| File name: | rodyzONTOP.exe |
| Full analysis: | https://app.any.run/tasks/5f241f68-50ff-4ea2-97d1-6c8671da3807 |
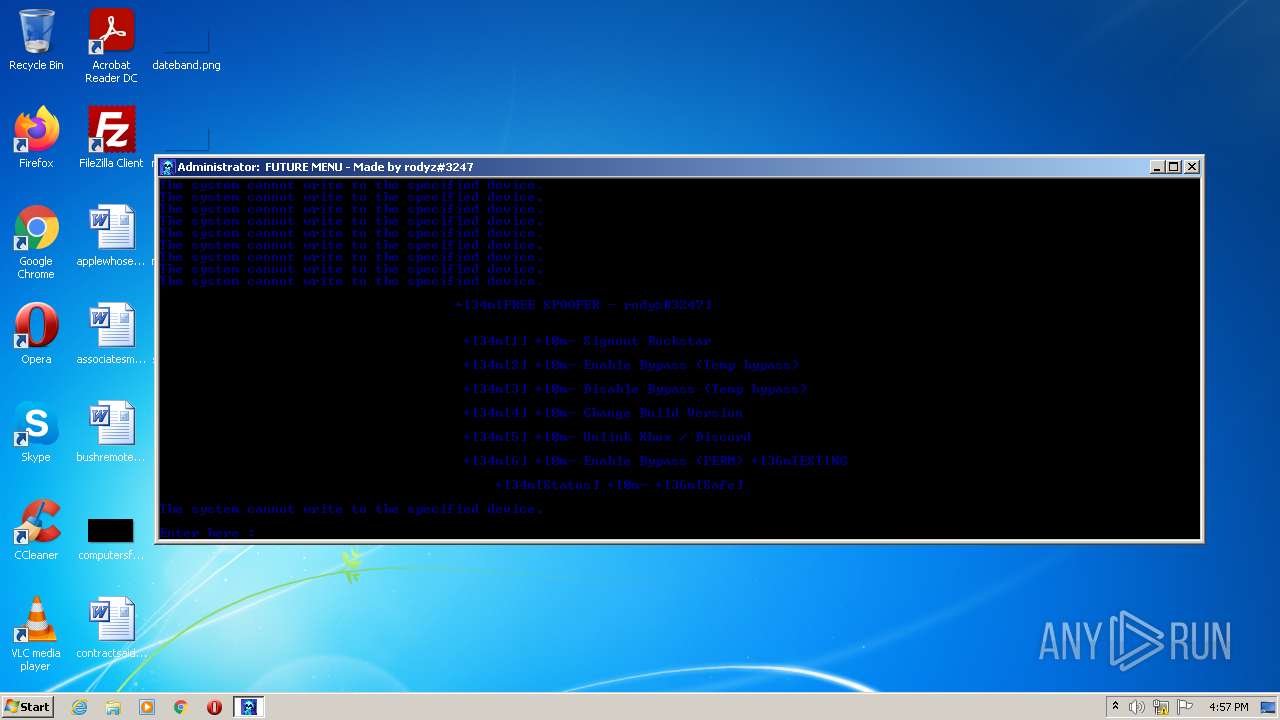
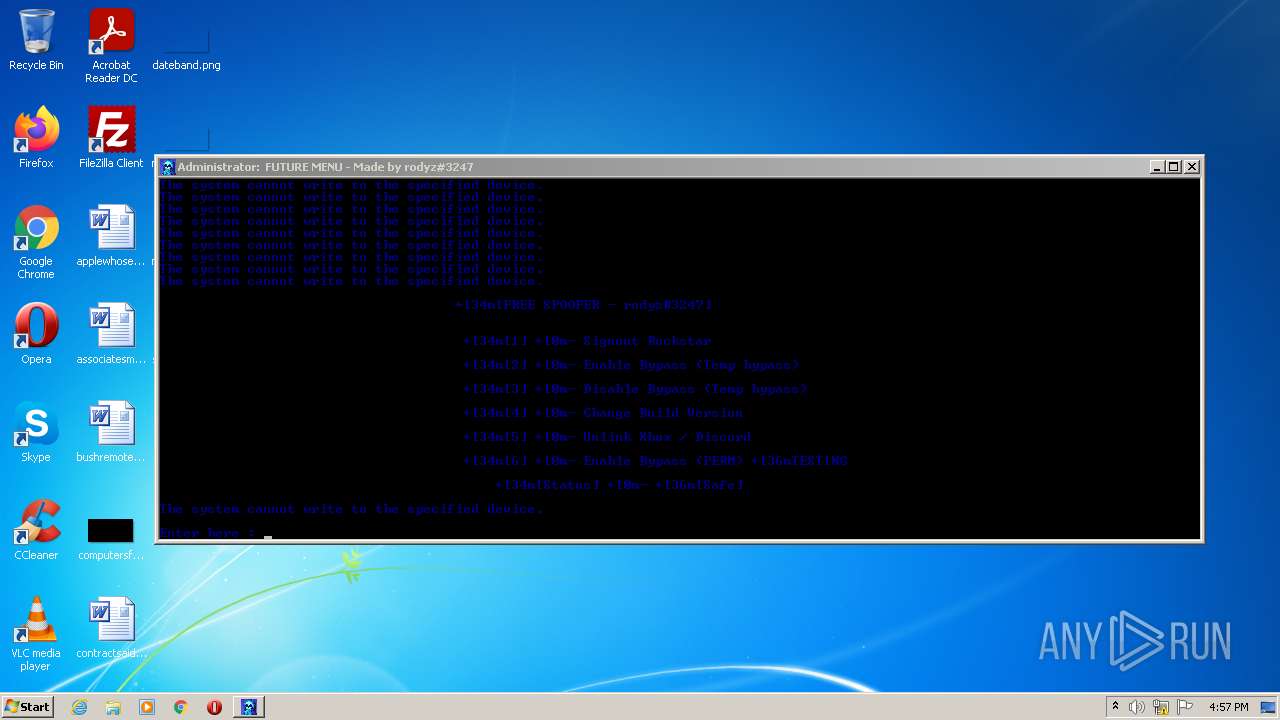
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 15:57:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | A1CC0EDE329305FC76EF2E4F31884A0F |
| SHA1: | 119F12982968C6FAC67A266A8B9150E9AEA61FEA |
| SHA256: | 22E7A458A21B898444C56D99286226A91A69BC8BB59284EFBD5EC30E8C73823D |
| SSDEEP: | 1536:I7fbN3eEDhDPA/pICdUkbBtW7upvaLU0bI5taxKo0IOlnToIf6wPVg6VO2EQQhaW:G7DhdC6kzWypvaQ0FxyNTBf6Uh027W |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 1216)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1216)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3864)
SUSPICIOUS
Starts CMD.EXE for commands execution
- rodyzONTOP.exe (PID: 3692)
Checks supported languages
- rodyzONTOP.exe (PID: 3692)
- cmd.exe (PID: 1216)
- chcp.com (PID: 1328)
- mode.com (PID: 1820)
- mode.com (PID: 2952)
- chcp.com (PID: 3624)
- mode.com (PID: 1660)
- chcp.com (PID: 3596)
- powershell.exe (PID: 3424)
Starts application with an unusual extension
- cmd.exe (PID: 1216)
Modifies files in Chrome extension folder
- chrome.exe (PID: 368)
Reads the computer name
- powershell.exe (PID: 3424)
Starts SC.EXE for service management
- cmd.exe (PID: 1216)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1216)
INFO
Manual execution by user
- chrome.exe (PID: 368)
Checks supported languages
- chrome.exe (PID: 368)
- chrome.exe (PID: 1764)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 1404)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 1844)
- timeout.exe (PID: 2784)
- timeout.exe (PID: 1560)
- sc.exe (PID: 2900)
- sc.exe (PID: 1248)
- sc.exe (PID: 2420)
- sc.exe (PID: 3476)
- sc.exe (PID: 2312)
- sc.exe (PID: 844)
- sc.exe (PID: 2644)
- sc.exe (PID: 1984)
- schtasks.exe (PID: 3864)
- reg.exe (PID: 2708)
- schtasks.exe (PID: 3060)
- reg.exe (PID: 3660)
Reads the computer name
- chrome.exe (PID: 368)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 3908)
- sc.exe (PID: 2900)
- sc.exe (PID: 1248)
- sc.exe (PID: 2312)
- sc.exe (PID: 2644)
- sc.exe (PID: 3476)
- sc.exe (PID: 844)
- sc.exe (PID: 2420)
- sc.exe (PID: 1984)
- schtasks.exe (PID: 3864)
Application launched itself
- chrome.exe (PID: 368)
Reads the hosts file
- chrome.exe (PID: 368)
- chrome.exe (PID: 3504)
Checks Windows Trust Settings
- powershell.exe (PID: 3424)
Reads settings of System Certificates
- powershell.exe (PID: 3424)
- chrome.exe (PID: 3504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
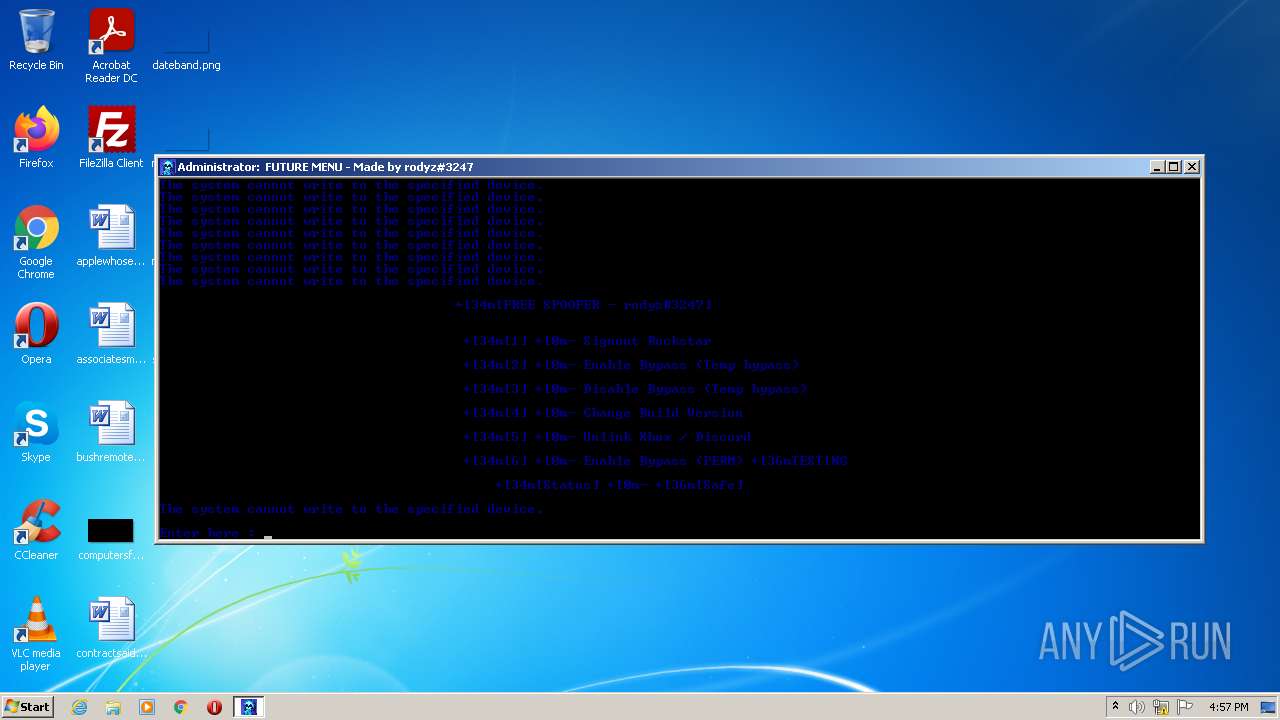
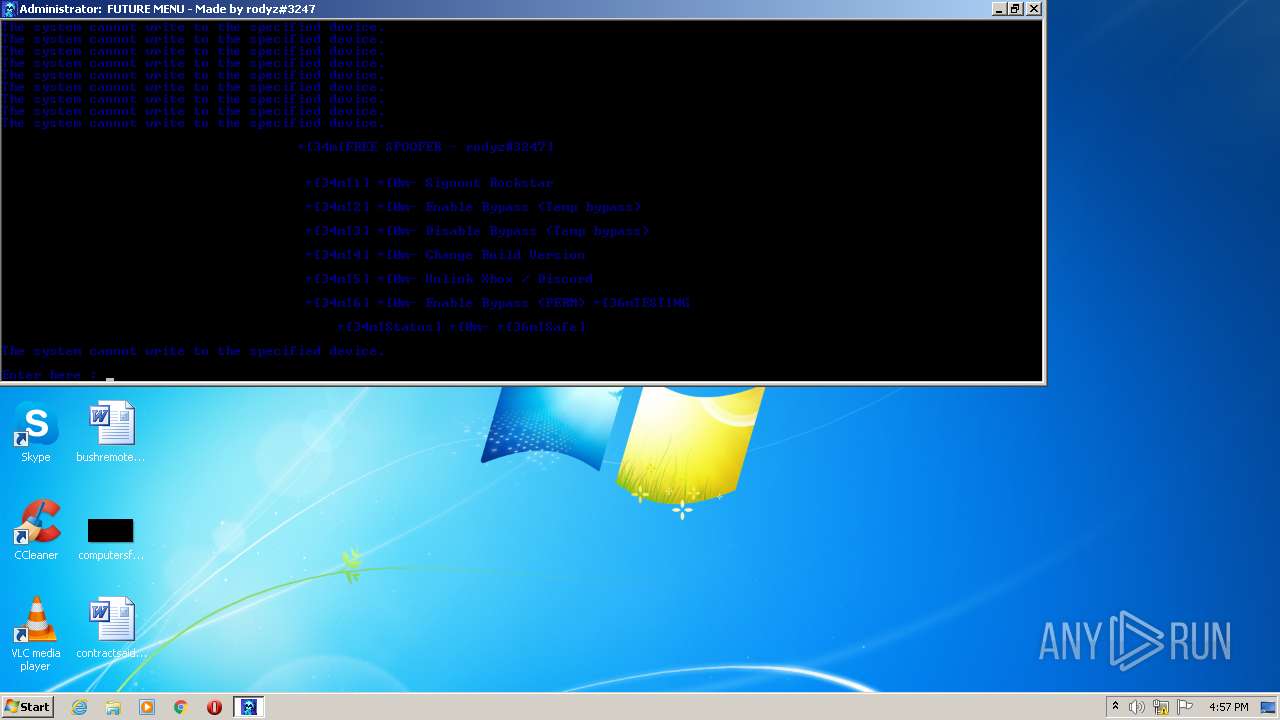
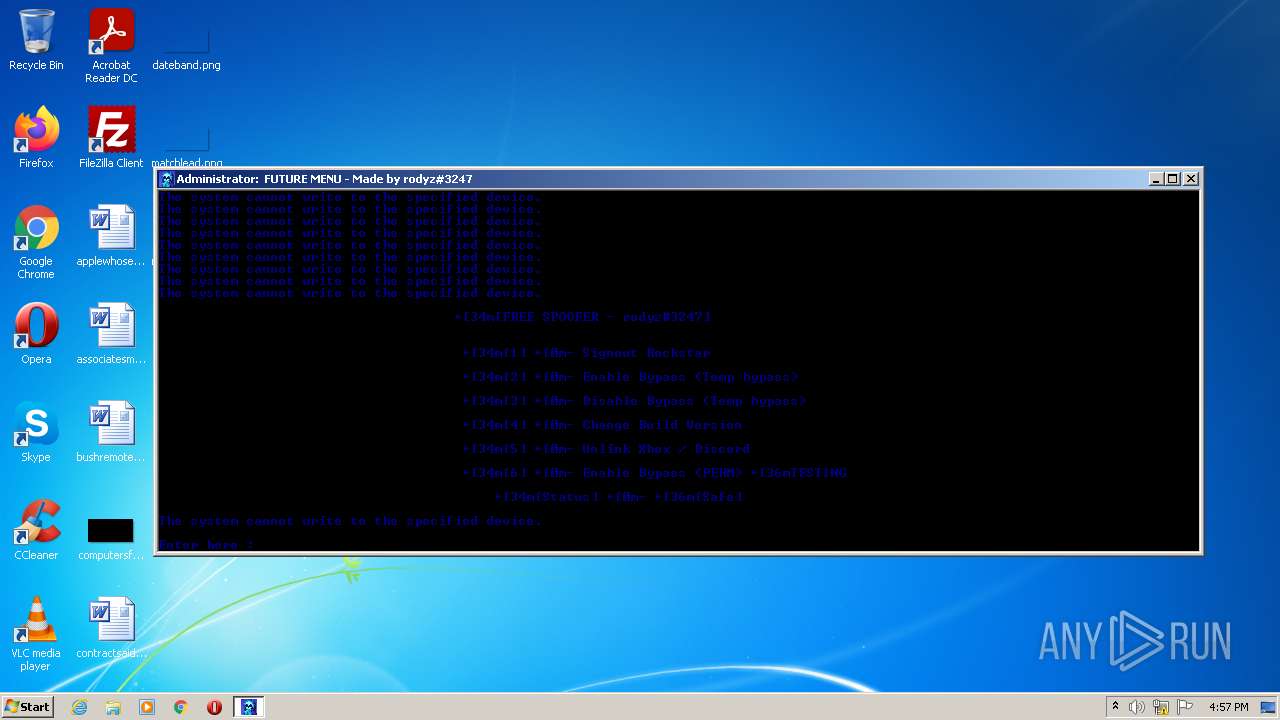
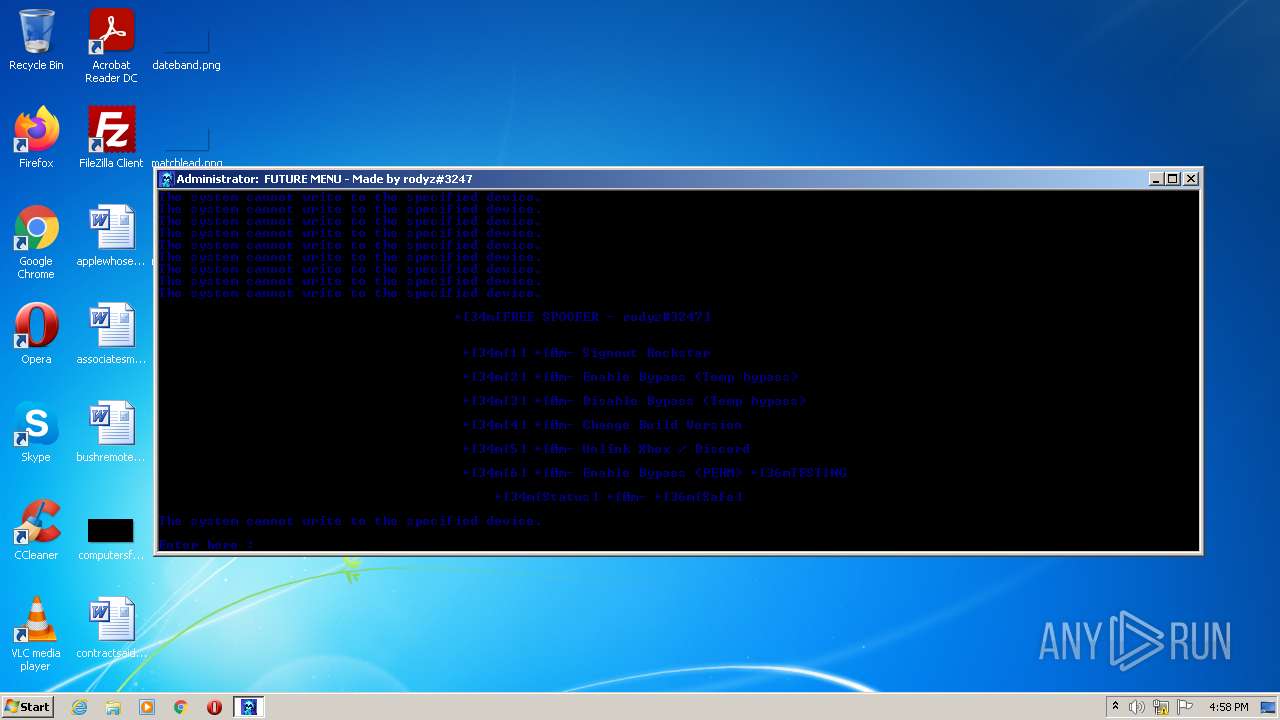
| Comments: | FREE SPOOFER |
|---|---|
| SpecialBuild: | FREE SPOOFER |
| PrivateBuild: | FREE SPOOFER |
| LegalCopyright: | FREE SPOOFER |
| LegalTrademarks: | FREE SPOOFER |
| CompanyName: | FREE SPOOFER |
| FileDescription: | FREE SPOOFER |
| InternalName: | FREE SPOOFER |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows 16-bit |
| FileFlags: | Debug, Pre-release, Private build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 48640 |
| CodeSize: | 70656 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2019:07:30 10:52:45+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 30-Jul-2019 08:52:45 |
| Detected languages: |
|
| InternalName: | FREE SPOOFER |
| FileDescription: | FREE SPOOFER |
| CompanyName: | FREE SPOOFER |
| LegalTrademarks: | FREE SPOOFER |
| LegalCopyright: | FREE SPOOFER |
| PrivateBuild: | FREE SPOOFER |
| SpecialBuild: | FREE SPOOFER |
| Comments: | FREE SPOOFER |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jul-2019 08:52:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0000387E | 0x00003A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.52922 |
.text | 0x00005000 | 0x0000D962 | 0x0000DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56249 |
.rdata | 0x00013000 | 0x000033A5 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11184 |
.data | 0x00017000 | 0x0000178C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.09949 |
.rsrc | 0x00019000 | 0x00007780 | 0x00007800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.58093 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
76E51AE63A | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
8D2D7E3643B5350C0769D6923A52D4ED6E6B0CB4 | 3 | 8 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D57599A6A6F2F1D73D790632CDDF1D91 | 3.23593 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
EE571821D827BA1540EC753A78241174 | 7.99022 | 18762 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
71
Monitored processes
34
Malicious processes
2
Suspicious processes
1
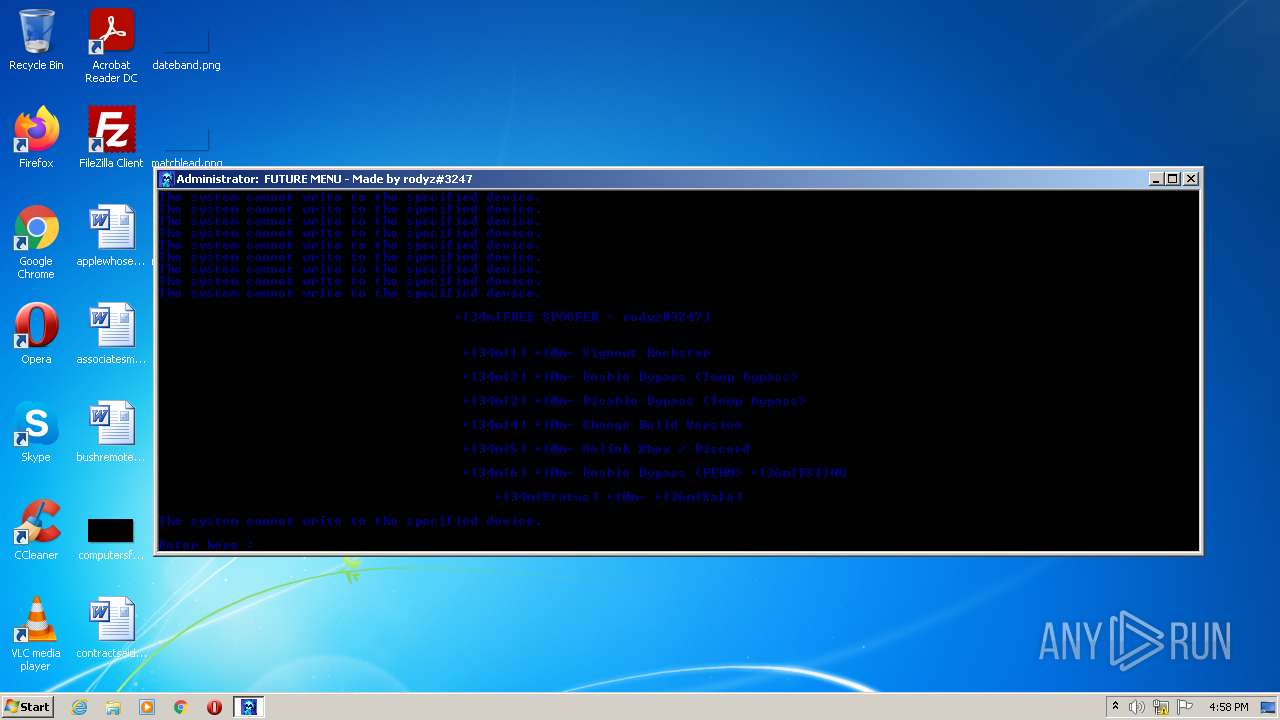
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Users\admin\AppData\Local\Temp\rodyzONTOP.exe" | C:\Users\admin\AppData\Local\Temp\rodyzONTOP.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 844 | sc delete XblGameSave | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\8FBF.tmp\8FCF.tmp\8FD0.bat C:\Users\admin\AppData\Local\Temp\rodyzONTOP.exe" | C:\Windows\system32\cmd.exe | — | rodyzONTOP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1248 | sc stop XblGameSave | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1328 | chcp 65001 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,1762355602506710975,18265324958356961420,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1560 | timeout 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1660 | mode 130,30 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f2fd988,0x6f2fd998,0x6f2fd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 340
Read events
13 284
Write events
56
Delete events
0
Modification events
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
22
Text files
43
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6287BA7B-170.pma | — | |
MD5:— | SHA256:— | |||
| 3692 | rodyzONTOP.exe | C:\Users\admin\AppData\Local\Temp\8FBF.tmp\8FCF.tmp\8FD0.bat | text | |
MD5:— | SHA256:— | |||
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10bce9.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d40df233-000b-404b-8fdd-e617bcb79bff.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1764 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
14
DNS requests
9
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
3504 | chrome.exe | 142.250.184.196:443 | www.google.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 216.58.206.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 142.250.186.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 142.250.74.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 142.250.181.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |