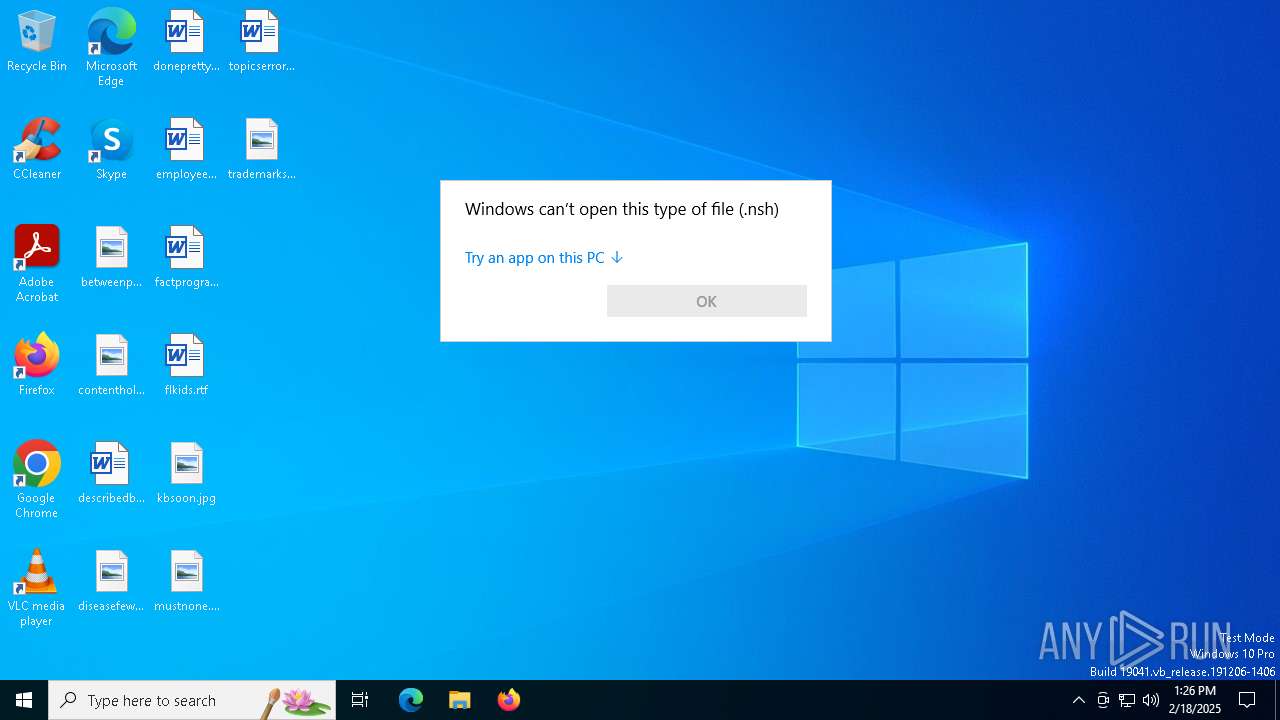
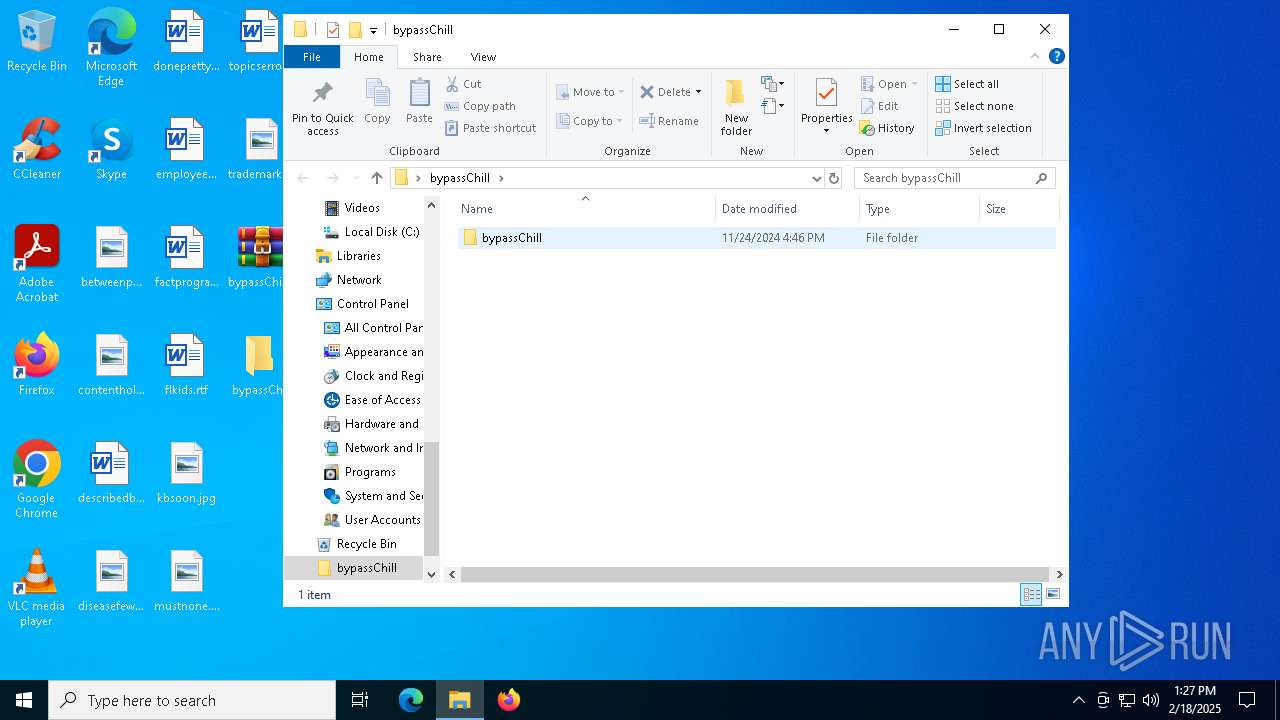
| File name: | Startup (1).nsh |
| Full analysis: | https://app.any.run/tasks/5dc1c643-78c8-4edd-bde7-1086a1230641 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2025, 13:26:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 7D2F3F41E5ED9239F64A012EAB3452A3 |
| SHA1: | 93099500A0B03FFE4471F22289C89200F49562EB |
| SHA256: | 22C1B8DE7962BC1AEE0960DEEE17893CF83EEC6F2AACF31D291A9F4D7BE10B26 |
| SSDEEP: | 6:BZhxVTgjBOZhPy8ZIqPy8Z/QjZrySuvBZTeNJMuN5A8Z/JMuNP:rFLBvQtuxvSbPNZPNP |
MALICIOUS
No malicious indicators.SUSPICIOUS
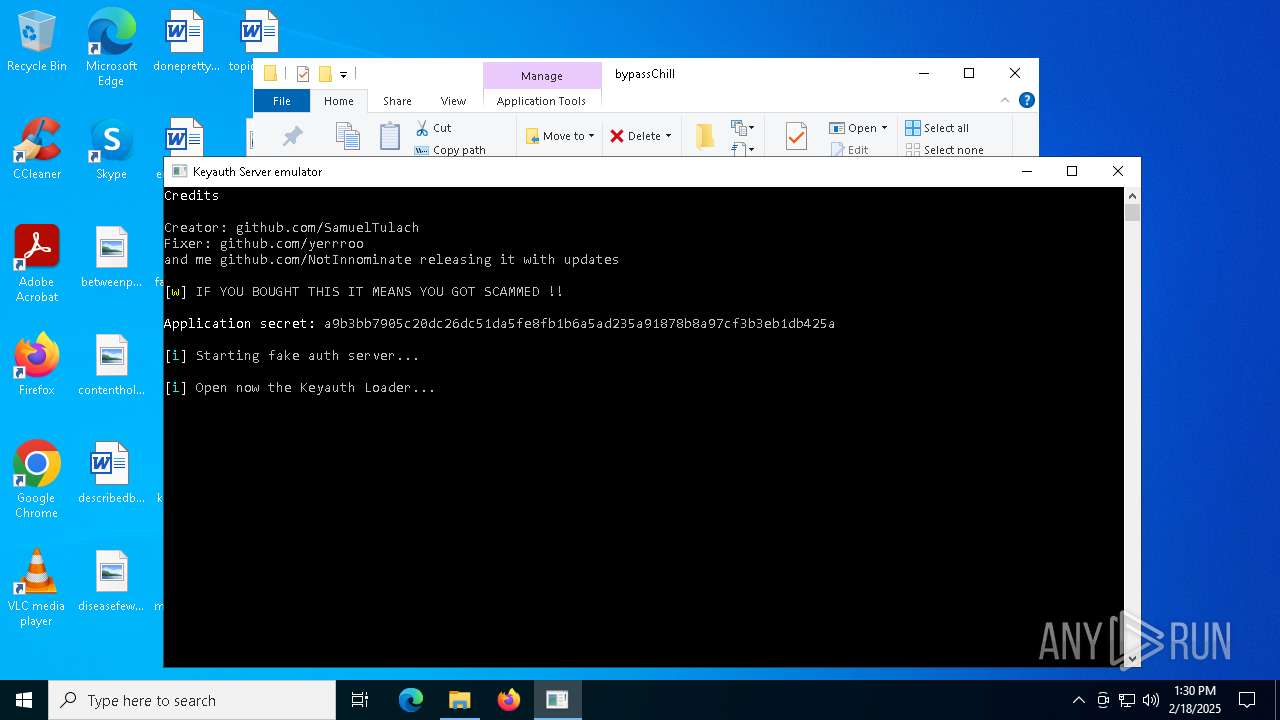
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 6328)
- rundll32.exe (PID: 1752)
Application launched itself
- rundll32.exe (PID: 6328)
- rundll32.exe (PID: 1752)
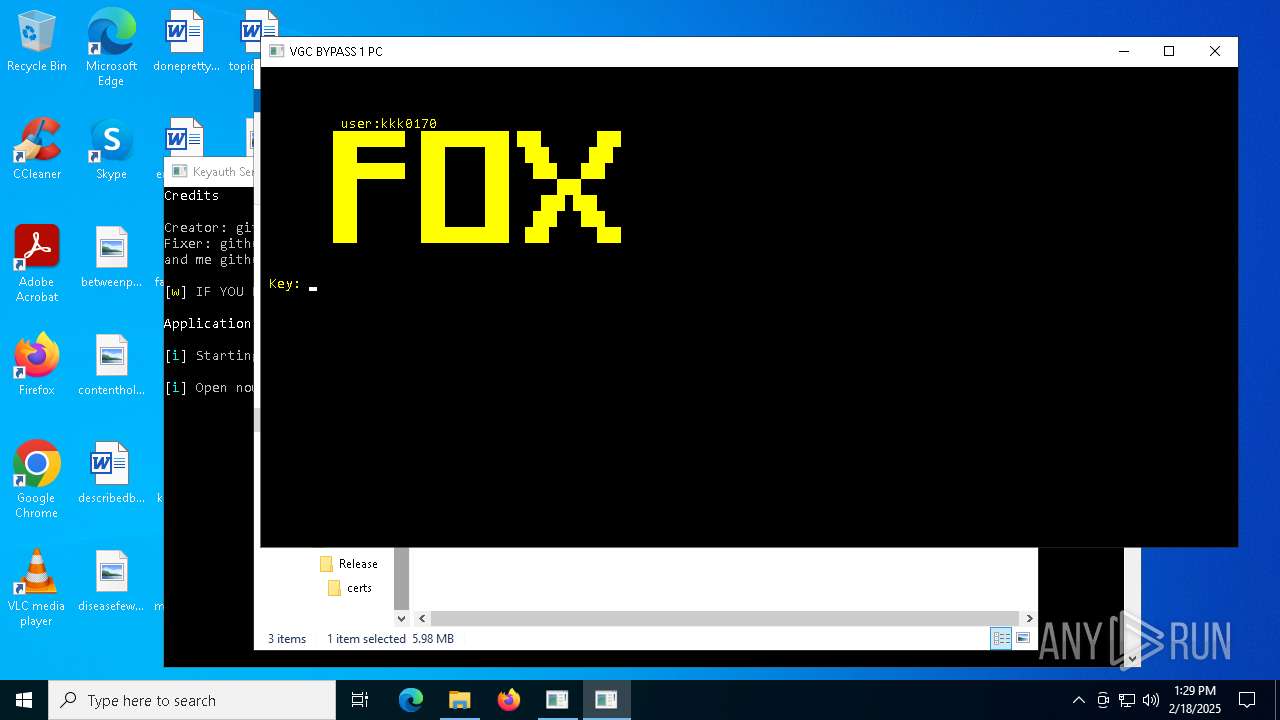
Reads the BIOS version
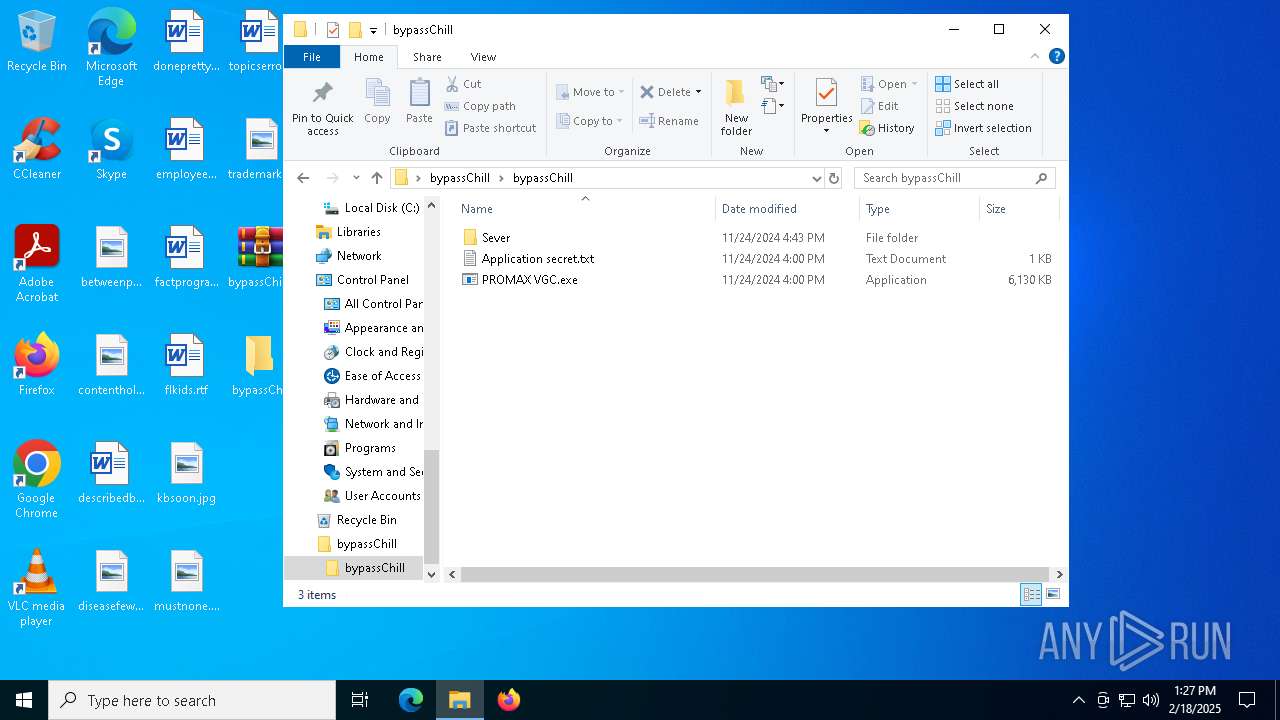
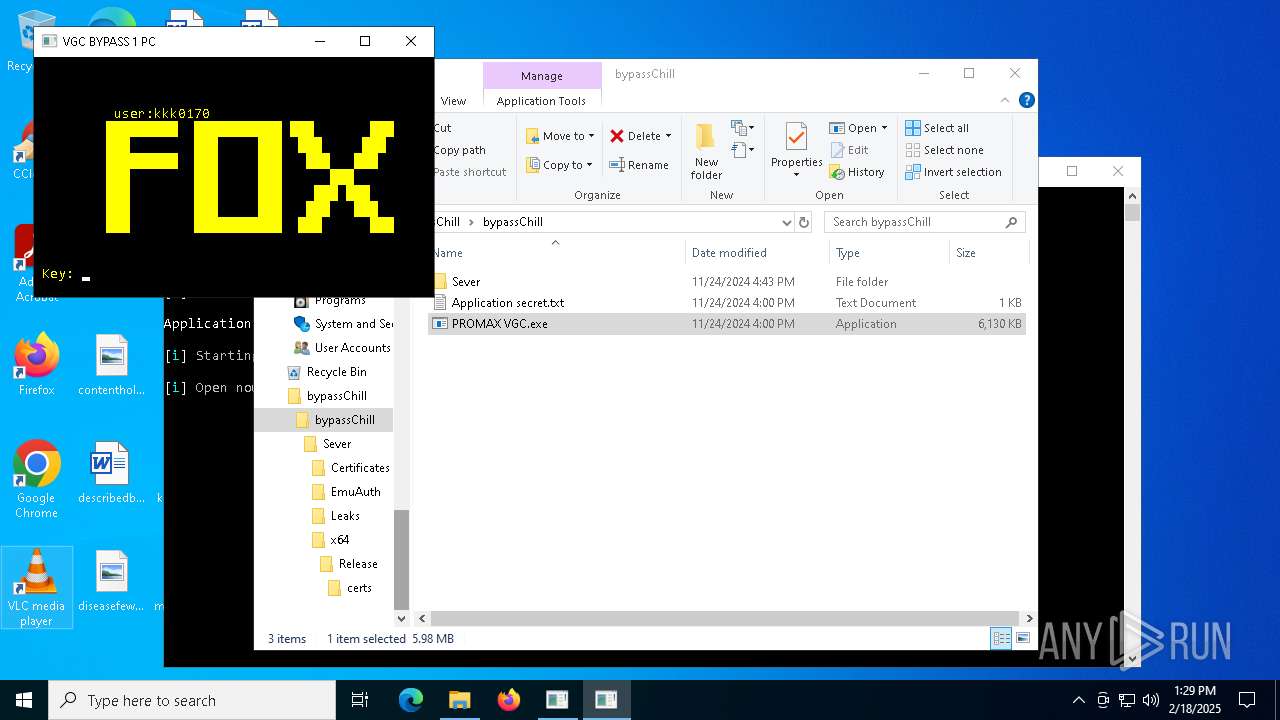
- PROMAX VGC.exe (PID: 2996)
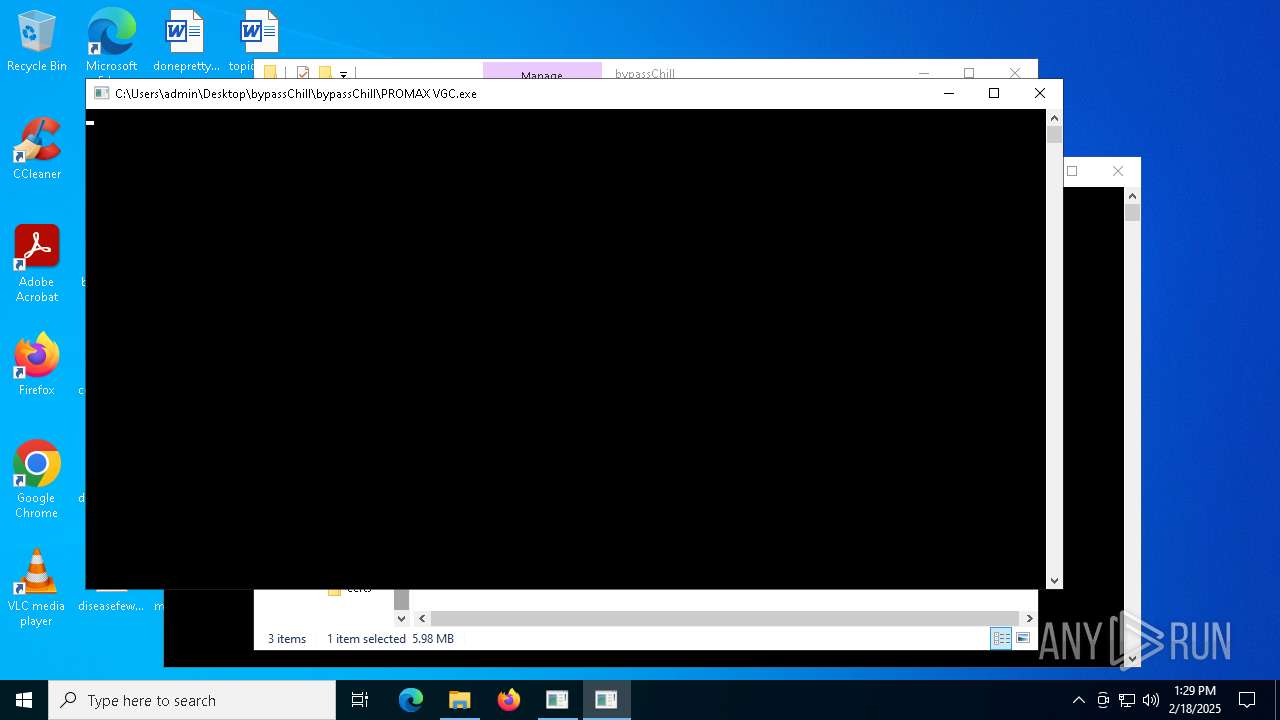
Starts CMD.EXE for commands execution
- PROMAX VGC.exe (PID: 2996)
- PROMAX VGC.exe (PID: 5212)
INFO
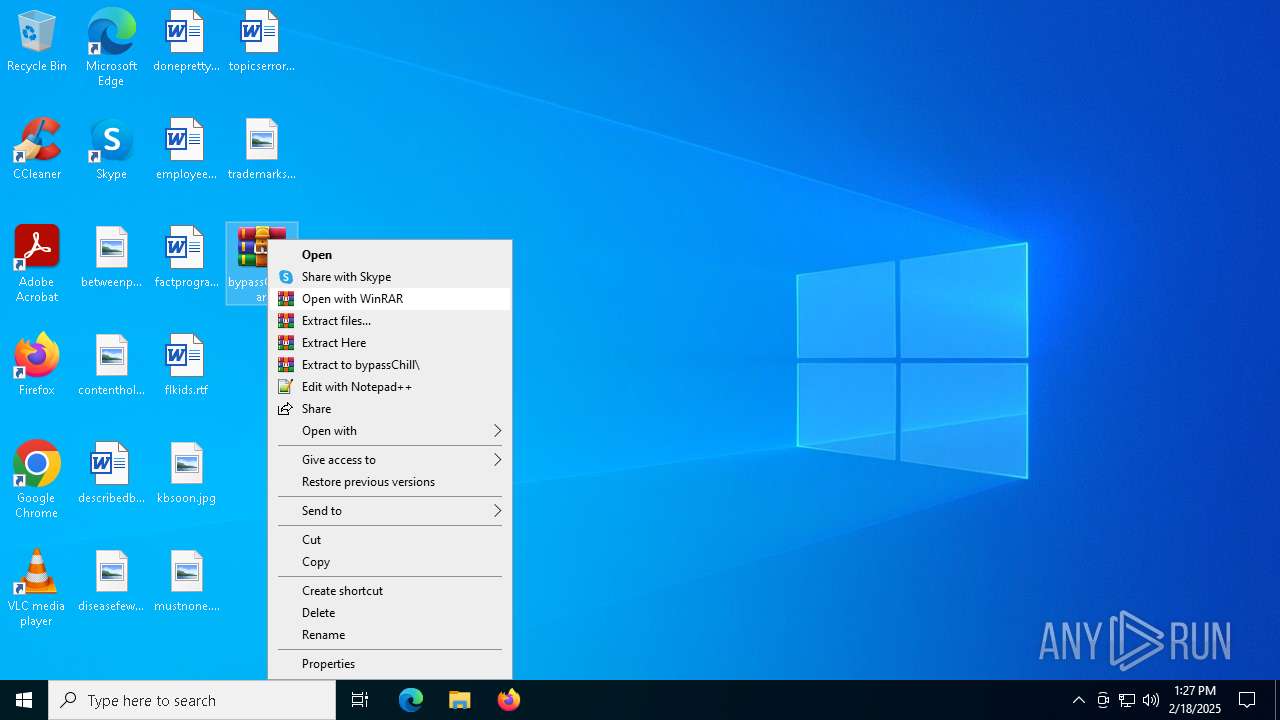
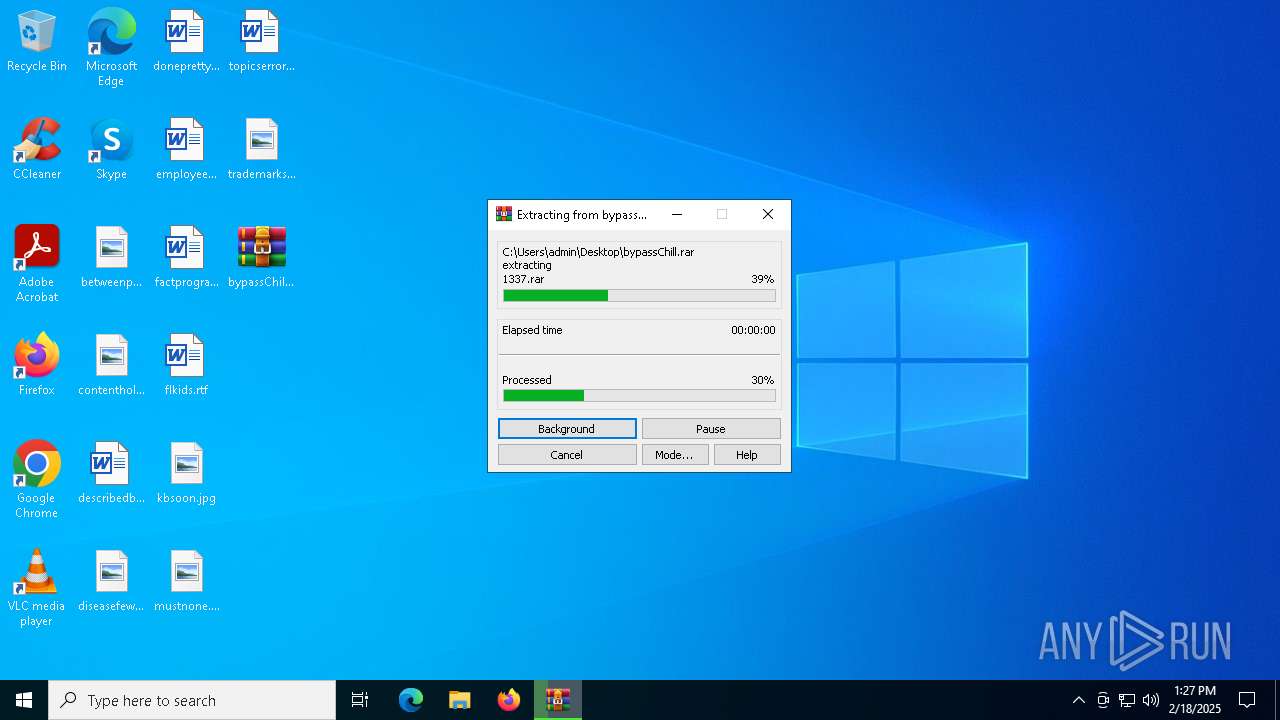
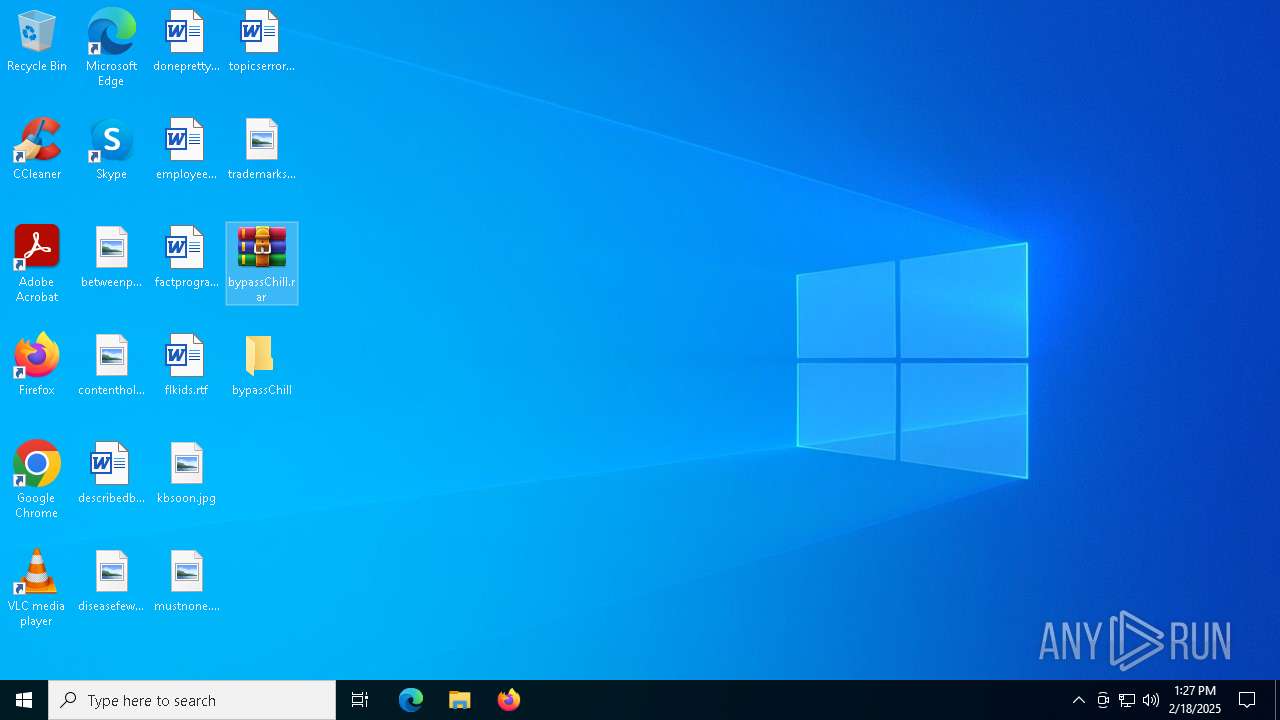
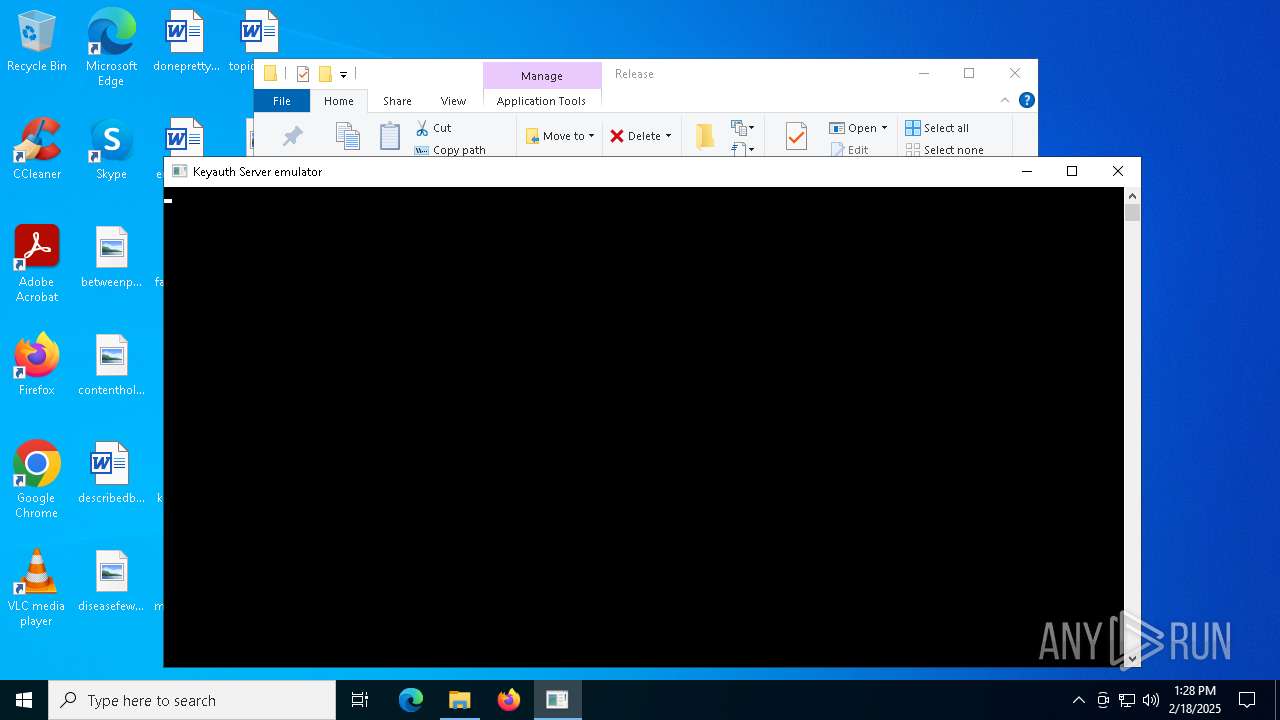
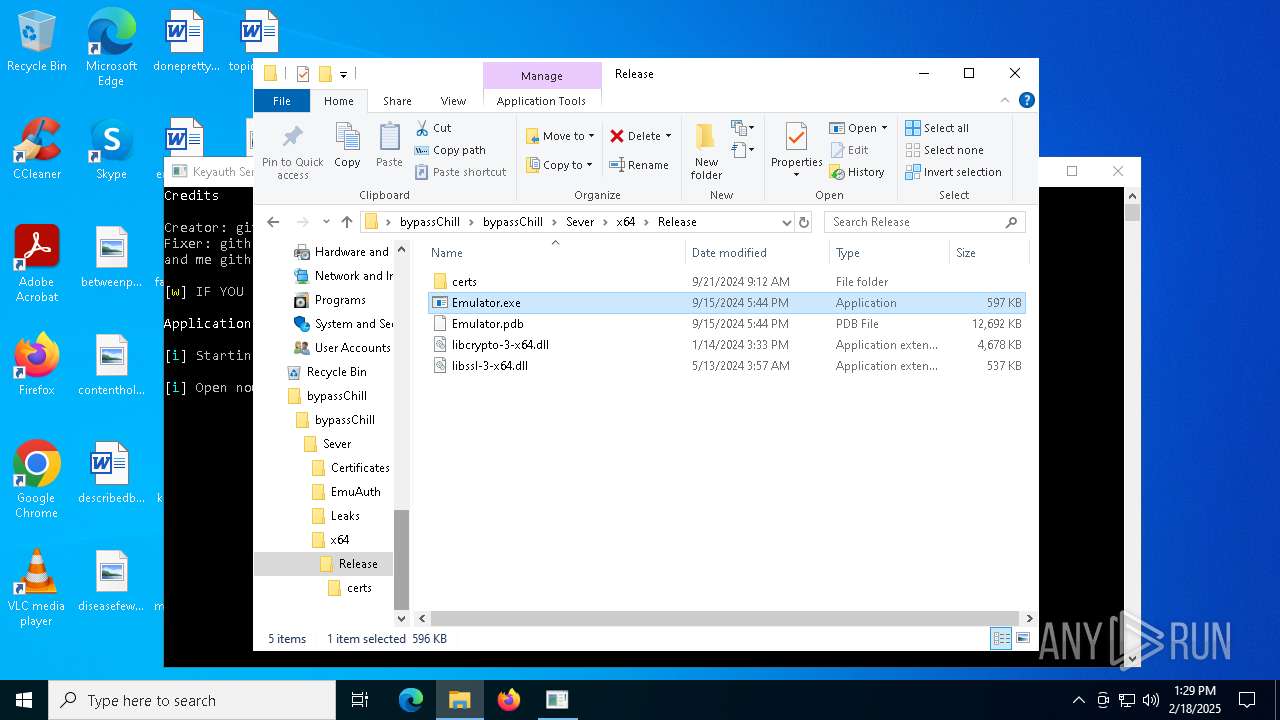
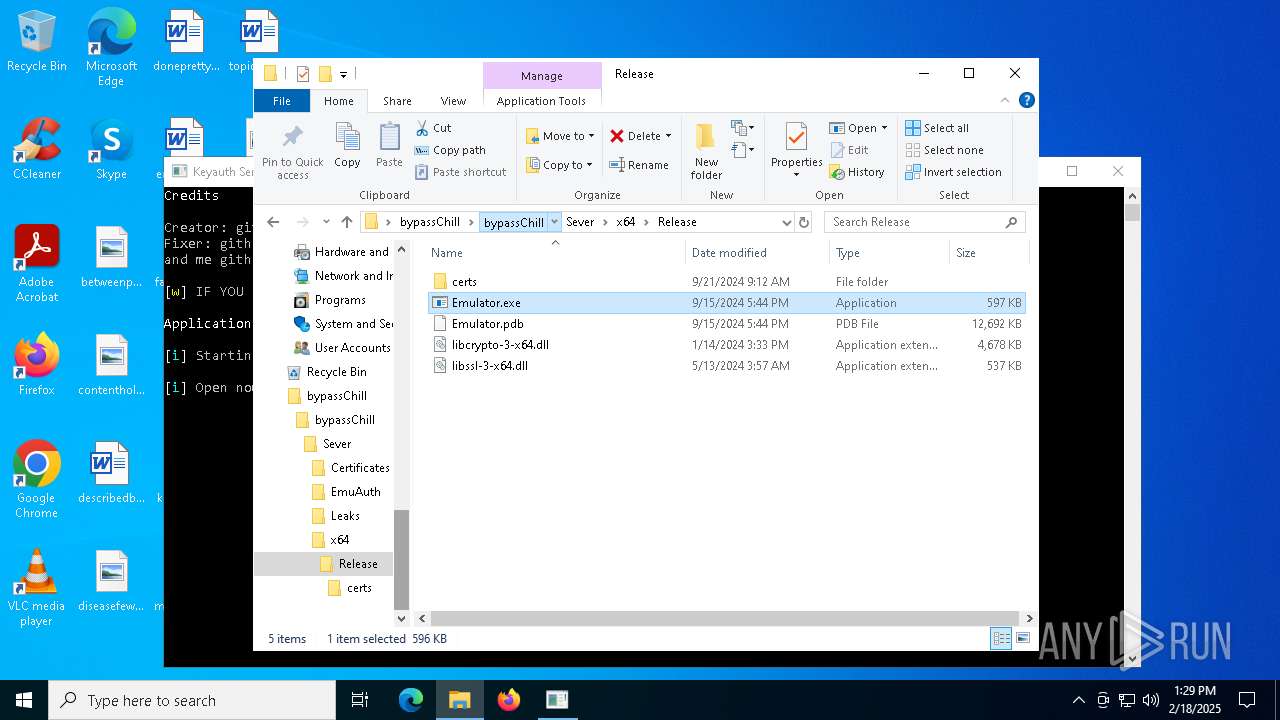
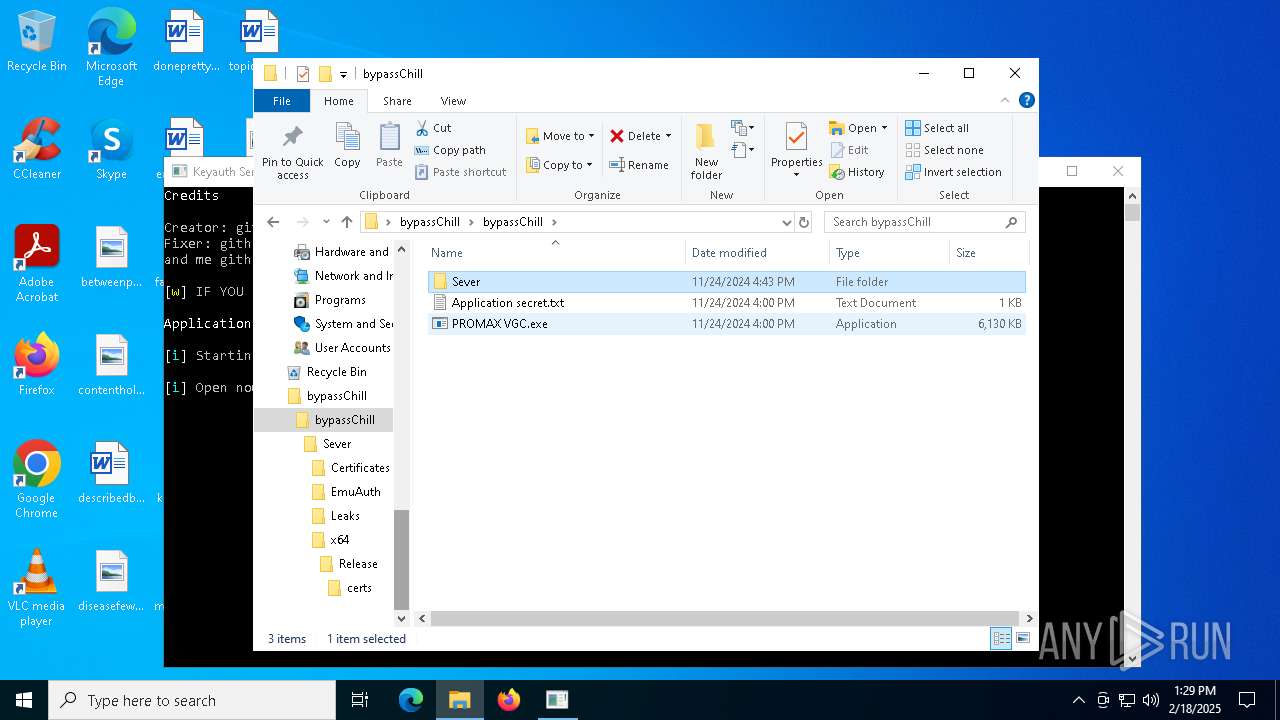
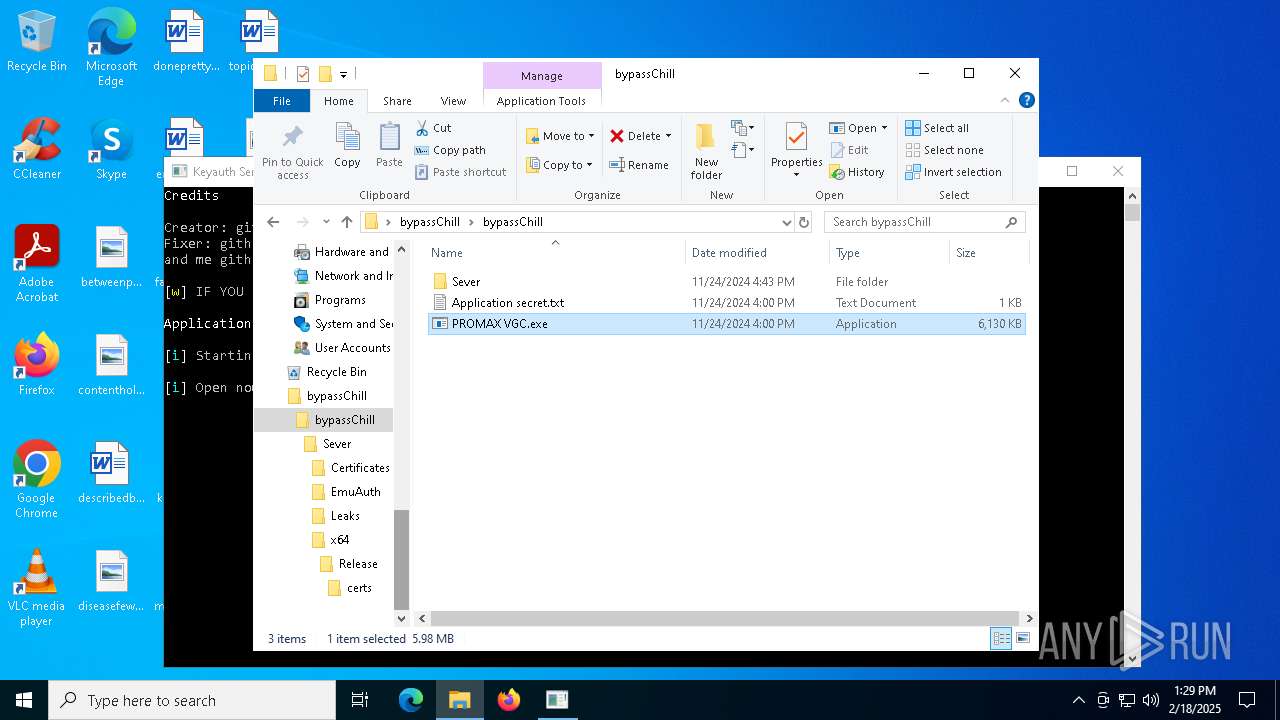
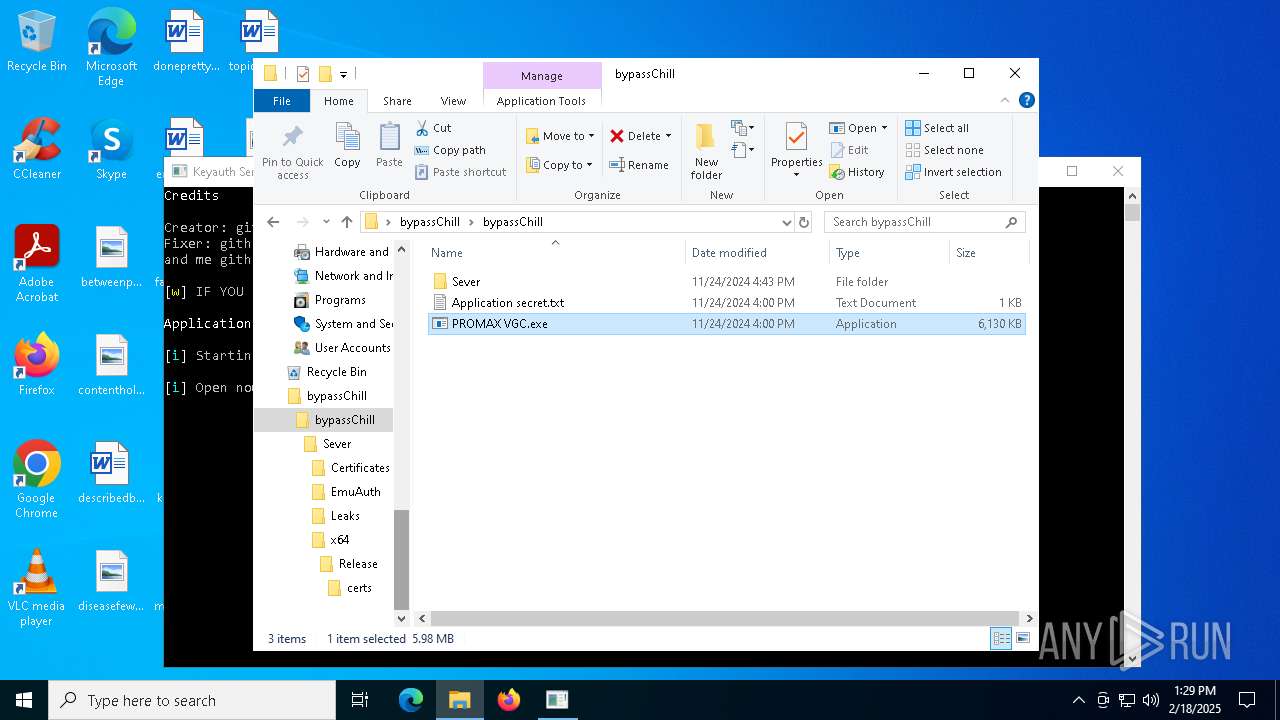
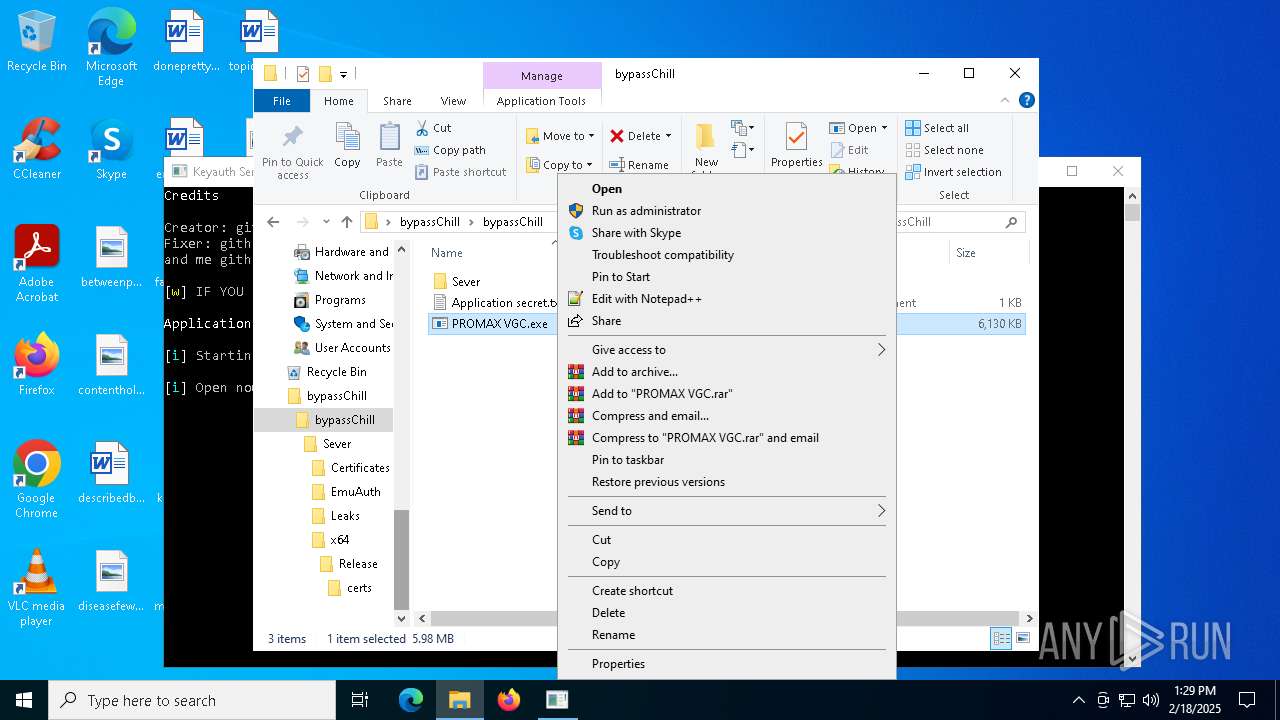
Manual execution by a user
- WinRAR.exe (PID: 4320)
- notepad.exe (PID: 5008)
- rundll32.exe (PID: 6328)
- rundll32.exe (PID: 1752)
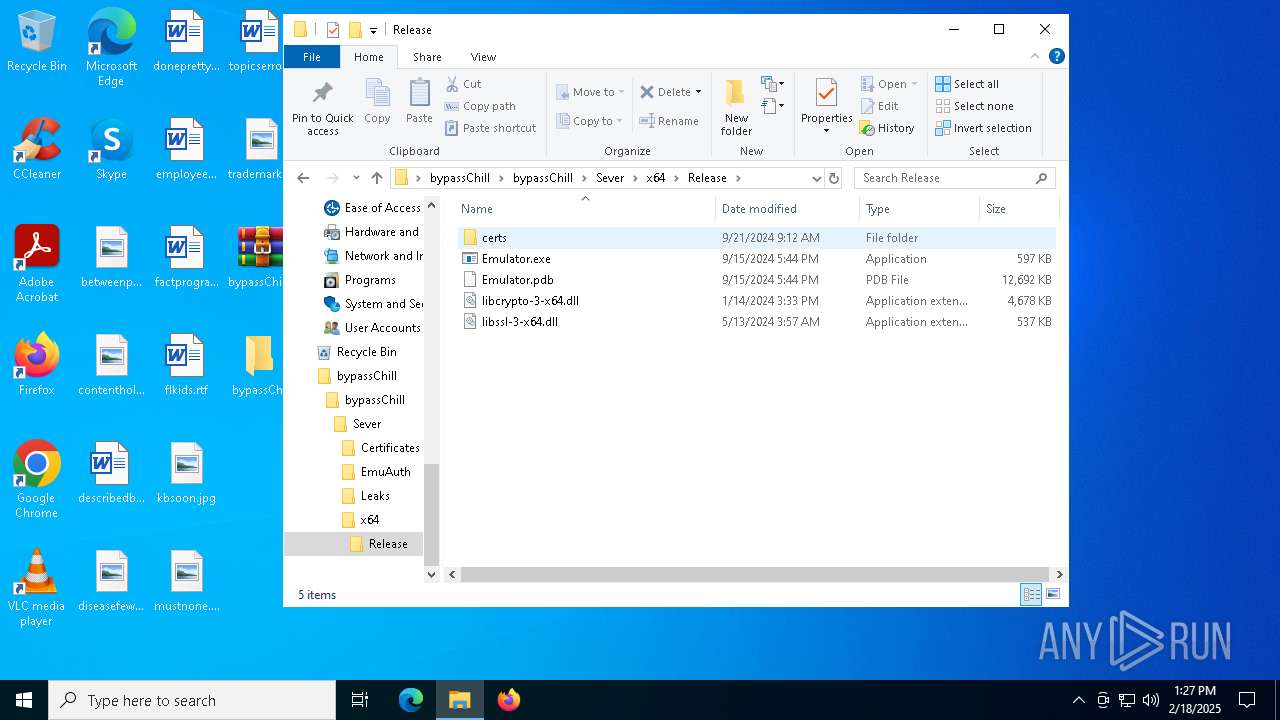
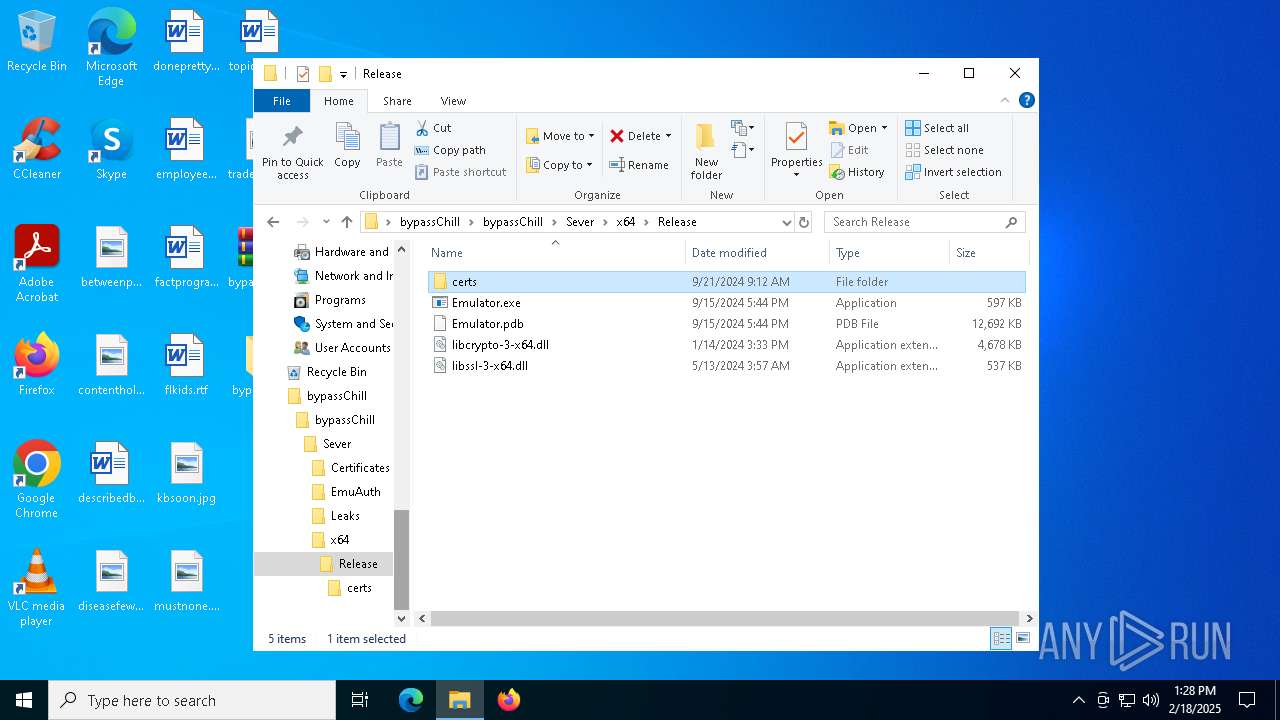
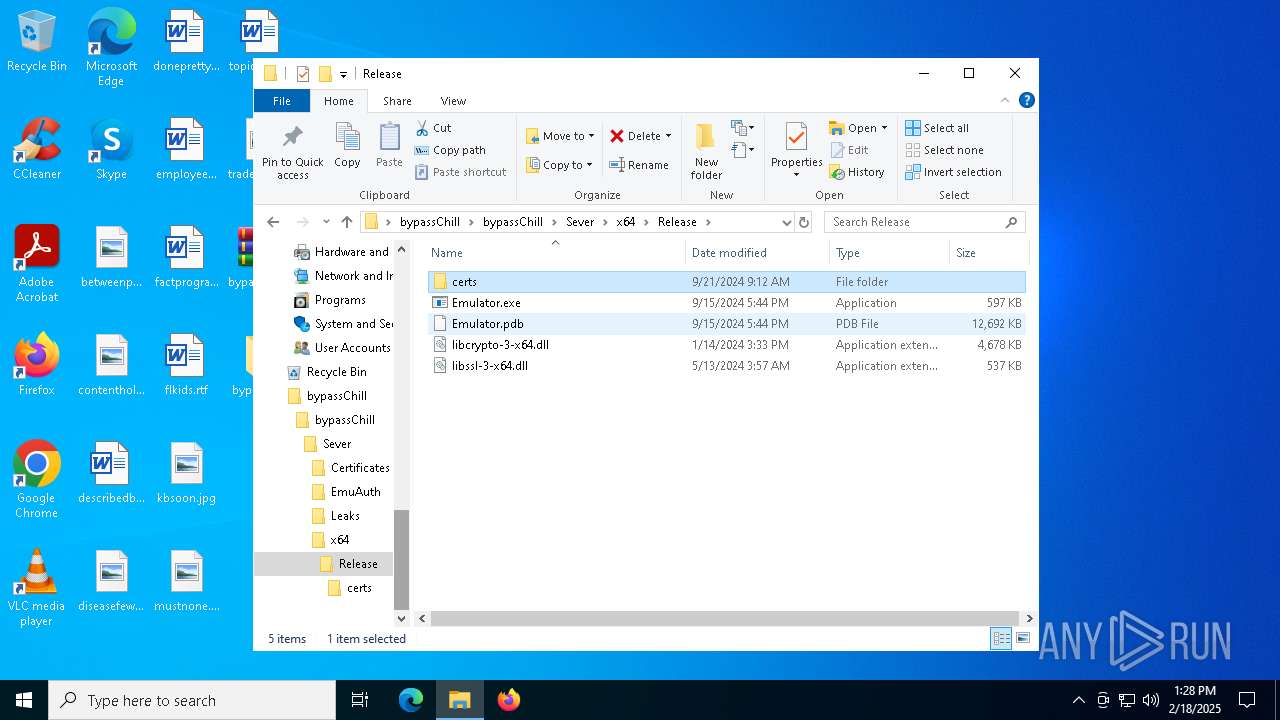
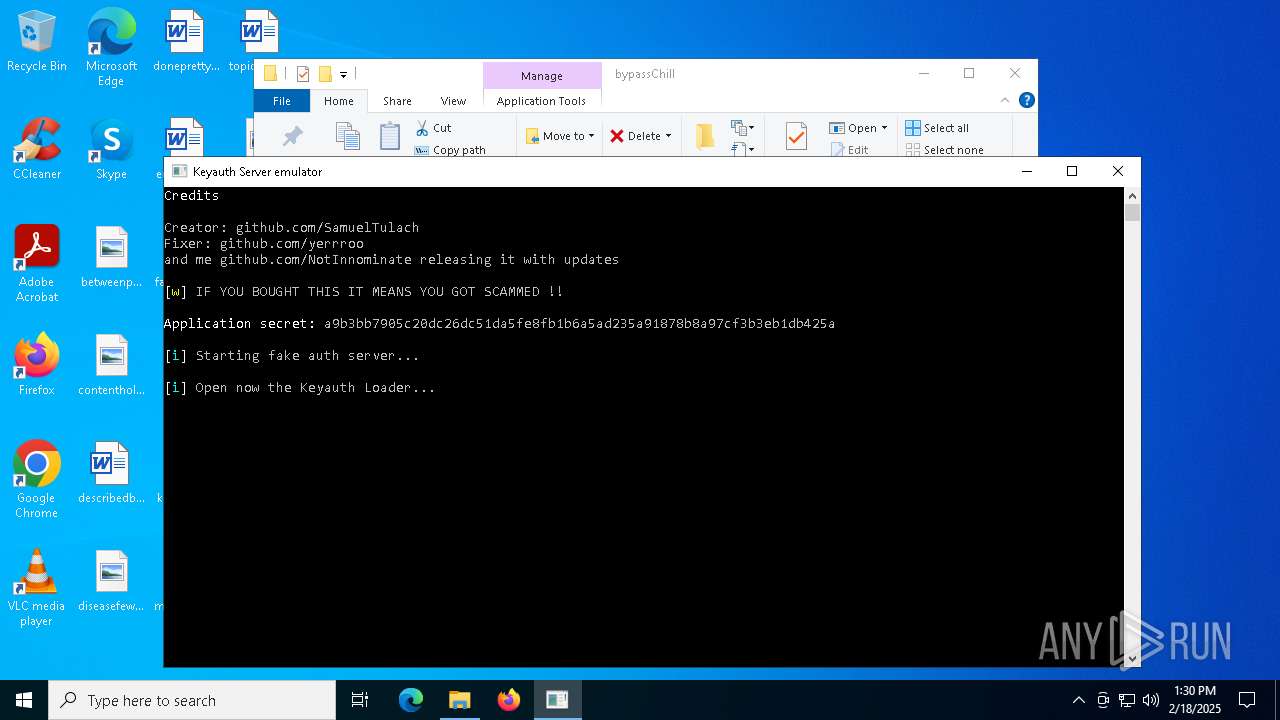
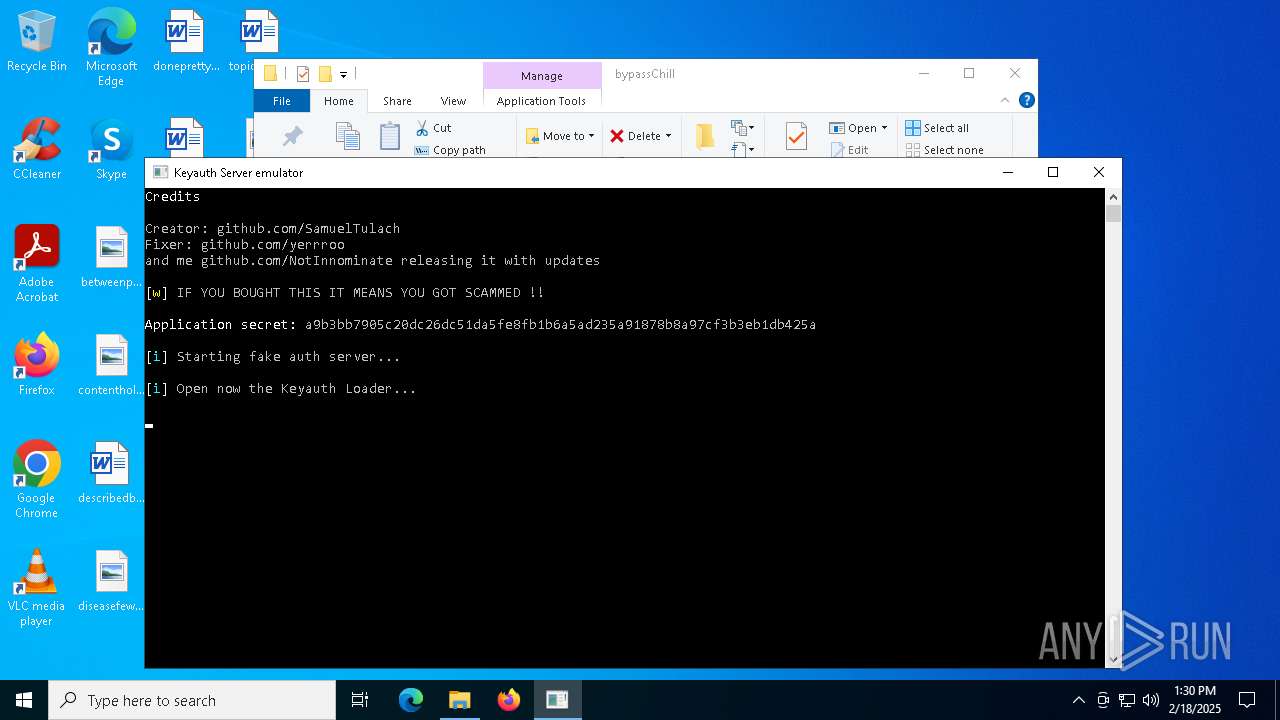
- Emulator.exe (PID: 6448)
- PROMAX VGC.exe (PID: 2996)
- PROMAX VGC.exe (PID: 5212)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4076)
The sample compiled with english language support
- WinRAR.exe (PID: 4320)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5008)
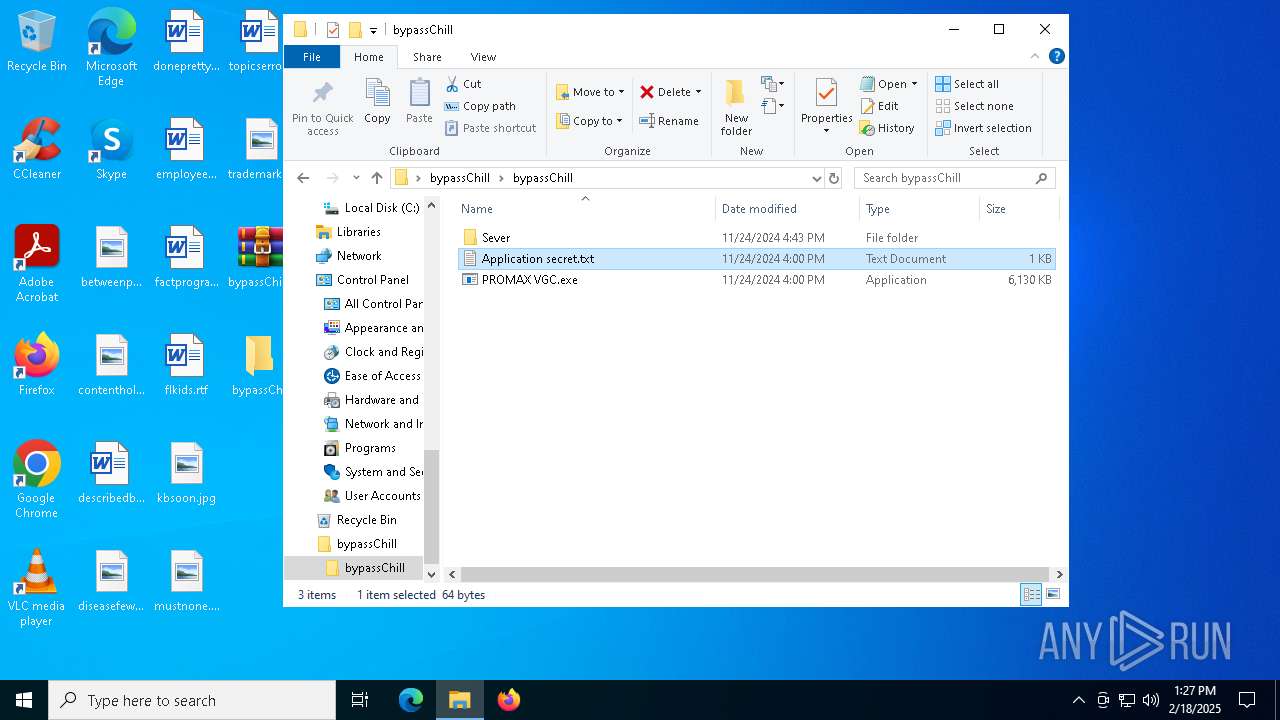
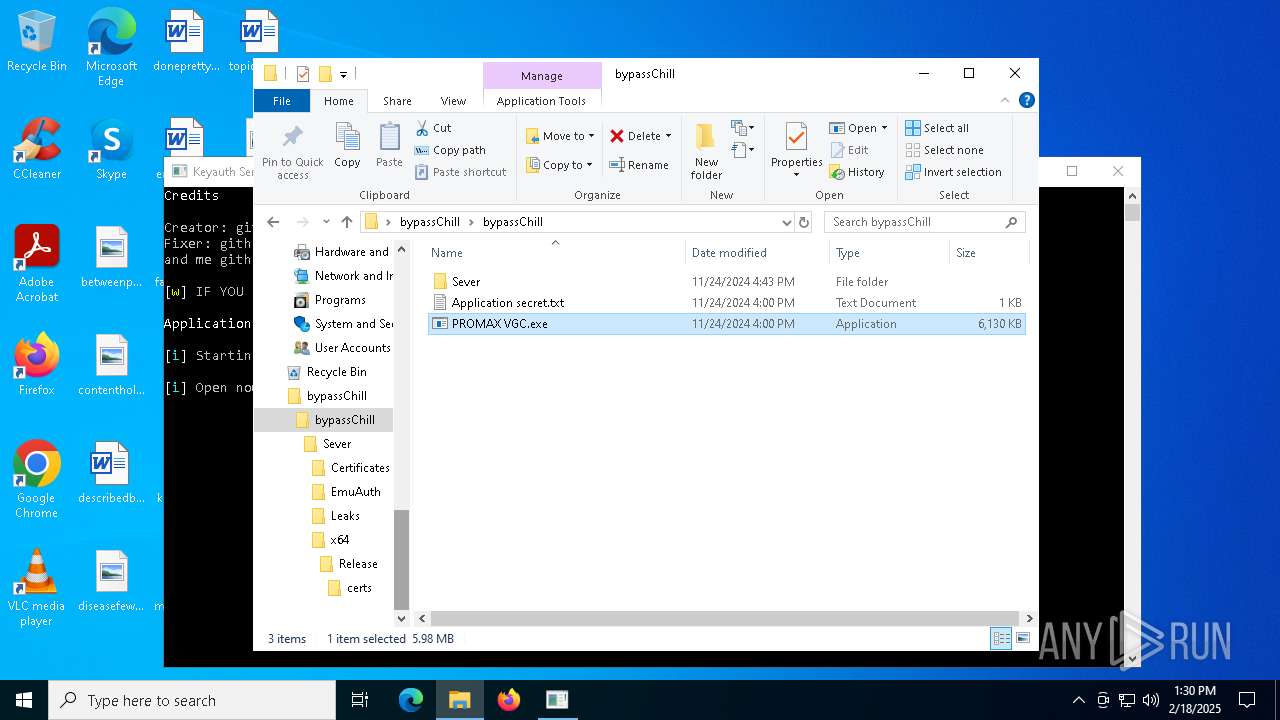
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4320)
Checks supported languages
- PROMAX VGC.exe (PID: 2996)
- PROMAX VGC.exe (PID: 5212)
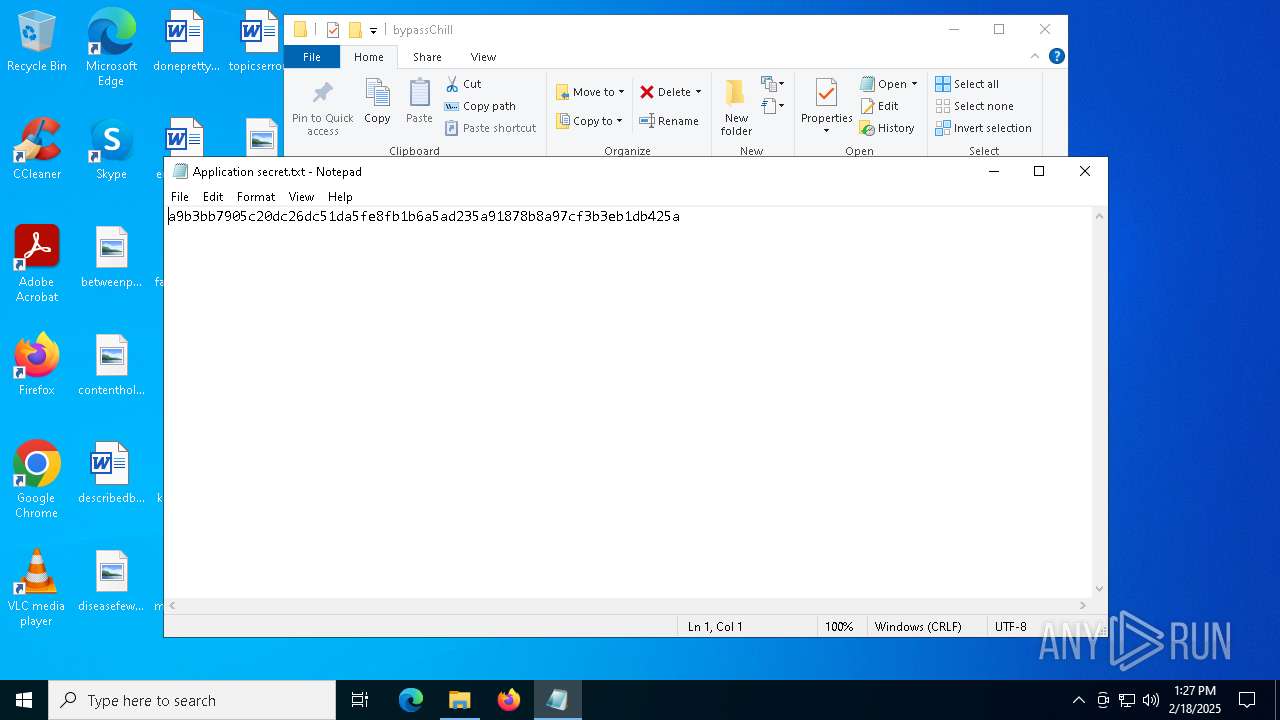
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 1876)
- certutil.exe (PID: 936)
Starts MODE.COM to configure console settings
- mode.com (PID: 4472)
- mode.com (PID: 3584)
Reads the computer name
- PROMAX VGC.exe (PID: 5212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
33
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | certutil -hashfile "C:\Users\admin\Desktop\bypassChill\bypassChill\PROMAX VGC.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
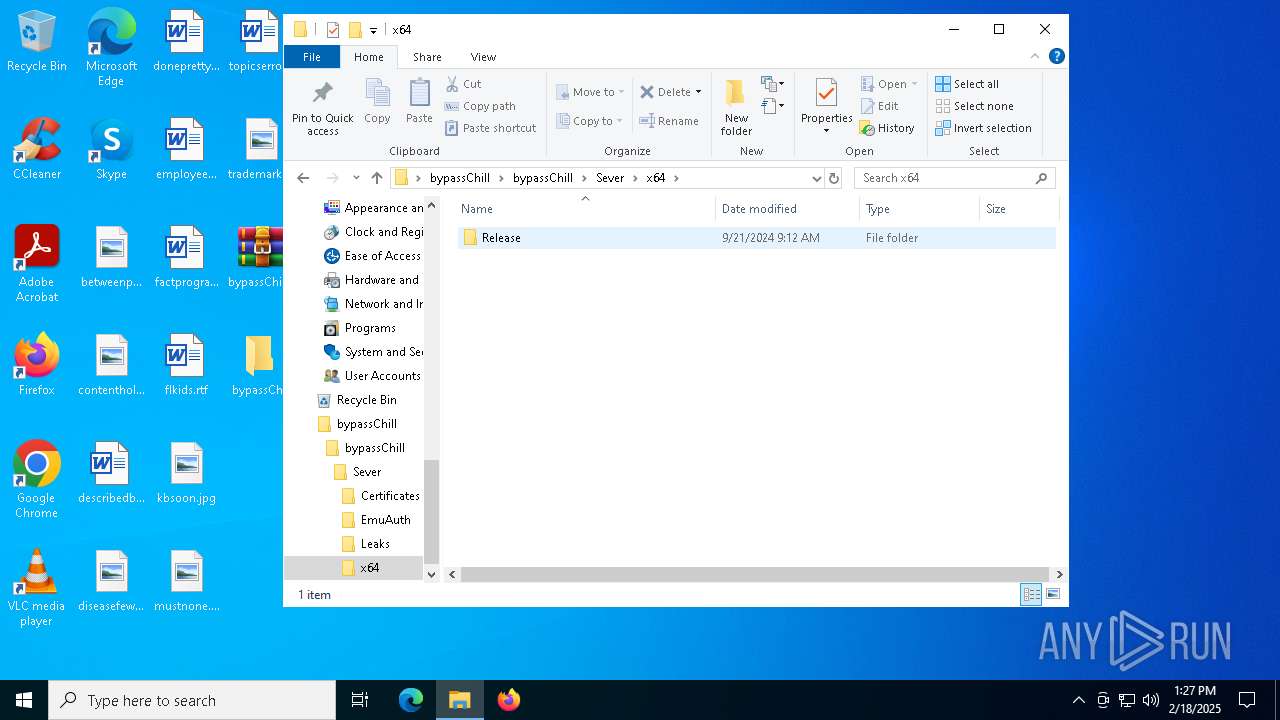
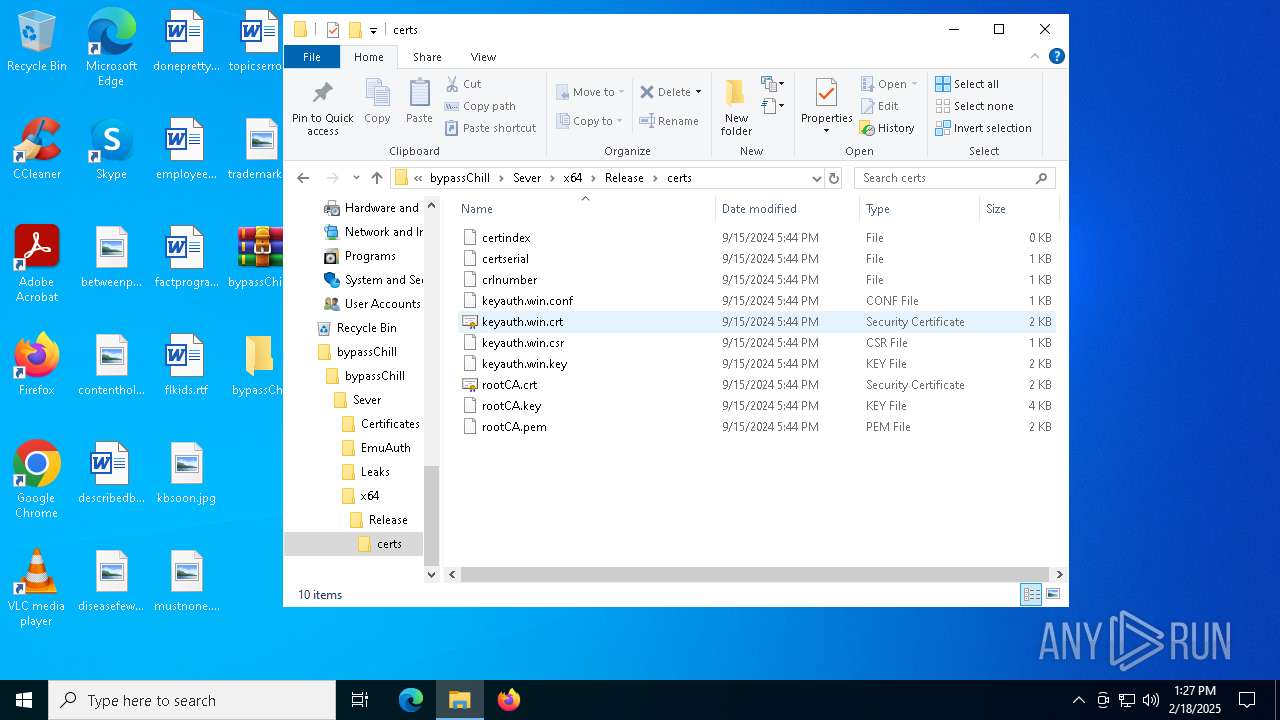
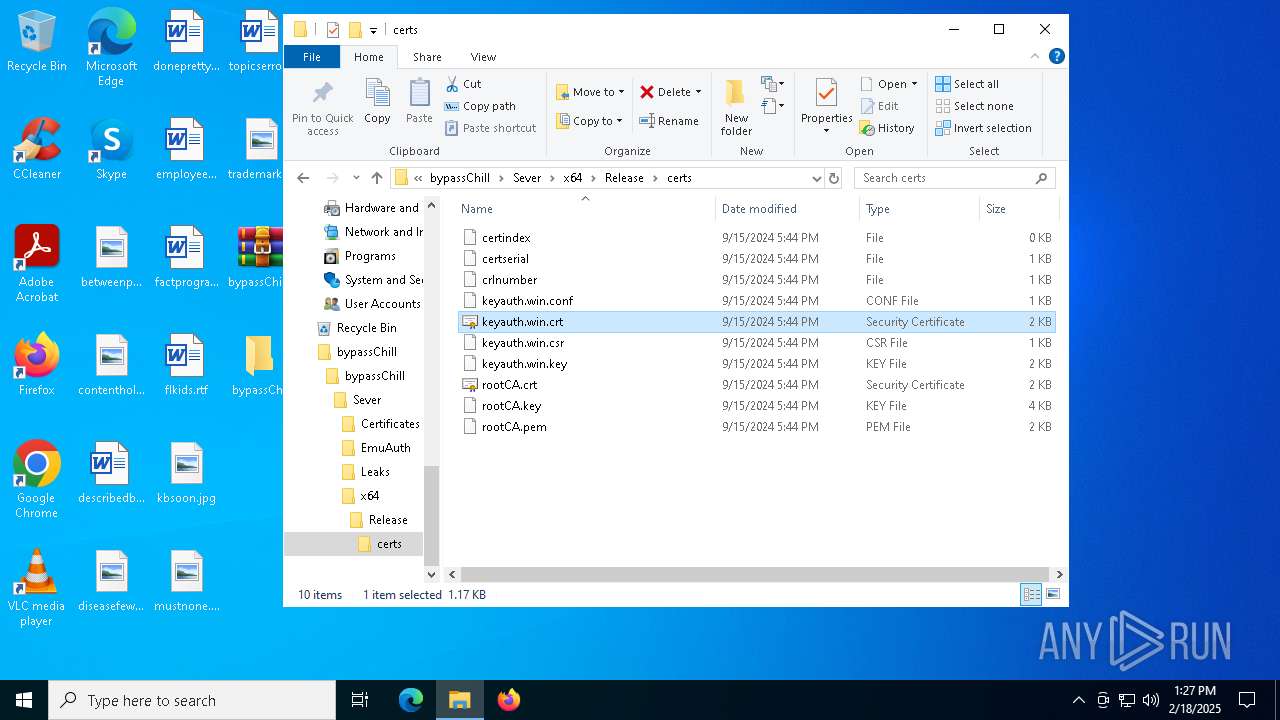
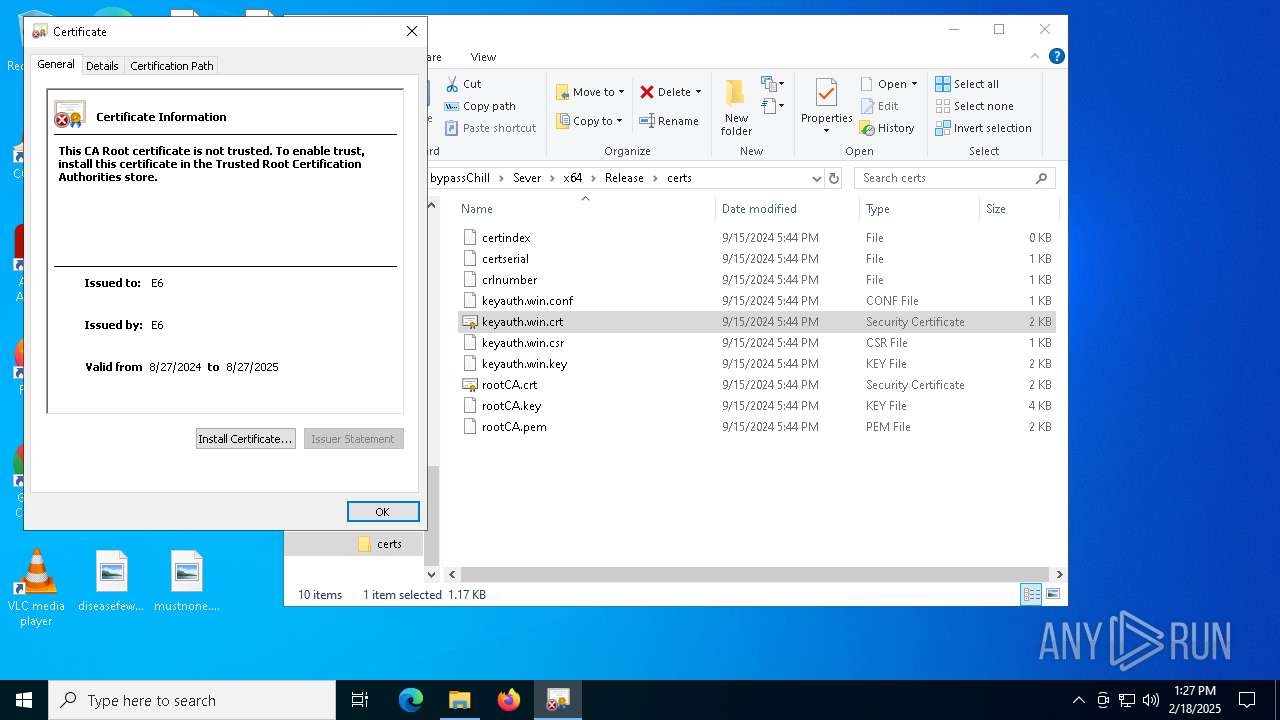
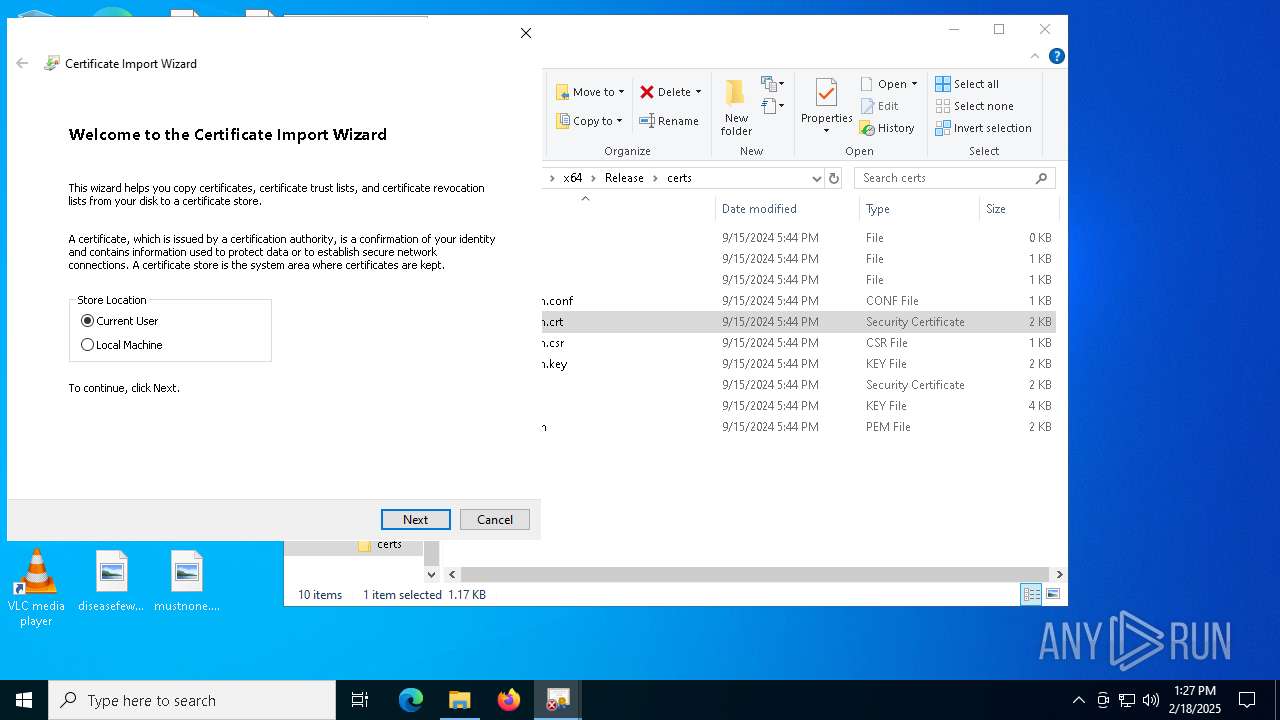
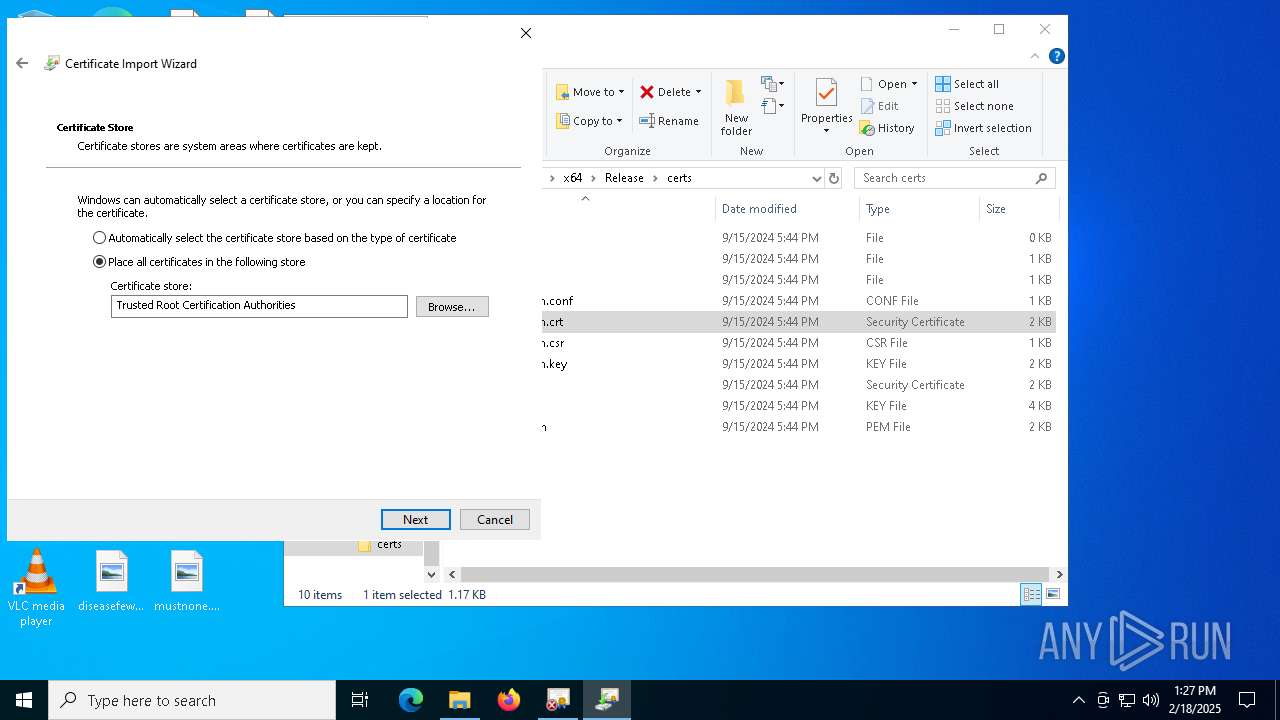
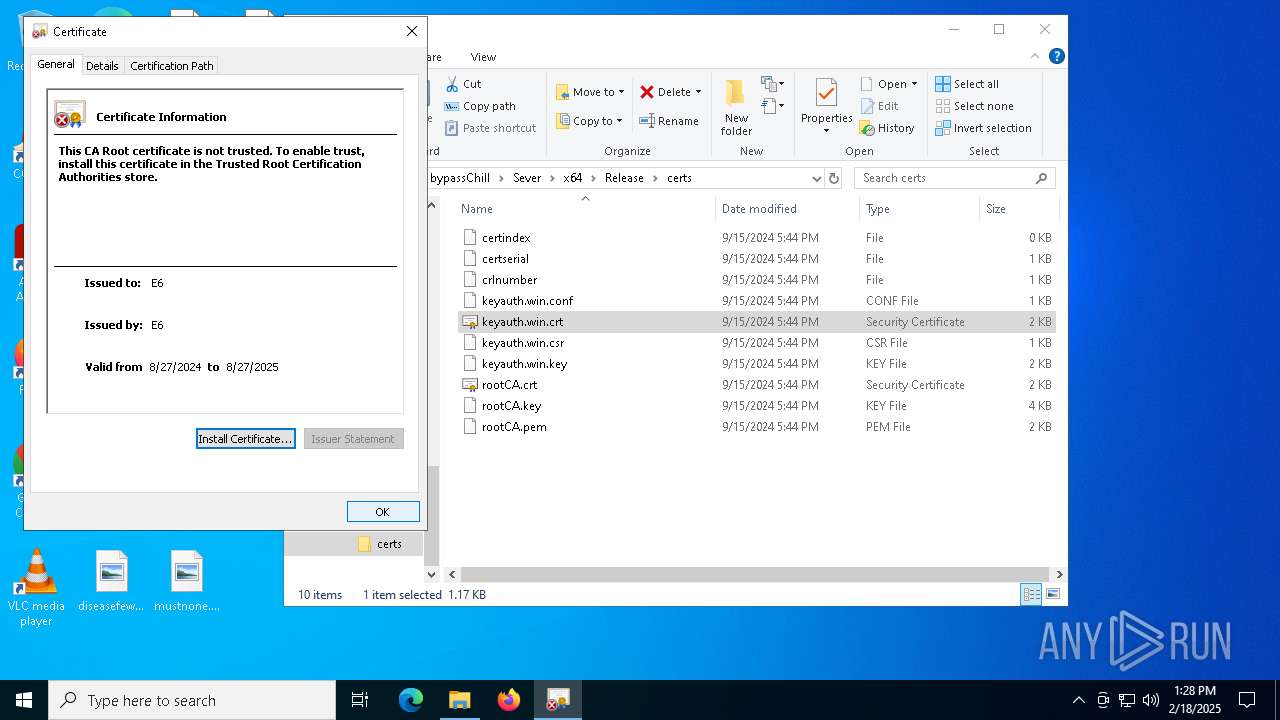
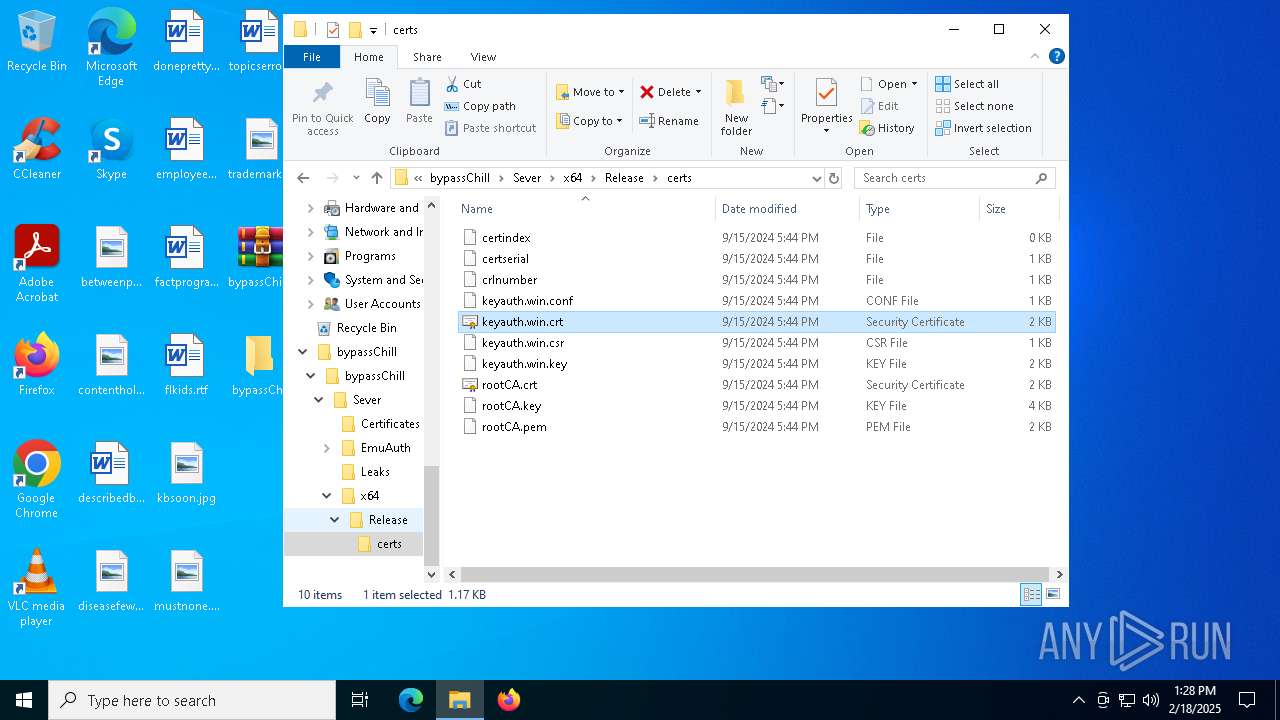
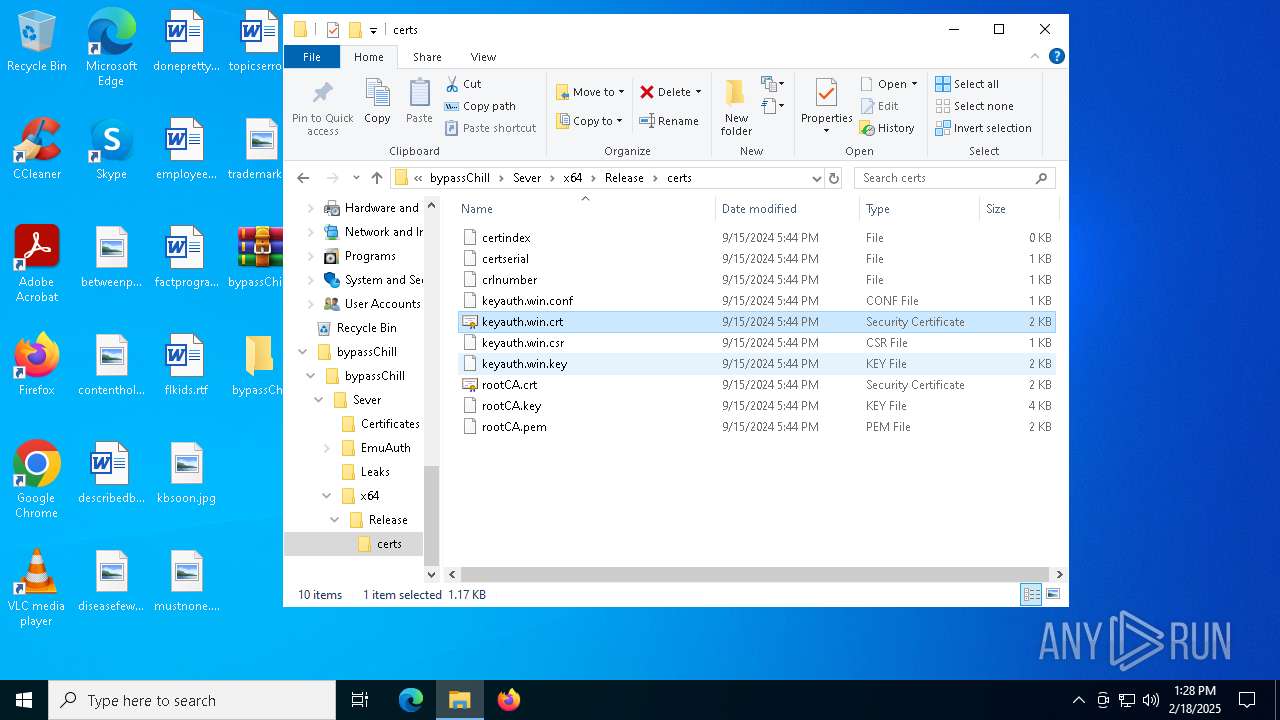
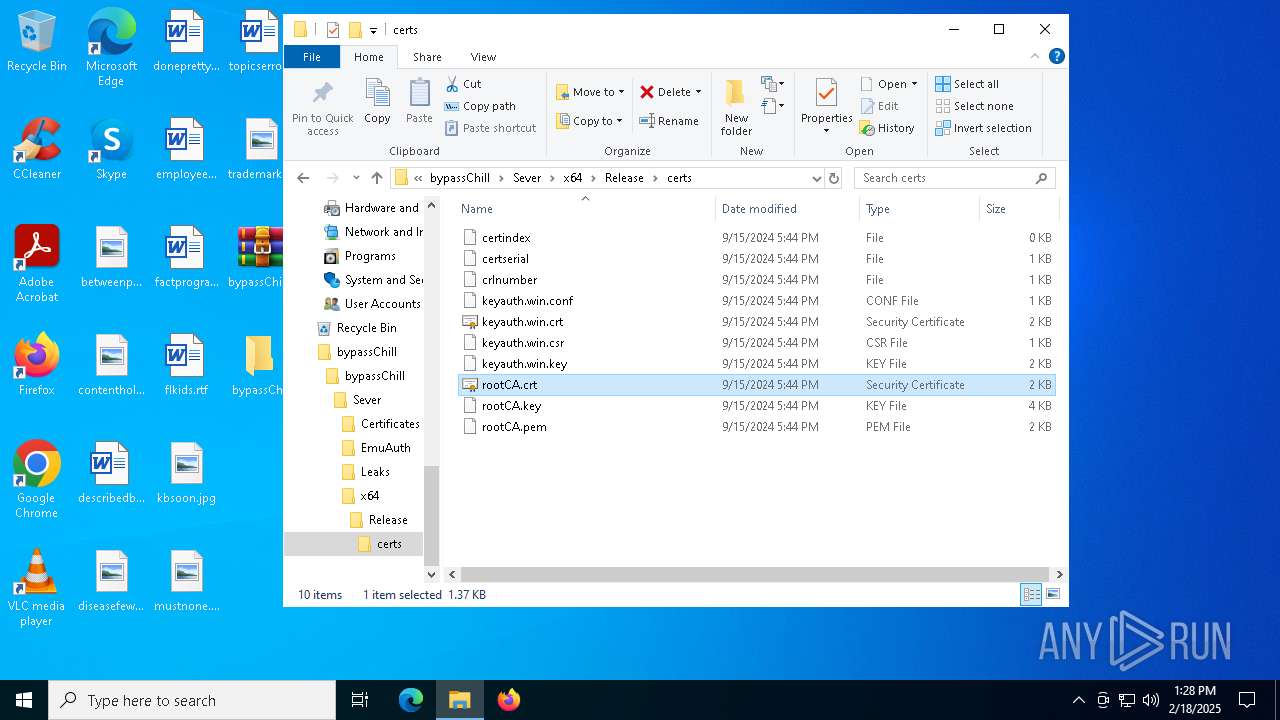
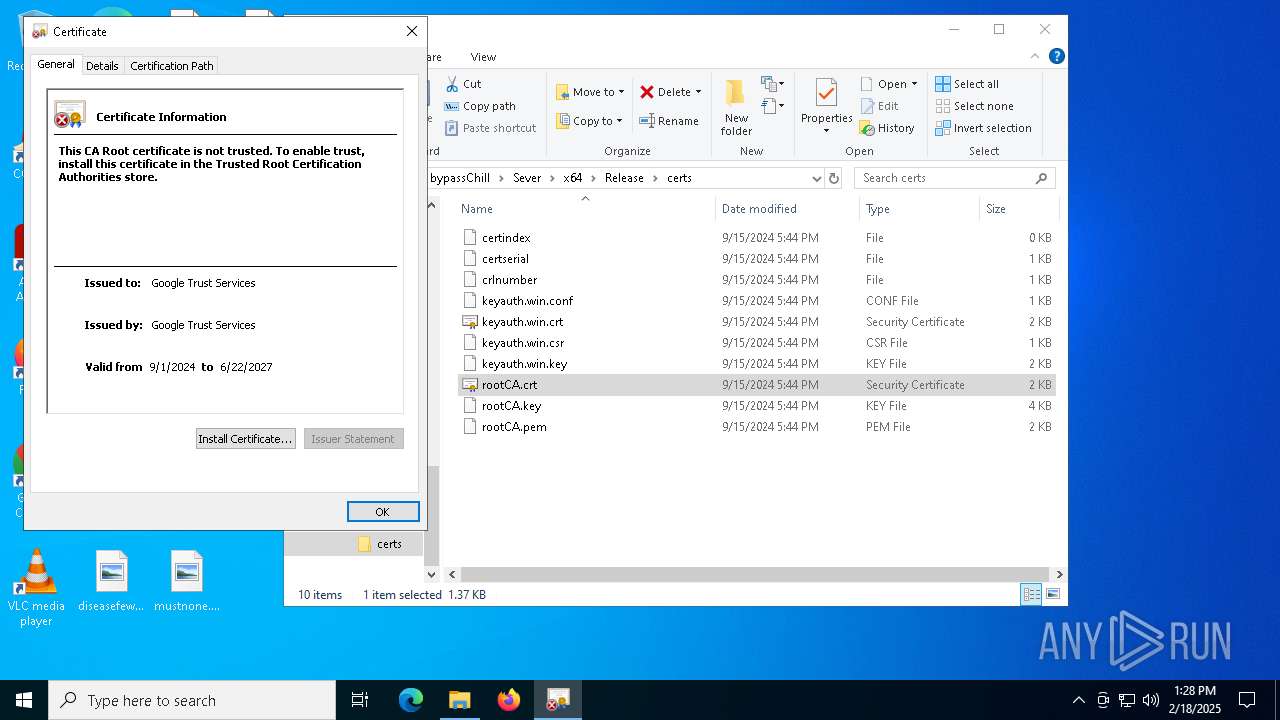
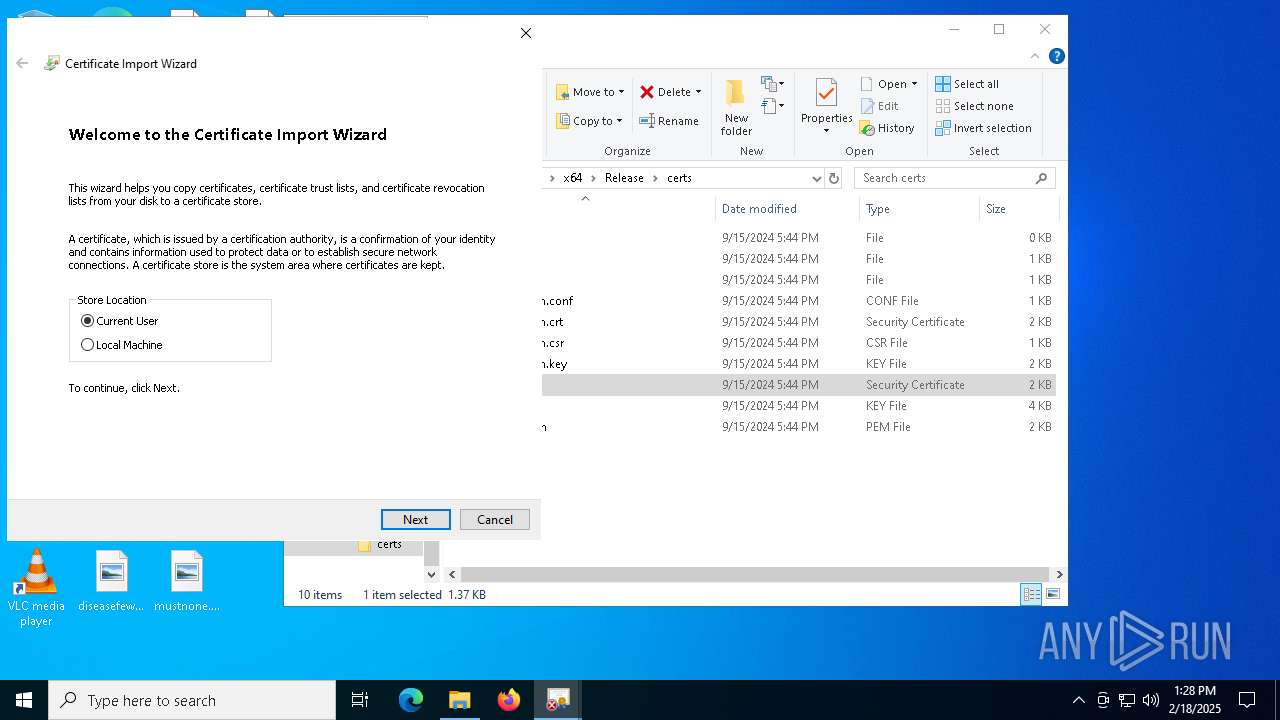
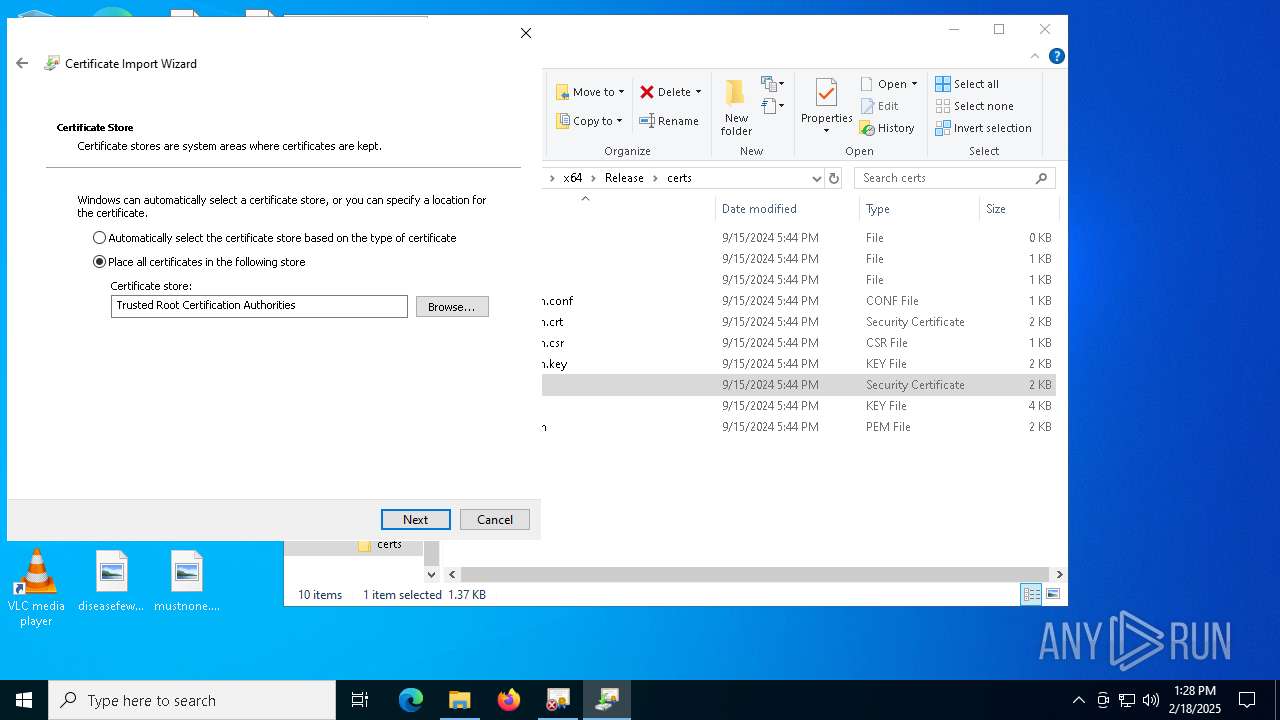
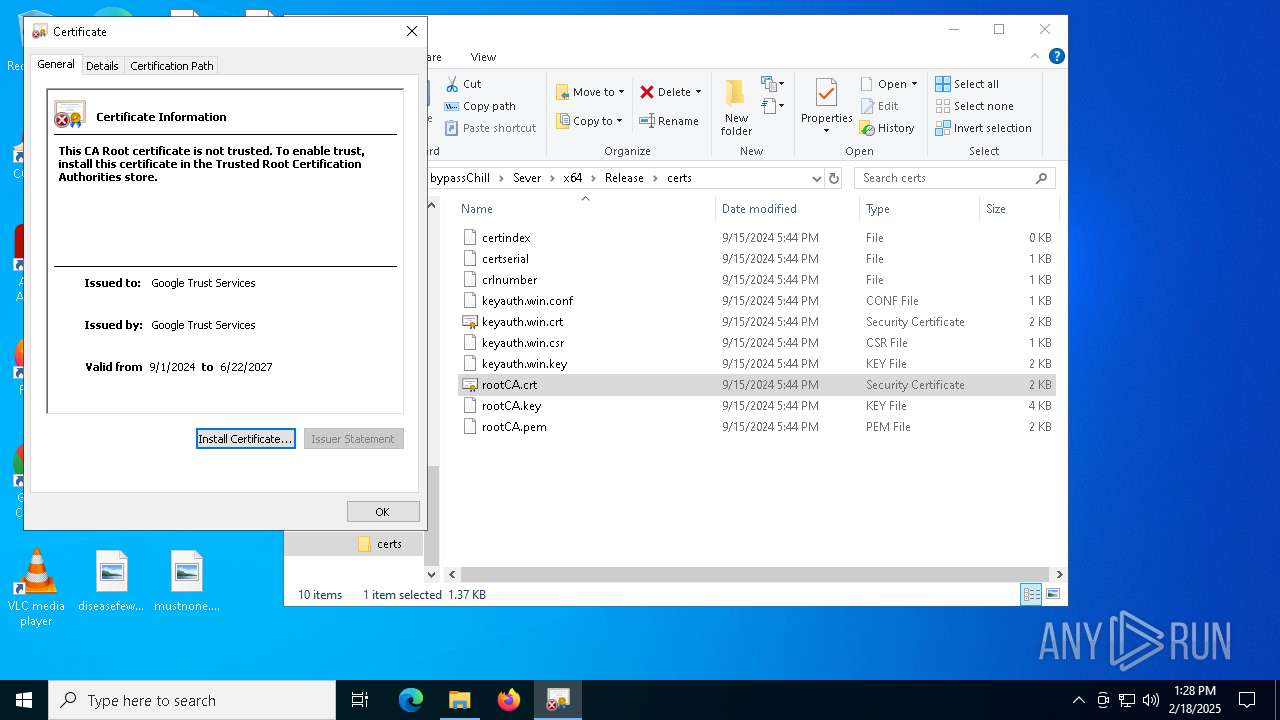
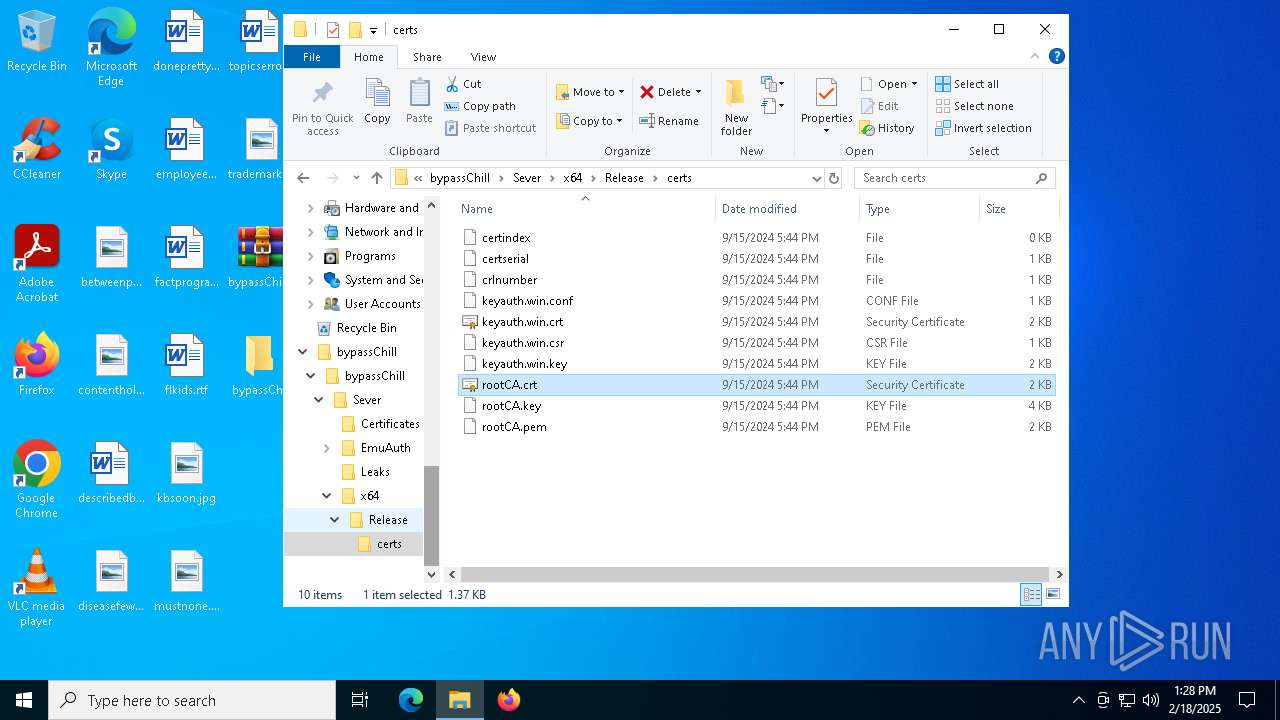
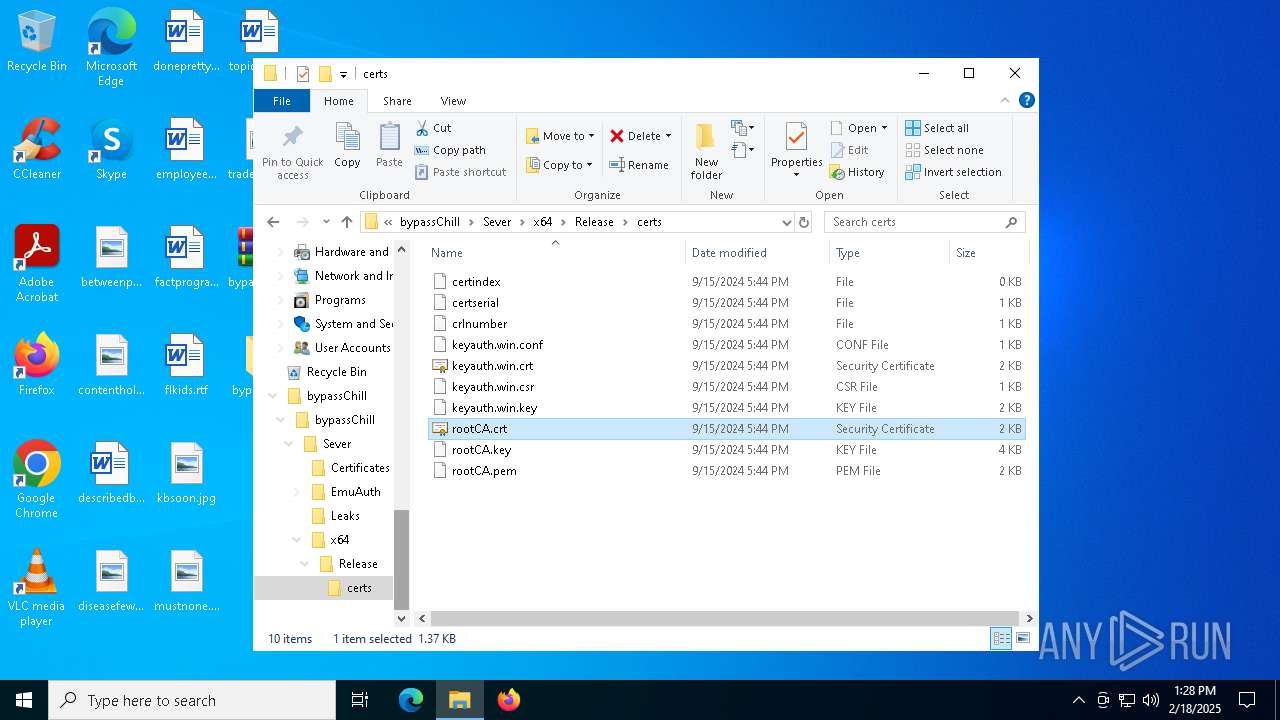
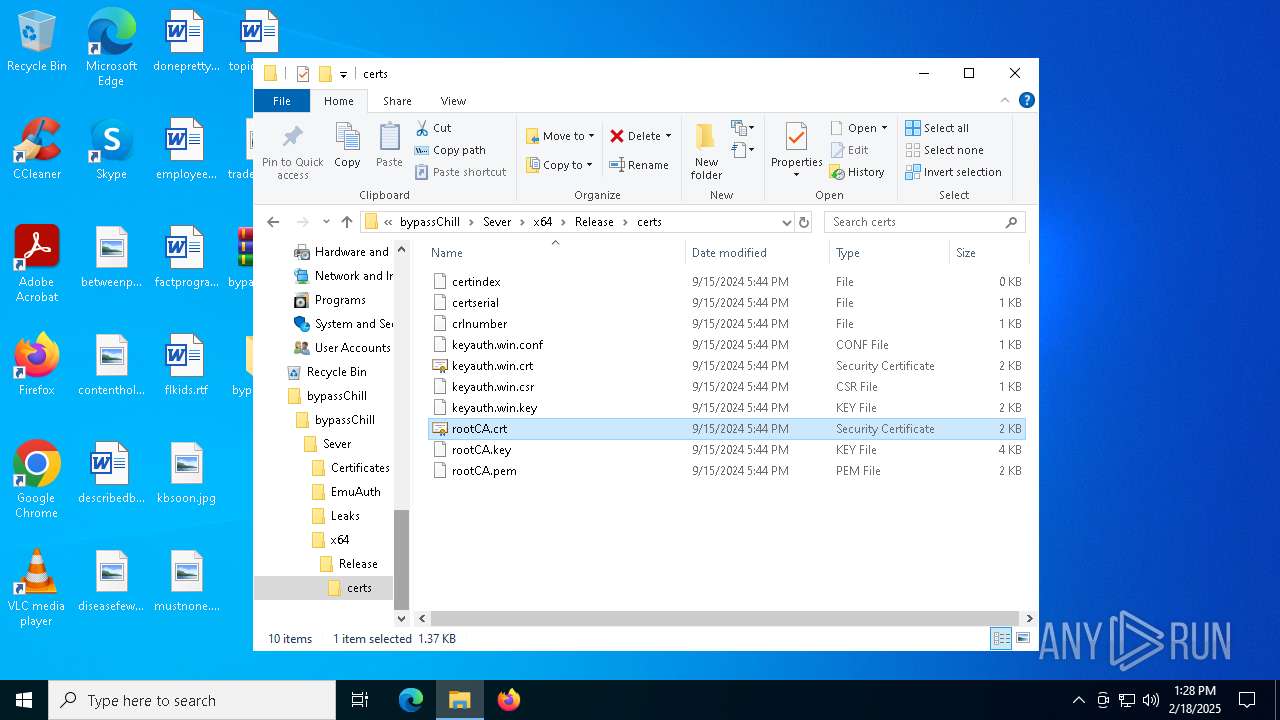
| 1752 | "C:\WINDOWS\system32\rundll32.exe" cryptext.dll,CryptExtOpenCER C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\x64\Release\certs\rootCA.crt | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1876 | certutil -hashfile "C:\Users\admin\Desktop\bypassChill\bypassChill\PROMAX VGC.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PROMAX VGC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PROMAX VGC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | C:\WINDOWS\system32\cmd.exe /c mode 50,15 | C:\Windows\System32\cmd.exe | — | PROMAX VGC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2680 | C:\WINDOWS\system32\cmd.exe /c certutil -hashfile "C:\Users\admin\Desktop\bypassChill\bypassChill\PROMAX VGC.exe" MD5 | find /i /v "md5" | find /i /v "certutil" | C:\Windows\System32\cmd.exe | — | PROMAX VGC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
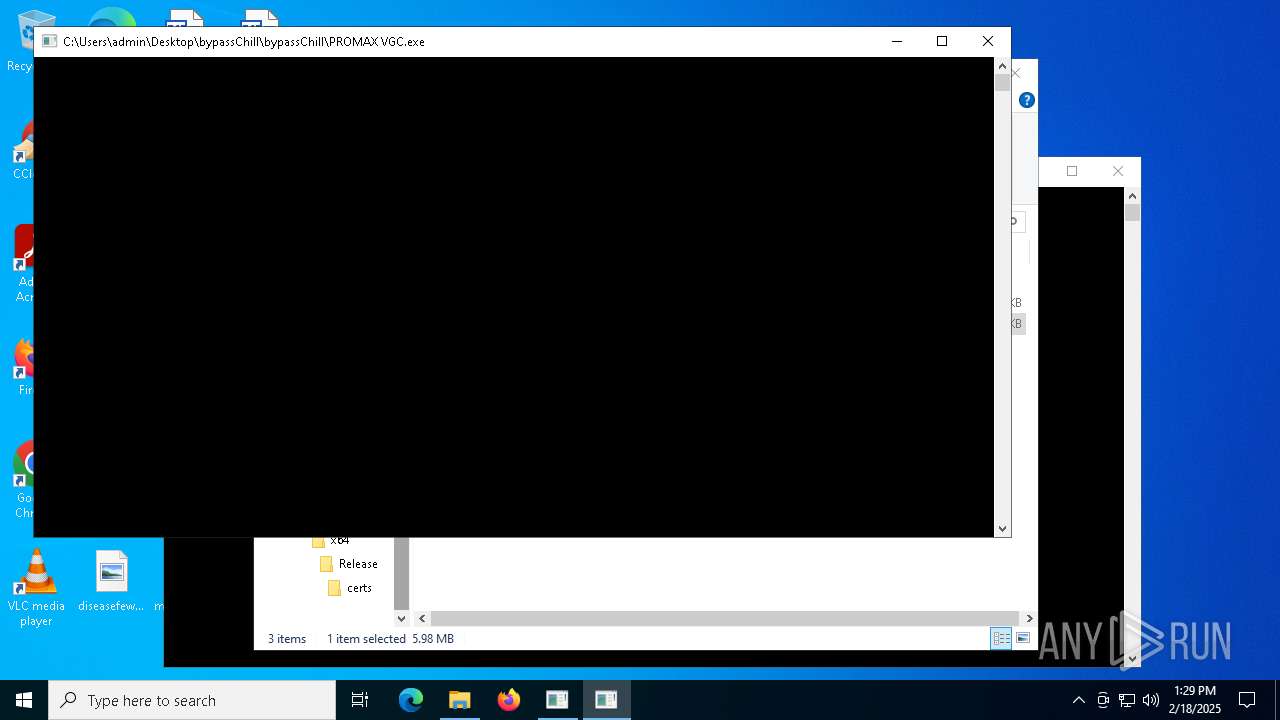
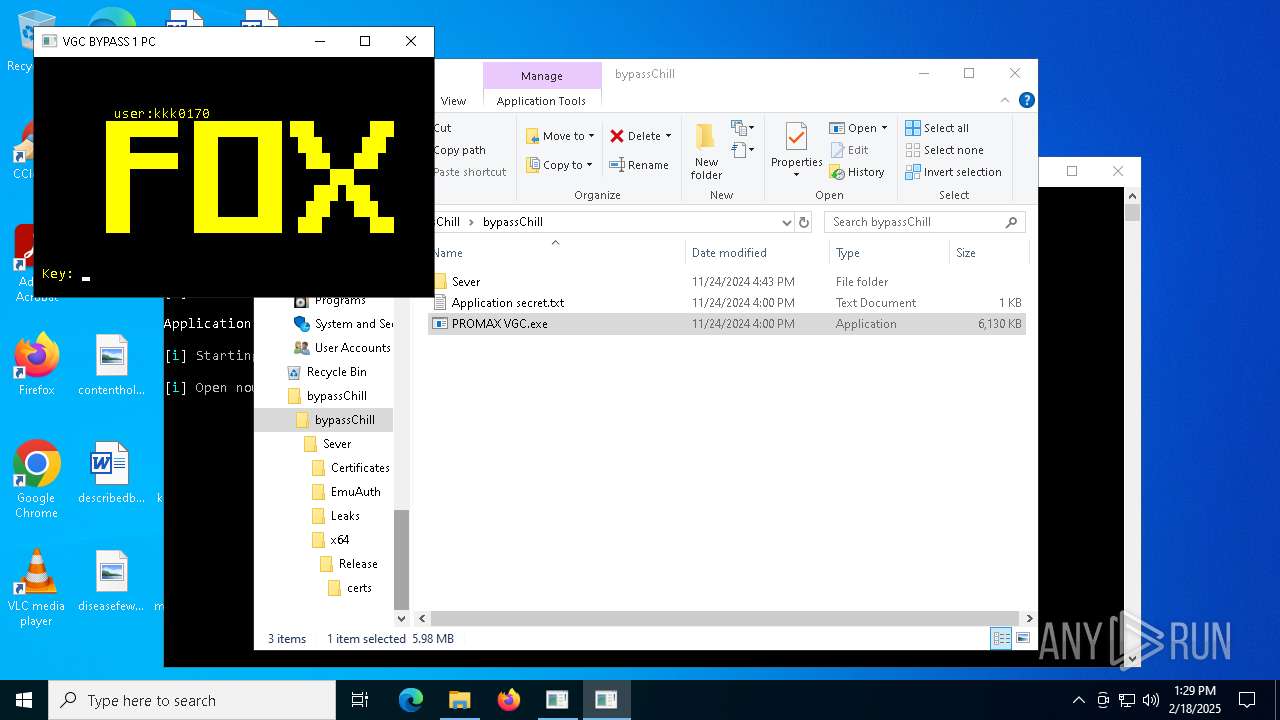
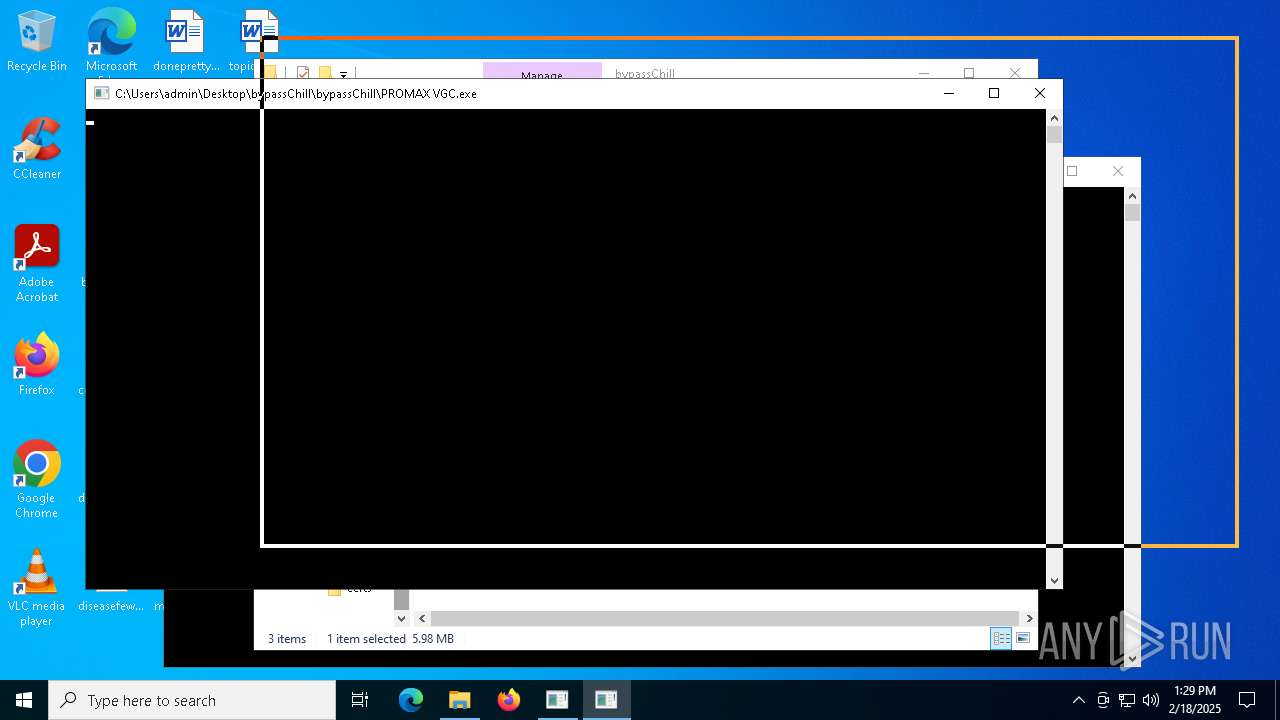
| 2996 | "C:\Users\admin\Desktop\bypassChill\bypassChill\PROMAX VGC.exe" | C:\Users\admin\Desktop\bypassChill\bypassChill\PROMAX VGC.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 3540 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 663
Read events
23 652
Write events
9
Delete events
2
Modification events
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
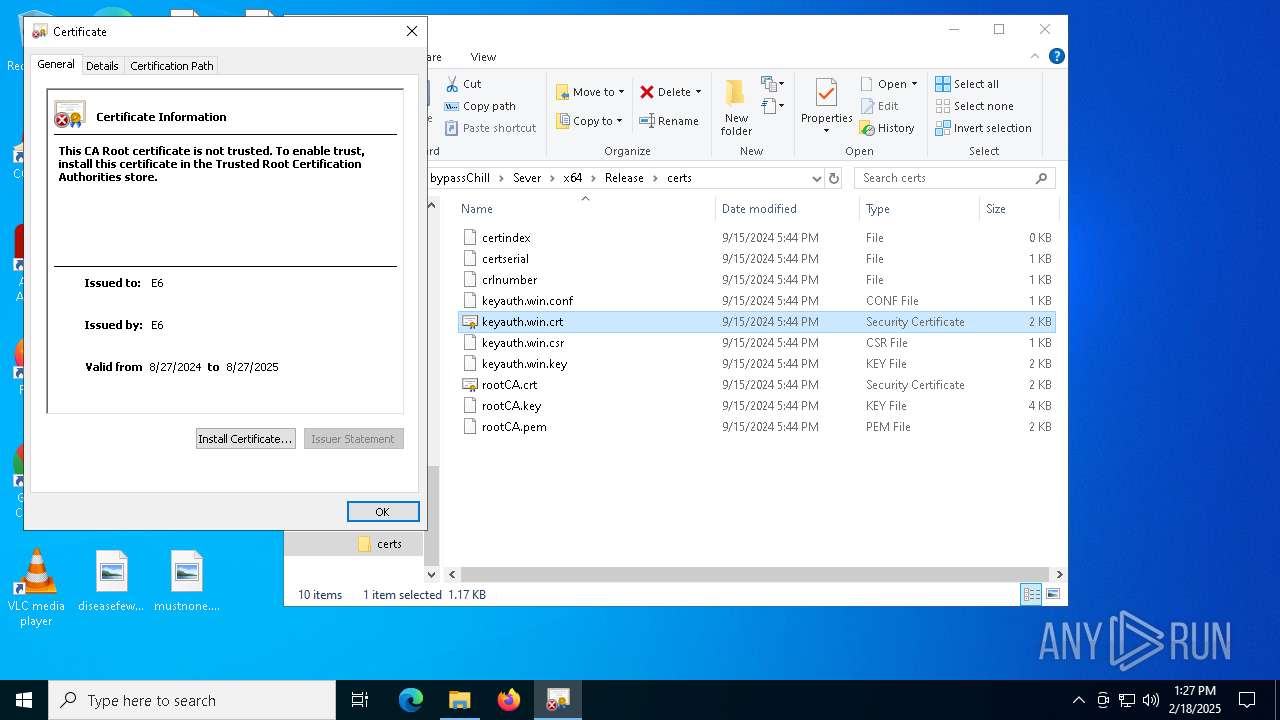
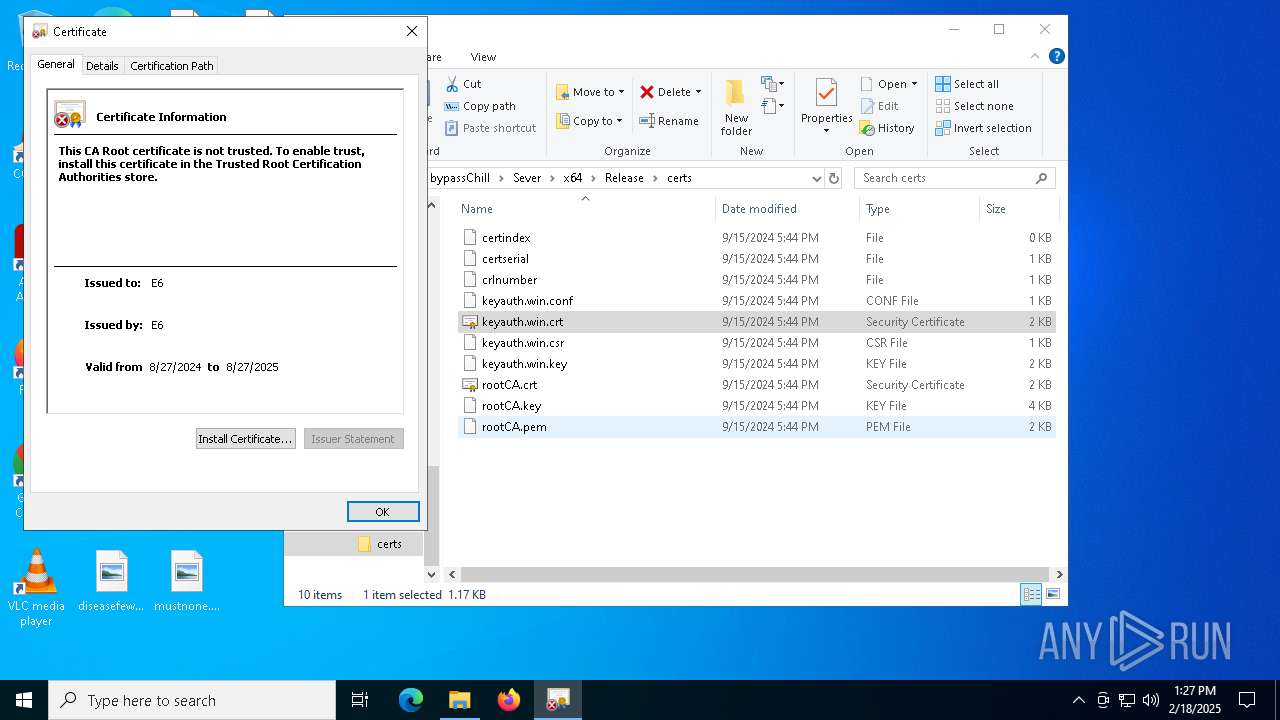
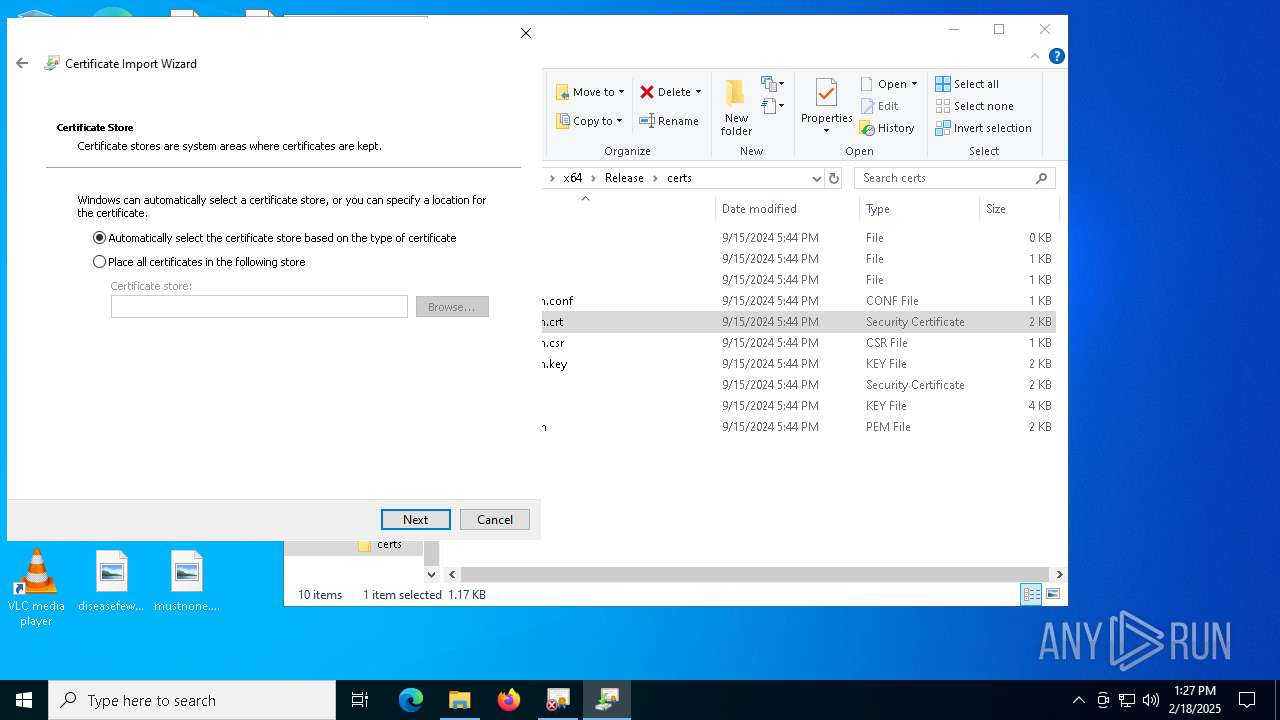
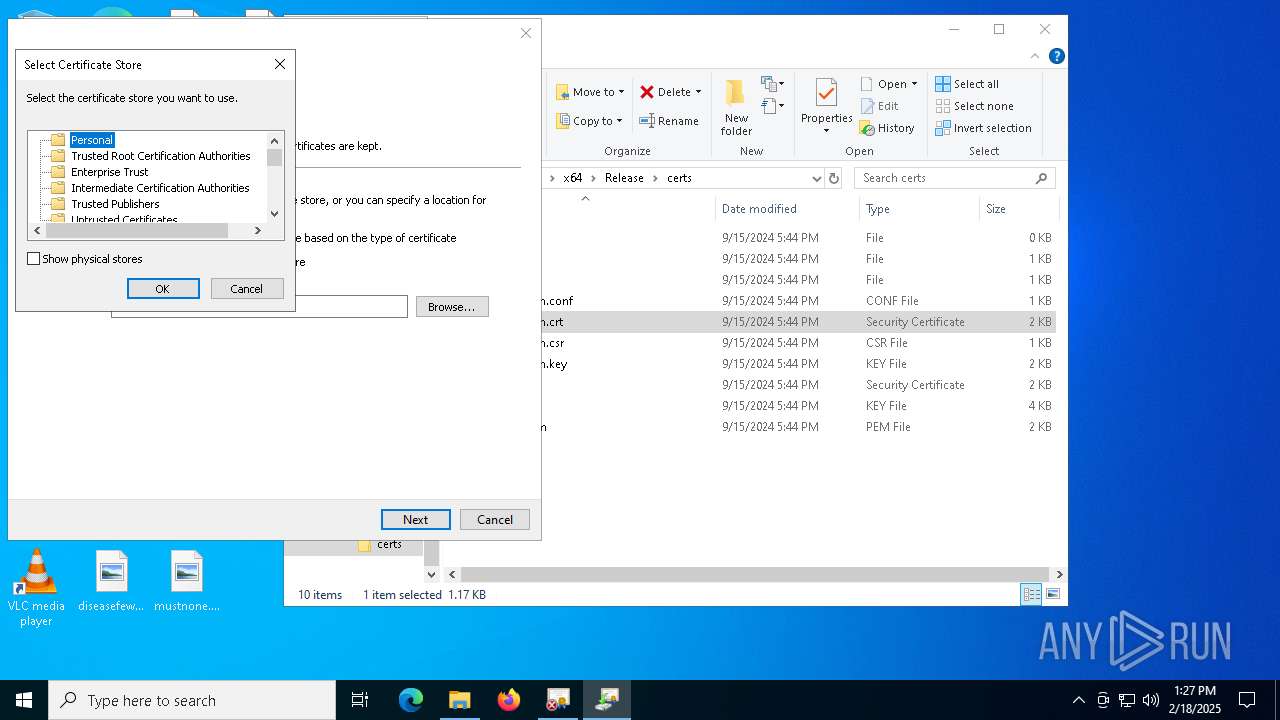
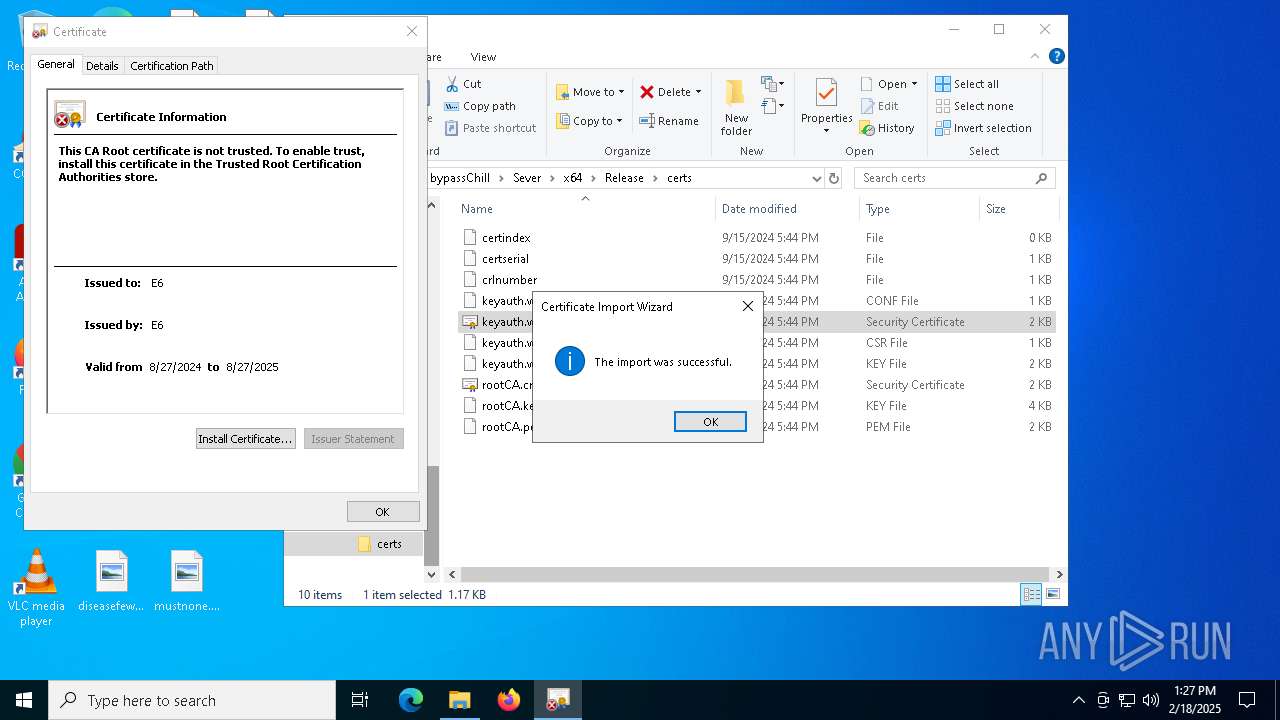
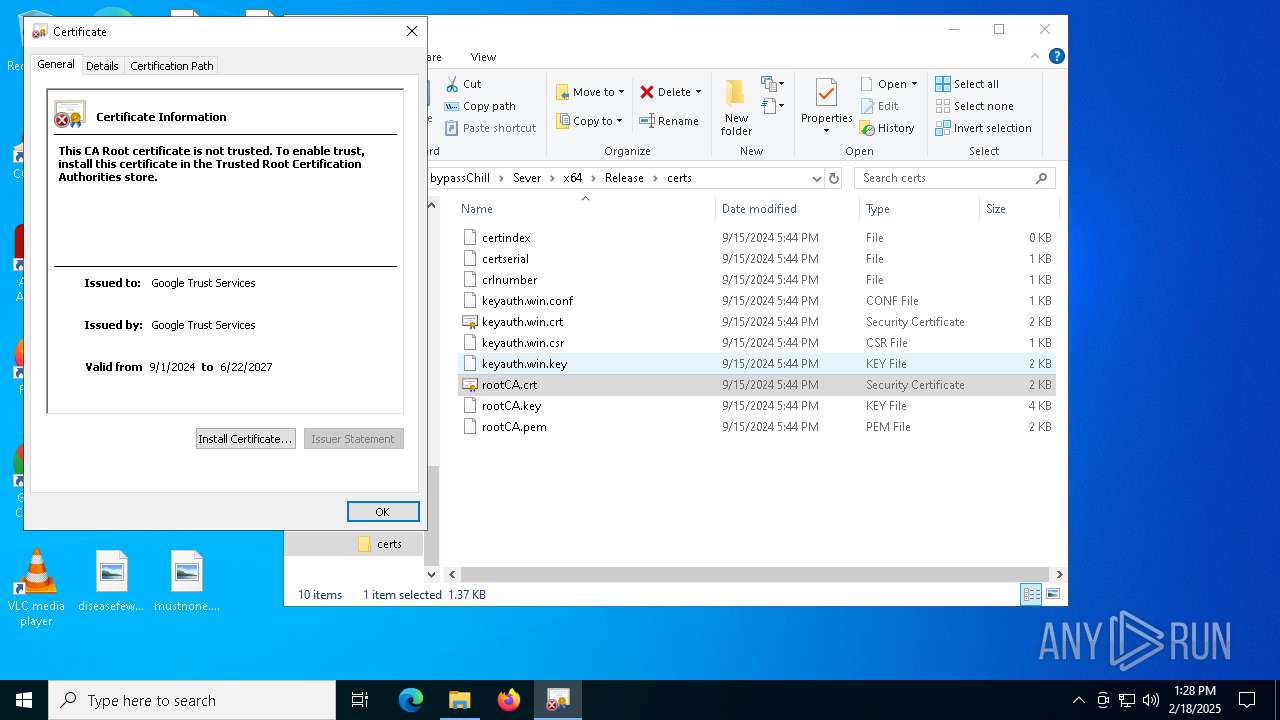
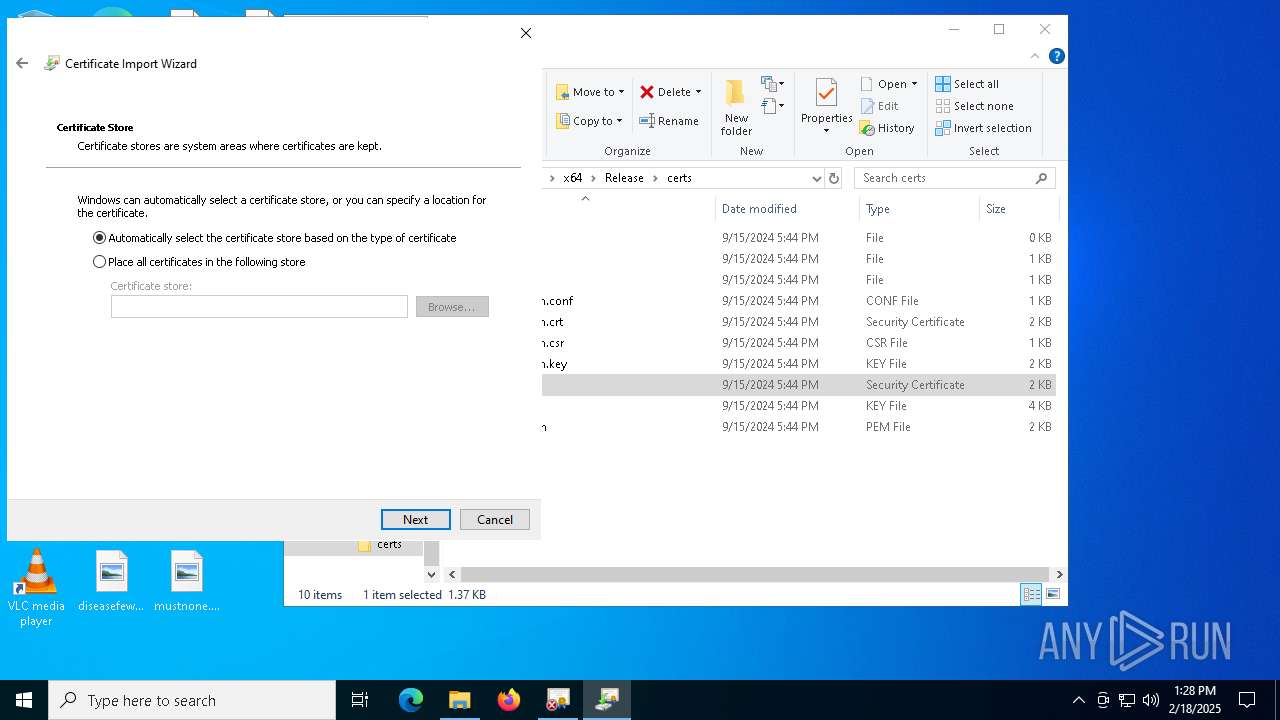
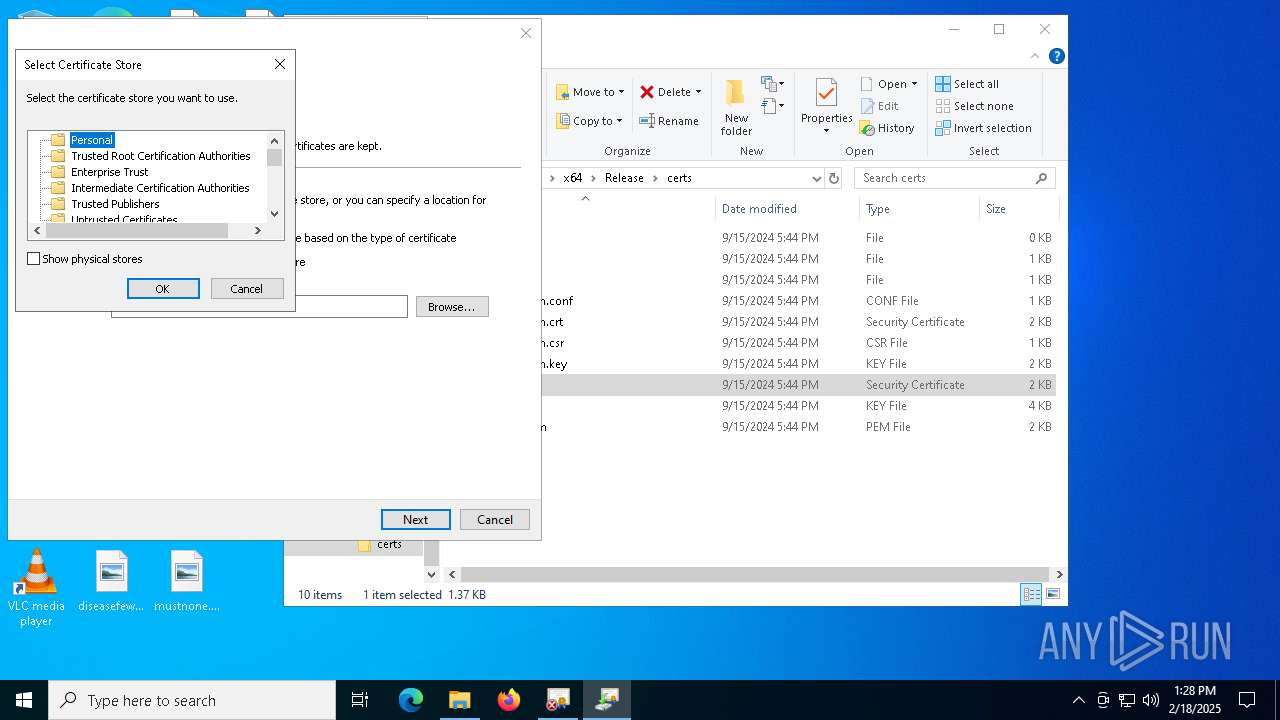
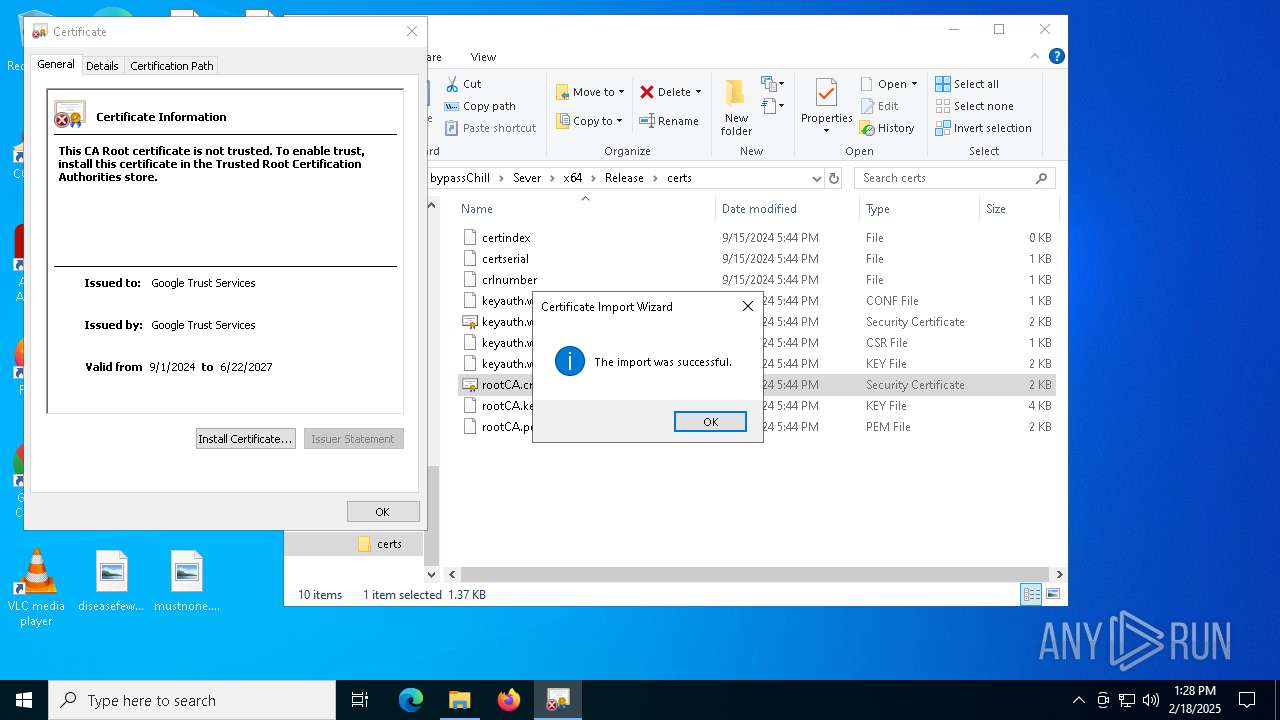
| (PID) Process: | (6516) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | 7976D14BA502C95403263A0AEE2A91DD357AAEB1 |
Value: | |||
| (PID) Process: | (6516) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\7976D14BA502C95403263A0AEE2A91DD357AAEB1 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000007A3E63B7CD74C7A657EFF7A33B2AB420F00000001000000200000001B110B5E195A2B4FF8D28A7B4B157708365B9F1D3F6F37133DBBF539BC4A32AB140000000100000014000000083B341918BC733B95B92864B57878F59EE4D44B1900000001000000100000007A0EE6665F7C51B3587C951EB94D94E40300000001000000140000007976D14BA502C95403263A0AEE2A91DD357AAEB15C00000001000000040000000008000020000000010000003F0300003082033B30820223A003020102021425827126FB88F0D0167CBAB089371092A40C7571300D06092A864886F70D01010B0500303A310B300906035504030C024536311E301C060355040A0C15476F6F676C65205472757374205365727669636573310B3009060355040613025553301E170D3234303832373136313130335A170D3235303832373136313130335A303A310B300906035504030C024536311E301C060355040A0C15476F6F676C65205472757374205365727669636573310B300906035504061302555330820122300D06092A864886F70D01010105000382010F003082010A0282010100A43FB28612A2A1AA1C2528E356EE87E4EAECD6ACEA46E92AE6AD57F72221E78D236A69D788260FC228A6E3FCDD9A63B9DCD72DFDDC6CD13F4D072ACA2C702AE4EA66AAE2F3F315C6872C1415B3FB63BA095FF853BA77748260CAA37D71772B8AC40B8507D0C1ECD60BF70E44B6B40B2439F776E95CB41084F5EEF4A5BFBB85EE40F059B23406CB5505F3763D3570B9B42AC7F15EB707713F8B151FC3FE42E88EB96845B8601A3432A6CBC395D823E75013151658D082689C196137DA55CEBC3749F9C02D399A5B39DC7A23E398C08FBF15B9365FA83D6ED2B9D1B262A2A382DE9E066814E2CAD2FE44C5610160862658247EE1B478E6C078C0E335DCDE6B5AE50203010001A339303730160603551D11040F300D820B6B6579617574682E77696E301D0603551D0E04160414083B341918BC733B95B92864B57878F59EE4D44B300D06092A864886F70D01010B05000382010100176D90883EE4576E694E7ABEAE08A6CF466032FEAB42C2A919BDA0C2056B0FEBA4D64BBBA9935A1BEBF1AFAFB79A19D8454E43B97FE9E2FFBC744A7AA57C7BA35A07D903242BC15FA05DDCF2FEA6285C8296CBD58880C02D8CCE8B9A2F7537B84EA7CAD4251F2A3AFDF8AFE5B8F898AC2CD4FEC68D492D4A2497590D8BE4C3AEE4683EFF3A64EAD0E069CF2754EF84800CD9E3D74BA4FD6F486E1F6B829E50C531EEB2D03BE4B70DAD6F4A220BE2C39905E46038131D854E3480AF3DDCE07CD70896C1A21501B80CD5F92FE0FE44FF3036B0EB27333701AEA147FD757628612DEEA19C09A36B3C00E482B5B5186D7A009F036630C362EAFCCE8DBED470B73498 | |||
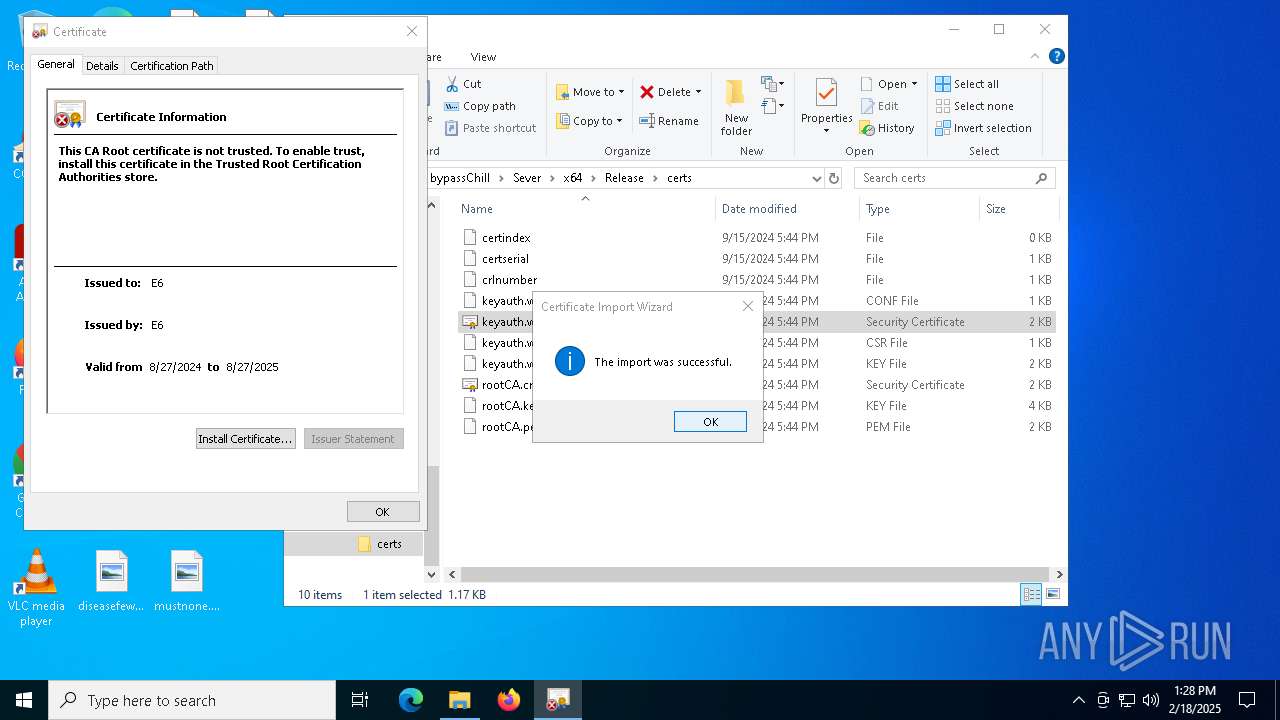
| (PID) Process: | (6808) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | ED72EB69C2652296528E0556C745CB0BB4B47CAD |
Value: | |||
| (PID) Process: | (6808) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\ED72EB69C2652296528E0556C745CB0BB4B47CAD |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000003B214D5DB3574EDC39295A92BDC6F7C80F00000001000000200000008CC225BA3A343F842CE131E1E899AEEECBA689606333AE67AF058FBF270F4DE9140000000100000014000000CE514D070120D0A1CF566514883B91EB0EFBEF891900000001000000100000002F63B7E6A0A6AE00C7B4032F44778E67030000000100000014000000ED72EB69C2652296528E0556C745CB0BB4B47CAD5C0000000100000004000000001000002000000001000000850500003082058130820369A00302010202141D4057E0A1838C7FB8D3E254D1AB74AC64938178300D06092A864886F70D01010B05003050310B30090603550406130254523111300F06035504080C08497374616E62756C310E300C06035504070C056369747974311E301C060355040A0C15476F6F676C65205472757374205365727669636573301E170D3234303930313033313330345A170D3237303632323033313330345A3050310B30090603550406130254523111300F06035504080C08497374616E62756C310E300C06035504070C056369747974311E301C060355040A0C15476F6F676C6520547275737420536572766963657330820222300D06092A864886F70D01010105000382020F003082020A0282020100DDC16BA6A694B23AFDDF7489C59DE59D20E844D428F37BE6DA0EB0A0CDF100B323836A8CB354C75D7BAAA87F22D36386A3264C3BCC08C9663A964E572D0DA7E7EB3B51B57EC74A7A0EA32B9BD33F623199DC44D1C6F33D5F1388FCBFDD91E5186BD64586B75AA93F2DEC25803C6FE1AC41AB42B56F11E1A5C7A45E3100F94AD55E8FC36BC7963327A25CD2F5730BBEF3C20DA896871017A05917582159E4748646467E21D8813D9E01E8CCC0D31B82617290880006BE579C2EACD487CCABFB2BB651DDFE9CDCF8265A2D11A74D707E599E121DB853EFB5B66BE2AFC2FD670DD142980BCB339A6951E8FB8A1AFEF6B60525B9BEC66EC7EF3AB4C207D89F616356EF26DA161D2931FB2ED429529CFC1A6587914ED8390C27531E36AC44C8E1AAFE5FEA8B34133936A2F59E038599860704328690059BE87535902D72DFF0D79728799143F46A7E83D8549EA64276508C07BF3971D273D9E51B23FB5EC8E36A9913DDBF0C40D74267DE521A404440C7BFCDCF31B214CEA922D6A8F7010736A3A0B1B30A09CDDB22DE65A9636ED17DE2142337F534CBA112AEB89D0E374BC490C2E4AE6665173B00839F70513E4C2400BEA5A1FCD4E93B1744762CD8D7278364C99F8CEAE1B3F9A6426FC253EF7D192D6D87F5F446D794512E89FECEC3A5BCAFF10F7D4B441164F704FC5698039E02A0C636EE497F51628B6417E72CAF531B73EFD50203010001A3533051301D0603551D0E04160414CE514D070120D0A1CF566514883B91EB0EFBEF89301F0603551D23041830168014CE514D070120D0A1CF566514883B91EB0EFBEF89300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382020100C5BAD472ED19B7967102E4E7D6C0C701B7910BBE2B83EFB46833F8AA1BB8AAFD68D9D1D0CEC9EF84B523CA393A29DE51D1B762F7D8746E5D178C4A77BE4F5E5AE5D139977A5564C5A3BDA57FE59F03458F2BA85D816EF24C5A13E83423F57CFCBD2F425120DB7E3611669926D68B0B4311D76164DC29AD1ECBE9225545528EBB45984C11E08892BA7CABBF076307B83A7B4E07FC1BBBFC6CA940C9828A0FE4BC124883F36B42D7262400631E97F4AAD83A215A943F2AA0E48172D710B018E9186DC031A839AED5A4449E95F8280A415A61821C0C26C6F4F868D57C21677E2126383B1B04A1E24B4558E489EE7FE4AF6DD21ECE9DEC10B1D6FAACCC8EFF208E9683DE75461E57C4A278DFCA21856A68E8EF917BA901B282EB711BD5FCC323070D65E48731AA7C623276FBD4E3011D1F00D07C05A8E875397ED7A68379E98CD0E4708C934E7123E526DE0992CA0ABF3B9973704F7BA2B1B5694AEDB8B42FA9D11D579A9C9C4D1AAF2C3CB246DC10A622713D51AB3627E08BDA1053F478FBECBD9D1D55CAE80BC0217C1E79423B4D13B611749ED62FD5A03DC8E0087D213F157B36F2B9D2C04803FE6FD3D017F3F12F1A6B0BFB92082CA688C1EBB149DAE35B86F6555E0FCA770F7E4ACEC75CE76431A1191AA6418C191FBDF6CBA9E7454ADA5FBF19877573F8D226F858DD4E37847EC69F93304F3BC0AE82E5882EC034326C6890 | |||
| (PID) Process: | (936) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.1!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_CA_REVOCATION | |||
| (PID) Process: | (936) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.2!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_END_REVOCATION | |||
Executable files
5
Suspicious files
2
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\PROMAX VGC.exe | executable | |
MD5:0654A7E272D5823C3D0C77A76BC75966 | SHA256:7CD8C3F2A419CA58D827F84E74BE2702ACA0B34C75AA08C0B6F86F22E093B6F1 | |||
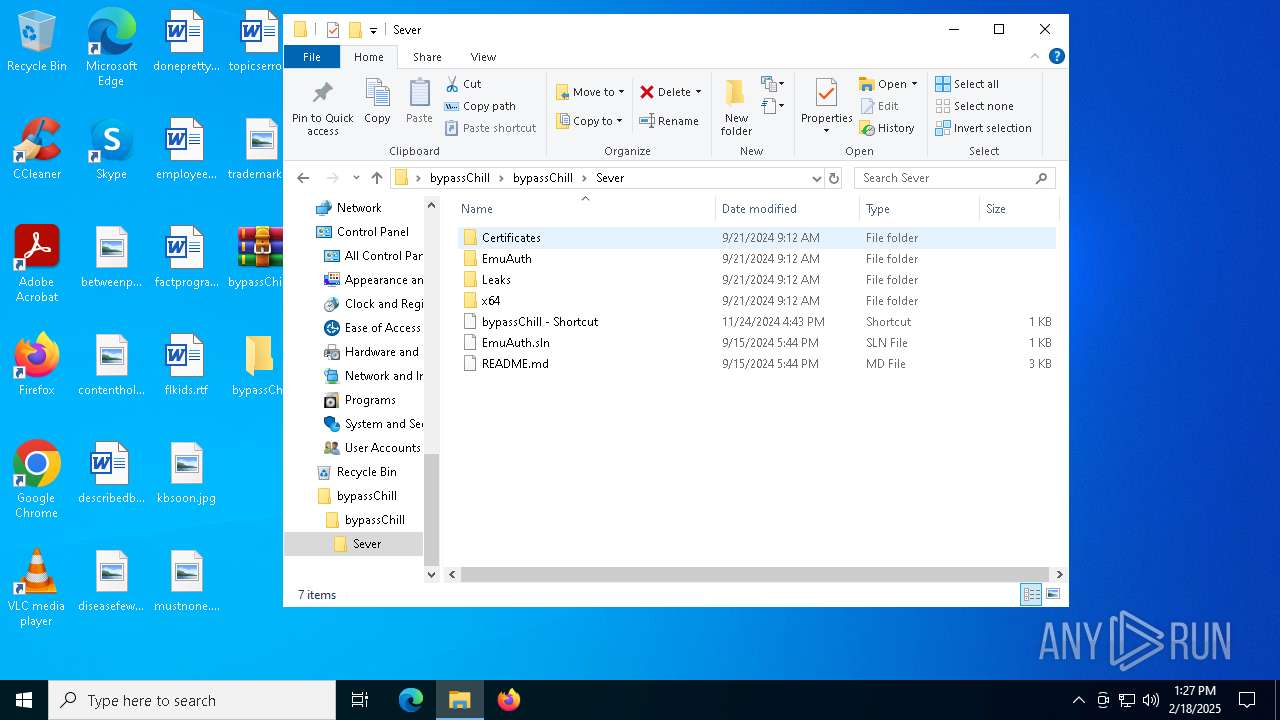
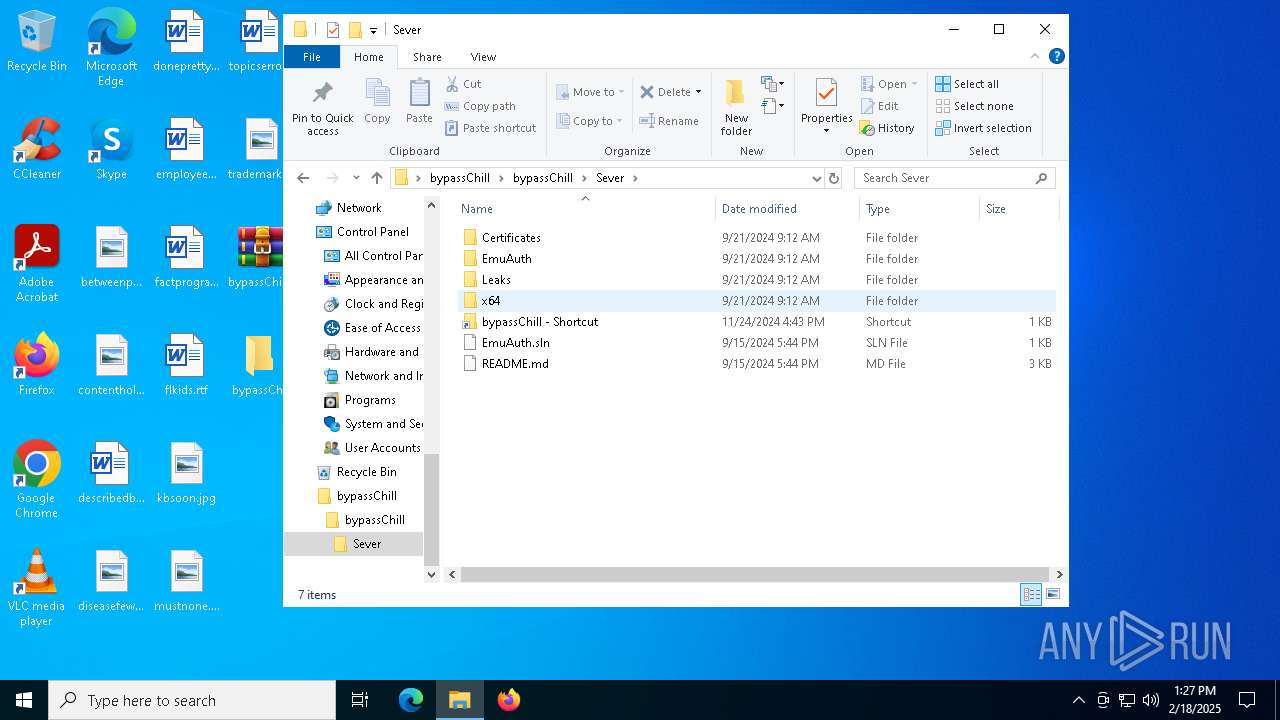
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\EmuAuth\Library\hmac_sha256.c | text | |
MD5:D9A7AB190C01B5FB681884D61E4EE2D4 | SHA256:15272F2982D8FEE5892F4320E9E69DC0B2D9C7C69438EE0FC65172E75FF63426 | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\bypassChill - Shortcut.lnk | binary | |
MD5:DC09EE5F5030B6634D12809297F31436 | SHA256:6893875AD2C3F4E9315280FFD68675E1DDC4F4A9B0552CE81ADD7130FA78496F | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\Leaks\1337.rar | — | |
MD5:— | SHA256:— | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\EmuAuth\EmuAuth.vcxproj.user | xml | |
MD5:244D056F5E959BE6D9A2F7E94686F1C8 | SHA256:C06A75B13F855A94D46616796E024C52B499F8F92CF00CCB571DDBC6FF574676 | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\Certificates\generate-certs.sh | text | |
MD5:CFBABD8034B1B13E82DC7E9E7DE3FD03 | SHA256:A559DCD94B5DC389F518ACD1F856E11E3146D1891A9026FB8691FF342836F447 | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\EmuAuth\Library\json.hpp | text | |
MD5:30B66ABABCEB852EC47ECF93FD370B8D | SHA256:9BEA4C8066EF4A1C206B2BE5A36302F8926F7FDC6087AF5D20B417D0CF103EA6 | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\EmuAuth\Library\sha256.c | text | |
MD5:29728E8BC1EE68DE8232B3630097D838 | SHA256:9560343C656DE49FB6A9C69DE618E1AD5B051A18B35AA43620755EB1DF5814DC | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\EmuAuth\Library\hmac_sha256.h | text | |
MD5:C09B971A32AF01CDF653B529D5EC17EB | SHA256:1FB1A921AC3720F9D89A7CCC1F3D213DCE1D46953B73A1951F97F54DE5F51DAA | |||
| 4320 | WinRAR.exe | C:\Users\admin\Desktop\bypassChill\bypassChill\Sever\EmuAuth\Library\sha256.h | text | |
MD5:BEB6FD465FED9863457056891135FCAE | SHA256:FD01C2BA6F62619F3C0A7D9BDA2B4FB1FA4787316AD3CDE154E6B6570B2E00C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
37
DNS requests
24
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3928 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3928 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6176 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
760 | lsass.exe | GET | 200 | 2.18.161.41:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.110.168:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3928 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3928 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3928 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
2996 | PROMAX VGC.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
5212 | PROMAX VGC.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
5212 | PROMAX VGC.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |