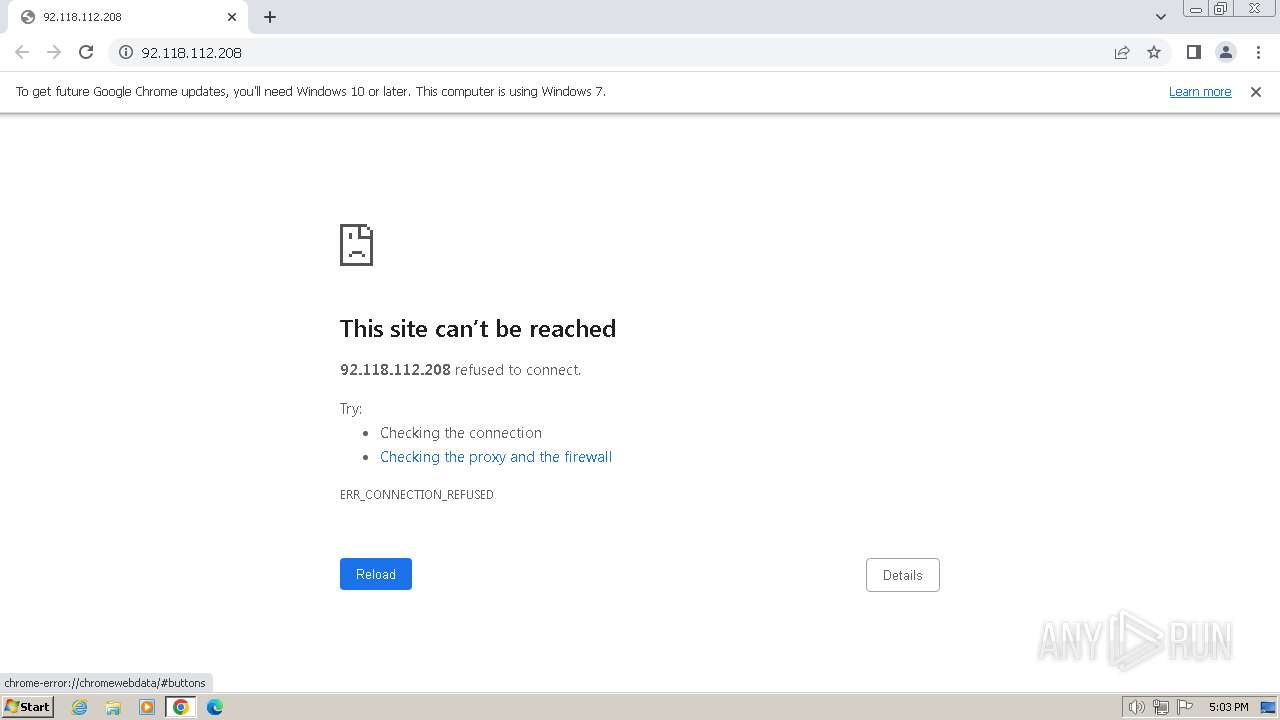
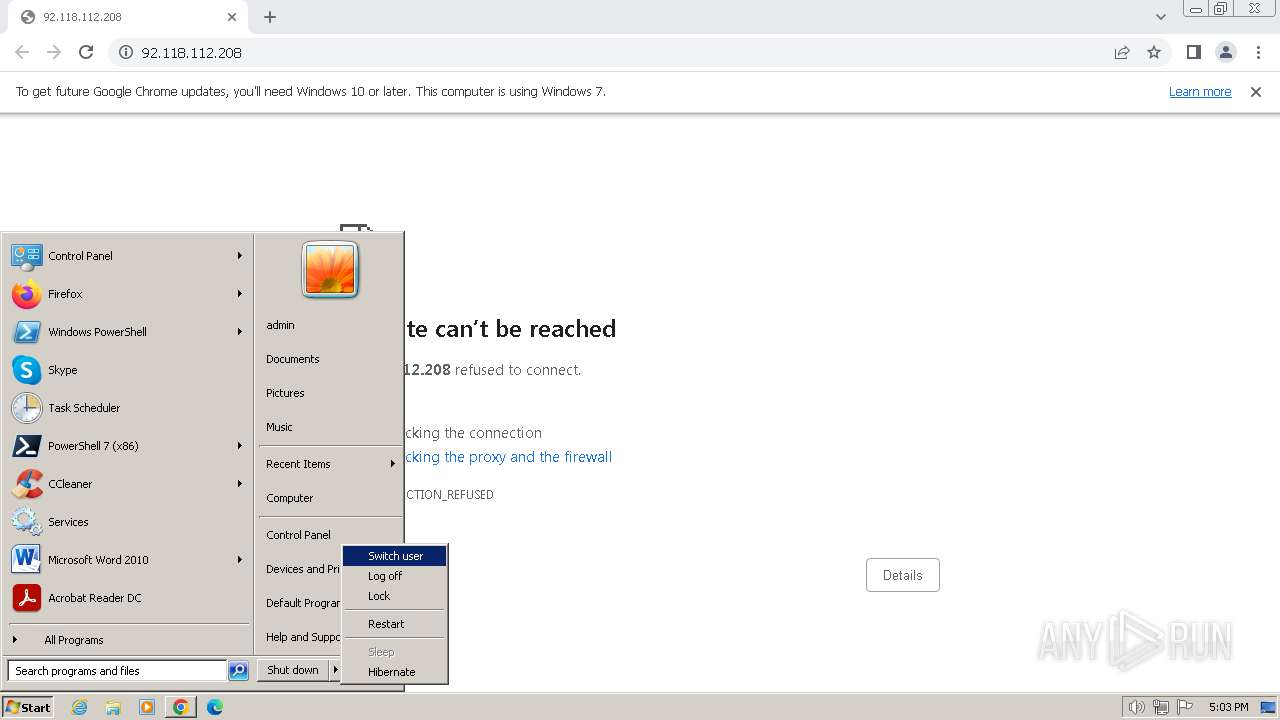
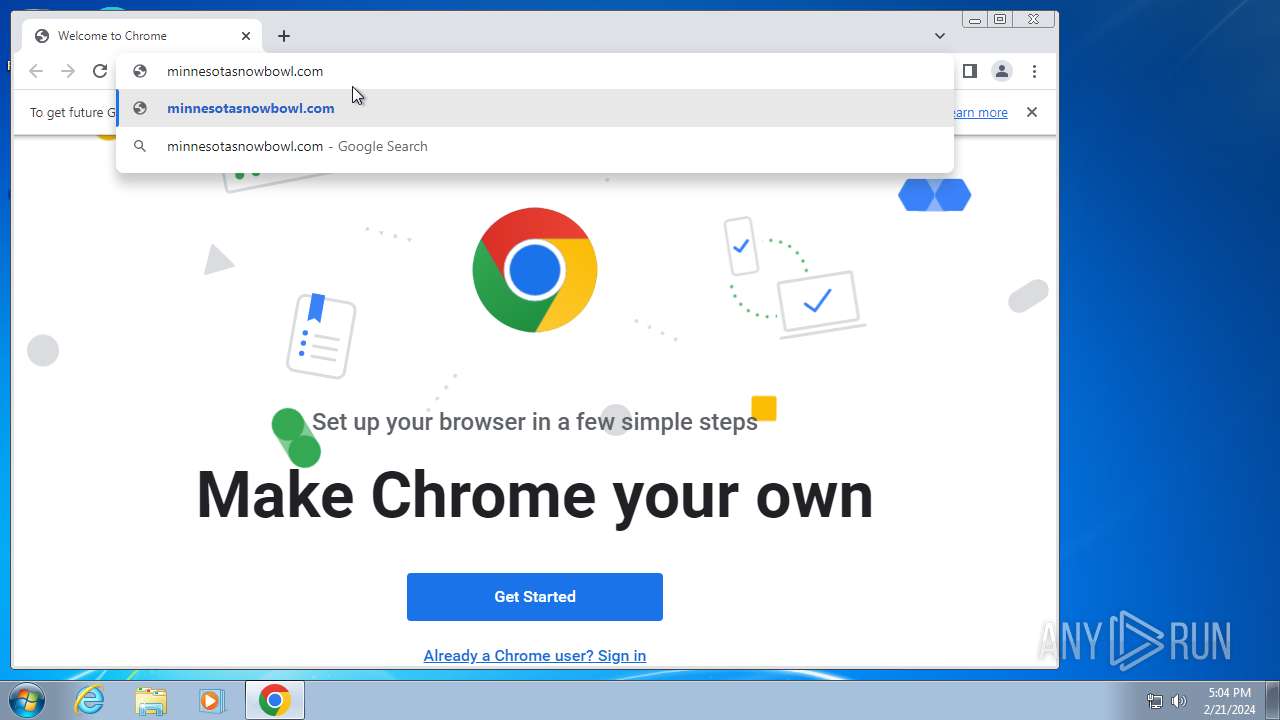
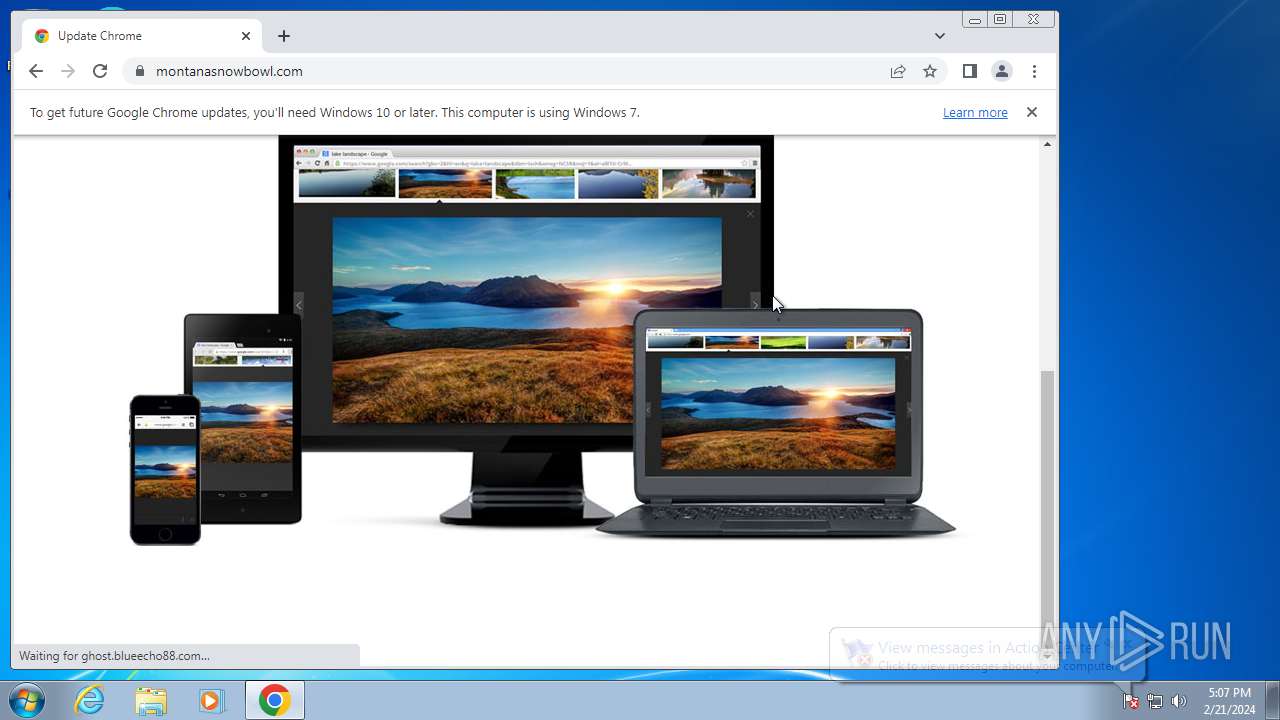
| URL: | 92.118.112.208 |
| Full analysis: | https://app.any.run/tasks/5b32343b-8125-46cc-8b7c-20452a3694ef |
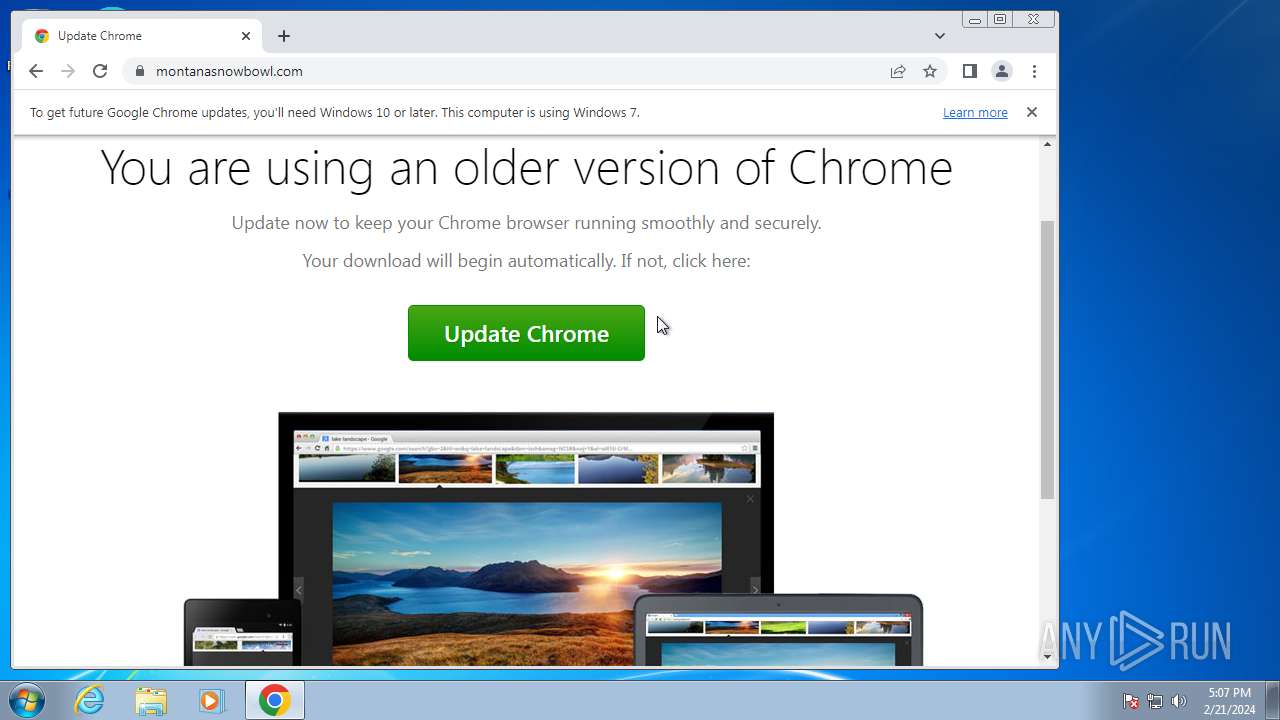
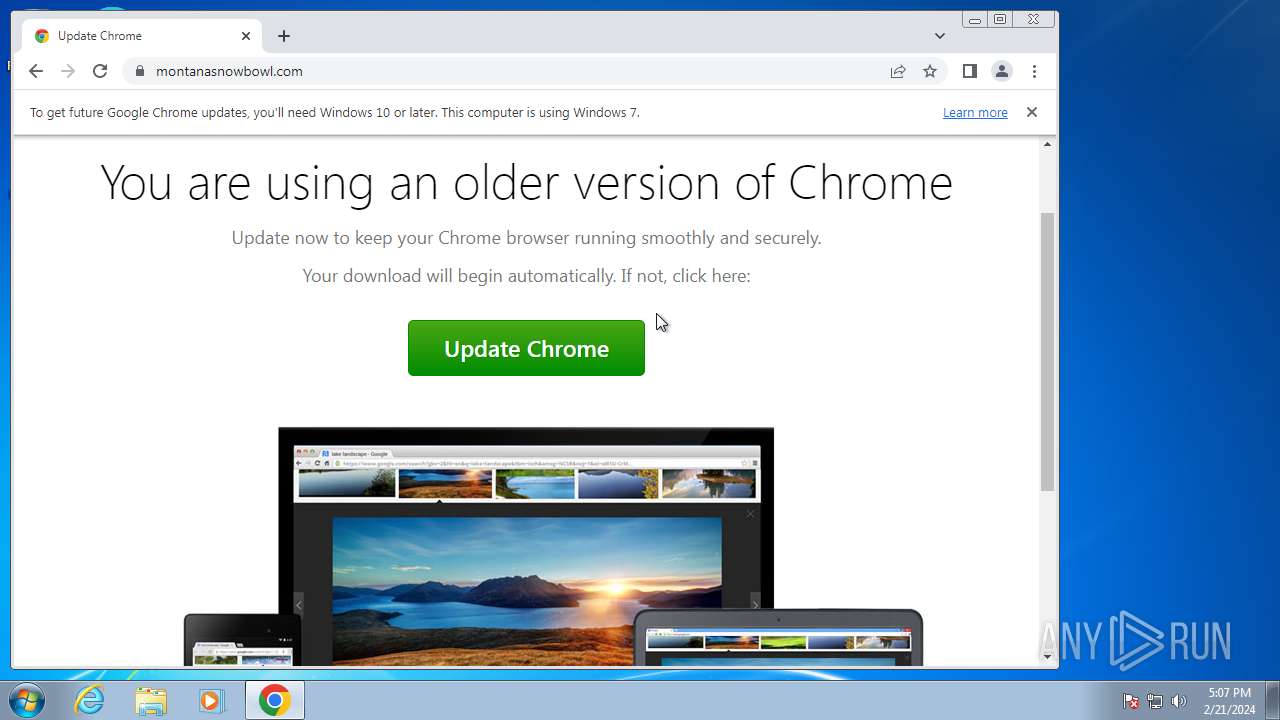
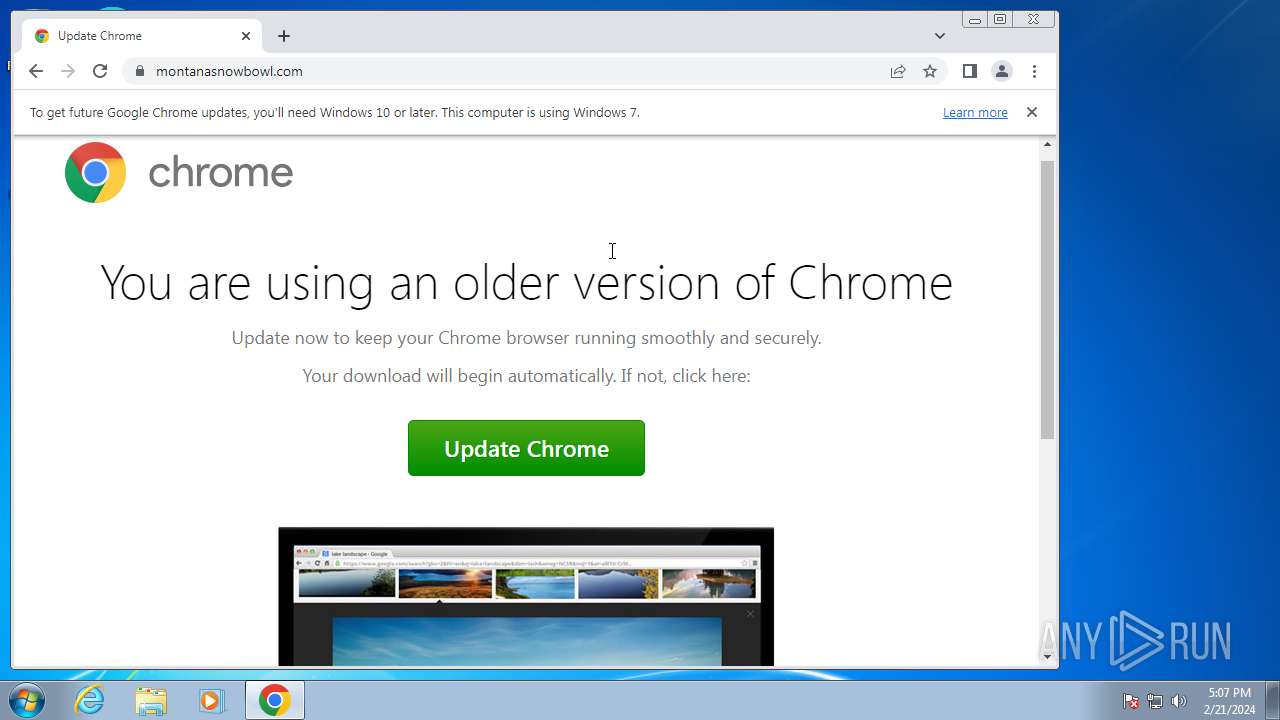
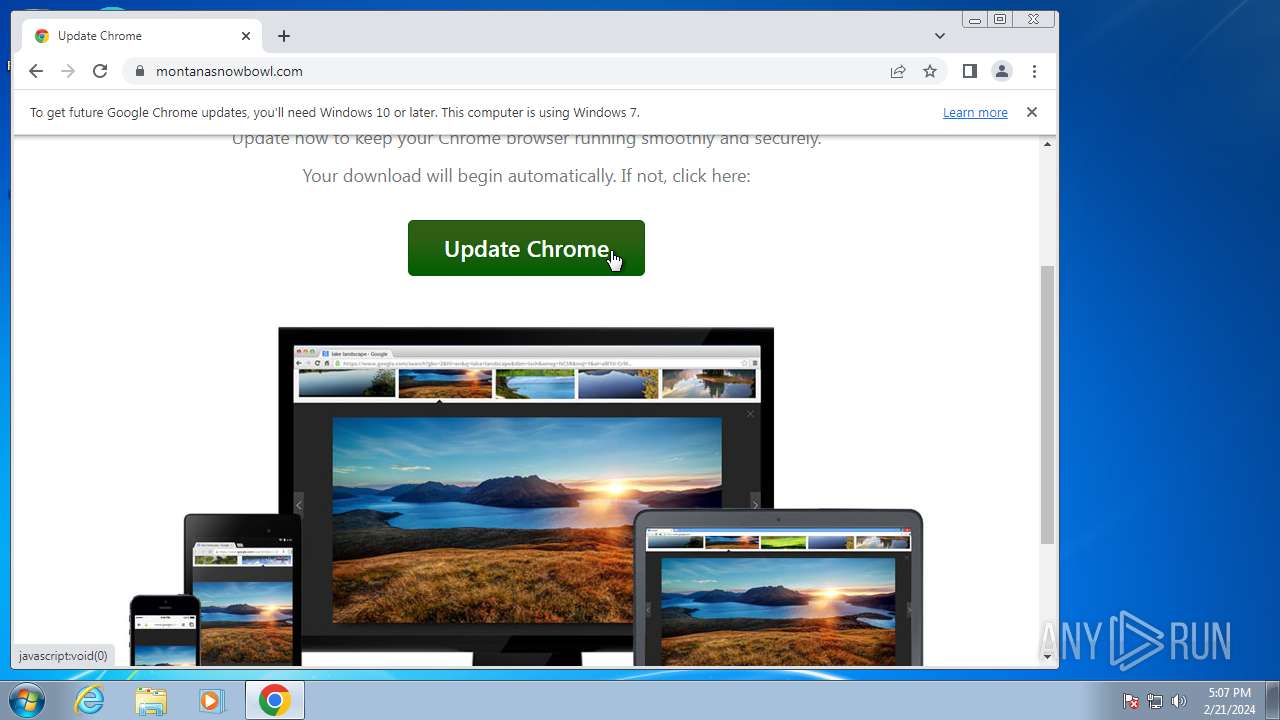
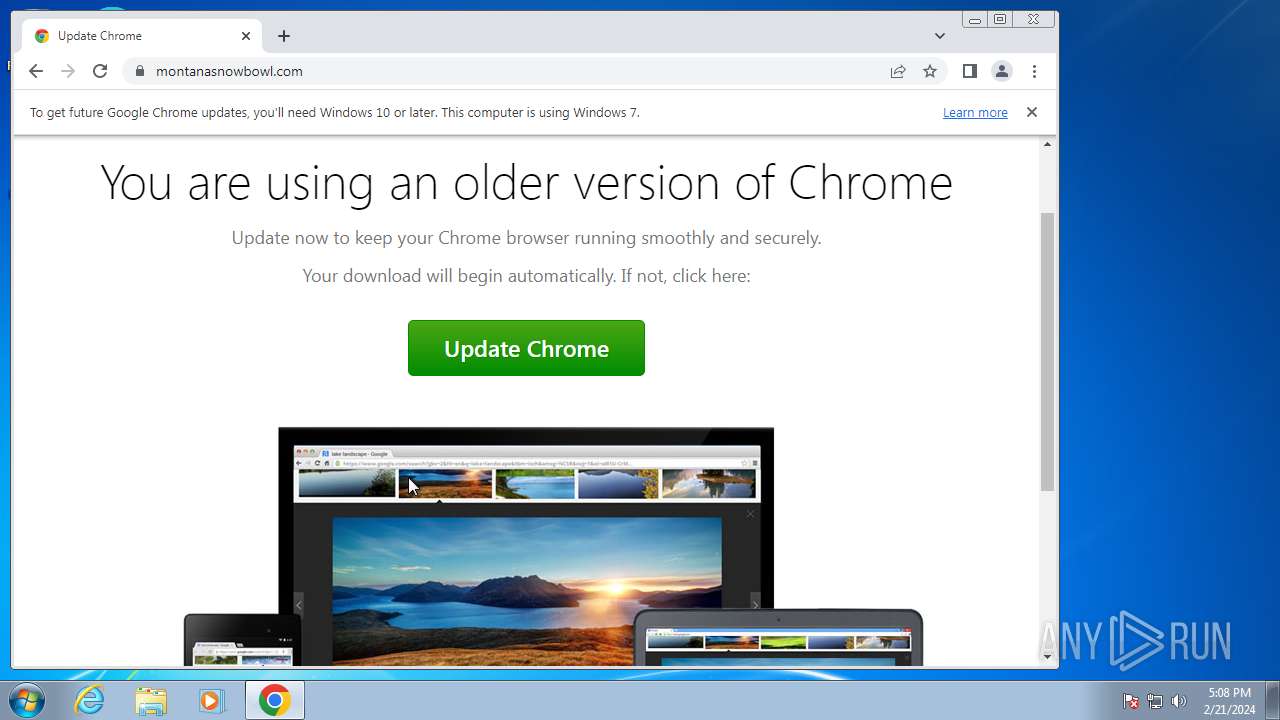
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2024, 17:03:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 13886385EDC36345E968A904E2DAAFA4 |
| SHA1: | 5E51741501319121E0800A66F32AEF0C1034AF5E |
| SHA256: | 2281686F371F395675C091536A00E3DE80E9DDE200FD4FE8E479F296ACEF18A8 |
| SSDEEP: | 3:m7xjVd:mZVd |
MALICIOUS
Steals credentials from Web Browsers
- taskhost.exe (PID: 2640)
- setup.exe (PID: 3408)
Changes the autorun value in the registry
- unregmp2.exe (PID: 1604)
- regsvr32.exe (PID: 3044)
Create files in the Startup directory
- regsvr32.exe (PID: 3044)
SUSPICIOUS
The process executes via Task Scheduler
- sipnotify.exe (PID: 3292)
Executes as Windows Service
- taskhost.exe (PID: 2640)
- EOSNotify.exe (PID: 492)
Reads the Internet Settings
- taskhost.exe (PID: 2640)
- sipnotify.exe (PID: 3292)
- ie4uinit.exe (PID: 3192)
- rundll32.exe (PID: 2828)
- rundll32.exe (PID: 1652)
- ie4uinit.exe (PID: 3468)
- ie4uinit.exe (PID: 2104)
Application launched itself
- ie4uinit.exe (PID: 3192)
- setup.exe (PID: 3408)
- rundll32.exe (PID: 2828)
Reads Internet Explorer settings
- ie4uinit.exe (PID: 3192)
Changes internet zones settings
- ie4uinit.exe (PID: 3192)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 3192)
- rundll32.exe (PID: 2828)
Reads Microsoft Outlook installation path
- ie4uinit.exe (PID: 3192)
Write to the desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 3192)
- unregmp2.exe (PID: 1604)
- regsvr32.exe (PID: 3044)
Changes default file association
- unregmp2.exe (PID: 1604)
Reads settings of System Certificates
- sipnotify.exe (PID: 3292)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 2348)
- ie4uinit.exe (PID: 3192)
- ie4uinit.exe (PID: 2104)
- ie4uinit.exe (PID: 3468)
- unregmp2.exe (PID: 1604)
- regsvr32.exe (PID: 3044)
- chrmstp.exe (PID: 3432)
- setup.exe (PID: 3408)
- IMEKLMG.EXE (PID: 748)
- IMEKLMG.EXE (PID: 1888)
- wmpnscfg.exe (PID: 2088)
- wmpnscfg.exe (PID: 984)
- chrome.exe (PID: 2820)
Application launched itself
- chrome.exe (PID: 3652)
- chrmstp.exe (PID: 3052)
- chrmstp.exe (PID: 3432)
- msedge.exe (PID: 1384)
- chrome.exe (PID: 2820)
- chrmstp.exe (PID: 3388)
- chrmstp.exe (PID: 3640)
Checks supported languages
- wmpnscfg.exe (PID: 2348)
- setup.exe (PID: 3408)
- setup.exe (PID: 3384)
- setup.exe (PID: 4040)
- IMEKLMG.EXE (PID: 748)
- IMKRMIG.EXE (PID: 1348)
- IMEKLMG.EXE (PID: 1888)
- wmpnscfg.exe (PID: 2088)
- wmpnscfg.exe (PID: 984)
Reads the computer name
- wmpnscfg.exe (PID: 2348)
- setup.exe (PID: 3384)
- setup.exe (PID: 4040)
- IMEKLMG.EXE (PID: 748)
- IMEKLMG.EXE (PID: 1888)
- wmpnscfg.exe (PID: 984)
- wmpnscfg.exe (PID: 2088)
Reads security settings of Internet Explorer
- ie4uinit.exe (PID: 3192)
- sipnotify.exe (PID: 3292)
Creates files in the program directory
- ie4uinit.exe (PID: 3192)
- chrmstp.exe (PID: 3052)
- chrmstp.exe (PID: 3432)
- setup.exe (PID: 3384)
- setup.exe (PID: 3408)
- setup.exe (PID: 4040)
- chrome.exe (PID: 2820)
- chrmstp.exe (PID: 3388)
- chrmstp.exe (PID: 3640)
Reads the software policy settings
- sipnotify.exe (PID: 3292)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 748)
- IMEKLMG.EXE (PID: 1888)
The process uses the downloaded file
- chrome.exe (PID: 4808)
- chrome.exe (PID: 4792)
- chrome.exe (PID: 5116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
154
Monitored processes
104
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2948 --field-trial-handle=1136,i,7843692125598411617,8209331122657371988,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4400 --field-trial-handle=1104,i,8712336130314779224,17282285379263865098,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1948 --field-trial-handle=1104,i,8712336130314779224,17282285379263865098,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 492 | C:\Windows\system32\EOSNotify.exe | C:\Windows\System32\EOSNotify.exe | — | services.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: EOS Notification Exit code: 0 Version: 6.1.7601.24544 (win7sp1_ldr_escrow.191230-1647) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=2996 --field-trial-handle=1104,i,8712336130314779224,17282285379263865098,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=1992 --field-trial-handle=1104,i,8712336130314779224,17282285379263865098,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Common Files\Microsoft Shared\IME14\IMEKR\imkrmig.exe" | C:\Program Files\Common Files\Microsoft Shared\IME14\IMEKR\IMKRMIG.EXE | — | IMEKLMG.EXE | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft IME 2010 Exit code: 0 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1380 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\System32\rundll32.exe | — | rundll32.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
35 401
Read events
33 779
Write events
1 382
Delete events
240
Modification events
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
11
Suspicious files
383
Text files
259
Unknown types
162
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF180d59.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF180fd9.TMP | text | |
MD5:B36B68CE4A71A5BFAF89A4D1CC07893F | SHA256:6422CC04455EF100D67FD9F299AACFEF3BA4F77D0FA1D2440D89E7D1CF65EBBC | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1815c5.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2df3299a-c816-4938-a3b7-b7ee8c6683cc.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF18299b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
121
DNS requests
100
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3292 | sipnotify.exe | HEAD | 200 | 104.102.39.173:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133530086277820000 | unknown | — | — | unknown |
1576 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | unknown | binary | 242 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | — | — | unknown |
3292 | sipnotify.exe | GET | 200 | 104.102.39.173:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133530086277820000 | unknown | compressed | 78.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | binary | 5.47 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | binary | 10.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | binary | 10.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | binary | 8.15 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adtp63xadzqu6yysjolme33hjxoq_20220505/dhlpobdgcjafebgbbhjdnapejmpkgiie_20220505_all_adfdqqtvlhuhhtrt6irlkpynghca.crx3 | unknown | binary | 35.1 Kb | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nte52k4gxkjl7s2fodjn67y2aa_867/efniojlnjndmcbiieegkicadnoecjjef_867_all_aciammajgupabp5xgx45thseb7vq.crx3 | unknown | binary | 148 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
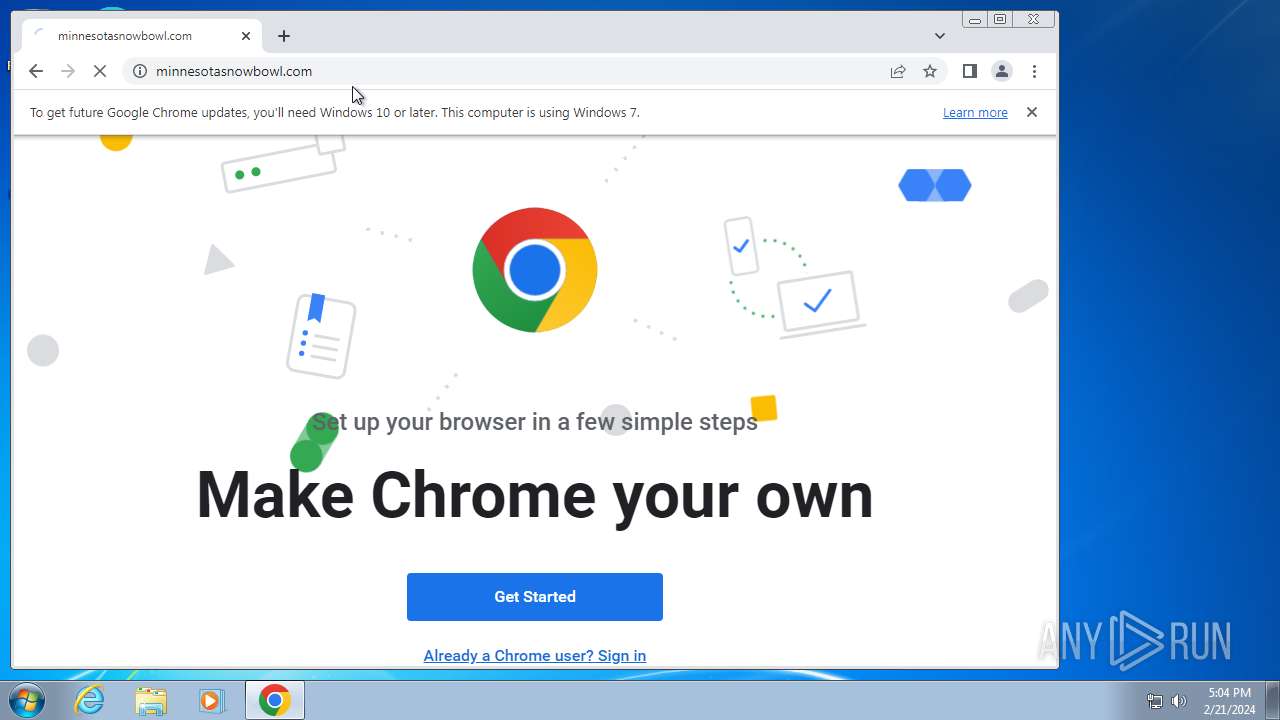
