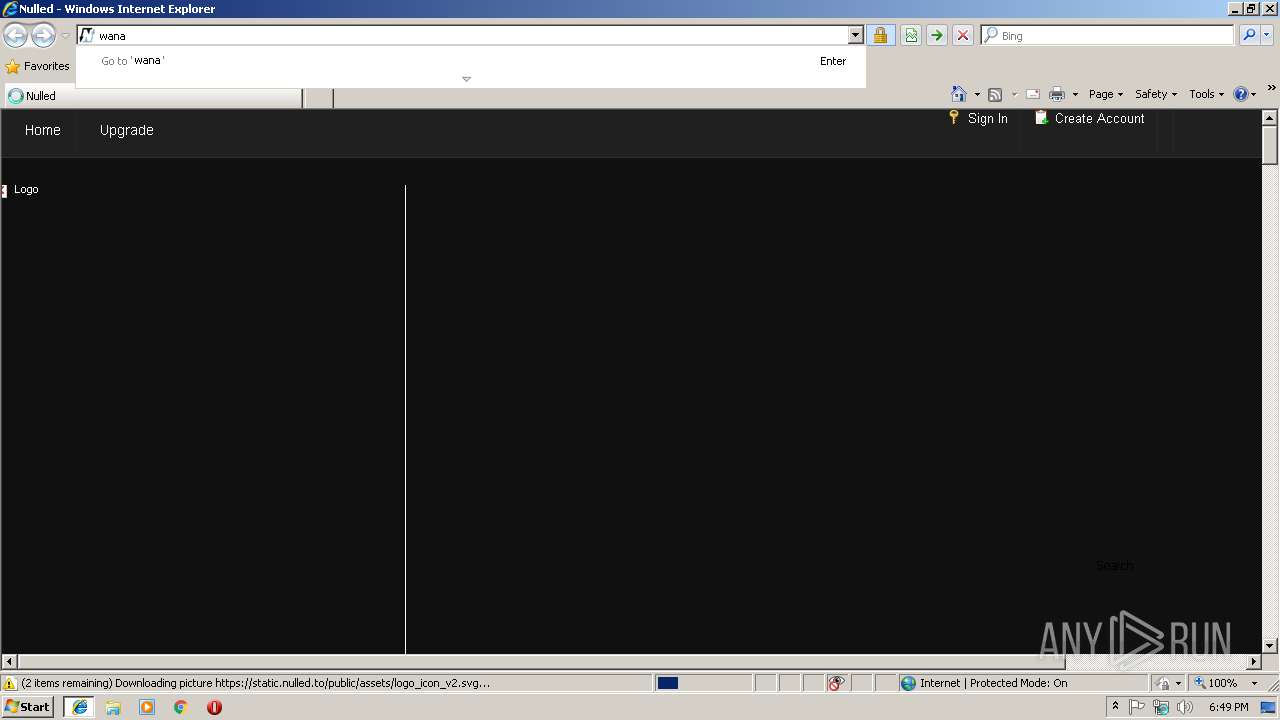
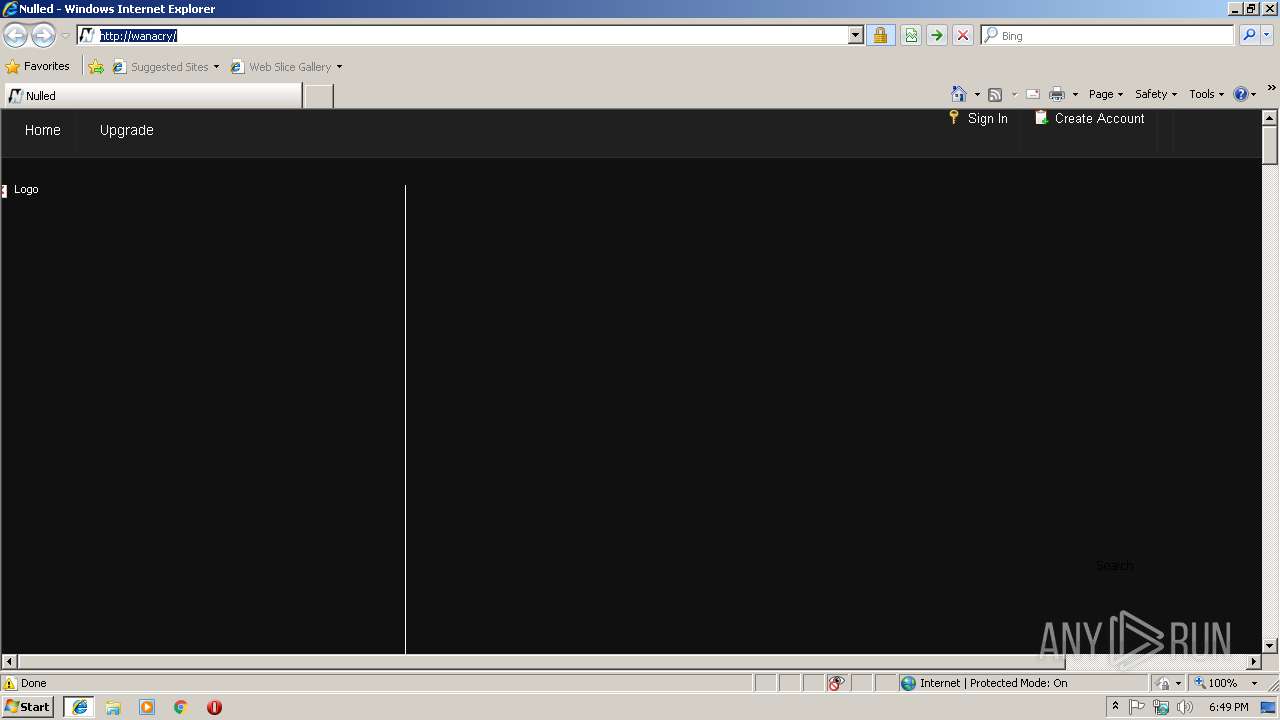
| URL: | https://www.nulled.to/ |
| Full analysis: | https://app.any.run/tasks/5a6fa042-d939-4c6b-87c0-49c910d4729d |
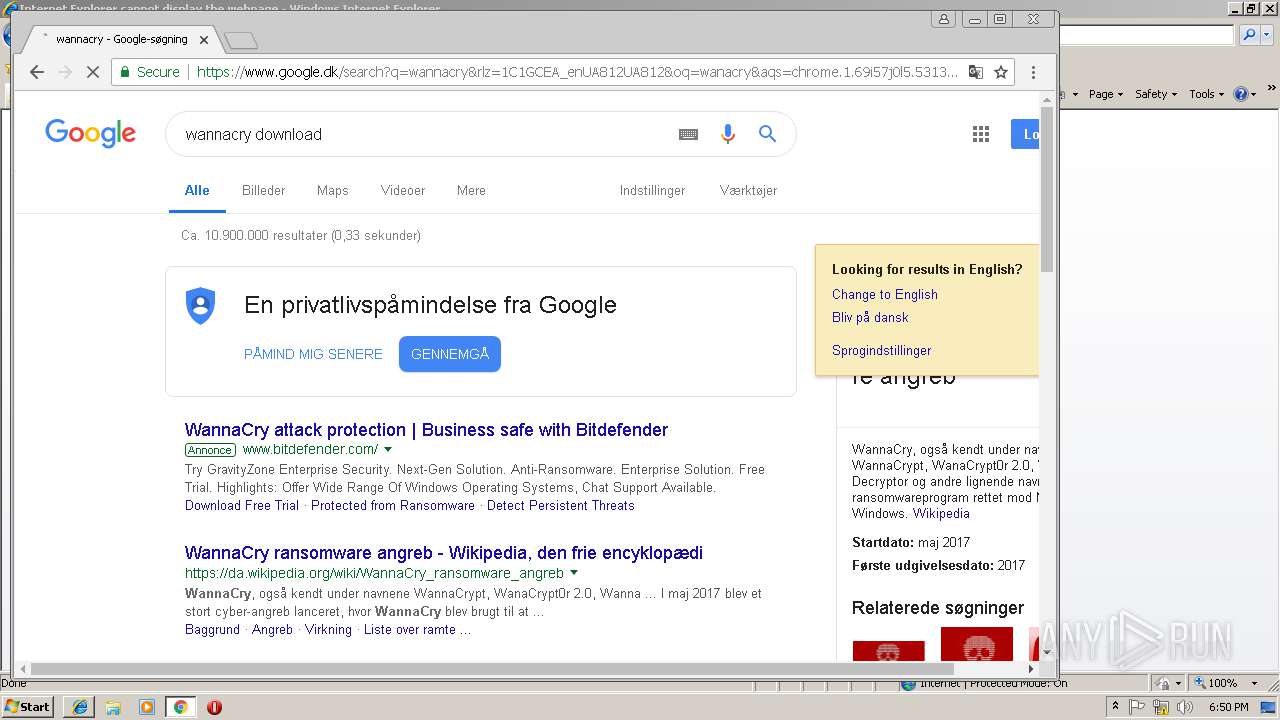
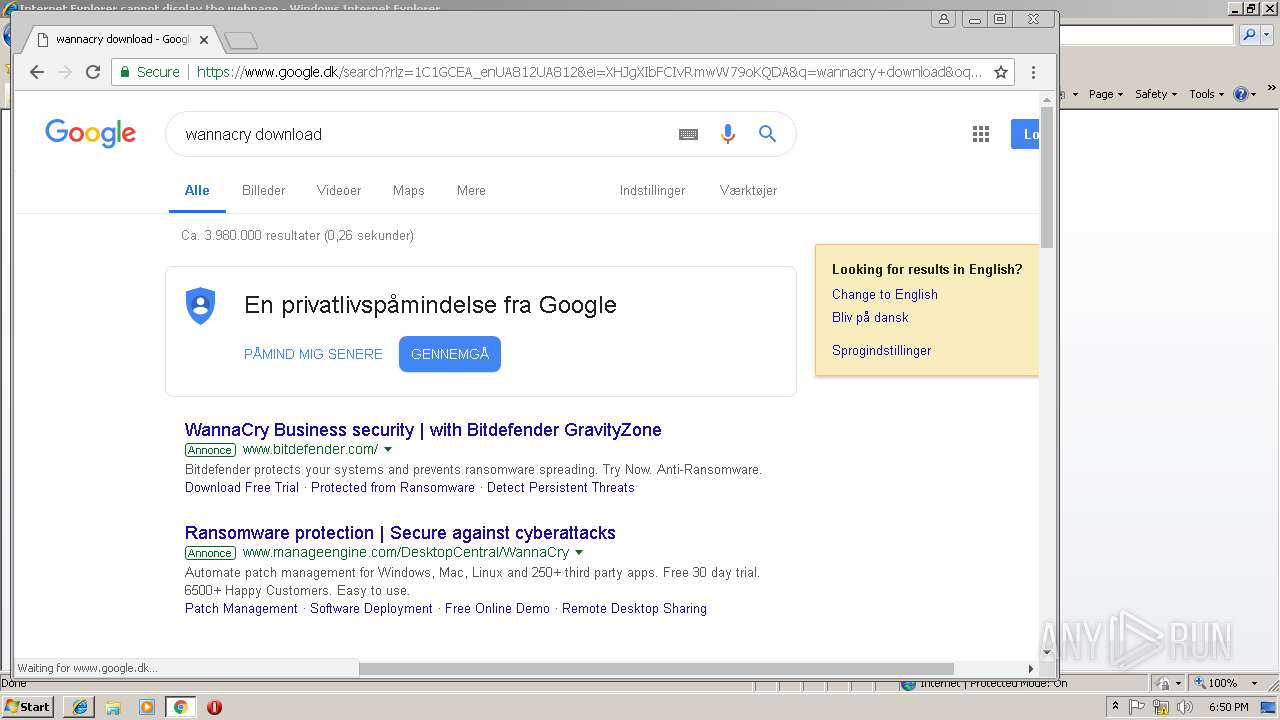
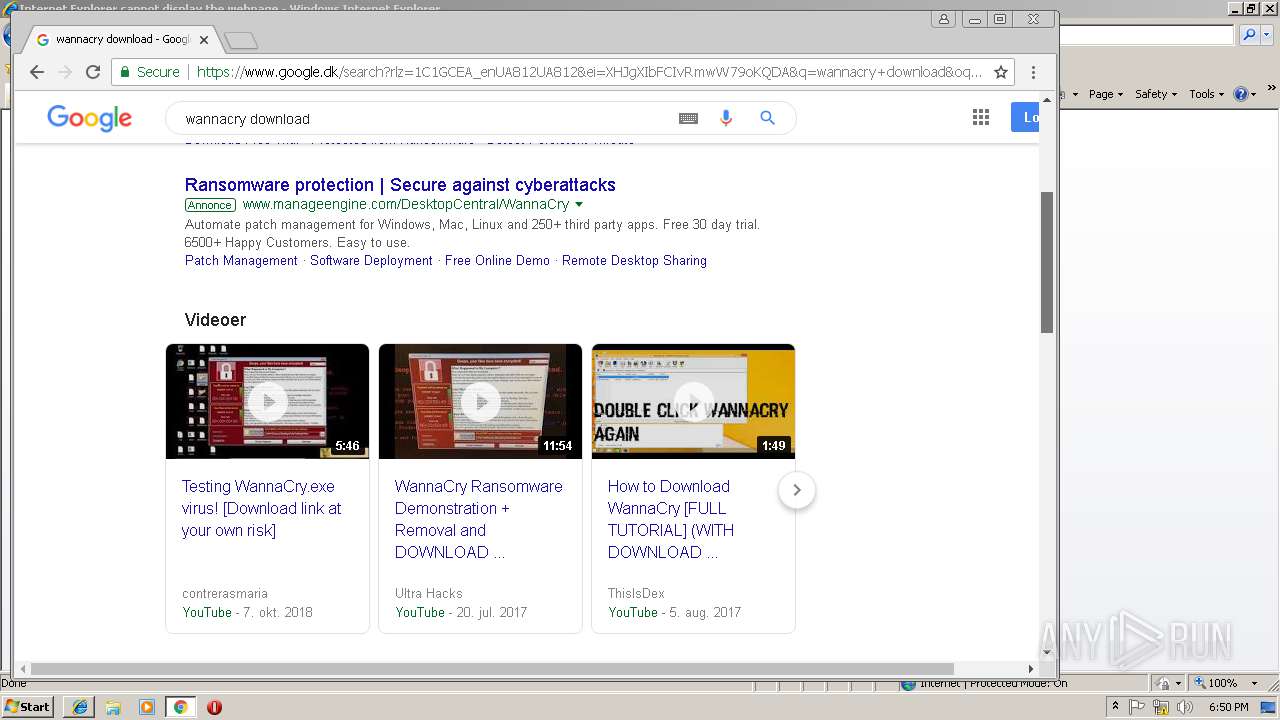
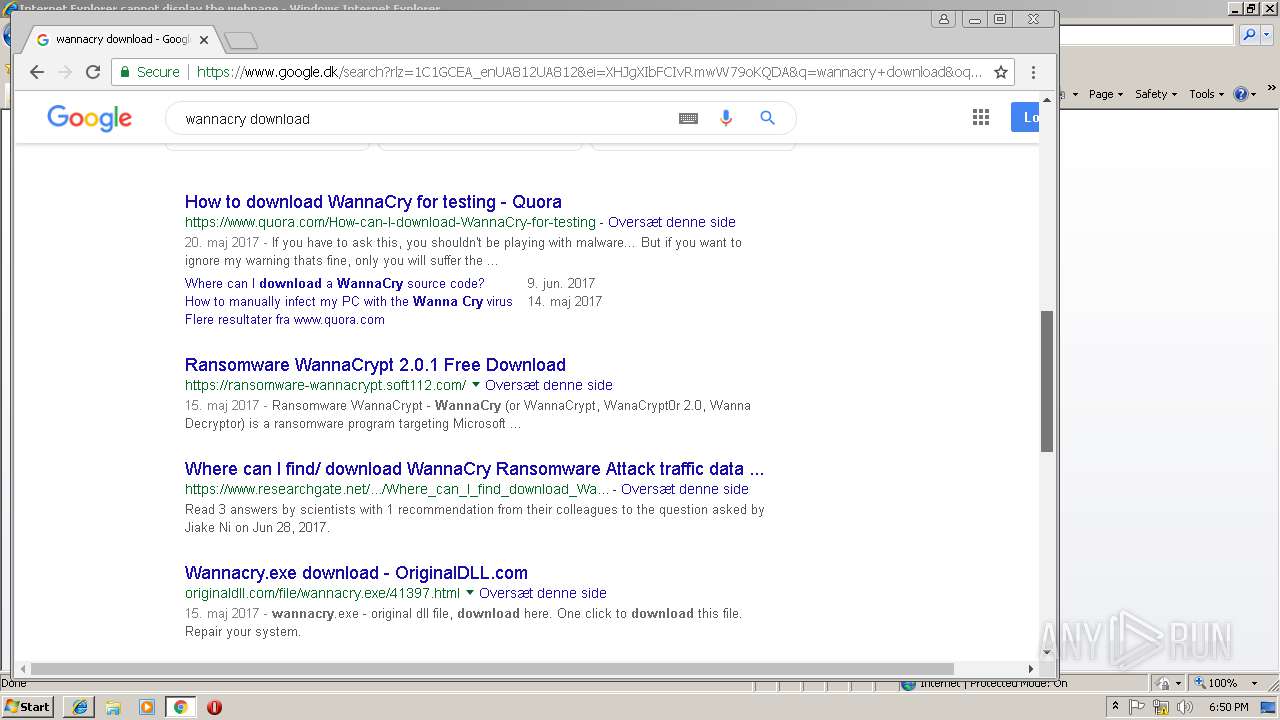
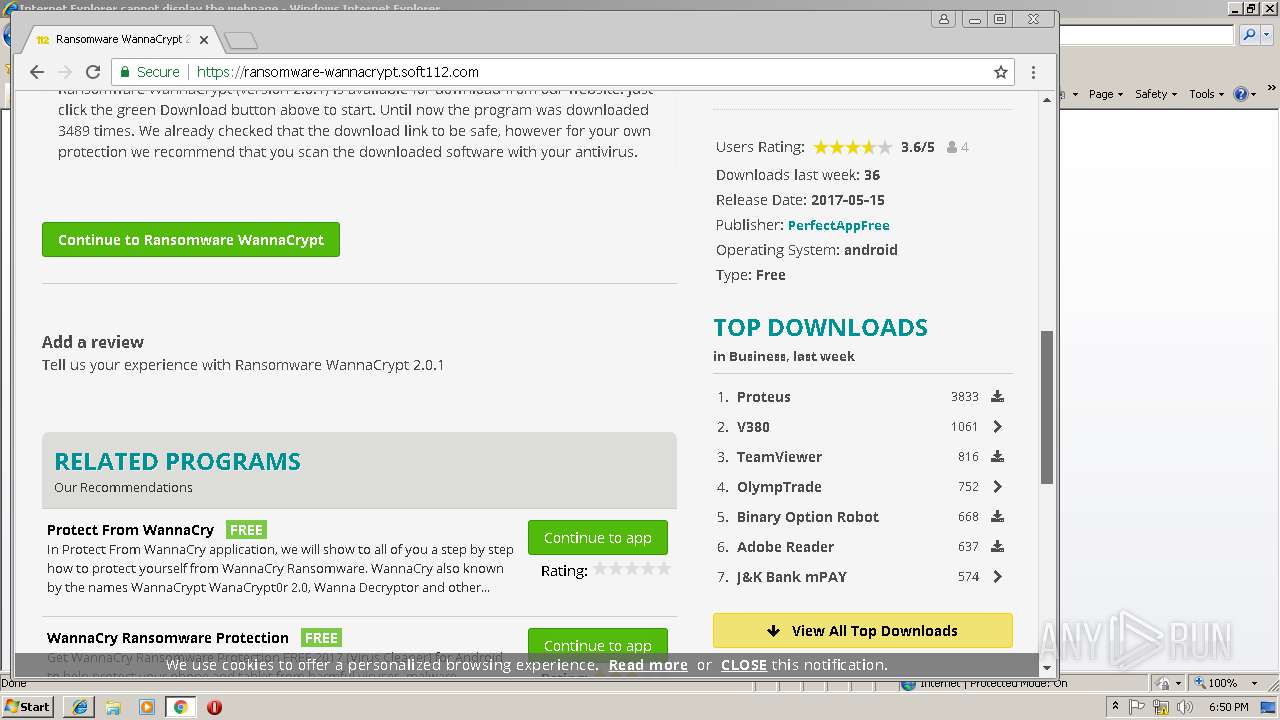
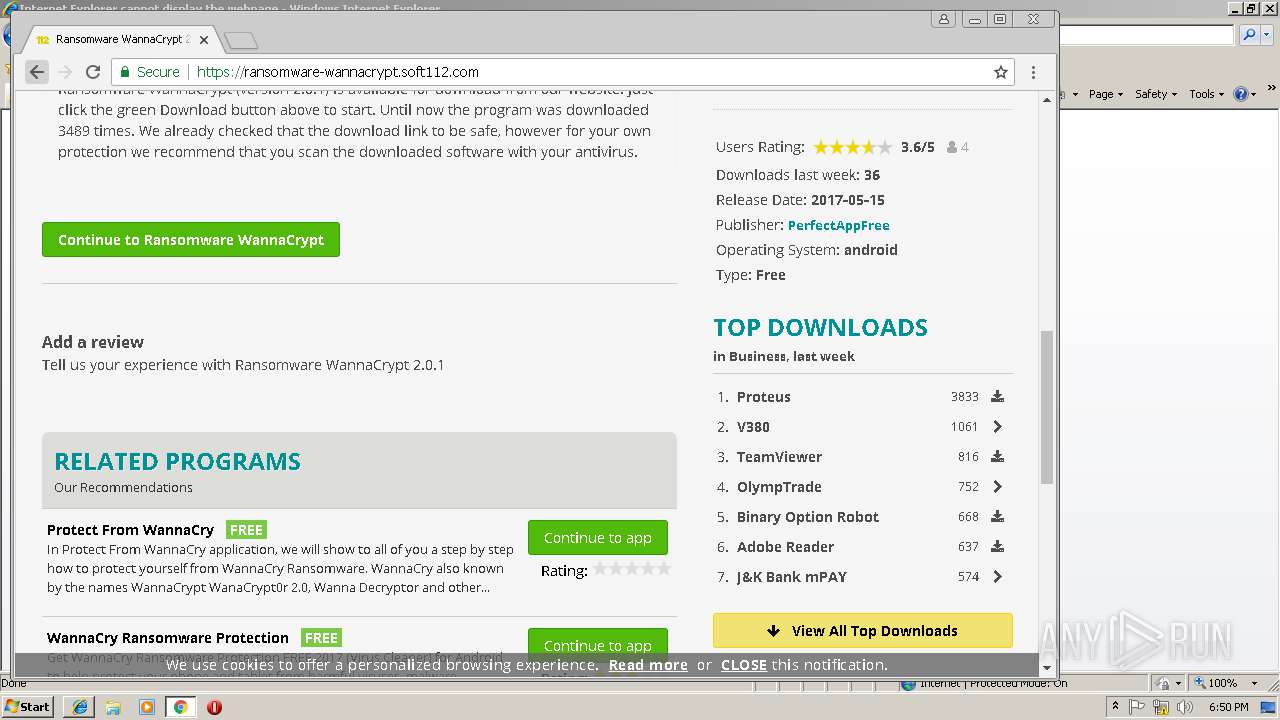
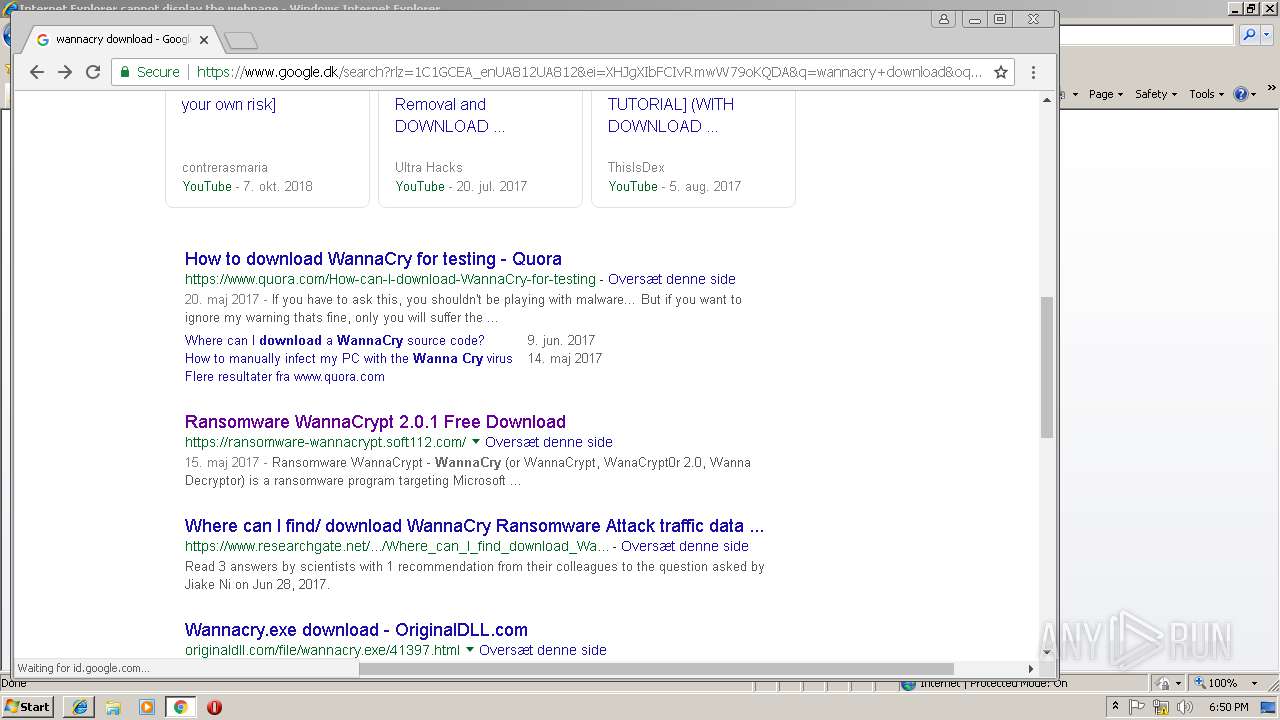
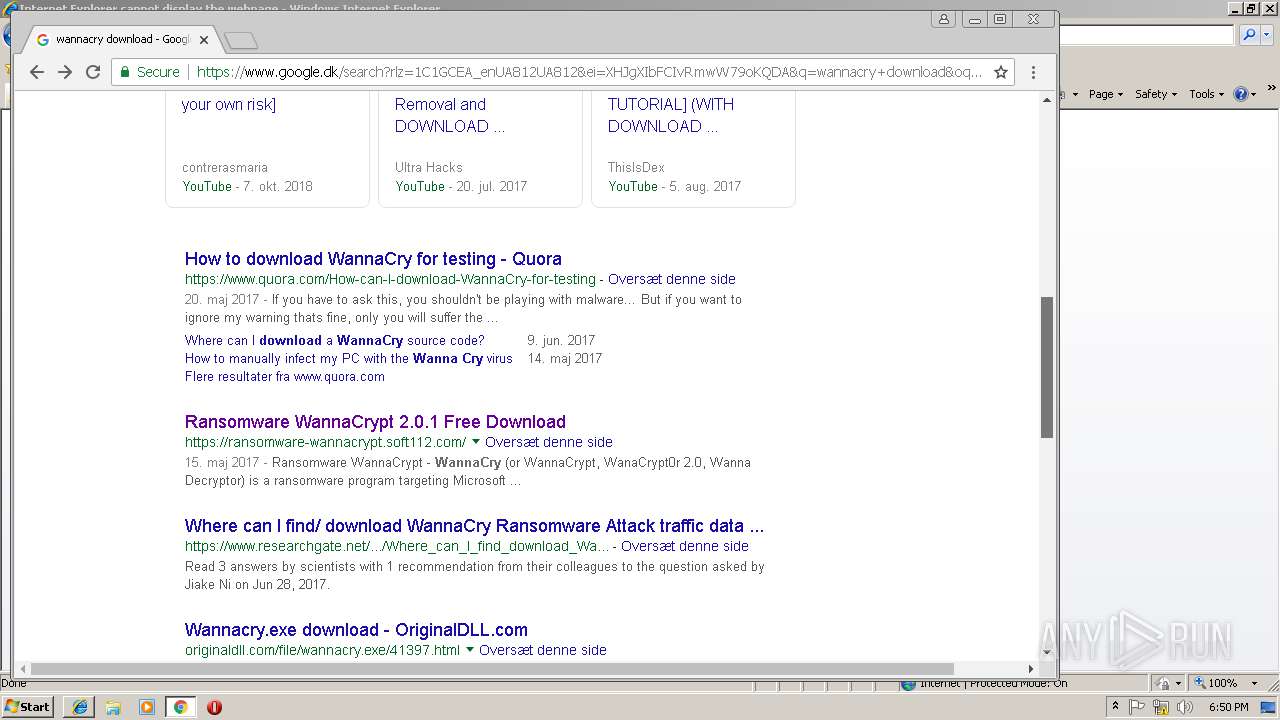
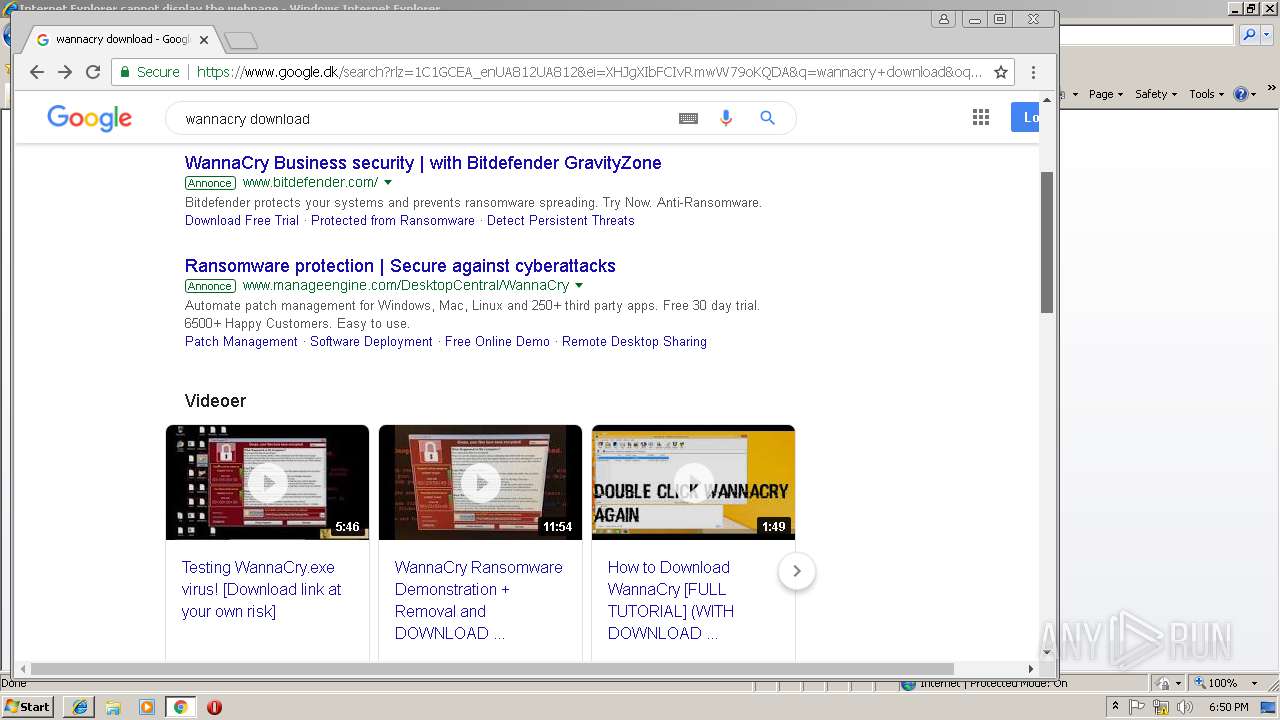
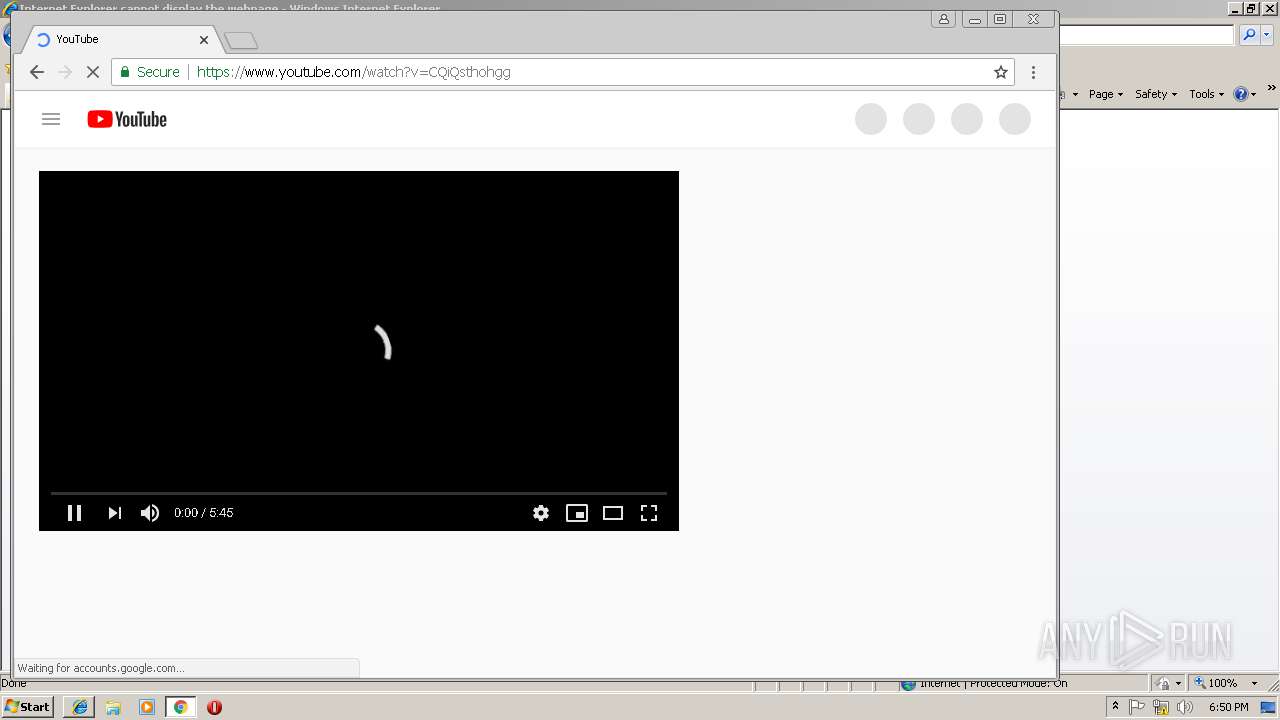
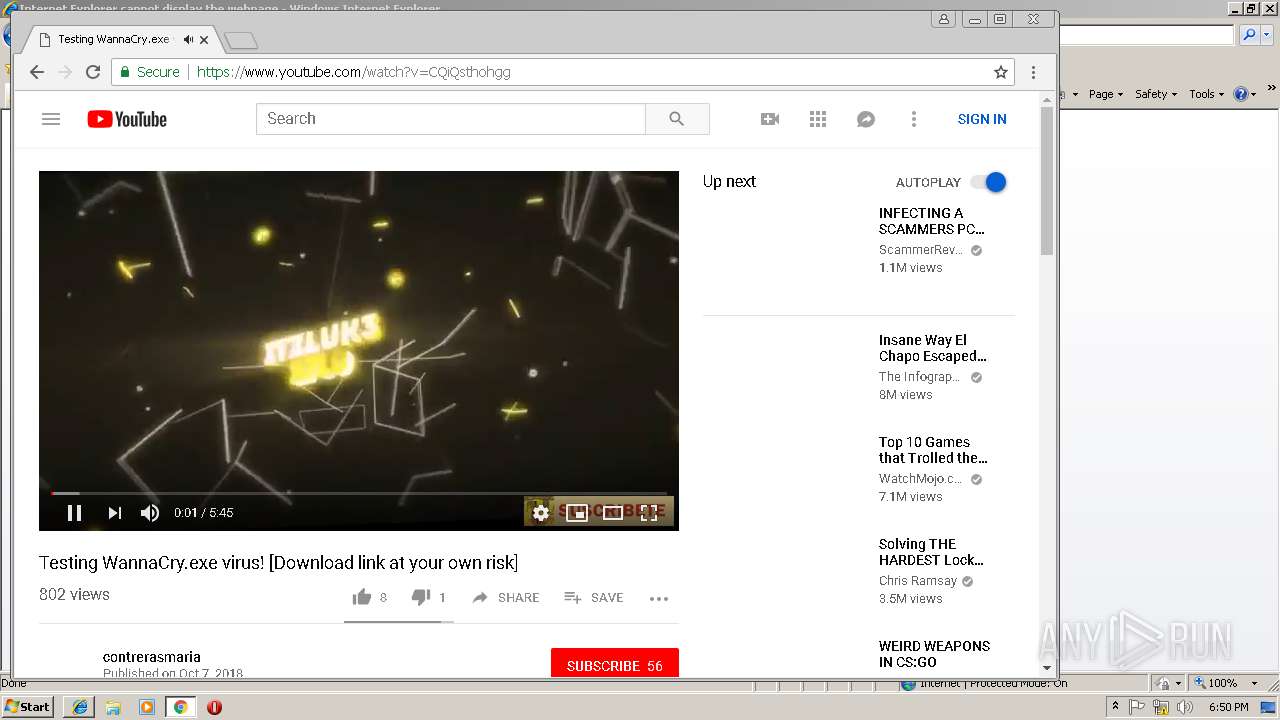
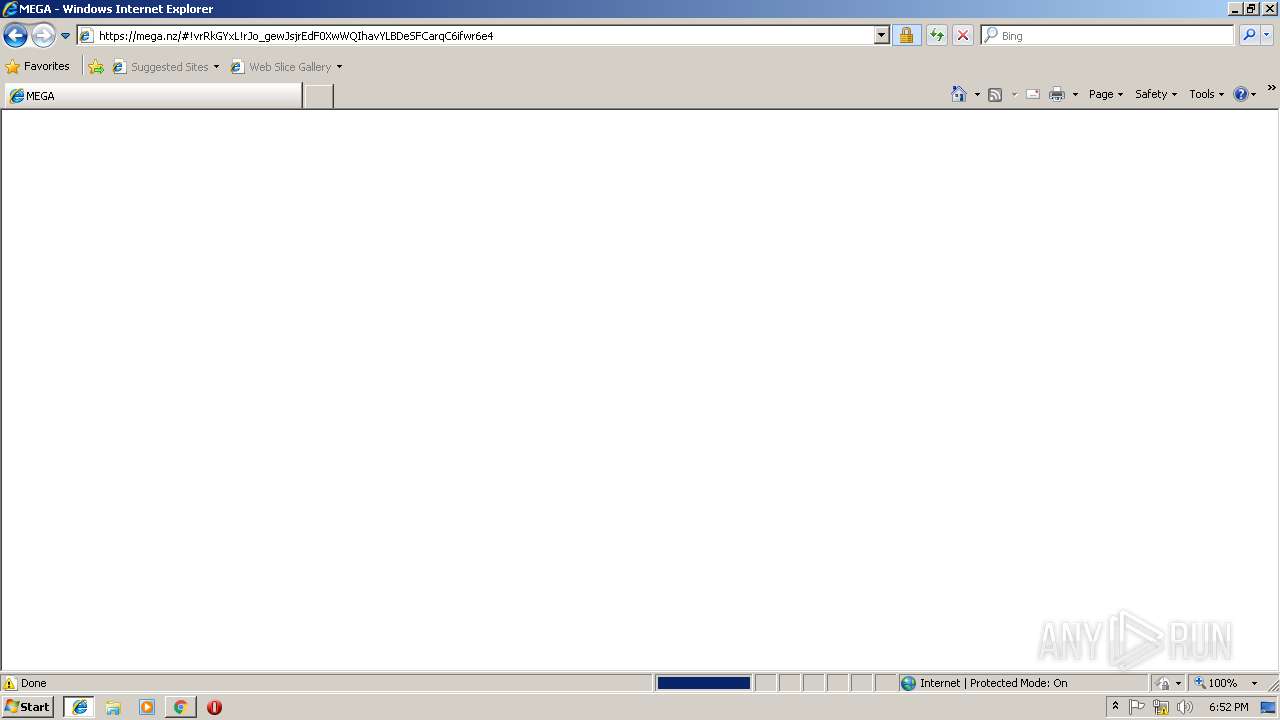
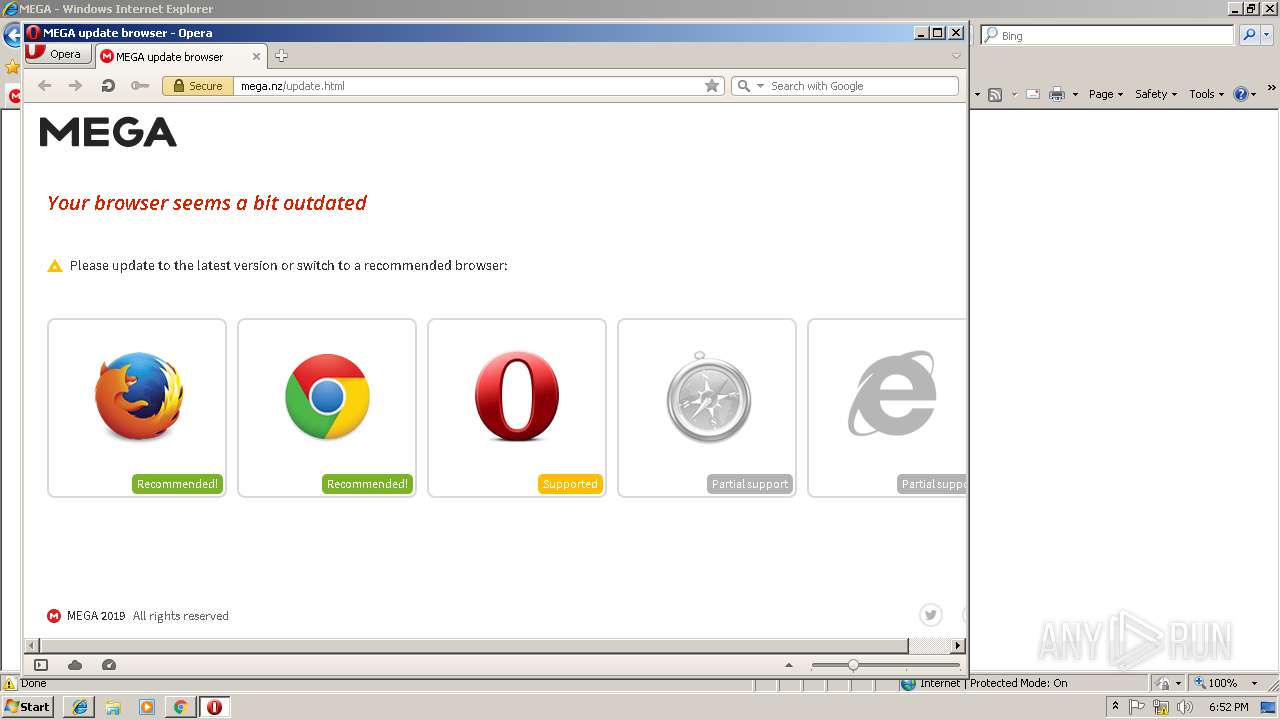
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2019, 18:48:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 35E0473B953C6B0332909D73C8AC35A6 |
| SHA1: | 09CF1B76FDC58B28F910800A403B3296C589674A |
| SHA256: | 22DE79E3661B55098C24CBB31A2A664702283C58BA463176EB62F30A7805F432 |
| SSDEEP: | 3:N8DSLkElRn:2OLkElRn |
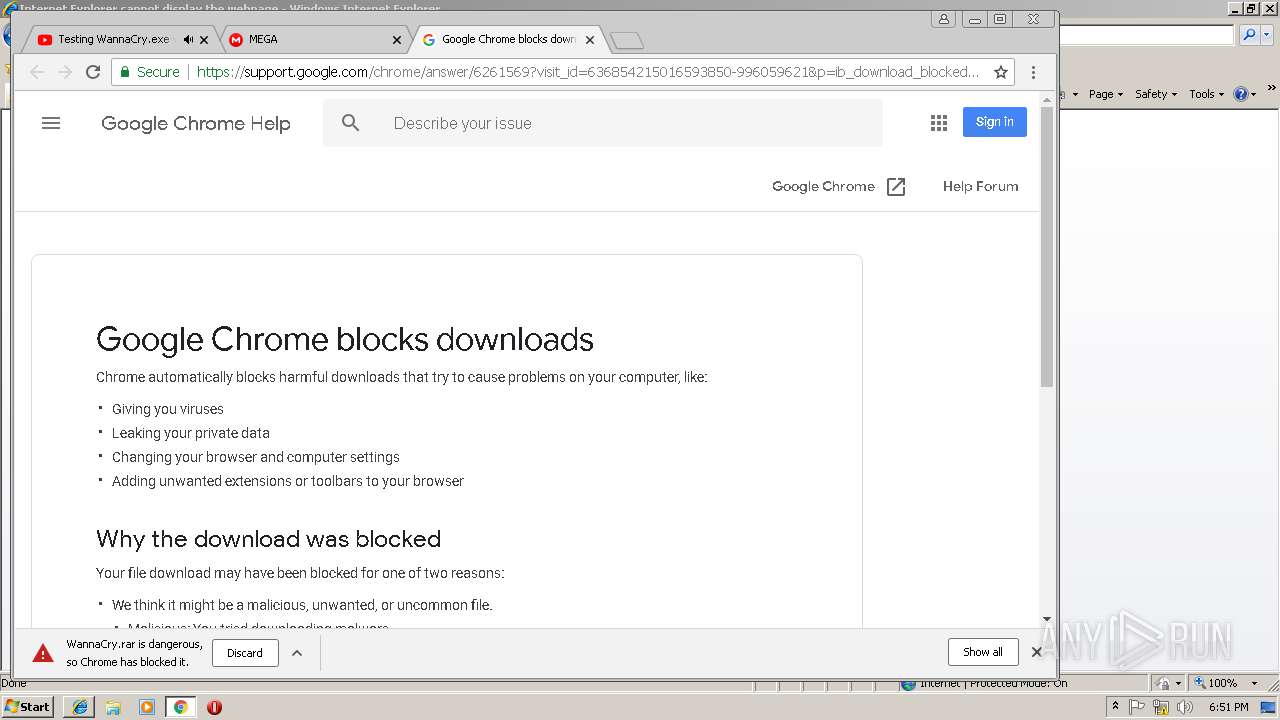
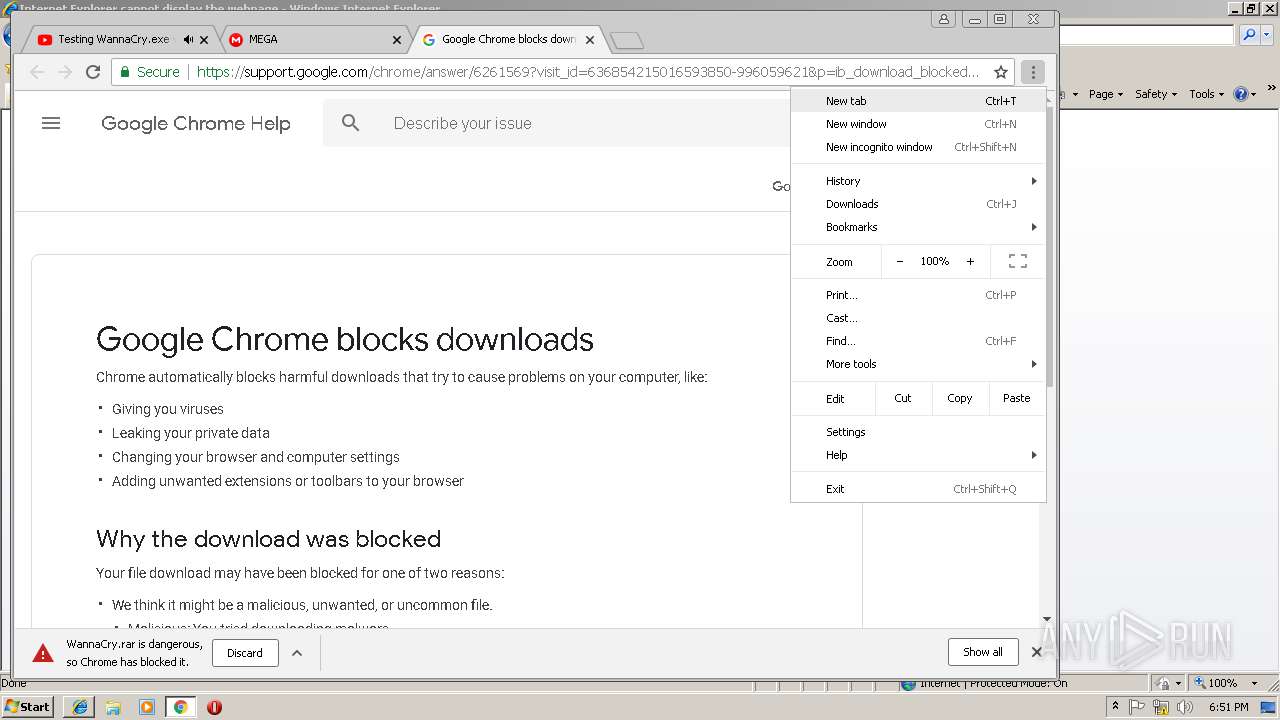
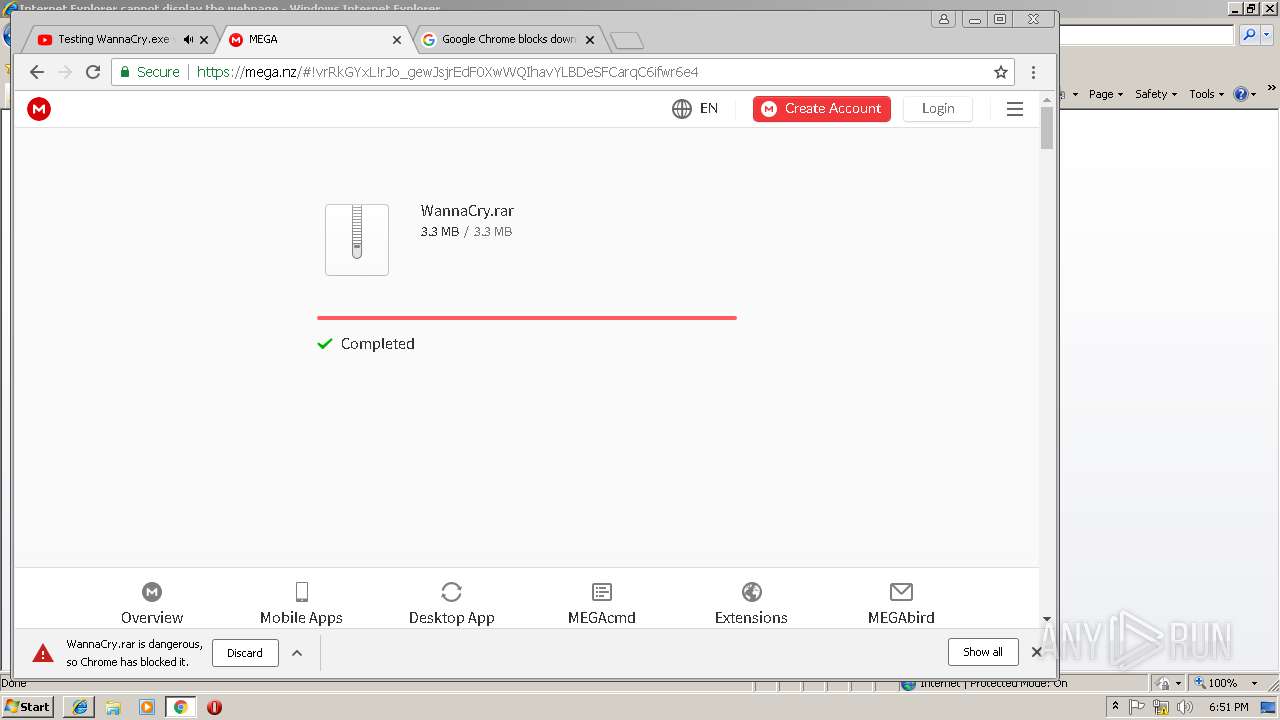
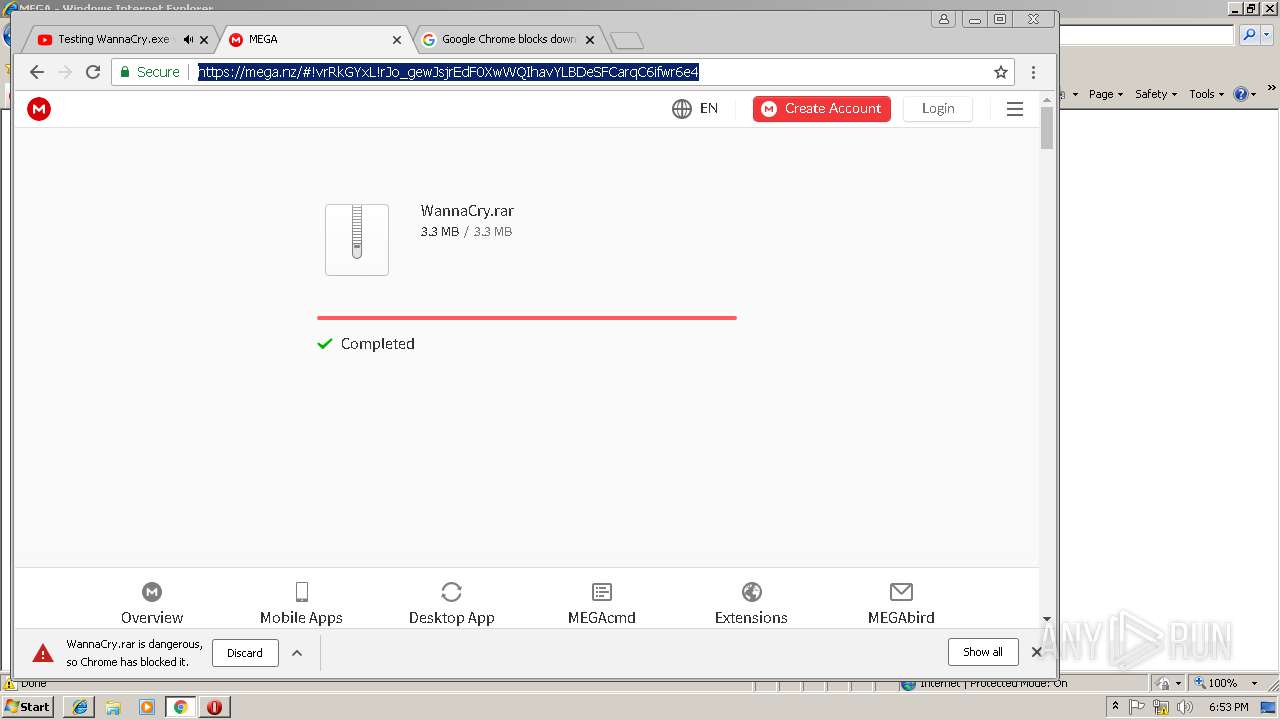
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
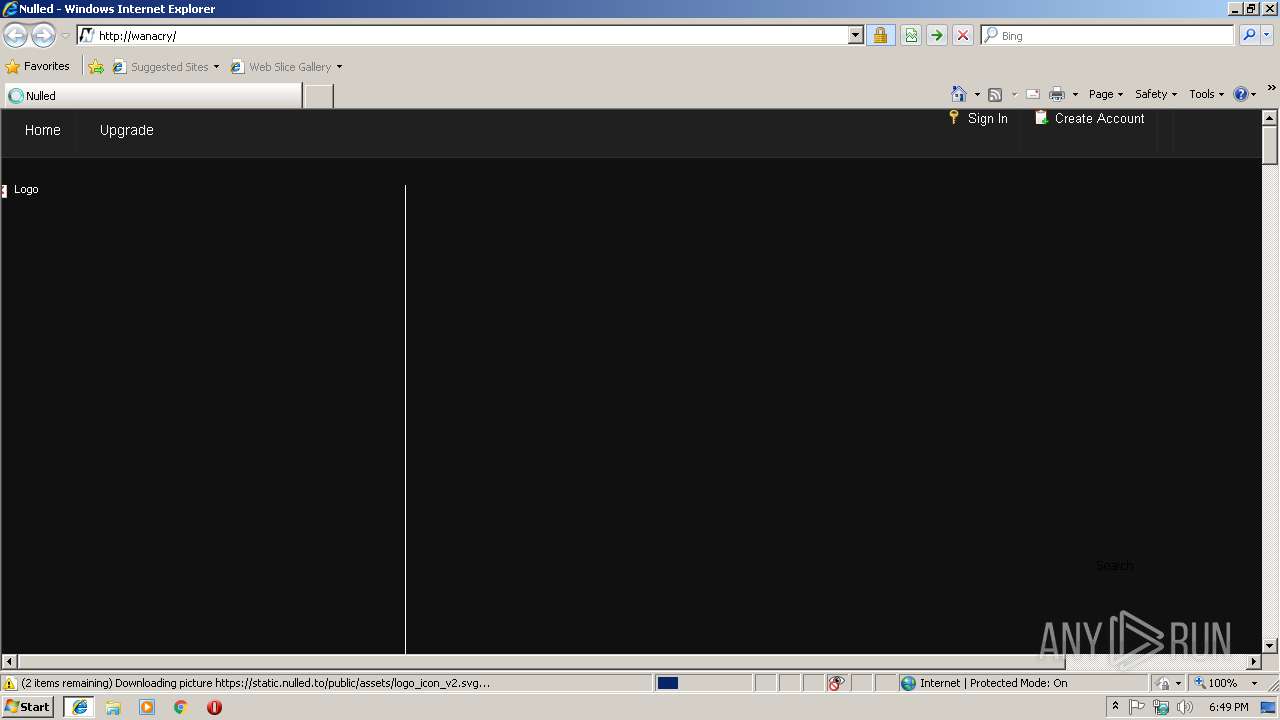
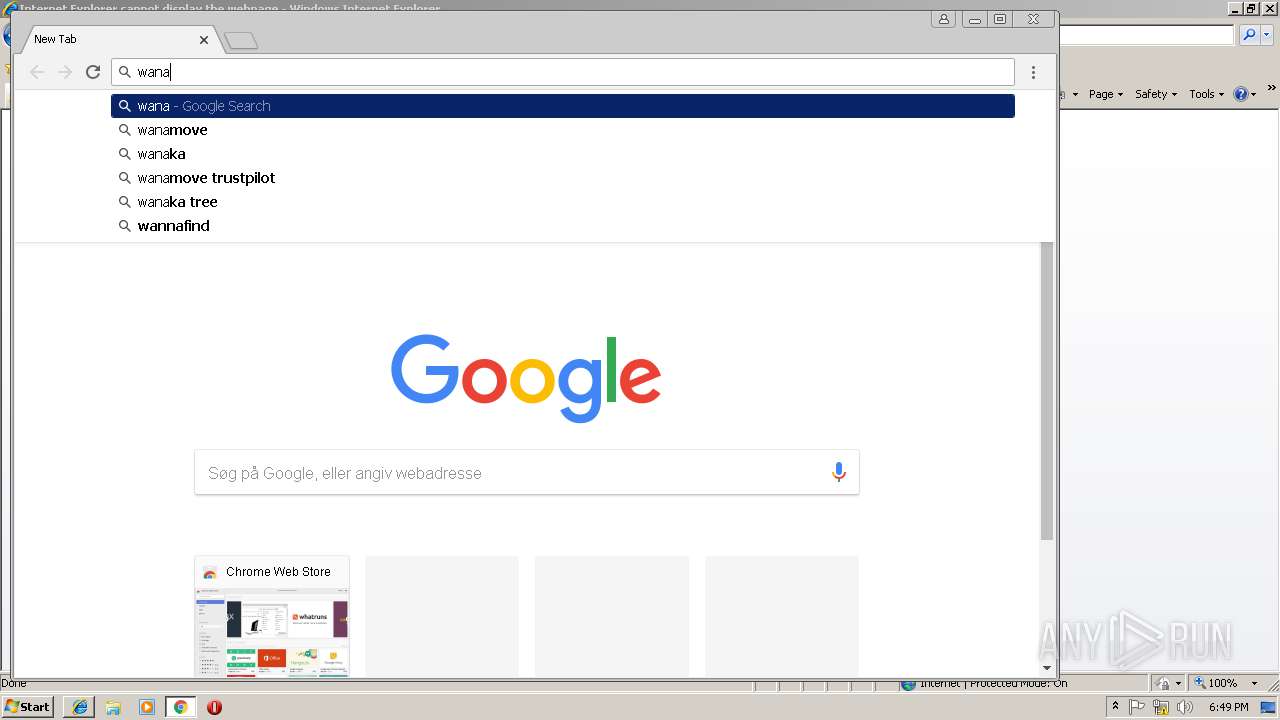
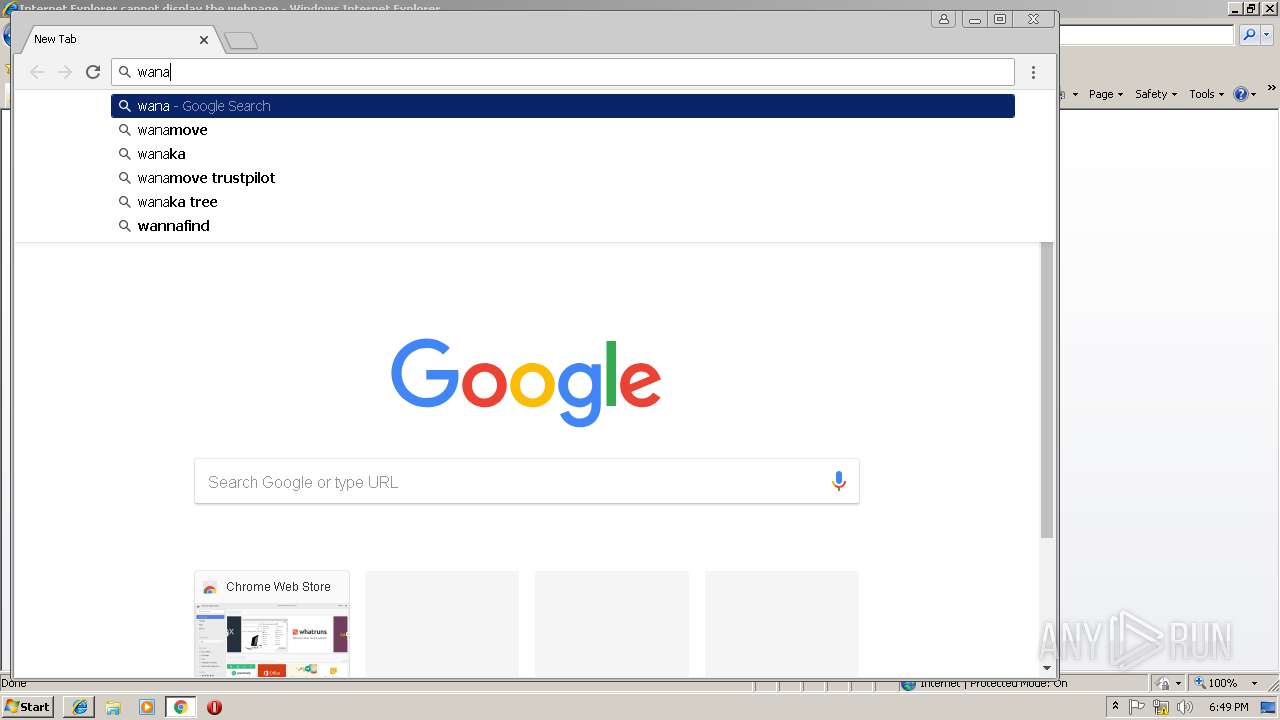
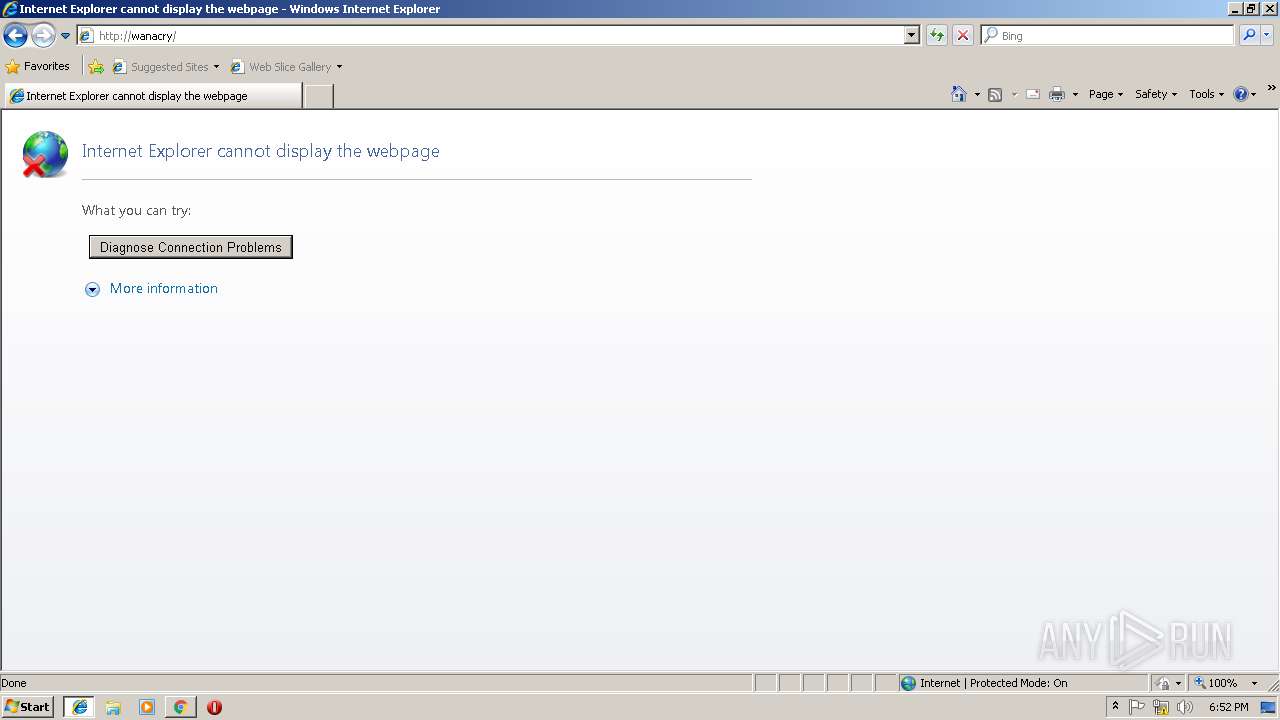
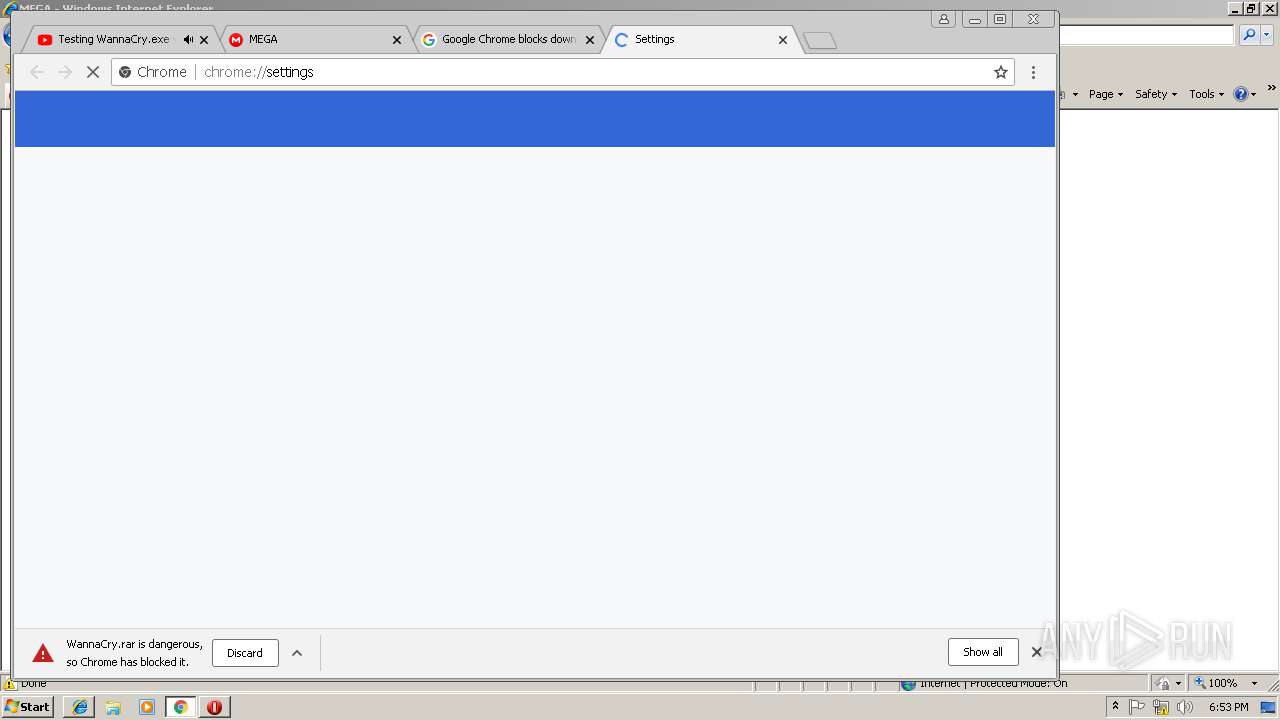
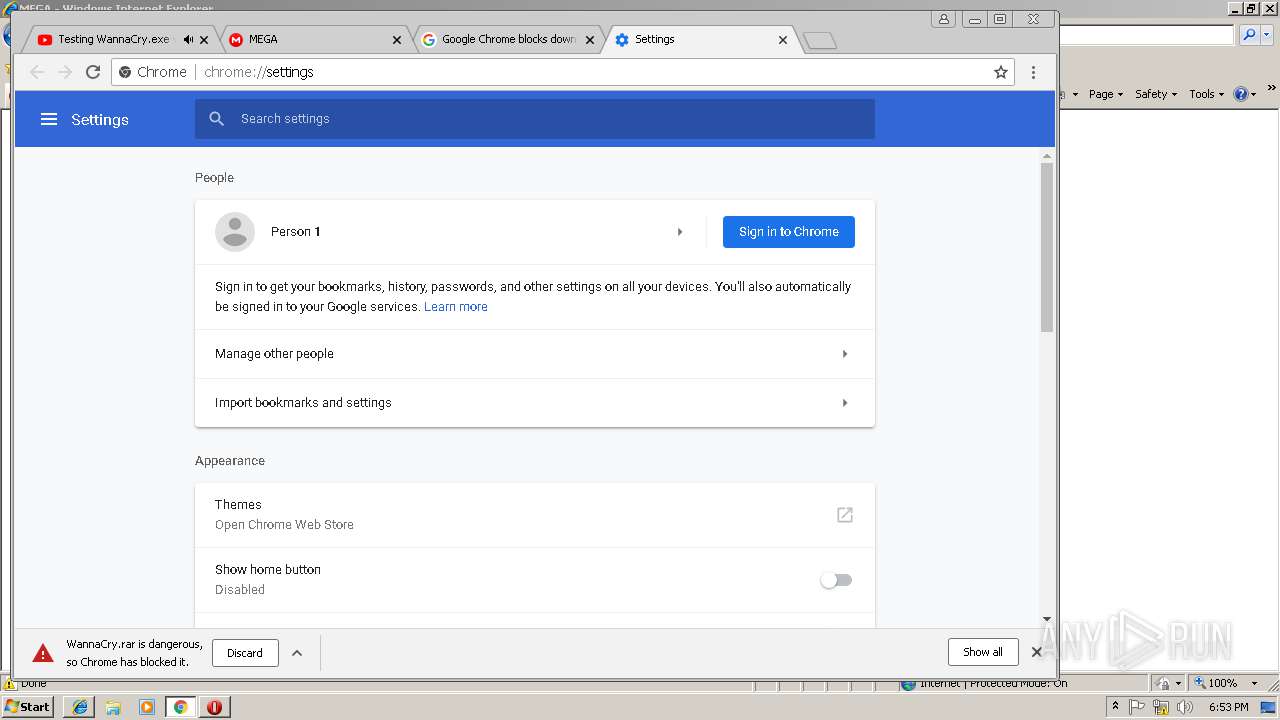
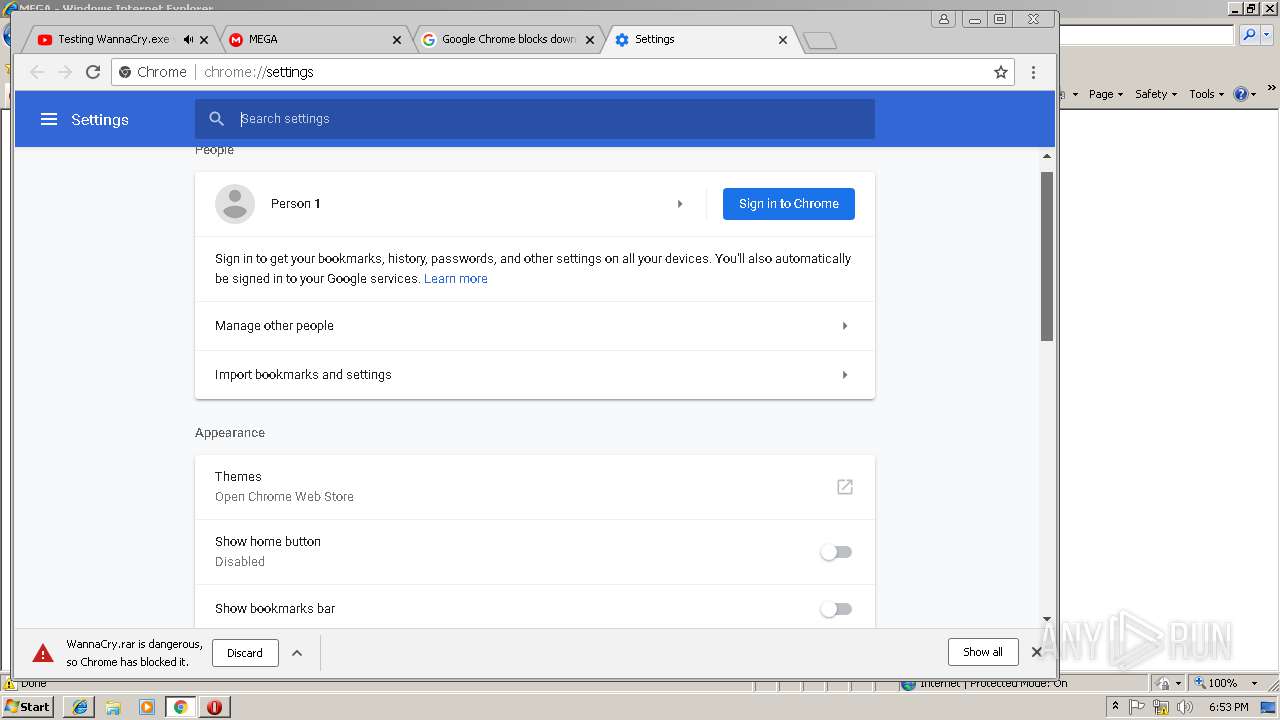
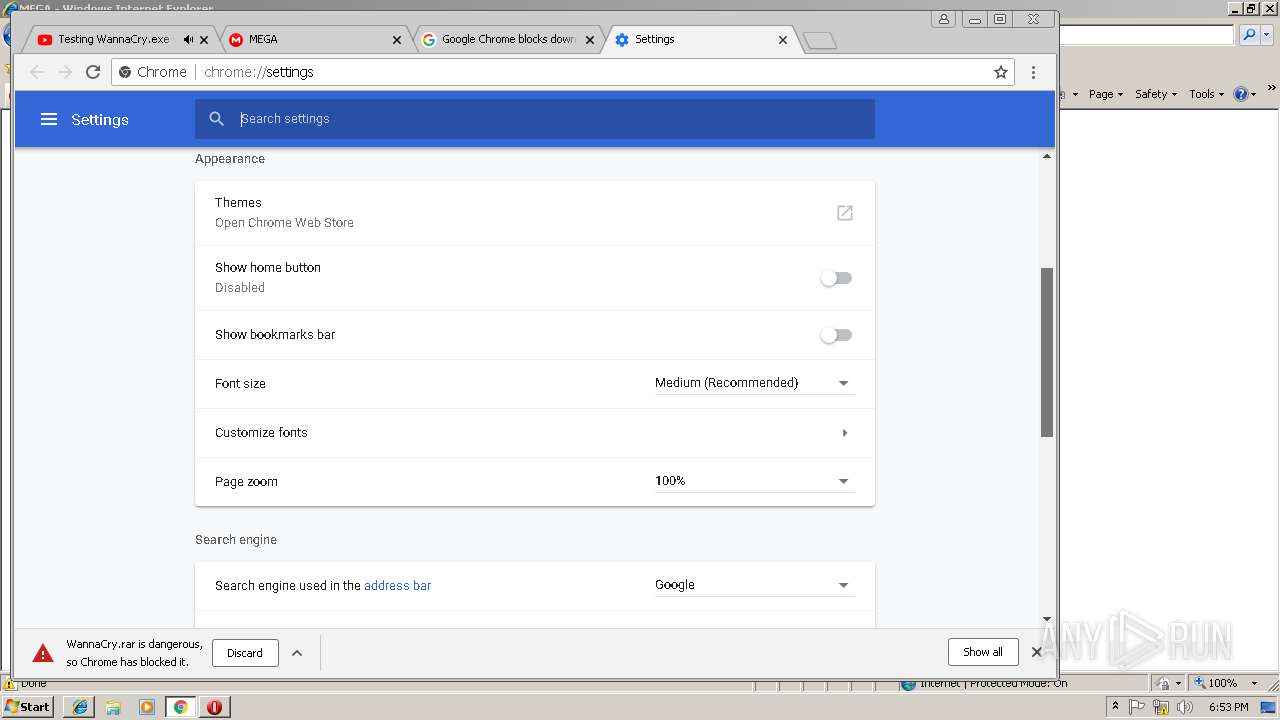
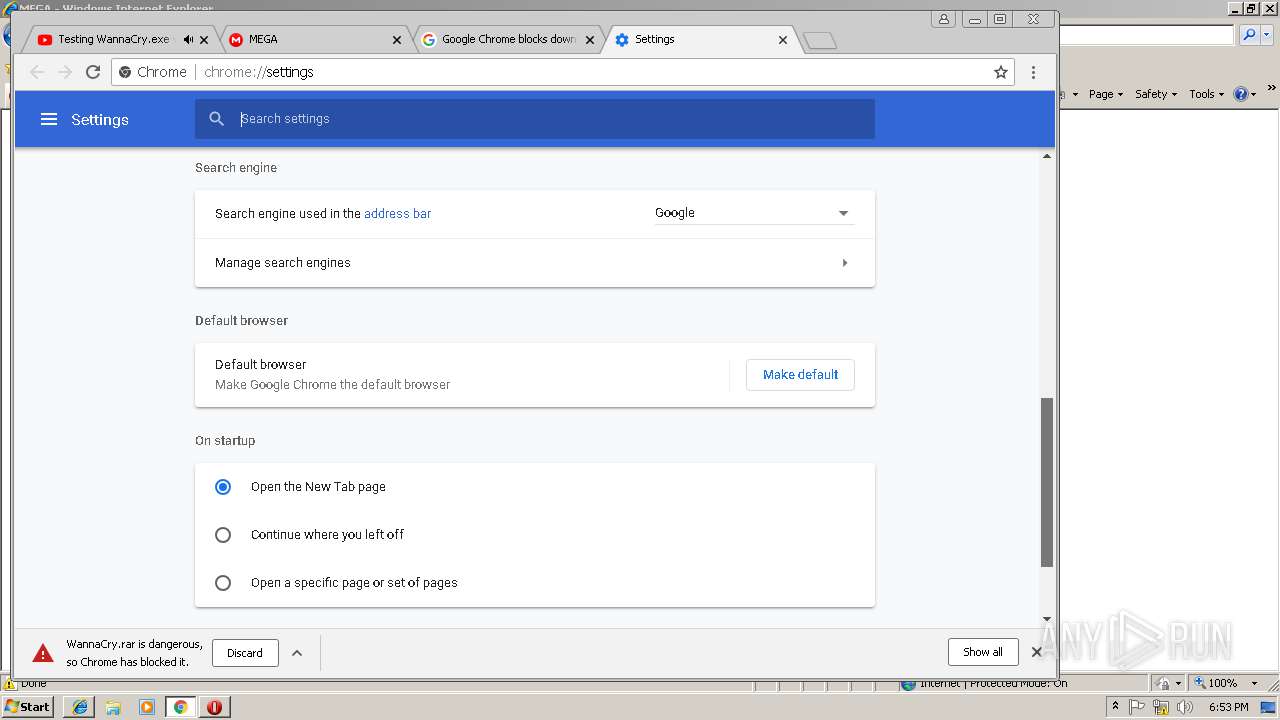
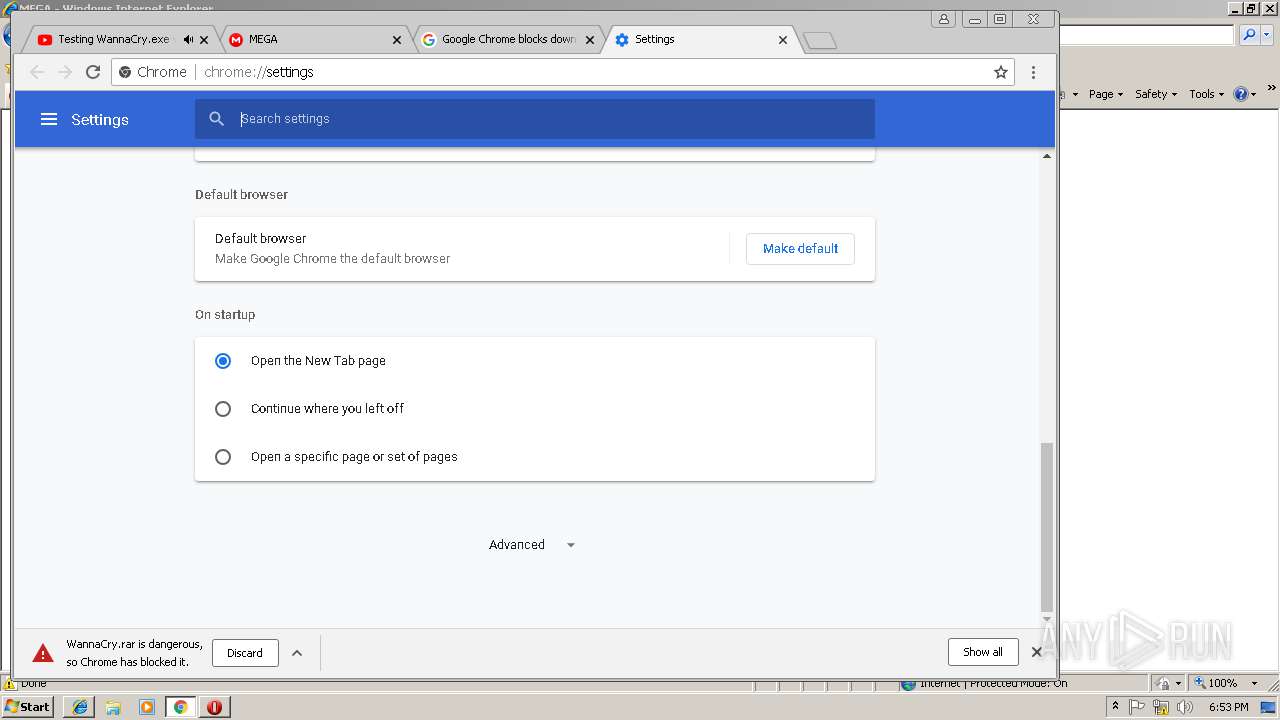
Changes internet zones settings
- iexplore.exe (PID: 2948)
Reads internet explorer settings
- iexplore.exe (PID: 3244)
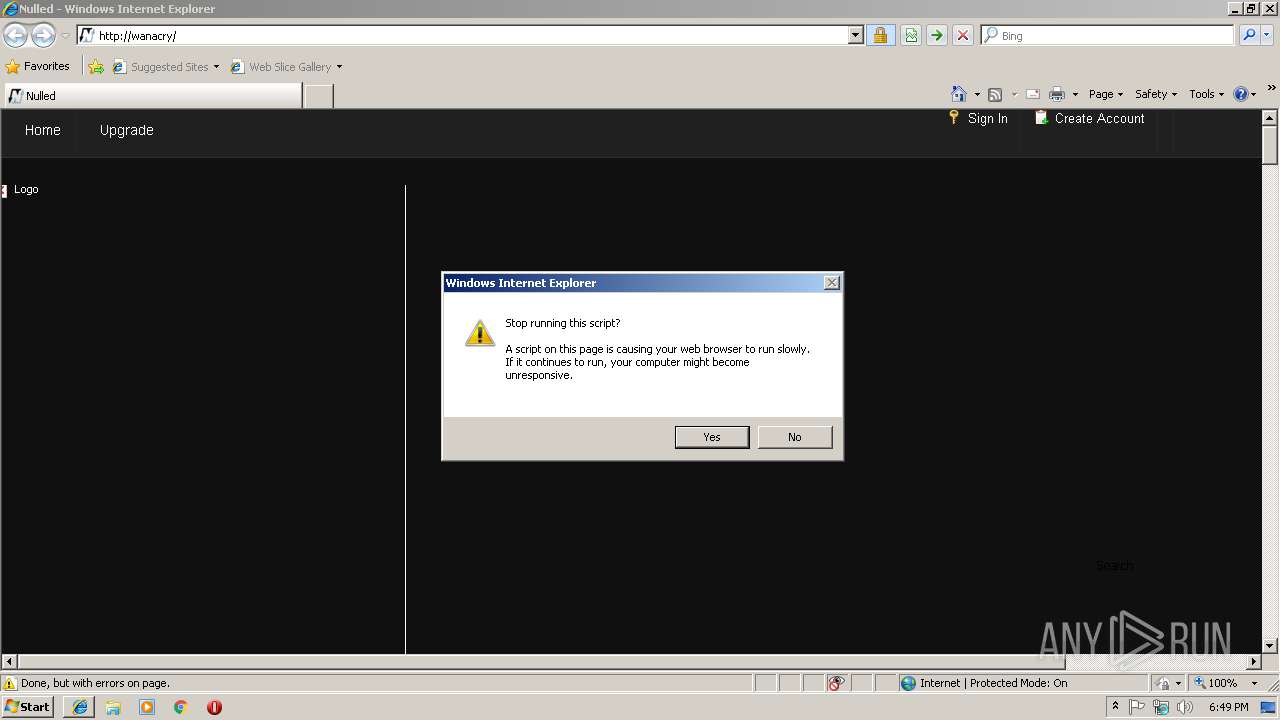
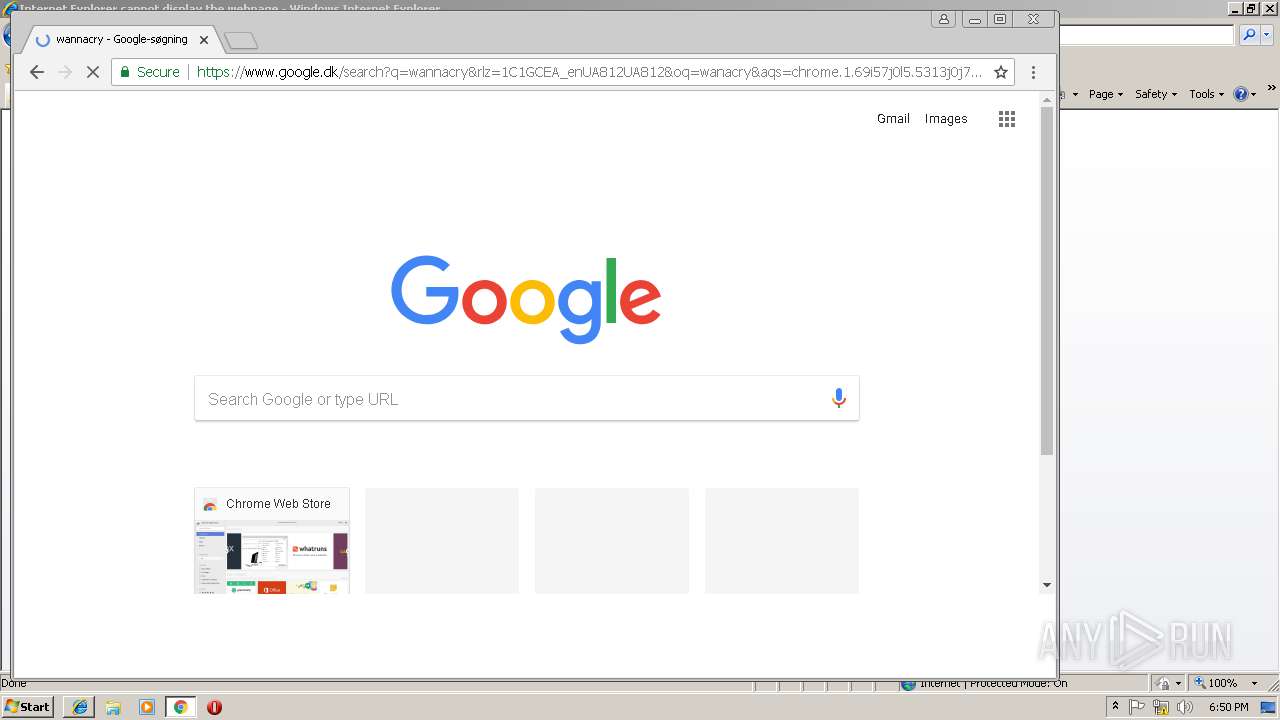
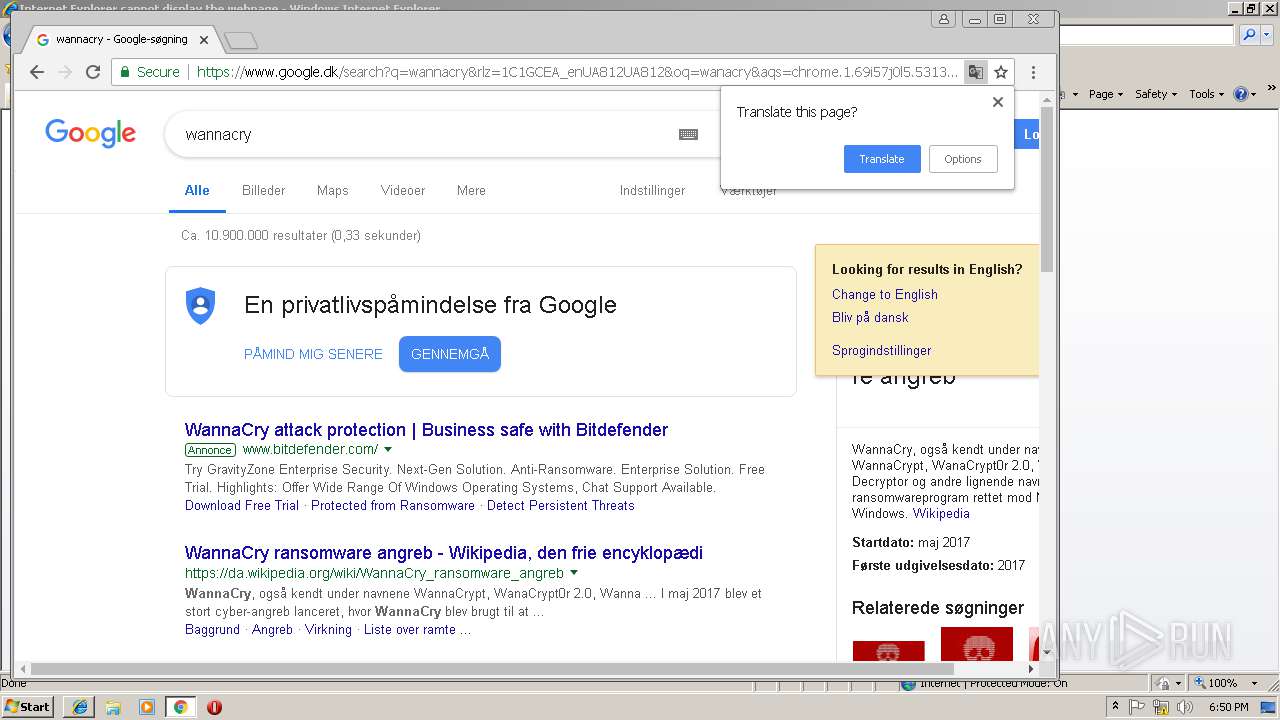
Application launched itself
- iexplore.exe (PID: 2948)
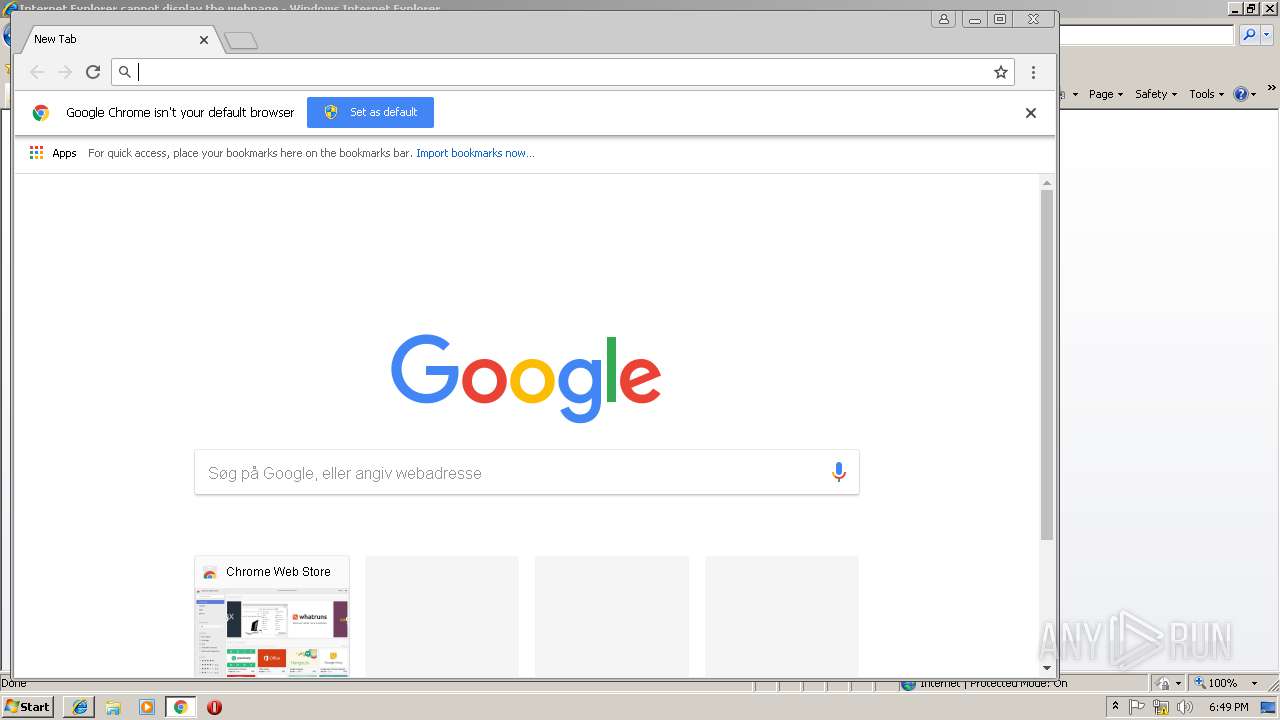
- chrome.exe (PID: 2340)
Reads Internet Cache Settings
- iexplore.exe (PID: 3244)
- iexplore.exe (PID: 2948)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2948)
Creates files in the user directory
- iexplore.exe (PID: 2948)
- opera.exe (PID: 2284)
- iexplore.exe (PID: 3244)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3212)
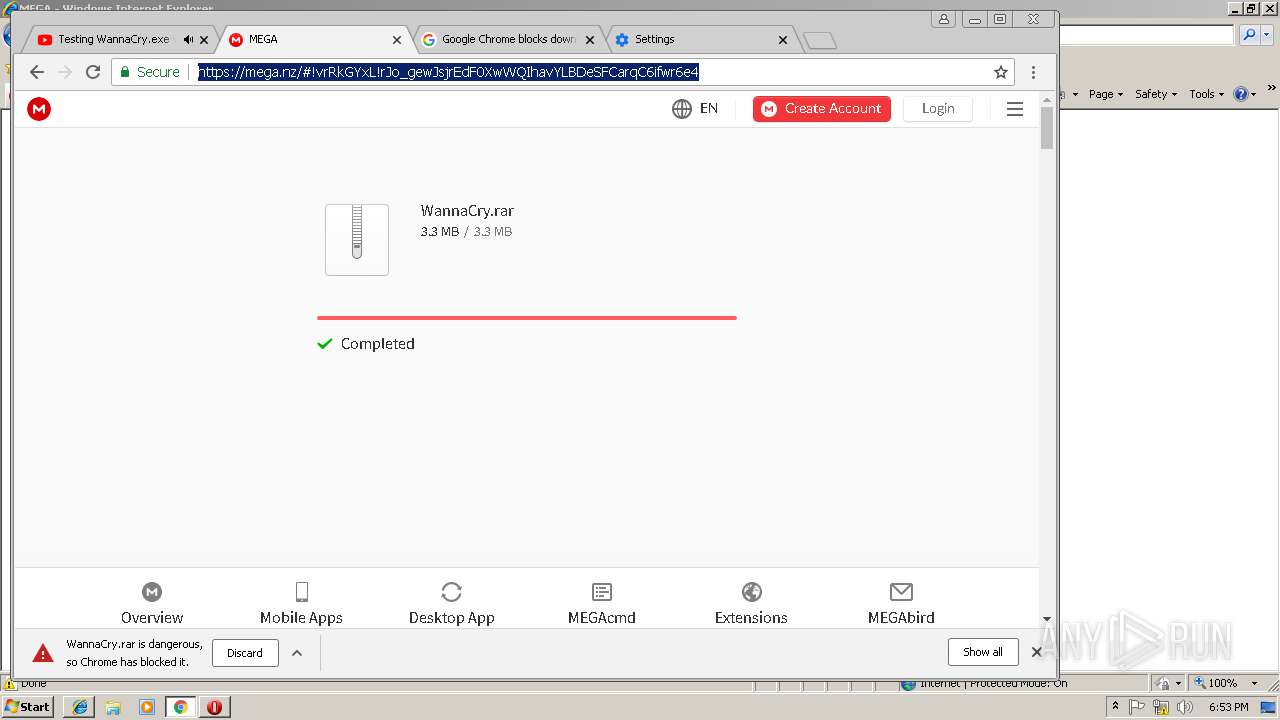
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3244)
Reads settings of System Certificates
- iexplore.exe (PID: 3244)
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 2340)
Changes settings of System certificates
- iexplore.exe (PID: 2948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=393C5CB49962BC839744D51EC0AB5EA9 --mojo-platform-channel-handle=3960 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9957A976721EFEA5137CA5F3F9C68276 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9957A976721EFEA5137CA5F3F9C68276 --renderer-client-id=12 --mojo-platform-channel-handle=3300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D9A3ABD7FC28D0A4FB25AC66B438A303 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D9A3ABD7FC28D0A4FB25AC66B438A303 --renderer-client-id=15 --mojo-platform-channel-handle=4864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=C598B84038679ABC6C6D01918EABE239 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=B80C3644545FBDEE16592A109B36B213 --mojo-platform-channel-handle=3760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2284 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F6FC07DC47167F56C782CF3864C970FE --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F6FC07DC47167F56C782CF3864C970FE --renderer-client-id=6 --mojo-platform-channel-handle=3460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F9E1C70368C4E0732FDF7B181B482598 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F9E1C70368C4E0732FDF7B181B482598 --renderer-client-id=7 --mojo-platform-channel-handle=3740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3DCD654EEEC49FB839EB897A04980D38 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3DCD654EEEC49FB839EB897A04980D38 --renderer-client-id=18 --mojo-platform-channel-handle=4532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 323
Read events
1 069
Write events
243
Delete events
11
Modification events
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {87F2BCC7-2D64-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307020000000A001200310002007803 | |||
Executable files
0
Suspicious files
264
Text files
244
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\nulled_to[1].txt | — | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@nulled[2].txt | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@nulled[1].txt | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\index[1].php | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\js.cookie[1].js | text | |
MD5:— | SHA256:— | |||
| 3244 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\nulled_to[1].htm | html | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@nulled[1].txt | text | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
181
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2340 | chrome.exe | GET | 204 | 52.205.77.87:80 | http://jungloconding.info/RHhKcGFrRykDXBE8EAoDA0kiMVEwHRI3NAApLRcsHil/NTcCSS1WFS0cd0ZRcEt8REc0ES5NUGILPhEVMQt3QUctFiwfXGIOd0FPd0xkQk90Xj4AACNFe1YRMAwmTVBxTHNIU3BOfENRfE0 | US | — | — | unknown |
2340 | chrome.exe | GET | 200 | 172.64.104.4:80 | http://cdn.atabencot.net/static/js/amvn.js | US | text | 136 Kb | shared |
2340 | chrome.exe | GET | 200 | 172.64.104.4:80 | http://cdn.atabencot.net/static/js/b64.js | US | text | 1.14 Kb | shared |
2340 | chrome.exe | GET | 200 | 52.85.221.92:80 | http://d1nmxiiewlx627.cloudfront.net/?ixmnd=709056 | US | text | 38.8 Kb | whitelisted |
2340 | chrome.exe | GET | 200 | 172.64.104.4:80 | http://cdn.atabencot.net/static/css/adfly_7.css | US | text | 869 b | shared |
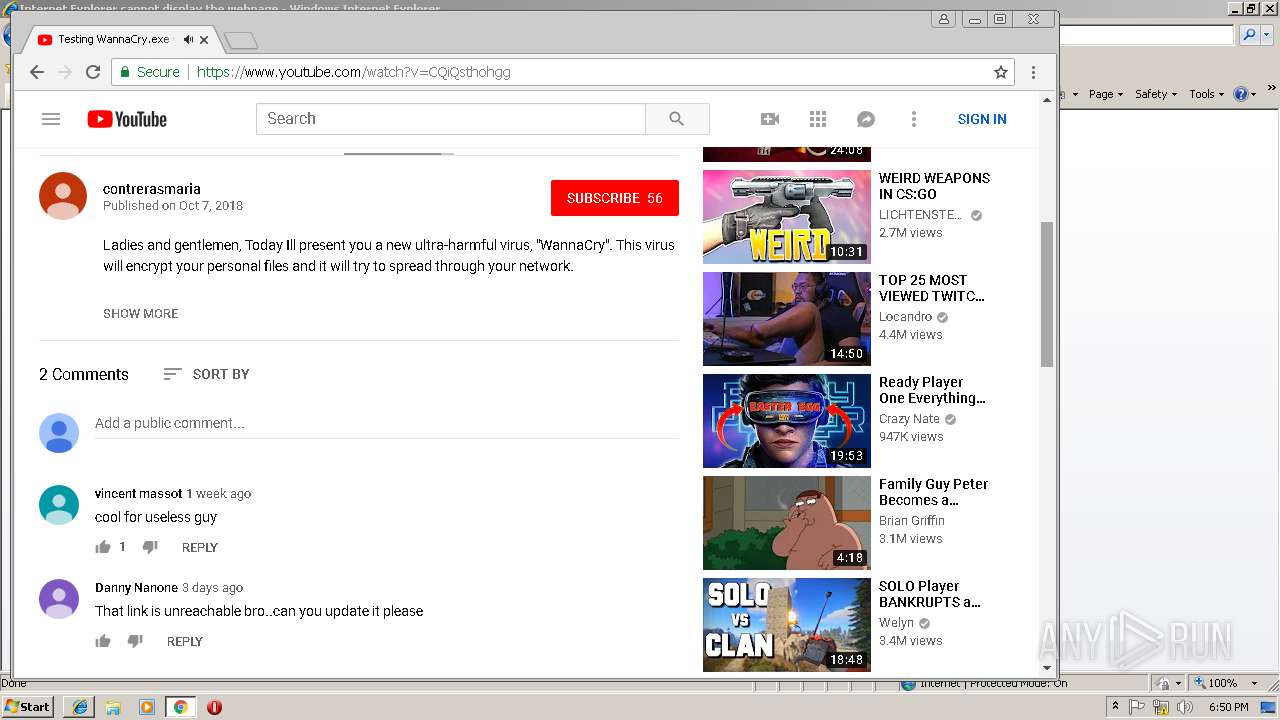
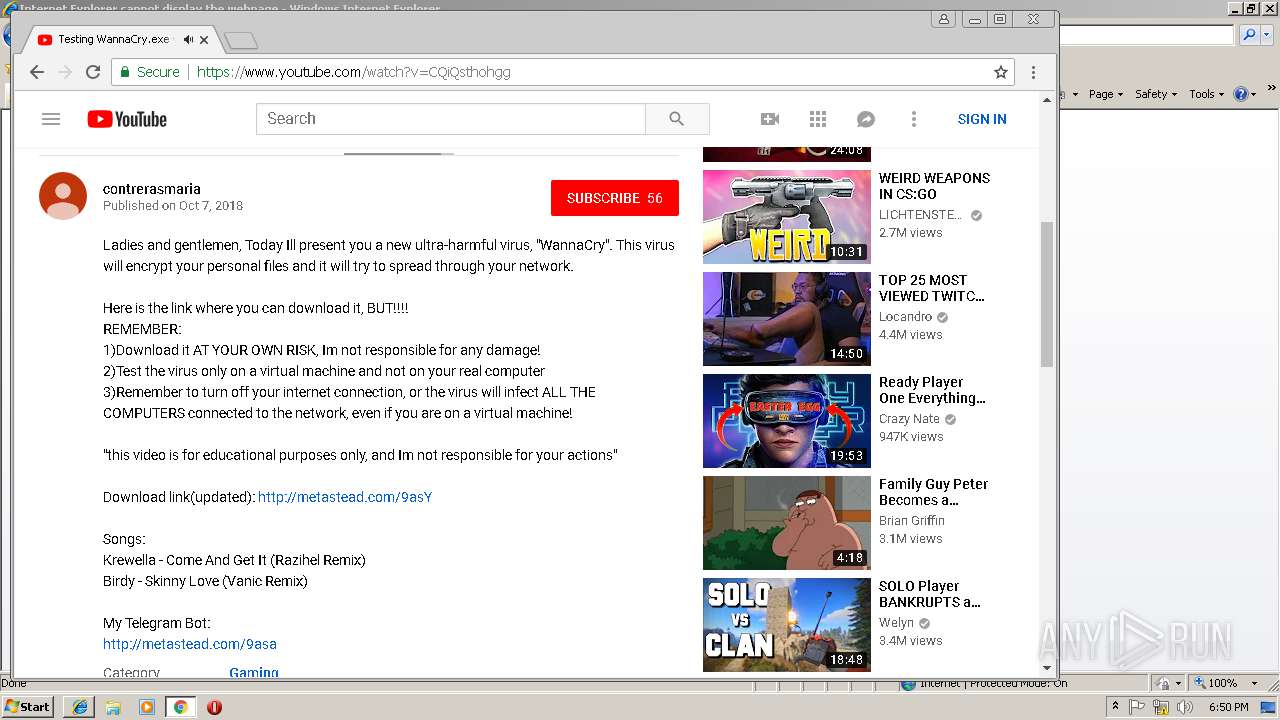
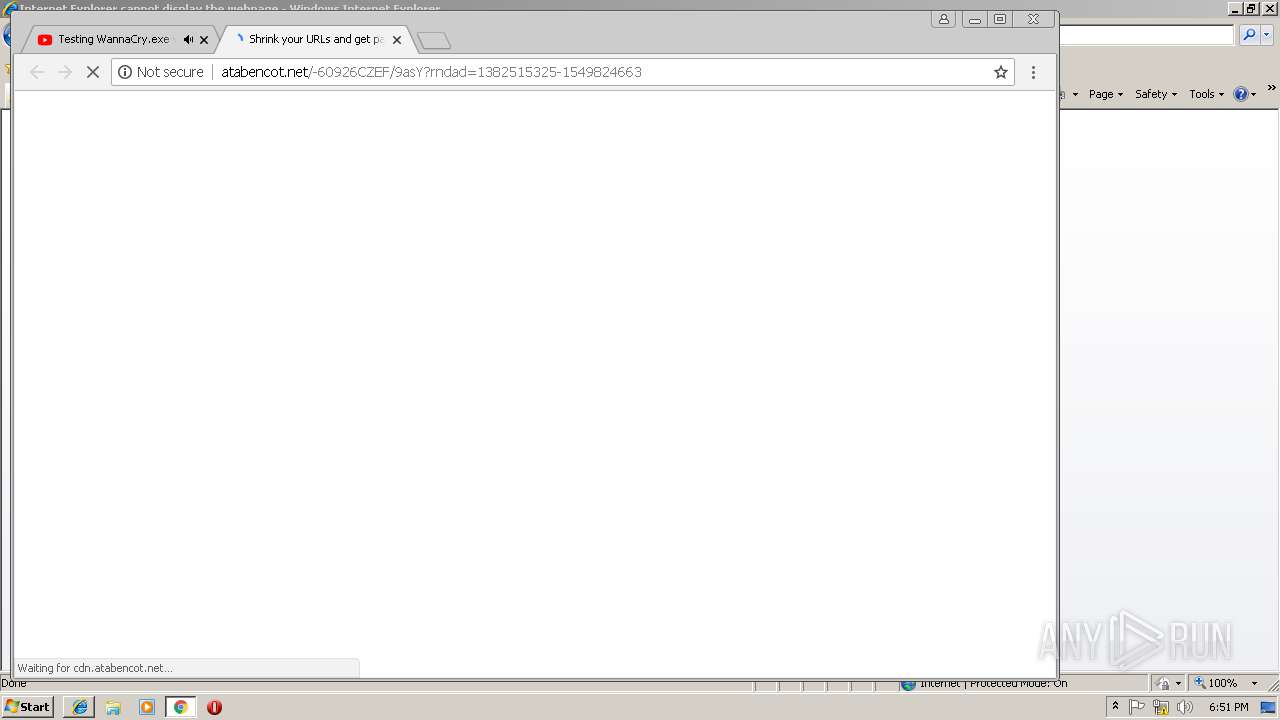
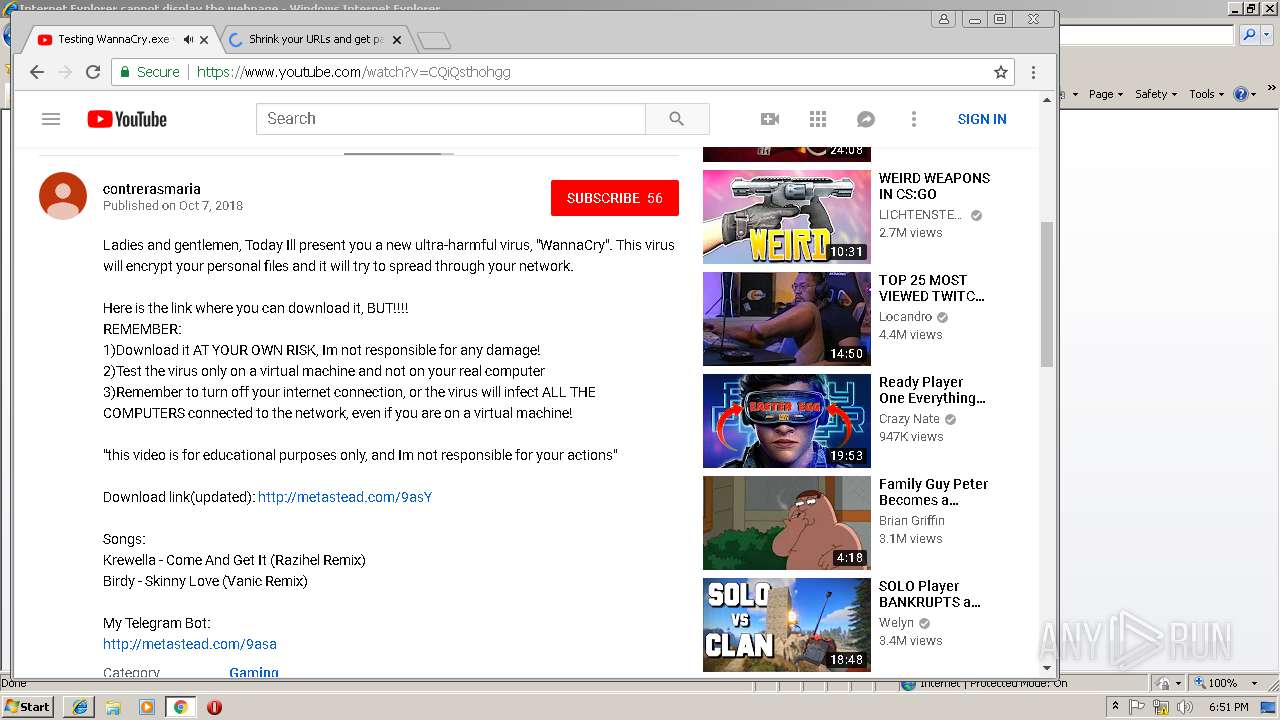
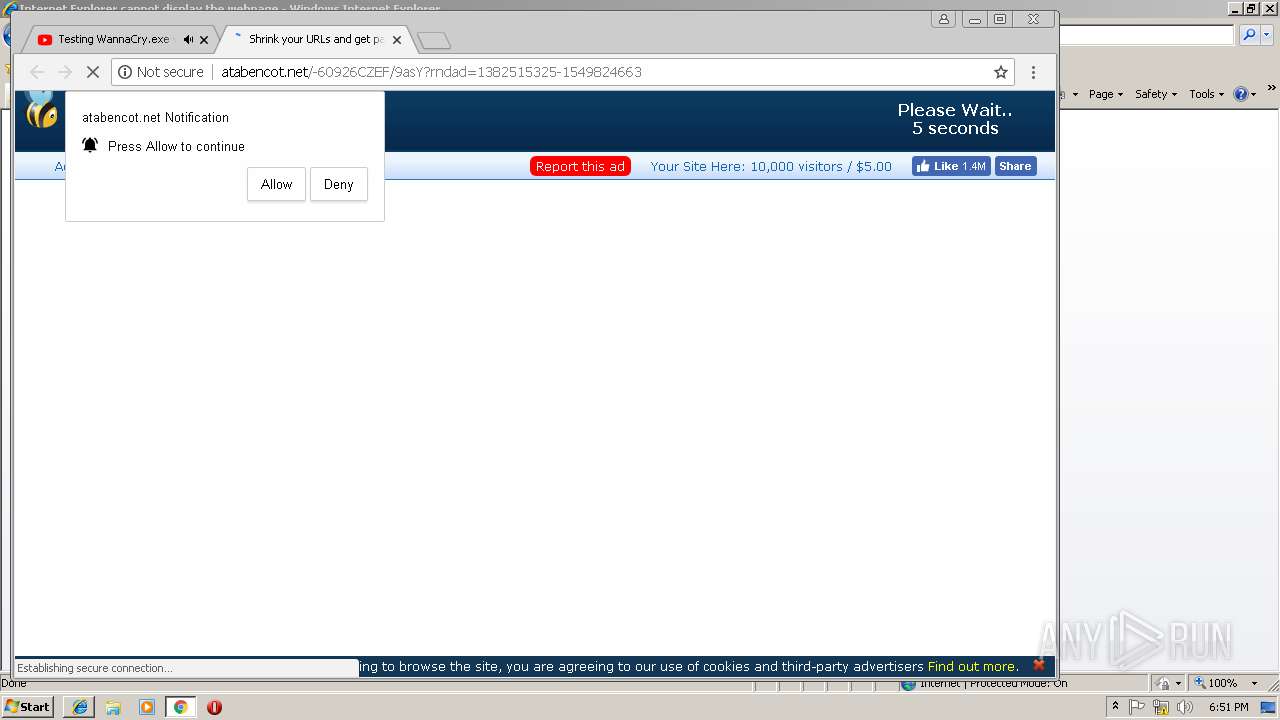
2340 | chrome.exe | GET | 200 | 172.64.105.4:80 | http://atabencot.net/-60926CZEF/9asY?rndad=1382515325-1549824663 | US | html | 11.0 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 172.64.104.4:80 | http://cdn.atabencot.net/static/js/main.js | US | text | 708 b | shared |
2340 | chrome.exe | GET | 200 | 172.64.105.4:80 | http://atabencot.net/js/display.js | US | text | 20.8 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 172.64.105.4:80 | http://atabencot.net/fp.rev10.php?nocache=7339 | US | text | 14.4 Kb | suspicious |
2340 | chrome.exe | GET | 200 | 172.64.104.4:80 | http://cdn.atabencot.net/static/image/logo_fb2.png | US | image | 6.14 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
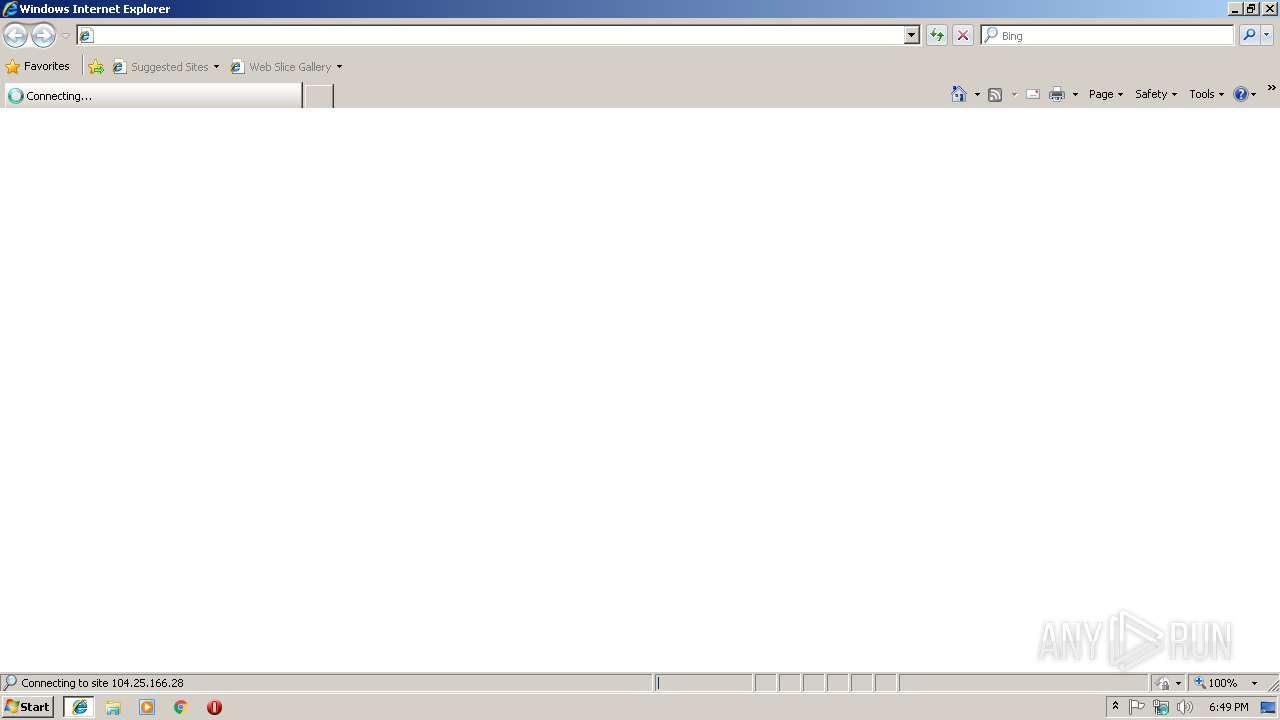
2948 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2948 | iexplore.exe | 104.25.166.28:443 | www.nulled.to | Cloudflare Inc | US | shared |
3244 | iexplore.exe | 172.217.16.194:443 | adservice.google.com | Google Inc. | US | whitelisted |
3244 | iexplore.exe | 74.125.206.105:443 | www.google.com | Google Inc. | US | whitelisted |
3244 | iexplore.exe | 104.20.185.62:443 | shoppy.gg | Cloudflare Inc | US | shared |
3244 | iexplore.exe | 151.101.120.193:443 | i.imgur.com | Fastly | US | malicious |
3244 | iexplore.exe | 172.217.16.206:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3244 | iexplore.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2340 | chrome.exe | 216.58.205.227:443 | www.google.de | Google Inc. | US | whitelisted |
2340 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.nulled.to |
| unknown |
static.nulled.to |
| unknown |
maxcdn.bootstrapcdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
adservice.google.dk |
| whitelisted |
adservice.google.com |
| whitelisted |
www.google.com |
| malicious |