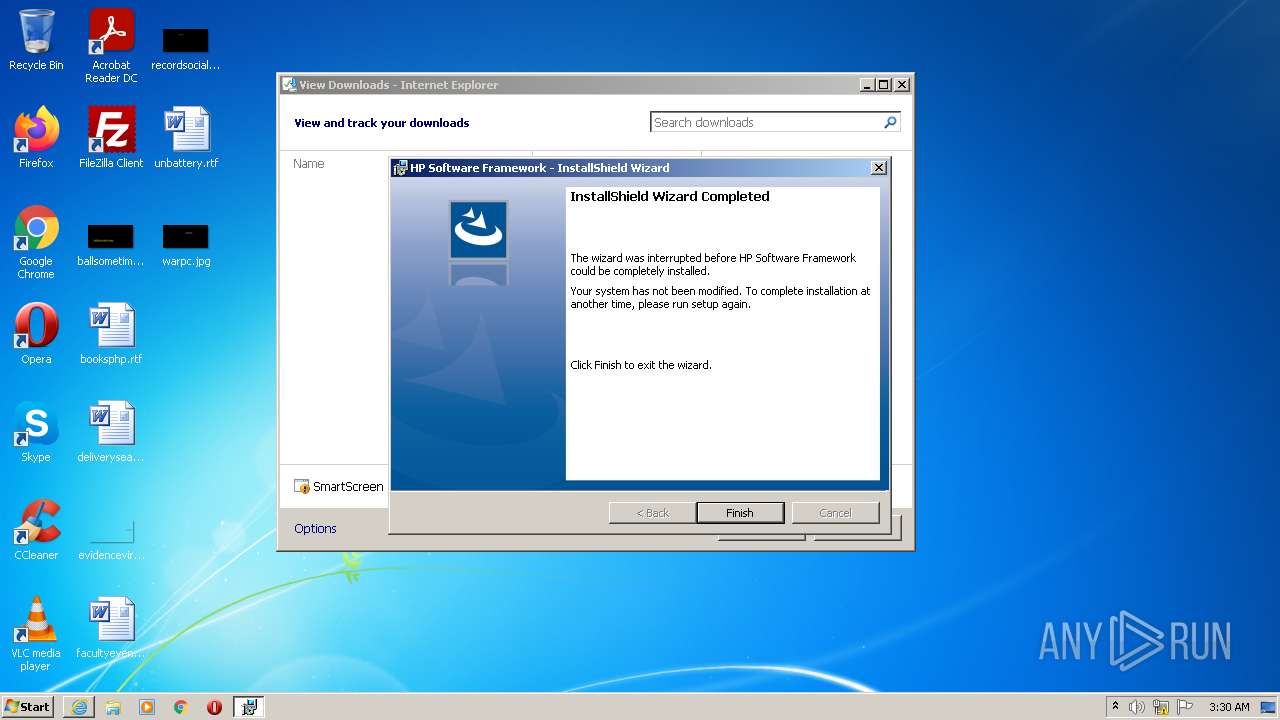
| URL: | https://ftp.hp.com/pub/caps-softpaq/cmit/softpaq/CASLSetup.exe |
| Full analysis: | https://app.any.run/tasks/1be2a555-2c1b-4c4f-8191-92276fef28c1 |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2022, 03:29:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F1CF407DF2DFD21501B752EADAA313A0 |
| SHA1: | C7B18405F106FCAA23BECFF322C773B7CF068A81 |
| SHA256: | 2304A9892AF07EBEDC566051D4A73F997C5DCEEE8771FF840D39ABC2ECE8949C |
| SSDEEP: | 3:N8pLrGT/HdEmWE/t2VL4A:2pLSTHzZEh4A |
MALICIOUS
Drops executable file immediately after starts
- CASLSetup.exe (PID: 3520)
- MSIEXEC.EXE (PID: 2868)
Application was dropped or rewritten from another process
- CASLSetup.exe (PID: 3520)
- CASLSetup.exe (PID: 1324)
- CASLSetup.exe (PID: 1220)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2464)
Drops a file that was compiled in debug mode
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 1256)
- CASLSetup.exe (PID: 3520)
- MSIEXEC.EXE (PID: 2868)
Executable content was dropped or overwritten
- iexplore.exe (PID: 1256)
- CASLSetup.exe (PID: 3520)
- MSIEXEC.EXE (PID: 2868)
- iexplore.exe (PID: 2464)
Checks supported languages
- CASLSetup.exe (PID: 3520)
- CASLSetup.exe (PID: 1324)
Reads the computer name
- CASLSetup.exe (PID: 3520)
- CASLSetup.exe (PID: 1324)
Starts itself from another location
- CASLSetup.exe (PID: 3520)
Executed as Windows Service
- msiexec.exe (PID: 2212)
Reads Windows owner or organization settings
- MSIEXEC.EXE (PID: 2868)
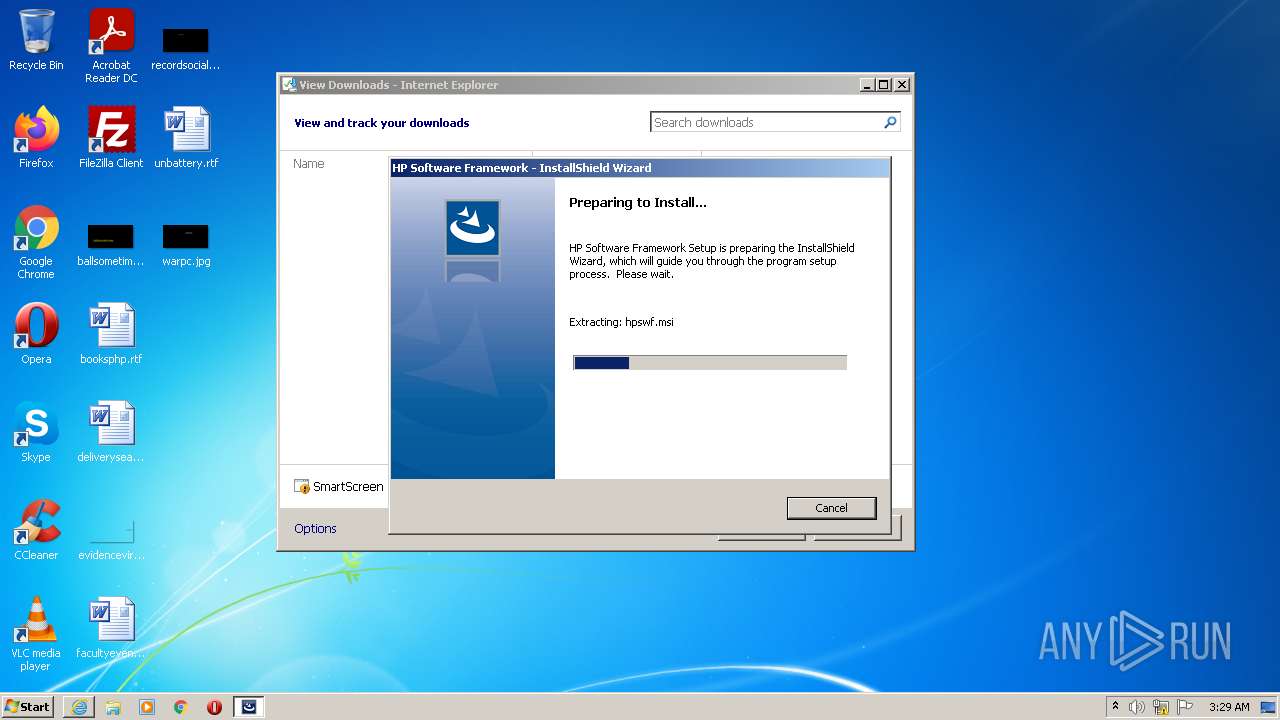
Starts Microsoft Installer
- CASLSetup.exe (PID: 1324)
Application launched itself
- msiexec.exe (PID: 2212)
Creates files in the user directory
- MsiExec.exe (PID: 2872)
Reads the Windows organization settings
- MSIEXEC.EXE (PID: 2868)
INFO
Reads the computer name
- iexplore.exe (PID: 1256)
- MSIEXEC.EXE (PID: 2868)
- msiexec.exe (PID: 2212)
- MsiExec.exe (PID: 2872)
- iexplore.exe (PID: 2464)
Checks supported languages
- iexplore.exe (PID: 1256)
- MSIEXEC.EXE (PID: 2868)
- msiexec.exe (PID: 2212)
- MsiExec.exe (PID: 2872)
- iexplore.exe (PID: 2464)
Application launched itself
- iexplore.exe (PID: 1256)
Reads settings of System Certificates
- iexplore.exe (PID: 1256)
- MSIEXEC.EXE (PID: 2868)
- iexplore.exe (PID: 2464)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1256)
Checks Windows Trust Settings
- iexplore.exe (PID: 1256)
- MSIEXEC.EXE (PID: 2868)
- iexplore.exe (PID: 2464)
Reads the date of Windows installation
- iexplore.exe (PID: 1256)
Changes internet zones settings
- iexplore.exe (PID: 1256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
9
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1220 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\CASLSetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\CASLSetup.exe | — | iexplore.exe | |||||||||||
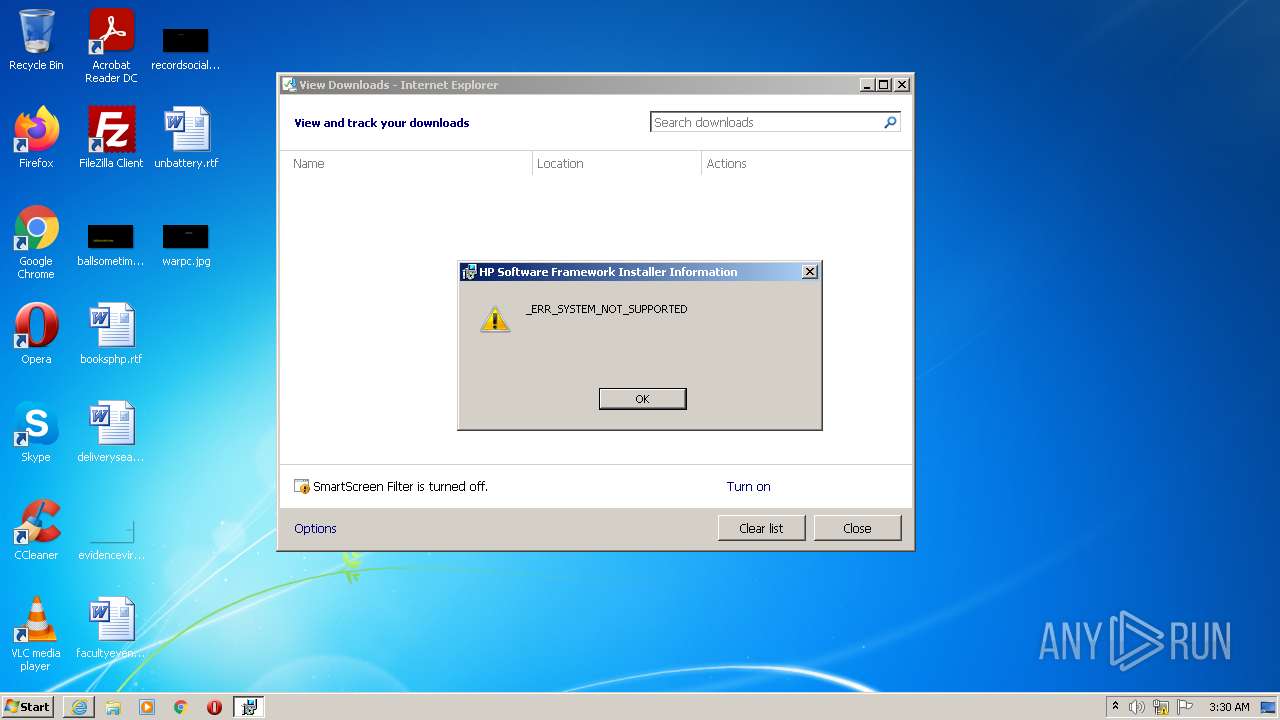
User: admin Company: HP Integrity Level: MEDIUM Description: Contact: Your local administrator Exit code: 3221226540 Version: 7.1.13.1 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ftp.hp.com/pub/caps-softpaq/cmit/softpaq/CASLSetup.exe" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1324 | C:\Users\admin\AppData\Local\Temp\{F10327A9-5D7D-48AA-ADDF-1FA805B6FEA6}\CASLSetup.exe /q"C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\CASLSetup.exe" /tempdisk1folder"C:\Users\admin\AppData\Local\Temp\{F10327A9-5D7D-48AA-ADDF-1FA805B6FEA6}" /IS_temp | C:\Users\admin\AppData\Local\Temp\{F10327A9-5D7D-48AA-ADDF-1FA805B6FEA6}\CASLSetup.exe | — | CASLSetup.exe | |||||||||||
User: admin Company: HP Integrity Level: HIGH Description: Contact: Your local administrator Exit code: 1603 Version: 7.1.13.1 Modules
| |||||||||||||||
| 1708 | explorer.exe | C:\Windows\explorer.exe | — | CASLSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1256 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2868 | "C:\Windows\system32\MSIEXEC.EXE" /i "C:\Users\admin\AppData\Local\Downloaded Installations\{6F1A0D94-D2DA-4FE9-BDEB-5B88C64FFF63}\hpswf.msi" SETUPEXEDIR="C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP" SETUPEXENAME="CASLSetup.exe" | C:\Windows\system32\MSIEXEC.EXE | CASLSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 1603 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | C:\Windows\system32\MsiExec.exe -Embedding 38D9F32E20DC5ECE890318467185C903 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3520 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\CASLSetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\CASLSetup.exe | iexplore.exe | ||||||||||||
User: admin Company: HP Integrity Level: HIGH Description: Contact: Your local administrator Exit code: 0 Version: 7.1.13.1 Modules
| |||||||||||||||
Total events
15 648
Read events
15 542
Write events
106
Delete events
0
Modification events
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939310 | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939310 | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1256) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
8
Text files
15
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_FB287BEB63DB9E8D59A799779773B97C | der | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3511432A9C855433197DDE28B90F02F4_08BB09EA60894C6B938FAA05B6D92801 | binary | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_FB287BEB63DB9E8D59A799779773B97C | binary | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3511432A9C855433197DDE28B90F02F4_08BB09EA60894C6B938FAA05B6D92801 | der | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3511432A9C855433197DDE28B90F02F4_43A02A2C1473EC0216C530BC71A9F232 | binary | |
MD5:— | SHA256:— | |||
| 1324 | CASLSetup.exe | C:\Users\admin\AppData\Local\Temp\{F10327A9-5D7D-48AA-ADDF-1FA805B6FEA6}\hpswf.msi | — | |
MD5:— | SHA256:— | |||
| 1324 | CASLSetup.exe | C:\Users\admin\AppData\Local\Downloaded Installations\{6F1A0D94-D2DA-4FE9-BDEB-5B88C64FFF63}\hpswf.msi | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\CASLSetup[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\CASLSetup[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
12
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAhflMAthXvozBT%2FU%2B2iPio%3D | US | der | 471 b | whitelisted |
1256 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAdJ0r1PzwZrTc3%2BpSTqBmU%3D | US | der | 471 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAmwRGJ3T7nf3ikAsZvq6Zw%3D | US | der | 471 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?50539304c6442a1b | US | compressed | 4.70 Kb | whitelisted |
2464 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4ce3e8b87316fdf2 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | iexplore.exe | 15.73.48.54:443 | ftp.hp.com | Hewlett-Packard Company | US | suspicious |
2464 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
2464 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1256 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1256 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2464 | iexplore.exe | 8.241.89.248:443 | ftp.ext.hp.com | Level 3 Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ftp.hp.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ftp.ext.hp.com |
| suspicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |