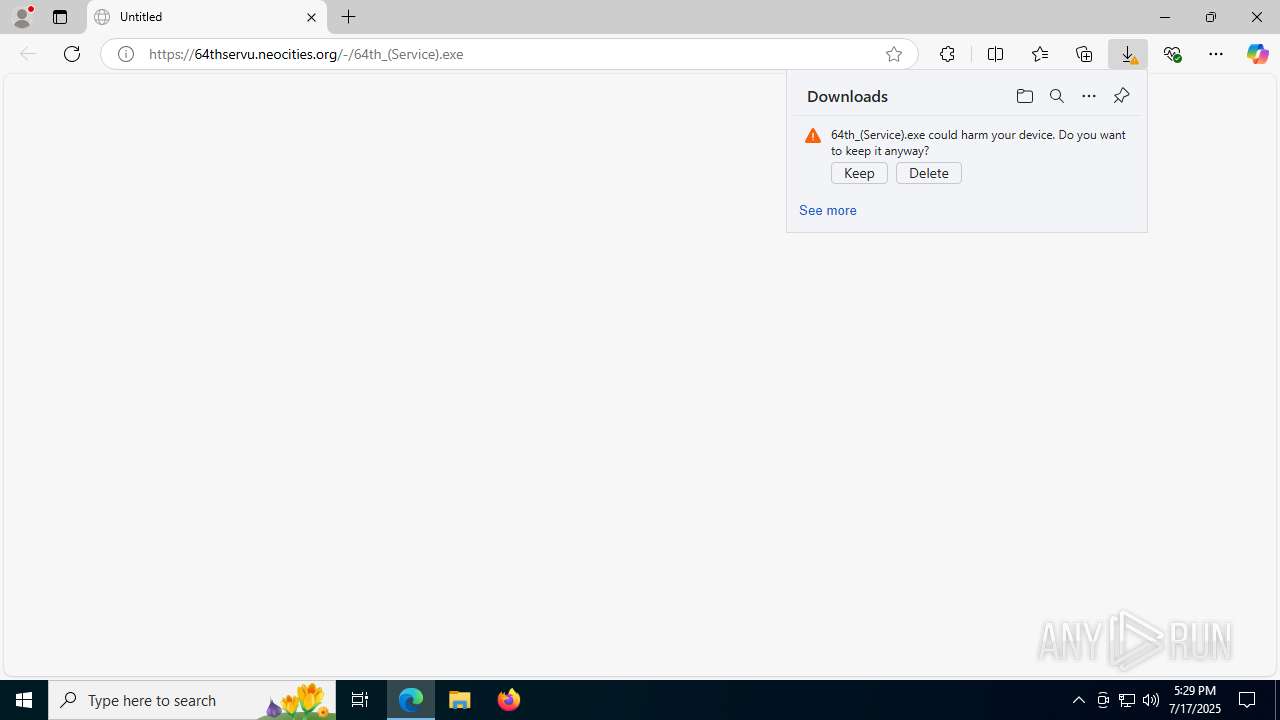
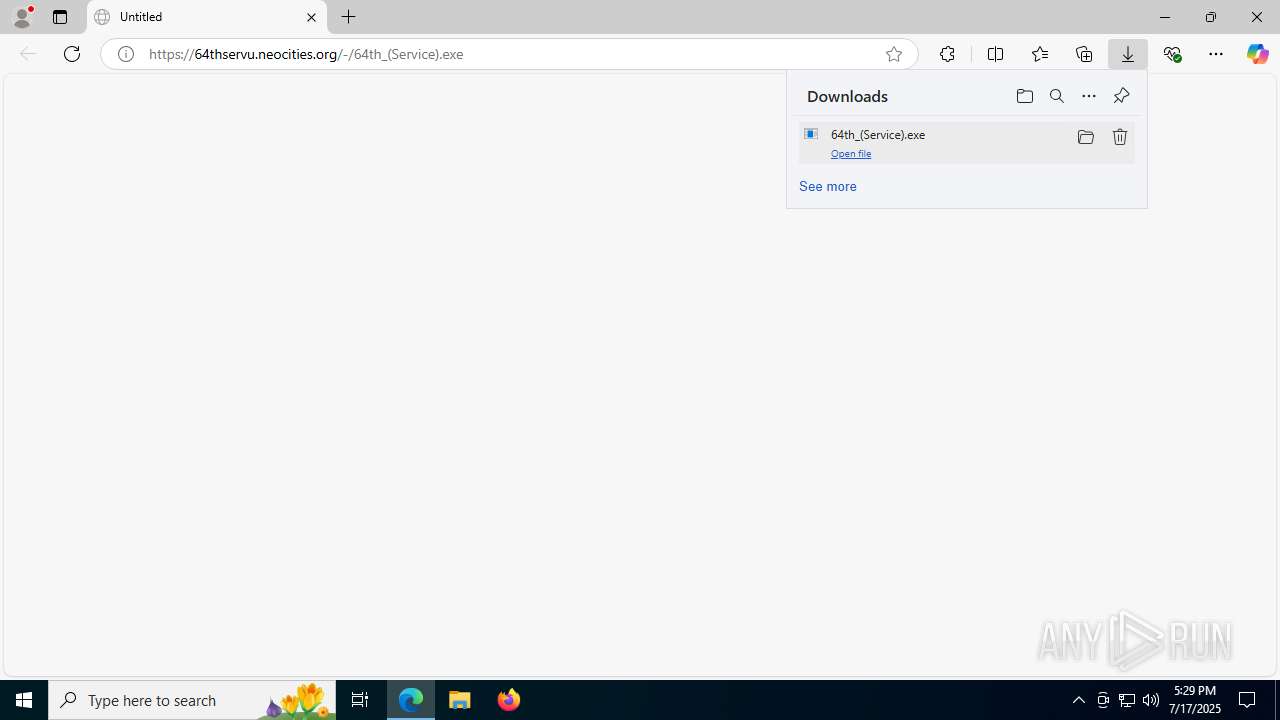
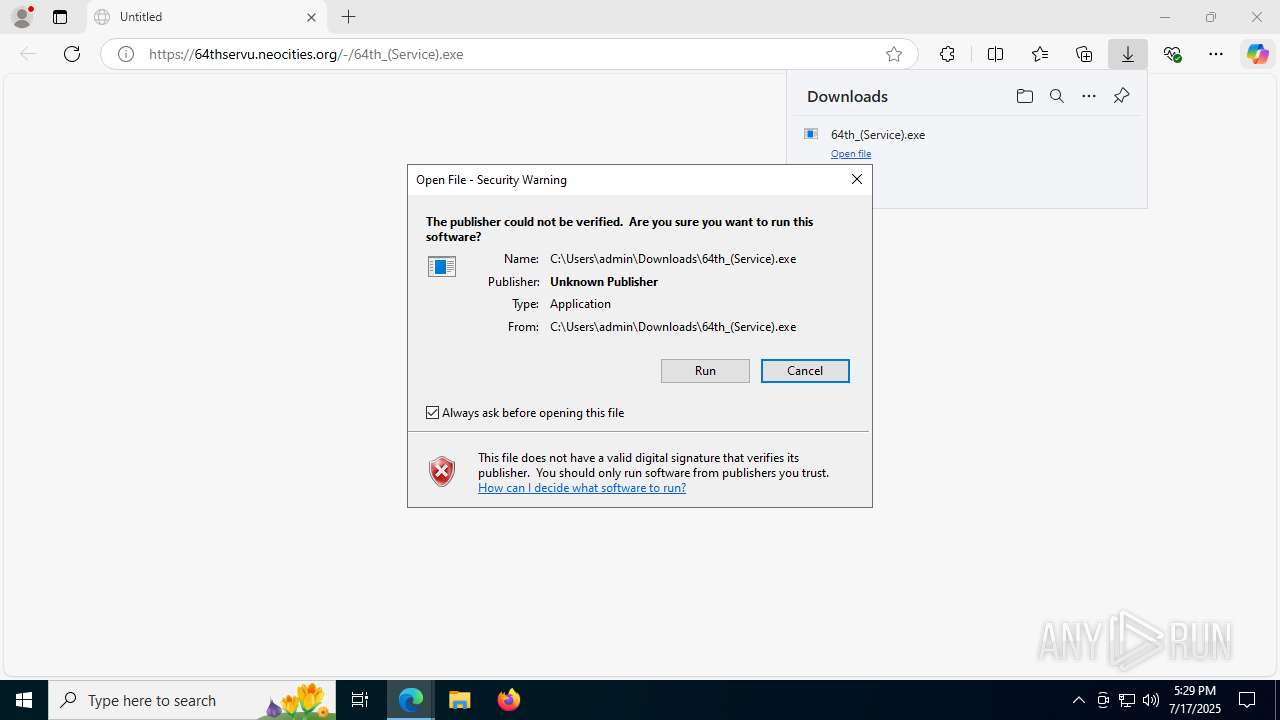
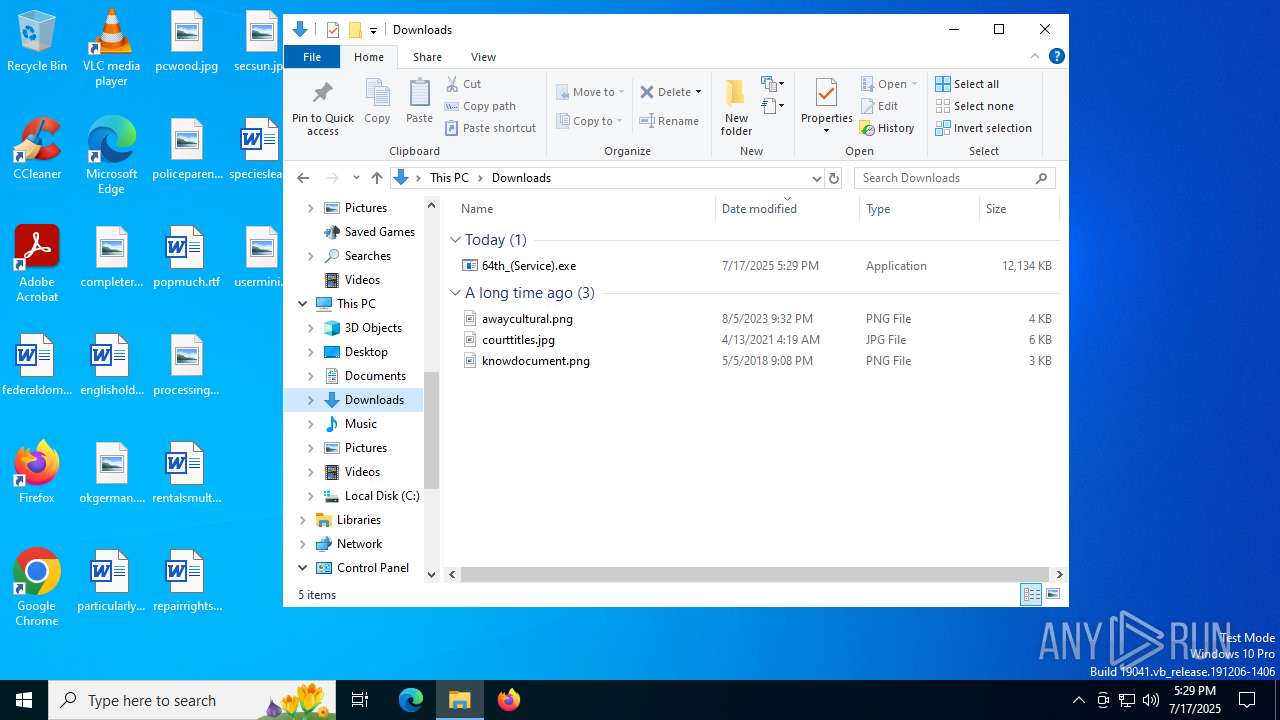
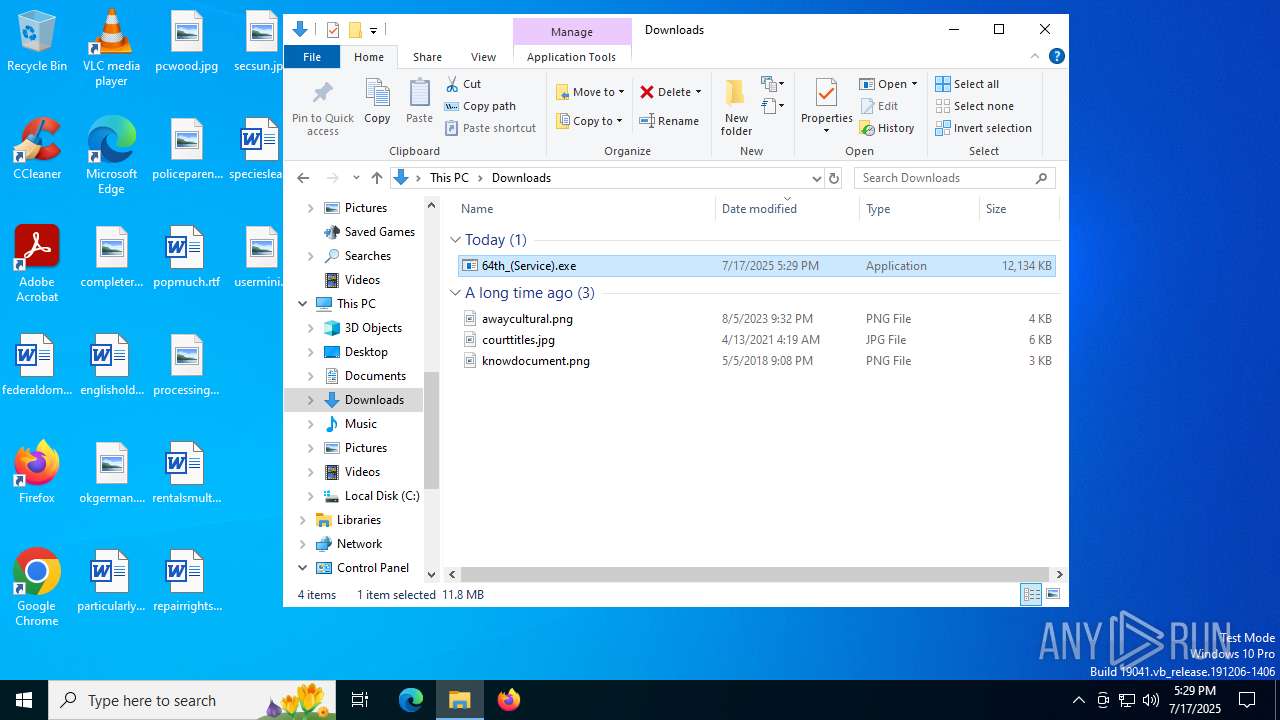
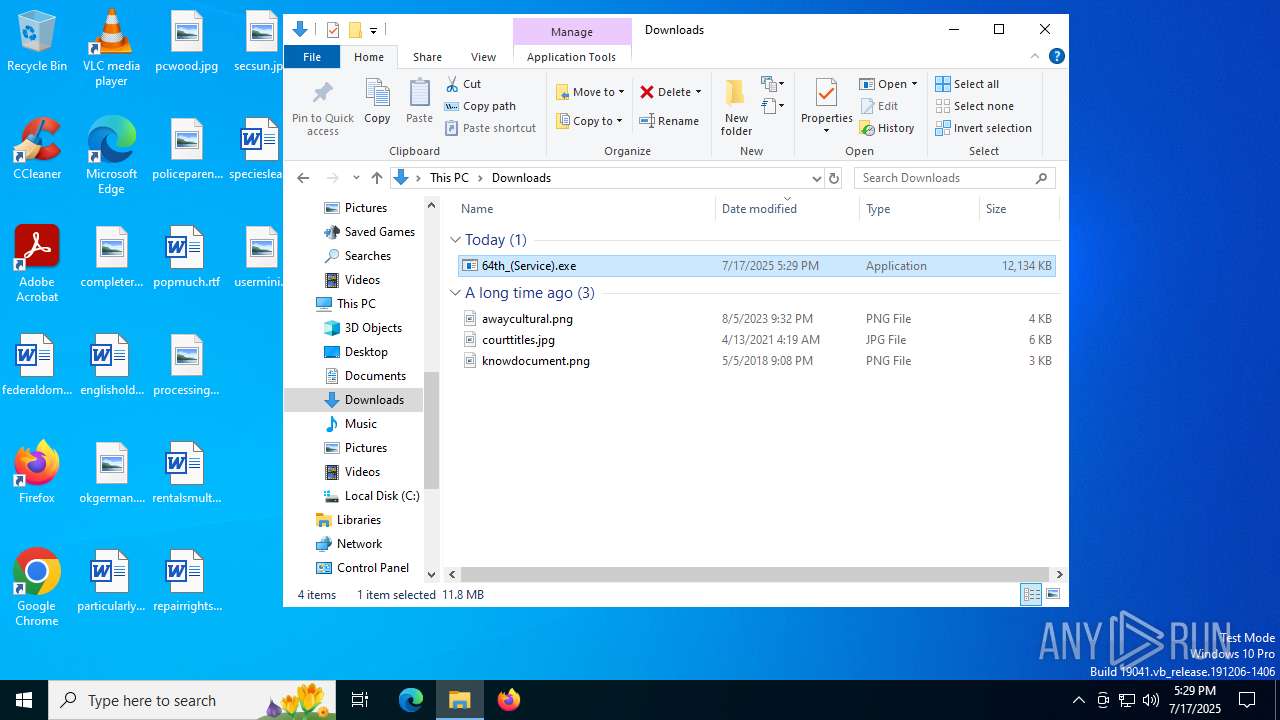
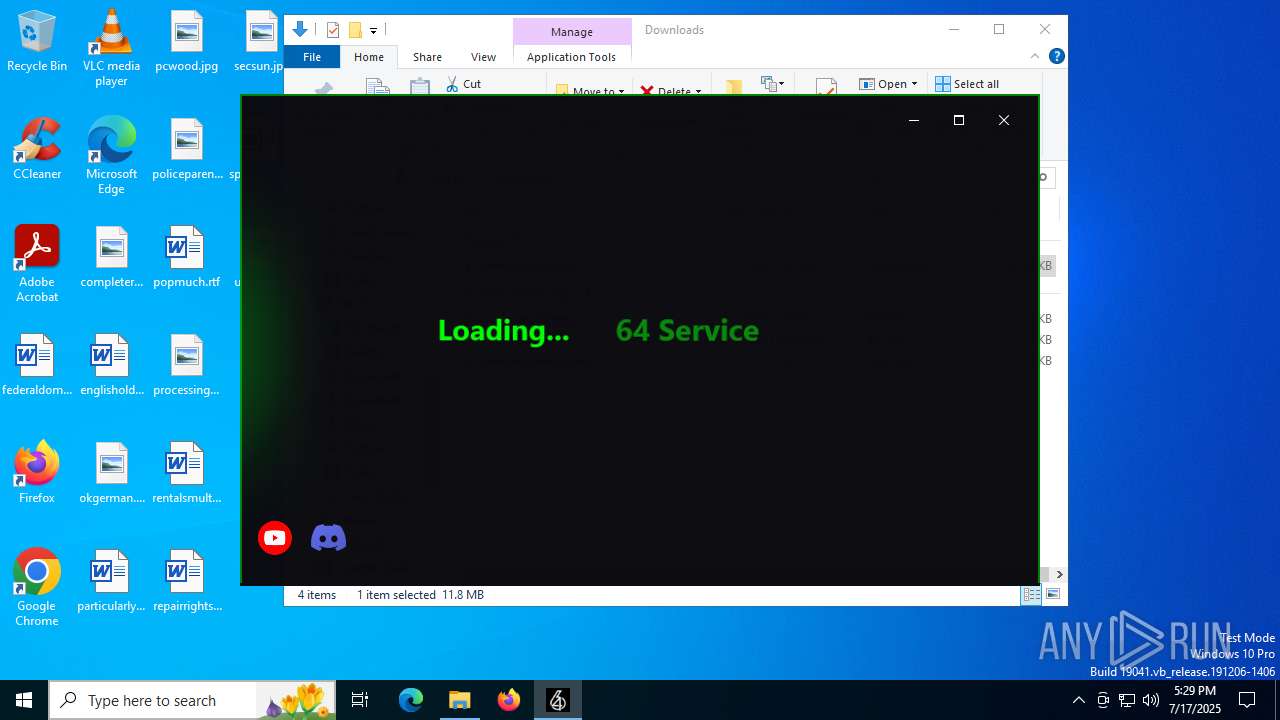
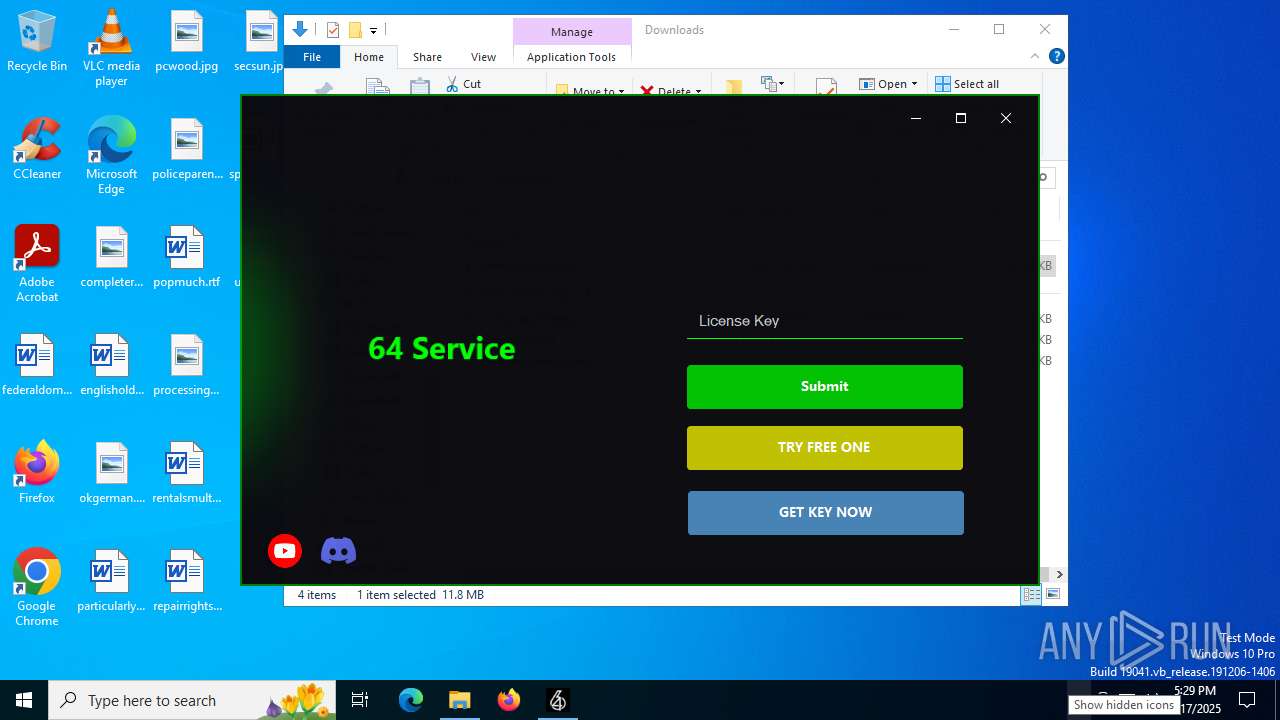
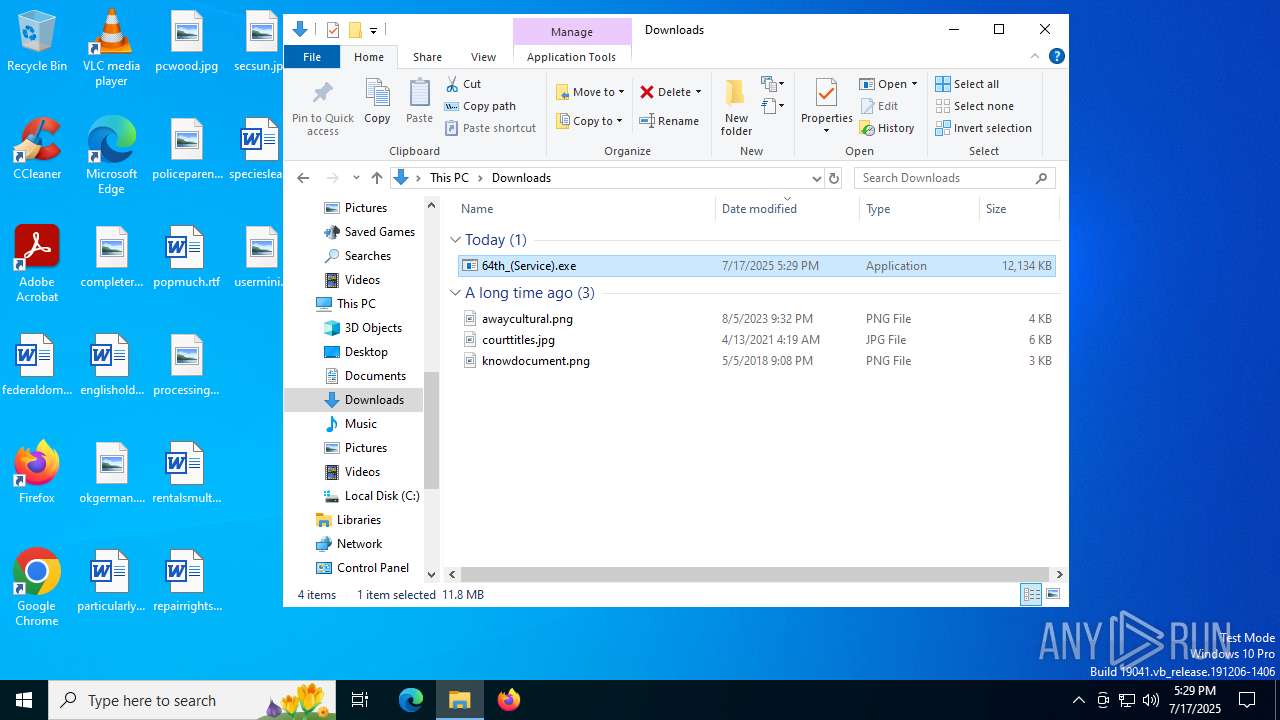
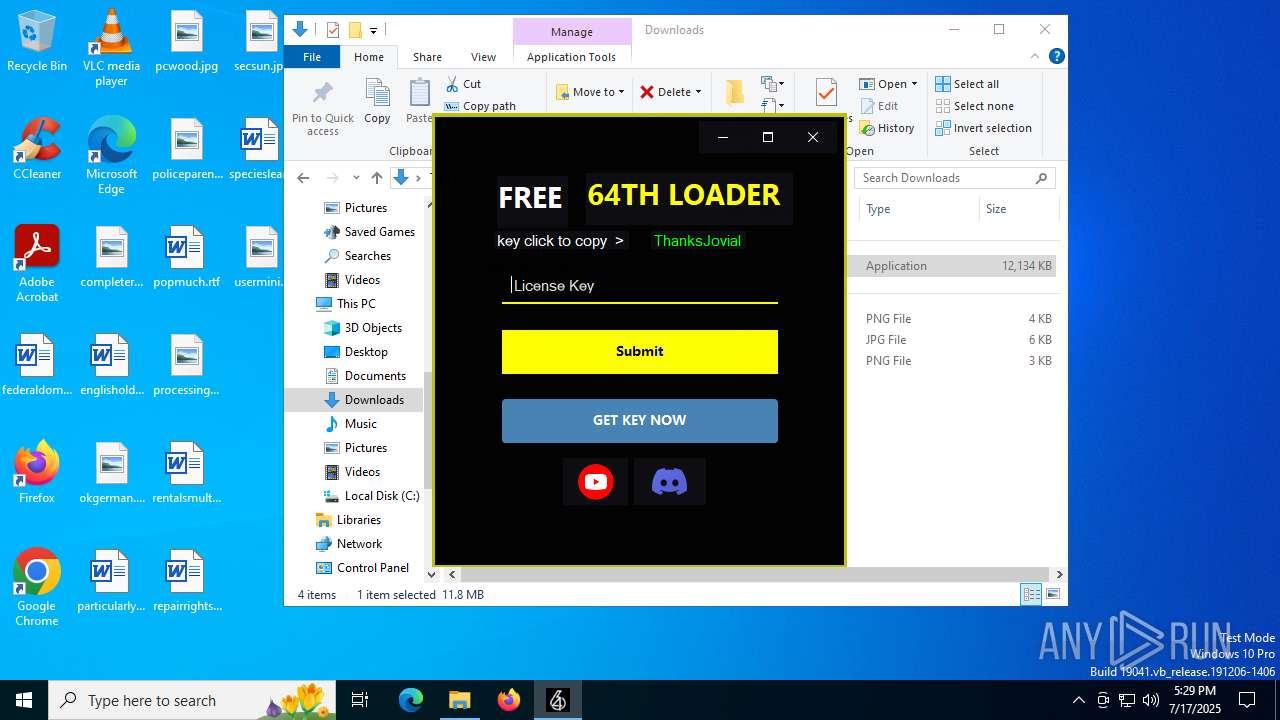
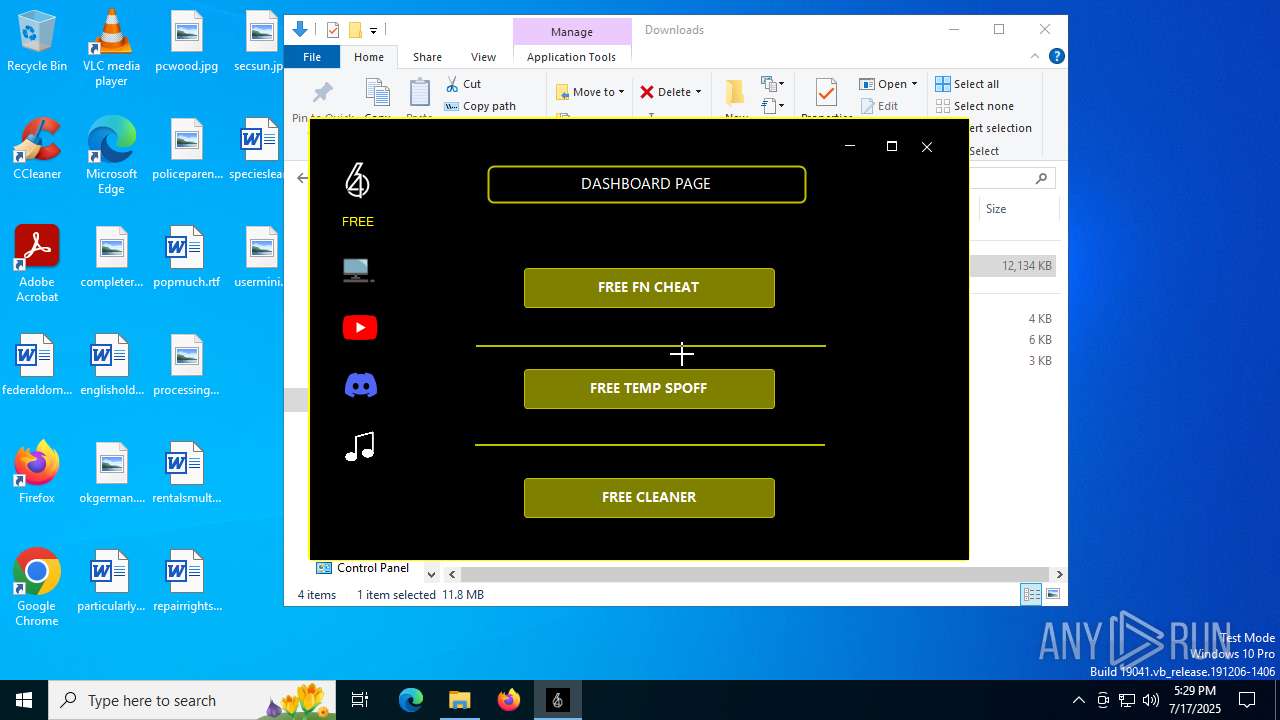
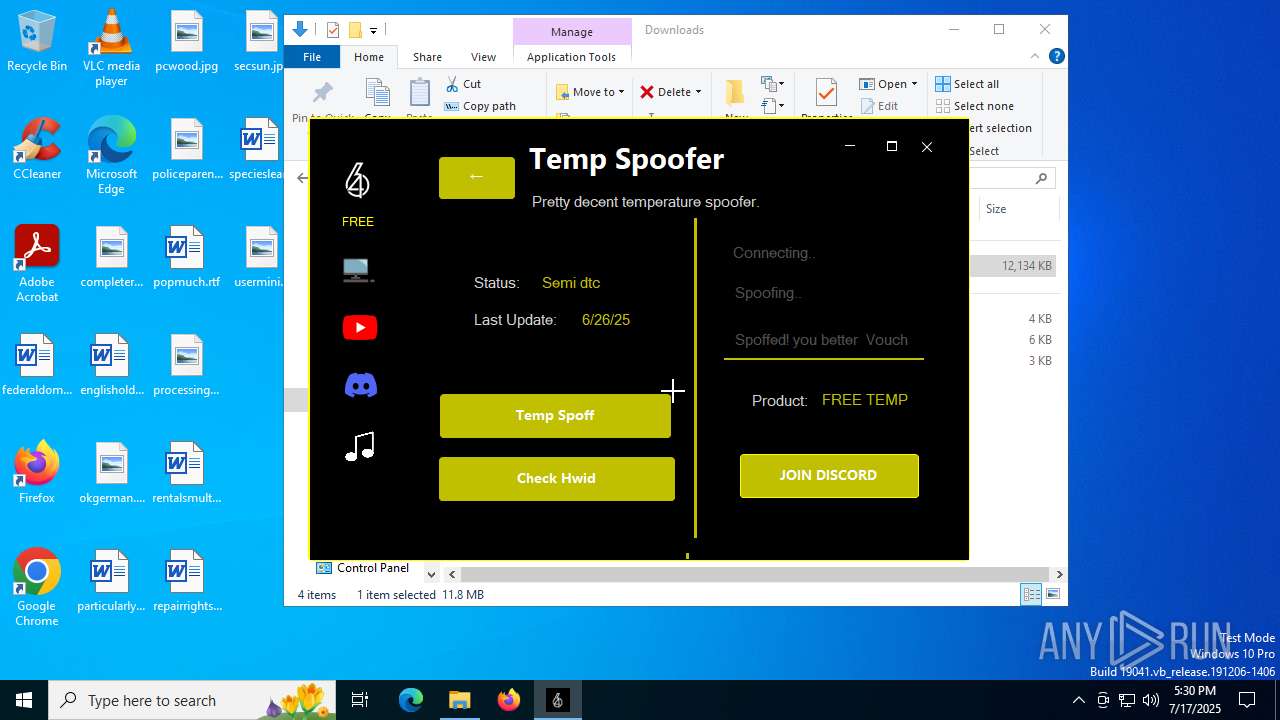
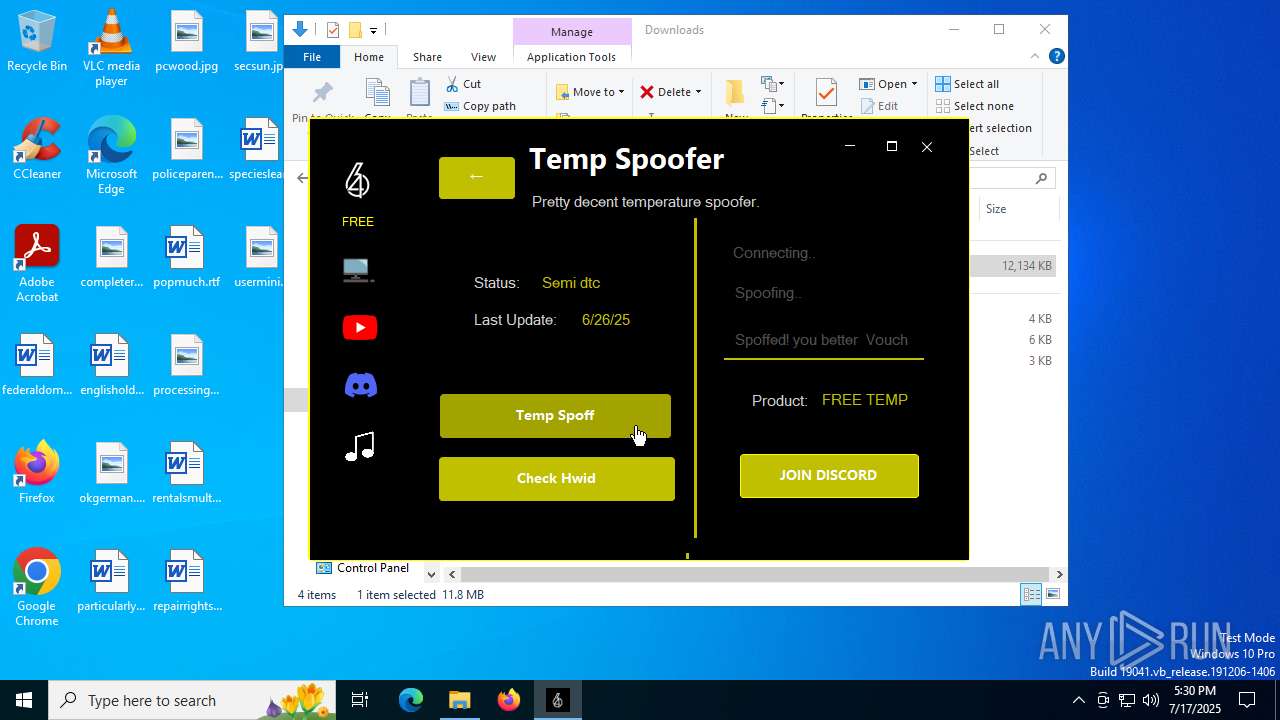
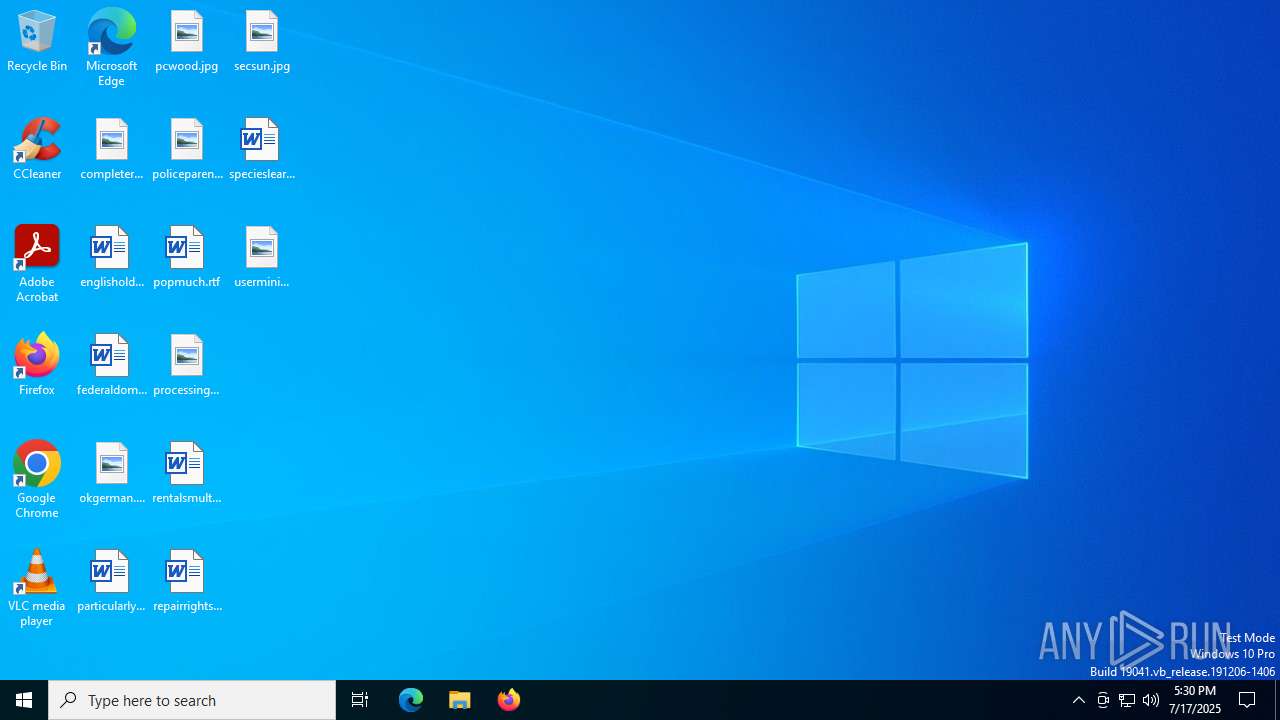
| URL: | https://64thservu.neocities.org/-/64th_(Service).exe |
| Full analysis: | https://app.any.run/tasks/988b86f1-8b3e-4fc1-aa63-4079f607c43d |
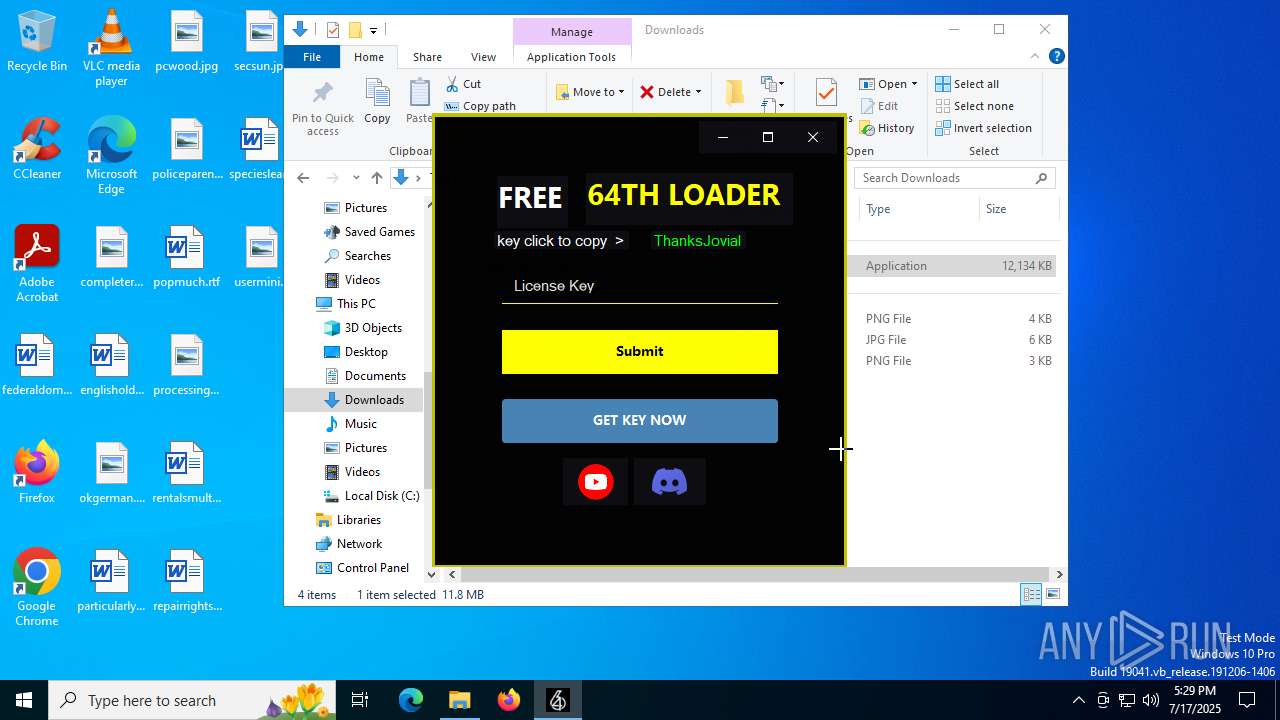
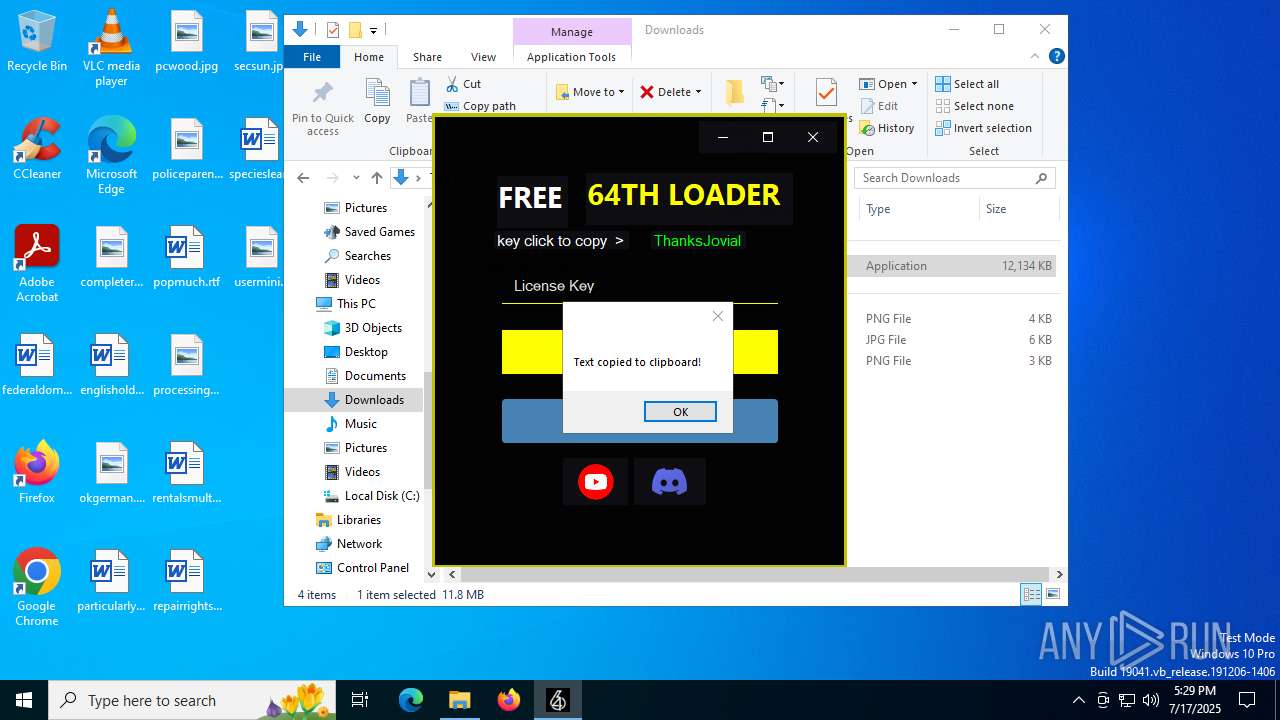
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
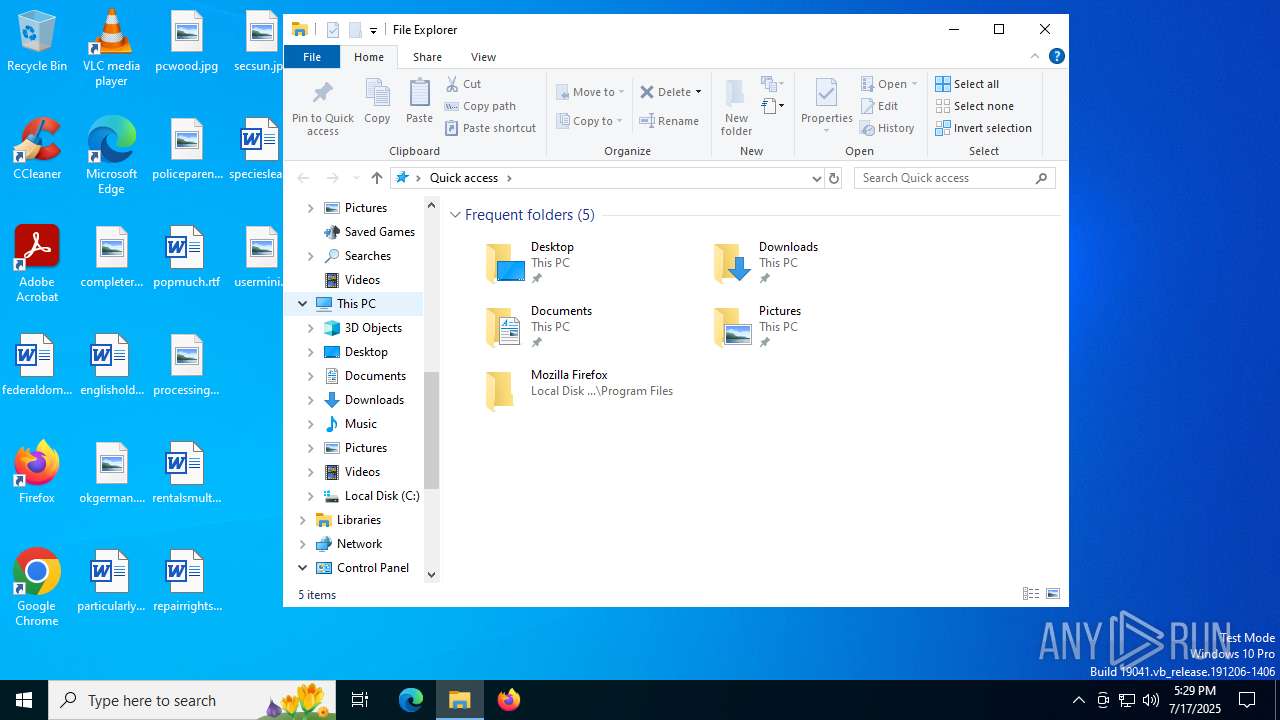
| Analysis date: | July 17, 2025, 17:29:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 123F5C5094339C38ECEEC3239ED1D30C |
| SHA1: | 7C949373DCDB61BA62520E77A2C22A7C13C71F4C |
| SHA256: | 22C52ED92839BA0D7E519E6F8F8E933A6BDE2F66577419D407B6A0216E88FF9E |
| SSDEEP: | 3:N89EAMLLAOXCTI3o5H:292L+H |
MALICIOUS
Changes Windows Defender settings
- 64th_(Service).exe (PID: 7684)
Adds path to the Windows Defender exclusion list
- 64th_(Service).exe (PID: 7684)
Run PowerShell with an invisible window
- powershell.exe (PID: 5032)
DCRAT has been found (auto)
- xgyrvixq.exe (PID: 2228)
Bypass execution policy to execute commands
- powershell.exe (PID: 7188)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1236)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7188)
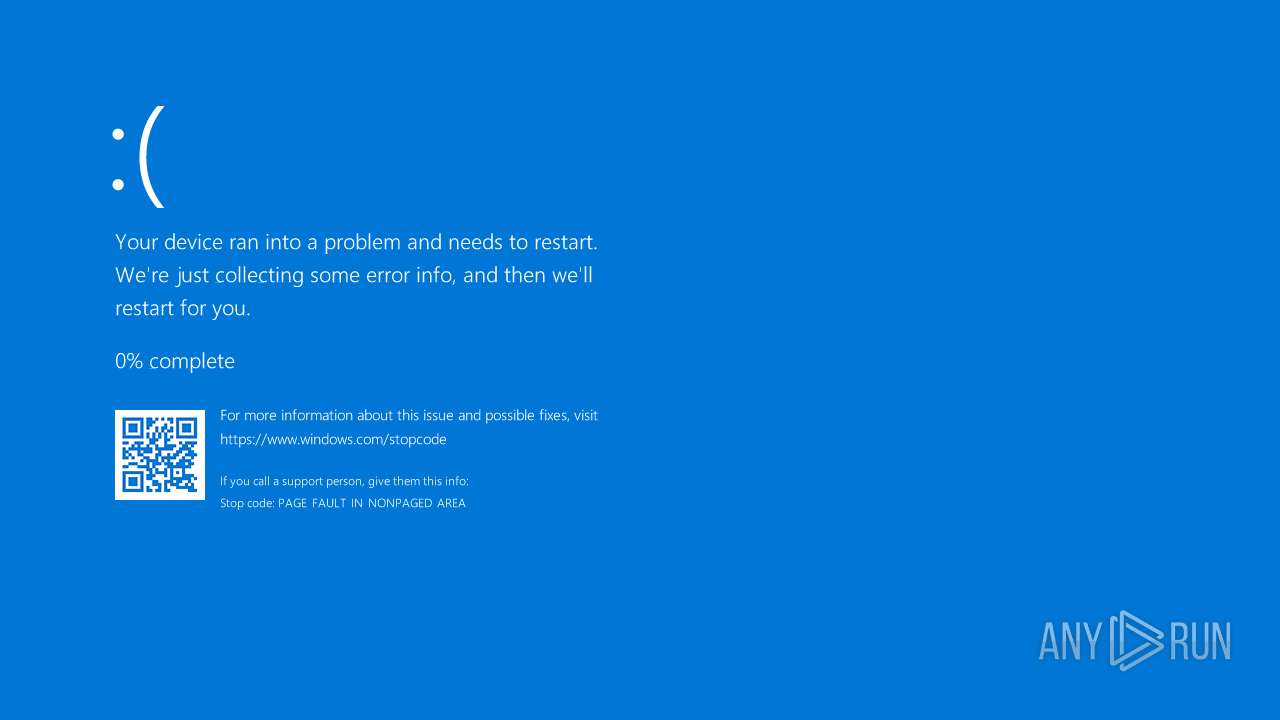
Vulnerable driver has been detected
- kp1q4gts.wly.exe (PID: 6180)
SUSPICIOUS
Reads the date of Windows installation
- 64th_(Service).exe (PID: 1160)
- 64th_(Service).exe (PID: 7684)
- xgyrvixq.exe (PID: 2228)
Reads security settings of Internet Explorer
- 64th_(Service).exe (PID: 1160)
- 64th_(Service).exe (PID: 7684)
- xgyrvixq.exe (PID: 2228)
Application launched itself
- 64th_(Service).exe (PID: 1160)
Script adds exclusion path to Windows Defender
- 64th_(Service).exe (PID: 7684)
Starts POWERSHELL.EXE for commands execution
- 64th_(Service).exe (PID: 7684)
- cmd.exe (PID: 1236)
The process bypasses the loading of PowerShell profile settings
- 64th_(Service).exe (PID: 7684)
- cmd.exe (PID: 1236)
Process drops legitimate windows executable
- xgyrvixq.exe (PID: 2228)
Executable content was dropped or overwritten
- xgyrvixq.exe (PID: 2228)
- 64th_(Service).exe (PID: 7684)
- powershell.exe (PID: 7188)
- kp1q4gts.wly.exe (PID: 6180)
Starts a Microsoft application from unusual location
- Microsoft.ServiceHub.exe (PID: 5288)
There is functionality for taking screenshot (YARA)
- xgyrvixq.exe (PID: 2228)
Executing commands from a ".bat" file
- Free shi.exe (PID: 3768)
Starts CMD.EXE for commands execution
- Free shi.exe (PID: 3768)
Manipulates environment variables
- powershell.exe (PID: 7188)
Executes script without checking the security policy
- powershell.exe (PID: 7188)
Probably download files using WebClient
- cmd.exe (PID: 1236)
Drops a system driver (possible attempt to evade defenses)
- powershell.exe (PID: 7188)
Creates or modifies Windows services
- kp1q4gts.wly.exe (PID: 6180)
Removes files via Powershell
- powershell.exe (PID: 7188)
INFO
Checks supported languages
- identity_helper.exe (PID: 7644)
- identity_helper.exe (PID: 8044)
- 64th_(Service).exe (PID: 1160)
- 64th_(Service).exe (PID: 7684)
- xgyrvixq.exe (PID: 2228)
- Microsoft.ServiceHub.exe (PID: 5288)
- Free shi.exe (PID: 3768)
- kp1q4gts.wly.exe (PID: 6180)
Application launched itself
- msedge.exe (PID: 5764)
- msedge.exe (PID: 8132)
Reads Environment values
- identity_helper.exe (PID: 7644)
- identity_helper.exe (PID: 8044)
- xgyrvixq.exe (PID: 2228)
- Free shi.exe (PID: 3768)
Executable content was dropped or overwritten
- msedge.exe (PID: 5764)
- msedge.exe (PID: 6264)
Reads the computer name
- identity_helper.exe (PID: 7644)
- identity_helper.exe (PID: 8044)
- 64th_(Service).exe (PID: 1160)
- 64th_(Service).exe (PID: 7684)
- Microsoft.ServiceHub.exe (PID: 5288)
- xgyrvixq.exe (PID: 2228)
- Free shi.exe (PID: 3768)
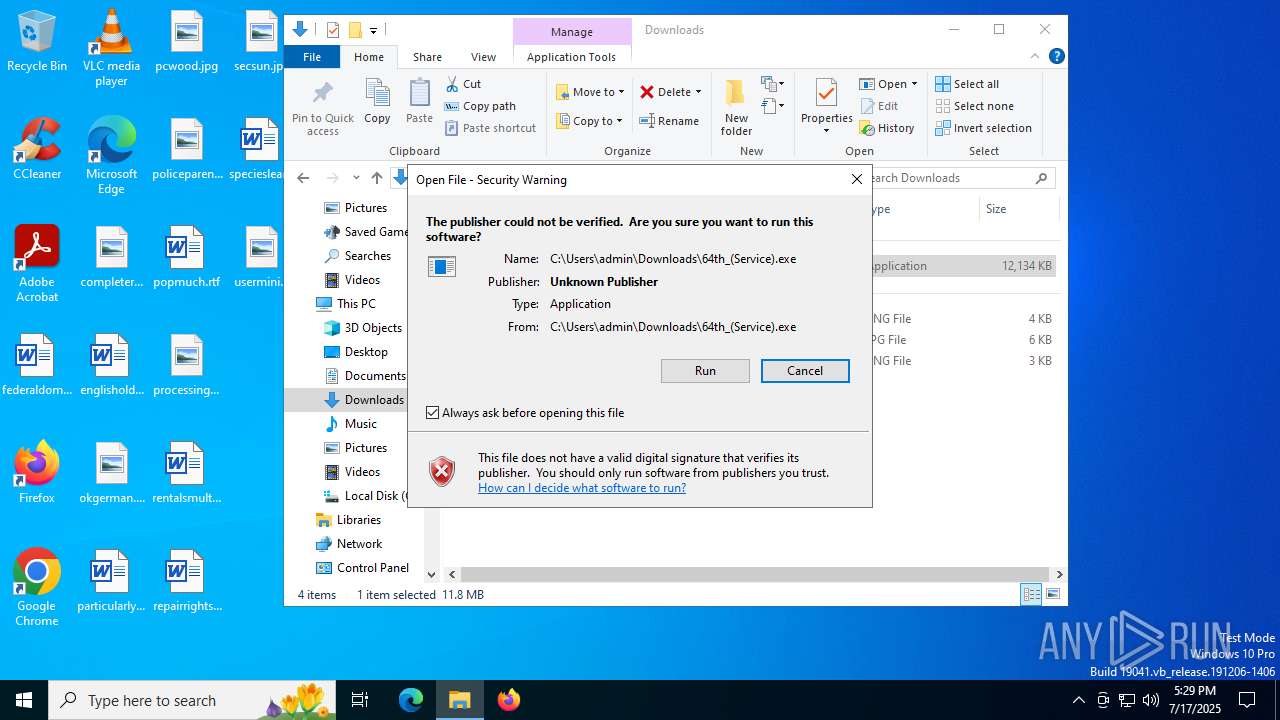
Manual execution by a user
- 64th_(Service).exe (PID: 1160)
Process checks computer location settings
- 64th_(Service).exe (PID: 1160)
- 64th_(Service).exe (PID: 7684)
- xgyrvixq.exe (PID: 2228)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5032)
Checks proxy server information
- 64th_(Service).exe (PID: 7684)
- xgyrvixq.exe (PID: 2228)
- Free shi.exe (PID: 3768)
- powershell.exe (PID: 7188)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5032)
Reads the software policy settings
- 64th_(Service).exe (PID: 7684)
- xgyrvixq.exe (PID: 2228)
- Free shi.exe (PID: 3768)
Reads the machine GUID from the registry
- 64th_(Service).exe (PID: 7684)
- Microsoft.ServiceHub.exe (PID: 5288)
- xgyrvixq.exe (PID: 2228)
- Free shi.exe (PID: 3768)
Creates files or folders in the user directory
- 64th_(Service).exe (PID: 7684)
Disables trace logs
- xgyrvixq.exe (PID: 2228)
- Free shi.exe (PID: 3768)
- powershell.exe (PID: 7188)
Create files in a temporary directory
- xgyrvixq.exe (PID: 2228)
- Microsoft.ServiceHub.exe (PID: 5288)
- Free shi.exe (PID: 3768)
- kp1q4gts.wly.exe (PID: 6180)
Confuser has been detected (YARA)
- xgyrvixq.exe (PID: 2228)
Creates files in the program directory
- xgyrvixq.exe (PID: 2228)
The sample compiled with english language support
- kp1q4gts.wly.exe (PID: 6180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
46
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4840,i,17119174676820781952,5623013554976089903,262144 --variations-seed-version --mojo-platform-channel-handle=4876 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1160 | "C:\Users\admin\Downloads\64th_(Service).exe" | C:\Users\admin\Downloads\64th_(Service).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5232,i,17119174676820781952,5623013554976089903,262144 --variations-seed-version --mojo-platform-channel-handle=5220 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1236 | C:\WINDOWS\system32\cmd.exe /c ""C:\$SysReset\Scratch\Free.bat"" | C:\Windows\System32\cmd.exe | — | Free shi.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4336f208,0x7ffc4336f214,0x7ffc4336f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1980 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 64th_(Service).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | "C:\WINDOWS\system32\xgyrvixq.exe" | C:\Windows\System32\xgyrvixq.exe | 64th_(Service).exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Version: 0 Modules
| |||||||||||||||
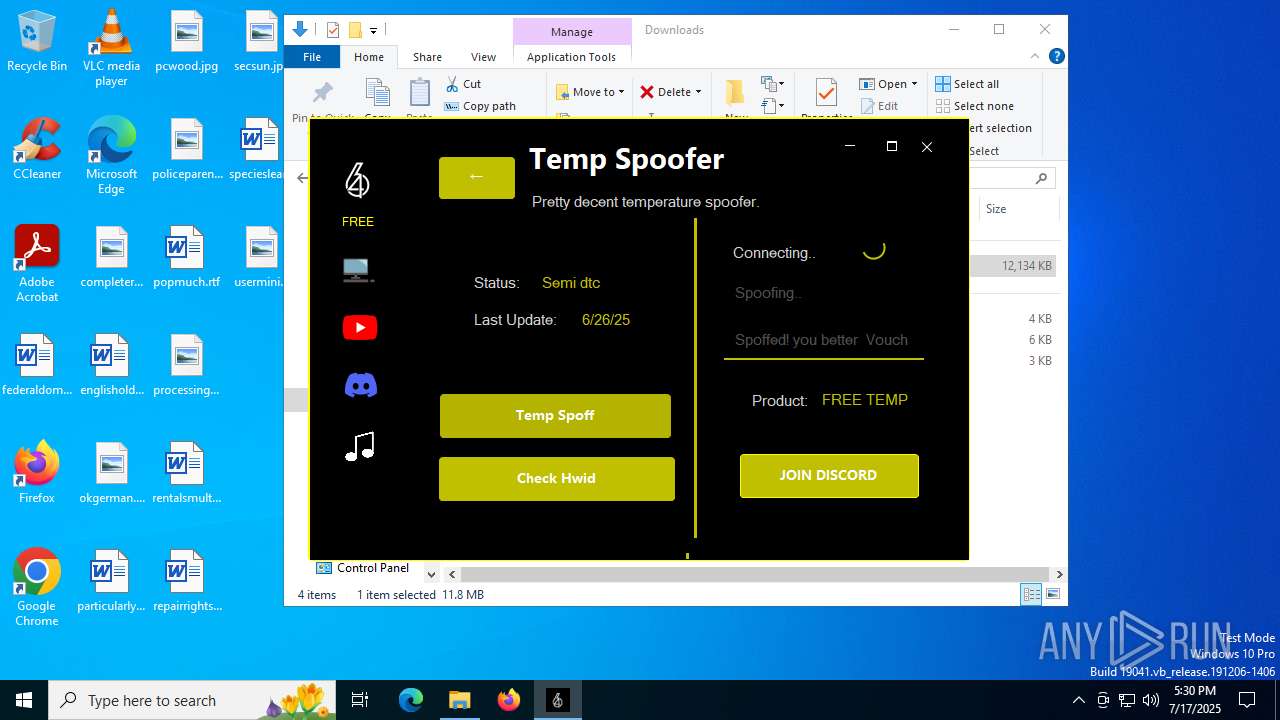
| 3768 | "C:\ProgramData\cloudware\Free shi.exe" | C:\ProgramData\cloudware\Free shi.exe | xgyrvixq.exe | ||||||||||||
User: admin Company: 64th spoffer & cheat Integrity Level: HIGH Description: 64th Services Version: 1.0.0.0 Modules
| |||||||||||||||
| 3896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3644,i,10066609542872644312,5122307358378666734,262144 --variations-seed-version --mojo-platform-channel-handle=3656 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
25 769
Read events
25 719
Write events
50
Delete events
0
Modification events
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0973C9A1B9982F00 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525096 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {488FBAB8-302D-4A30-991D-EEFBAD0F79BC} | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3811E7A1B9982F00 | |||
| (PID) Process: | (5764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
10
Suspicious files
73
Text files
86
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d23f.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d24f.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d24f.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d24f.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d23f.TMP | — | |
MD5:— | SHA256:— | |||
| 5764 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
77
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6264 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:F5YtcR_wpQPzxpo4vuSz_qBF9s2RJrRMv5QaO6GO2bM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7116 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5764 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
5764 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAjUv1pSnHJZl%2BD2xSZJXS8%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7684 | 64th_(Service).exe | GET | 200 | 104.18.21.213:80 | http://r10.c.lencr.org/49.crl | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
888 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2432 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6264 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6264 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6264 | msedge.exe | 23.143.32.13:443 | 64thservu.neocities.org | — | US | whitelisted |
6264 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6264 | msedge.exe | 2.23.227.211:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
64thservu.neocities.org |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |
xgyrvixq.exe | test |