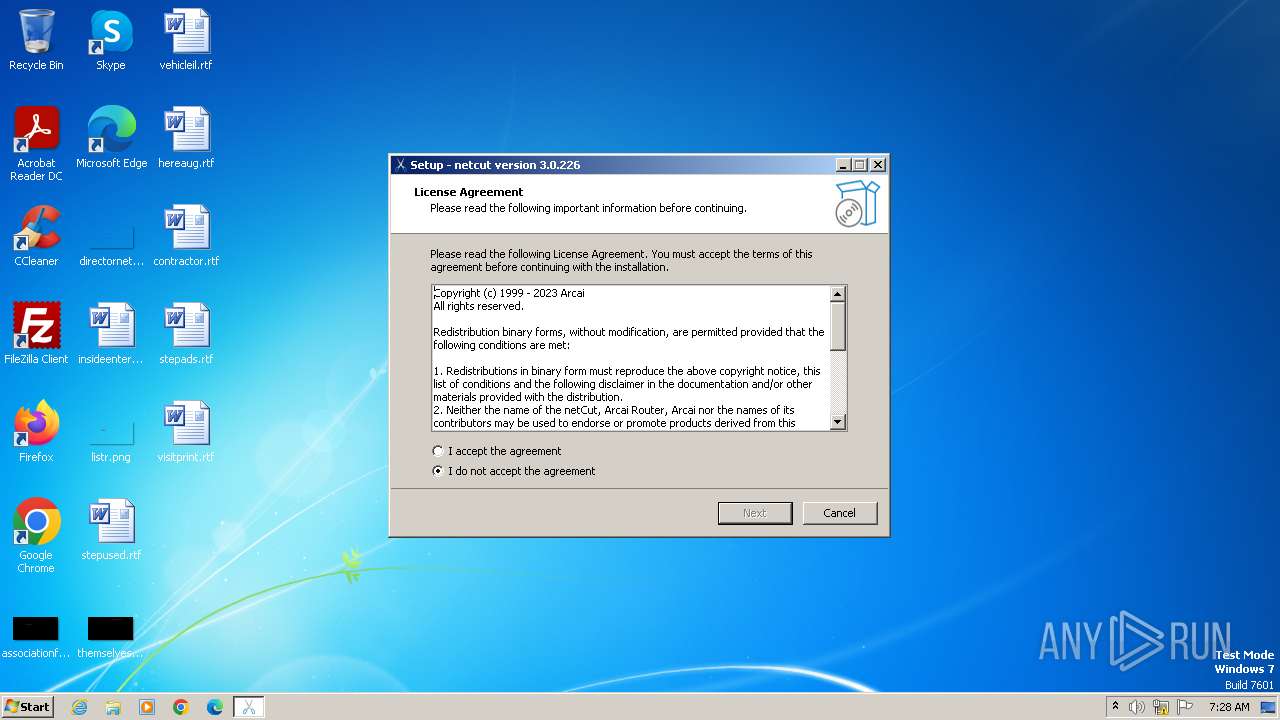
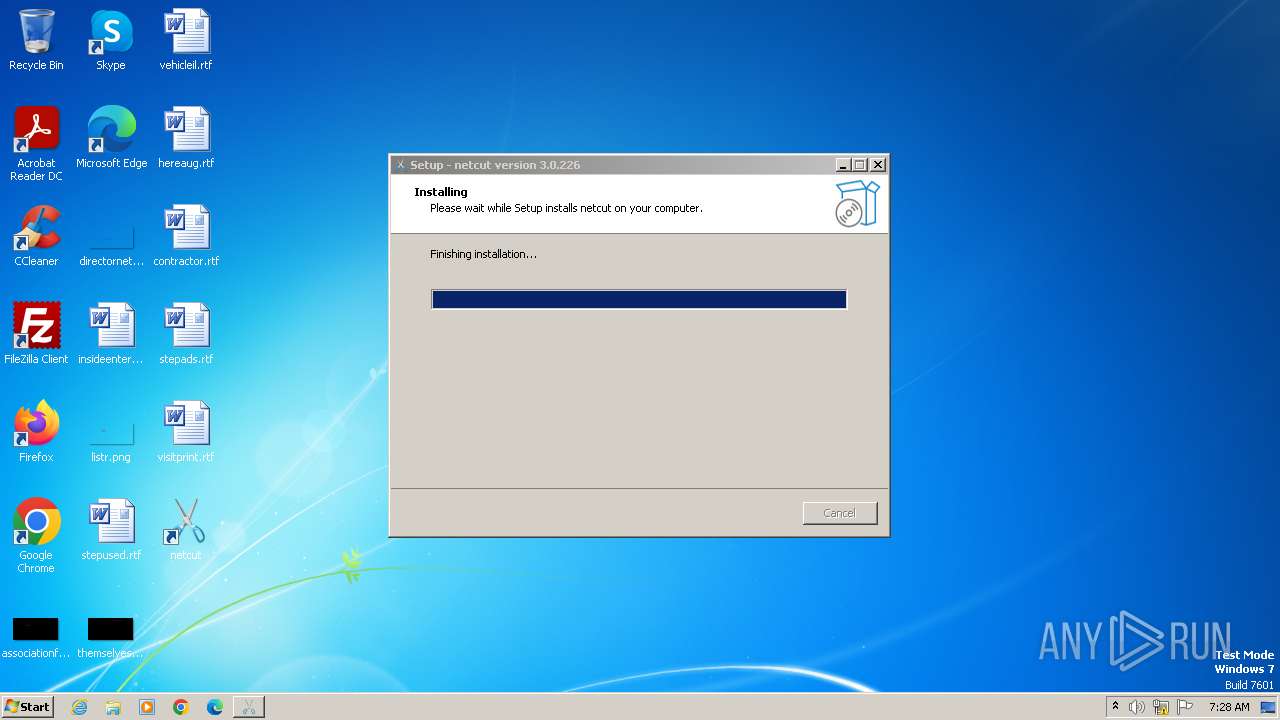
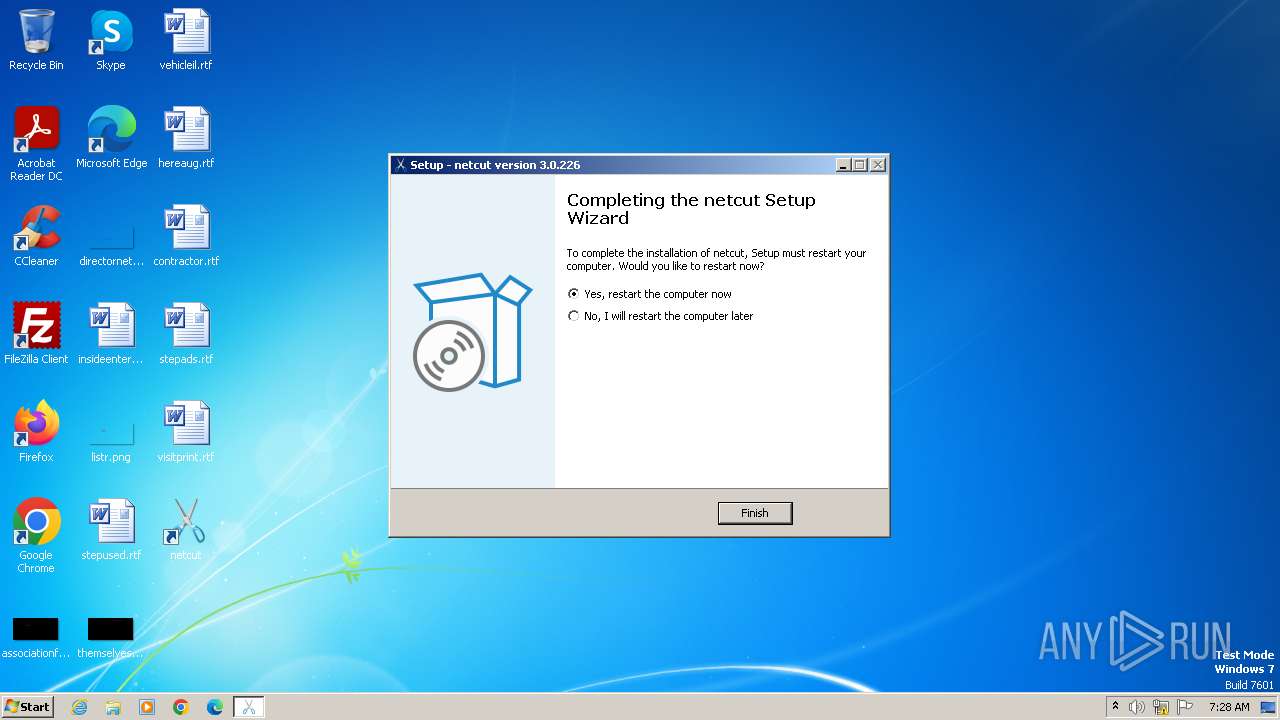
| File name: | netcut.exe |
| Full analysis: | https://app.any.run/tasks/2346dce1-0855-4013-8839-d3534ffadf7f |
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2023, 07:28:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B339BF3E08630D0BB7508989EE28AF25 |
| SHA1: | 8756572B47529432C25C565E706ED978F8F98F03 |
| SHA256: | 227B9530737E4026818CD0E2BBBE1FDE8235C82A57EC2197C29F5CCA468F53A8 |
| SSDEEP: | 98304:GkLKOfW+FeZrag8HWy/PGYAx8qCjt3MKjCP:xXW+UraP/zTl8KuP |
MALICIOUS
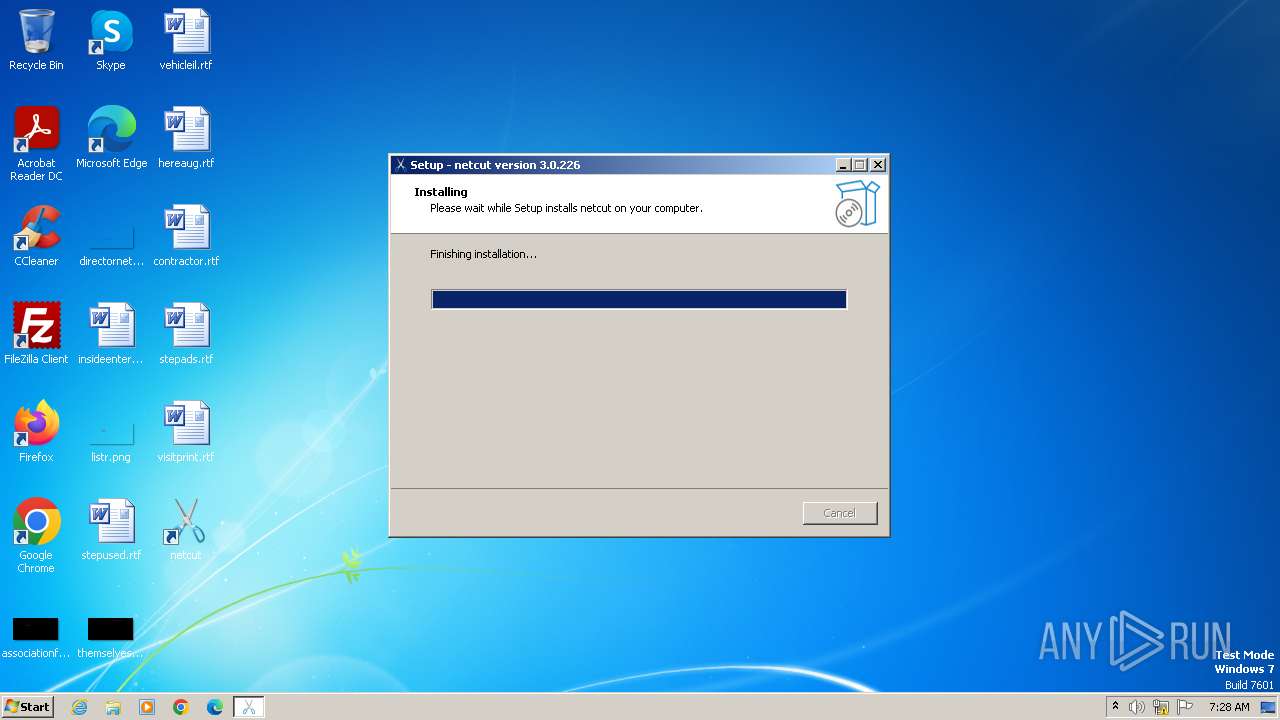
Drops the executable file immediately after the start
- netcut.exe (PID: 2532)
- netcut.exe (PID: 1864)
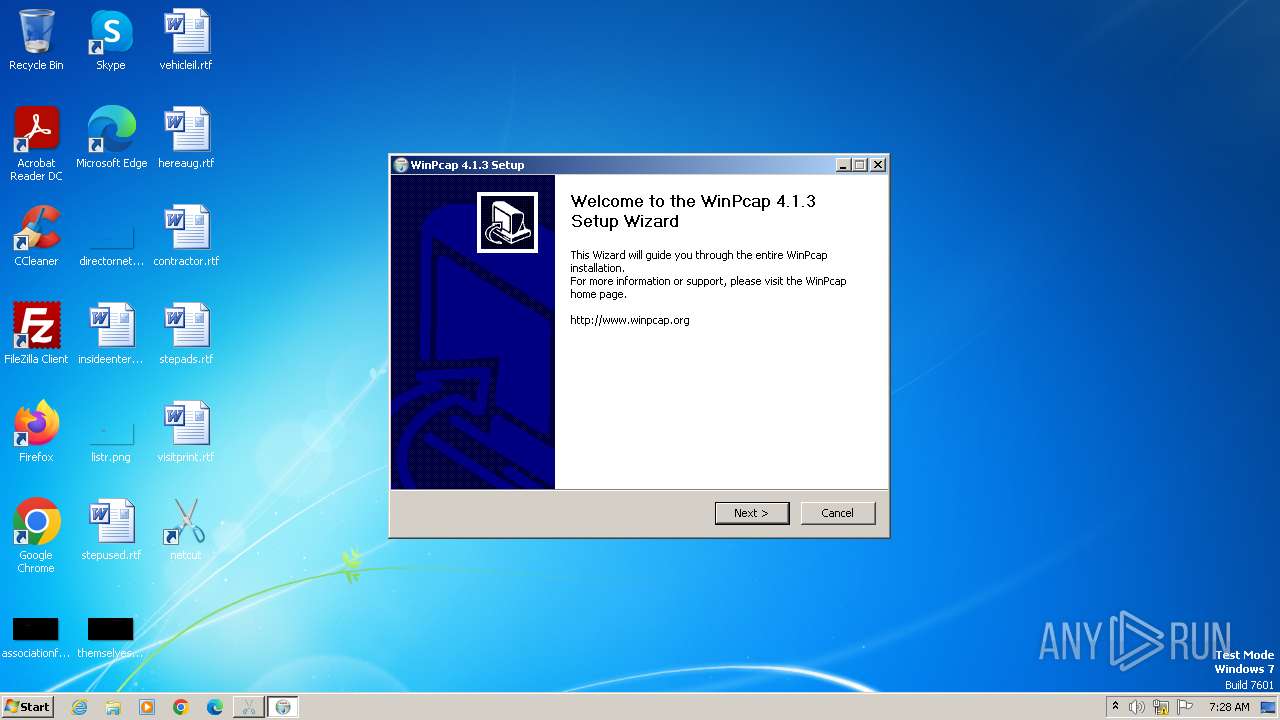
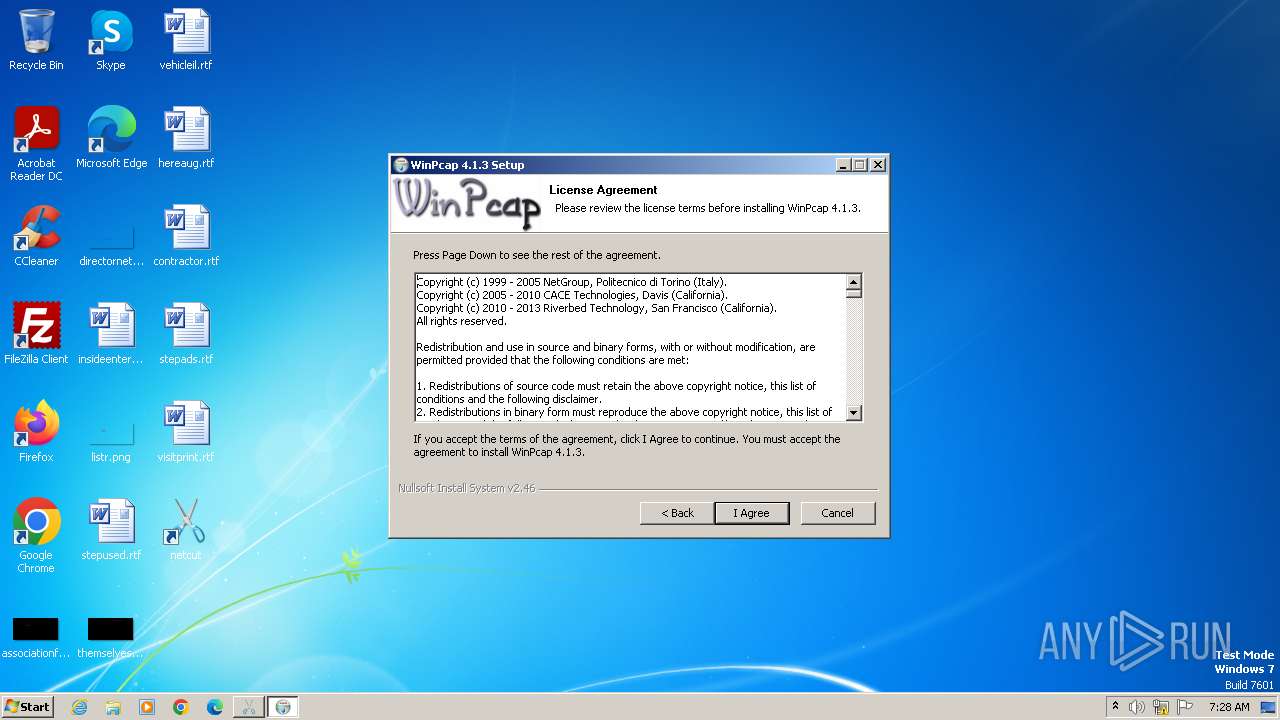
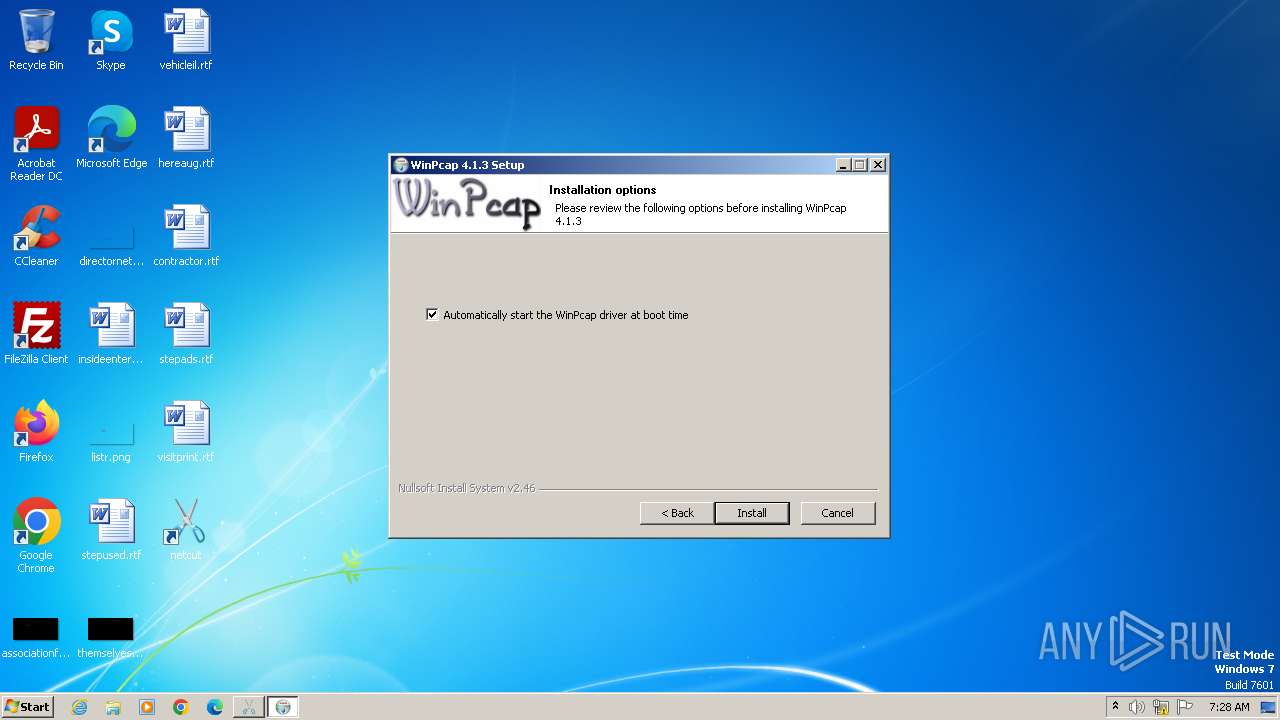
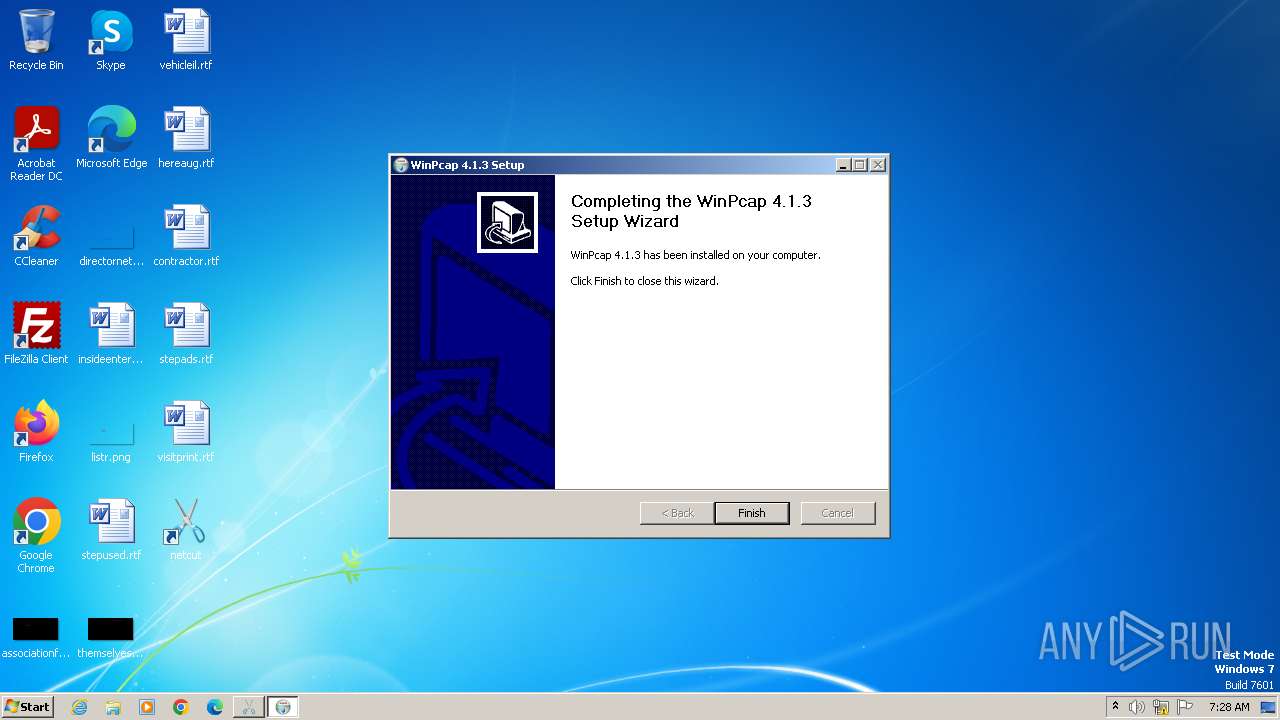
- WinPcap_4_1_3.exe (PID: 3080)
- netcut.tmp (PID: 2108)
Creates a writable file in the system directory
- WinPcap_4_1_3.exe (PID: 3080)
- netcut_windows.exe (PID: 2276)
Starts NET.EXE for service management
- WinPcap_4_1_3.exe (PID: 3080)
- net.exe (PID: 3276)
SUSPICIOUS
Reads the Windows owner or organization settings
- netcut.tmp (PID: 2108)
The process drops C-runtime libraries
- netcut.tmp (PID: 2108)
Process drops legitimate windows executable
- netcut.tmp (PID: 2108)
Starts SC.EXE for service management
- netcut.tmp (PID: 2108)
Drops a system driver (possible attempt to evade defenses)
- WinPcap_4_1_3.exe (PID: 3080)
Malware-specific behavior (creating "System.dll" in Temp)
- WinPcap_4_1_3.exe (PID: 3080)
Creates files in the driver directory
- WinPcap_4_1_3.exe (PID: 3080)
The process creates files with name similar to system file names
- WinPcap_4_1_3.exe (PID: 3080)
Creates or modifies Windows services
- WinPcap_4_1_3.exe (PID: 3080)
Executes as Windows Service
- aips.exe (PID: 2984)
Starts CMD.EXE for commands execution
- aips.exe (PID: 2984)
Reads the Internet Settings
- netcut.tmp (PID: 1556)
- sipnotify.exe (PID: 1700)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1480)
- sipnotify.exe (PID: 1700)
Reads settings of System Certificates
- sipnotify.exe (PID: 1700)
Connects to unusual port
- netcut_windows.exe (PID: 2276)
INFO
Create files in a temporary directory
- netcut.exe (PID: 1864)
- WinPcap_4_1_3.exe (PID: 3080)
- netcut.exe (PID: 2532)
Creates files or folders in the user directory
- netcut.tmp (PID: 2108)
Checks supported languages
- WinPcap_4_1_3.exe (PID: 3080)
- netcut.tmp (PID: 2108)
- netcut.exe (PID: 1864)
- netcut.tmp (PID: 1556)
- aips.exe (PID: 2072)
- aips.exe (PID: 2984)
- netcut_windows.exe (PID: 3936)
- netcut_windows.exe (PID: 3092)
- IMEKLMG.EXE (PID: 408)
- IMEKLMG.EXE (PID: 2060)
- netcut_windows.exe (PID: 2244)
- netcut_windows.exe (PID: 2276)
- wmpnscfg.exe (PID: 2704)
- wmpnscfg.exe (PID: 2748)
- wmpnscfg.exe (PID: 3068)
- netcut.exe (PID: 2532)
Reads Environment values
- WinPcap_4_1_3.exe (PID: 3080)
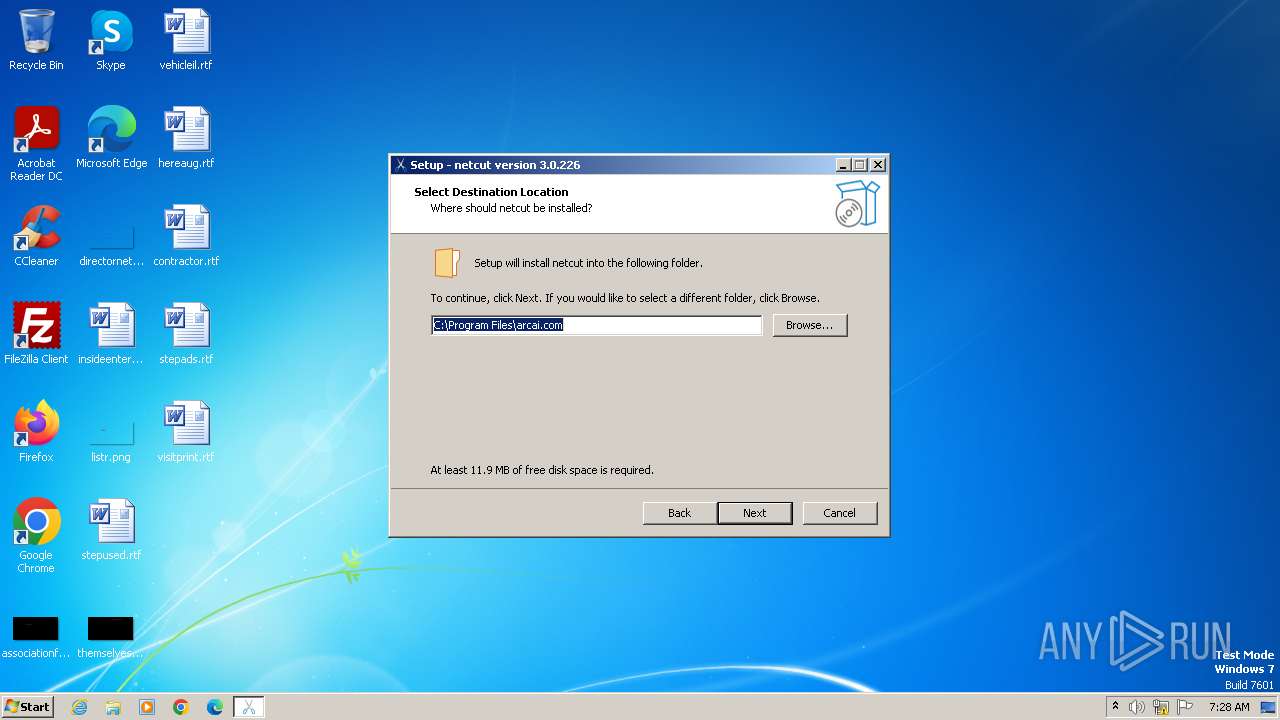
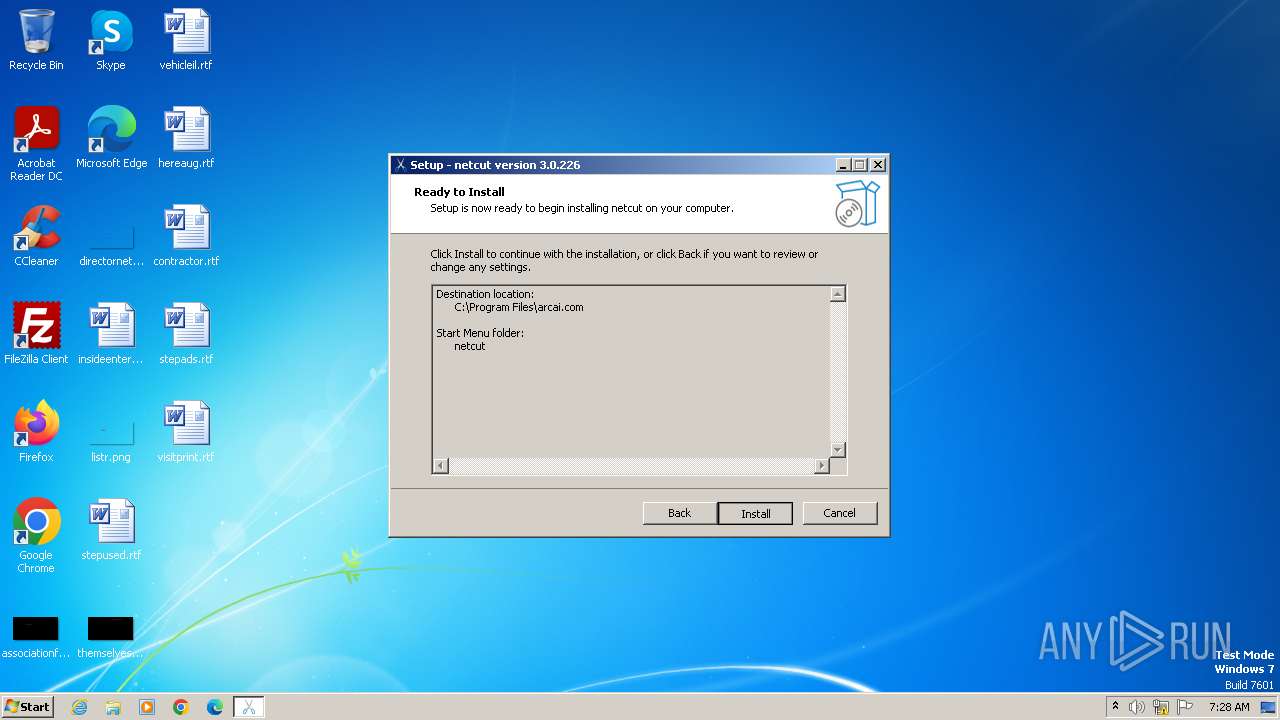
Creates files in the program directory
- netcut.tmp (PID: 2108)
- WinPcap_4_1_3.exe (PID: 3080)
- netcut_windows.exe (PID: 2276)
Reads the computer name
- WinPcap_4_1_3.exe (PID: 3080)
- netcut.tmp (PID: 1556)
- aips.exe (PID: 2072)
- aips.exe (PID: 2984)
- netcut_windows.exe (PID: 3092)
- netcut.exe (PID: 1864)
- IMEKLMG.EXE (PID: 408)
- IMEKLMG.EXE (PID: 2060)
- netcut_windows.exe (PID: 2276)
- wmpnscfg.exe (PID: 2704)
- wmpnscfg.exe (PID: 2748)
- wmpnscfg.exe (PID: 3068)
- netcut.tmp (PID: 2108)
Reads the machine GUID from the registry
- netcut_windows.exe (PID: 3092)
- netcut_windows.exe (PID: 2276)
Application launched itself
- msedge.exe (PID: 3556)
Manual execution by a user
- IMEKLMG.EXE (PID: 408)
- IMEKLMG.EXE (PID: 2060)
- wmpnscfg.exe (PID: 2704)
- wmpnscfg.exe (PID: 2748)
- wmpnscfg.exe (PID: 3068)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1700)
Process checks are UAC notifies on
- IMEKLMG.EXE (PID: 2060)
- IMEKLMG.EXE (PID: 408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:04:14 18:10:23+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 133120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | arcai.com |
| FileDescription: | netcut Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | netcut |
| ProductVersion: | 3.0.226 |
Total processes
121
Monitored processes
30
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1016 | C:\Windows\system32\net1 start npf | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1480 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\Temp\is-HTQJL.tmp\netcut.tmp" /SL5="$1B0142,4285390,876032,C:\Users\admin\AppData\Local\Temp\netcut.exe" | C:\Users\admin\AppData\Local\Temp\is-HTQJL.tmp\netcut.tmp | — | netcut.exe | |||||||||||
User: admin Company: arcai.com Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1700 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\Temp\netcut.exe" | C:\Users\admin\AppData\Local\Temp\netcut.exe | — | explorer.exe | |||||||||||
User: admin Company: arcai.com Integrity Level: MEDIUM Description: netcut Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\arcai.com\aips.exe" install | C:\Program Files\arcai.com\aips.exe | — | netcut.tmp | |||||||||||
User: admin Company: Arcai.com Integrity Level: HIGH Description: Arp Intelligent Protection Service Exit code: 1 Version: 214 Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\AppData\Local\Temp\is-D4F8F.tmp\netcut.tmp" /SL5="$1801F0,4285390,876032,C:\Users\admin\AppData\Local\Temp\netcut.exe" /SPAWNWND=$180194 /NOTIFYWND=$1B0142 | C:\Users\admin\AppData\Local\Temp\is-D4F8F.tmp\netcut.tmp | — | netcut.exe | |||||||||||
User: admin Company: arcai.com Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2244 --field-trial-handle=1260,i,18328365570645118995,12640780371941476504,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
7 363
Read events
7 326
Write events
31
Delete events
6
Modification events
| (PID) Process: | (3080) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\NPF |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 8A1A1F2B695E2F00 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (3556) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 1 | |||
Executable files
26
Suspicious files
57
Text files
28
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | netcut.exe | C:\Users\admin\AppData\Local\Temp\is-D4F8F.tmp\netcut.tmp | executable | |
MD5:5B0A08B2C0DCD9034A73A9EAC02432BE | SHA256:465837EA5B381B4F000B29A74448C02E1DFC8E5D8C32231FBB4919B5DE5AECA3 | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\unins000.exe | executable | |
MD5:5B0A08B2C0DCD9034A73A9EAC02432BE | SHA256:465837EA5B381B4F000B29A74448C02E1DFC8E5D8C32231FBB4919B5DE5AECA3 | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\is-Q9MTS.tmp | executable | |
MD5:A11A2F0CFE6D0B4C50945989DB6360CD | SHA256:FC4623B113A1F603C0D9AD5F83130BD6DE1C62B973BE9892305132389C8588DE | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\msvcr120.dll | executable | |
MD5:034CCADC1C073E4216E9466B720F9849 | SHA256:86E39B5995AF0E042FCDAA85FE2AEFD7C9DDC7AD65E6327BD5E7058BC3AB615F | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\is-V8DA8.tmp | executable | |
MD5:6D17ABC0B89BDC8BA7014D912A947FB9 | SHA256:1B08657C59B410A7B83556DC788CA50131C03737550EFF31AFDF3A01F79235DB | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\is-LGDSS.tmp | text | |
MD5:527FA19FEF2324A6FA9EBE504B13A957 | SHA256:B4A61D49CB5140083D583278BF4E15E46FFE3BF0B916B89F0916C5374166D0E3 | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\is-HRH1O.tmp | executable | |
MD5:C8954F9EE1955D3B9A253758F1224190 | SHA256:D747B71F54C58E131BDEC5C3DB271E5883962B83283C31F4FC0E518685A80291 | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\WinPcap_4_1_3.exe | executable | |
MD5:A11A2F0CFE6D0B4C50945989DB6360CD | SHA256:FC4623B113A1F603C0D9AD5F83130BD6DE1C62B973BE9892305132389C8588DE | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\macdata | text | |
MD5:527FA19FEF2324A6FA9EBE504B13A957 | SHA256:B4A61D49CB5140083D583278BF4E15E46FFE3BF0B916B89F0916C5374166D0E3 | |||
| 2108 | netcut.tmp | C:\Program Files\arcai.com\is-DN3RD.tmp | executable | |
MD5:5B0A08B2C0DCD9034A73A9EAC02432BE | SHA256:465837EA5B381B4F000B29A74448C02E1DFC8E5D8C32231FBB4919B5DE5AECA3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
67
DNS requests
110
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1112 | aips.exe | GET | 200 | 188.114.97.3:80 | http://www.arcai.com/netCut/Update3.php?query=bmFtZT1uZXRjdXRfd2luZG93cy5leGU6dmVyc2lvbj0yMjY= | unknown | text | 12 b | unknown |
1700 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133470989317650000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3092 | netcut_windows.exe | 172.105.129.132:443 | load.arcai.com | Linode, LLC | US | unknown |
3092 | netcut_windows.exe | 188.114.96.3:443 | www.arcai.com | CLOUDFLARENET | NL | unknown |
1700 | sipnotify.exe | 23.197.138.118:80 | query.prod.cms.rt.microsoft.com | Akamai International B.V. | US | unknown |
1156 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2276 | netcut_windows.exe | 172.105.129.132:443 | load.arcai.com | Linode, LLC | US | unknown |
2276 | netcut_windows.exe | 188.114.97.3:443 | www.arcai.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.arcai.com |
| whitelisted |
load.arcai.com |
| unknown |
query.prod.cms.rt.microsoft.com |
| whitelisted |
svc.arcai.com |
| unknown |
loadcache.arcai.com |
| unknown |
dns.yandex.ru |
| whitelisted |
secondary.family.dns.yandex.ru |
| unknown |
dns-unfiltered.adguard.com |
| unknown |
ns1.recursive.dnsbycomodo.com |
| unknown |
familyshield.opendns.com |
| unknown |