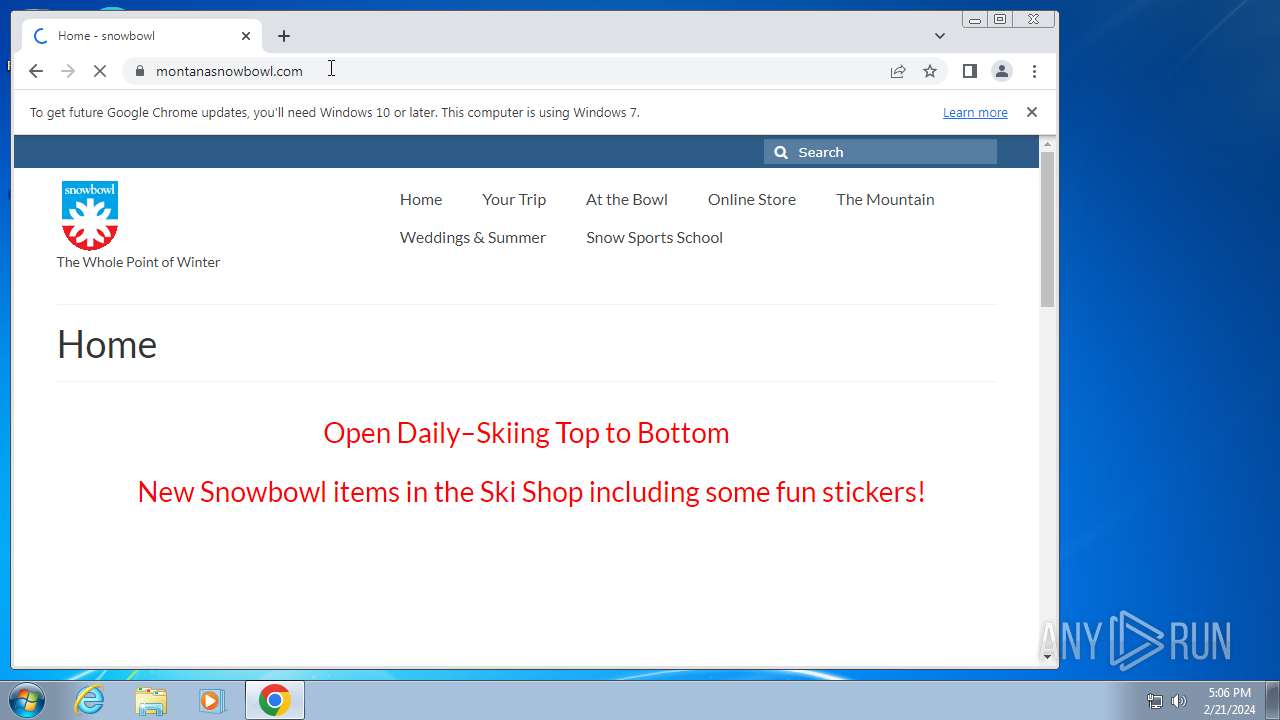
3304 | chrome.exe | 92.118.112.208:80 | — | Adman LLC | RU | unknown |
3652 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3304 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
3304 | chrome.exe | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
3652 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3292 | sipnotify.exe | 104.102.39.173:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | unknown |
3304 | chrome.exe | 142.250.186.74:443 | www.googleapis.com | GOOGLE | US | whitelisted |
2820 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-4g5ednss.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1576 | chrome.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (ghost .blueecho88 .com) |
1576 | chrome.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (ghost .blueecho88 .com) |
1576 | chrome.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in TLS SNI (ghost .blueecho88 .com) |
1576 | chrome.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |