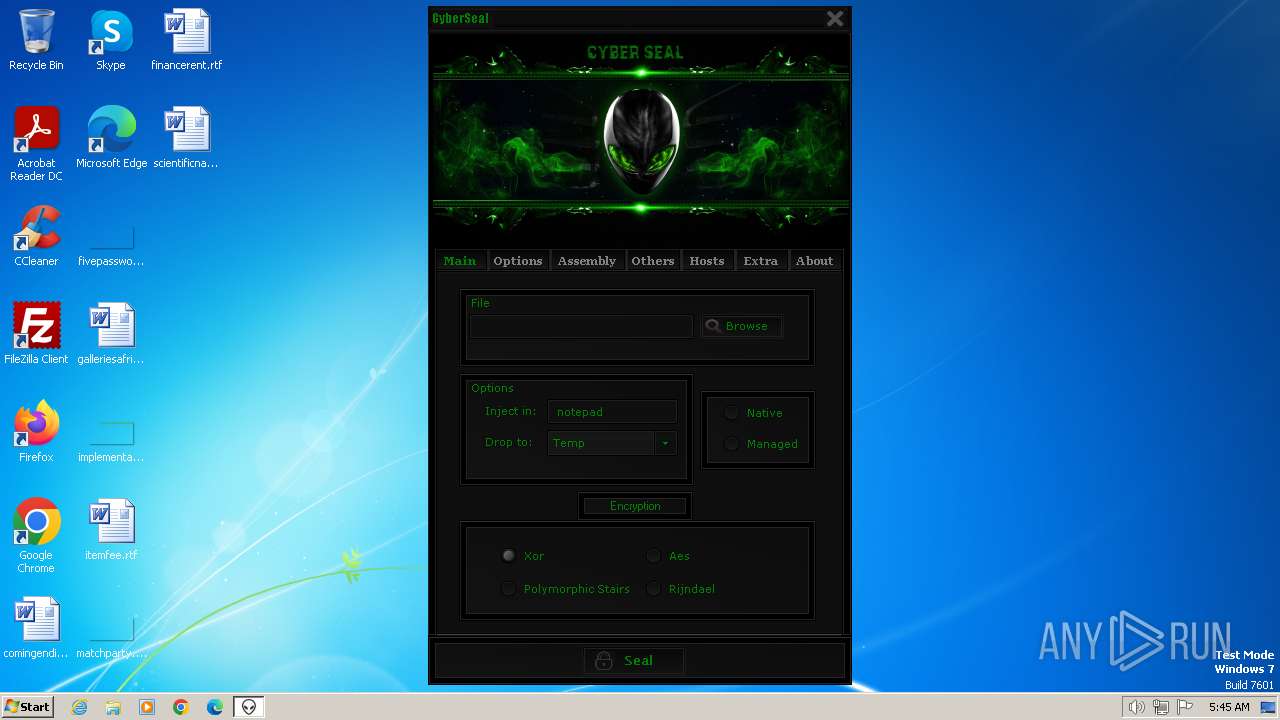
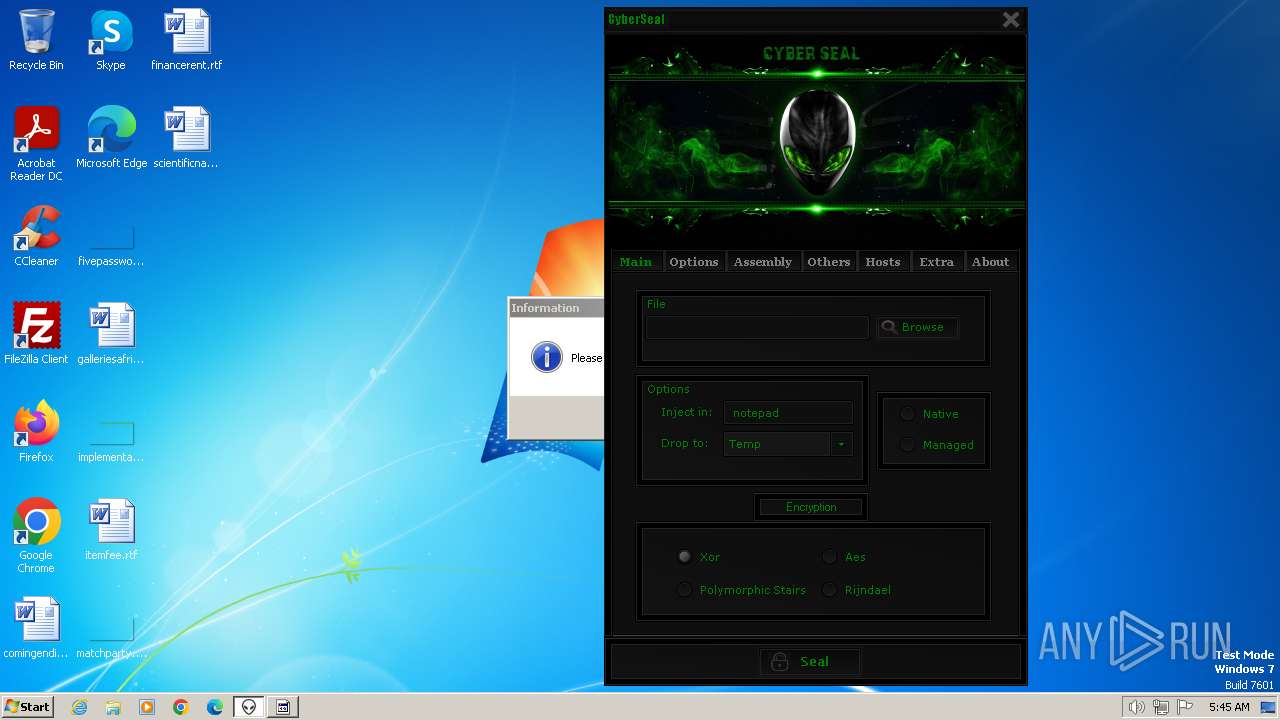
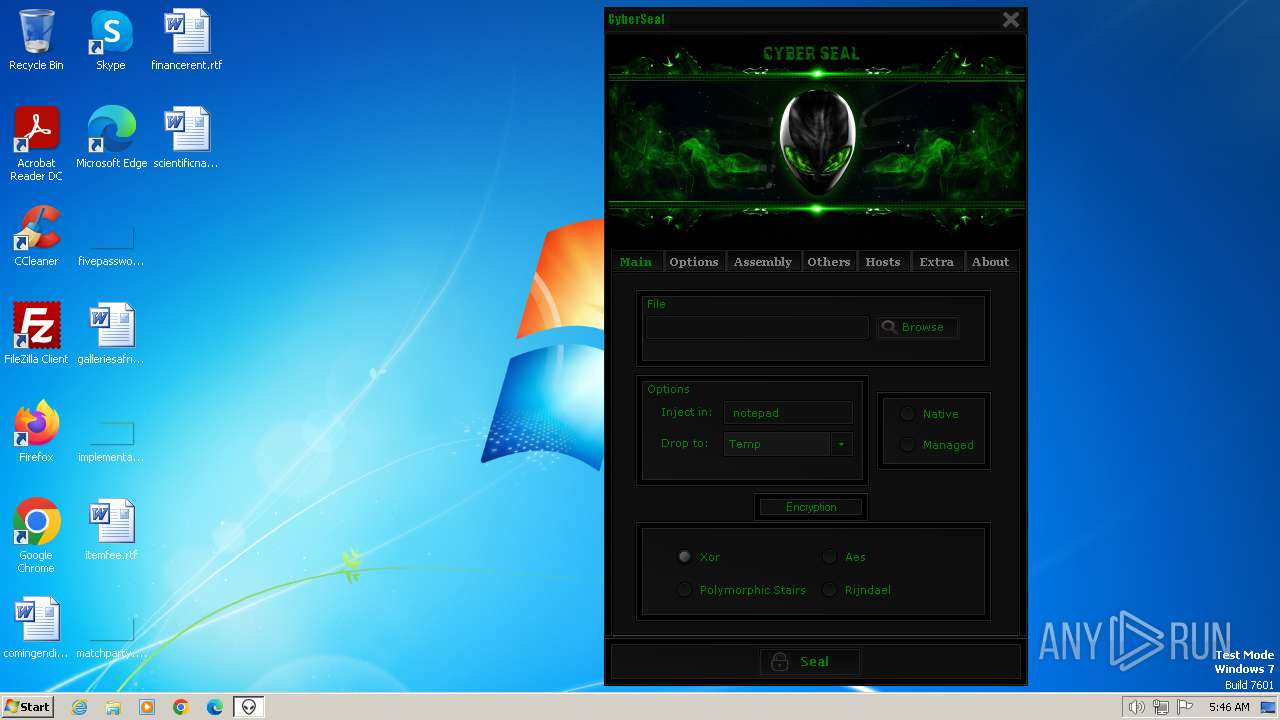
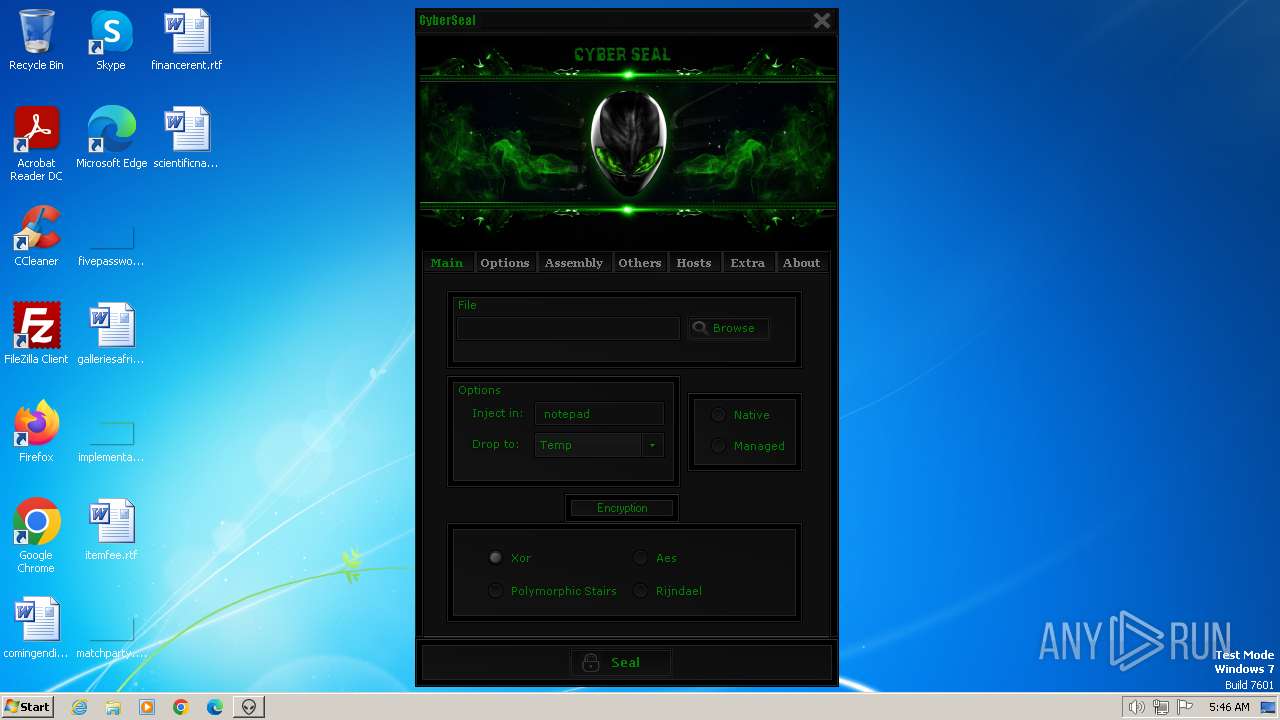
| File name: | CyberSeal Crypter Cracked.exe |
| Full analysis: | https://app.any.run/tasks/6646da27-2e6c-41ef-b46a-52abeb04d2e0 |
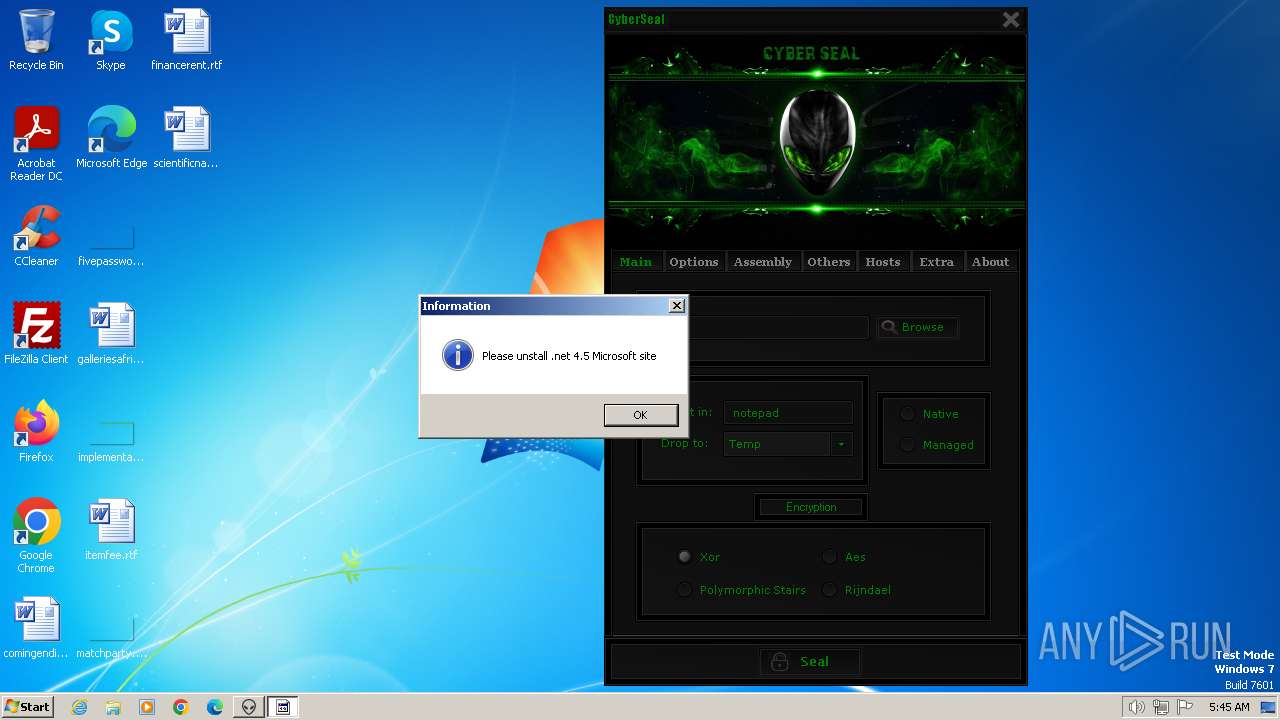
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2024, 05:45:09 |
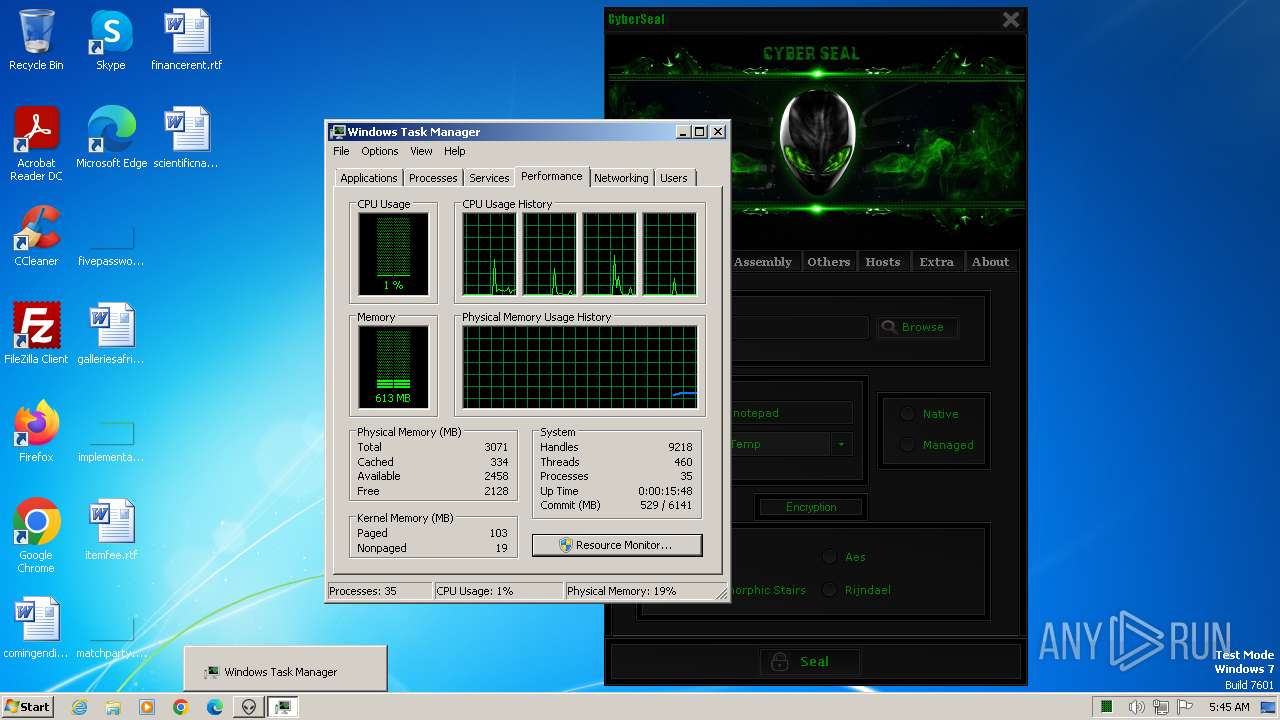
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D72067D649B5D5F8CE3AED7E174F77F3 |
| SHA1: | 922B64A69F50CA22BE451AA036288642669B7DA3 |
| SHA256: | 22D81EBFB89EB89C7864A94E16EE3474E31F258520786F205653BDEF1AA2DFB9 |
| SSDEEP: | 98304:G2cPK8+doZd0MyLnwb9RA7fxIbxh5Q3kLj1xl0FGhXcYz3dr:pCKhdoEMyLns9KJIbxh52kLZ56Yz3p |
MALICIOUS
Drops the executable file immediately after the start
- CyberSeal Crypter Cracked.exe (PID: 1776)
- CyberSeal Cracked by ImFred.exe (PID: 1864)
SUSPICIOUS
Executable content was dropped or overwritten
- CyberSeal Crypter Cracked.exe (PID: 1776)
- CyberSeal Cracked by ImFred.exe (PID: 1864)
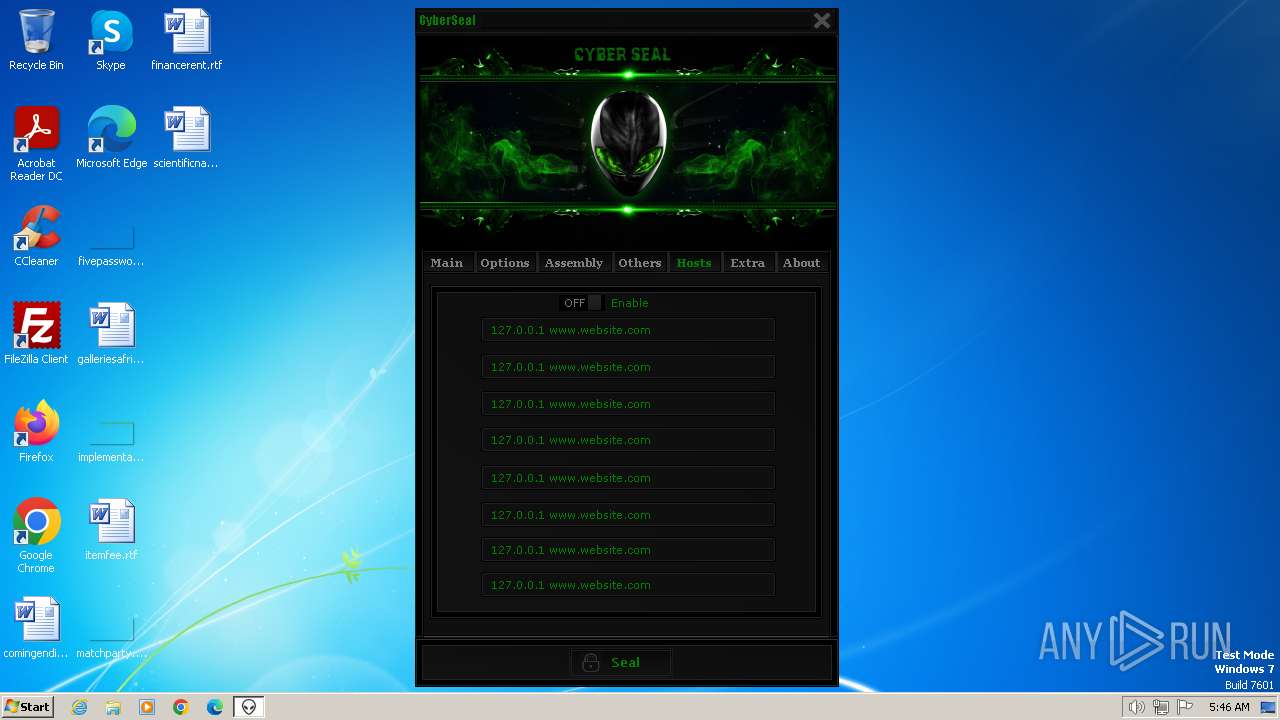
Reads the Internet Settings
- CyberSeal Crypter Cracked.exe (PID: 1776)
- cetrjnxwdvg.exe (PID: 1056)
Process requests binary or script from the Internet
- cetrjnxwdvg.exe (PID: 1056)
INFO
Reads mouse settings
- CyberSeal Crypter Cracked.exe (PID: 1776)
Reads the computer name
- CyberSeal Crypter Cracked.exe (PID: 1776)
- cetrjnxwdvg.exe (PID: 1056)
- CyberSeal Cracked by ImFred.exe (PID: 1864)
Checks supported languages
- CyberSeal Crypter Cracked.exe (PID: 1776)
- cetrjnxwdvg.exe (PID: 1056)
- CyberSeal Cracked by ImFred.exe (PID: 1864)
Create files in a temporary directory
- CyberSeal Crypter Cracked.exe (PID: 1776)
Creates files or folders in the user directory
- CyberSeal Crypter Cracked.exe (PID: 1776)
Reads the machine GUID from the registry
- cetrjnxwdvg.exe (PID: 1056)
- CyberSeal Cracked by ImFred.exe (PID: 1864)
Reads Environment values
- cetrjnxwdvg.exe (PID: 1056)
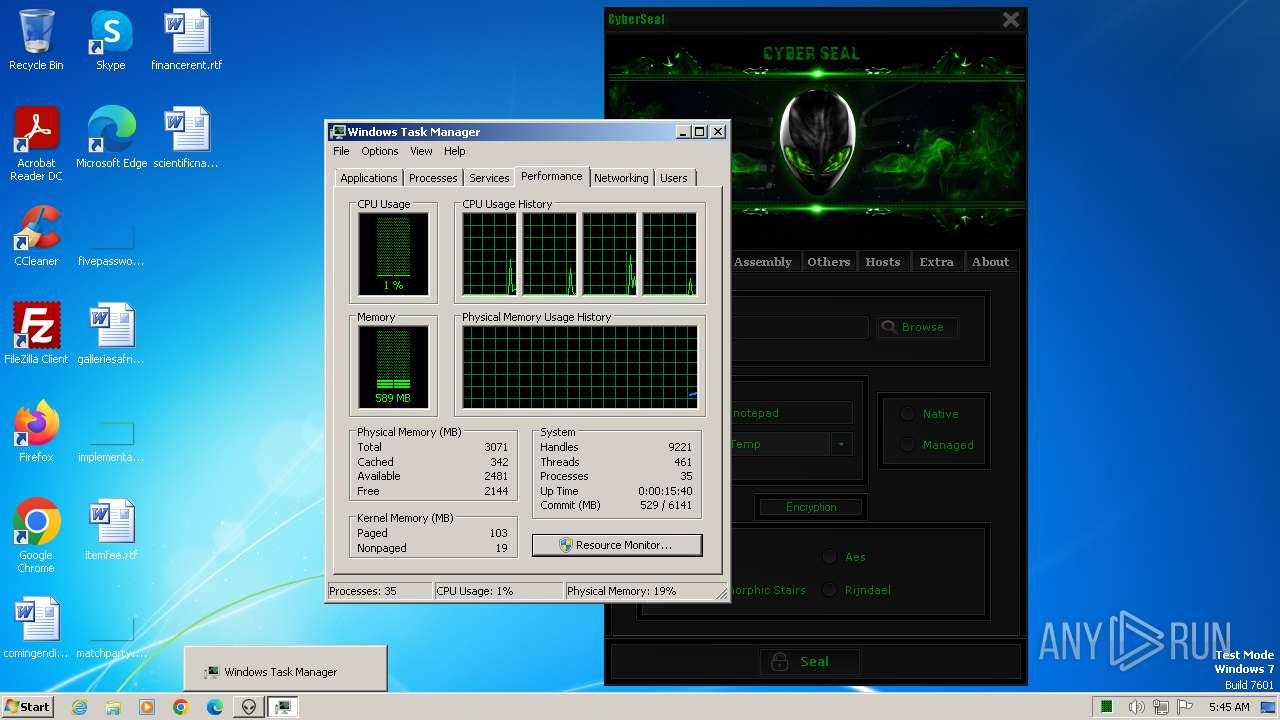
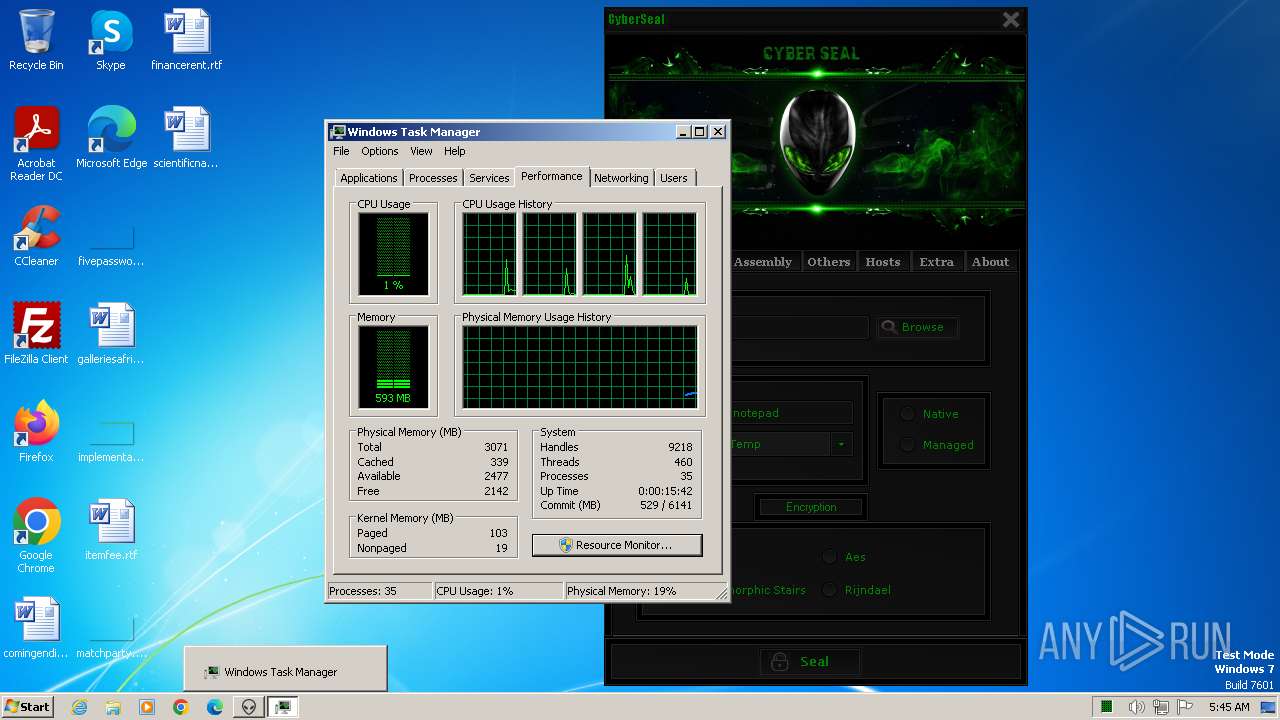
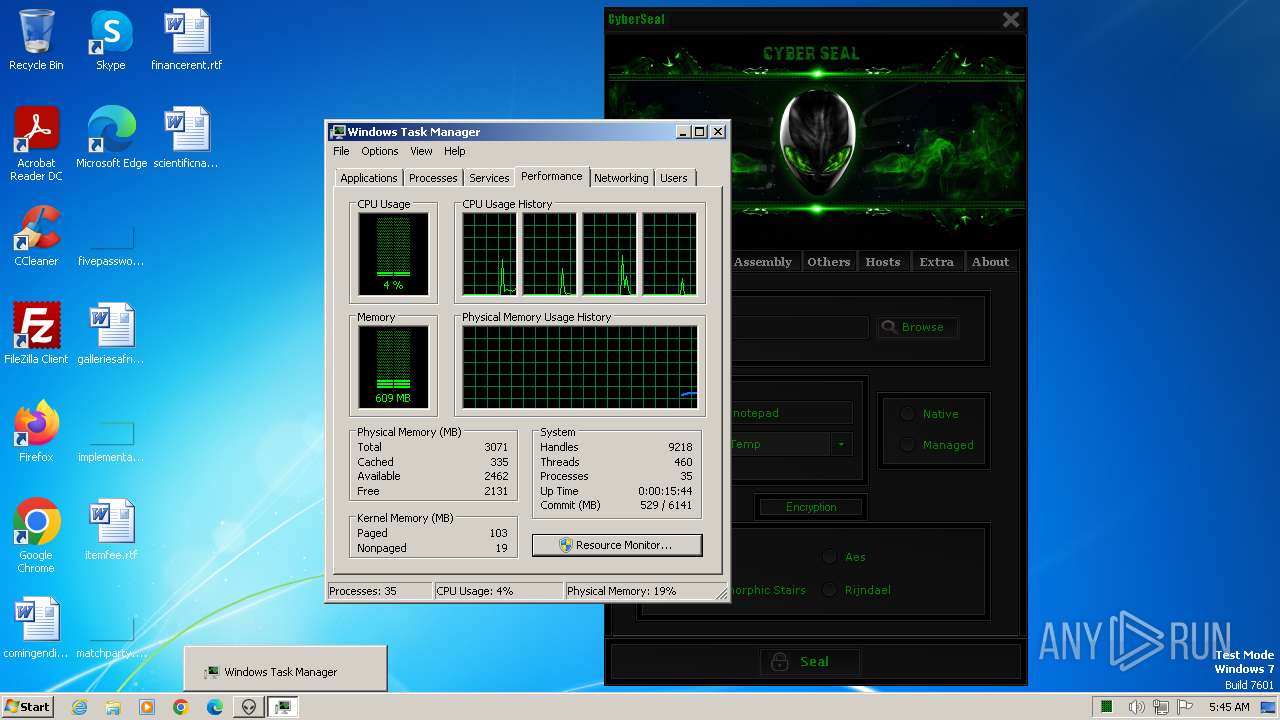
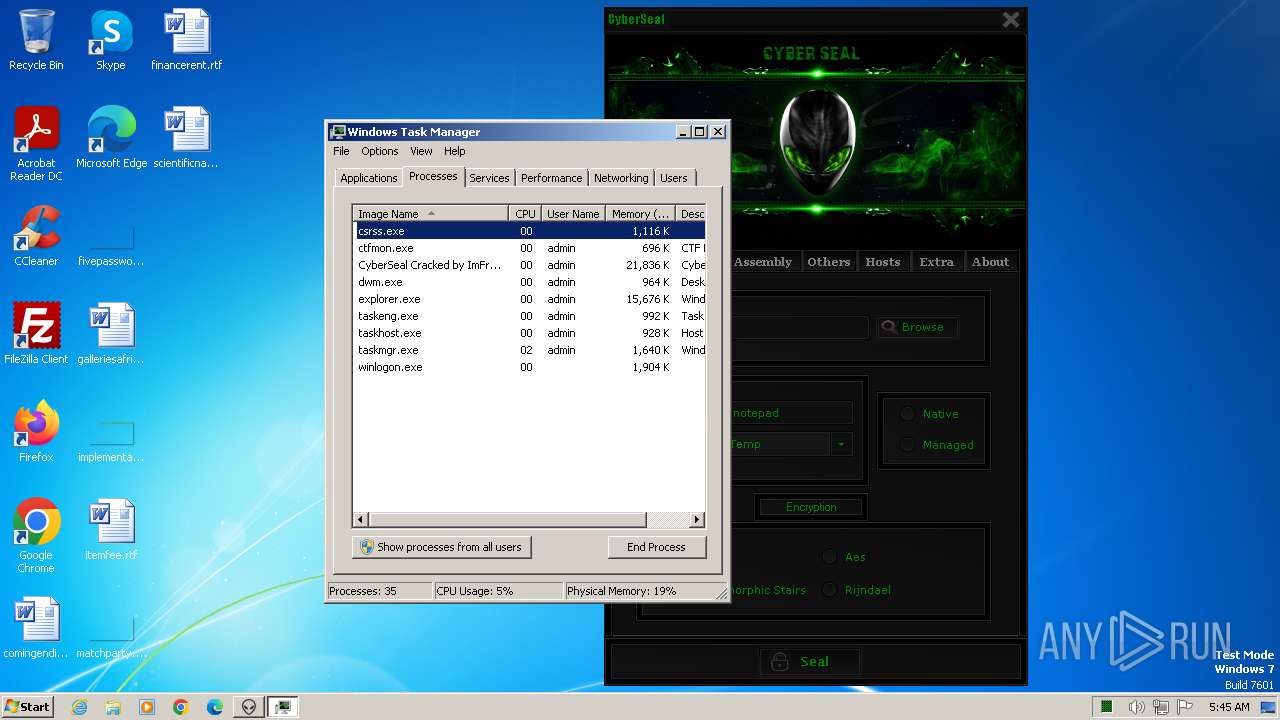
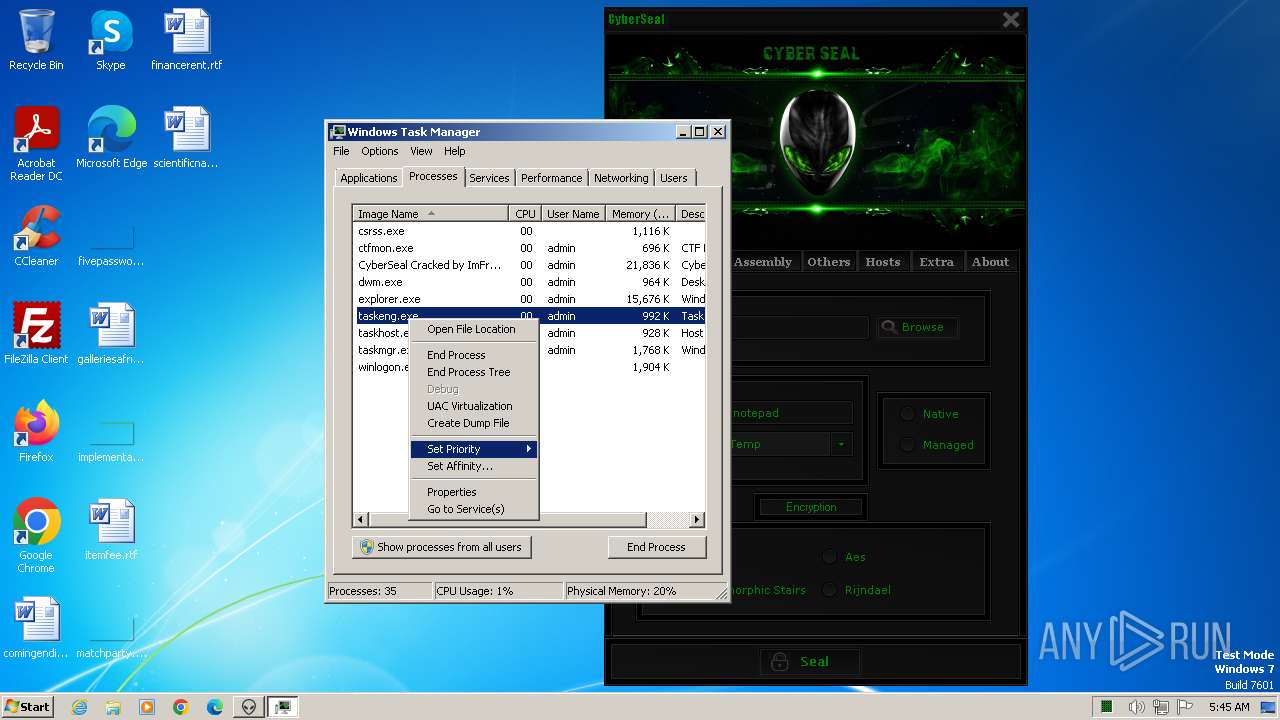
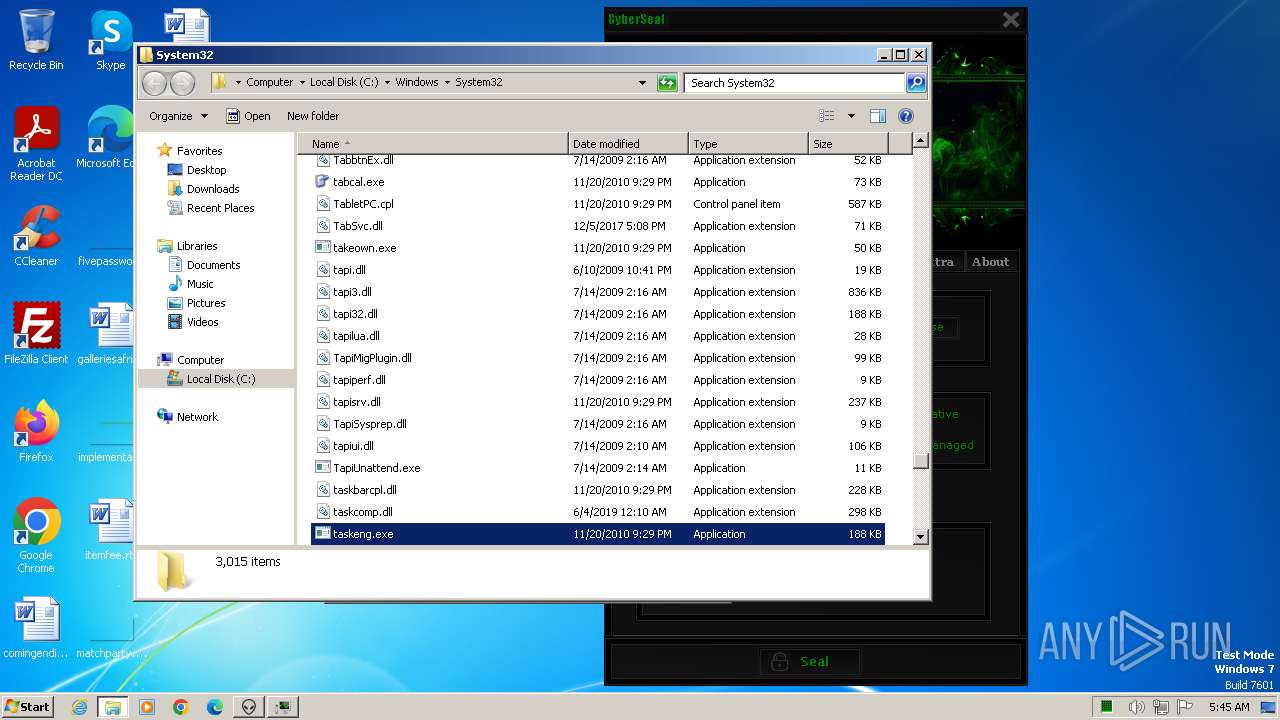
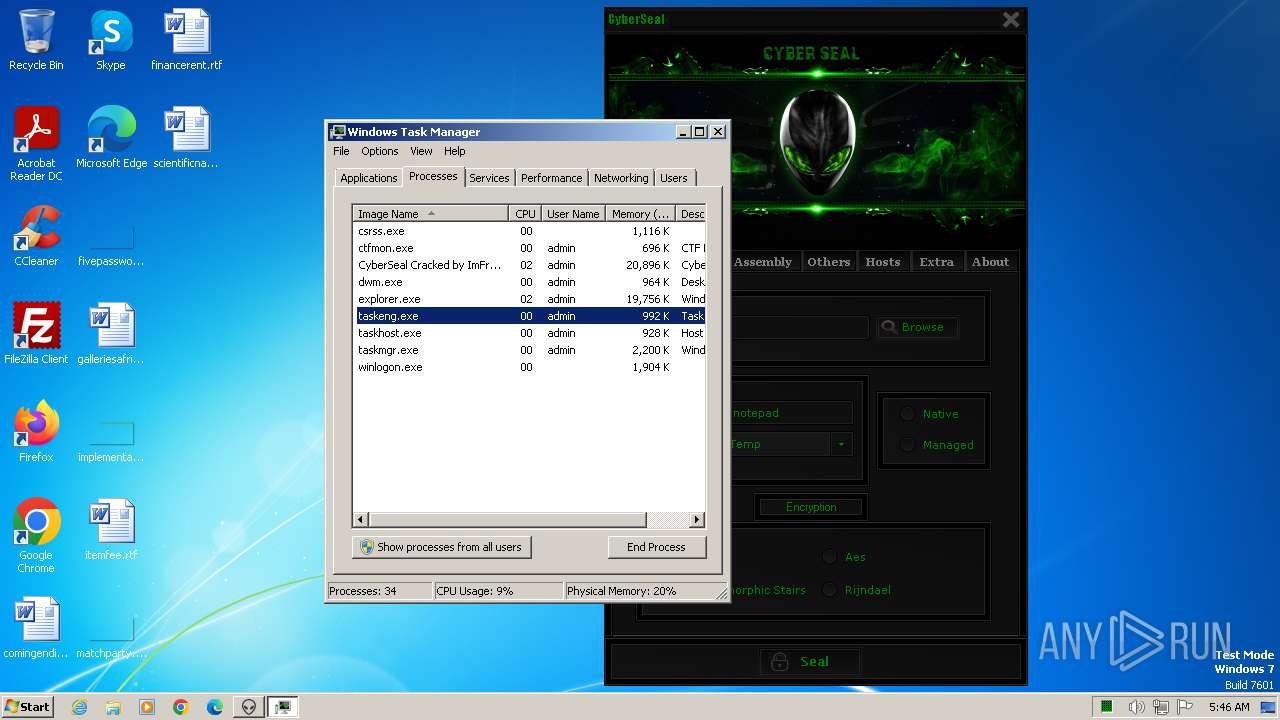
Manual execution by a user
- taskmgr.exe (PID: 1732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:20 03:33:48+01:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 4111360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
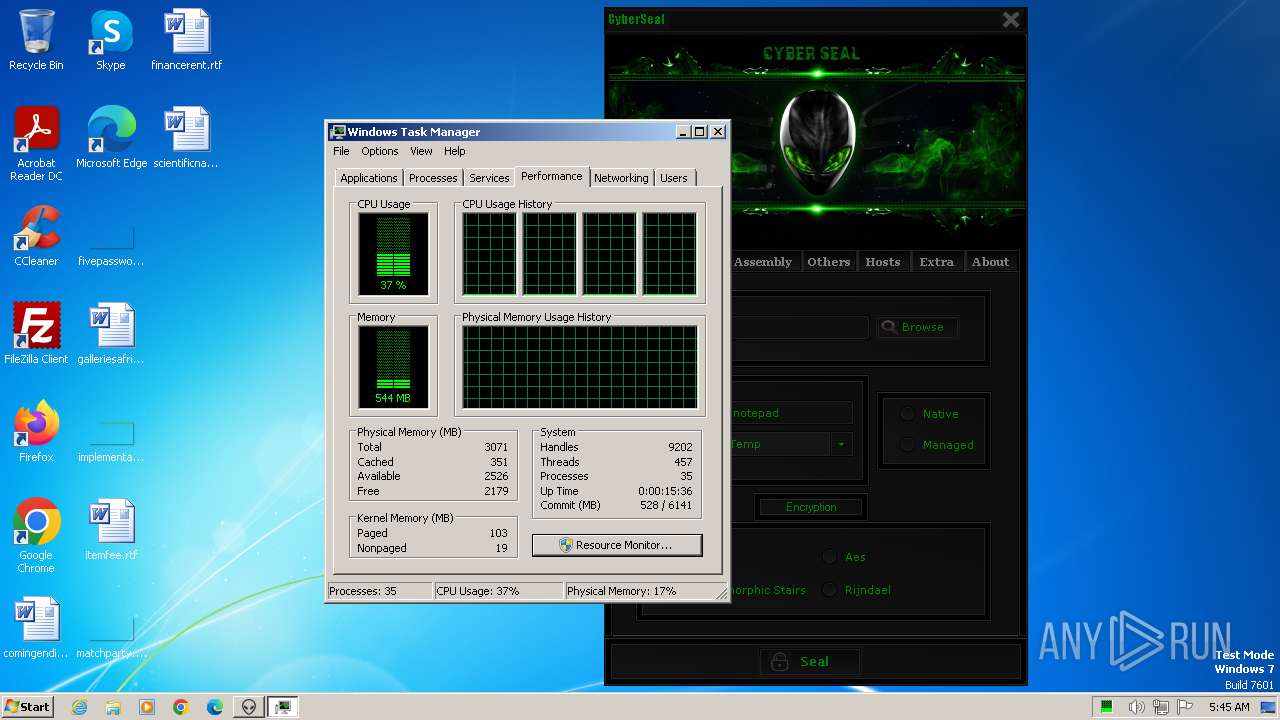
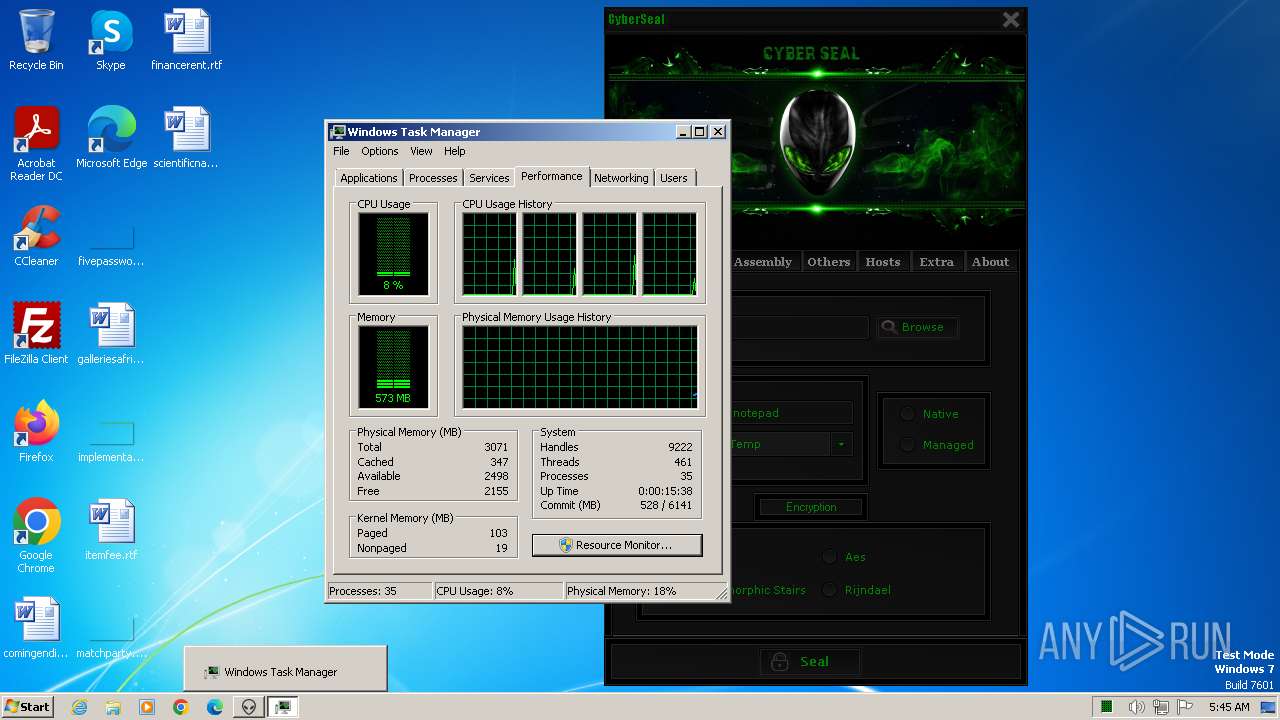
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | "C:\Users\admin\AppData\Roaming\Z46842481\cetrjnxwdvg.exe" | C:\Users\admin\AppData\Roaming\Z46842481\cetrjnxwdvg.exe | CyberSeal Crypter Cracked.exe | ||||||||||||
User: admin Company: cwvdwei0vfc Integrity Level: MEDIUM Description: m2joxdcouwy Exit code: 0 Version: 5.0.3.5 Modules
| |||||||||||||||
| 1732 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\System32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1776 | "C:\Users\admin\AppData\Local\Temp\CyberSeal Crypter Cracked.exe" | C:\Users\admin\AppData\Local\Temp\CyberSeal Crypter Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
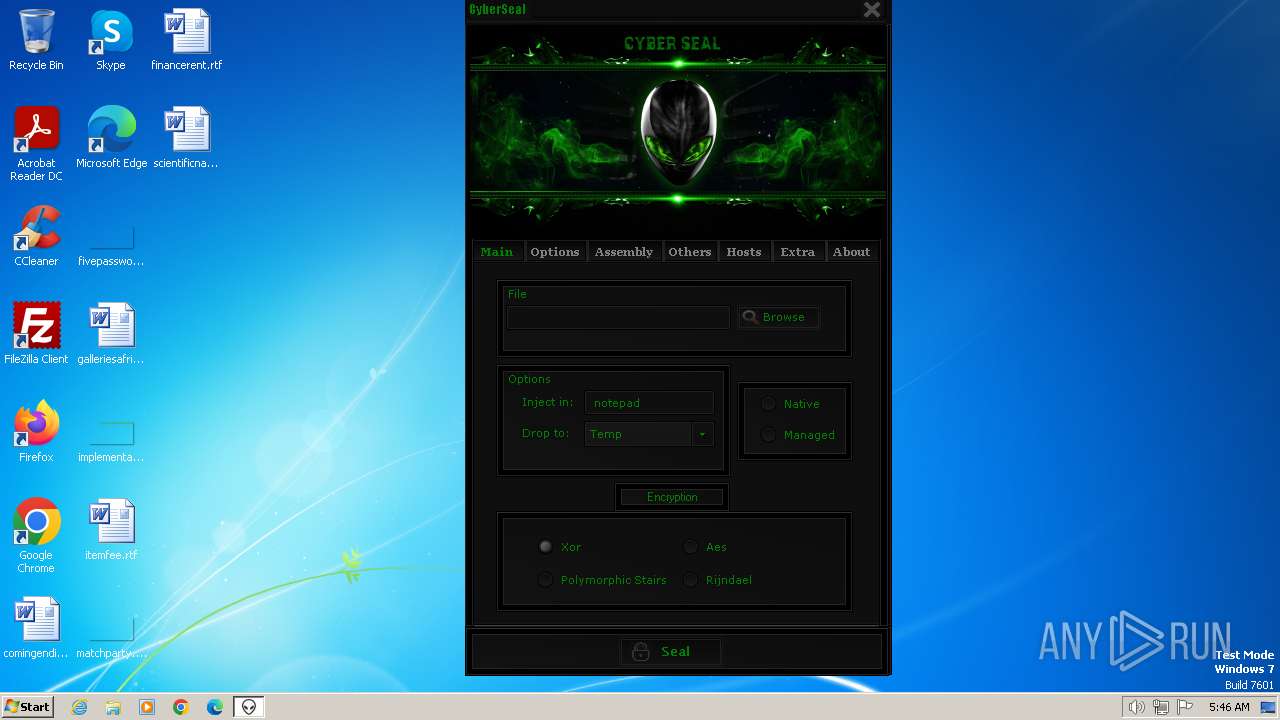
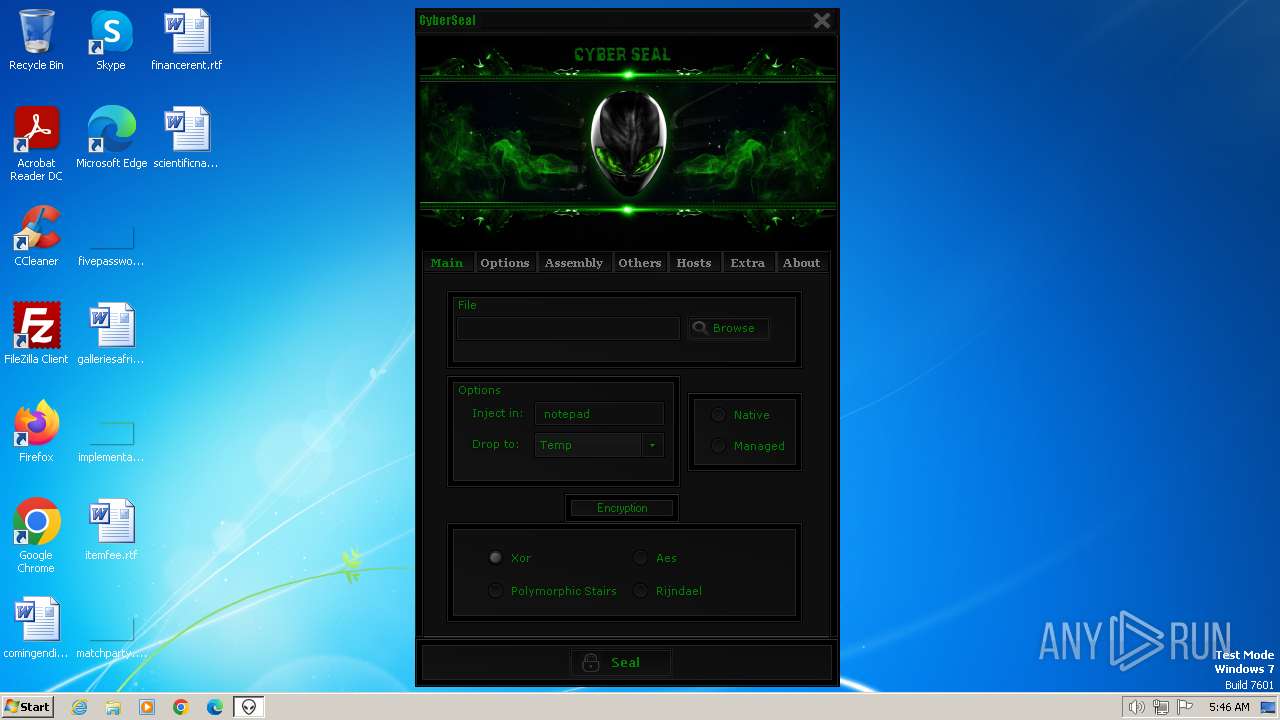
| 1864 | "C:\Users\admin\AppData\Roaming\Z46842481\CyberSeal Cracked by ImFred.exe" | C:\Users\admin\AppData\Roaming\Z46842481\CyberSeal Cracked by ImFred.exe | CyberSeal Crypter Cracked.exe | ||||||||||||
User: admin Company: CyberSeal Integrity Level: HIGH Description: CyberSeal Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Roaming\Z46842481\CyberSeal Cracked by ImFred.exe" | C:\Users\admin\AppData\Roaming\Z46842481\CyberSeal Cracked by ImFred.exe | — | CyberSeal Crypter Cracked.exe | |||||||||||
User: admin Company: CyberSeal Integrity Level: MEDIUM Description: CyberSeal Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 498
Read events
1 488
Write events
10
Delete events
0
Modification events
| (PID) Process: | (1776) CyberSeal Crypter Cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1776) CyberSeal Crypter Cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1776) CyberSeal Crypter Cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1776) CyberSeal Crypter Cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1732) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (1732) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E803000001000000010000004401000077000000DC0200005C0200000300000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF02000000FFFFFFFF4F00000028000000970000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
Executable files
3
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1776 | CyberSeal Crypter Cracked.exe | C:\Users\admin\AppData\Local\Temp\aut123B.tmp | binary | |
MD5:AE613A69800023F85930103DE711B292 | SHA256:D5DA17AC027BCBD6A2B0D645EF768E81AD6CABEB4FBA10C20272D9A4EF3CF09D | |||
| 1776 | CyberSeal Crypter Cracked.exe | C:\Users\admin\AppData\Local\Temp\aut12F8.tmp | binary | |
MD5:88D50FD30DEE79E71318E3EF501211E5 | SHA256:CA313DC7B992E15F4B59F8B7D8642731DABDB460095FA0153181FB4BA71889DA | |||
| 1864 | CyberSeal Cracked by ImFred.exe | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cyber1.dll | executable | |
MD5:23C63B4C32F9E562891A5F1B6C647B2C | SHA256:6840787F96CCFAEA140B1DC846715EC25666EA0E59857B8836BB1A55716F2C42 | |||
| 1776 | CyberSeal Crypter Cracked.exe | C:\Users\admin\AppData\Roaming\Z46842481\CyberSeal Cracked by ImFred.exe | executable | |
MD5:B09F0D68DE349F863B8F34DFC8656862 | SHA256:D4E82E5048623DC755ECF925515F26BF35D8D10EFE717D9B34D3432C240C6C28 | |||
| 1776 | CyberSeal Crypter Cracked.exe | C:\Users\admin\AppData\Roaming\Z46842481\cetrjnxwdvg.exe | executable | |
MD5:192D71847E028C310DC36641F3EA30DA | SHA256:FF12F3548A25589FF110EB62961BBF26ED2A13341F00FFA4E686FA92D869370E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1056 | cetrjnxwdvg.exe | GET | 404 | 162.240.81.18:80 | http://frilance.online/addbot.exe | unknown | html | 3.56 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1056 | cetrjnxwdvg.exe | 162.240.81.18:80 | frilance.online | UNIFIEDLAYER-AS-1 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
frilance.online |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | cetrjnxwdvg.exe | A Network Trojan was detected | ET HUNTING SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
1056 | cetrjnxwdvg.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |