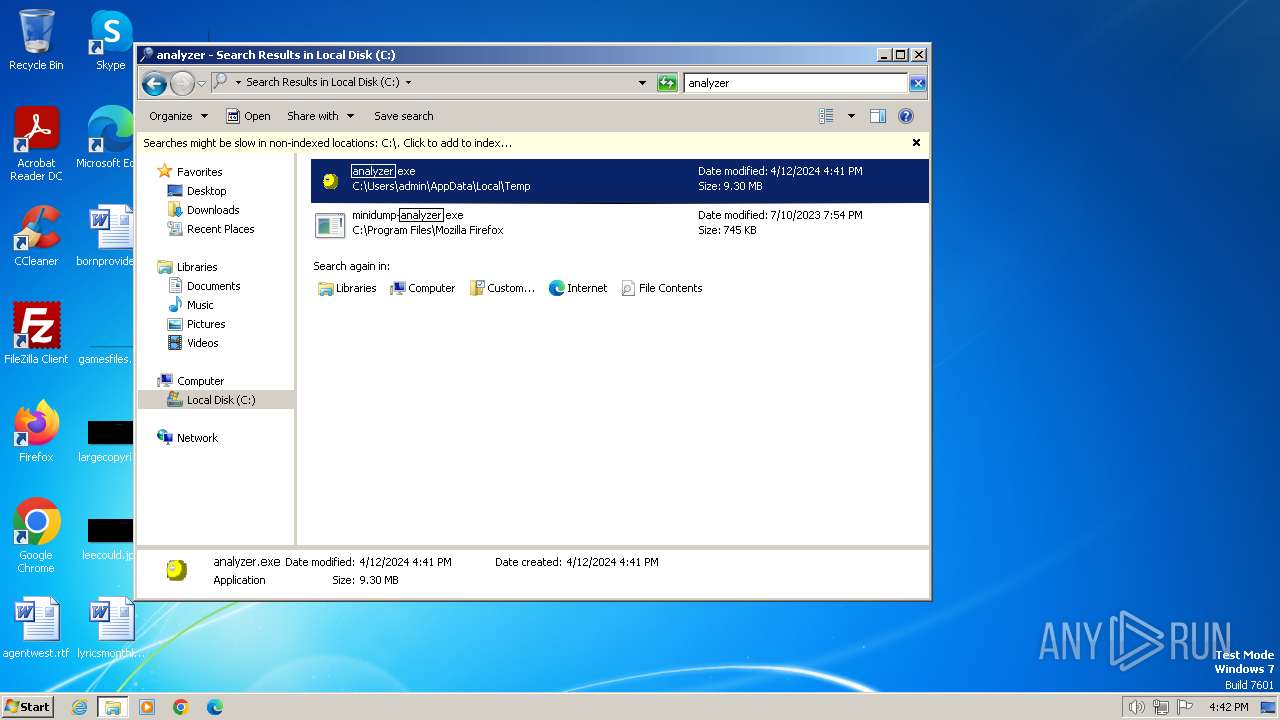
| File name: | analyzer.exe |
| Full analysis: | https://app.any.run/tasks/6cf6a8e8-7ec1-40a3-929d-6984b6eecb23 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2024, 15:40:59 |
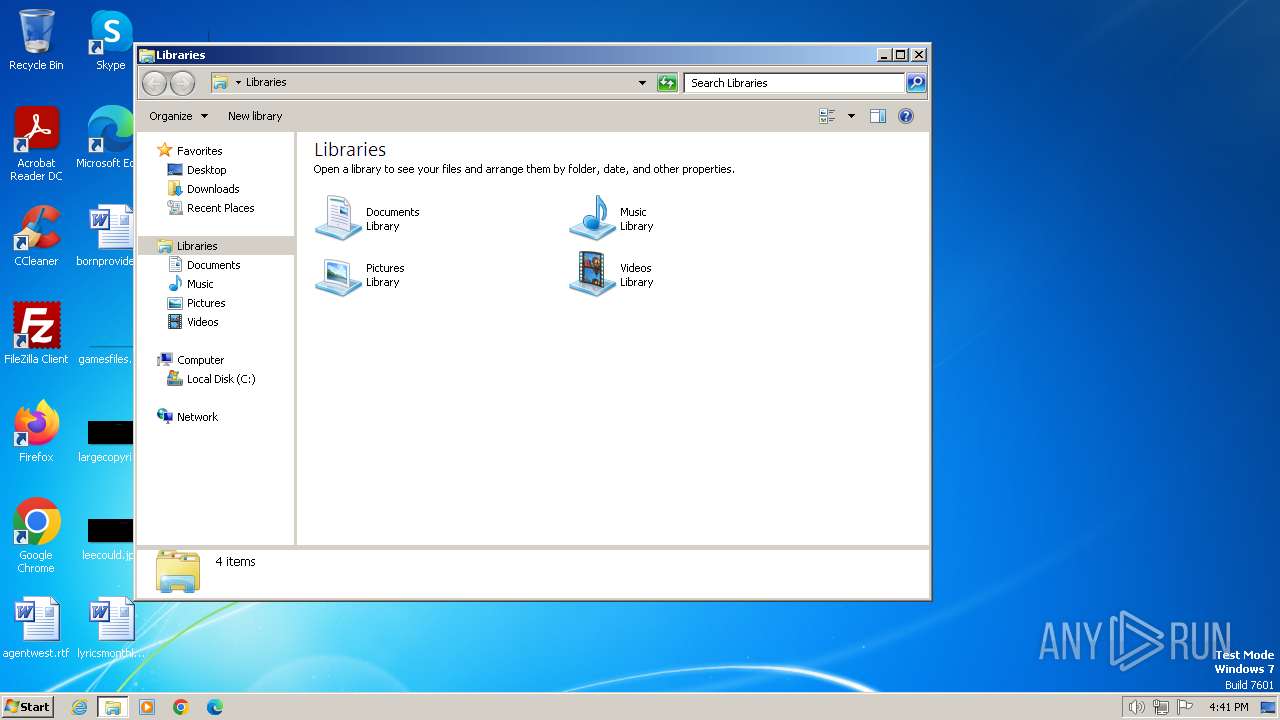
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
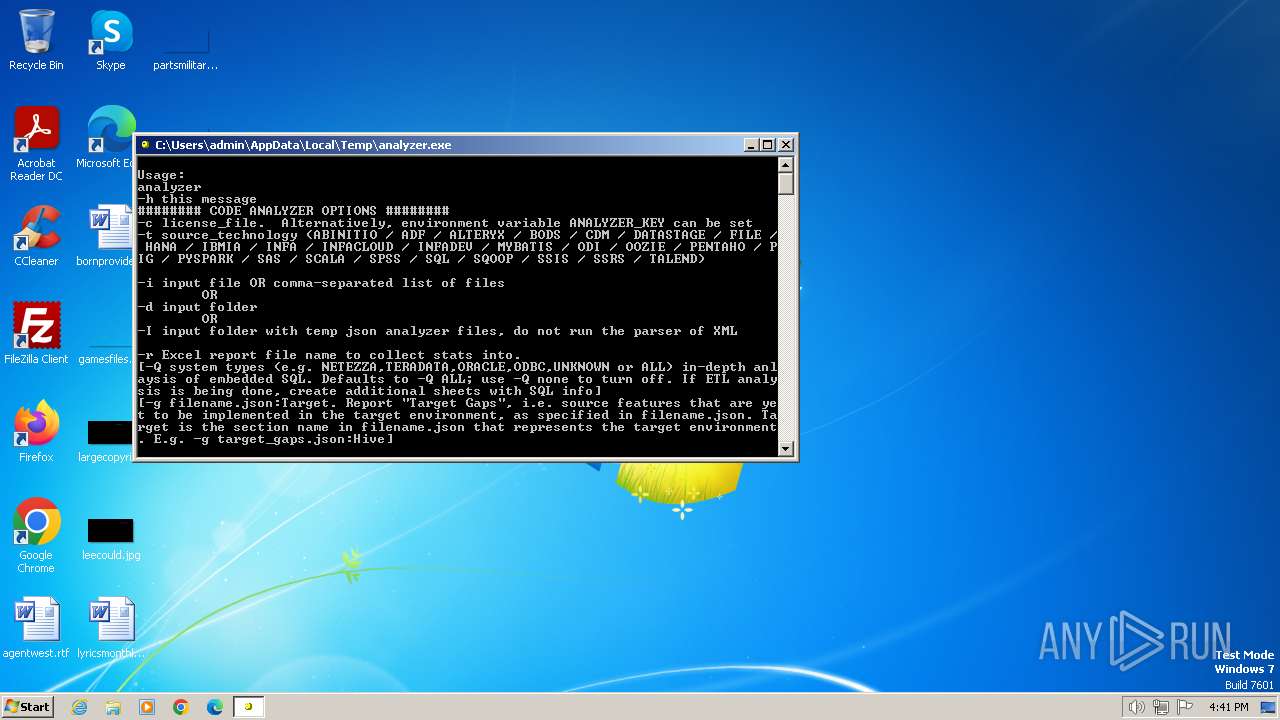
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 4F799AB5B393E7B8384EA66F3FFFE899 |
| SHA1: | 3E8EA813CFBABB39E408BC3AED83CD75B3462AAB |
| SHA256: | 22ABB209A2109D79012353006E0506398FA8F4CE961C1491B166D1E46EE1C2E3 |
| SSDEEP: | 98304:zMeACc8L+rw/mMVx6vLmdXPL+tFWAl9Sd8aejqDIbOmIqbo2JaxbbdFBlkflNwLN:fjUkRpxy+XBNjHeh0h |
MALICIOUS
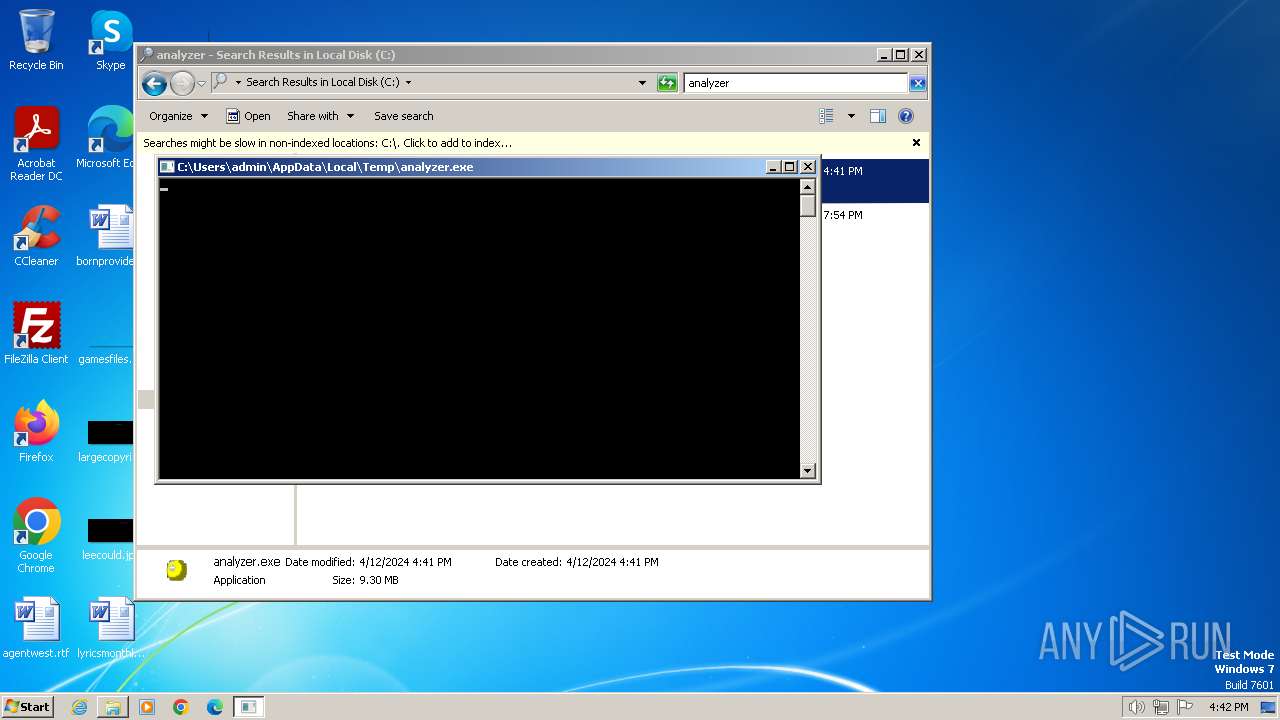
Drops the executable file immediately after the start
- analyzer.exe (PID: 4060)
- analyzer.exe (PID: 1368)
SUSPICIOUS
Executable content was dropped or overwritten
- analyzer.exe (PID: 4060)
- analyzer.exe (PID: 1368)
INFO
Checks supported languages
- analyzer.exe (PID: 4060)
- analyzer.exe (PID: 1368)
Reads the computer name
- analyzer.exe (PID: 4060)
- analyzer.exe (PID: 1368)
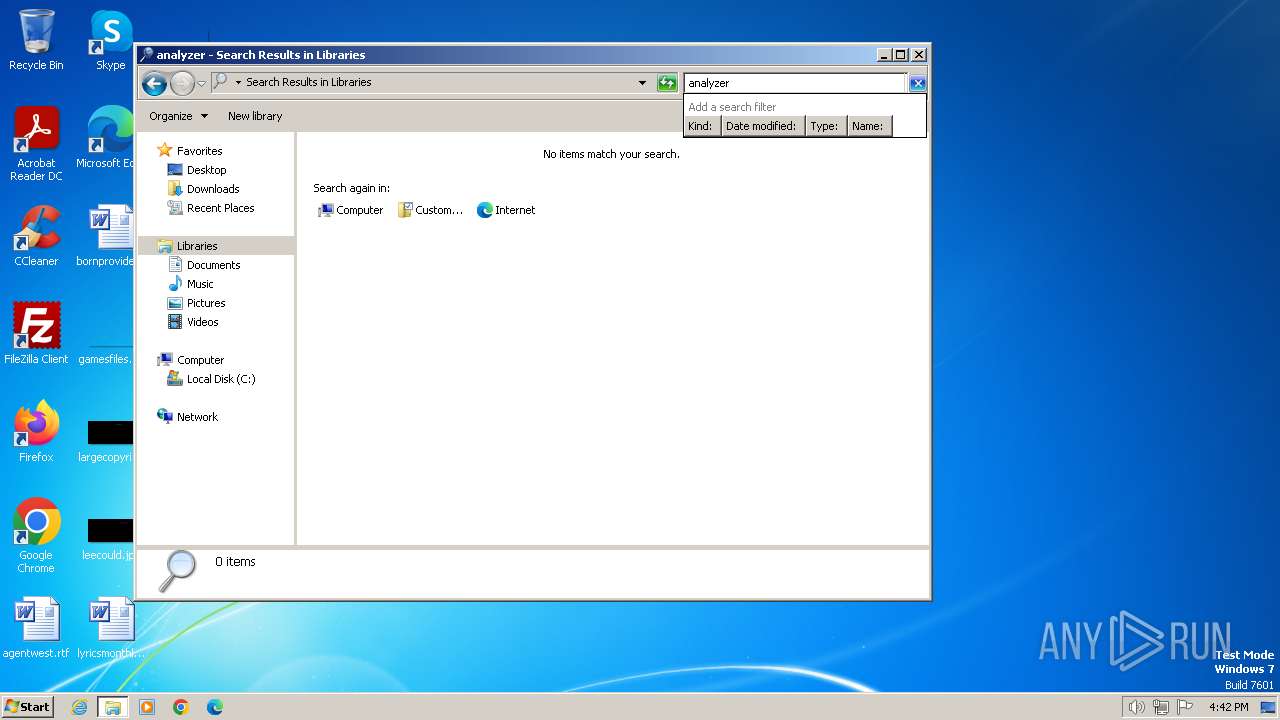
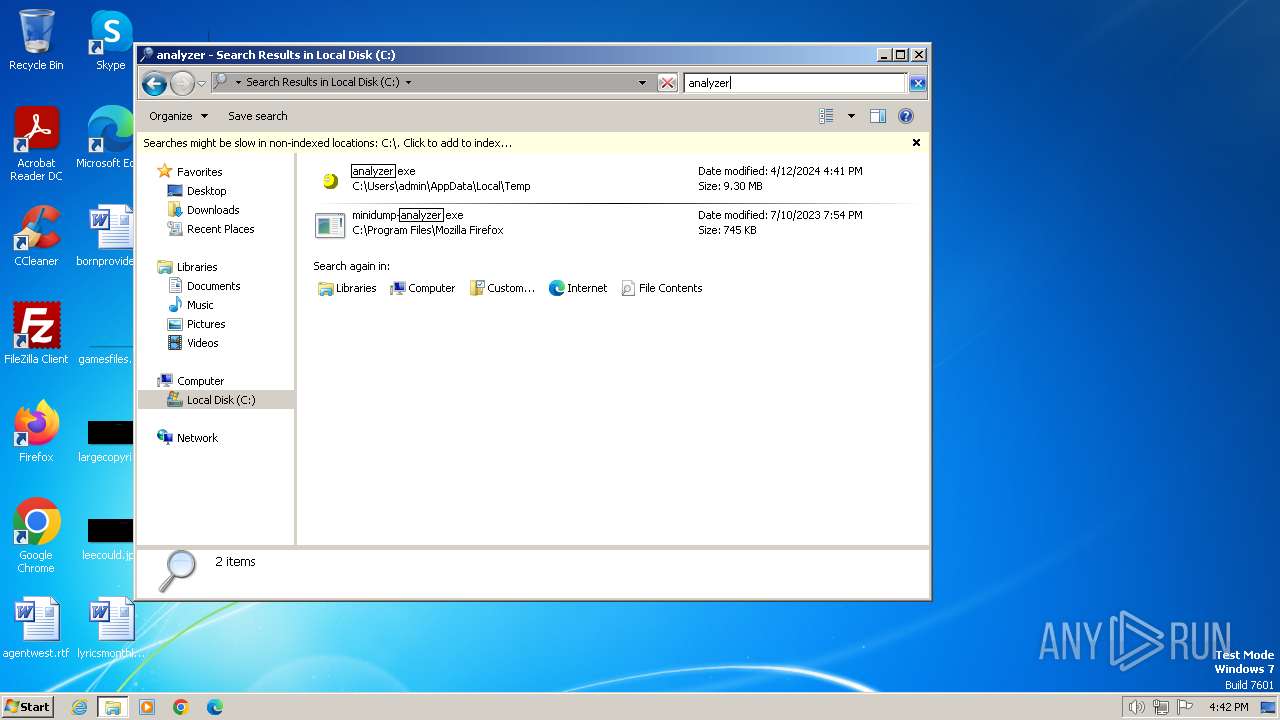
Manual execution by a user
- explorer.exe (PID: 1692)
- analyzer.exe (PID: 1368)
Create files in a temporary directory
- analyzer.exe (PID: 1368)
- analyzer.exe (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (25.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (22.8) |
| .exe | | | UPX compressed Win32 Executable (22.3) |
| .exe | | | Win32 EXE Yoda's Crypter (21.9) |
| .exe | | | Win32 Executable (generic) (3.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:08:11 17:11:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 8192 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2196 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | - |
| Comment: | - |
Total processes
41
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1368 | "C:\Users\admin\AppData\Local\Temp\analyzer.exe" | C:\Users\admin\AppData\Local\Temp\analyzer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 255 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1692 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Local\Temp\analyzer.exe" | C:\Users\admin\AppData\Local\Temp\analyzer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 255 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
245
Read events
245
Write events
0
Delete events
0
Modification events
Executable files
78
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\p2x5142.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\Data\Dumper\Dumper.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\List\Util\Util.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\re\re.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\Cwd\Cwd.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\Win32API\File\File.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\Fcntl\Fcntl.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\Win32\Win32.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\Win32\Console\Console.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | analyzer.exe | C:\Users\admin\AppData\Local\Temp\p2xtmp-4060\auto\B\B.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |