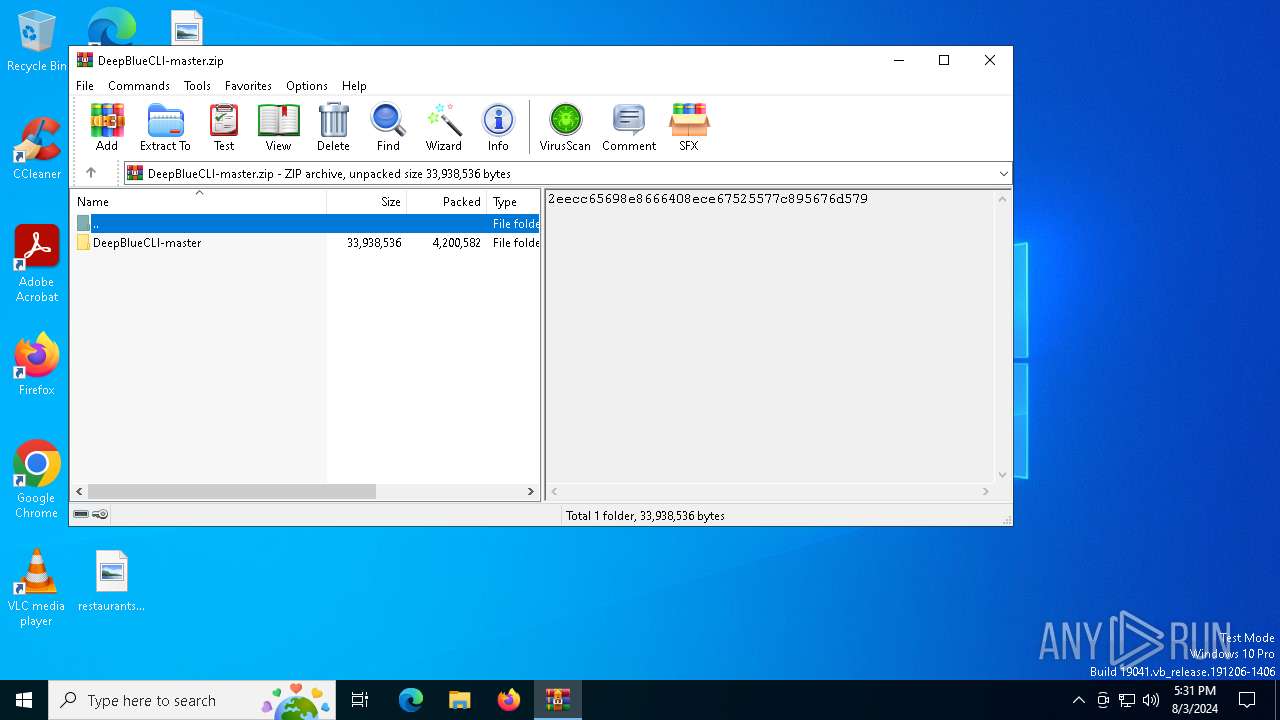
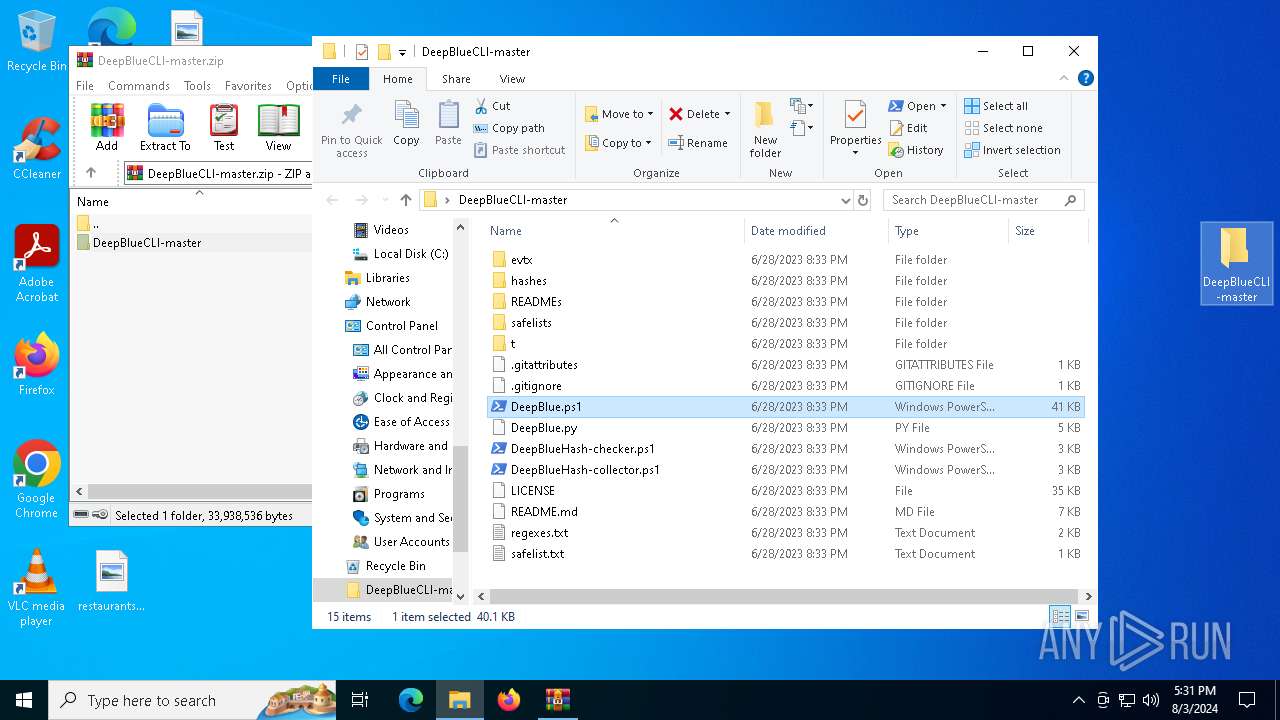
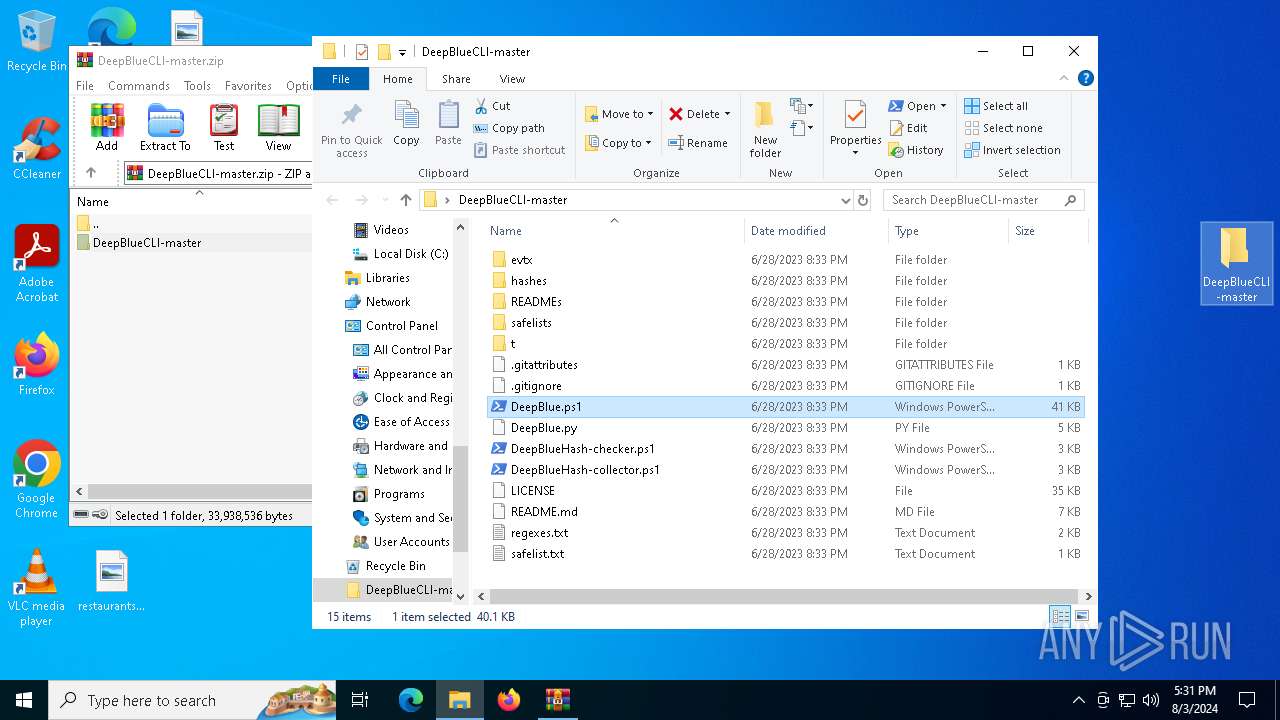
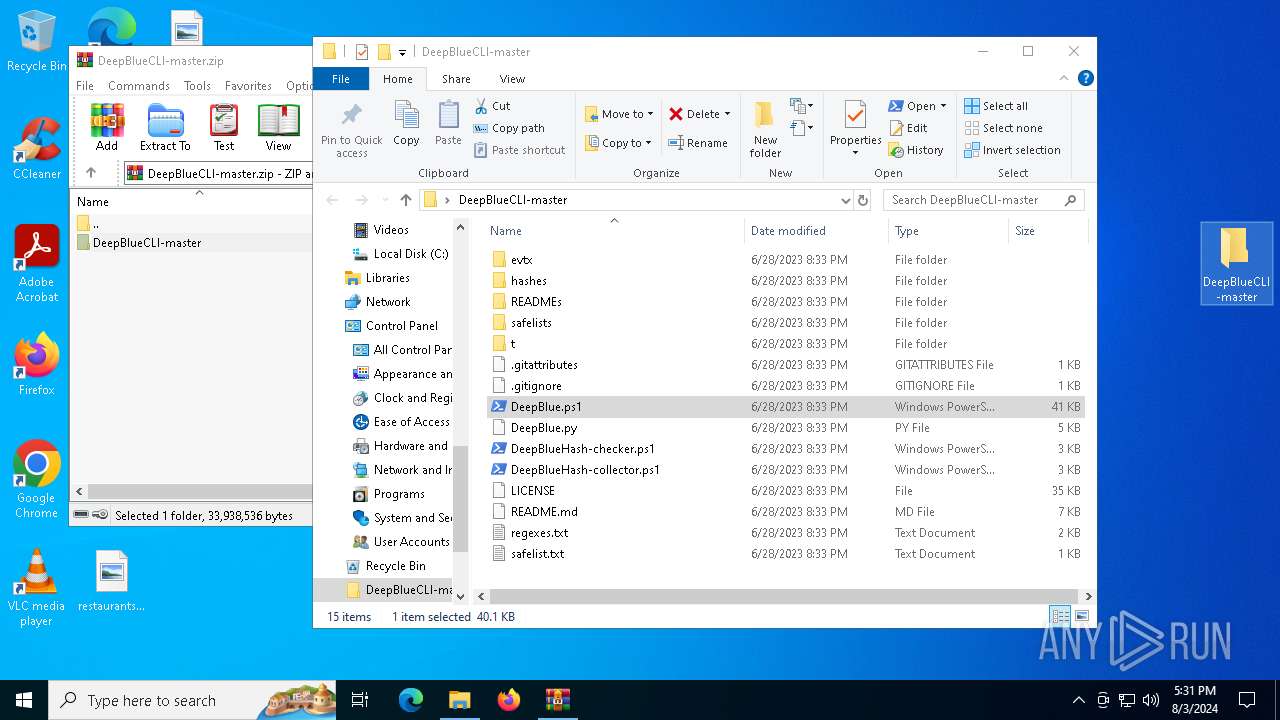
| File name: | DeepBlueCLI-master.zip |
| Full analysis: | https://app.any.run/tasks/f98ddcb8-4416-4a24-bf20-74e93af2035c |
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2024, 17:30:49 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 38A9BAB10238ECB9D83FB253EFE63ECB |
| SHA1: | F1CBA9D37C75AD4CCCE6CC4443838D3E16DD544F |
| SHA256: | 2295C0E92697A8F5425F20E4119F7A049428C2A47AF48F88ABABA206309DEE51 |
| SSDEEP: | 98304:QrrbSkWpyqYIPEPJWWoKhXzMaN4JINXzfXFbit85AfijZwY4UicpwQ0LMRJ22sSq:WZZzGWHXq |
MALICIOUS
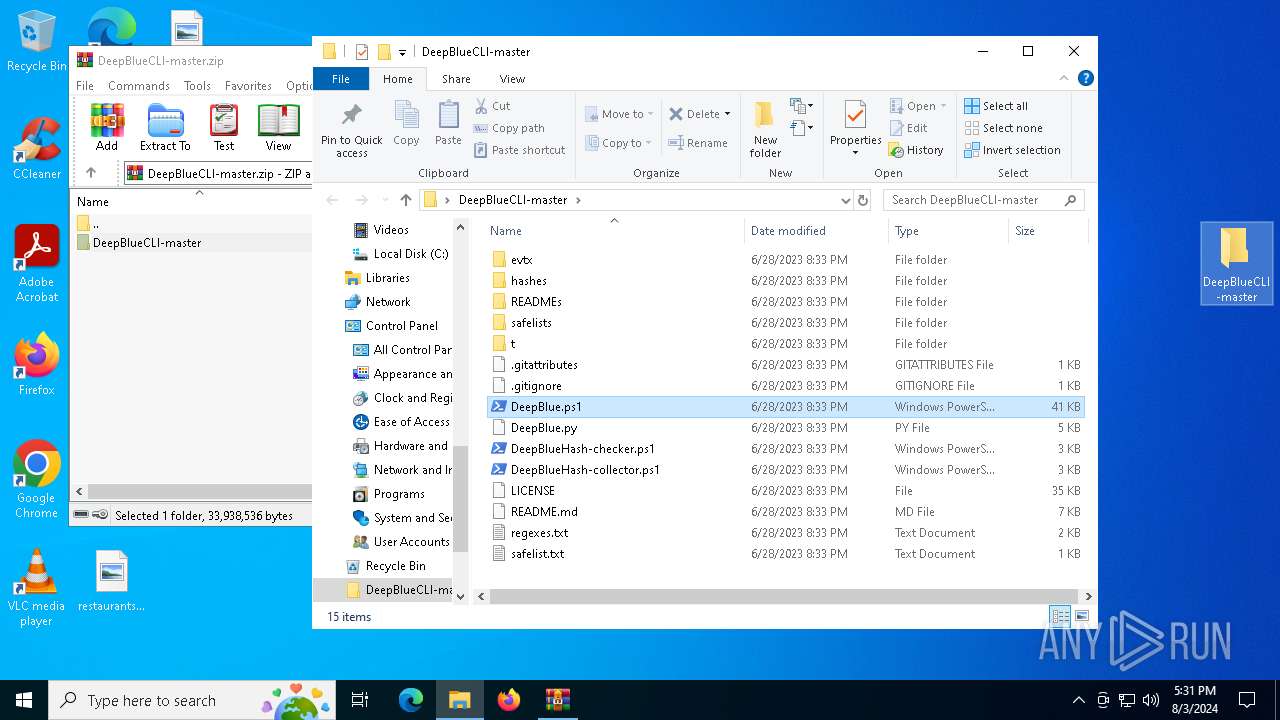
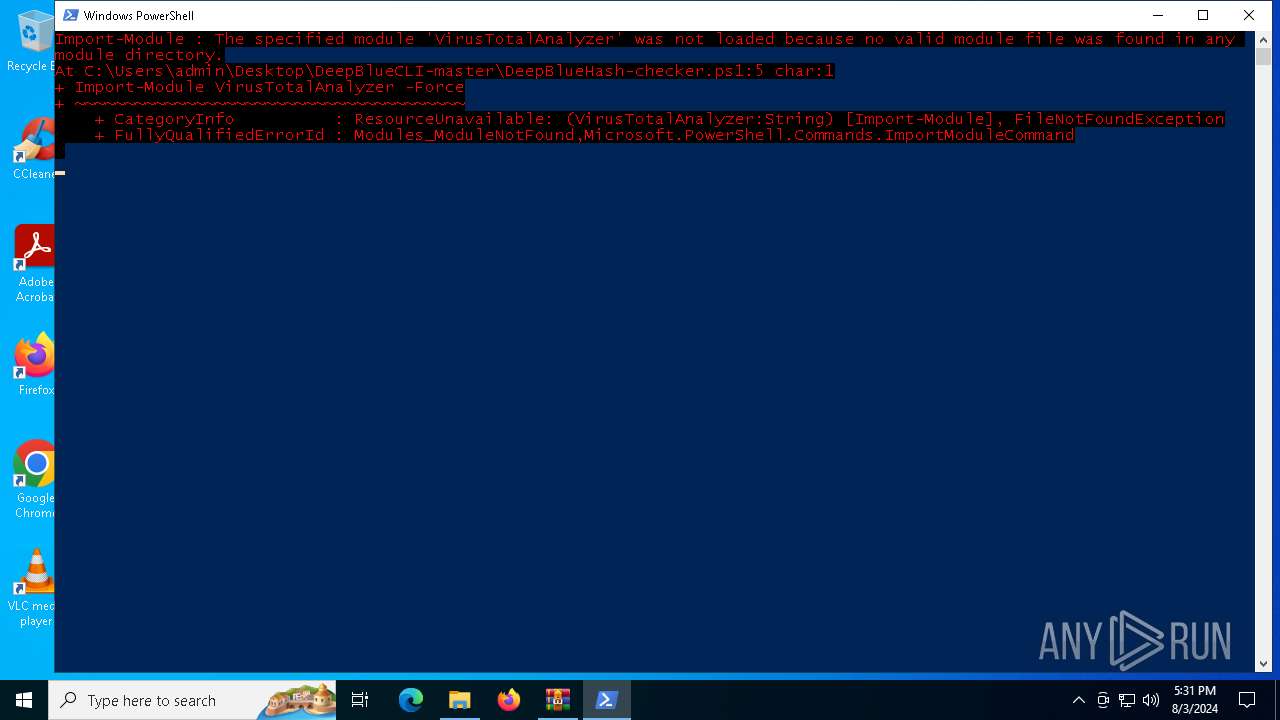
Bypass execution policy to execute commands
- powershell.exe (PID: 6960)
- powershell.exe (PID: 6340)
- powershell.exe (PID: 2928)
- powershell.exe (PID: 6896)
- powershell.exe (PID: 6956)
SUSPICIOUS
No suspicious indicators.INFO
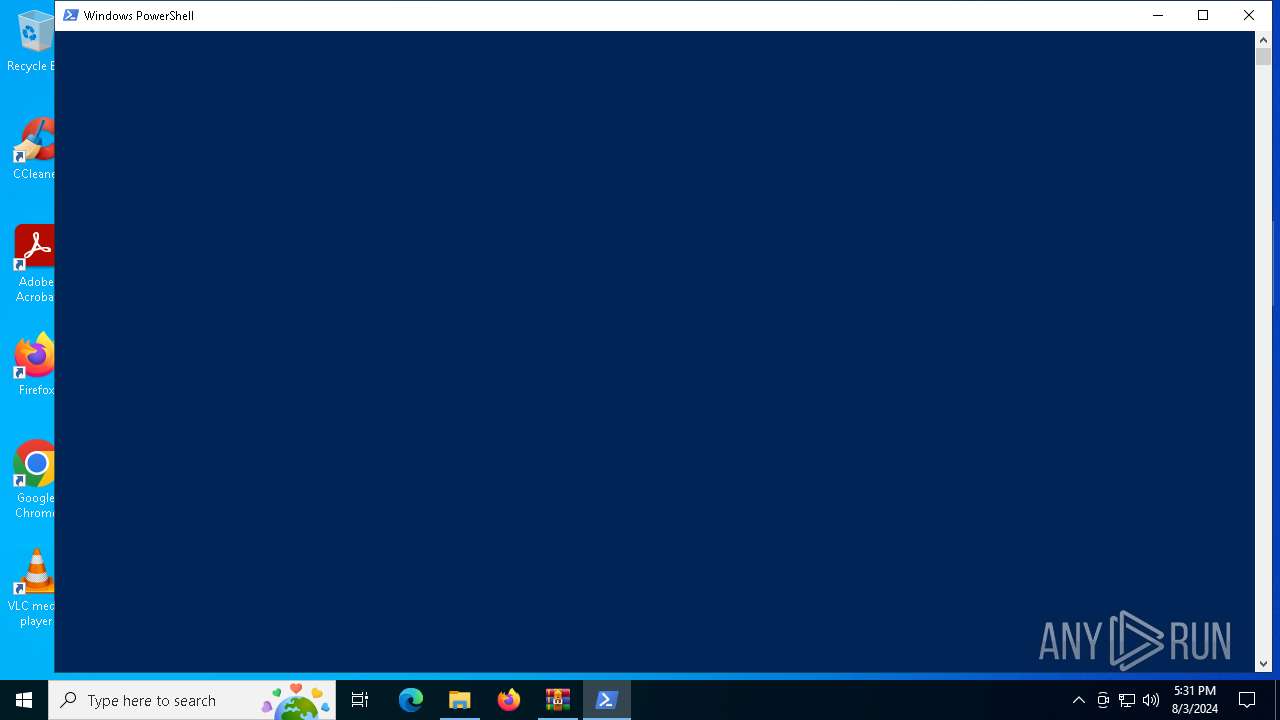
Manual execution by a user
- powershell.exe (PID: 6340)
- powershell.exe (PID: 6960)
- powershell.exe (PID: 2928)
- powershell.exe (PID: 6956)
- powershell.exe (PID: 6896)
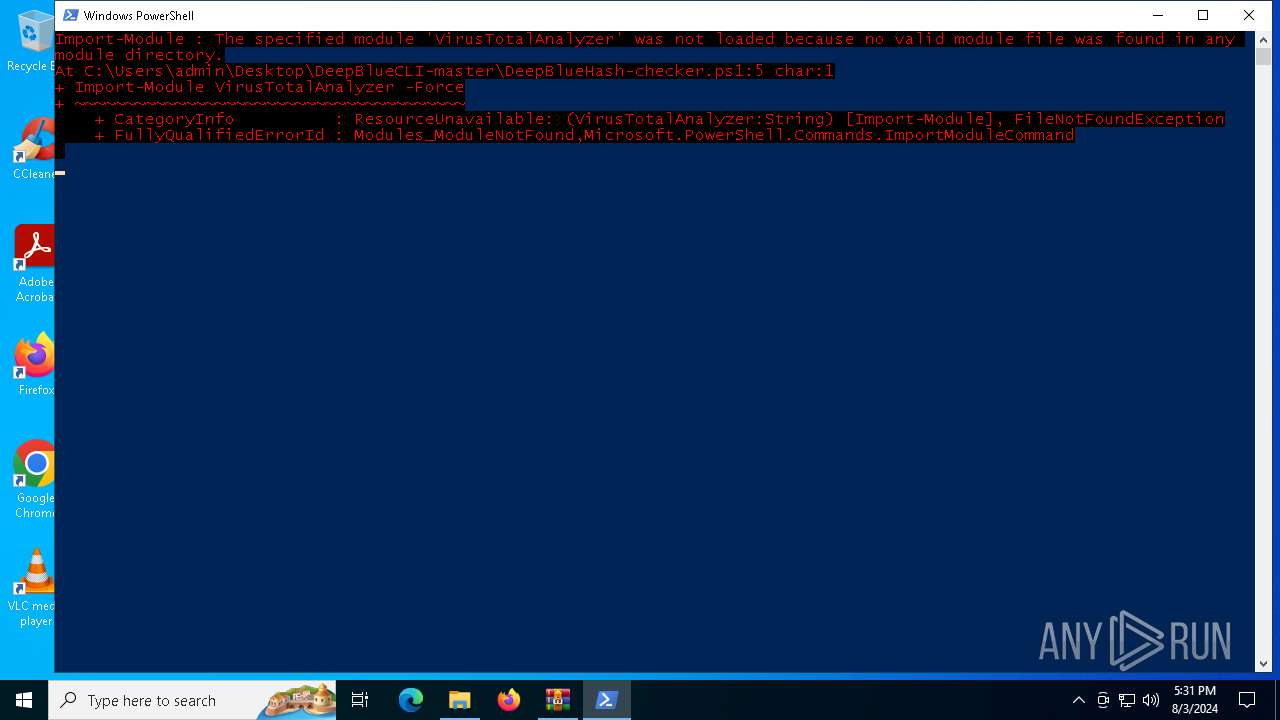
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6340)
- powershell.exe (PID: 2928)
- powershell.exe (PID: 6896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:06:28 13:33:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
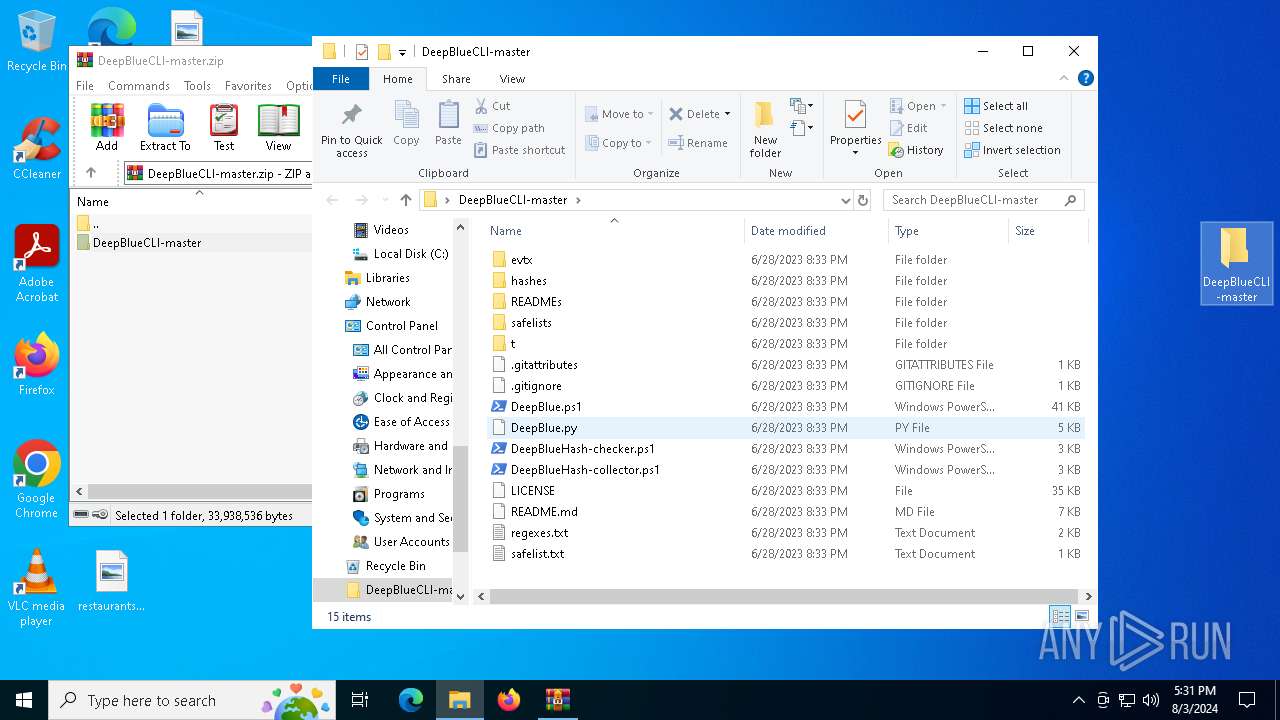
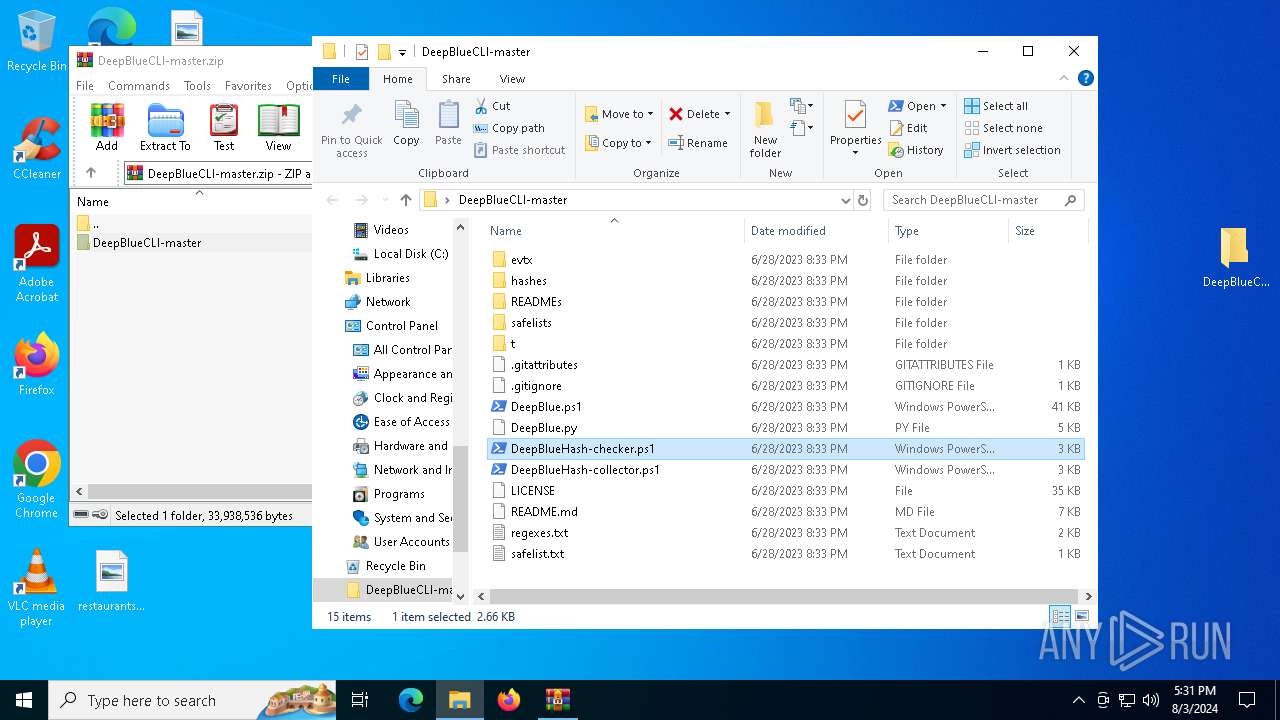
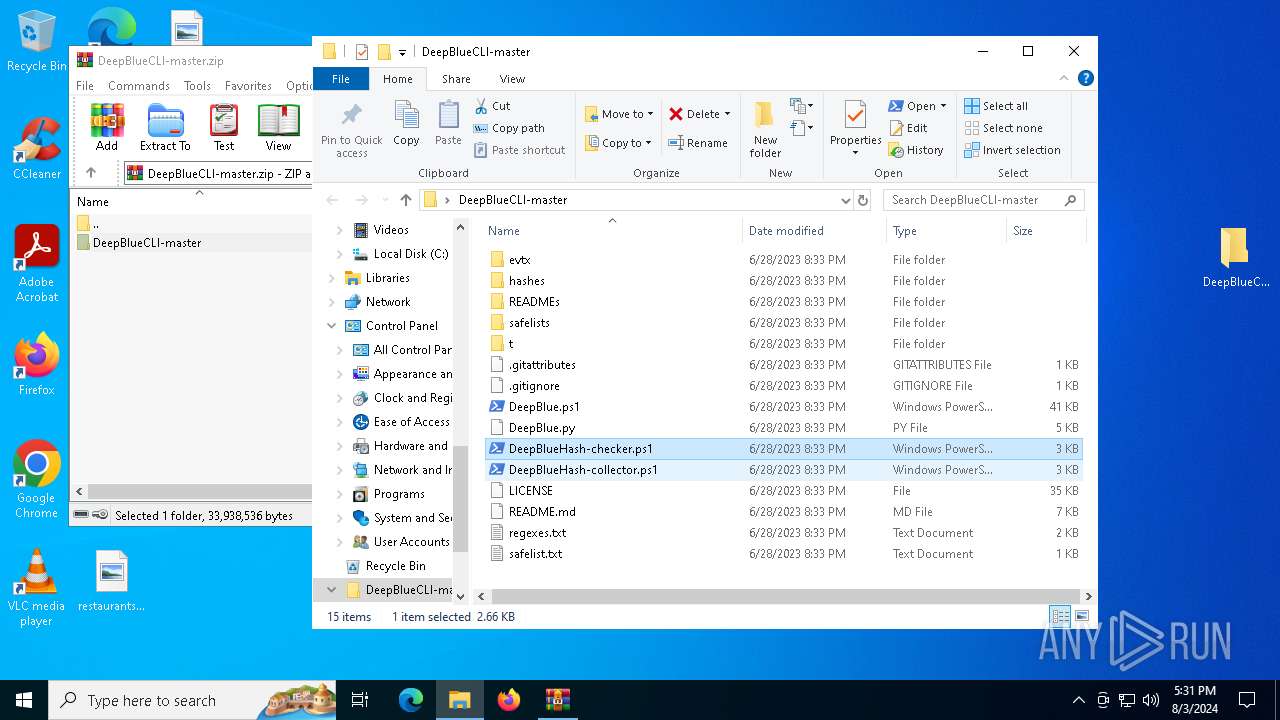
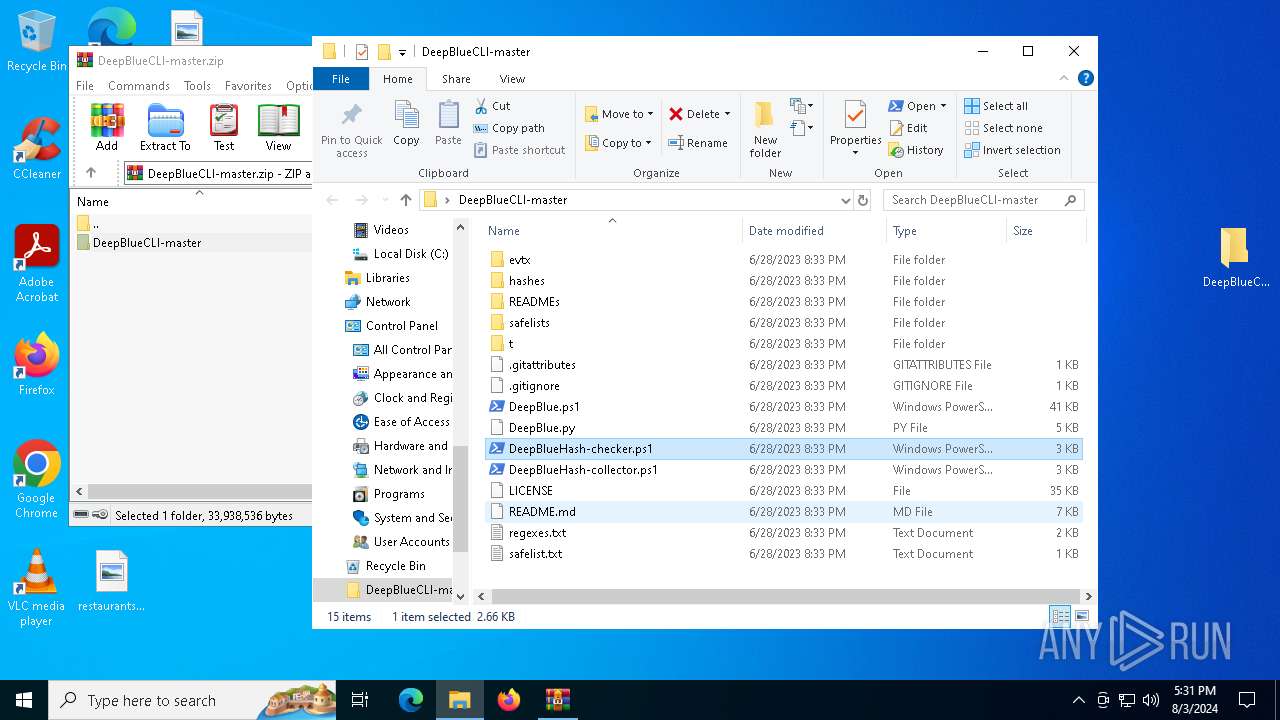
| ZipFileName: | DeepBlueCLI-master/ |
Total processes
147
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
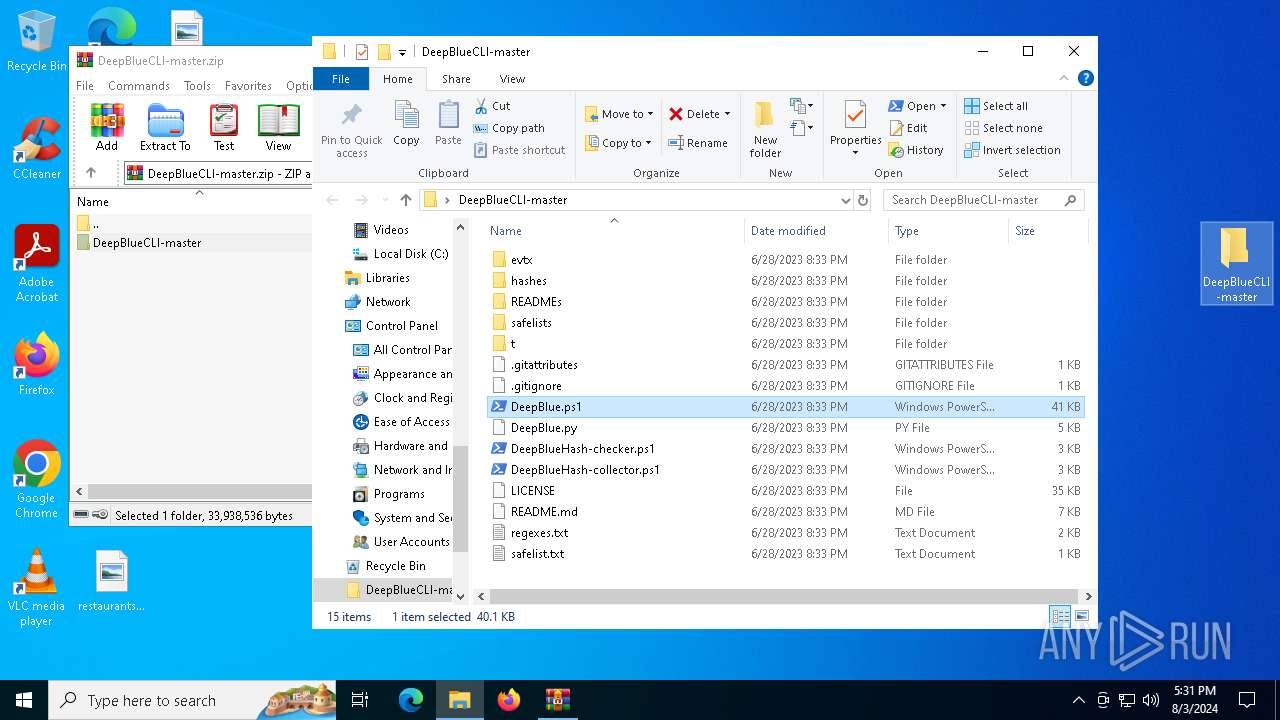
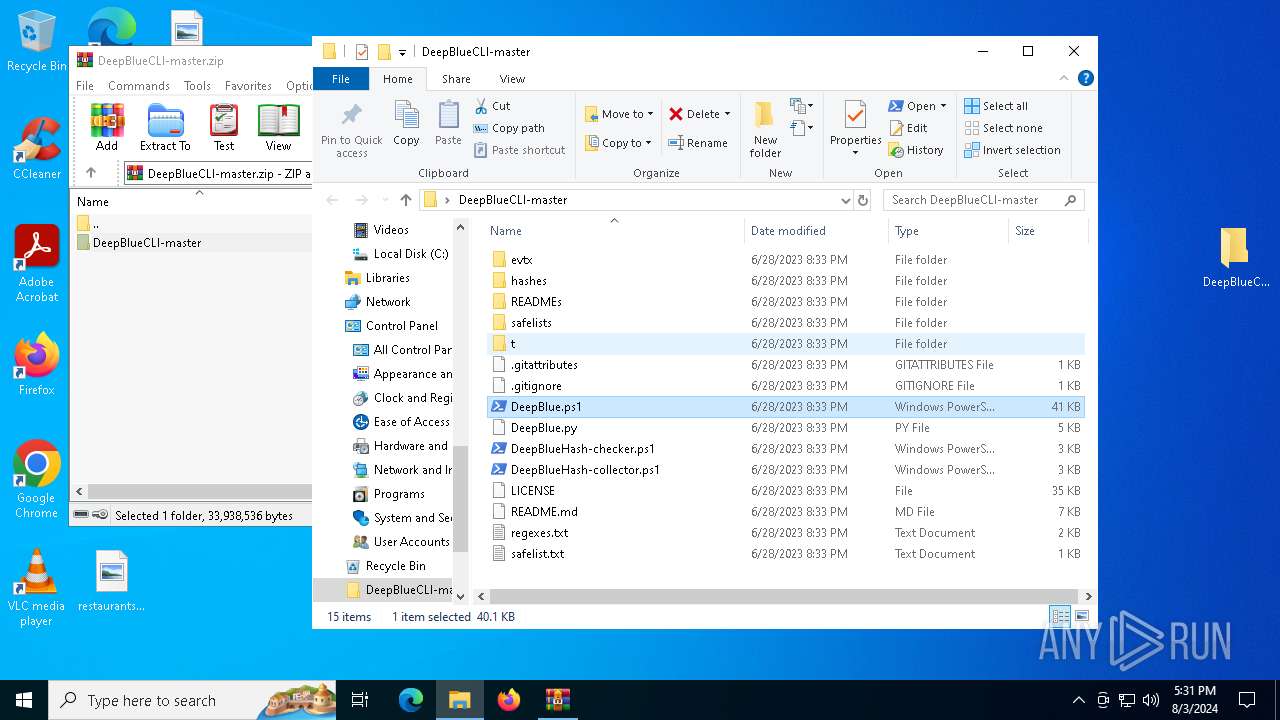
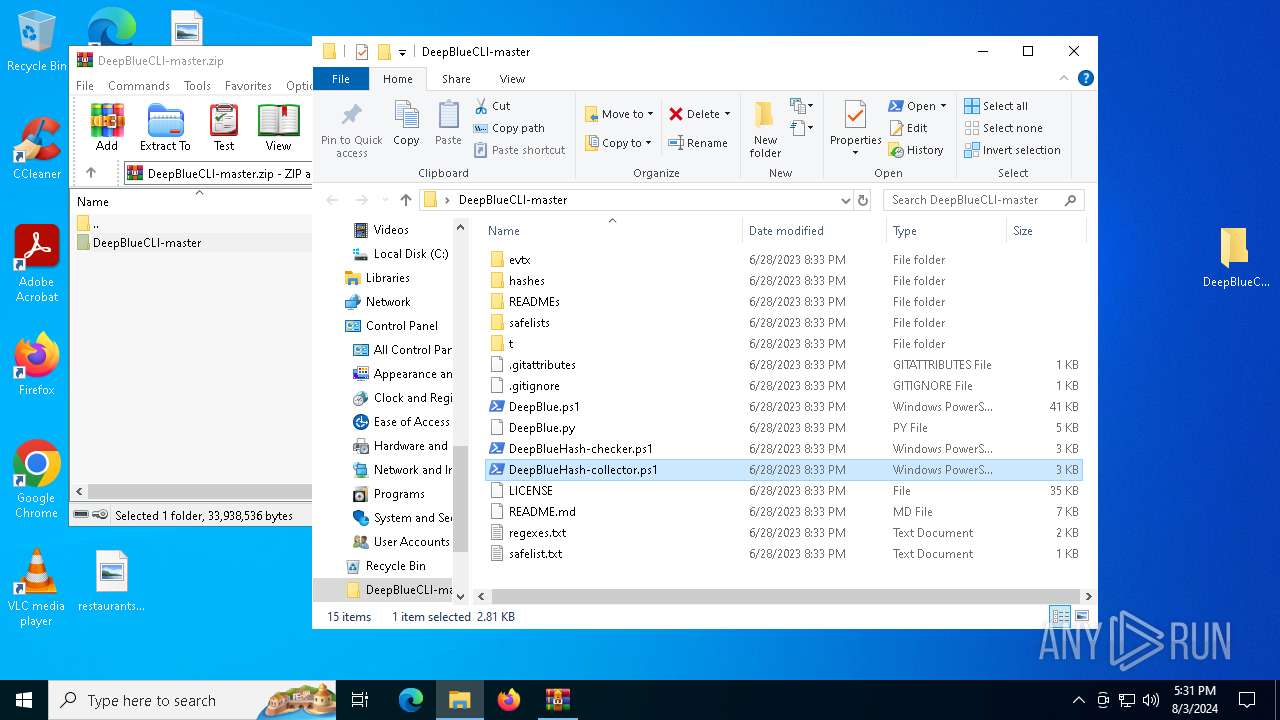
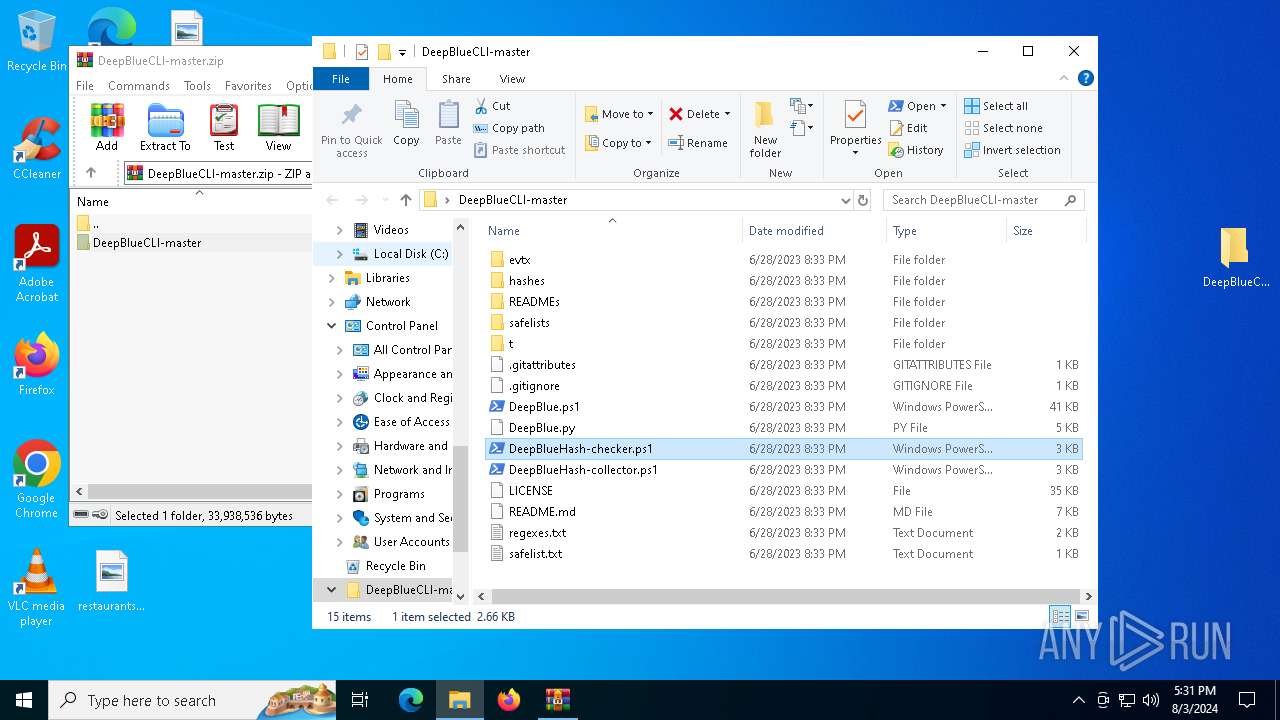
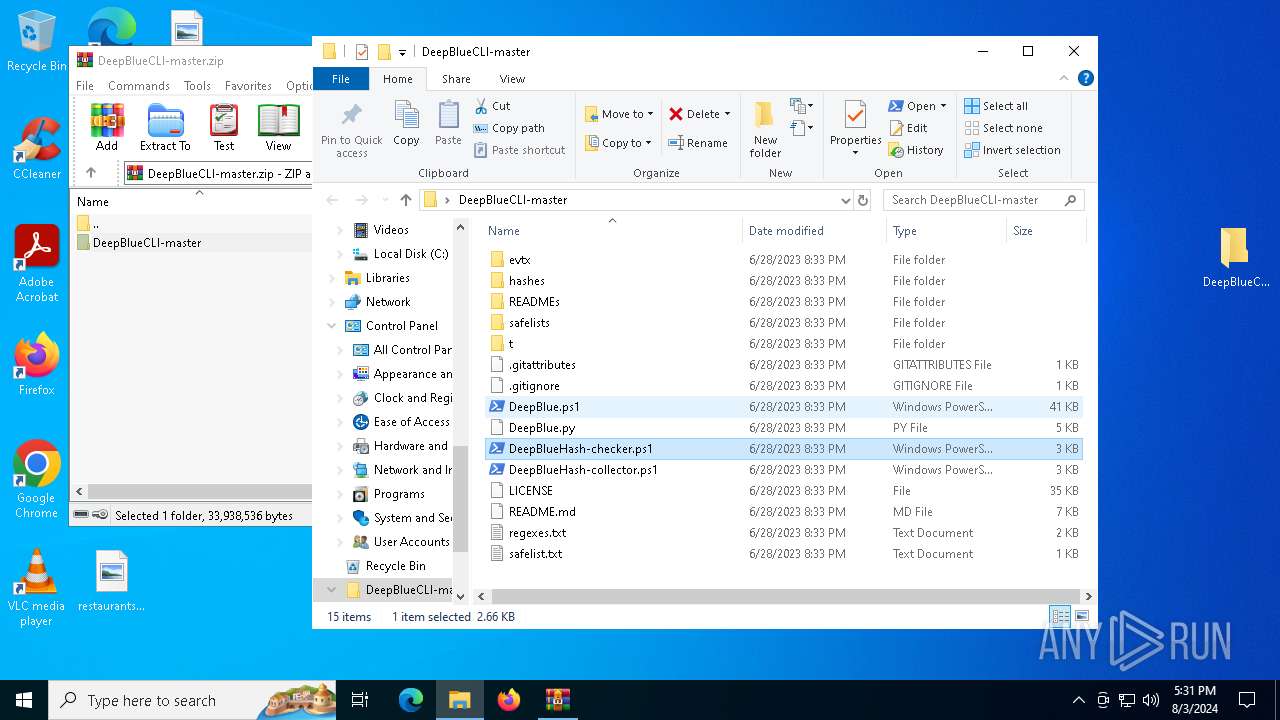
| 2928 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\DeepBlueCLI-master\DeepBlueHash-collector.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
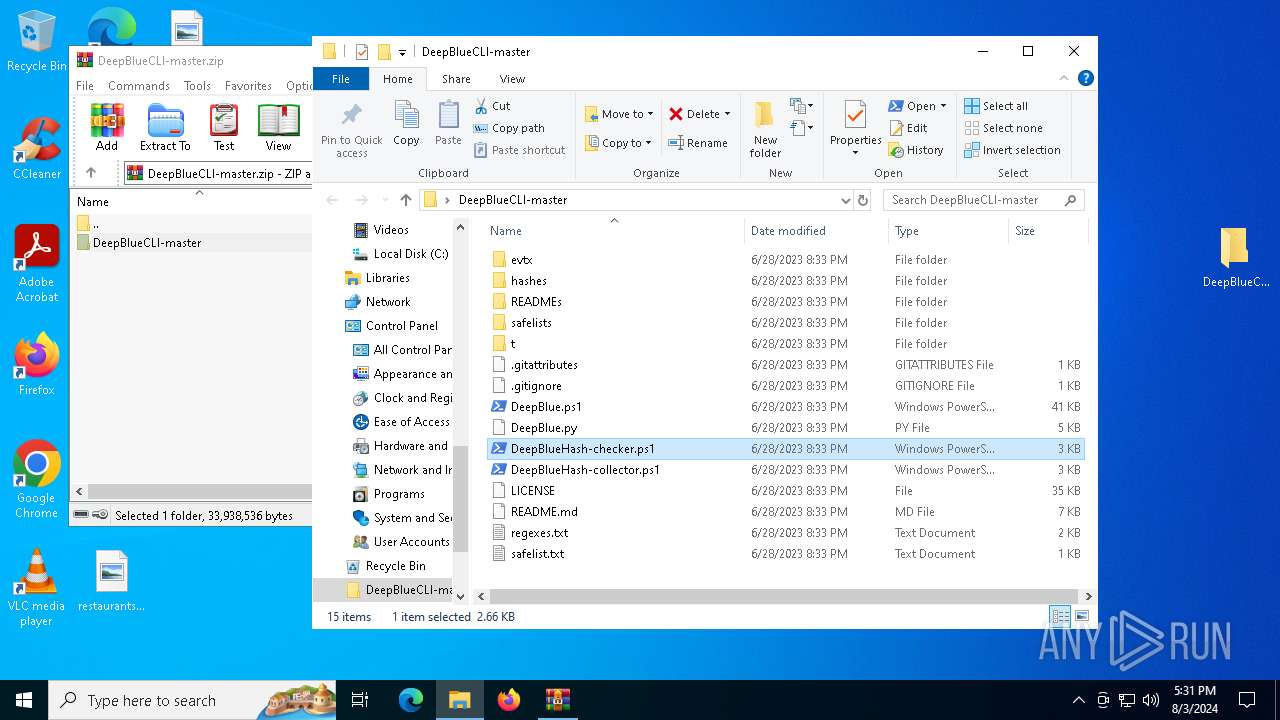
| 6340 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\DeepBlueCLI-master\DeepBlueHash-checker.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6392 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
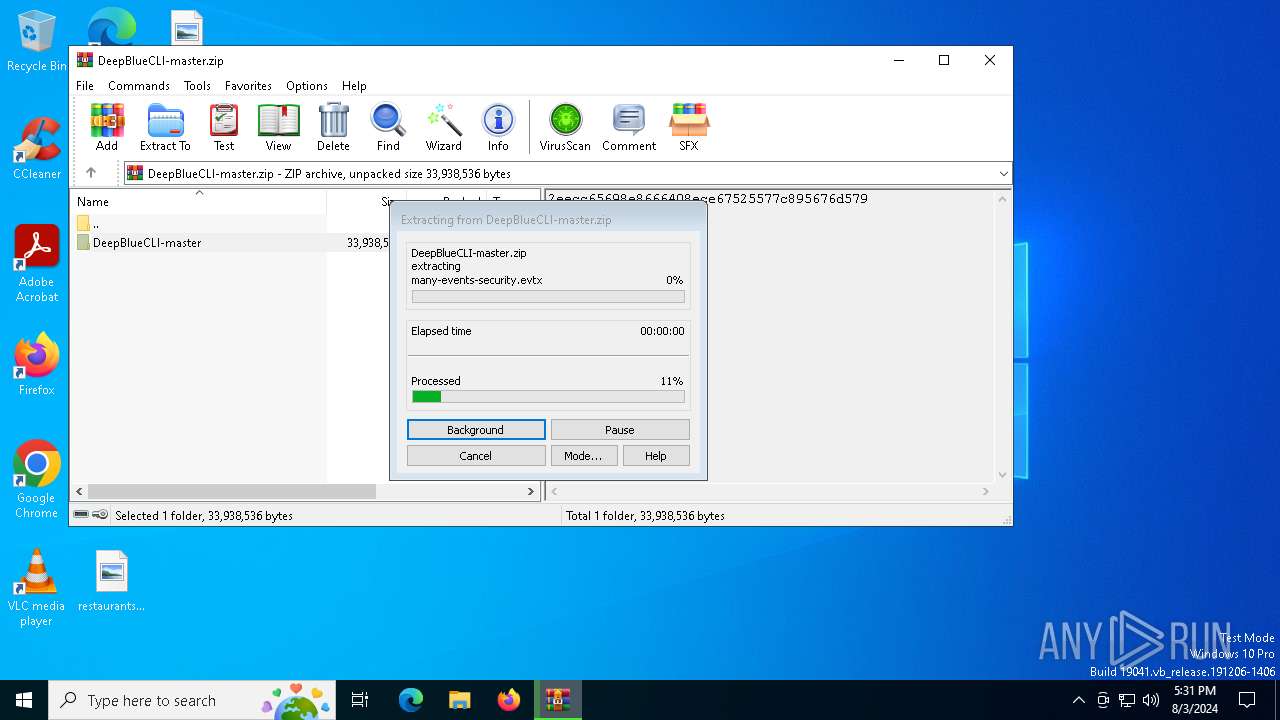
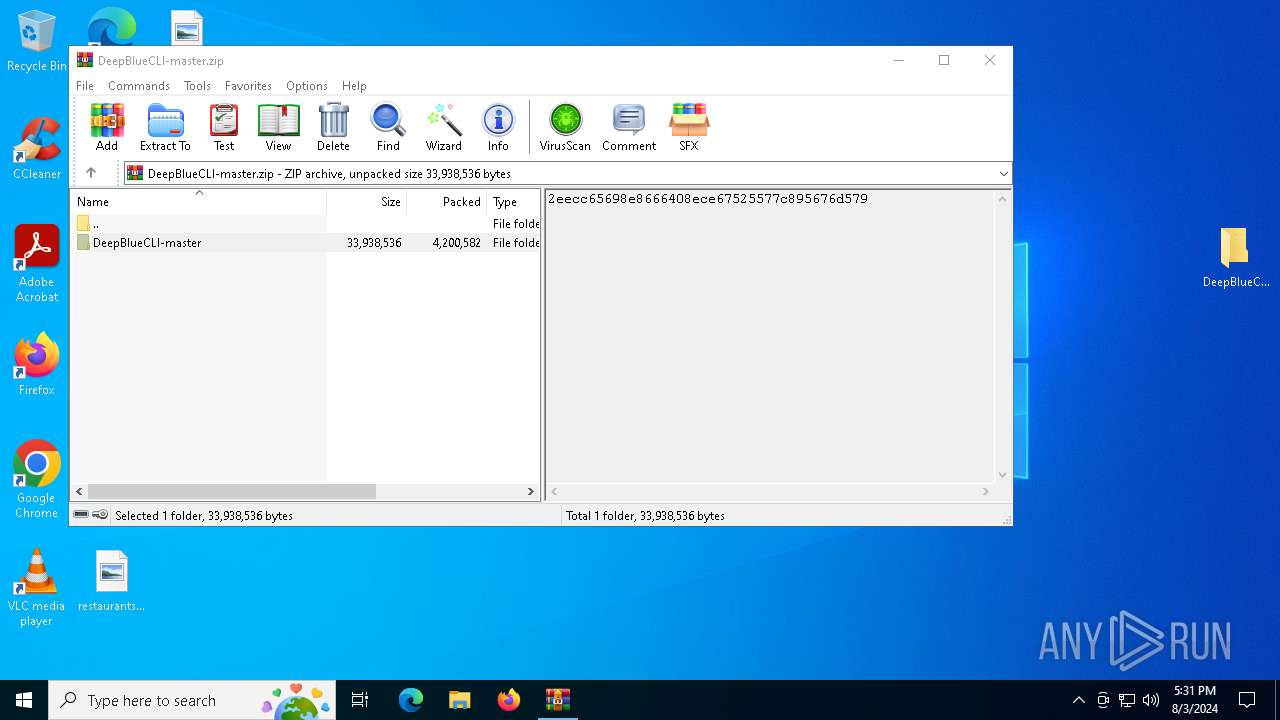
| 6456 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\DeepBlueCLI-master.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6652 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6896 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\DeepBlueCLI-master\DeepBlueHash-checker.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6956 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\DeepBlueCLI-master\DeepBlue.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6960 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\DeepBlueCLI-master\DeepBlue.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
44 528
Read events
44 520
Write events
8
Delete events
0
Modification events
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DeepBlueCLI-master.zip | |||
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6456) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
19
Text files
28
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\evtx\many-events-security.evtx | — | |
MD5:— | SHA256:— | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\evtx\many-events-system.evtx | — | |
MD5:— | SHA256:— | |||
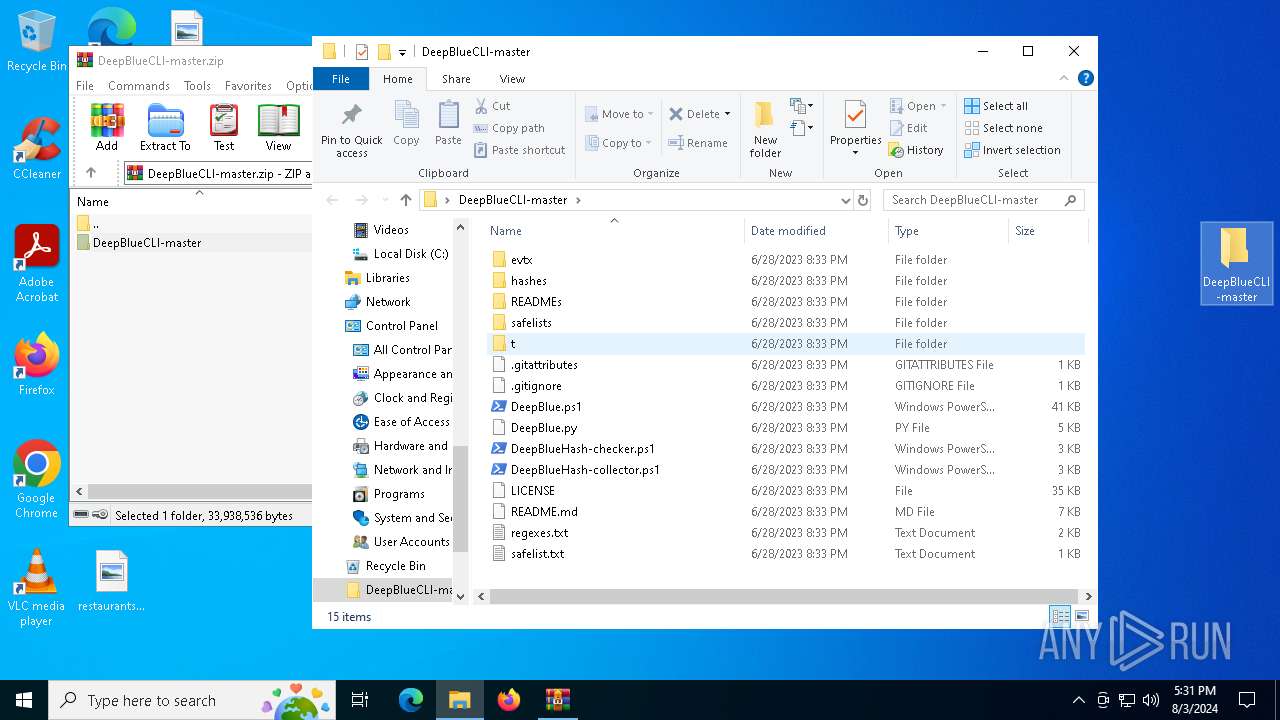
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\.gitattributes | text | |
MD5:2293876AB46E03CC868A97AE7FECC41C | SHA256:87489E8356F94C93D0BF8299AA3D6E69AA136255BE569023C5831AB4B602FA8E | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\DeepBlue.py | text | |
MD5:E2D9BC8557C825DBA716FA61DA0712C4 | SHA256:5453CE0E9F6916F22AB530668EB4C02B3F3FEDB05C37124724F6364AB9E53DE7 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\DeepBlue.ps1 | text | |
MD5:214719ABCFD6448AD28016B3E8E6D8B1 | SHA256:14B8B2496EAD140E9D63EF7535F72676934341654CC551DEDCE503911597149F | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\README.md | text | |
MD5:7046ECF5A0858CE7CE5BA63D28B78EEA | SHA256:B581AED92BE19E958312B7193A757C201E56C5B6358813A7F09B8376E1D8DC6F | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\DeepBlueHash-collector.ps1 | text | |
MD5:3B8D13778822F66D0F7AC35E8765F915 | SHA256:2D324E92B9FEDDC0CE0DAA5354FAA9233FFC9325F7657C9DD8464B20391723E7 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\DeepBlueHash-checker.ps1 | text | |
MD5:C6CA9F8A3032F64B05910059A50E7150 | SHA256:6D6FBD26E1D920C915E85F974518B81FEA4D3BFDD077153EC3D7F033D09E7C45 | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\evtx\Powershell-Invoke-Obfuscation-many.evtx | evtx | |
MD5:F6E1ECE2D6E7A1E3444CC63DB023D2F5 | SHA256:2FA243E52AB2BBA2AD3BC7A1A14EA653A1508575E703C494CFC36E78C219A5AD | |||
| 6456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6456.7456\DeepBlueCLI-master\evtx\Powershell-Invoke-Obfuscation-string-menu.evtx | evtx | |
MD5:F039588FCD0AE6BE7CBFA97AB4768BE2 | SHA256:32C7E1B5169F6F7C2C27AA1F9E7272D7EEFBA35EA13B469FB57234A17613C6AC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
42
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4132 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7160 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7136 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4160 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4080 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5336 | SearchApp.exe | 92.123.104.49:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4132 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
r.bing.com |
| whitelisted |