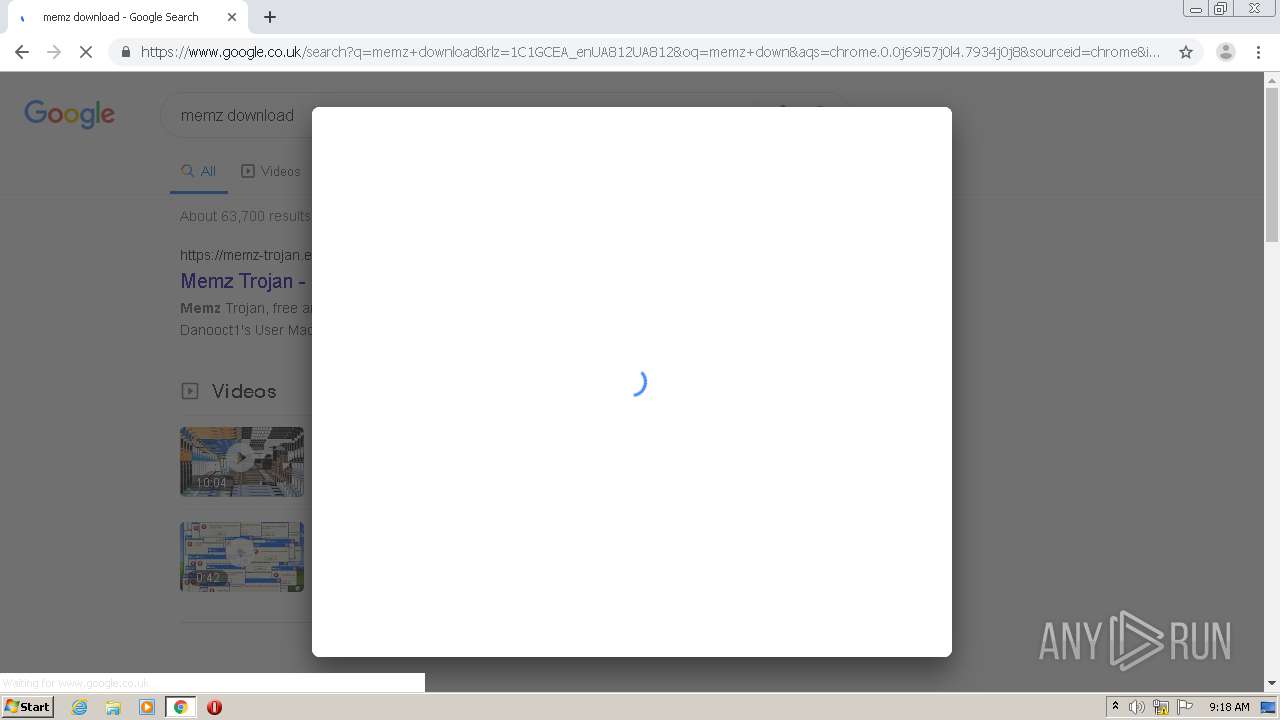
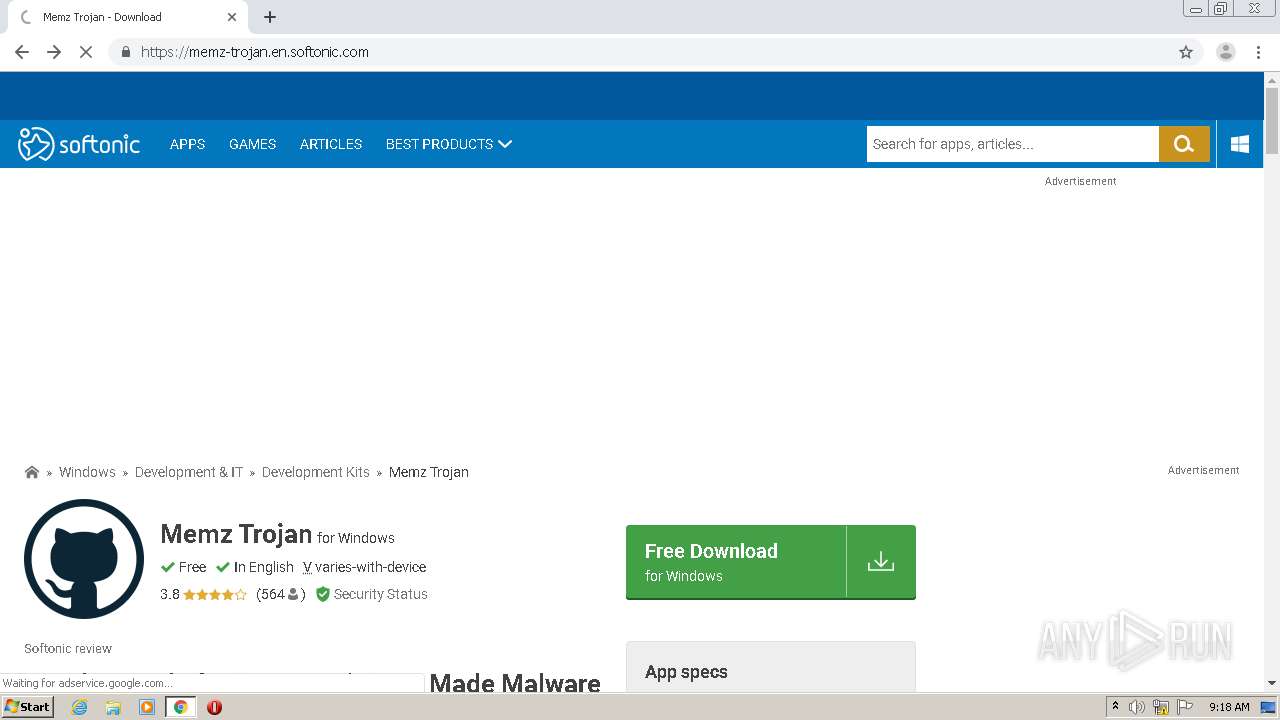
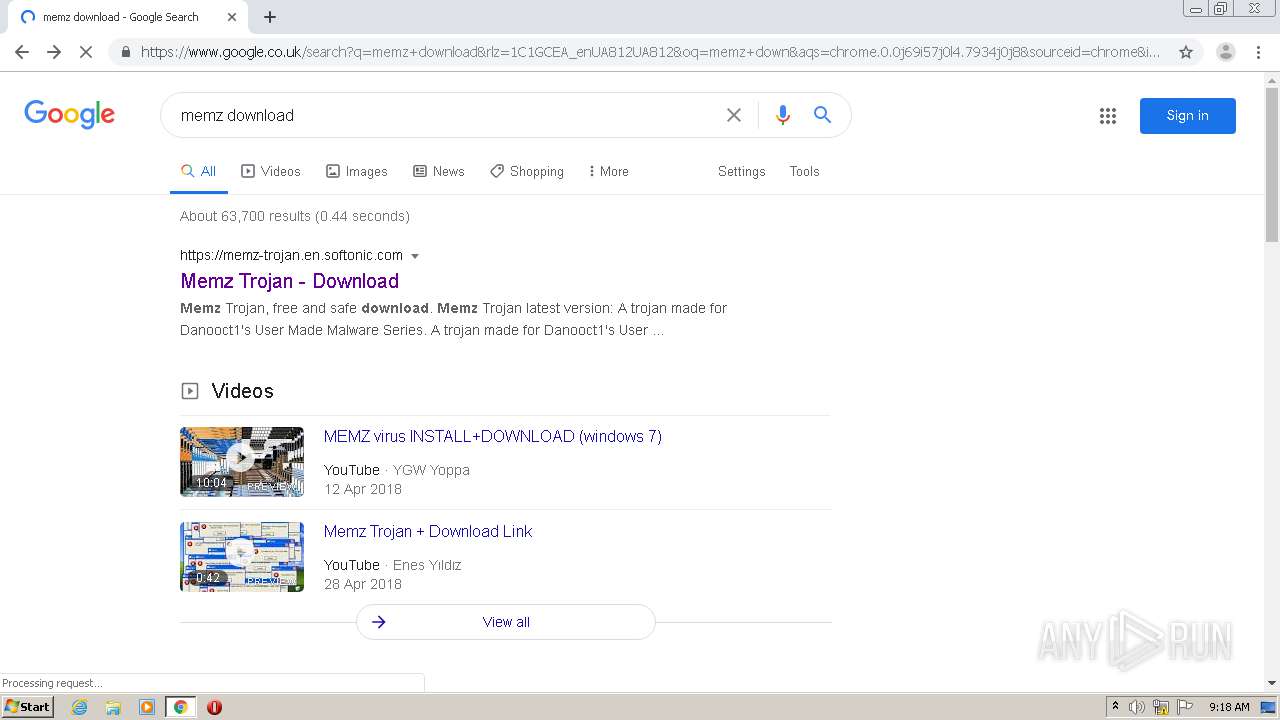
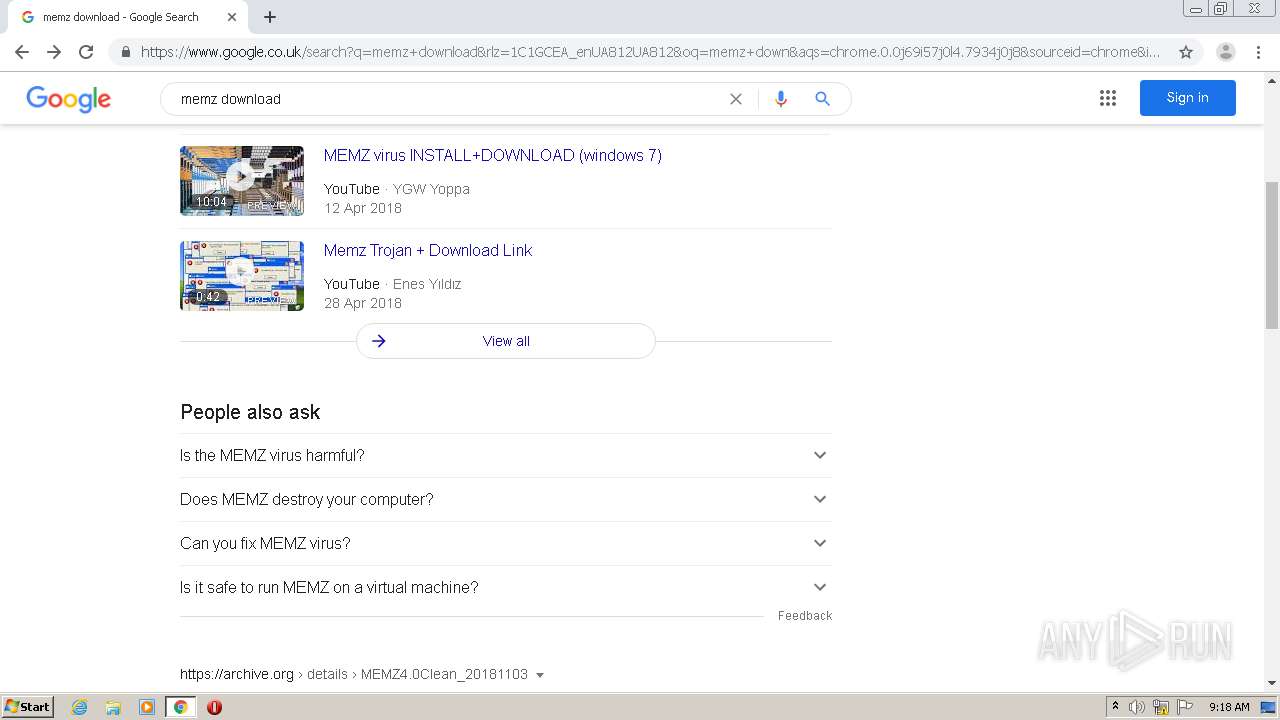
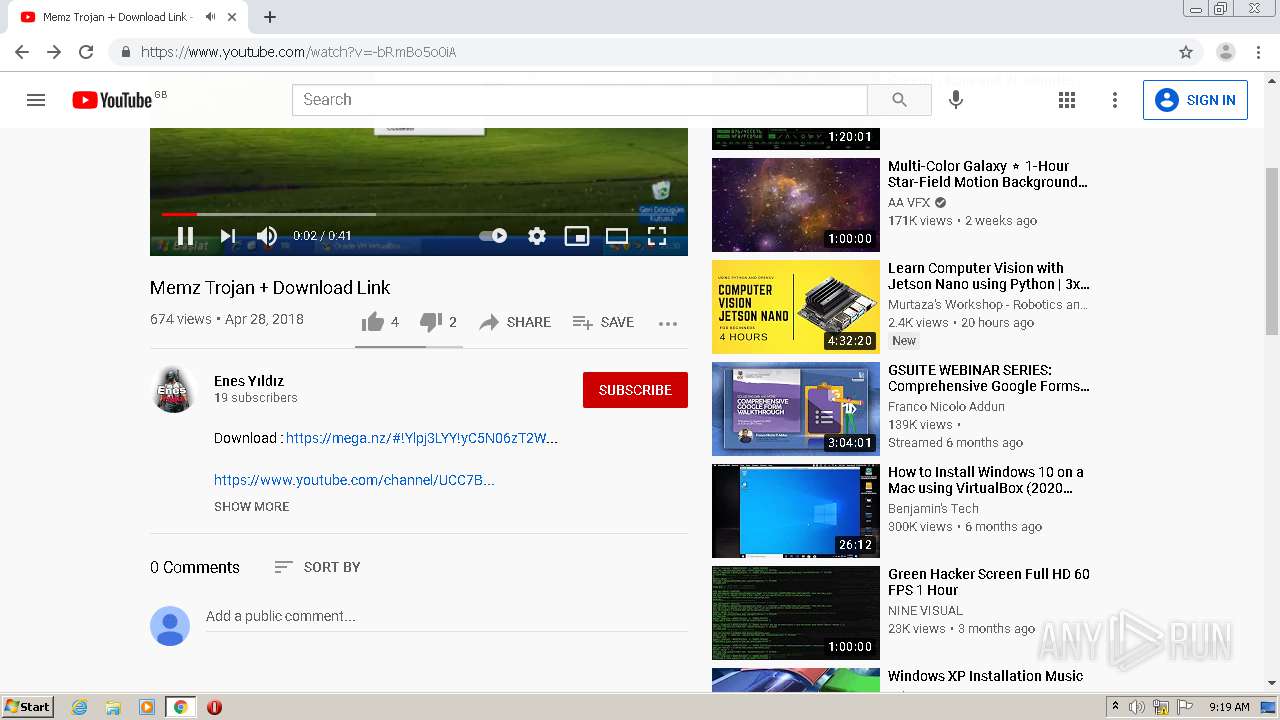
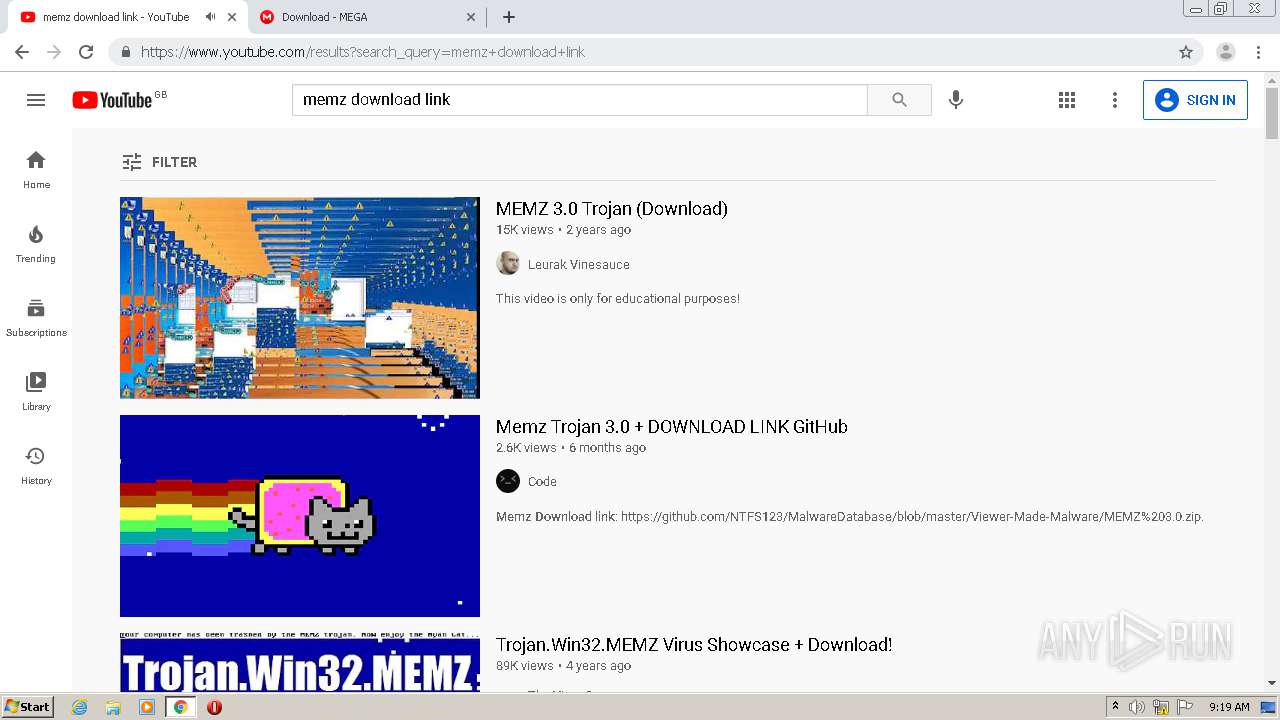
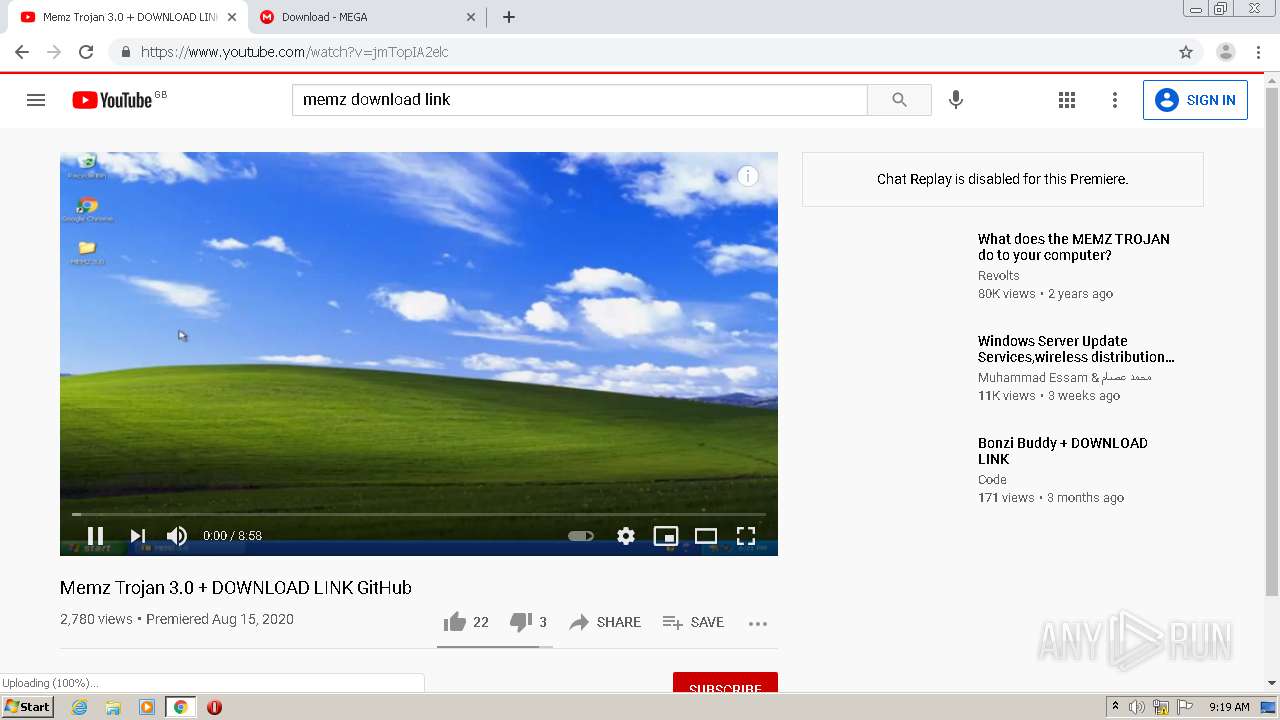
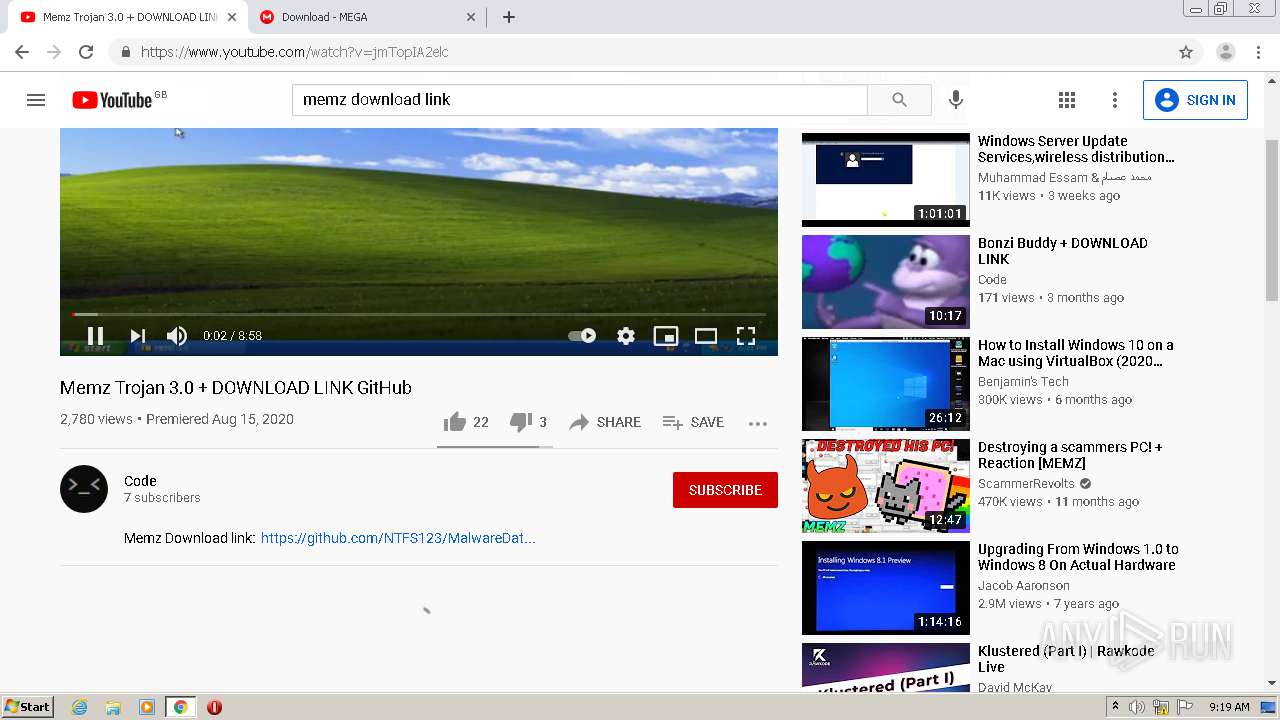
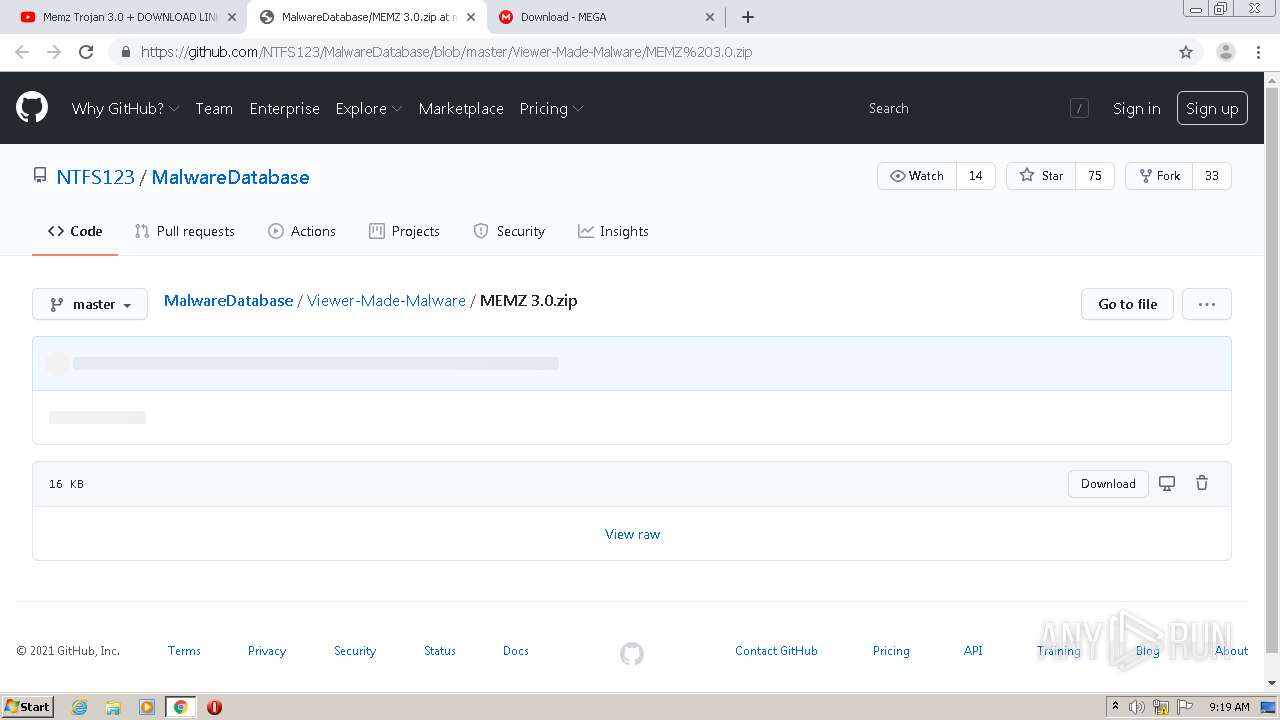
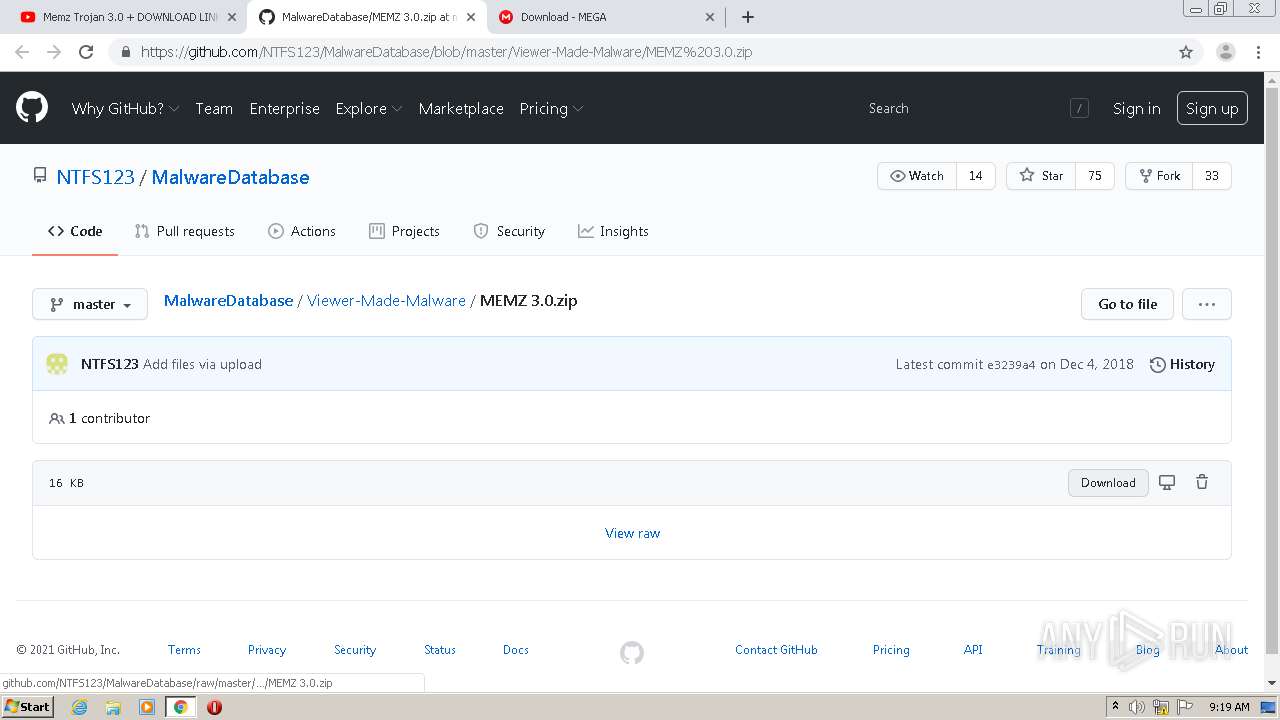
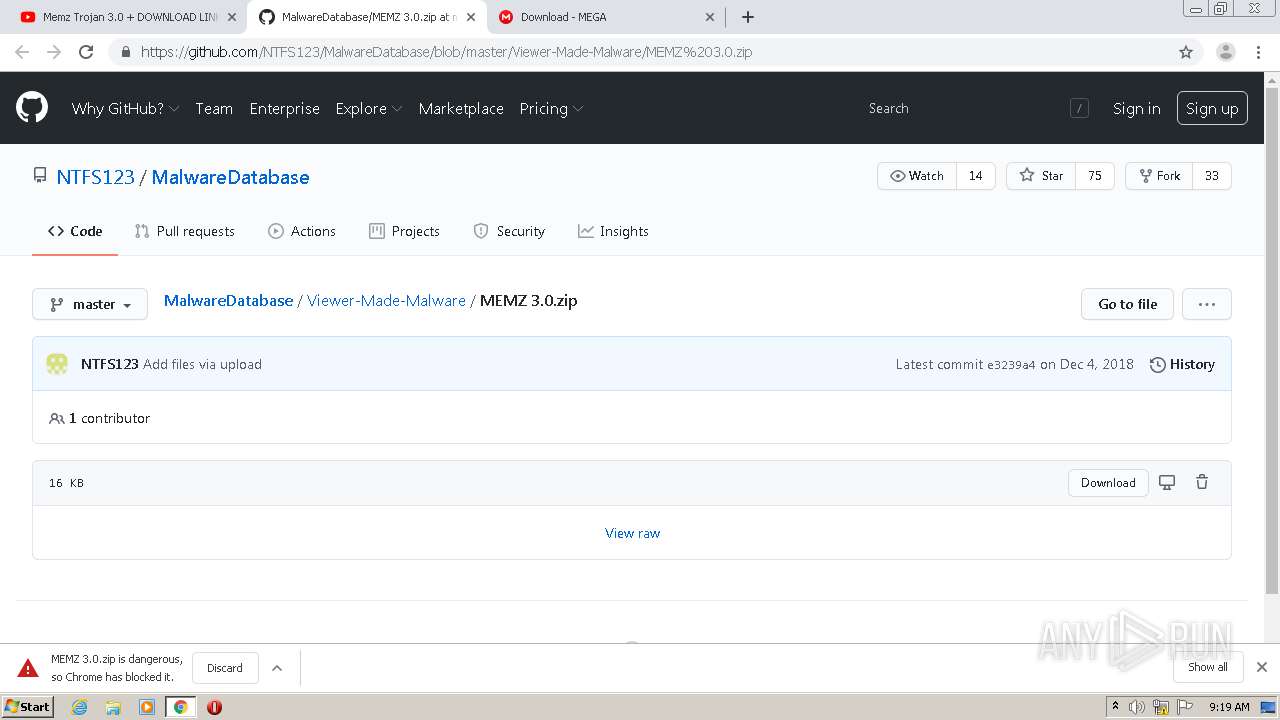
| URL: | https://github.com/NTFS123/MalwareDat... |
| Full analysis: | https://app.any.run/tasks/1498d74d-9ef6-43c6-b093-ee4e7c1e7e01 |
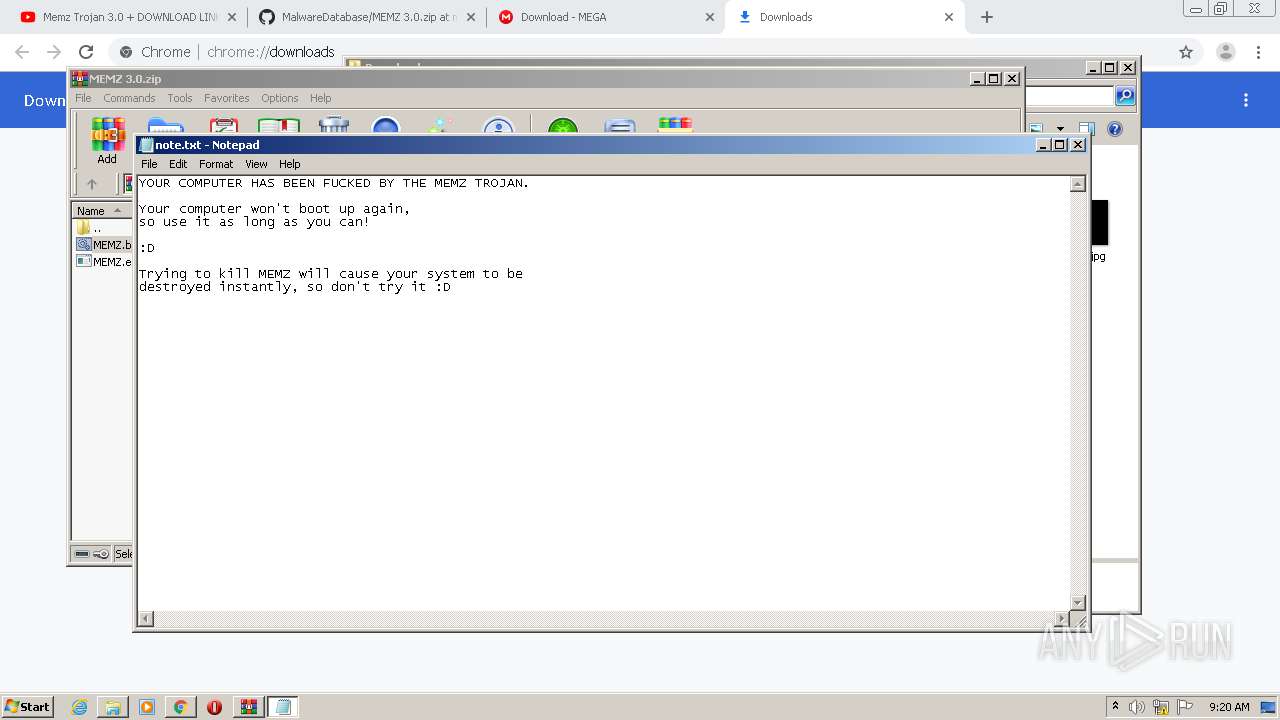
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2021, 09:16:58 |
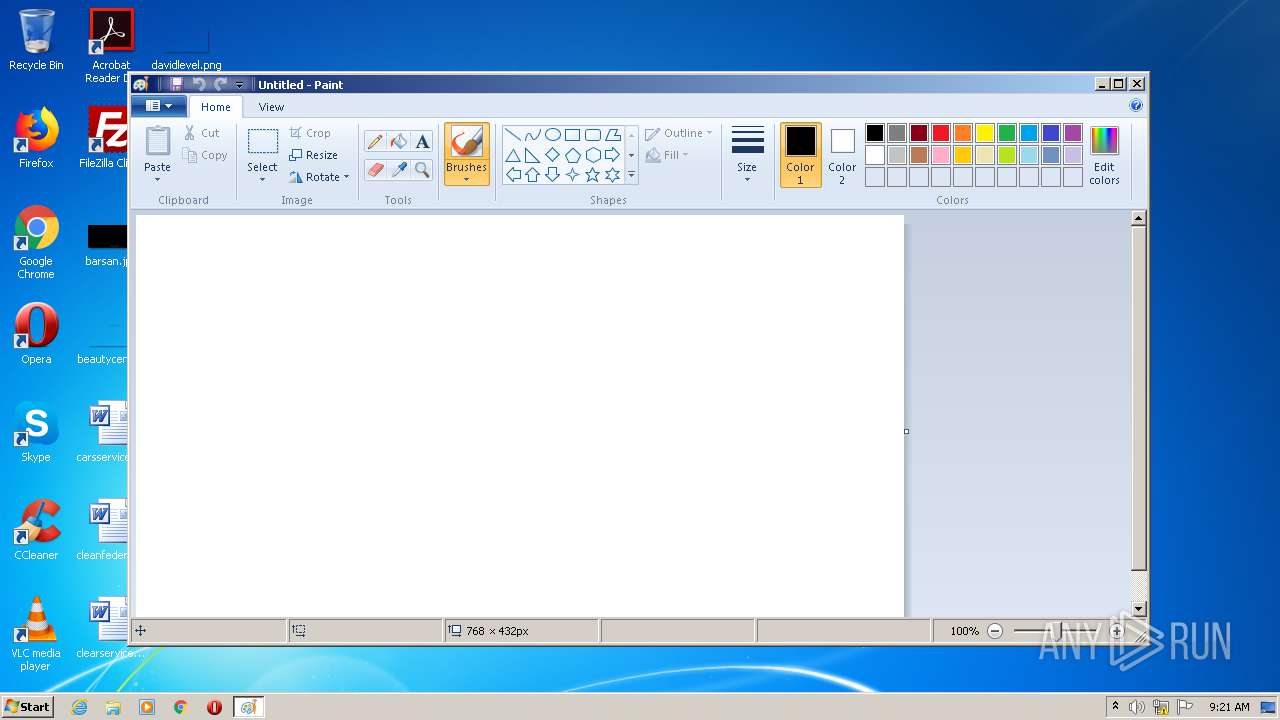
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C4233789D0F737EF2E6FE4D8EE7734CC |
| SHA1: | 98A050B4143D47691122BAA63BEADAD99573532D |
| SHA256: | 230C97E4E5445C9733F975C4E2000F2D6247E396E7AFEE41DCAFA3FBAB3B2EC2 |
| SSDEEP: | 3:N8tEdVj7WUSELL:2uj00 |
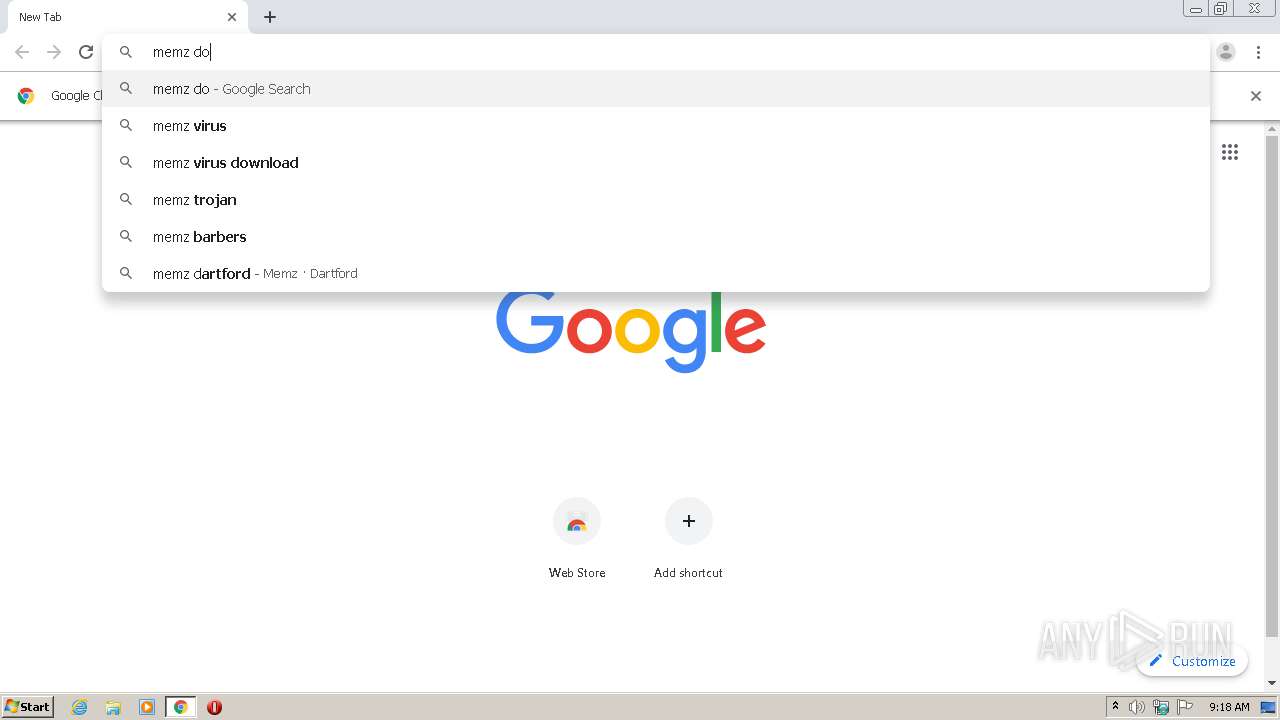
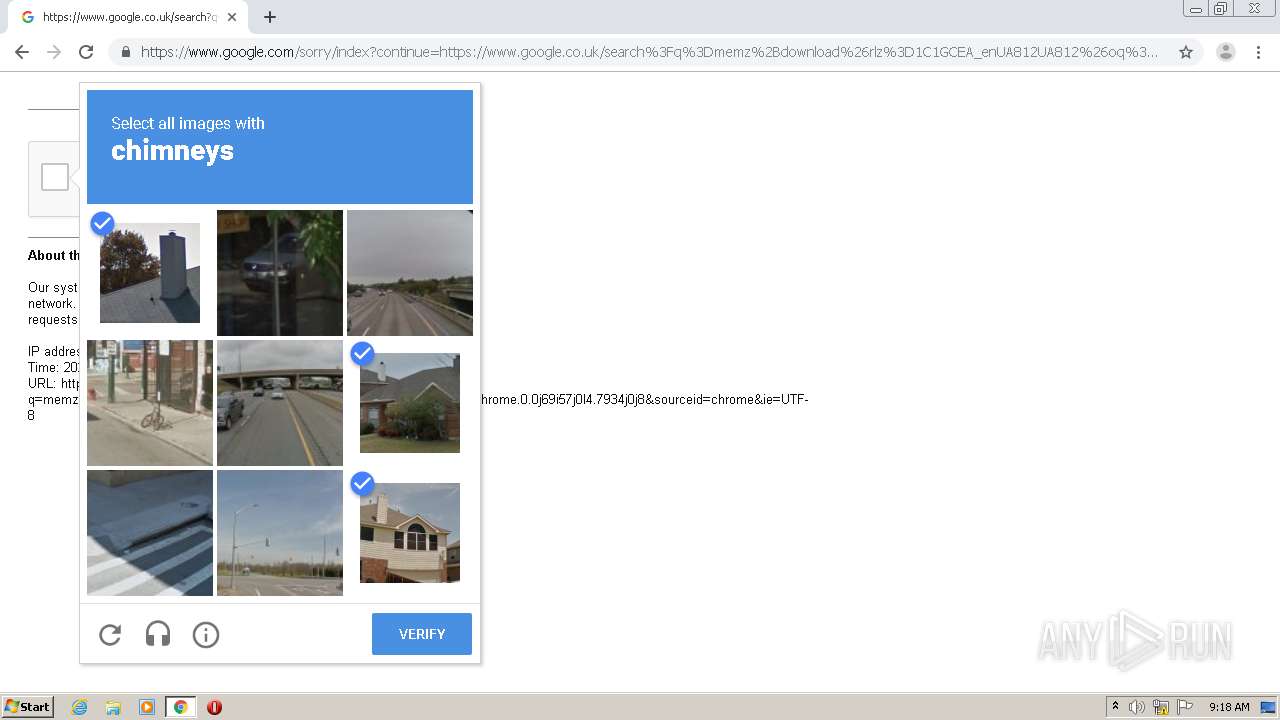
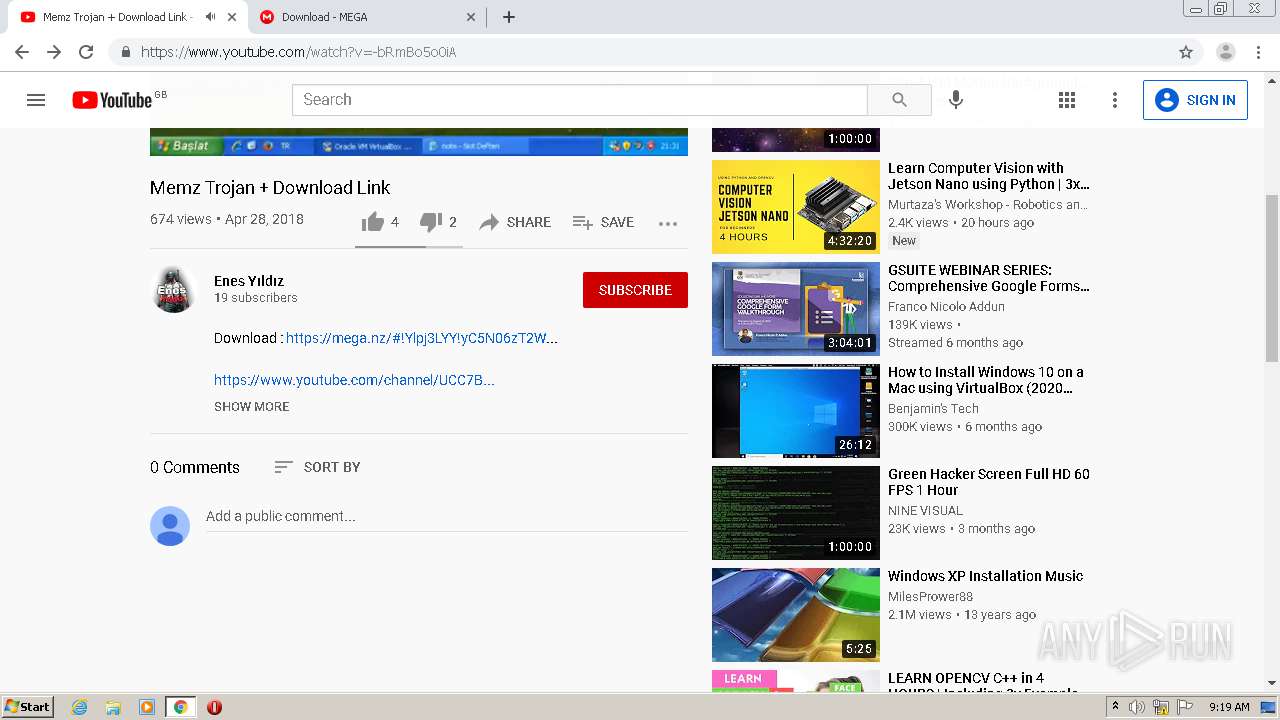
MALICIOUS
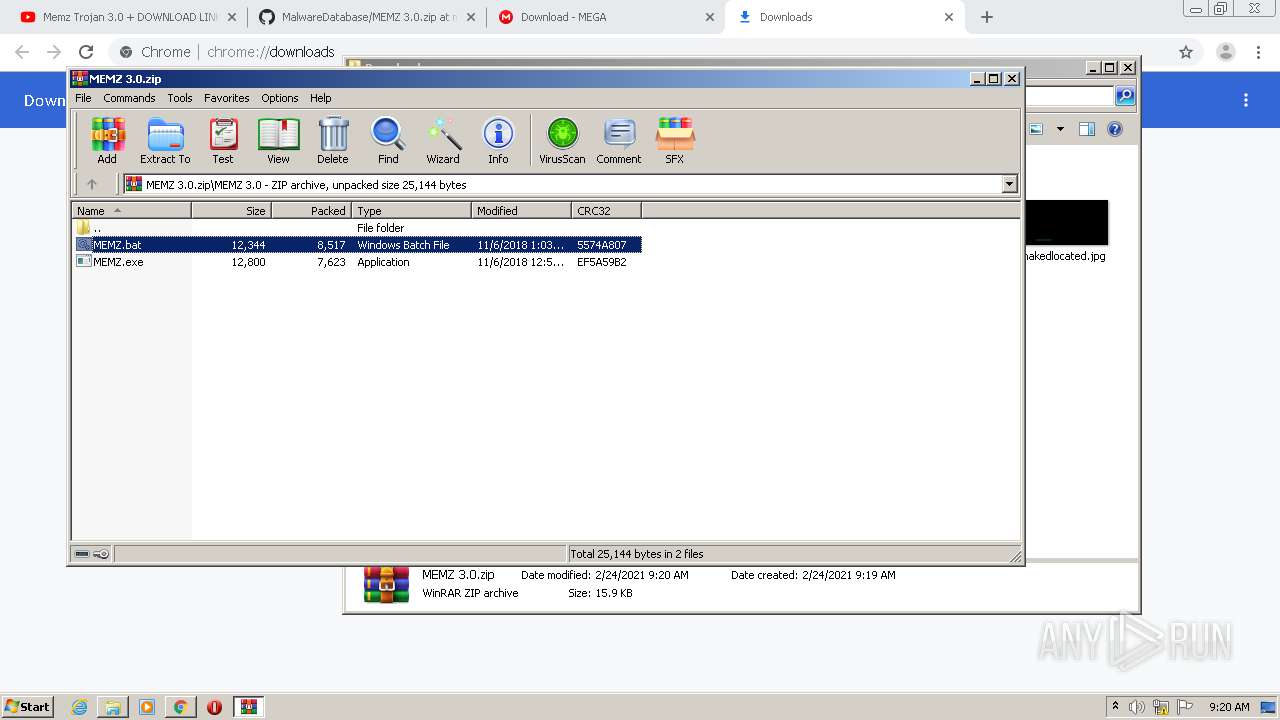
Application was dropped or rewritten from another process
- MEMZ.exe (PID: 1436)
- MEMZ.exe (PID: 2988)
- MEMZ.exe (PID: 2280)
- MEMZ.exe (PID: 3476)
- MEMZ.exe (PID: 3500)
- MEMZ.exe (PID: 3472)
- MEMZ.exe (PID: 2380)
- MEMZ.exe (PID: 2596)
- MEMZ.exe (PID: 3820)
- MEMZ.exe (PID: 2196)
- MEMZ.exe (PID: 1784)
- MEMZ.exe (PID: 952)
- MEMZ.exe (PID: 1860)
- MEMZ.exe (PID: 2796)
- MEMZ.exe (PID: 1768)
- MEMZ.exe (PID: 3020)
- MEMZ.exe (PID: 3200)
Low-level write access rights to disk partition
- MEMZ.exe (PID: 2380)
- MEMZ.exe (PID: 2796)
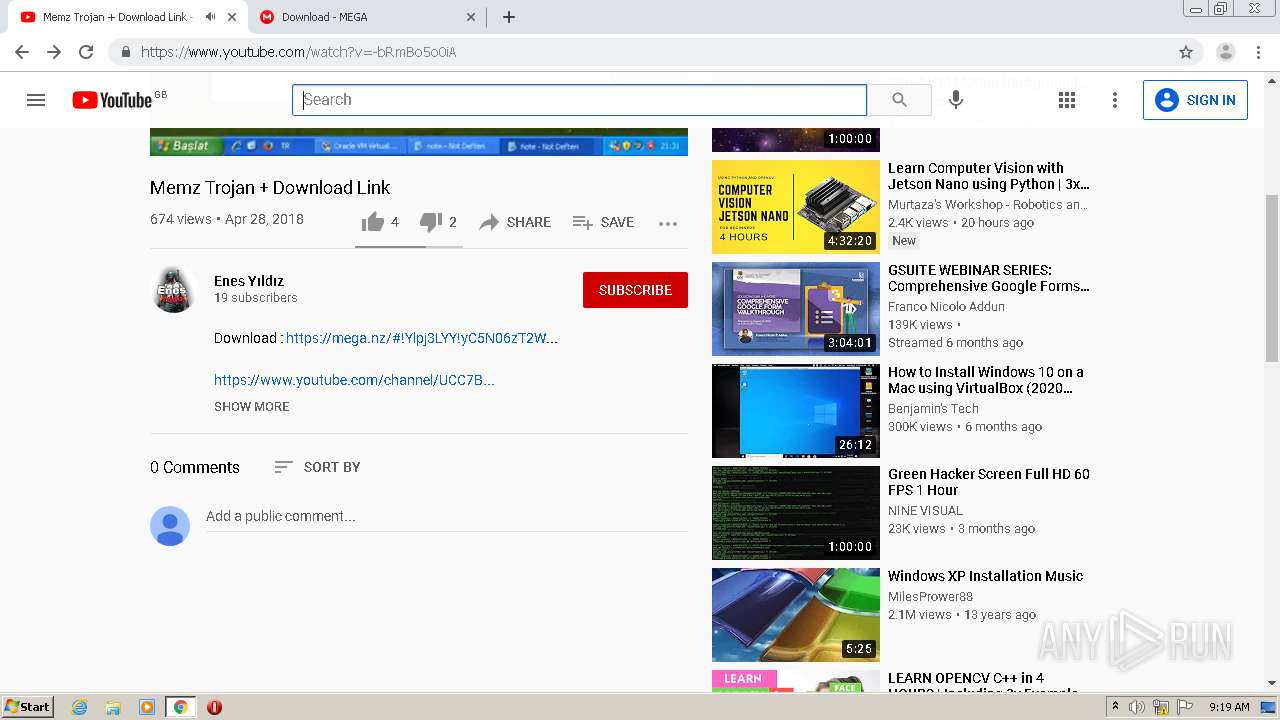
SUSPICIOUS
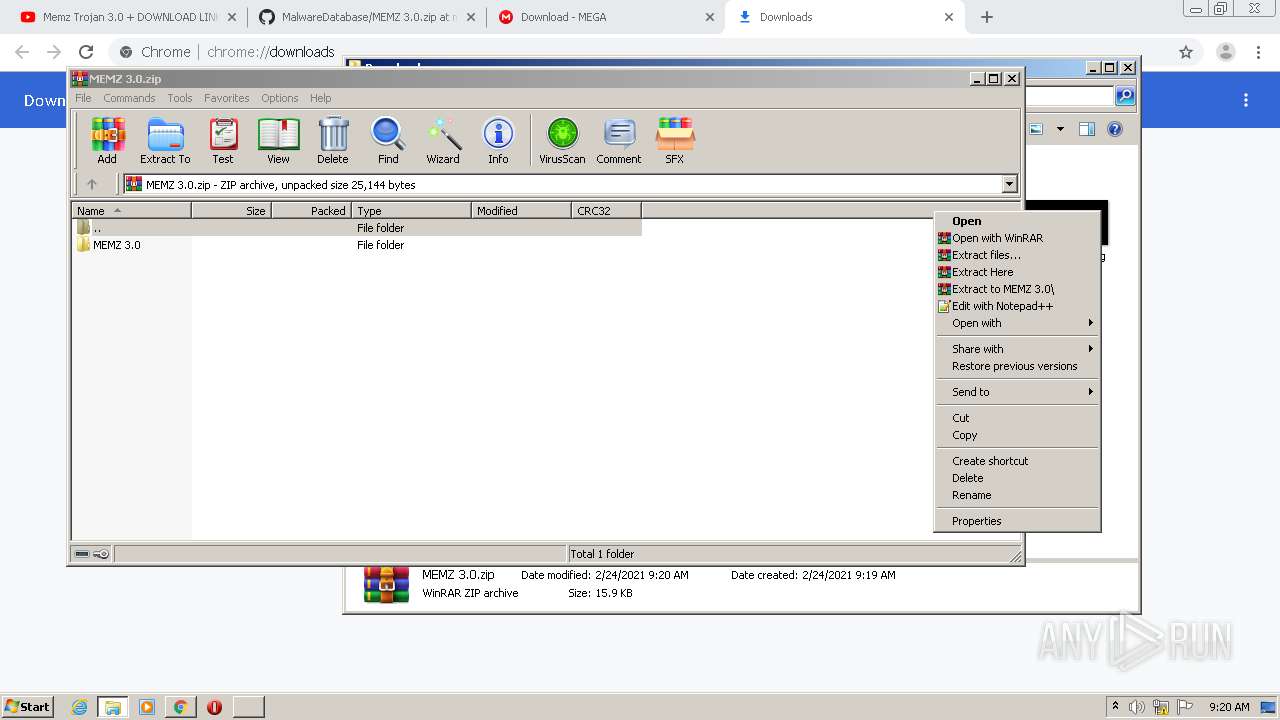
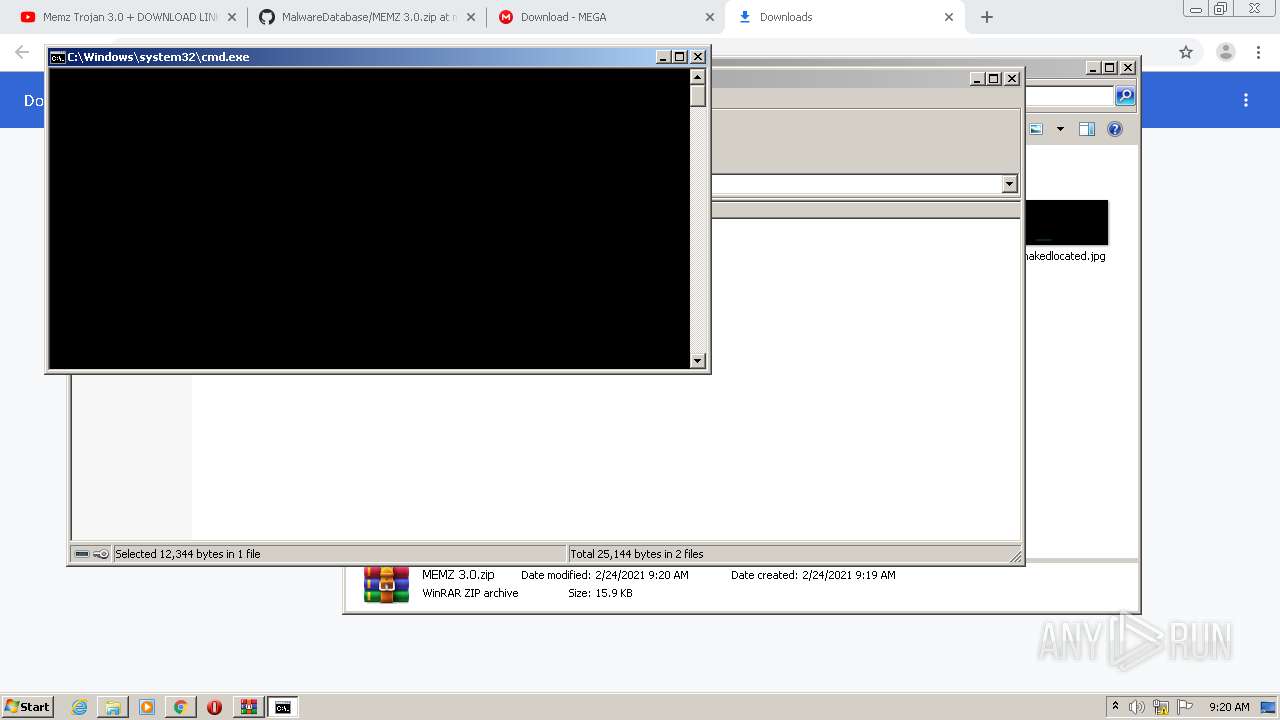
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 752)
Executes scripts
- cmd.exe (PID: 3892)
Application launched itself
- MEMZ.exe (PID: 2988)
- MEMZ.exe (PID: 3820)
Modifies files in Chrome extension folder
- chrome.exe (PID: 784)
Executable content was dropped or overwritten
- cscript.exe (PID: 3492)
- WinRAR.exe (PID: 752)
Low-level read access rights to disk partition
- MEMZ.exe (PID: 2380)
- MEMZ.exe (PID: 2796)
Creates files in the user directory
- cscript.exe (PID: 3492)
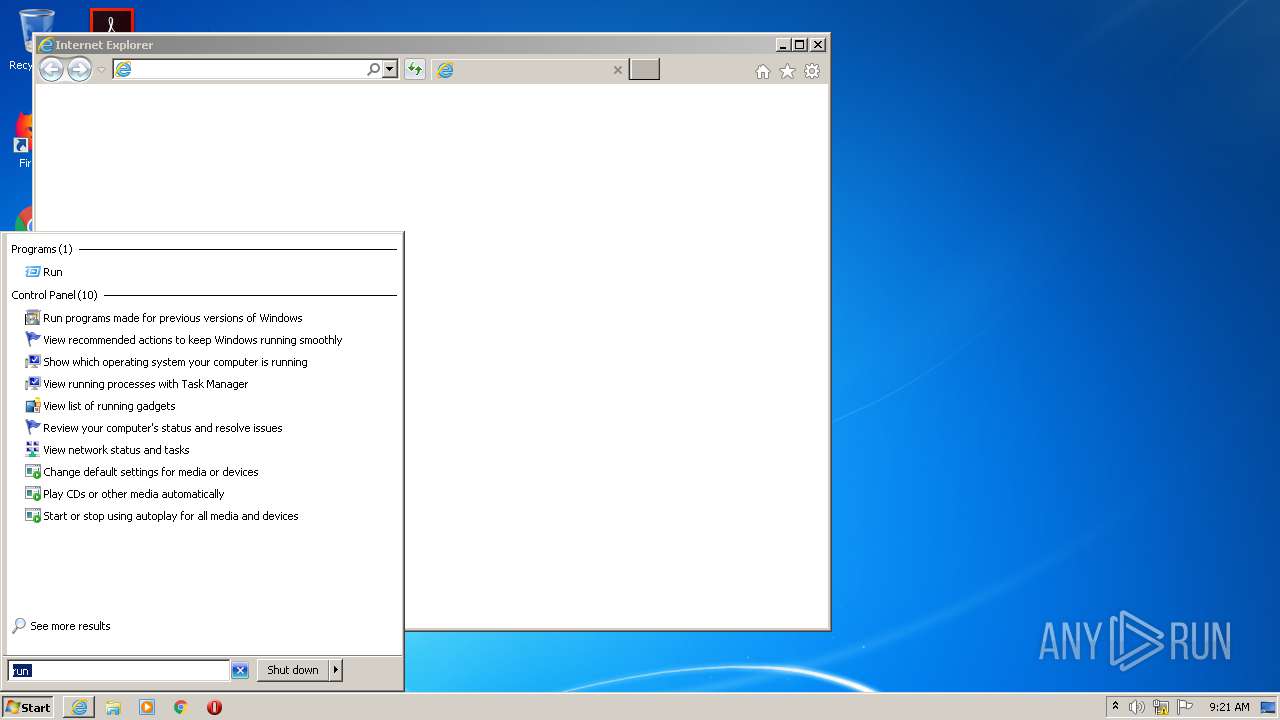
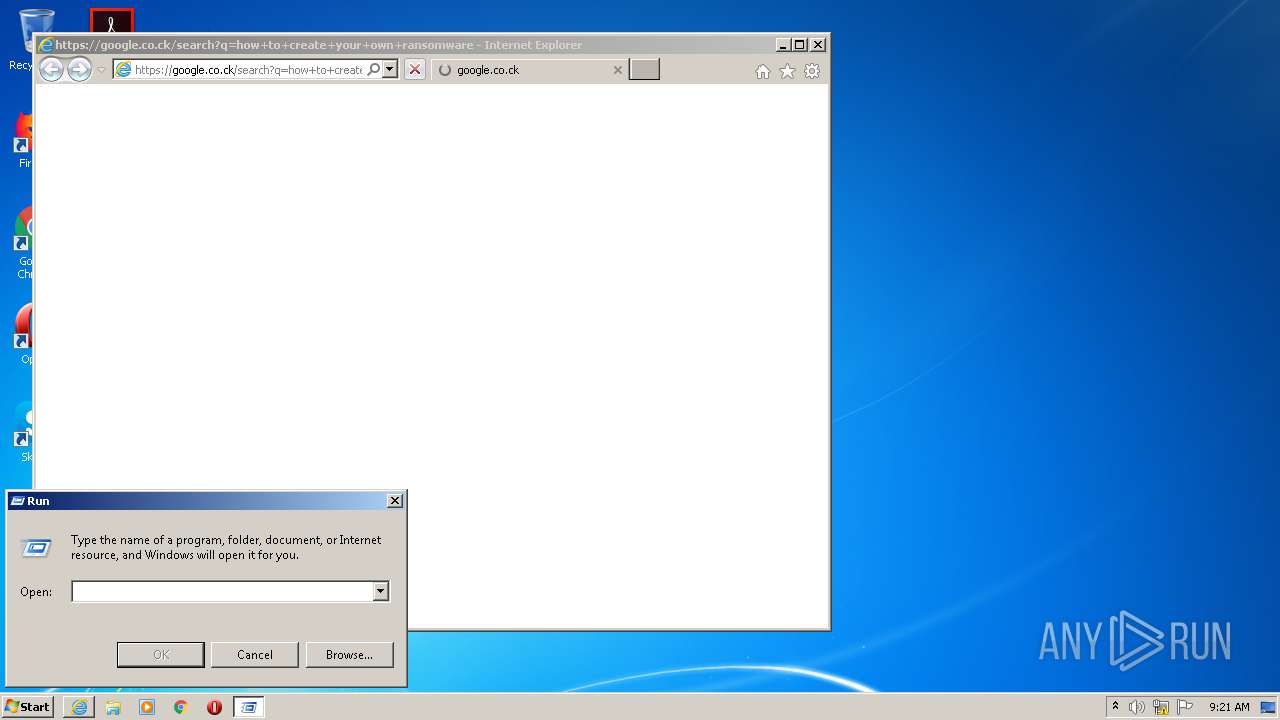
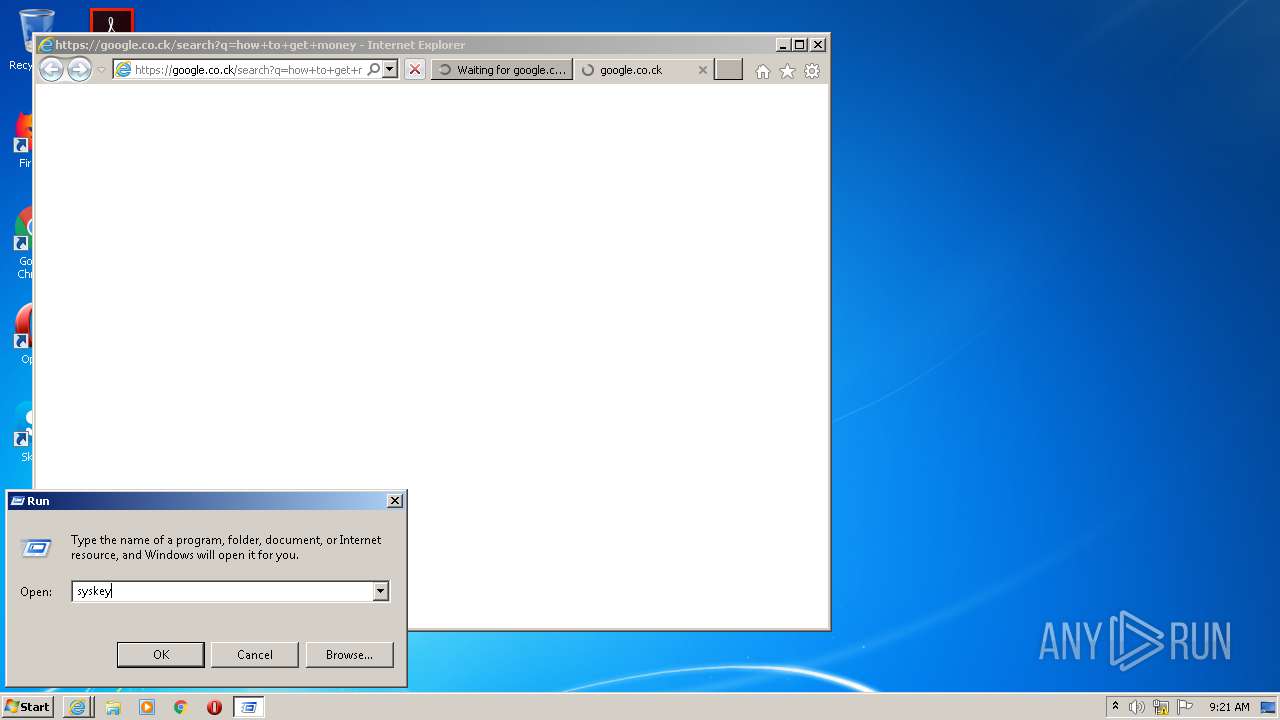
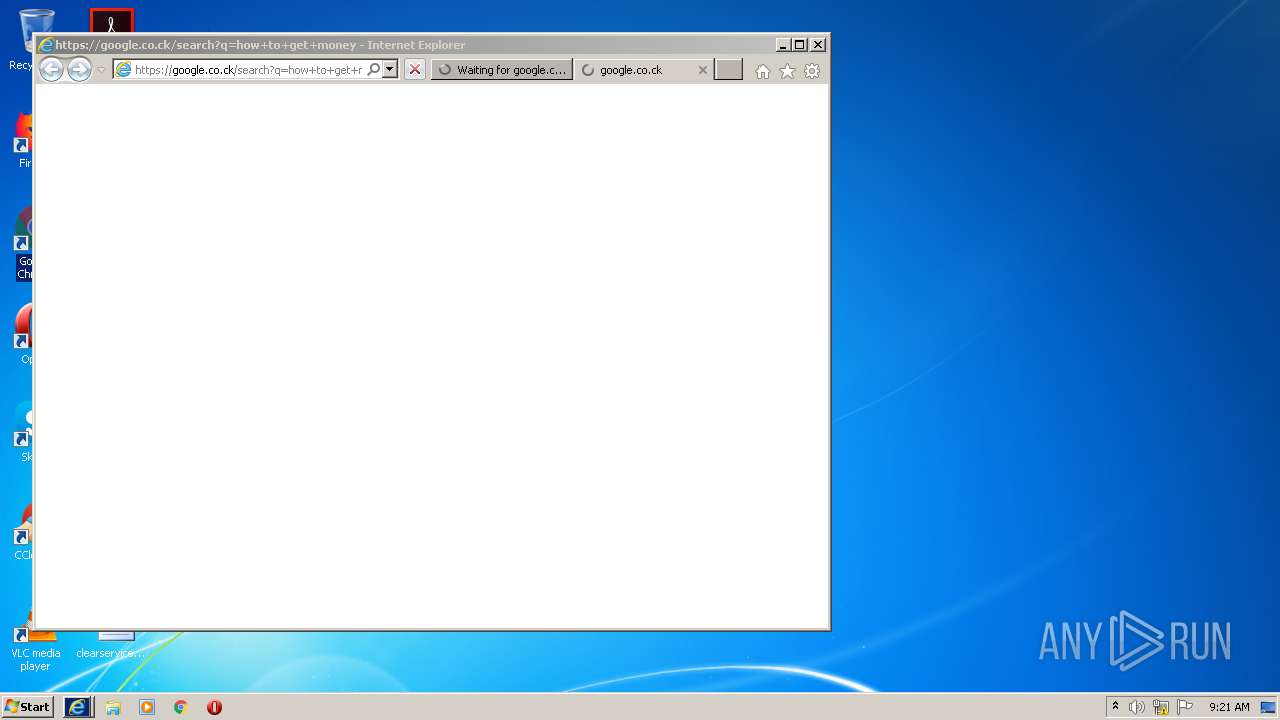
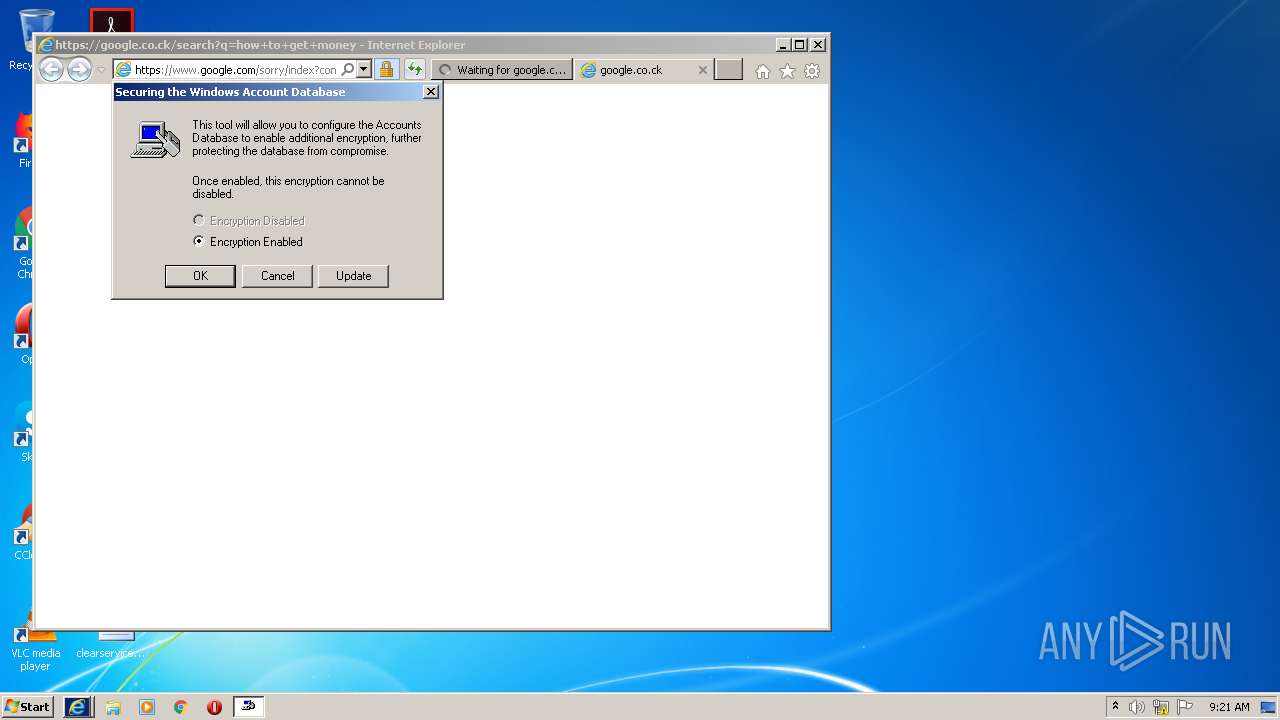
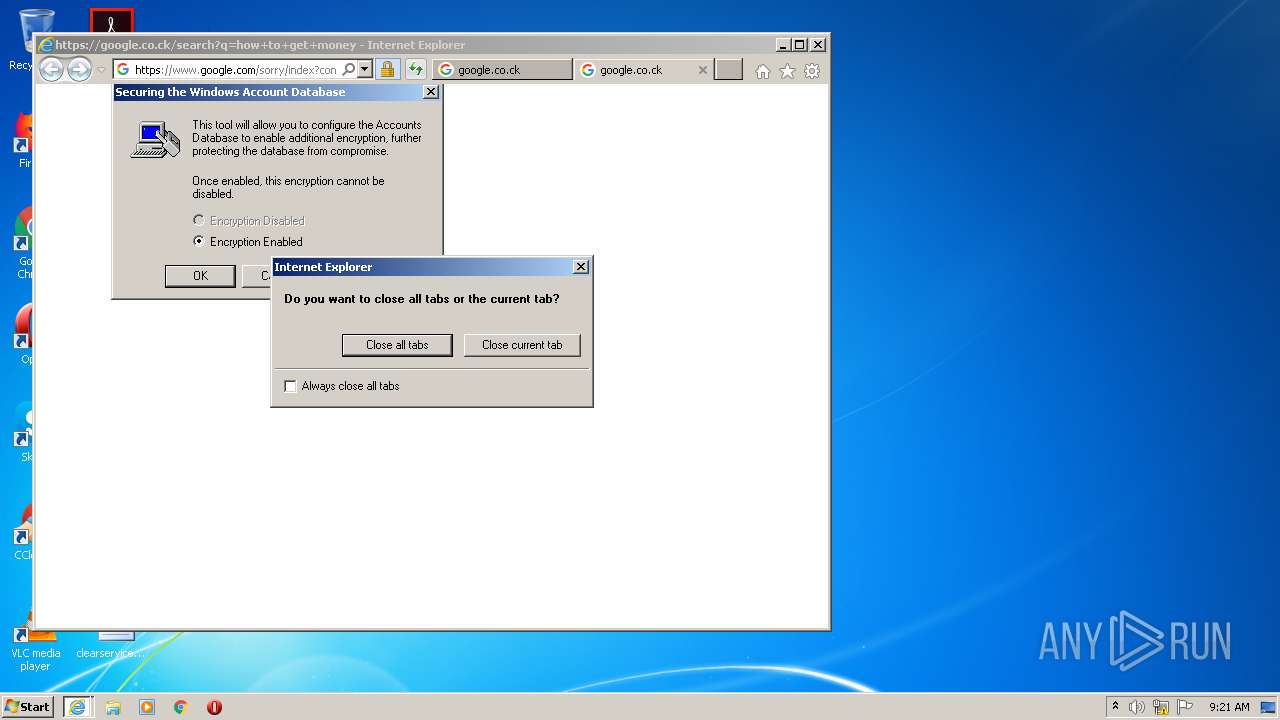
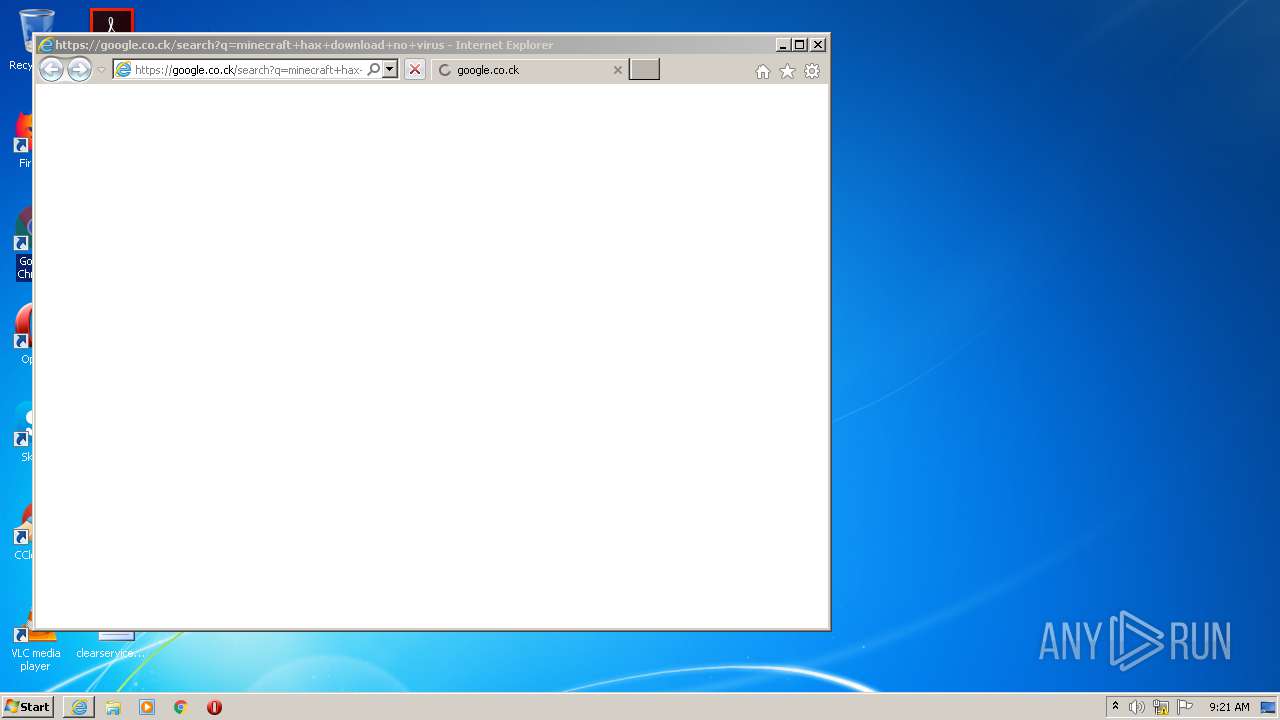
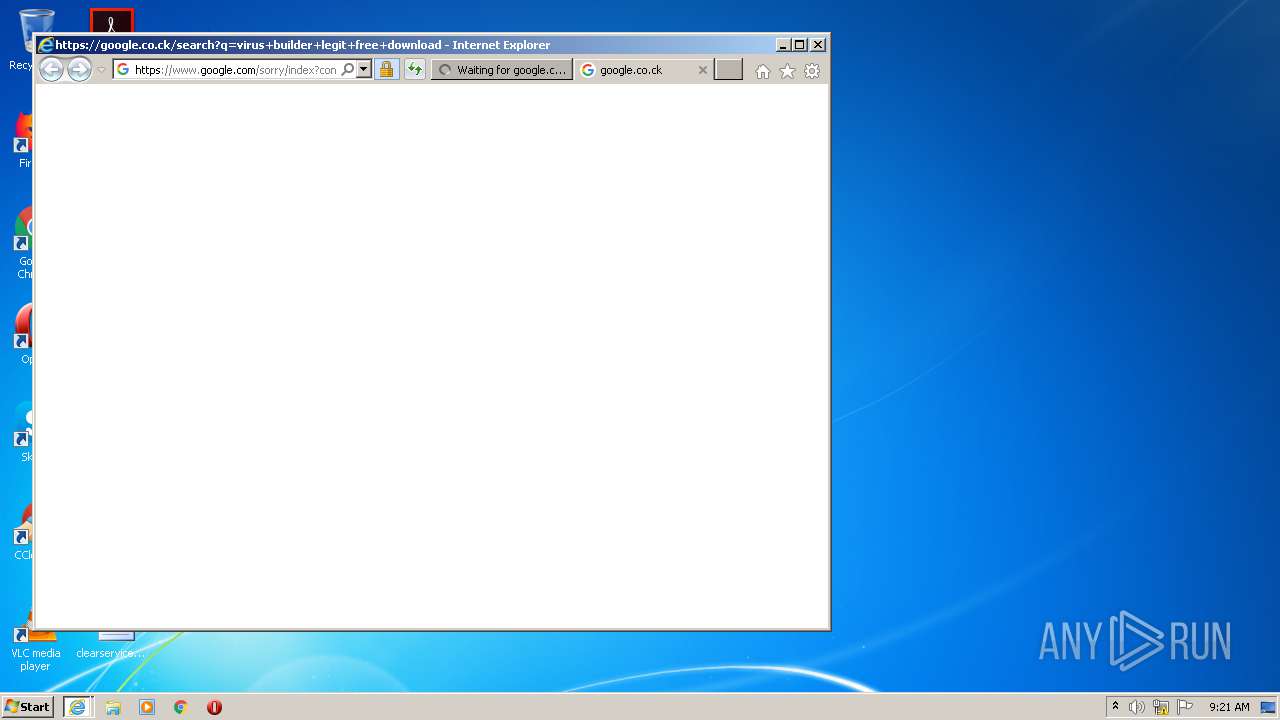
Starts Internet Explorer
- MEMZ.exe (PID: 2380)
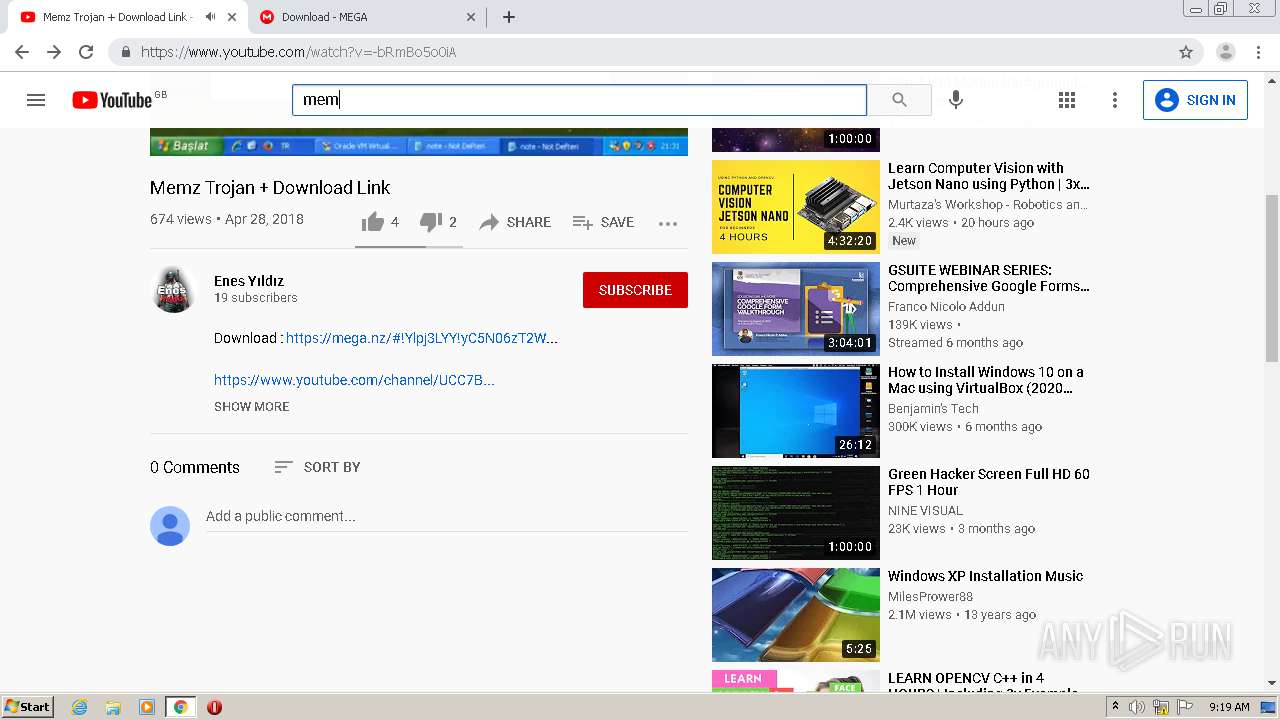
INFO
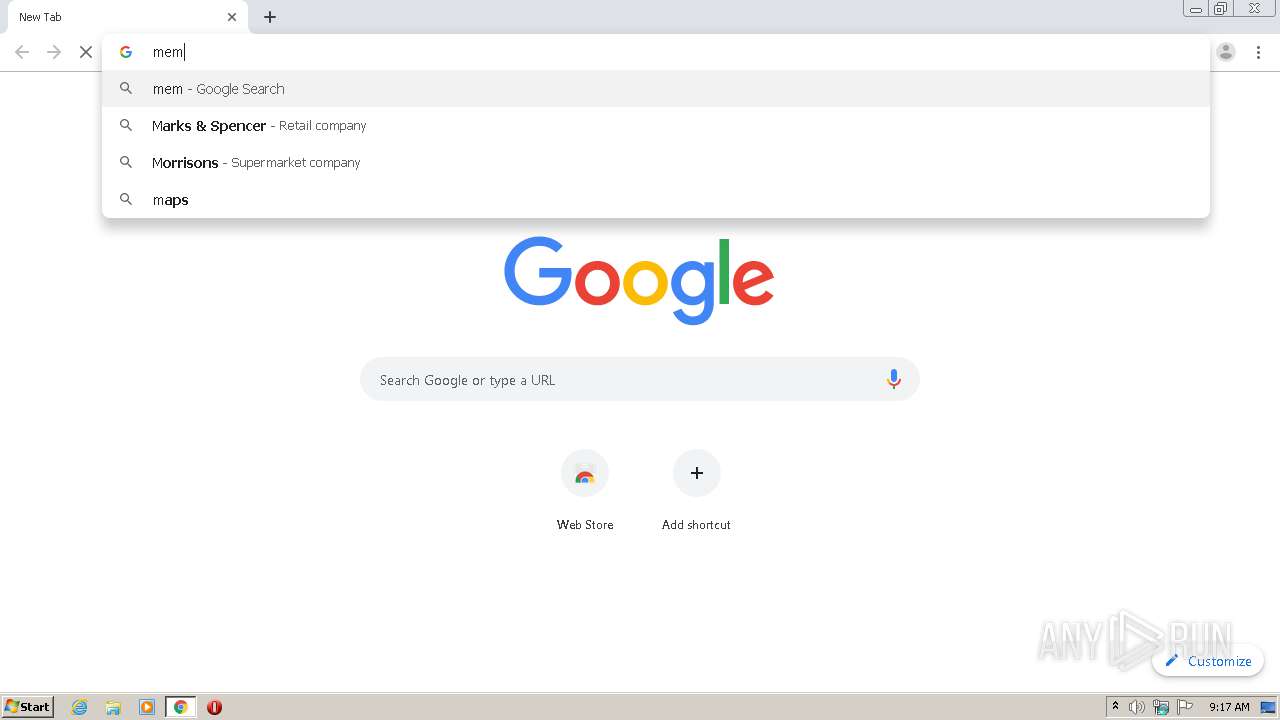
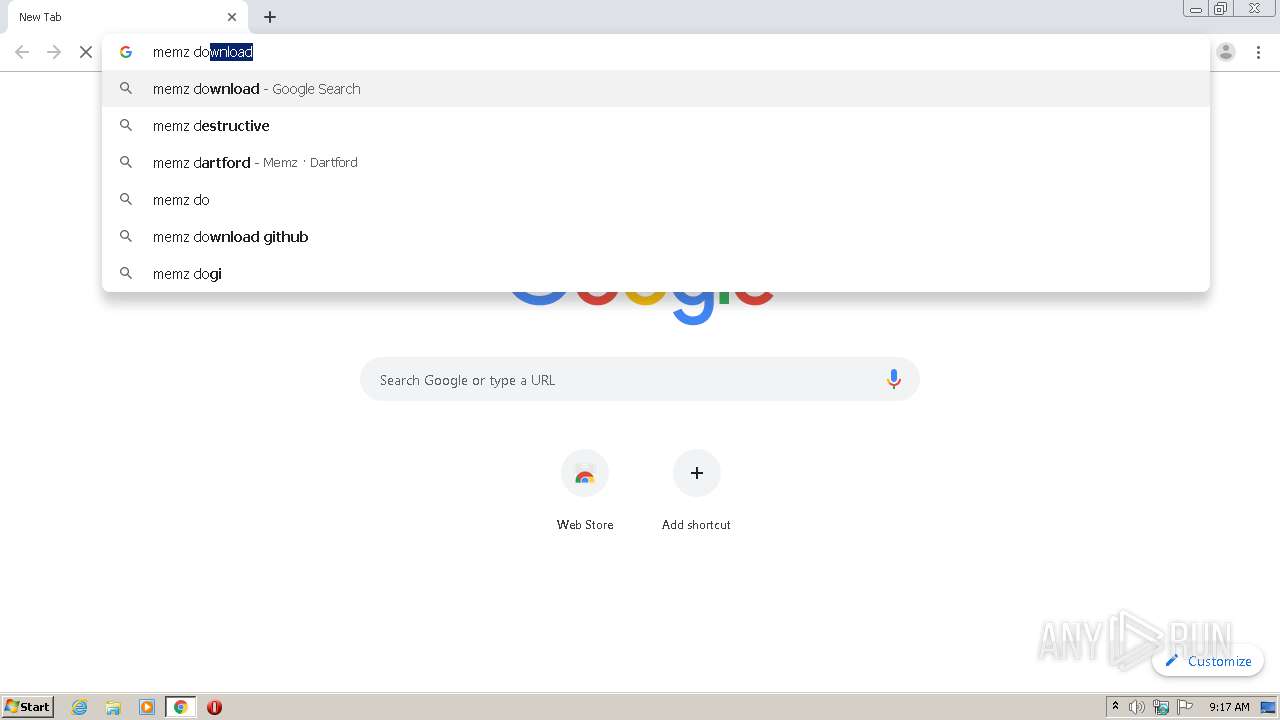
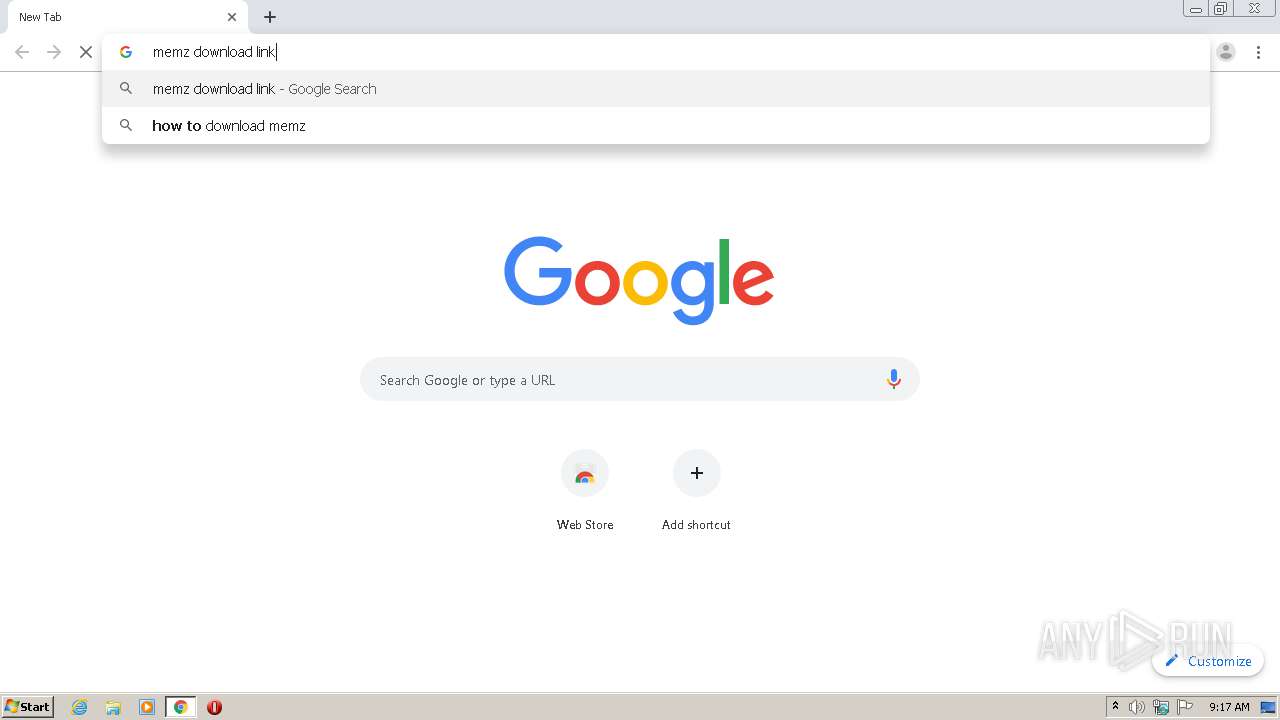
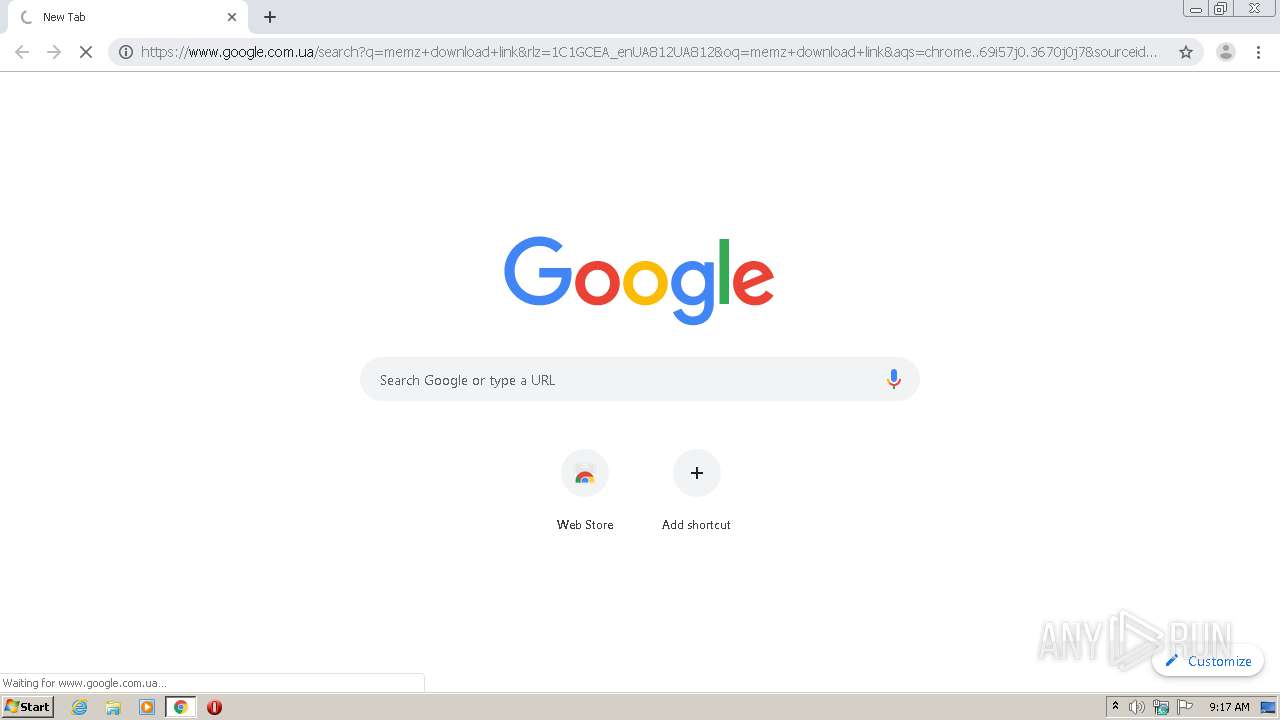
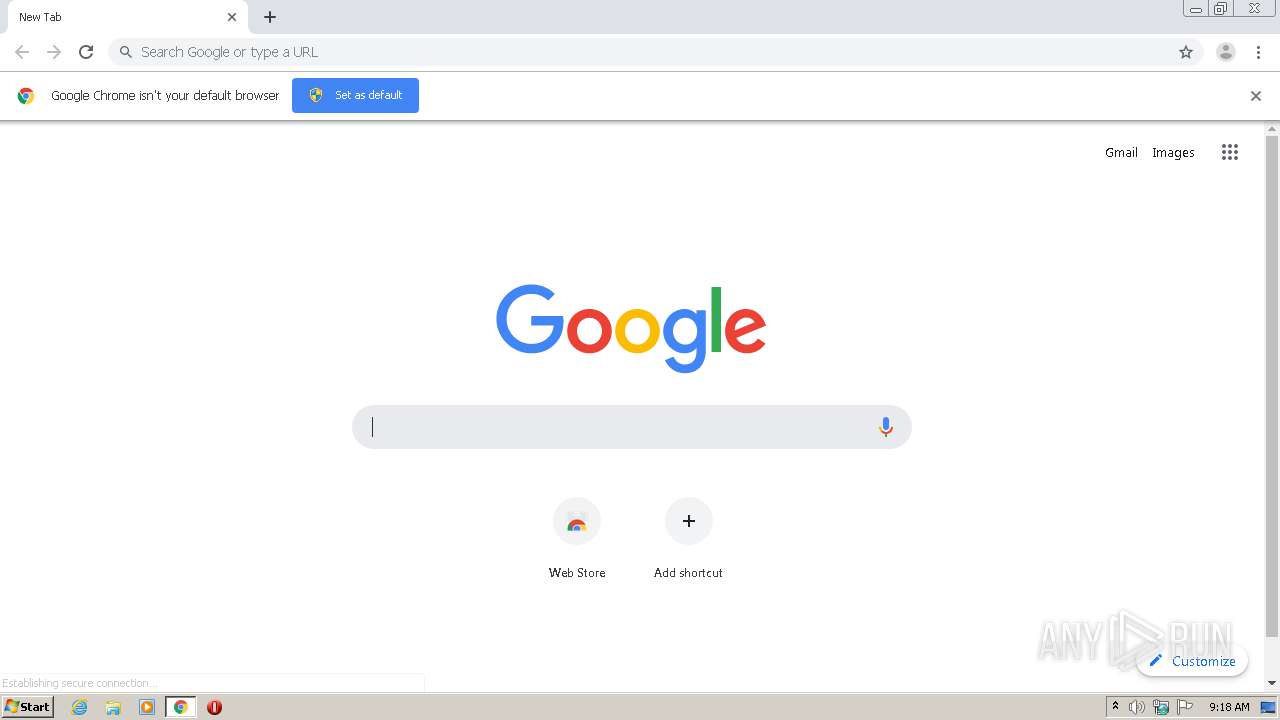
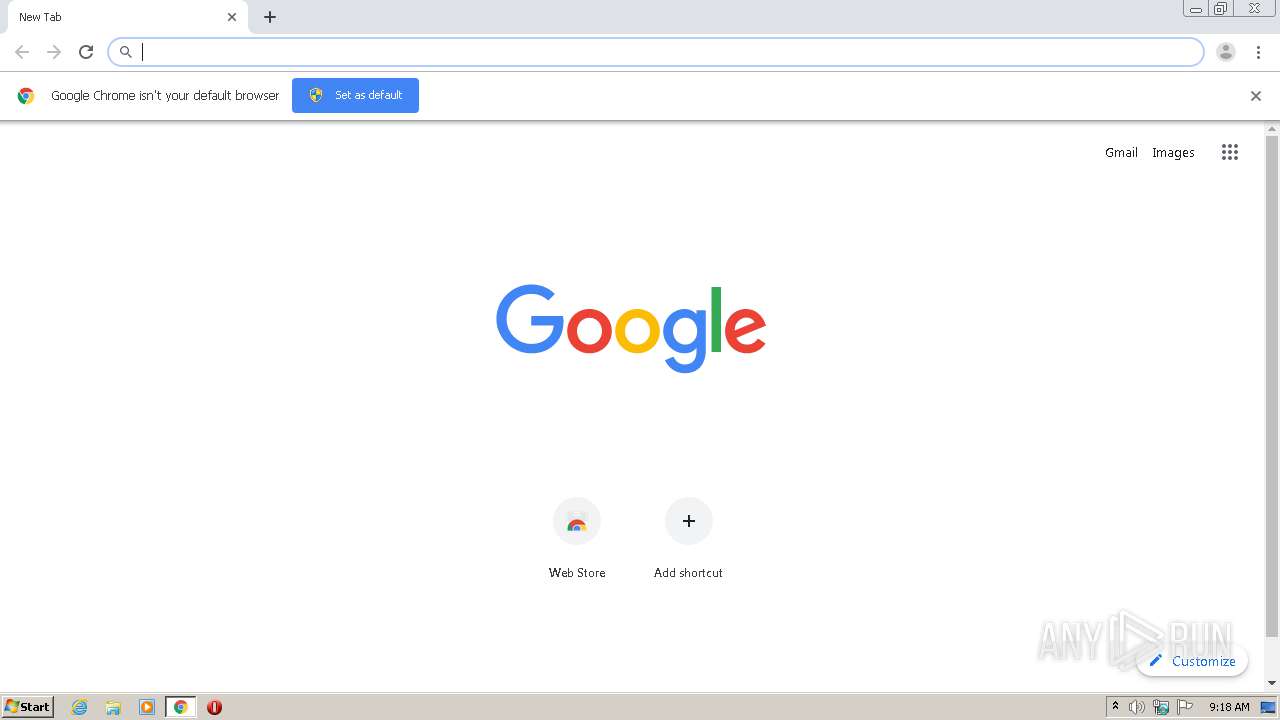
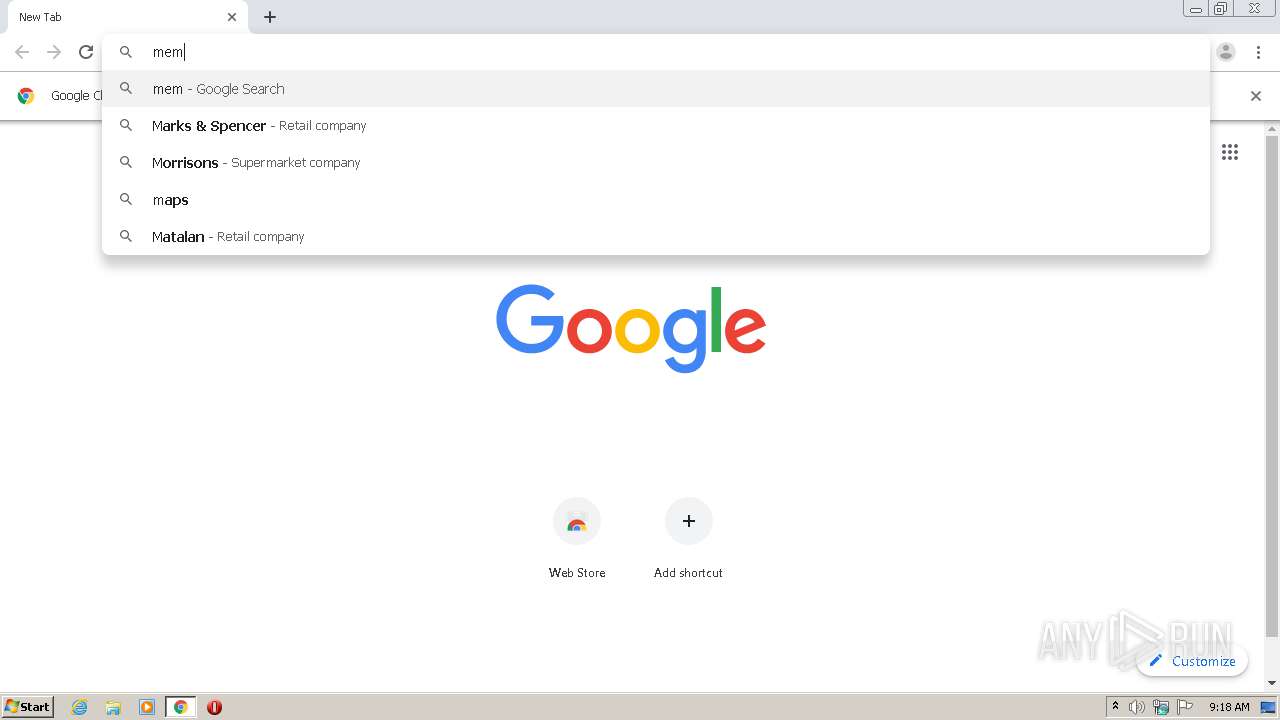
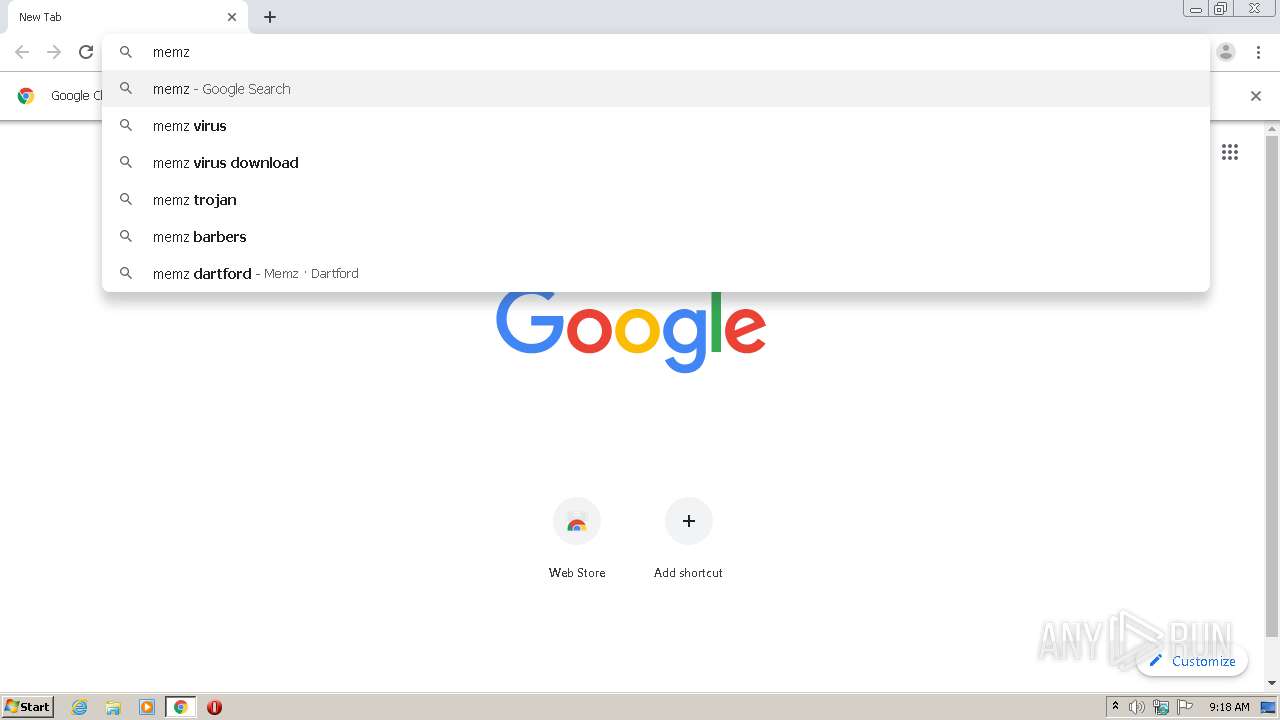
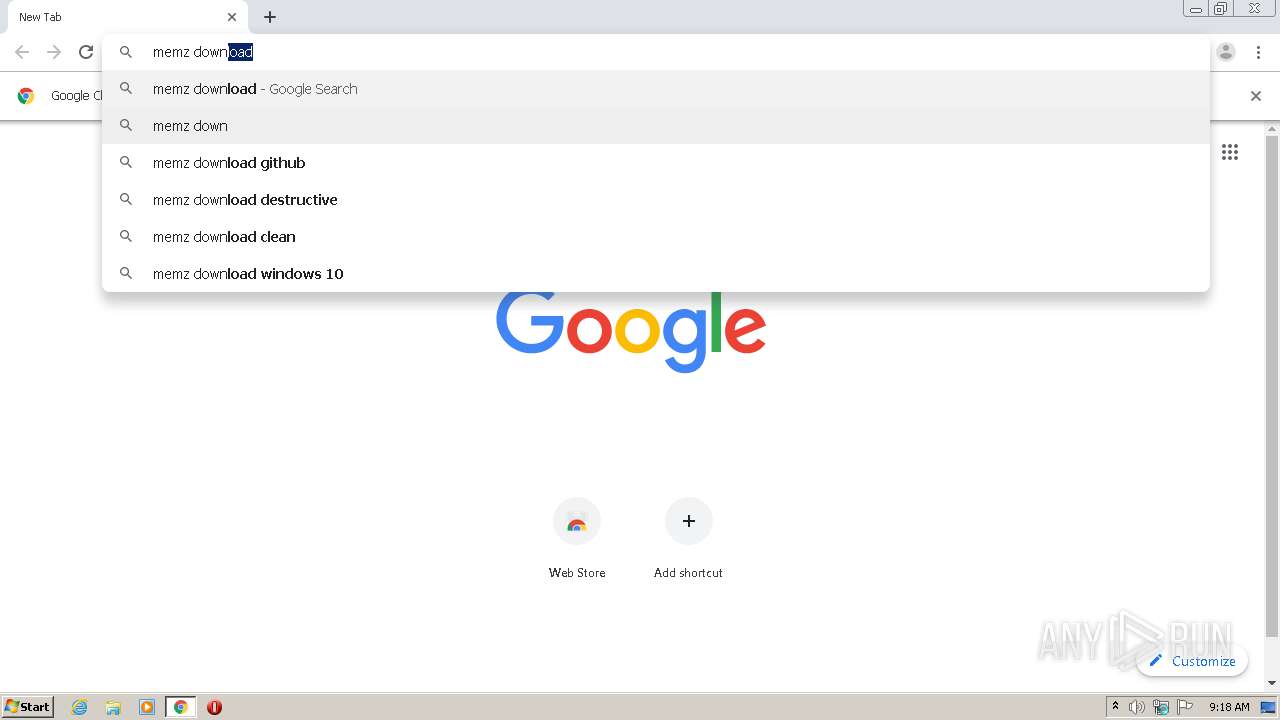
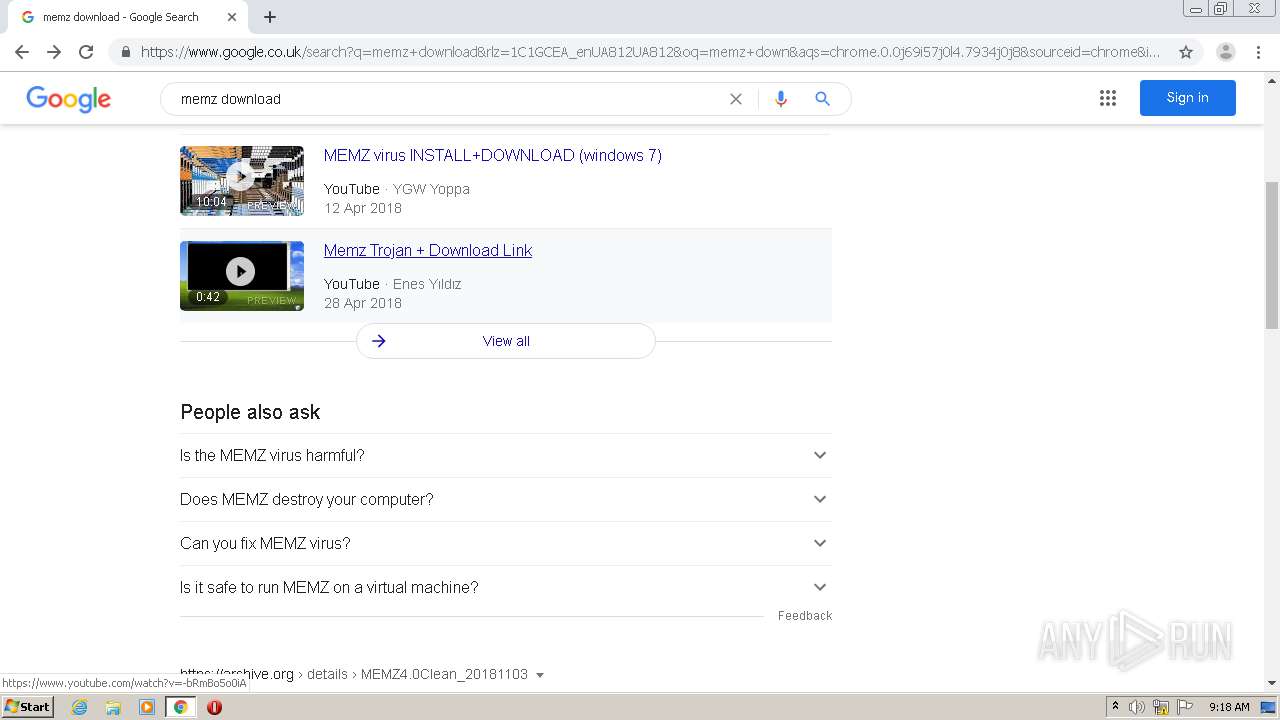
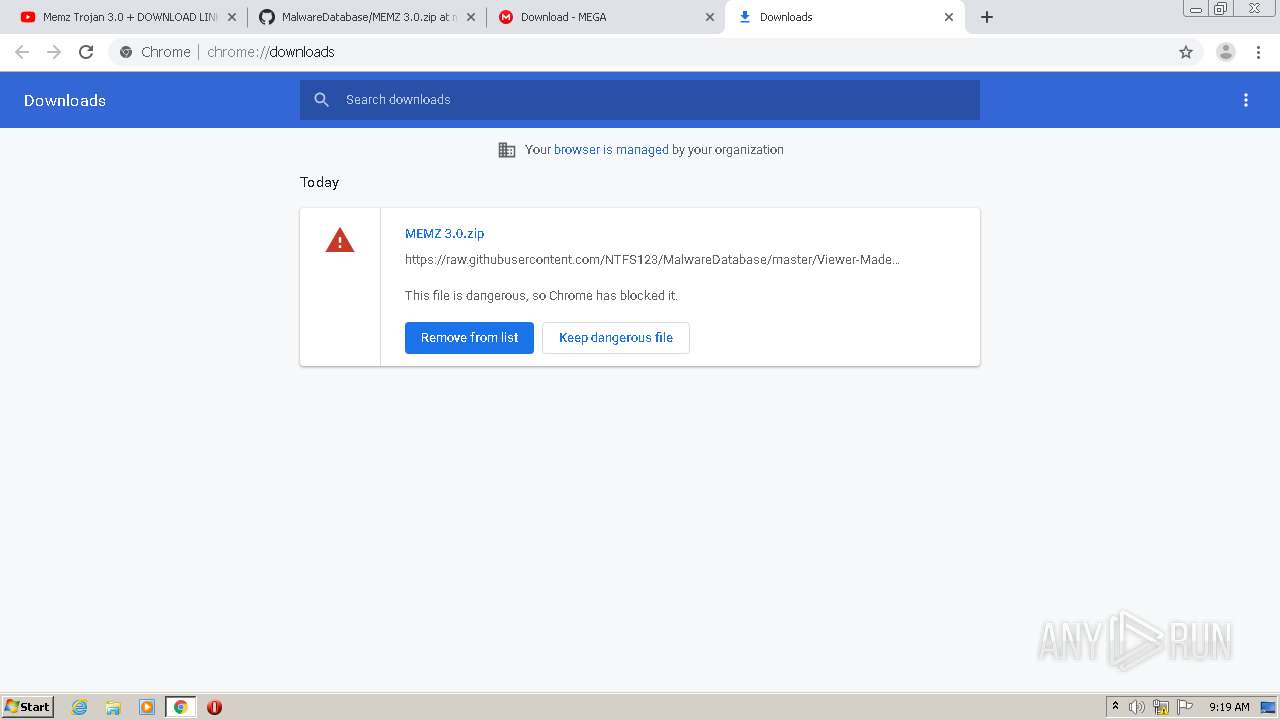
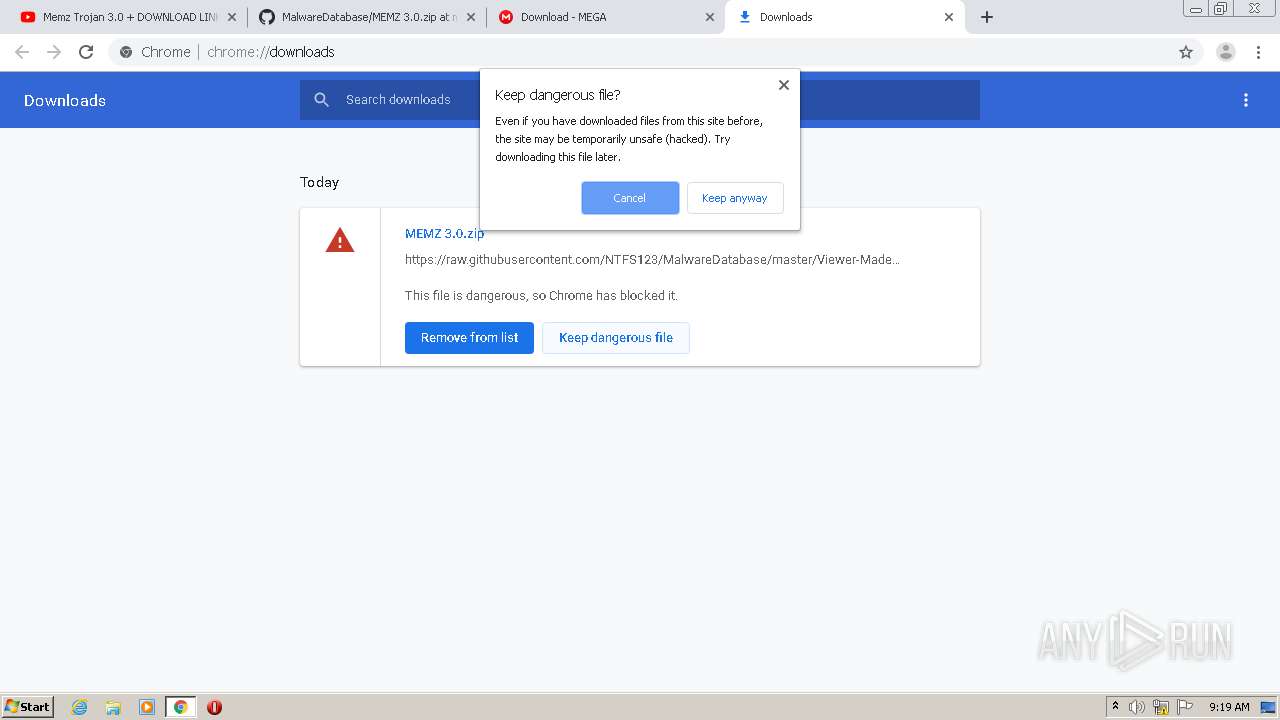
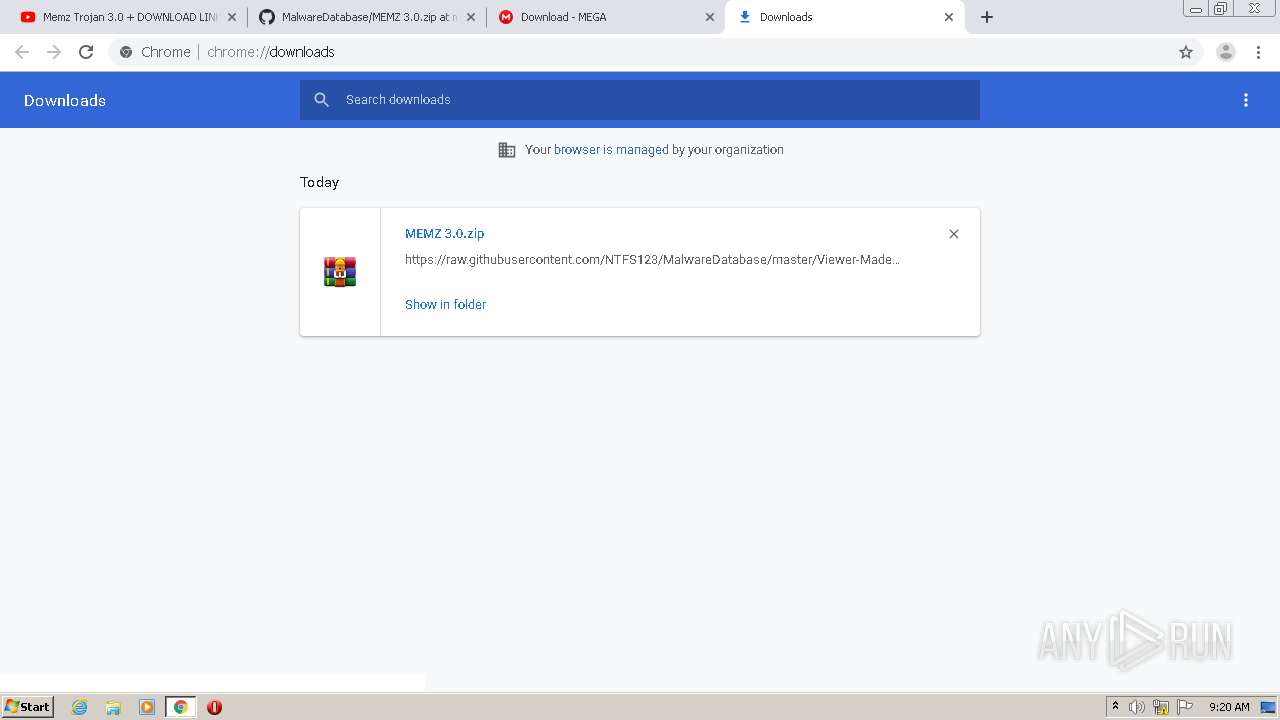
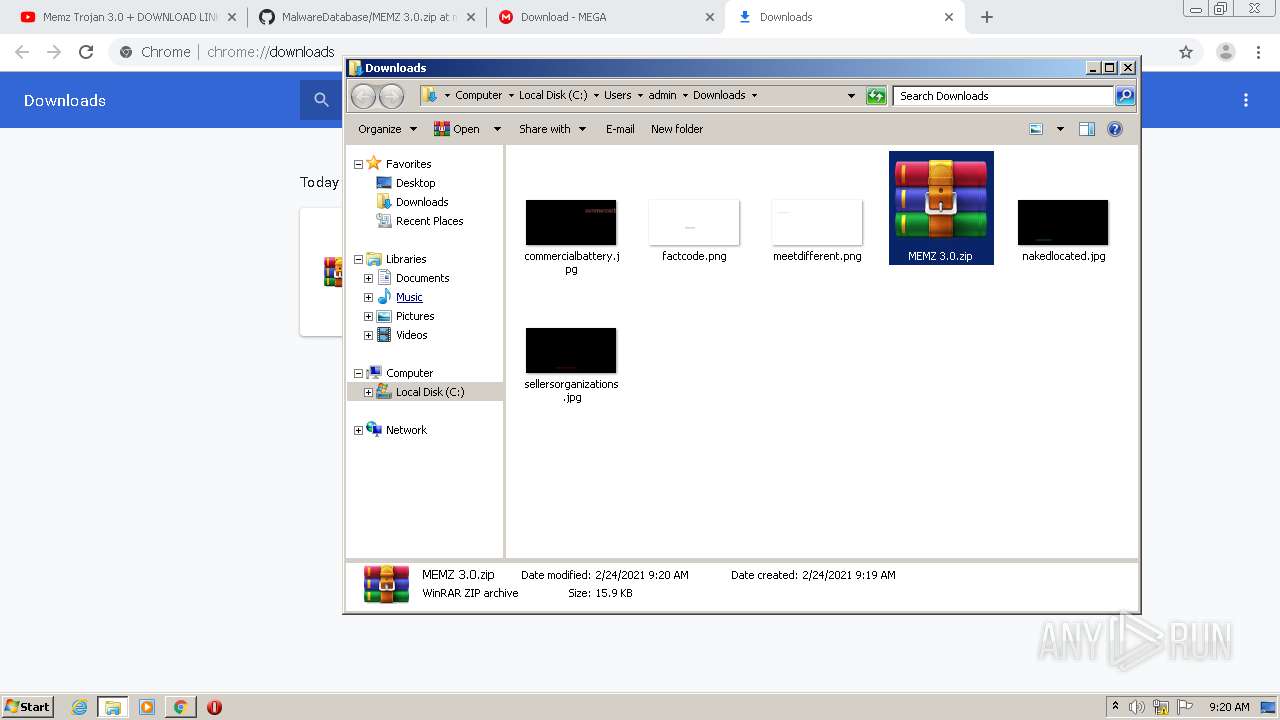
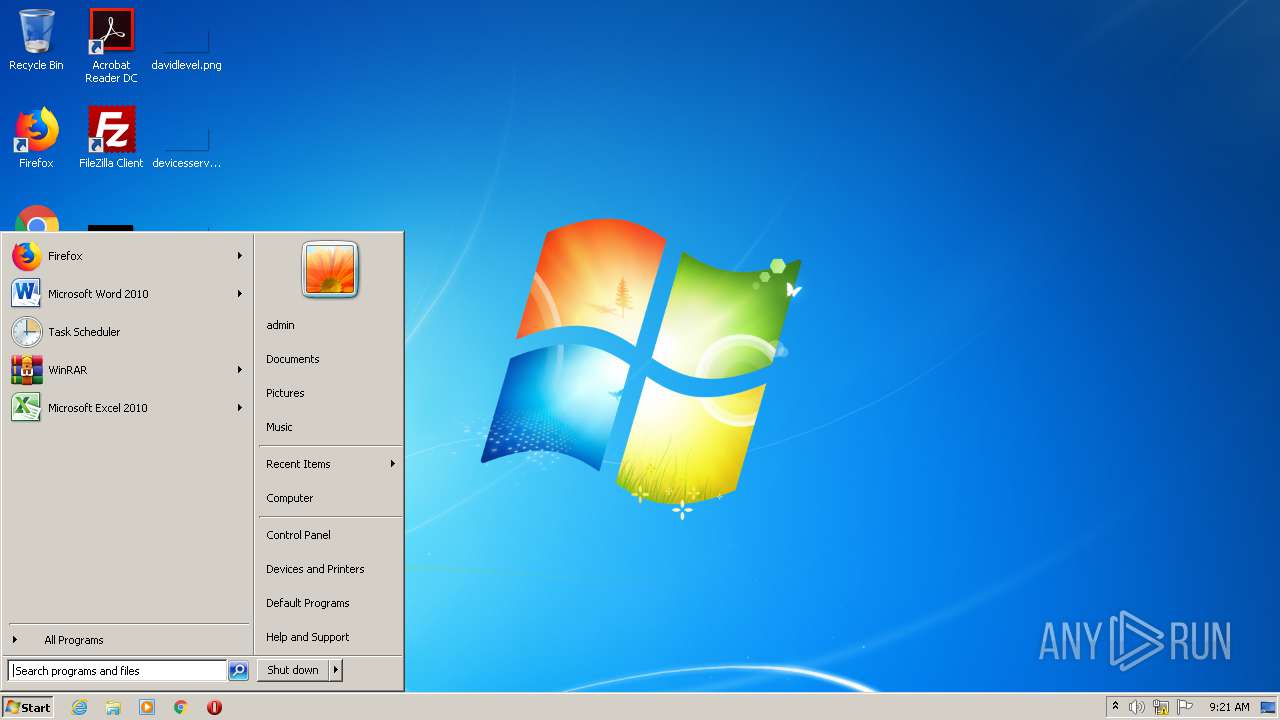
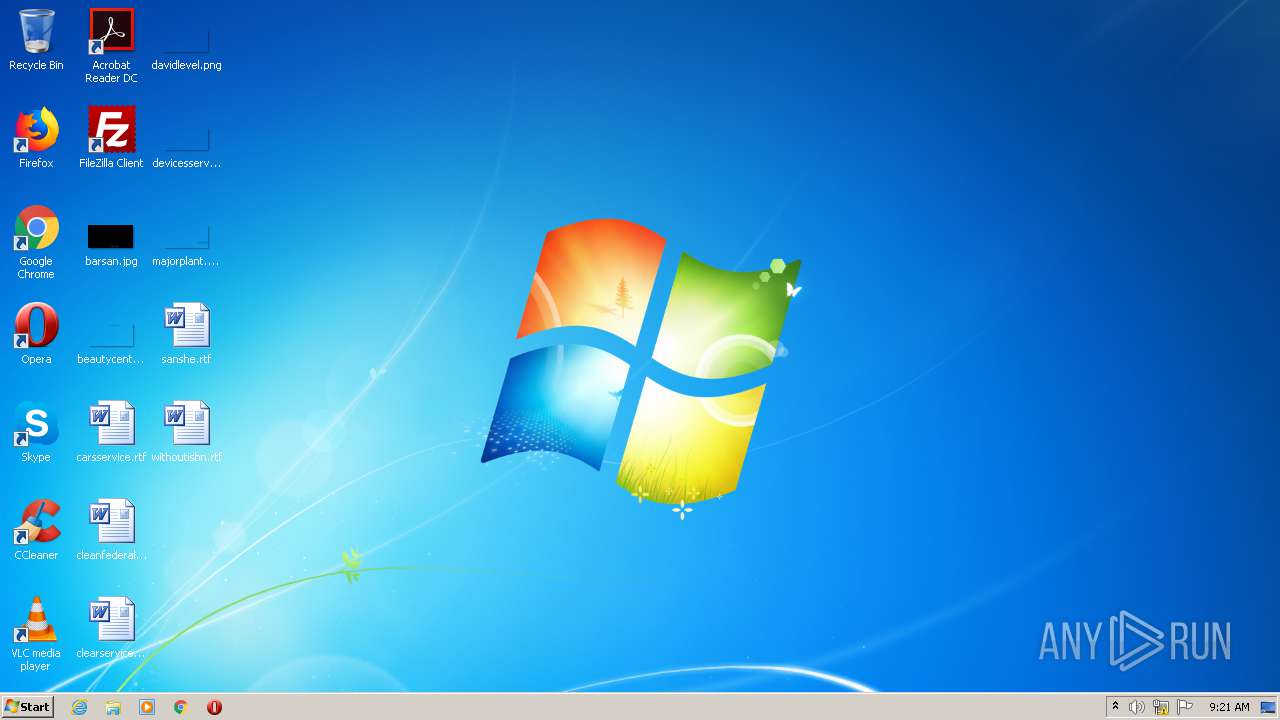
Manual execution by user
- chrome.exe (PID: 784)
- WinRAR.exe (PID: 752)
- chrome.exe (PID: 1248)
- syskey.exe (PID: 3656)
- syskey.exe (PID: 3976)
Reads the hosts file
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1684)
- chrome.exe (PID: 784)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2632)
- chrome.exe (PID: 1248)
Reads settings of System Certificates
- chrome.exe (PID: 3028)
- chrome.exe (PID: 1684)
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 2348)
Application launched itself
- chrome.exe (PID: 784)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1248)
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 1960)
Changes settings of System certificates
- chrome.exe (PID: 2632)
Adds / modifies Windows certificates
- chrome.exe (PID: 2632)
Changes internet zones settings
- iexplore.exe (PID: 2732)
- iexplore.exe (PID: 1960)
Reads internet explorer settings
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 1440)
- iexplore.exe (PID: 2348)
Creates files in the user directory
- iexplore.exe (PID: 2440)
- iexplore.exe (PID: 1440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
185
Monitored processes
125
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5123272437048226681,3385473350402613747,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4578497942042531579 --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5123272437048226681,3385473350402613747,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12809516485184315309 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3672 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,7704034551248023585,5954872579015590869,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1211603198078351750 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,5123272437048226681,3385473350402613747,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15717979972842798385 --mojo-platform-channel-handle=1180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
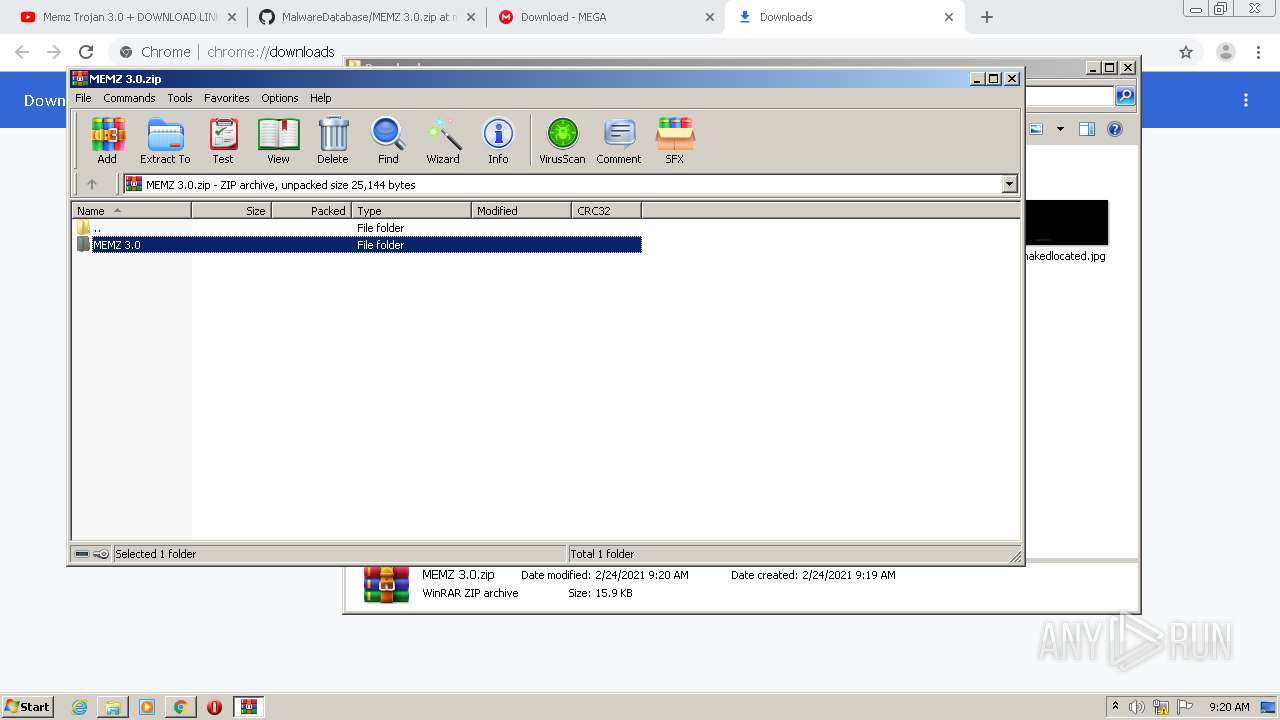
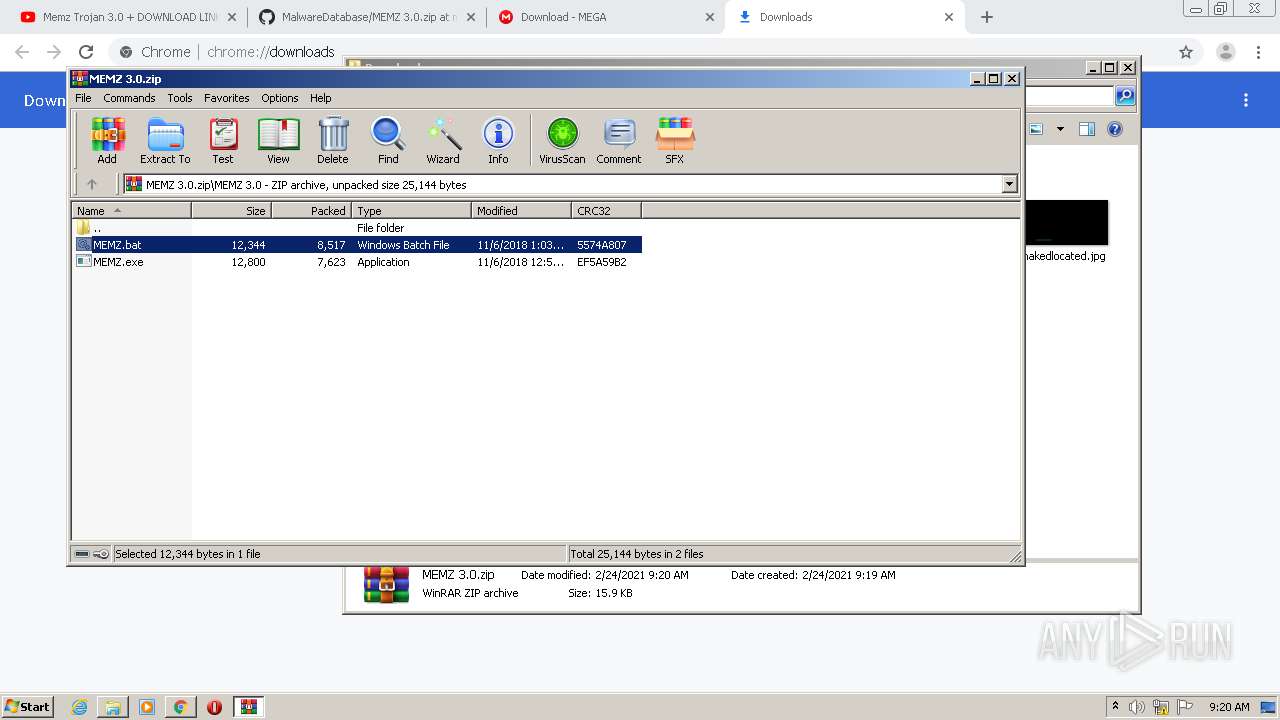
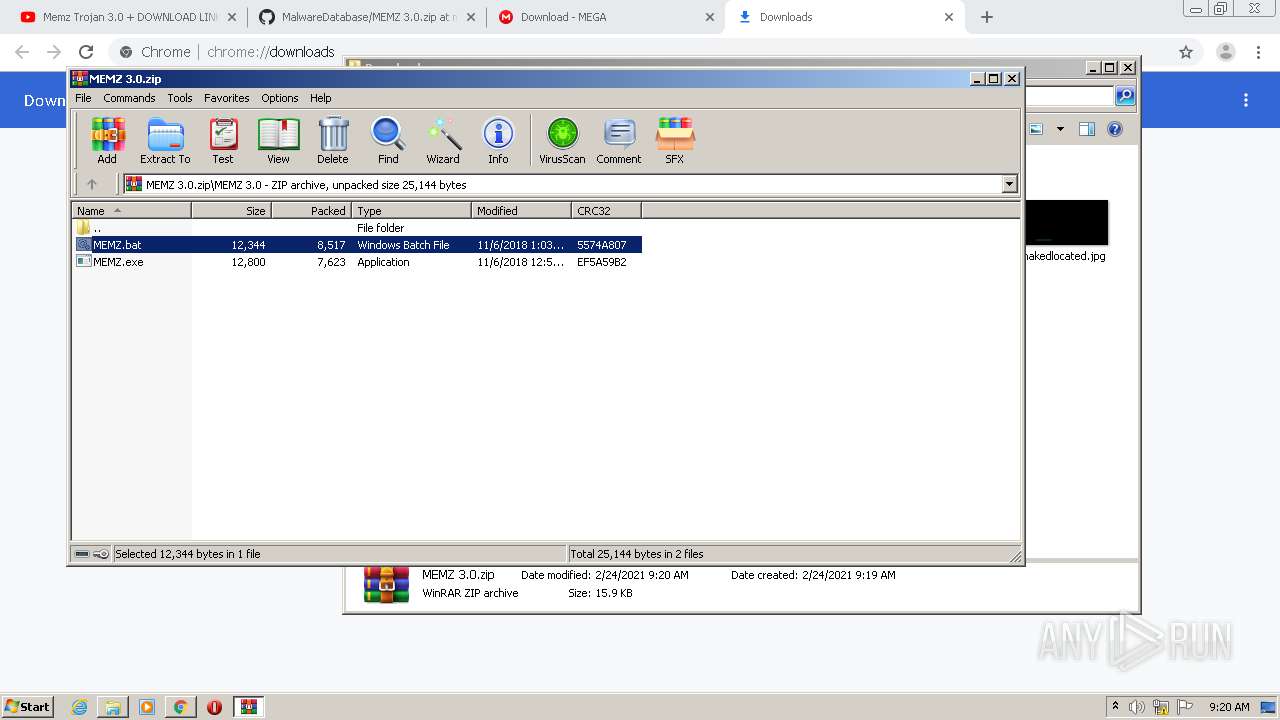
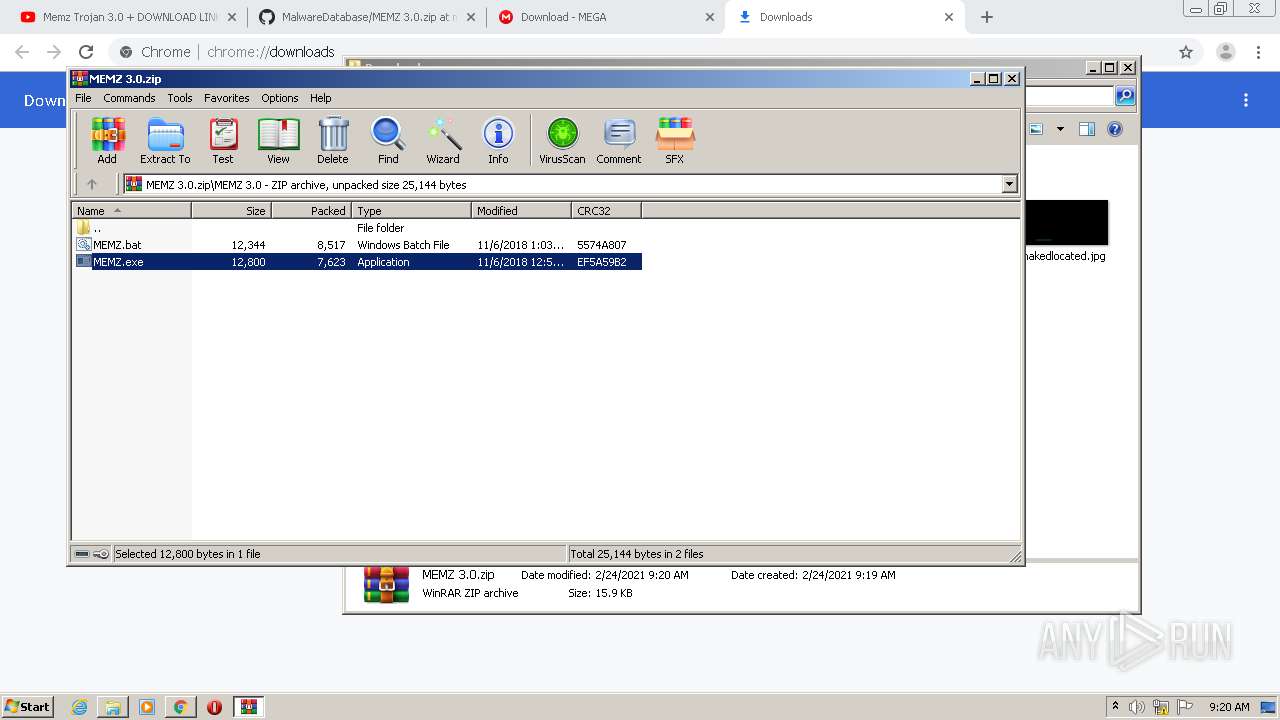
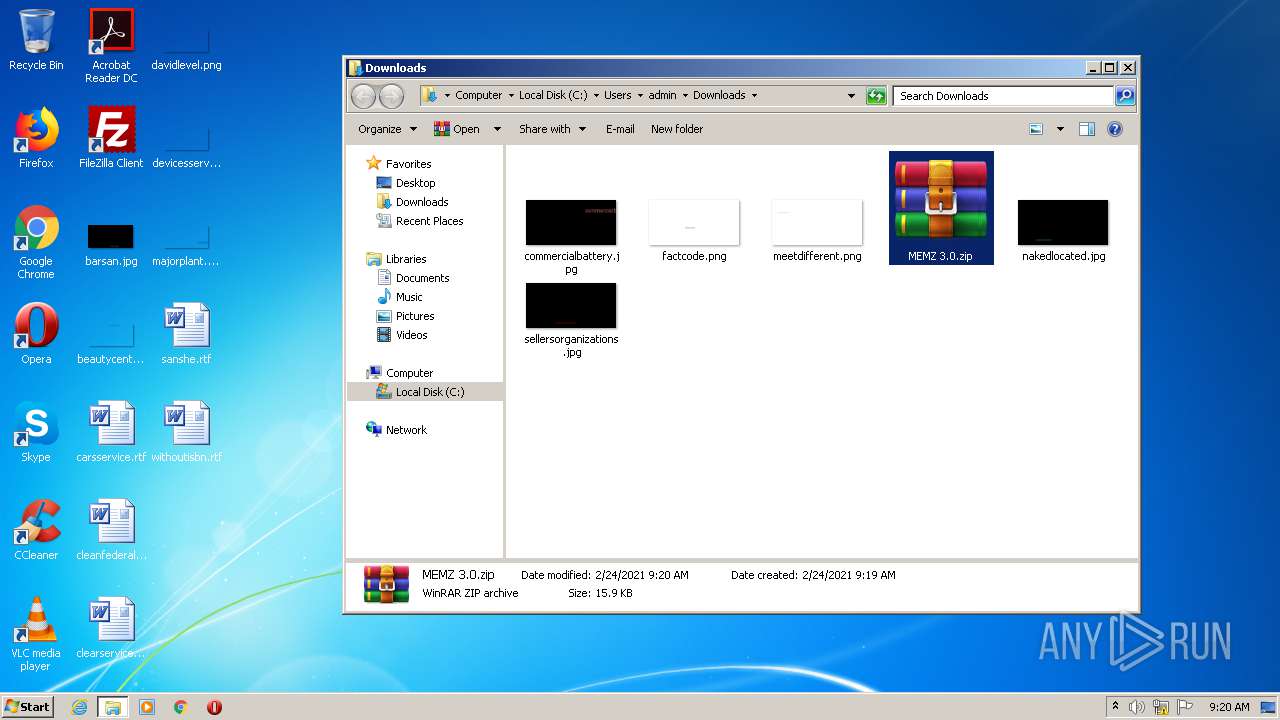
| 752 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\MEMZ 3.0.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5123272437048226681,3385473350402613747,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14648289138311577780 --renderer-client-id=64 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,5123272437048226681,3385473350402613747,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8620740282921473019 --mojo-platform-channel-handle=1300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa752.25460\MEMZ 3.0\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\Rar$EXa752.25460\MEMZ 3.0\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,5123272437048226681,3385473350402613747,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14579704247828388590 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 866
Read events
4 312
Write events
542
Delete events
12
Modification events
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4020) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3788-13258631834754000 |
Value: 259 | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3788) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
356
Text files
677
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6036199B-ECC.pma | — | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13229e.TMP | — | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\acf37bce-4ca5-4040-a662-98aa4925b519.tmp | — | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF13233b.TMP | text | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF132492.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
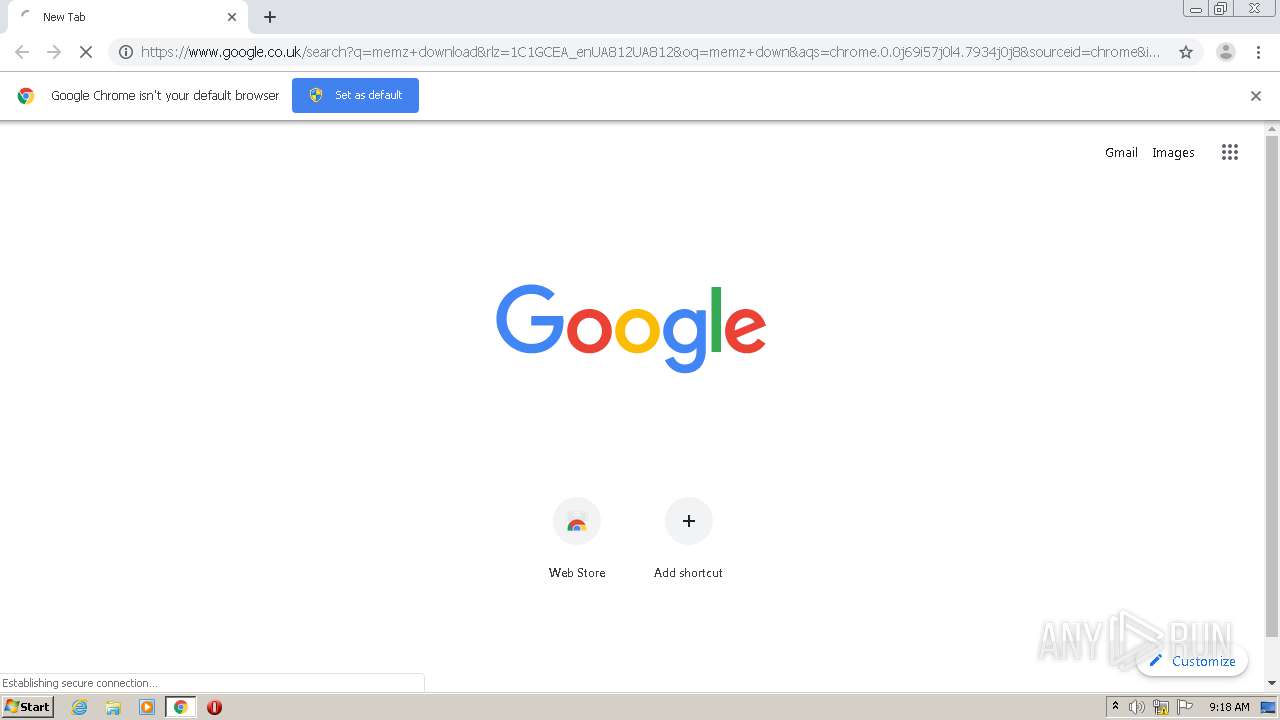
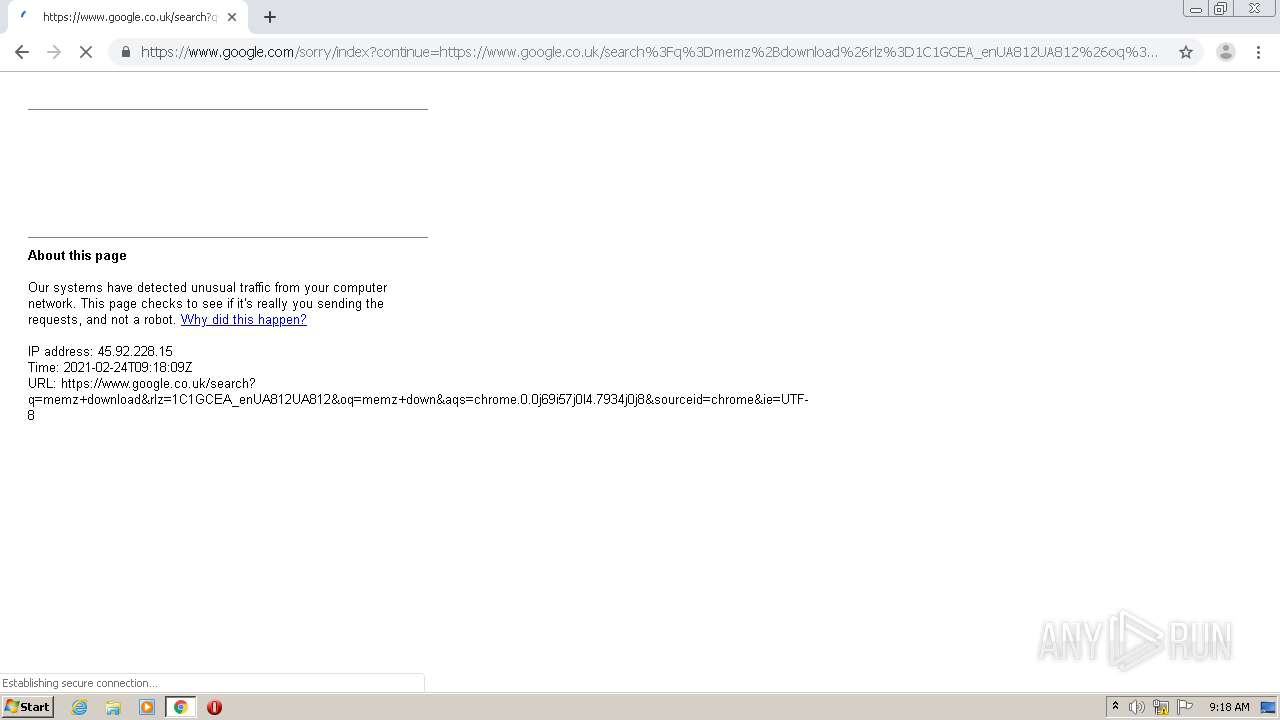
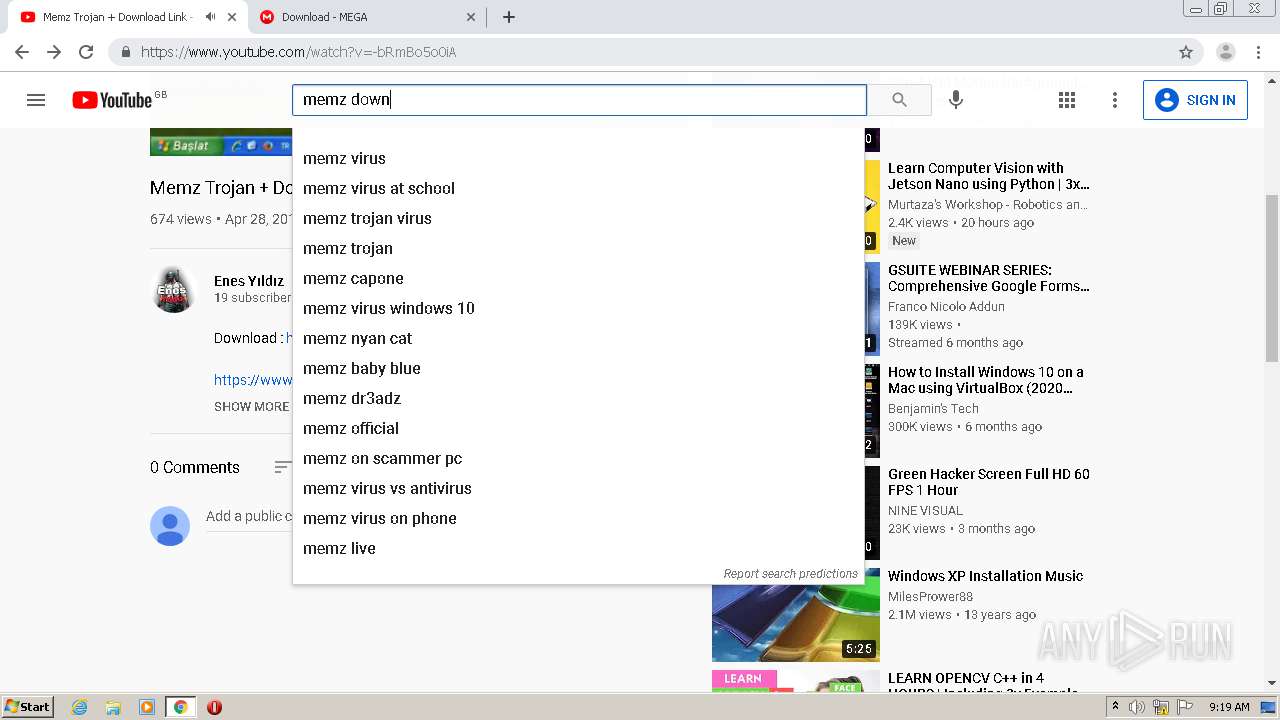
HTTP(S) requests
11
TCP/UDP connections
220
DNS requests
142
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | chrome.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEE%2FYp%2FAP0In4AwAAAADLQKc%3D | US | der | 471 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEA30lC2dcqTOAwAAAADLQMs%3D | US | der | 471 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEE%2FYp%2FAP0In4AwAAAADLQKc%3D | US | der | 471 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDtYUIPuvFnZwUAAAAAh0pf | US | der | 472 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDtYUIPuvFnZwUAAAAAh0pf | US | der | 472 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2440 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2732 | iexplore.exe | GET | 200 | 13.107.22.200:80 | http://www.bing.com/favicon.ico | US | image | 4.19 Kb | whitelisted |
3028 | chrome.exe | GET | 200 | 173.194.150.215:80 | http://r1---sn-5goeen7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=45.92.228.15&mm=28&mn=sn-5goeen7r&ms=nvh&mt=1614157953&mv=m&mvi=1&pl=27&shardbypass=yes | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1684 | chrome.exe | 140.82.121.4:443 | github.com | — | US | malicious |
1684 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
1684 | chrome.exe | 142.250.185.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1684 | chrome.exe | 140.82.121.6:443 | api.github.com | — | US | suspicious |
1684 | chrome.exe | 3.224.212.168:443 | collector.githubapp.com | — | US | unknown |
1684 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
1684 | chrome.exe | 142.250.185.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1684 | chrome.exe | 142.250.185.206:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
1684 | chrome.exe | 142.250.186.65:443 | lh5.googleusercontent.com | Google Inc. | US | whitelisted |
1684 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
collector.githubapp.com |
| whitelisted |
api.github.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |