| File name: | Sandboxie-Classic-x64-v5.69.8.exe |
| Full analysis: | https://app.any.run/tasks/f3b6f76c-2be5-404f-9c95-d82cfe2f3ad7 |
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2024, 13:27:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E40DF696420D4120650F41F2AD309691 |
| SHA1: | AFC524587C8A305696A2EE708E2890E7F49AFEED |
| SHA256: | 22E7BCCA423DD57974DC82D9E90DBFFF76CA18D077C85C1DDC125C5AAF872937 |
| SSDEEP: | 98304:E37F4l2wvacT9KMnLegxdWCcww2FO4i/kvOPIPn1Npn1K2uDQ2zZCnoM7MBN3Y4j:D9LtCQw5p |
MALICIOUS
Changes the autorun value in the registry
- SbieCtrl.exe (PID: 5148)
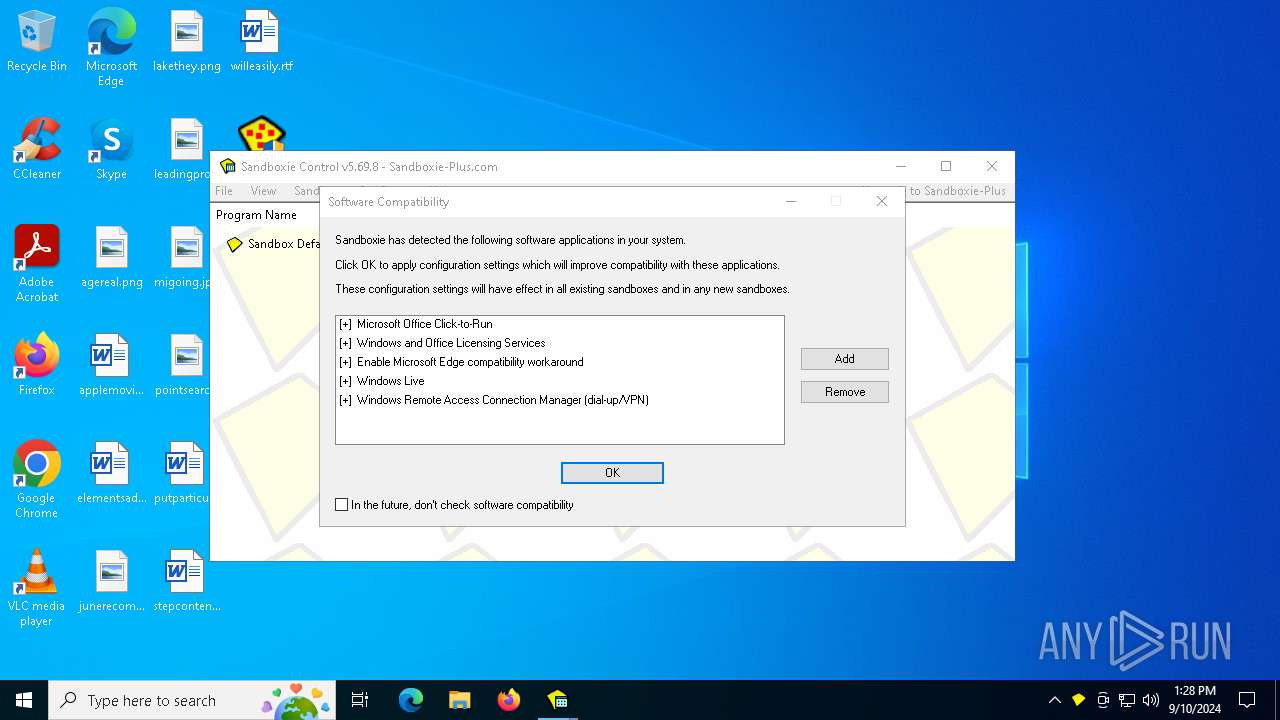
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
The process creates files with name similar to system file names
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
Executable content was dropped or overwritten
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
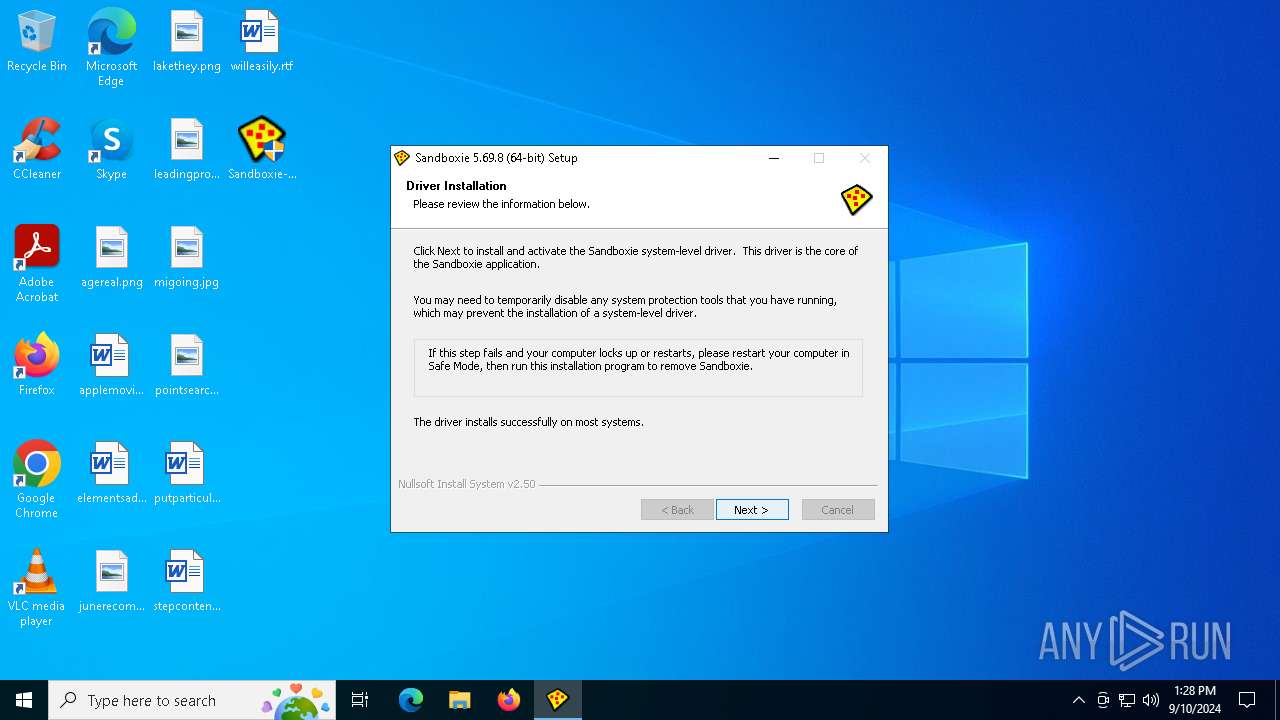
Drops a system driver (possible attempt to evade defenses)
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
Reads security settings of Internet Explorer
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
- SbieCtrl.exe (PID: 5148)
Creates a software uninstall entry
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
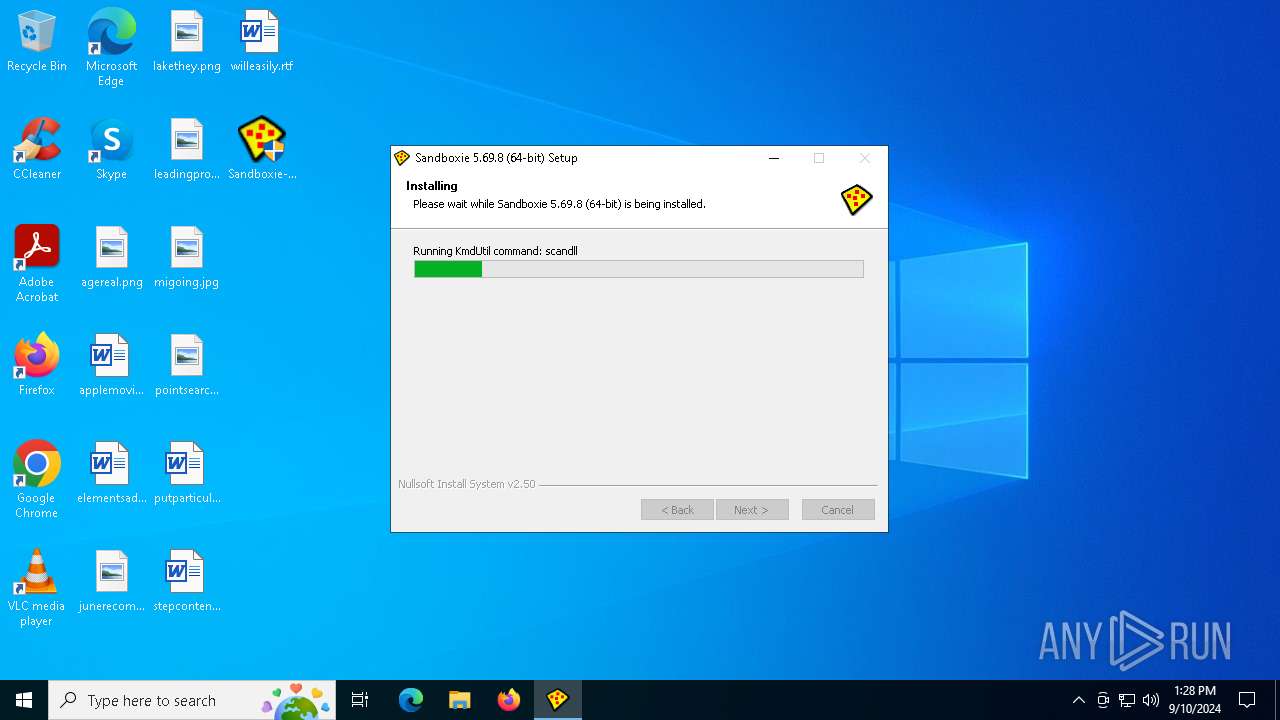
Creates or modifies Windows services
- KmdUtil.exe (PID: 6248)
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
Reads Microsoft Outlook installation path
- SbieCtrl.exe (PID: 5148)
Executes as Windows Service
- SbieSvc.exe (PID: 2624)
Reads Internet Explorer settings
- SbieCtrl.exe (PID: 5148)
INFO
Create files in a temporary directory
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
Checks supported languages
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
- KmdUtil.exe (PID: 7156)
- KmdUtil.exe (PID: 7028)
- KmdUtil.exe (PID: 3164)
- KmdUtil.exe (PID: 2264)
- UpdUtil.exe (PID: 2008)
- KmdUtil.exe (PID: 6416)
- KmdUtil.exe (PID: 6248)
- SbieCtrl.exe (PID: 5148)
- SbieSvc.exe (PID: 2624)
- Start.exe (PID: 5888)
Reads Environment values
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
Reads the computer name
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
- KmdUtil.exe (PID: 7028)
- KmdUtil.exe (PID: 3164)
- KmdUtil.exe (PID: 2264)
- KmdUtil.exe (PID: 6416)
- KmdUtil.exe (PID: 7156)
- KmdUtil.exe (PID: 6248)
- Start.exe (PID: 5888)
- SbieSvc.exe (PID: 2624)
- SbieCtrl.exe (PID: 5148)
Creates files in the program directory
- Sandboxie-Classic-x64-v5.69.8.exe (PID: 2456)
Creates files or folders in the user directory
- SbieCtrl.exe (PID: 5148)
Checks proxy server information
- SbieCtrl.exe (PID: 5148)
The process uses the downloaded file
- SbieCtrl.exe (PID: 5148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:27 05:38:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x324f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.69.8.0 |
| ProductVersionNumber: | 5.69.8.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Sandboxie-Plus.com |
| FileDescription: | Sandboxie Installer |
| FileVersion: | 5.69.8 |
| LegalCopyright: | Copyright © 2020-2024 by David Xanatos (xanasoft.com) |
| ProductName: | Sandboxie |
| ProductVersion: | 5.69.8 |
Total processes
137
Monitored processes
13
Malicious processes
2
Suspicious processes
1
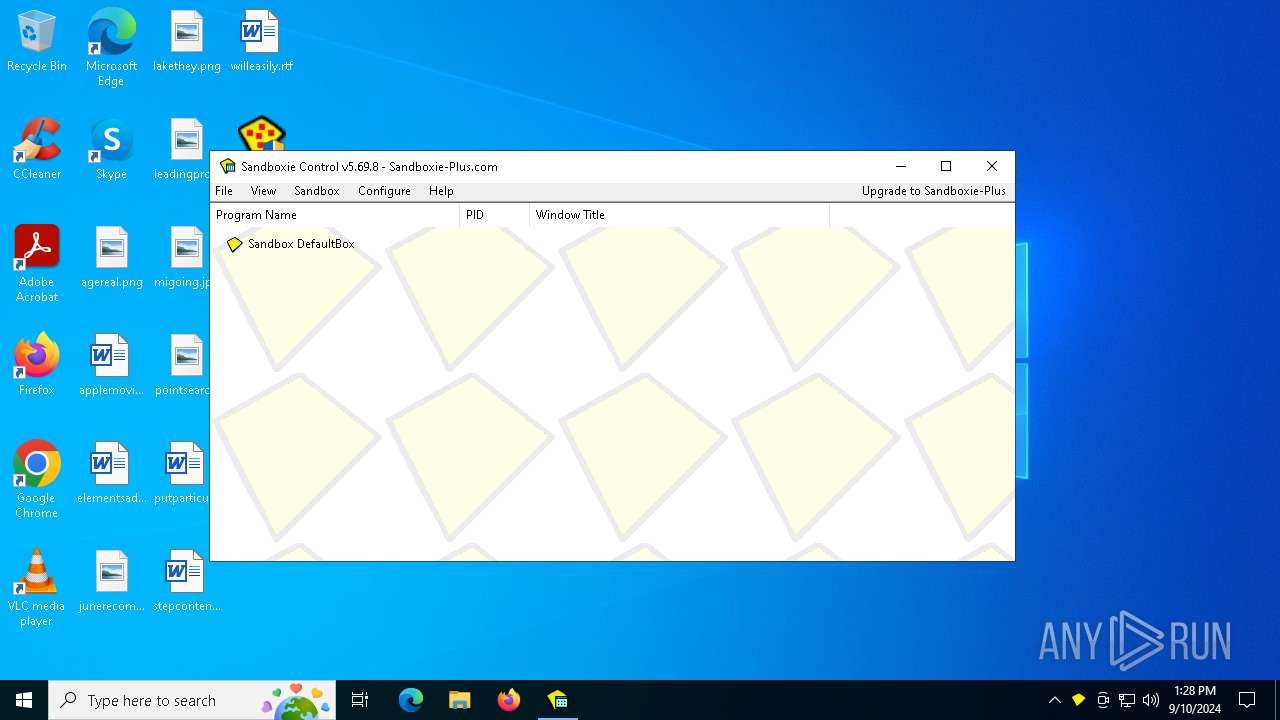
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2008 | "C:\Program Files\Sandboxie\UpdUtil.exe" install sandboxie /step:scan /scope:meta /version:5.69.8 | C:\Program Files\Sandboxie\UpdUtil.exe | — | Sandboxie-Classic-x64-v5.69.8.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967293 Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\KmdUtil.exe" /lang=1033 start SbieSvc | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\KmdUtil.exe | — | Sandboxie-Classic-x64-v5.69.8.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.69.8 Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\Desktop\Sandboxie-Classic-x64-v5.69.8.exe" | C:\Users\admin\Desktop\Sandboxie-Classic-x64-v5.69.8.exe | explorer.exe | ||||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie Installer Exit code: 0 Version: 5.69.8 Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Sandboxie\SbieSvc.exe" | C:\Program Files\Sandboxie\SbieSvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Sandboxie-Plus.com Integrity Level: SYSTEM Description: Sandboxie Service Version: 5.69.8 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\KmdUtil.exe" /lang=1033 install SbieSvc "\"C:\Program Files\Sandboxie\SbieSvc.exe"\" type=own start=auto "display=Sandboxie Service" group=UIGroup "msgfile=C:\Program Files\Sandboxie\SbieMsg.dll" | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\KmdUtil.exe | — | Sandboxie-Classic-x64-v5.69.8.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.69.8 Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\Desktop\Sandboxie-Classic-x64-v5.69.8.exe" | C:\Users\admin\Desktop\Sandboxie-Classic-x64-v5.69.8.exe | — | explorer.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: MEDIUM Description: Sandboxie Installer Exit code: 3221226540 Version: 5.69.8 Modules
| |||||||||||||||
| 5148 | "C:\Program Files\Sandboxie\SbieCtrl.exe" /open /sync /postsetup | C:\Program Files\Sandboxie\SbieCtrl.exe | SbieSvc.exe | ||||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: MEDIUM Description: Sandboxie Control Version: 5.69.8 Modules
| |||||||||||||||
| 5888 | "C:\Program Files\Sandboxie\Start.exe" open_agent:"SbieCtrl.exe /open /sync /postsetup" | C:\Program Files\Sandboxie\Start.exe | — | Sandboxie-Classic-x64-v5.69.8.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie Start Exit code: 0 Version: 5.69.8 Modules
| |||||||||||||||
| 6172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UpdUtil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6248 | "C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\KmdUtil.exe" /lang=1033 install SbieDrv "C:\Program Files\Sandboxie\SbieDrv.sys" type=kernel start=demand "msgfile=C:\Program Files\Sandboxie\SbieMsg.dll" altitude=86900 | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\KmdUtil.exe | — | Sandboxie-Classic-x64-v5.69.8.exe | |||||||||||
User: admin Company: Sandboxie-Plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.69.8 Modules
| |||||||||||||||
Total events
995
Read events
970
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2456) Sandboxie-Classic-x64-v5.69.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | DisplayName |
Value: Sandboxie 5.69.8 (64-bit) | |||
| (PID) Process: | (2456) Sandboxie-Classic-x64-v5.69.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Sandboxie\Start.exe | |||
| (PID) Process: | (2456) Sandboxie-Classic-x64-v5.69.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | DisplayVersion |
Value: 5.69.8 | |||
| (PID) Process: | (2456) Sandboxie-Classic-x64-v5.69.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | Publisher |
Value: Sandboxie-Plus.com | |||
| (PID) Process: | (2456) Sandboxie-Classic-x64-v5.69.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | UninstallString |
Value: "C:\WINDOWS\Installer\SandboxieInstall64.exe" /remove | |||
| (PID) Process: | (2456) Sandboxie-Classic-x64-v5.69.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sandboxie |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\WINDOWS\Installer\SandboxieInstall64.exe" /remove /S | |||
| (PID) Process: | (2456) Sandboxie-Classic-x64-v5.69.8.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\AutoplayHandlers\CancelAutoplay\CLSID |
| Operation: | write | Name: | 7E950284-E123-49F4-B32B-A806C090D747 |
Value: | |||
| (PID) Process: | (6248) KmdUtil.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\SbieDrv |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Program Files\Sandboxie\SbieMsg.dll | |||
| (PID) Process: | (6248) KmdUtil.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\SbieDrv |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
| (PID) Process: | (6248) KmdUtil.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\SbieDrv |
| Operation: | write | Name: | DependOnService |
Value: FltMgr | |||
Executable files
24
Suspicious files
13
Text files
133
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\ioSpecial.ini | ini | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\SbieDll.dll | executable | |
MD5:B3DB4CA56236259D3BCAC59CB28B2F60 | SHA256:643B5B445982A5245183FCAD19122792B77BFC67A92F6CD79C12B35A31525C75 | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\SbieMsg.dll | executable | |
MD5:2417644763C20B691D27D0365B2130F9 | SHA256:8BDDADFF1E79C8C43BF7B5BF44CF756CC8C4CB16844AE71587B533DC1E8FA97C | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Users\admin\AppData\Local\Temp\nseBBE8.tmp\KmdUtil.exe | executable | |
MD5:FEDA44302A440BC3FE2704DF2436CA90 | SHA256:CCC03D5104C040F90179A52A9DD690AB639AA8EF7838302C830EA7BA907029C2 | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Program Files\Sandboxie\SbieSvc.exe | executable | |
MD5:6FEB53F09367CF76F1E7078D303DC592 | SHA256:E3D83680294232C3F775F5406FB15E8D96D842EB31FE67C1A2CA14700EAFBC29 | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Program Files\Sandboxie\32\SbieDll.dll | executable | |
MD5:440CEA5DCA83301A8B446F41E56952AD | SHA256:26548FA79D45403E1B5E49065BE4FEBA4FE410F8BD3A2E78E357BBB7816A0536 | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Program Files\Sandboxie\SbieDll.dll | executable | |
MD5:B3DB4CA56236259D3BCAC59CB28B2F60 | SHA256:643B5B445982A5245183FCAD19122792B77BFC67A92F6CD79C12B35A31525C75 | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Program Files\Sandboxie\SbieSvc.exe.sig | binary | |
MD5:9BDE4430C4C952C22725AF6C23ADBBC9 | SHA256:6001CC886CC4A1DB1A8684328CADC134A0AC7F12A65F900125AE8EF90D19904D | |||
| 2456 | Sandboxie-Classic-x64-v5.69.8.exe | C:\Program Files\Sandboxie\32\SbieSvc.exe | executable | |
MD5:EB3367D9DF012F18B75FC9594C761363 | SHA256:13E203E5E4C752056B807932C802D4C67C73B9A990743E966003CF53709F07B5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
18
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4760 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1064 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4760 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1064 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4760 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1064 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4760 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |